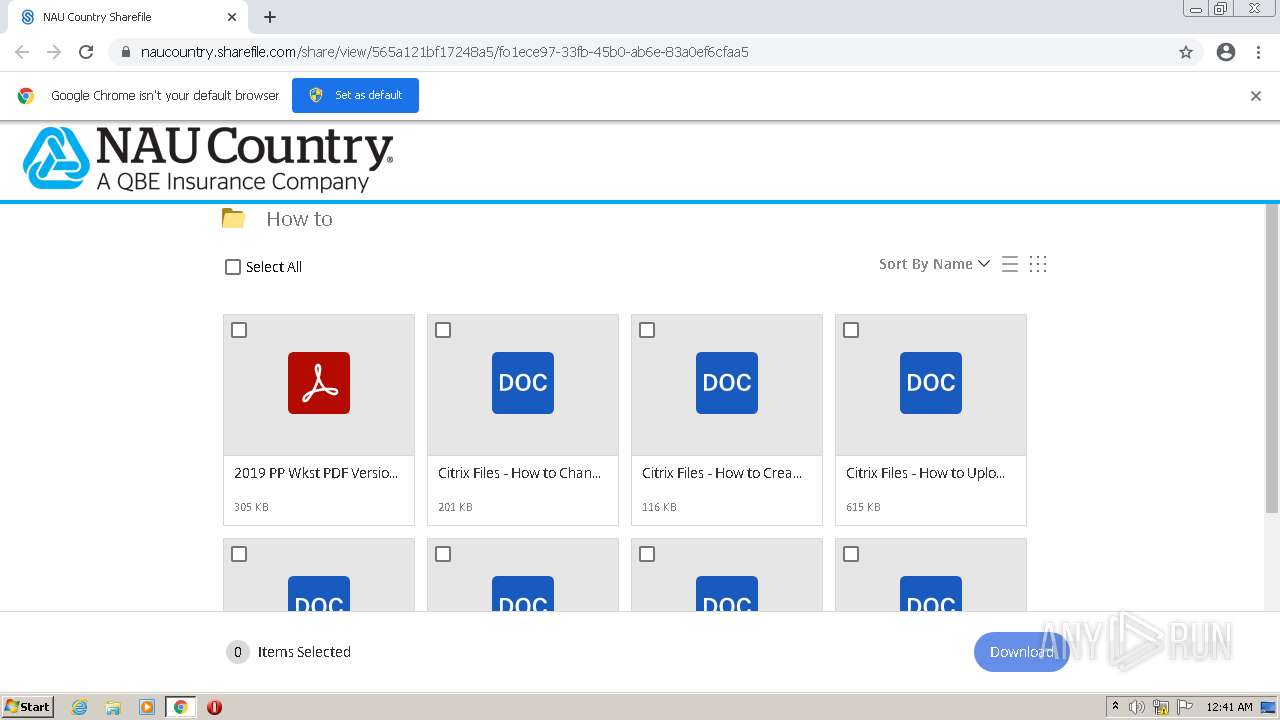
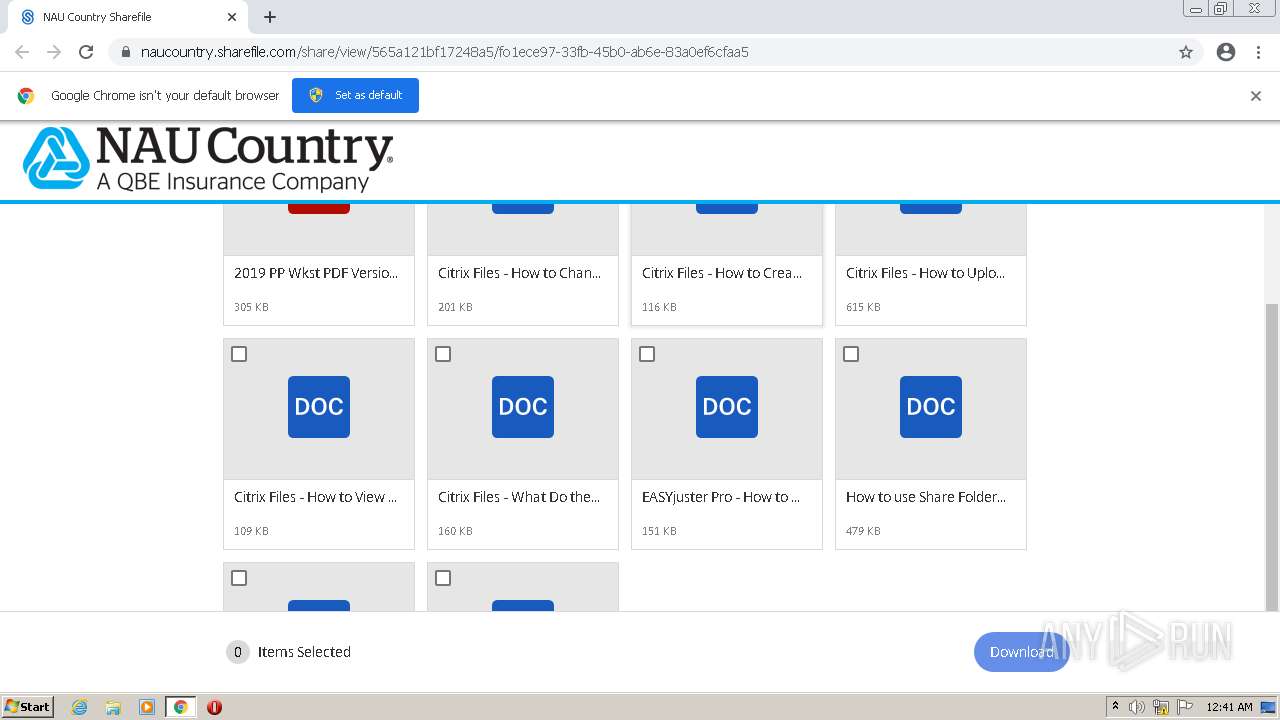
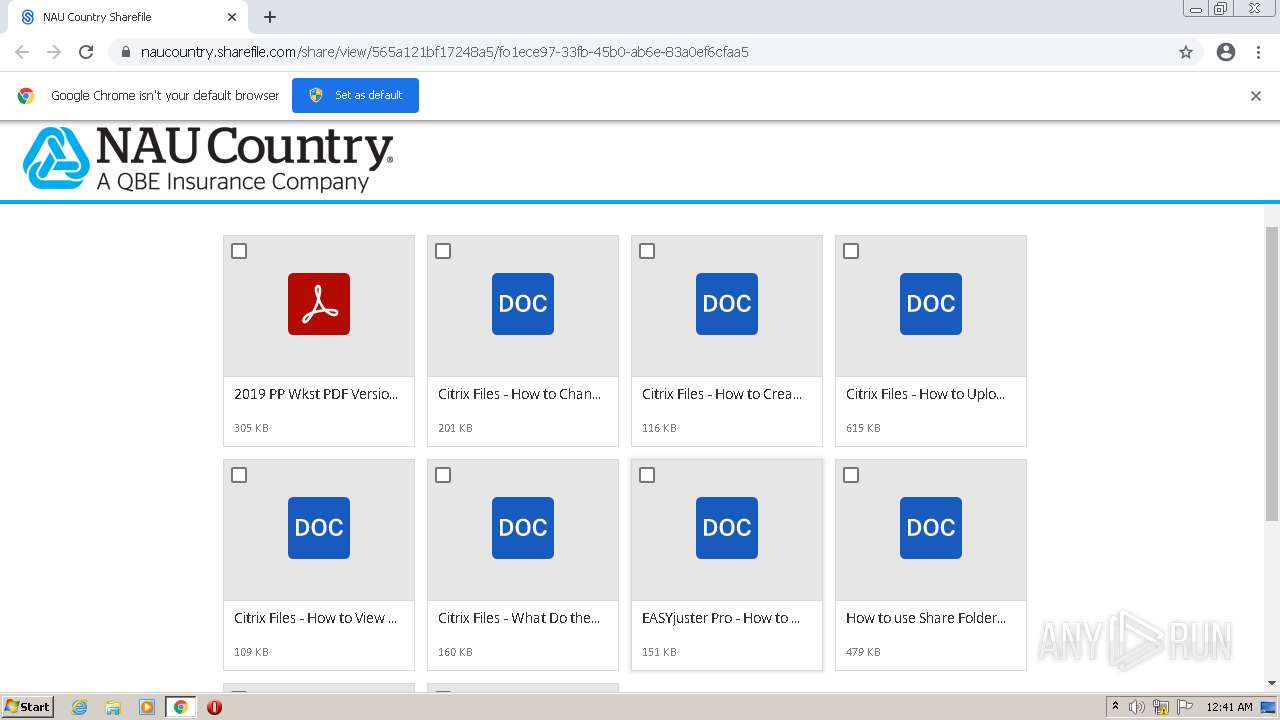
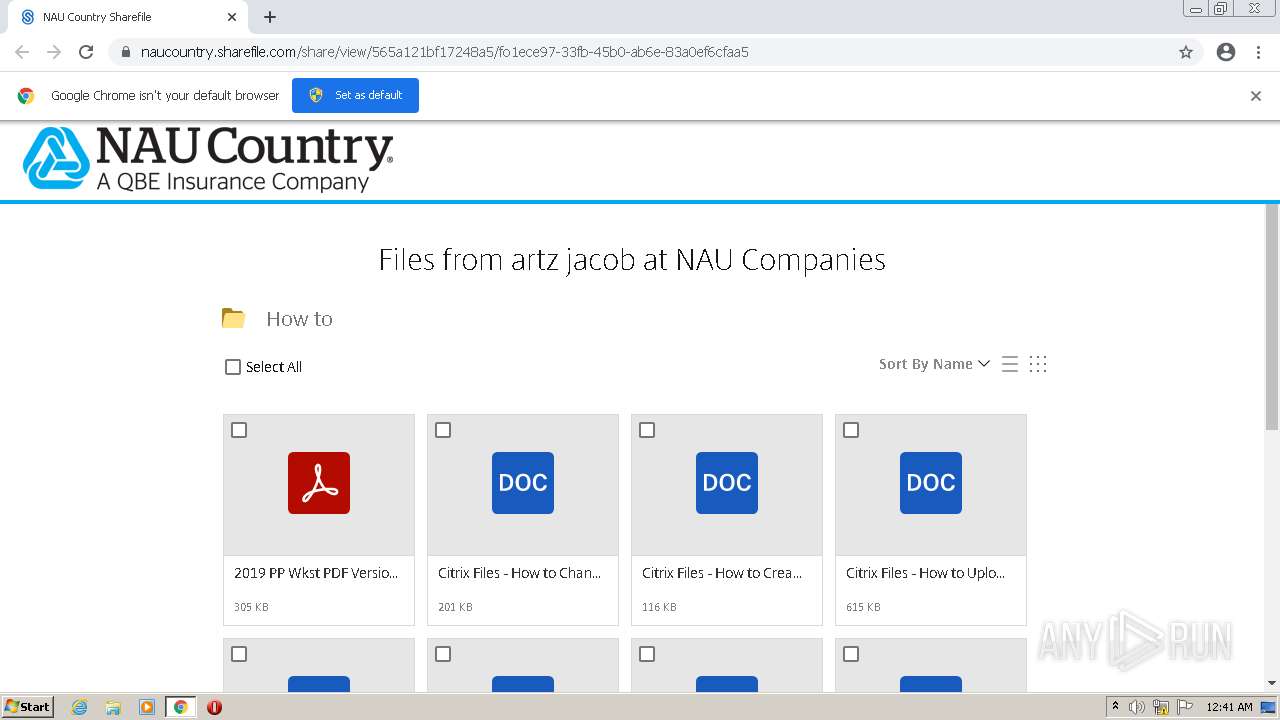
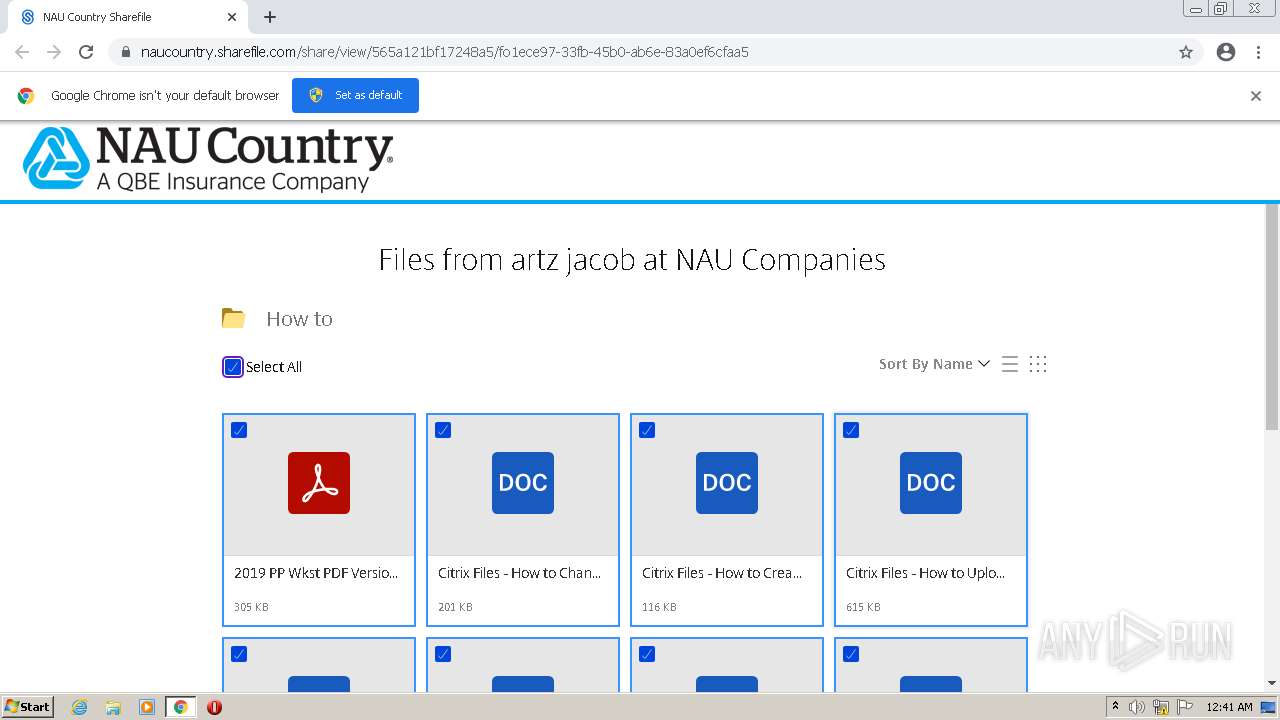
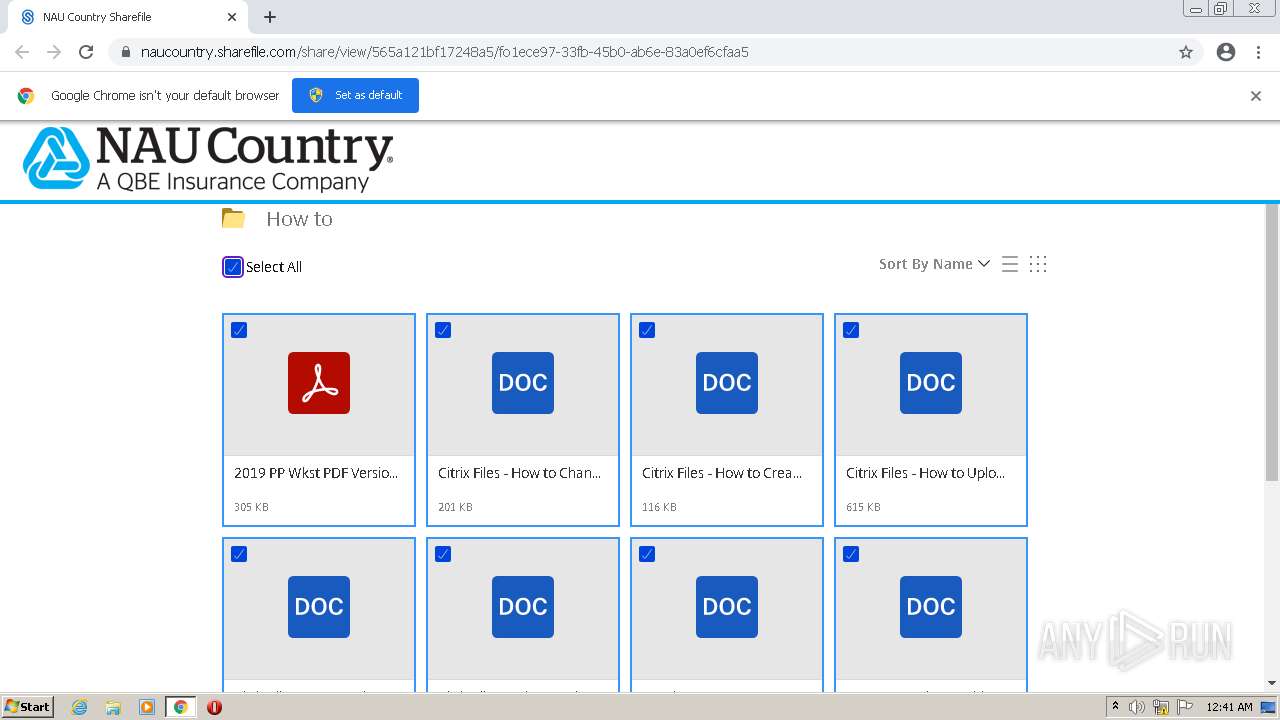
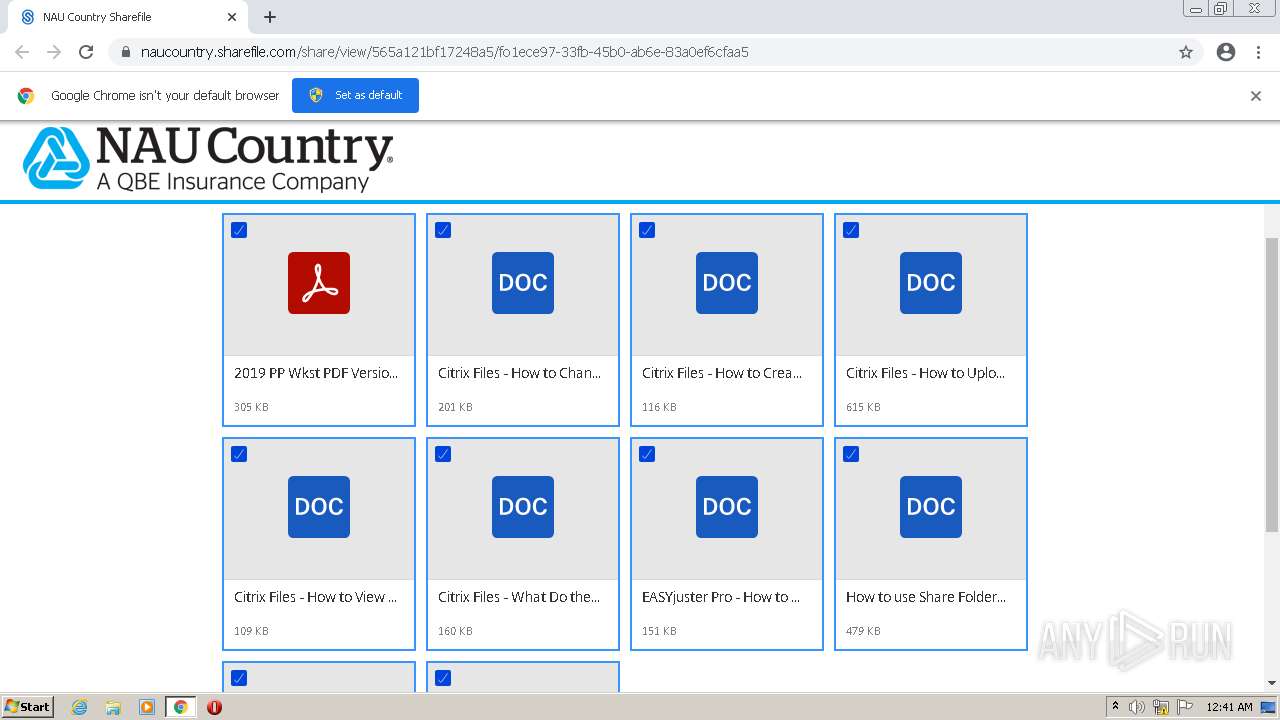
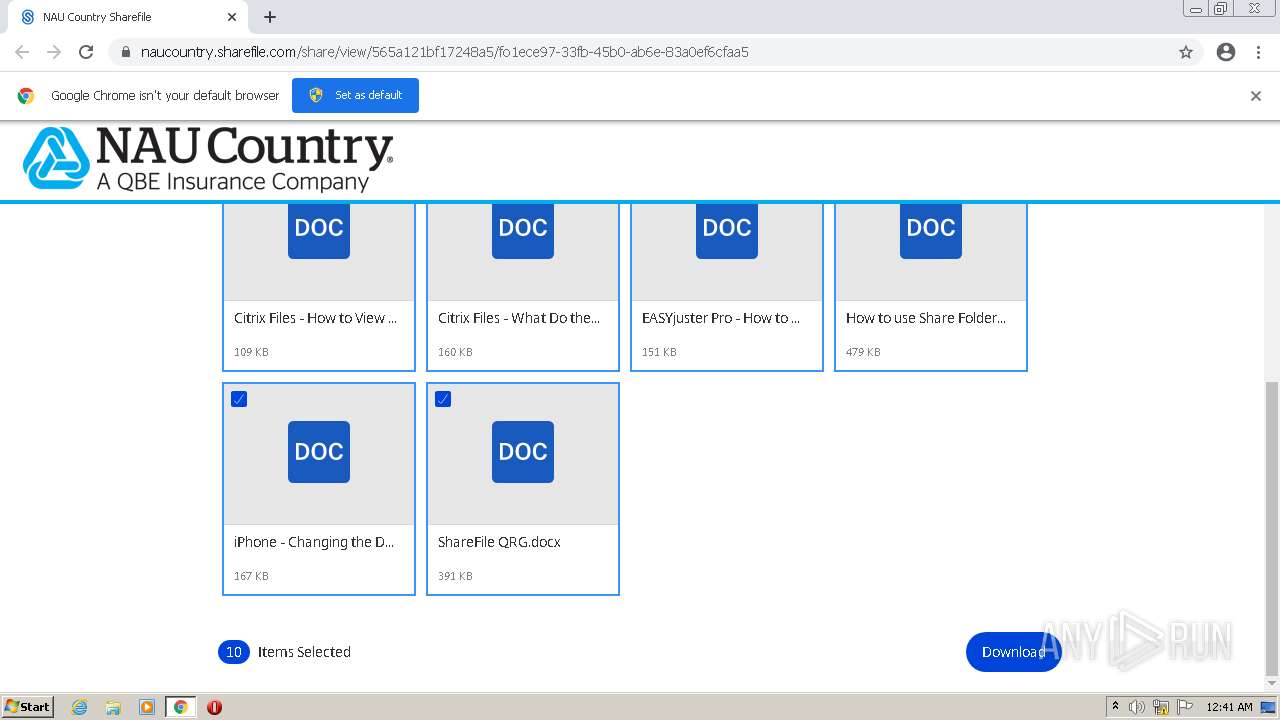
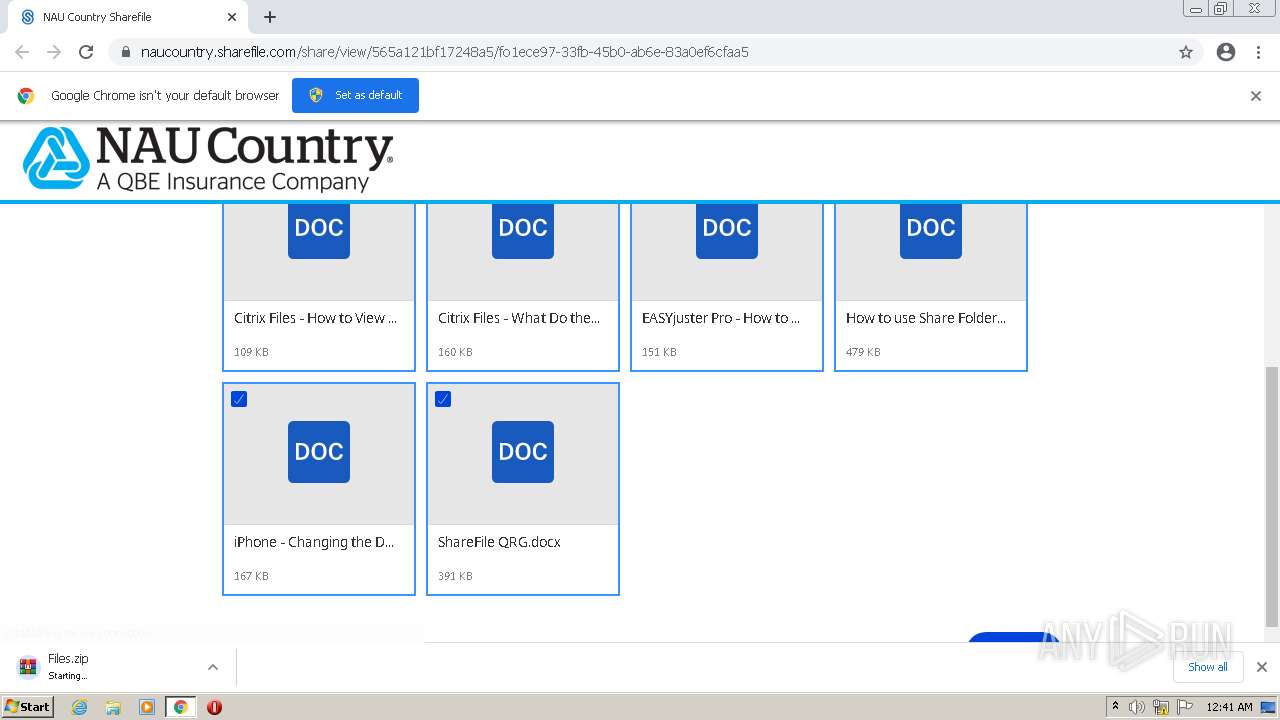
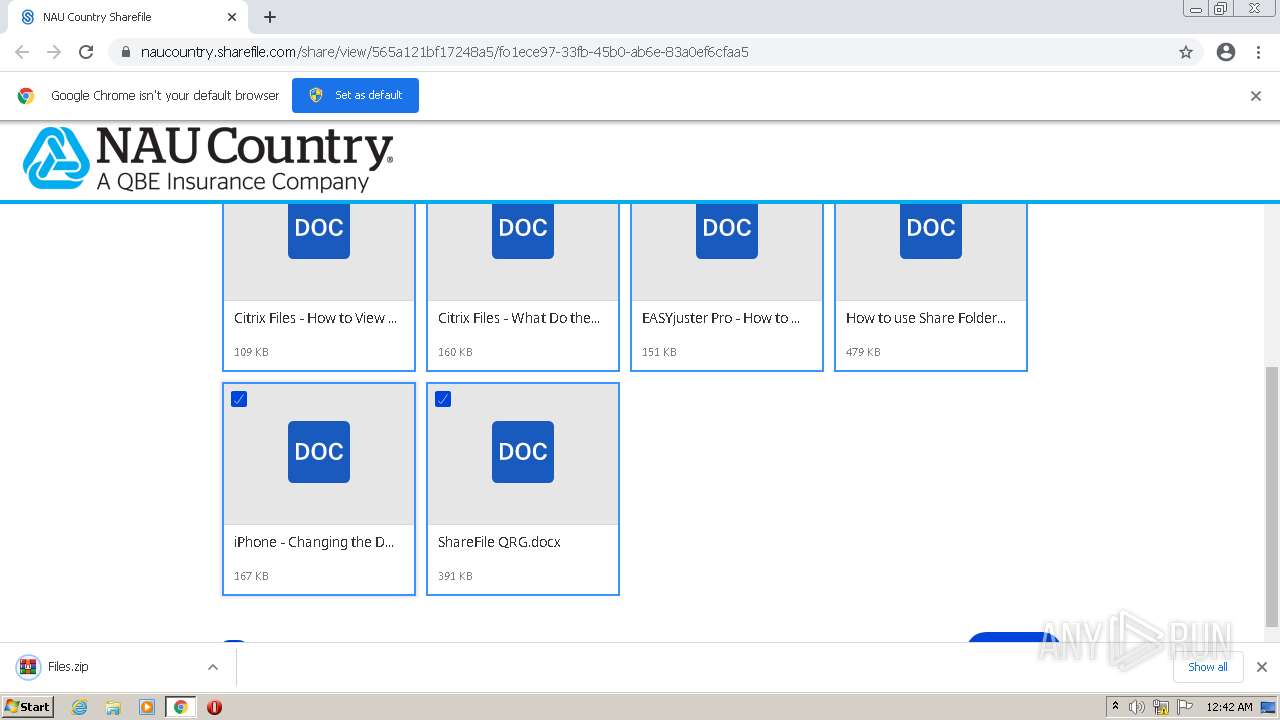
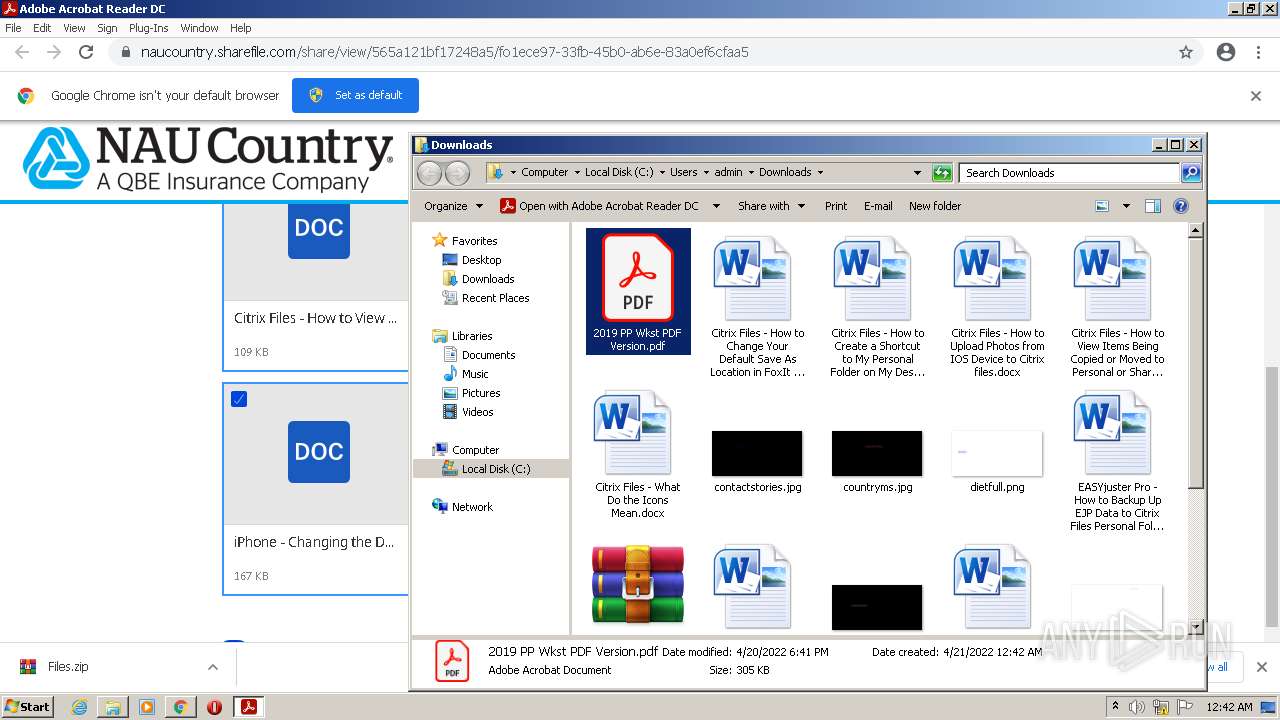
| URL: | https://naucountry.sharefile.com/d-565a121bf17248a5 |
| Full analysis: | https://app.any.run/tasks/71162007-05b5-42c3-823e-d0509f6c4b77 |
| Verdict: | Malicious activity |
| Analysis date: | April 20, 2022, 23:41:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AB12CCB38B6588984F7C4601FAB2E524 |
| SHA1: | 0BD234477DC9F023E4E5B1AC53DA2542FFBFEE0A |
| SHA256: | 787343FE92ED6CE2AD21427DB6BE886A82C6032140916656FDBA959959161E4B |
| SSDEEP: | 3:N8alX6KEXAQOIQeaRHn:2aeXAQndaHn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1580)
Reads the computer name
- WinRAR.exe (PID: 2016)
- AdobeARM.exe (PID: 1188)
Checks supported languages
- WinRAR.exe (PID: 2016)
- AdobeARM.exe (PID: 1188)
