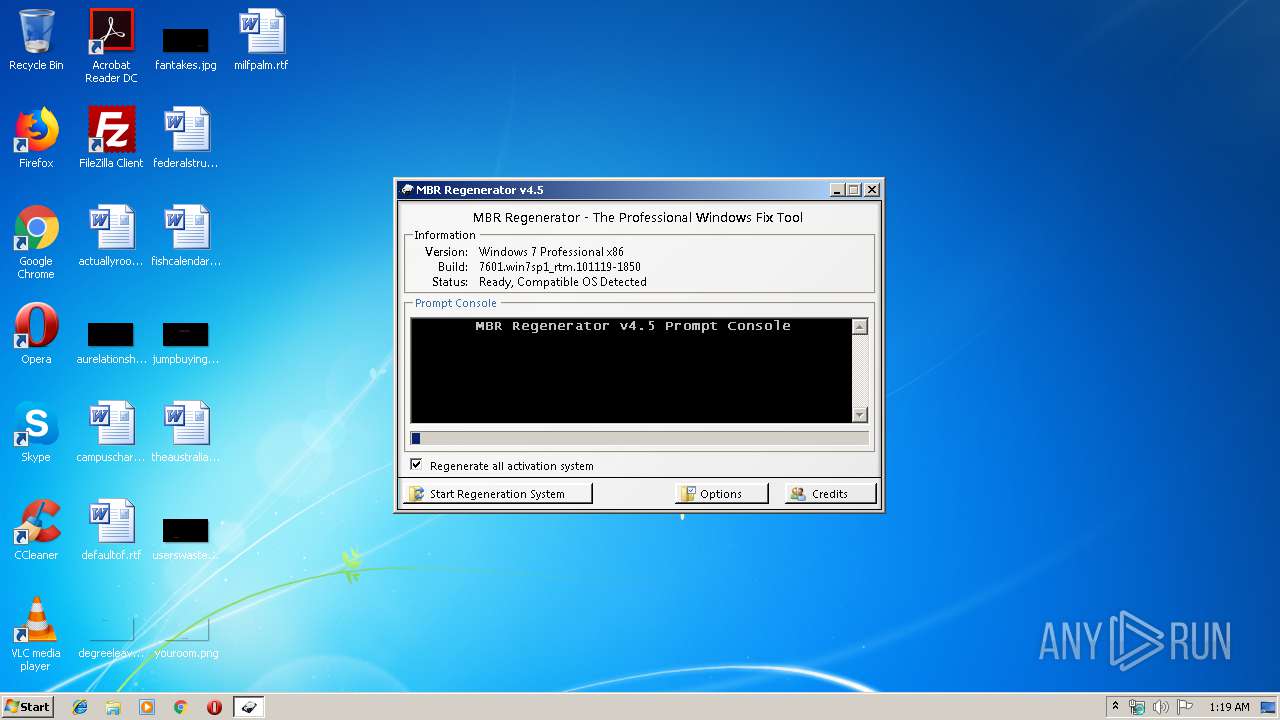