- Reader_sl.exe (PID: 1832)
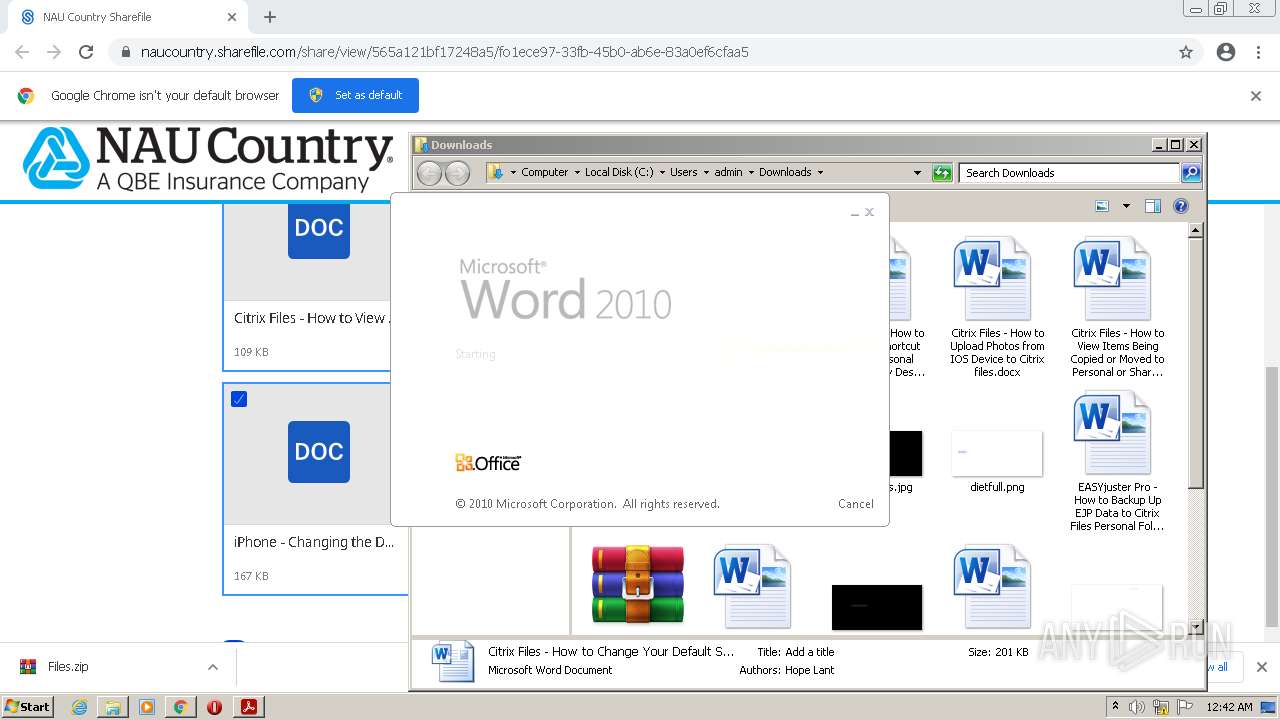
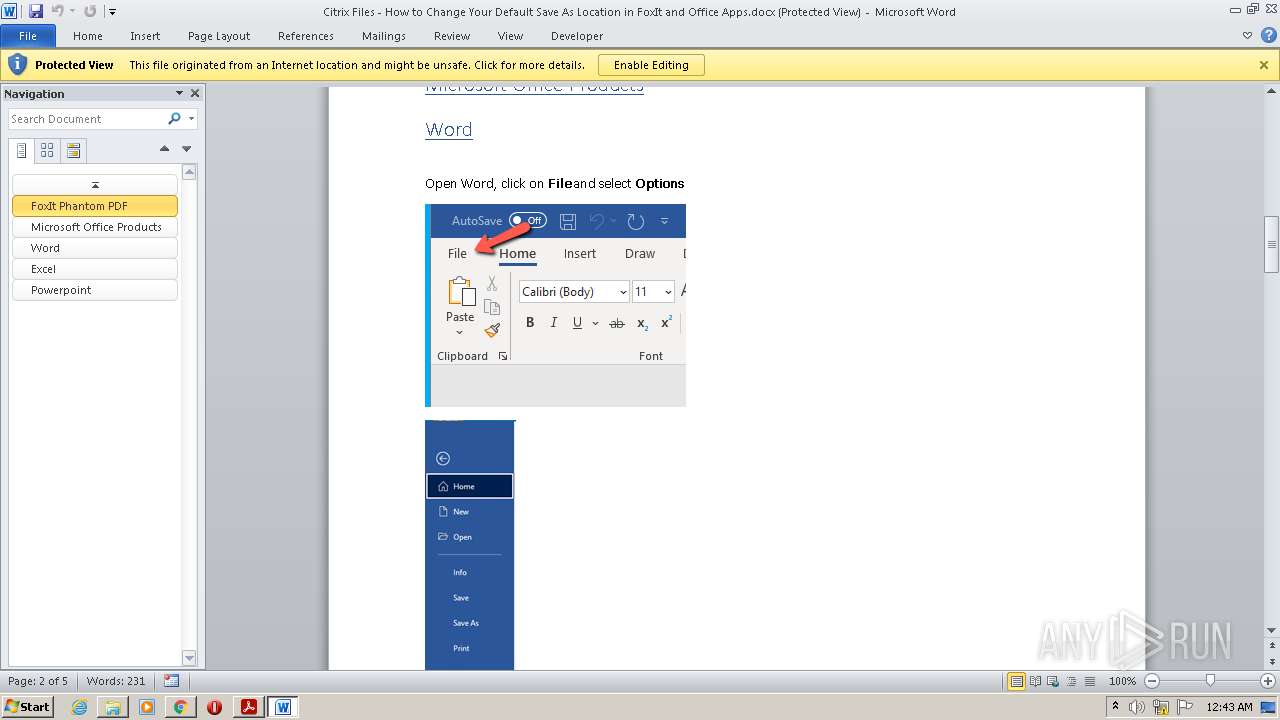
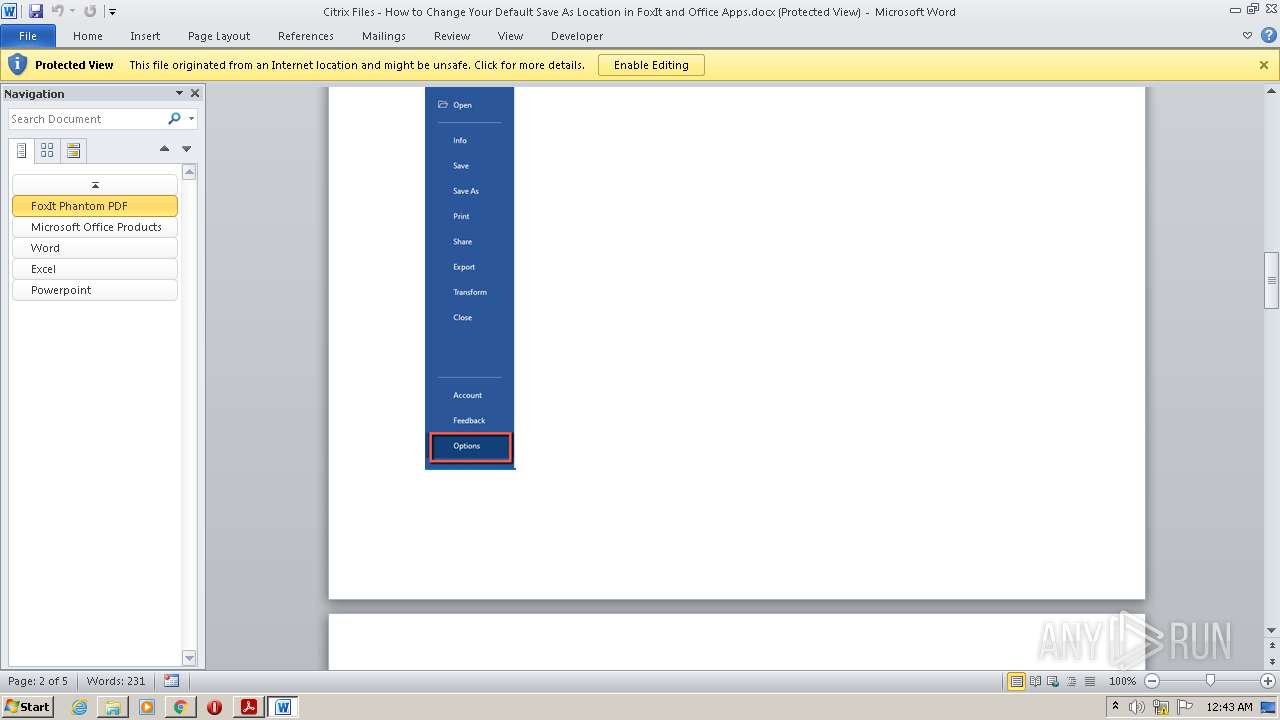
Application launched itself
- WINWORD.EXE (PID: 3496)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 2008)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3496)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 2008)
Creates files in the program directory
- AdobeARM.exe (PID: 1188)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 1188)
INFO
Checks supported languages
- chrome.exe (PID: 2376)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 316)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2524)
- AcroRd32.exe (PID: 1164)
- AcroRd32.exe (PID: 3148)
- RdrCEF.exe (PID: 3364)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 928)
- chrome.exe (PID: 1824)
- RdrCEF.exe (PID: 2220)
- RdrCEF.exe (PID: 532)
- RdrCEF.exe (PID: 3628)
- RdrCEF.exe (PID: 1032)
- RdrCEF.exe (PID: 3792)
- chrome.exe (PID: 2100)
- WINWORD.EXE (PID: 3496)
- WINWORD.EXE (PID: 2816)
- chrome.exe (PID: 2980)
- RdrCEF.exe (PID: 3816)
- RdrCEF.exe (PID: 1320)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 680)
- chrome.exe (PID: 3492)
- WINWORD.EXE (PID: 2008)
- WINWORD.EXE (PID: 2608)
Reads the computer name
- chrome.exe (PID: 2376)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2524)
- AcroRd32.exe (PID: 1164)
- AcroRd32.exe (PID: 3148)
- RdrCEF.exe (PID: 3364)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 928)
- WINWORD.EXE (PID: 3496)
- WINWORD.EXE (PID: 2816)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 680)
- chrome.exe (PID: 3492)
- WINWORD.EXE (PID: 2008)
- WINWORD.EXE (PID: 2608)
Reads settings of System Certificates
- chrome.exe (PID: 928)
- AcroRd32.exe (PID: 1164)
- RdrCEF.exe (PID: 3364)
- AdobeARM.exe (PID: 1188)
Application launched itself
- chrome.exe (PID: 1580)
- AcroRd32.exe (PID: 1164)
- RdrCEF.exe (PID: 3364)
Changes settings of System certificates
- chrome.exe (PID: 928)
Reads the date of Windows installation
- chrome.exe (PID: 272)
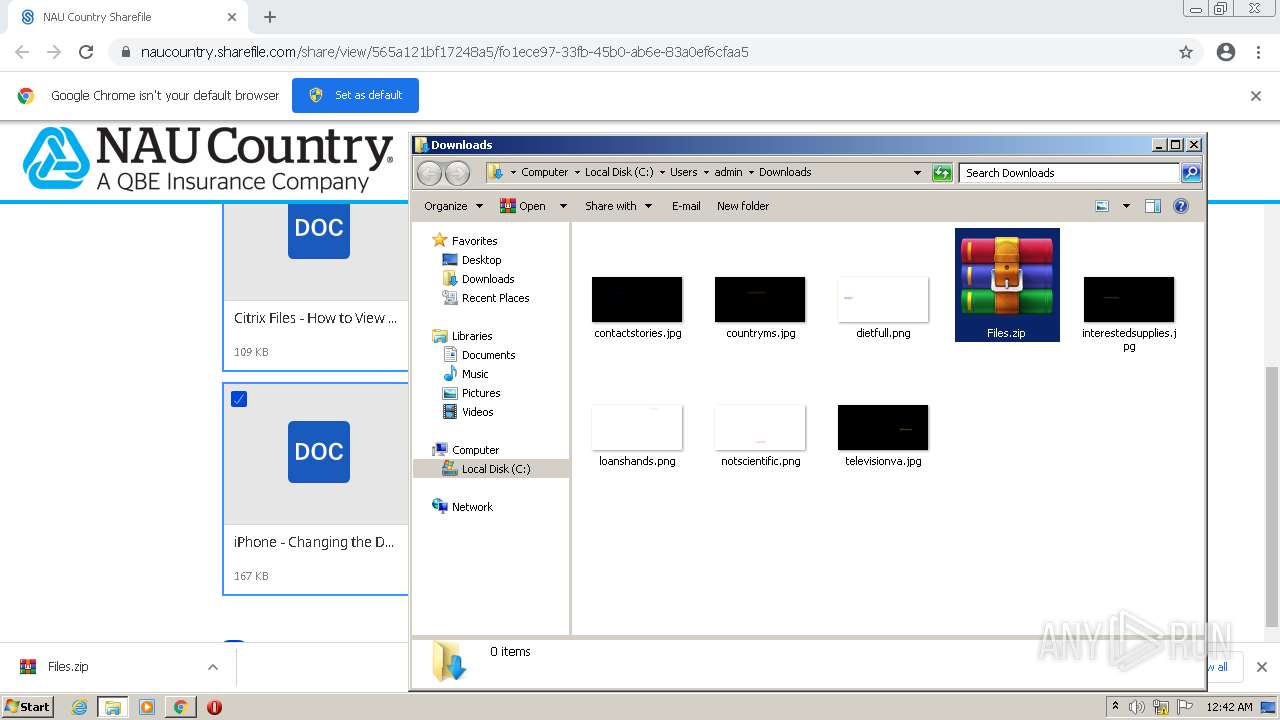
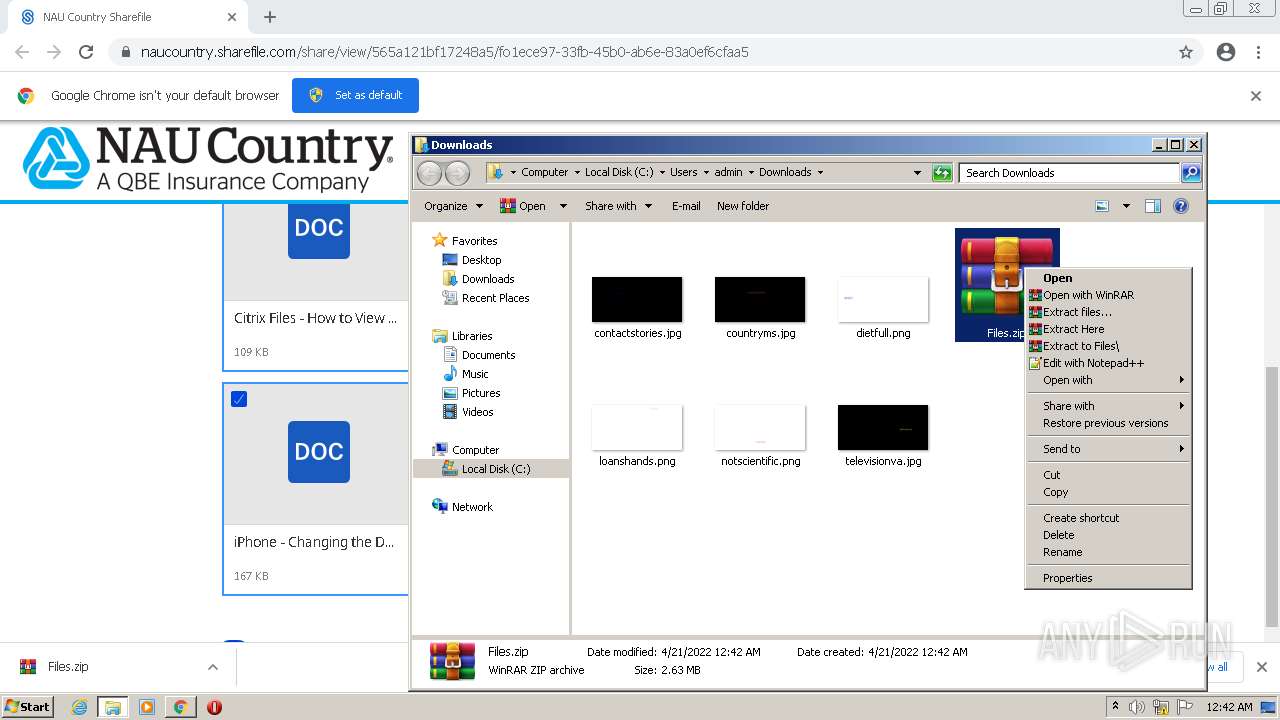
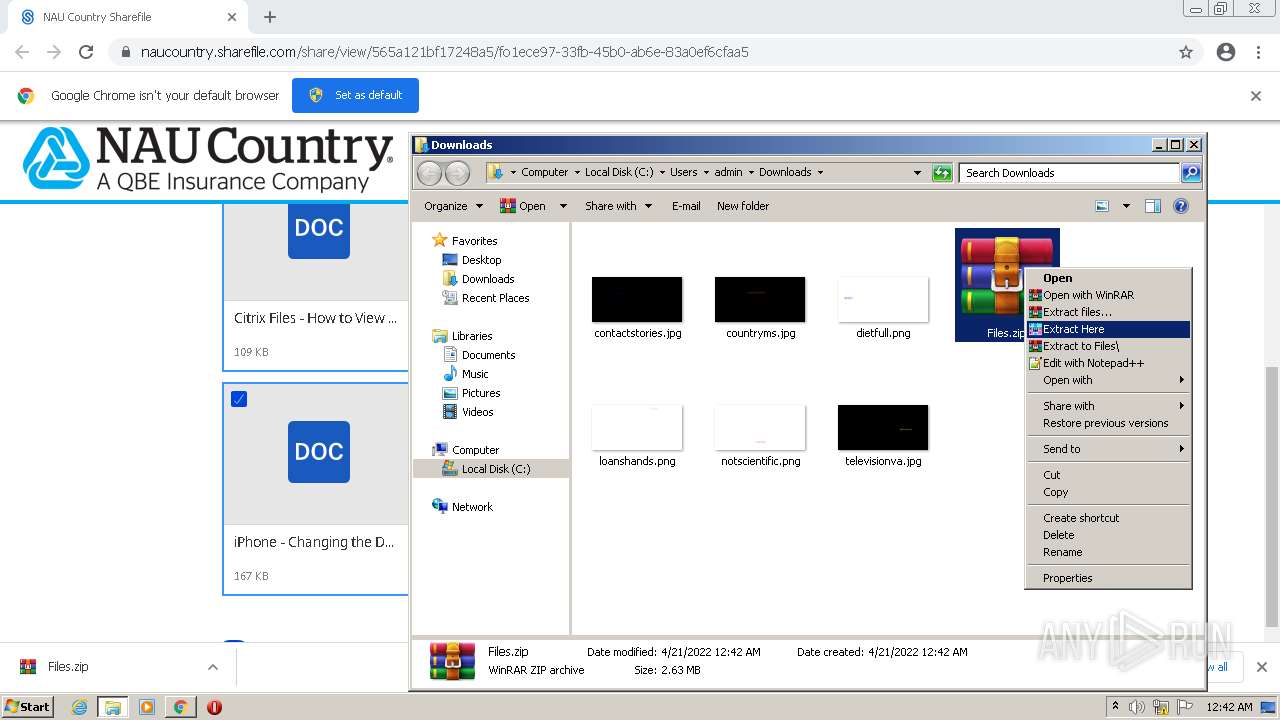
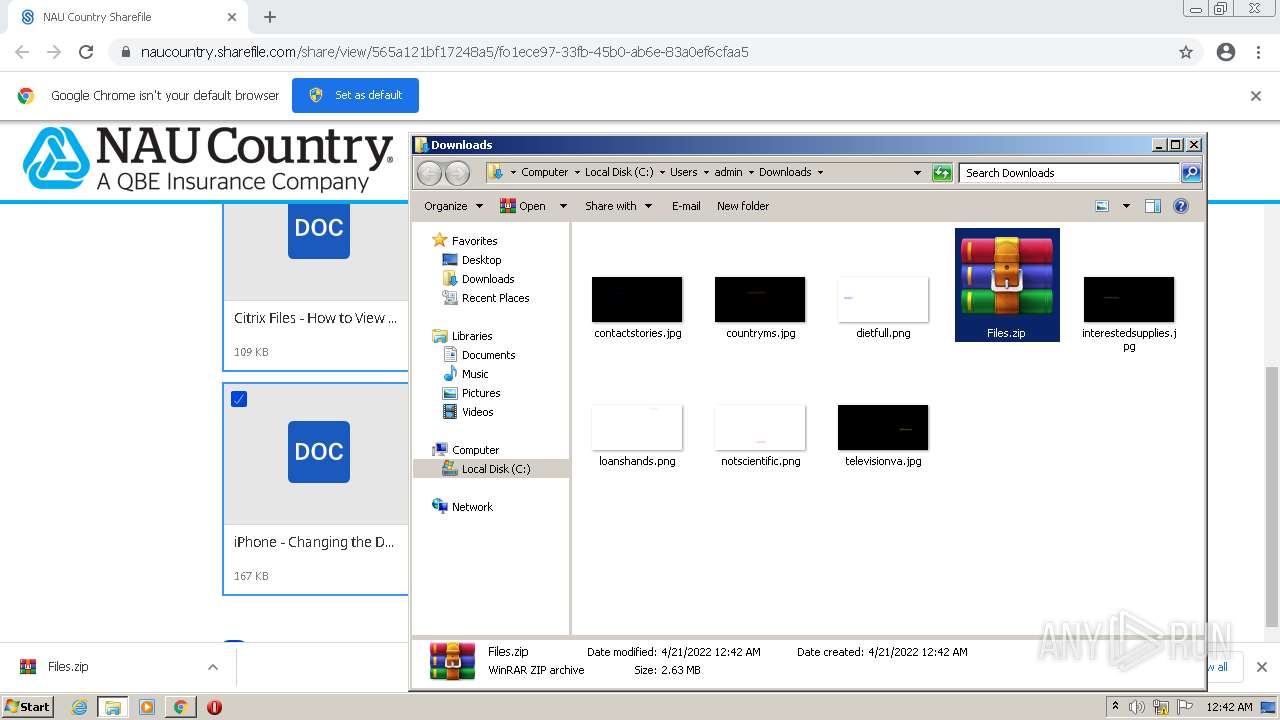
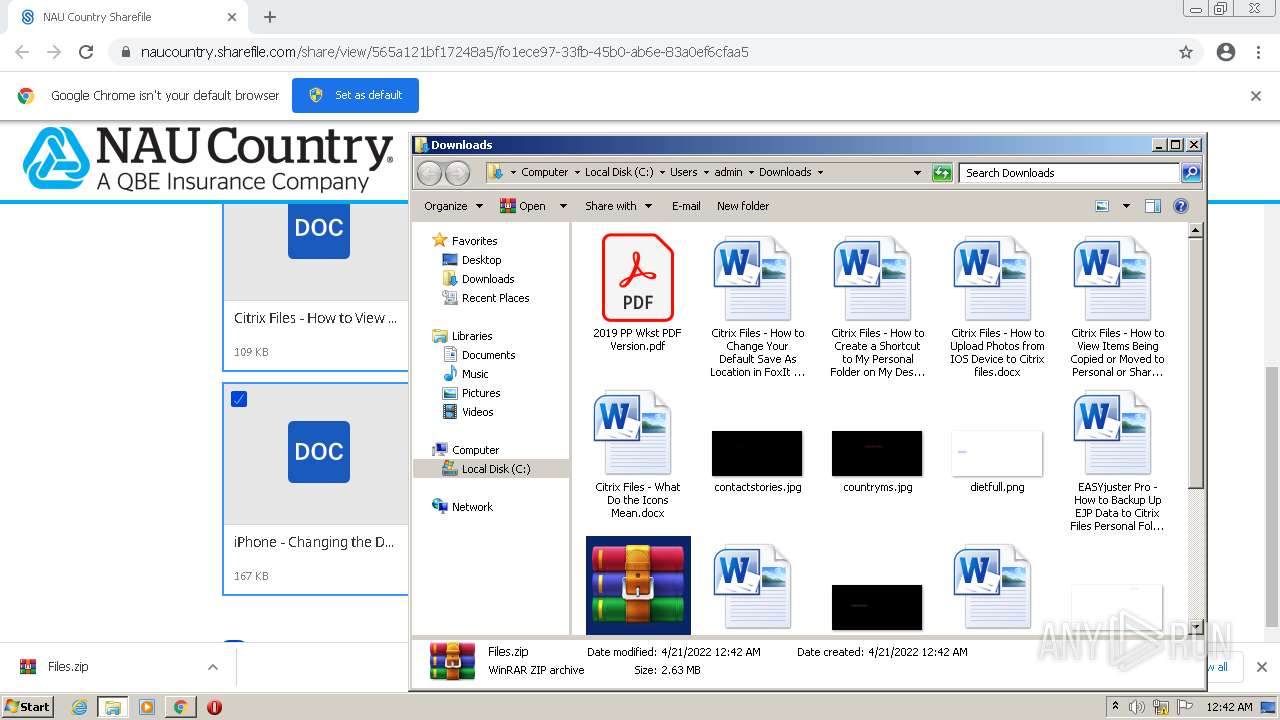
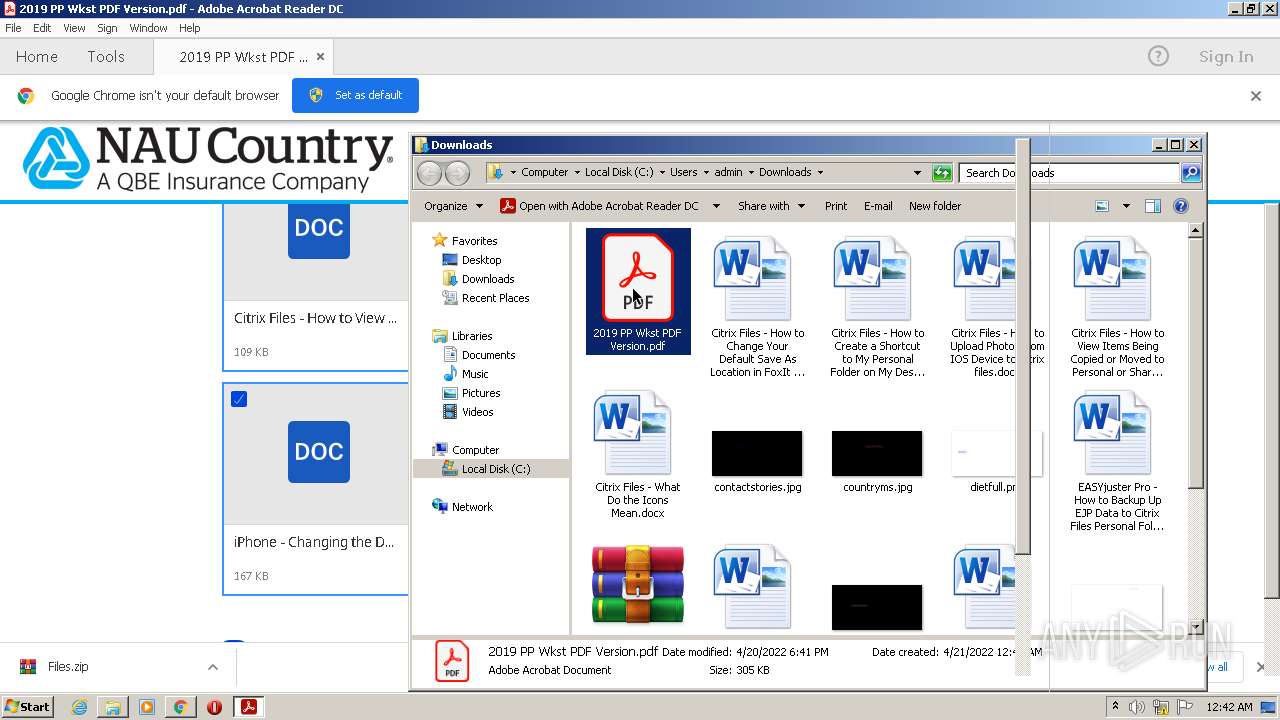
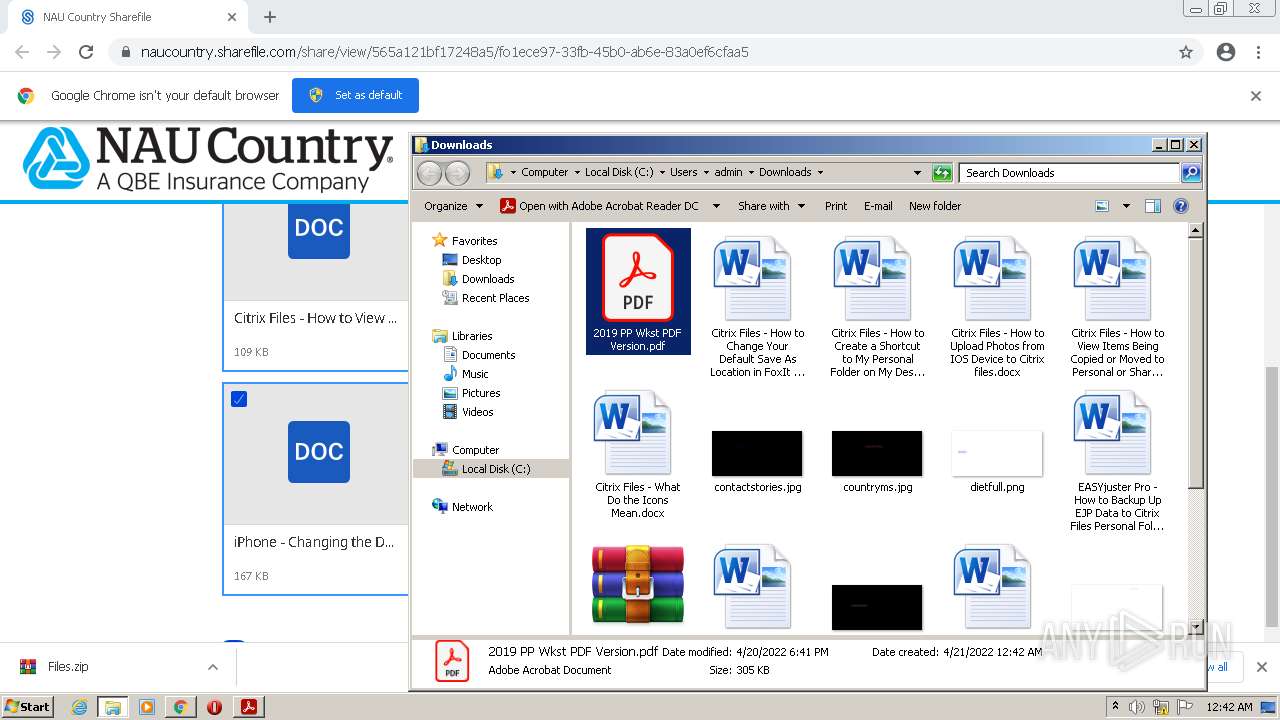
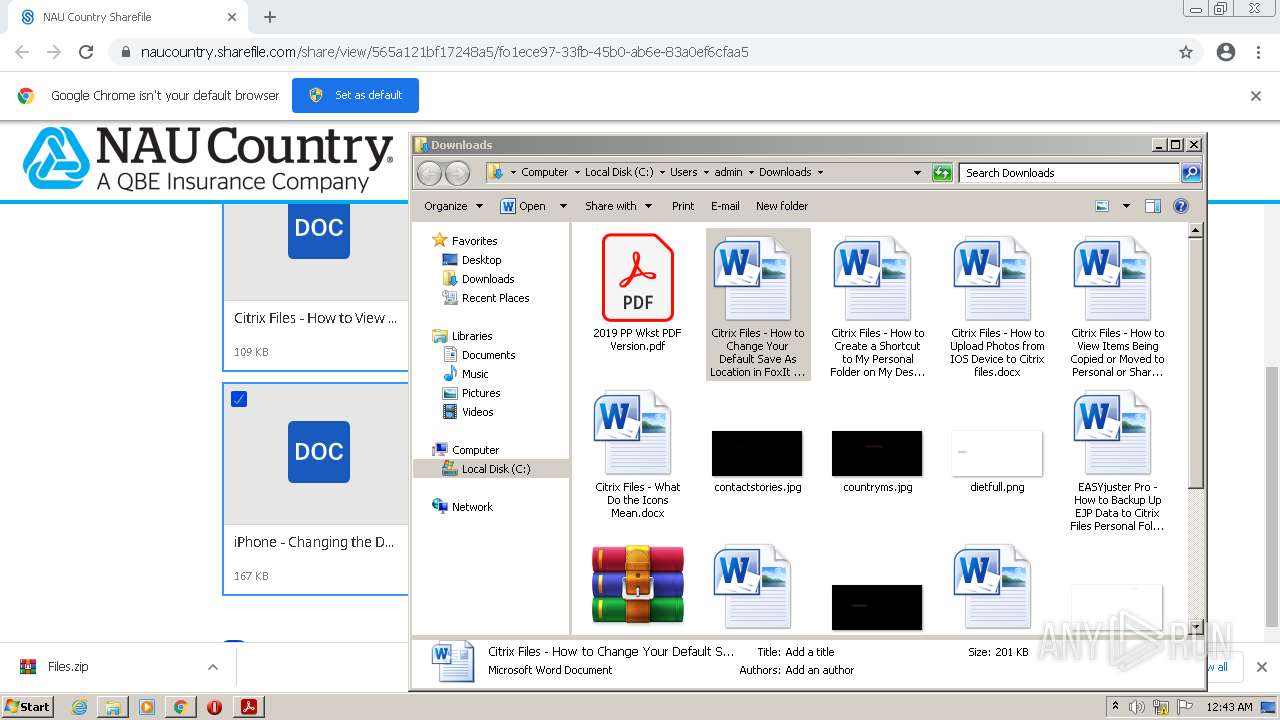
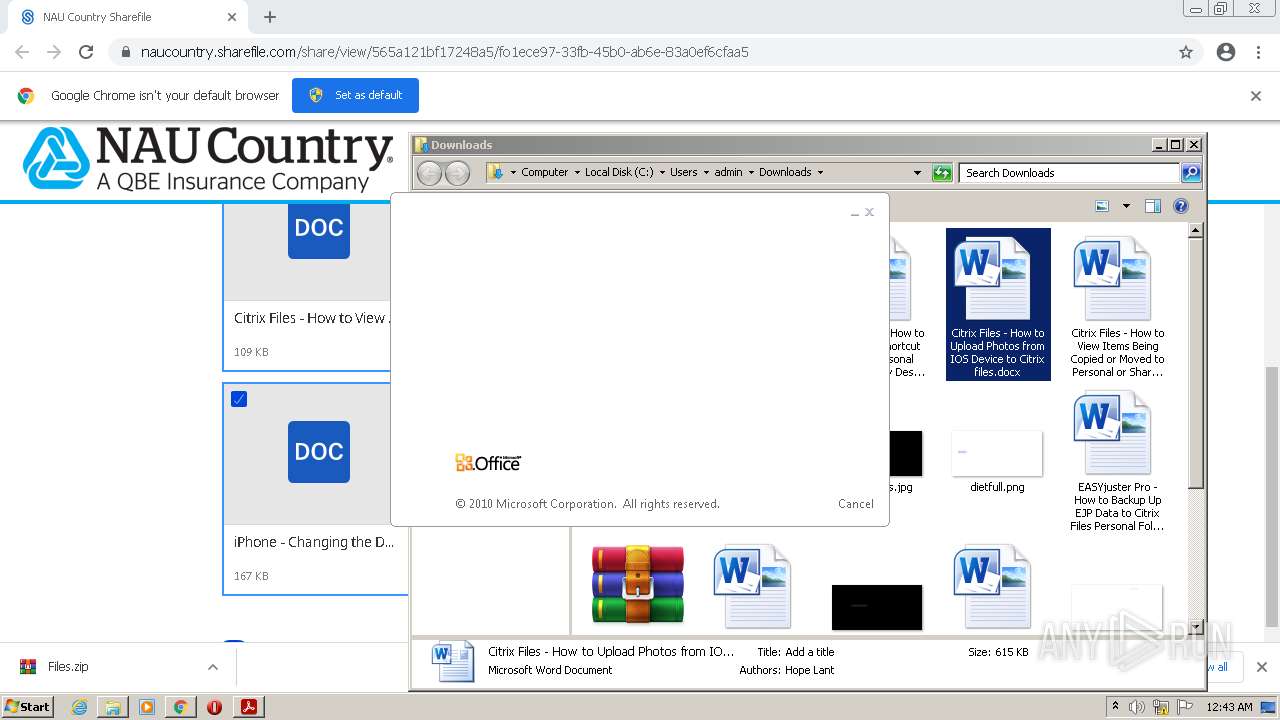
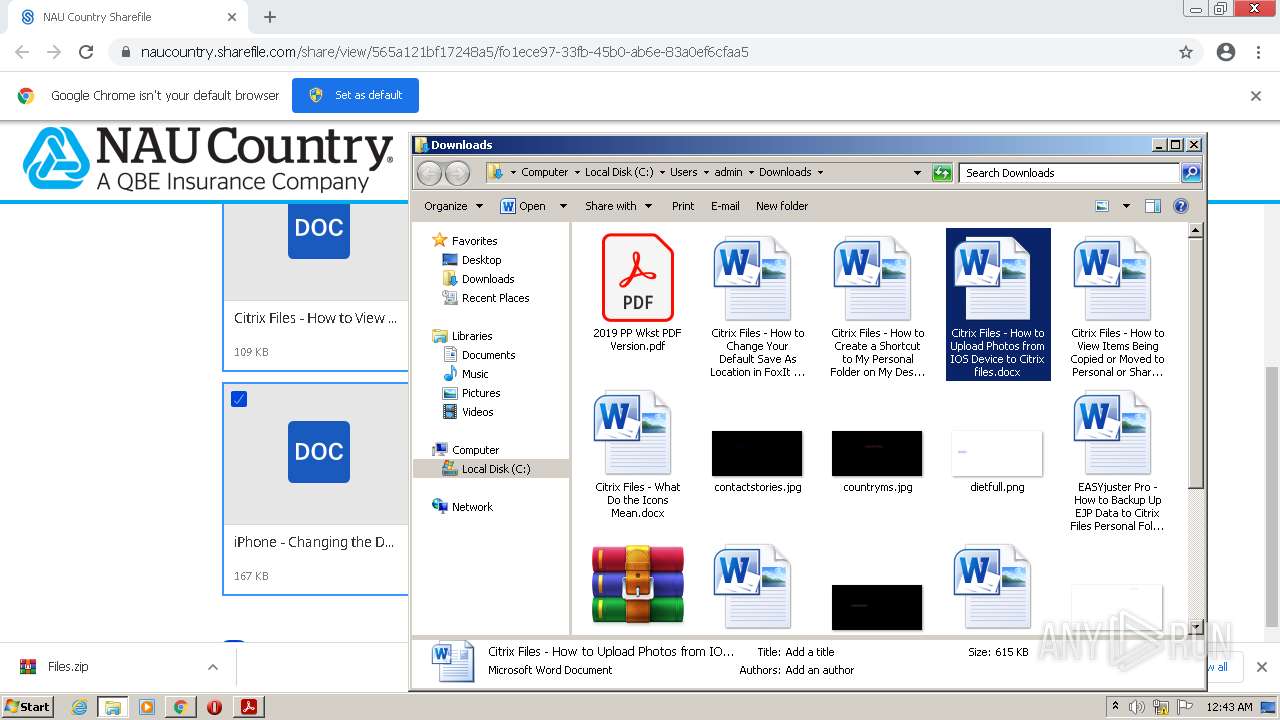
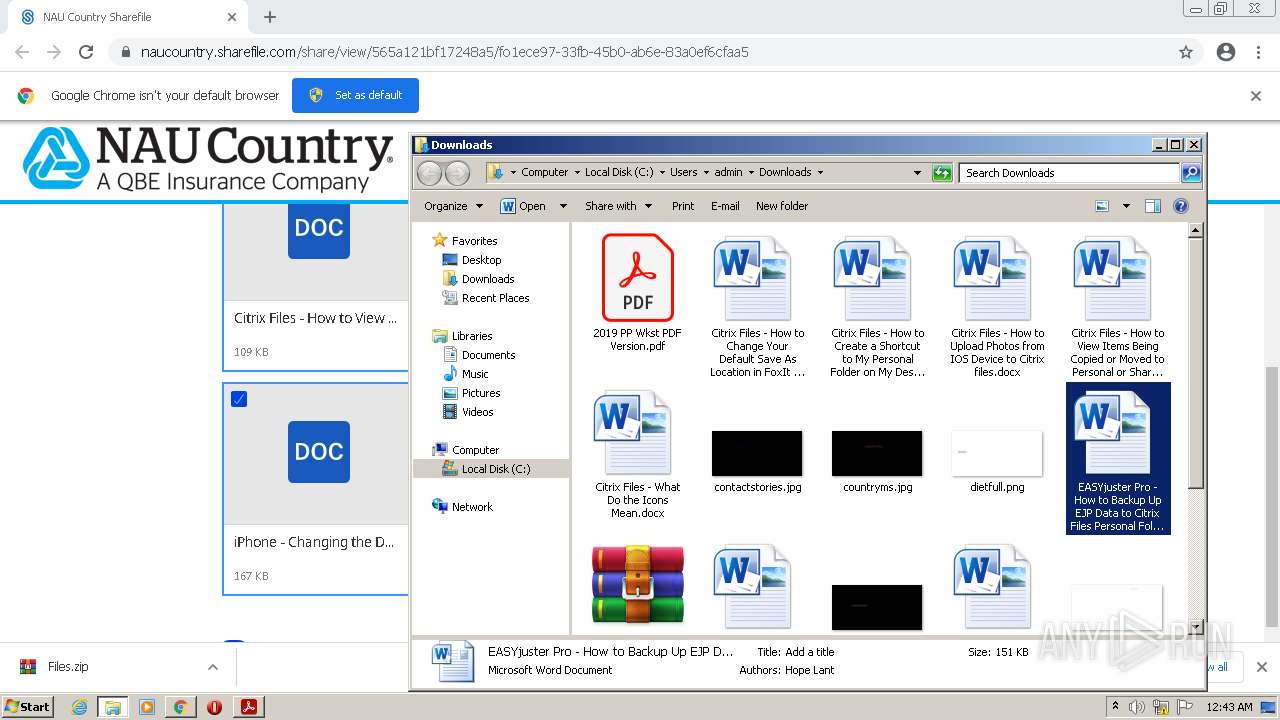
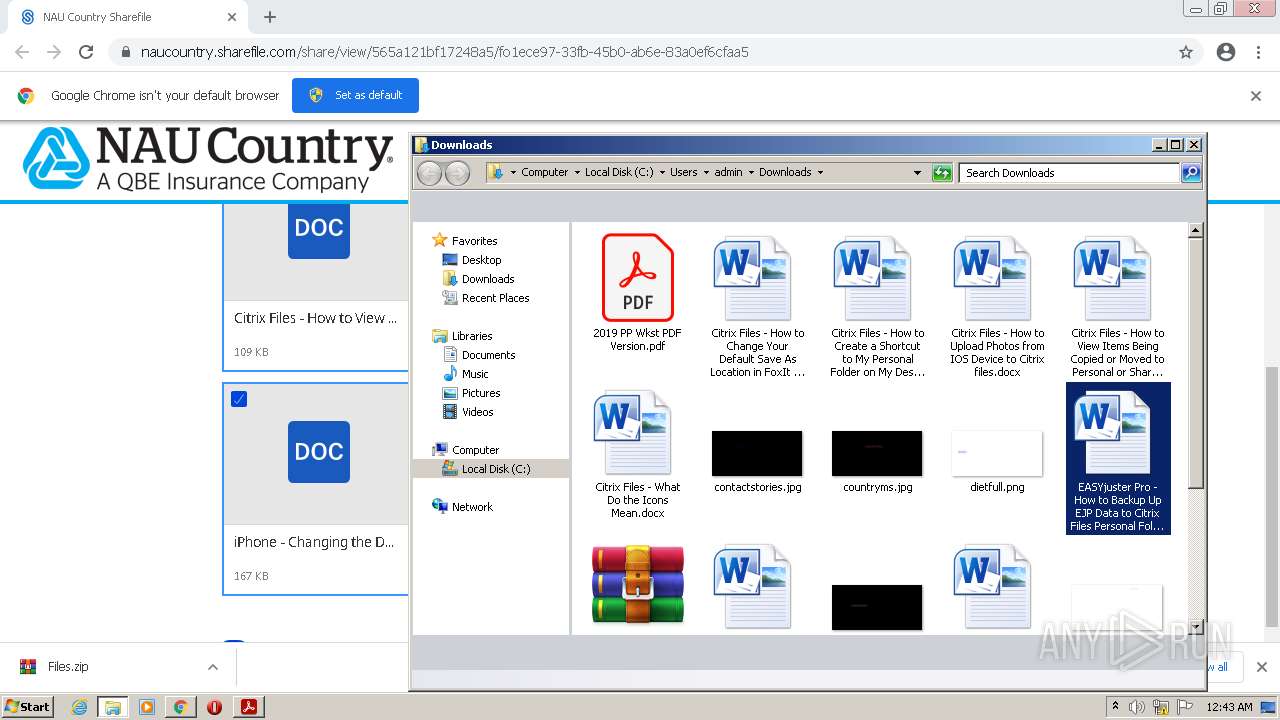
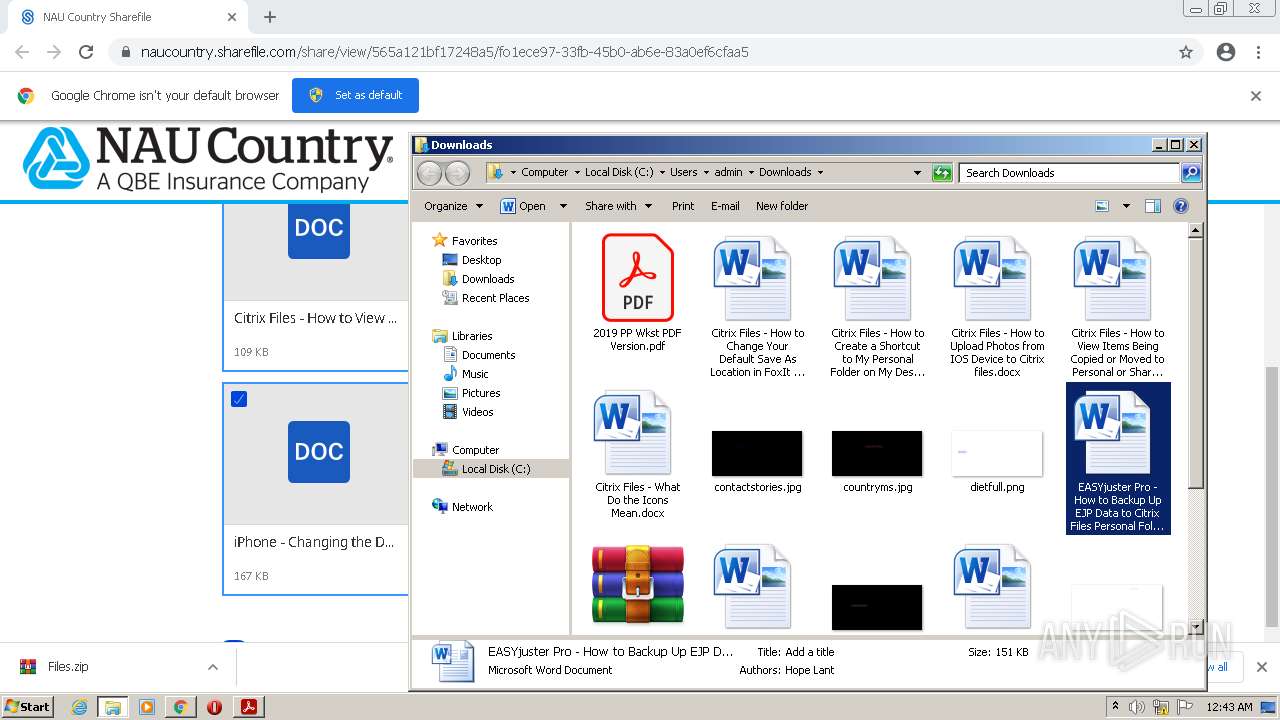
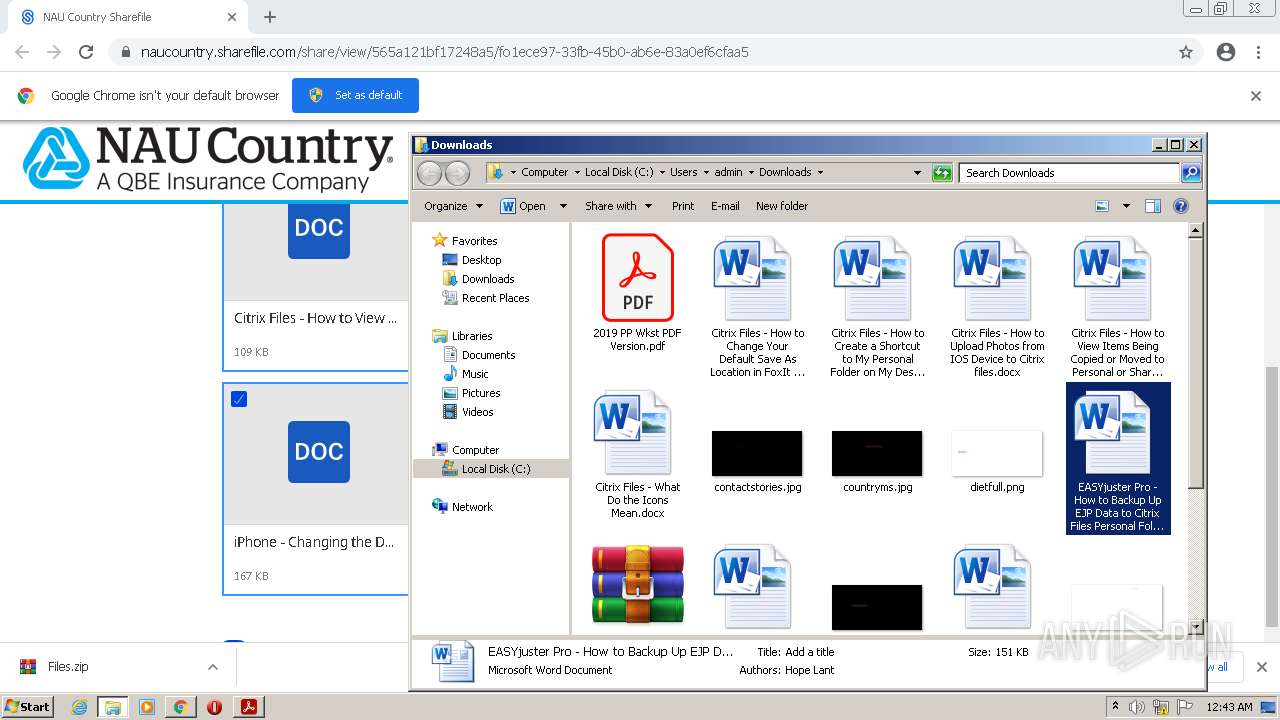
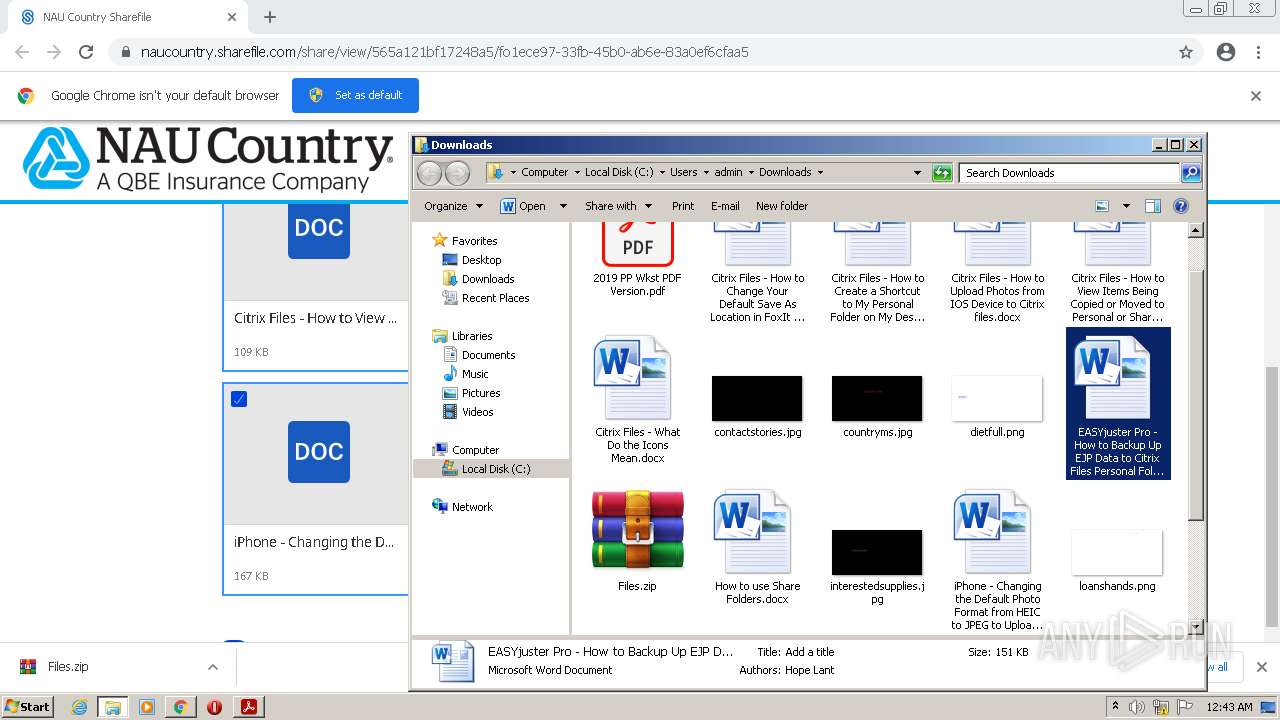
Manual execution by user
- WinRAR.exe (PID: 2016)
- AcroRd32.exe (PID: 1164)
- WINWORD.EXE (PID: 3496)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 2008)
Searches for installed software
- AcroRd32.exe (PID: 1164)
- AcroRd32.exe (PID: 3148)
Reads CPU info
- AcroRd32.exe (PID: 3148)
Reads the hosts file
- chrome.exe (PID: 928)
- RdrCEF.exe (PID: 3364)
- chrome.exe (PID: 1580)
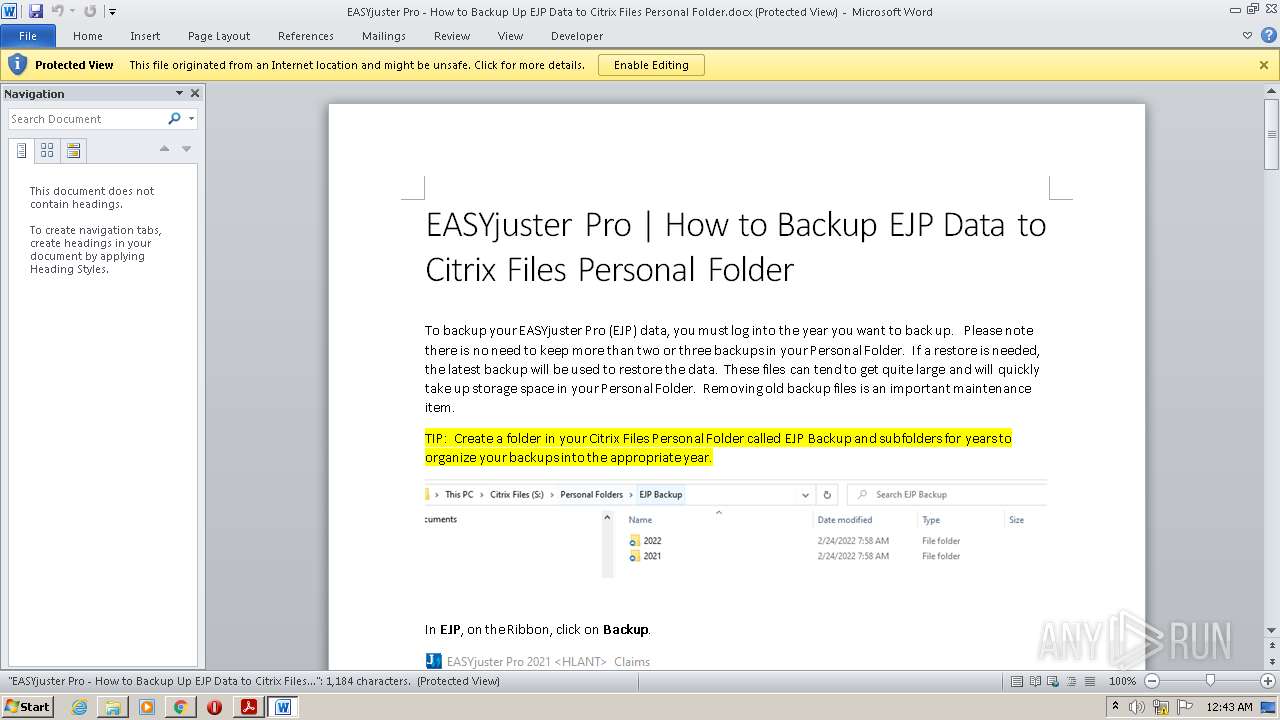
Creates files in the user directory
- WINWORD.EXE (PID: 3496)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 2008)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2816)
- WINWORD.EXE (PID: 680)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 2608)
- WINWORD.EXE (PID: 2008)
- WINWORD.EXE (PID: 3496)
Checks Windows Trust Settings
- AcroRd32.exe (PID: 1164)
- AdobeARM.exe (PID: 1188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=996,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2220 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1176,13080624194771646161,16843502095097149575,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=5769783580774688442 --mojo-platform-channel-handle=1212 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=996,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1240 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1176,13080624194771646161,16843502095097149575,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=10414080199398739730 --mojo-platform-channel-handle=1388 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
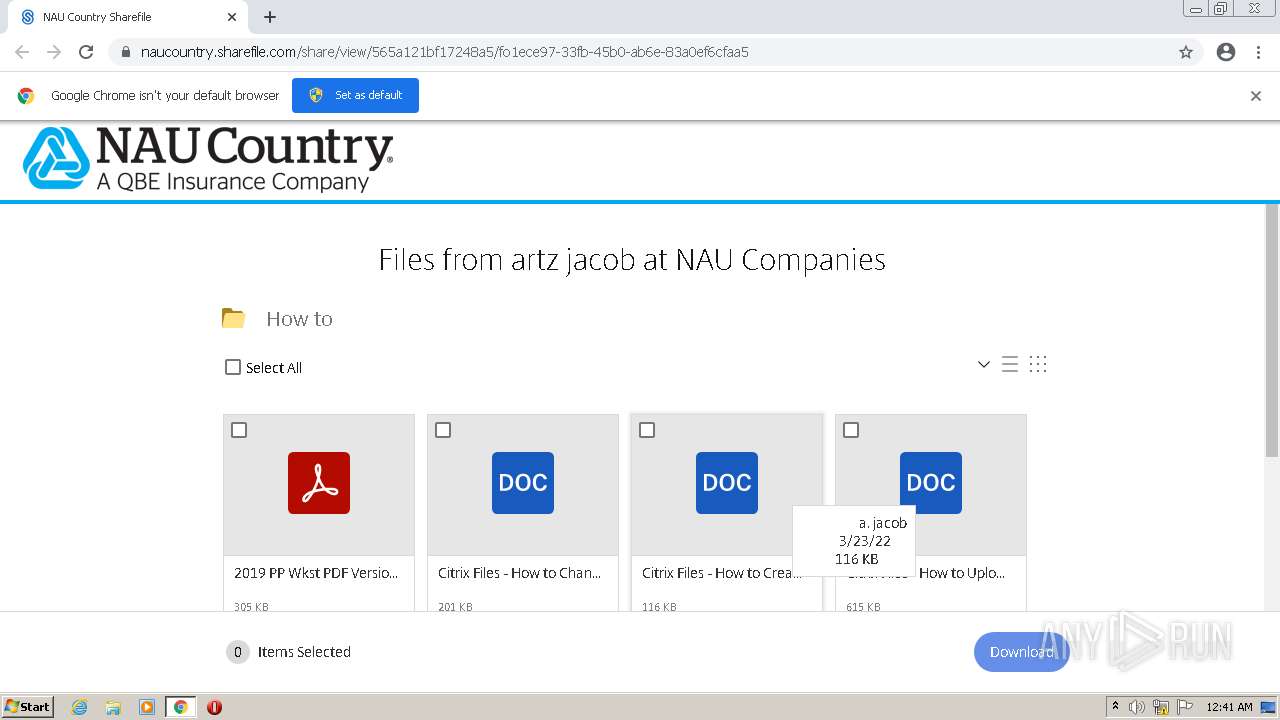
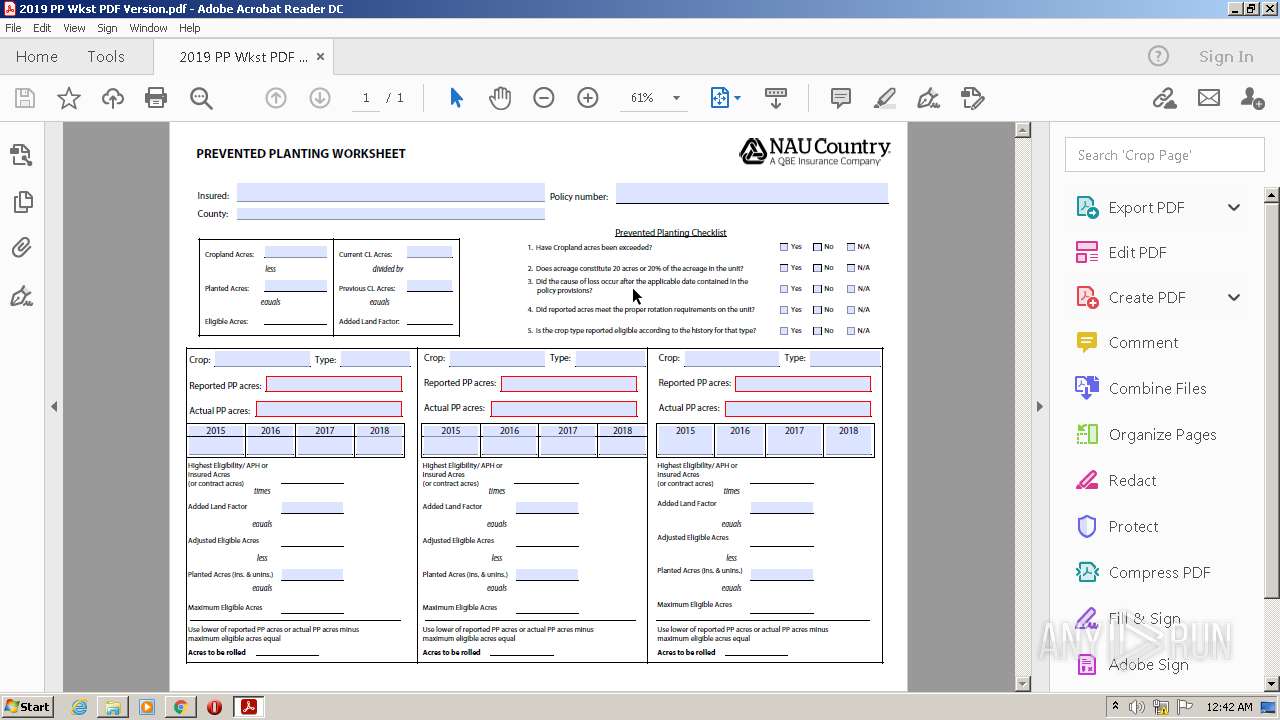
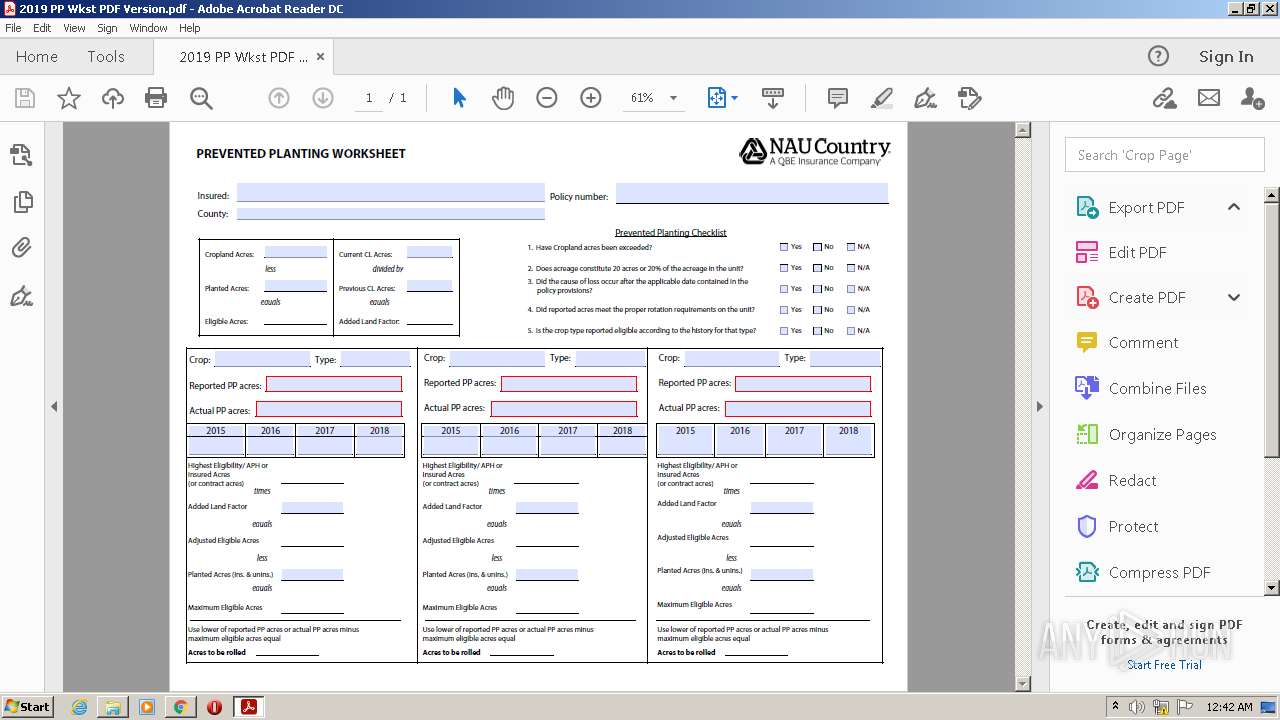
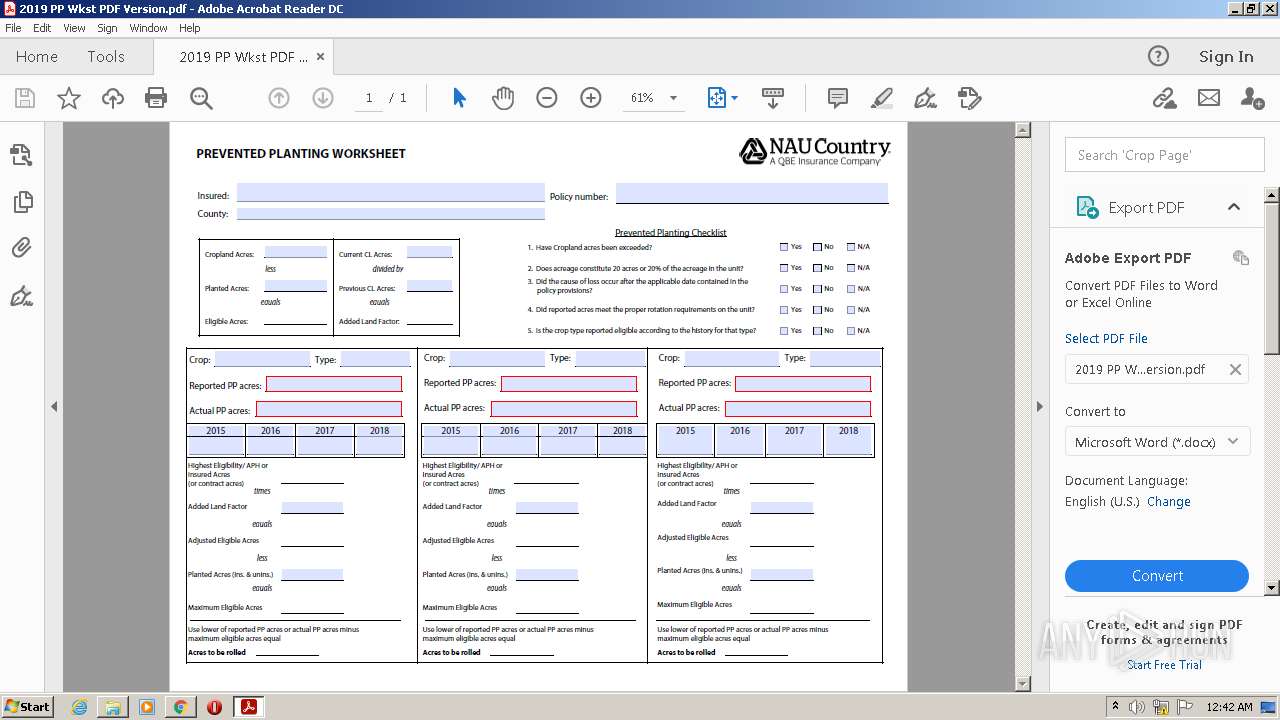
| 1164 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Downloads\2019 PP Wkst PDF Version.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:20.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Inc. Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.39.9311 Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1176,13080624194771646161,16843502095097149575,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9210173839641443877 --renderer-client-id=8 --mojo-platform-channel-handle=1812 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://naucountry.sharefile.com/d-565a121bf17248a5" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
41 574
Read events
40 842
Write events
607
Delete events
125
Modification events
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1
Suspicious files
203
Text files
127
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62609A19-62C.pma | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\097ab28a-c4de-4328-85e2-6874d5de7599.tmp | text | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf96c8.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFf9a24.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\472cae5f-84d1-4390-850c-06caf04e2bf4.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFf9801.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
50
DNS requests
28
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.186.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
— | — | HEAD | 200 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650497777&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | — | — | whitelisted |
928 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEAZz6Qa7dMrIYuKhX1Wz4Gc%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650497777&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 5.64 Kb | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650497777&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 9.51 Kb | whitelisted |
928 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650497777&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 43.3 Kb | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650497777&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 9.49 Kb | whitelisted |
— | — | GET | 302 | 142.250.186.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 574 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
928 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
928 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
928 | chrome.exe | 142.250.185.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
928 | chrome.exe | 34.107.168.21:443 | citrix-sharefile-content.customer.pendo.io | — | US | suspicious |
928 | chrome.exe | 13.248.193.251:443 | naucountry.sharefile.com | — | US | suspicious |
— | — | 142.250.186.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
928 | chrome.exe | 76.223.1.166:443 | naucountry.sharefile.com | AT&T Services, Inc. | US | unknown |
928 | chrome.exe | 104.18.38.174:80 | cacerts.geotrust.com | Cloudflare Inc | US | shared |
928 | chrome.exe | 151.101.194.217:443 | app.launchdarkly.com | Fastly | US | suspicious |
928 | chrome.exe | 216.71.100.41:443 | sharefile.naucountry.com | OLM, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
naucountry.sharefile.com |
| suspicious |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
app.launchdarkly.com |
| shared |
radar.cedexis.com |
| whitelisted |
citrix-sharefile-content.customer.pendo.io |
| whitelisted |
naucountry.sf-api.com |
| suspicious |
events.launchdarkly.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |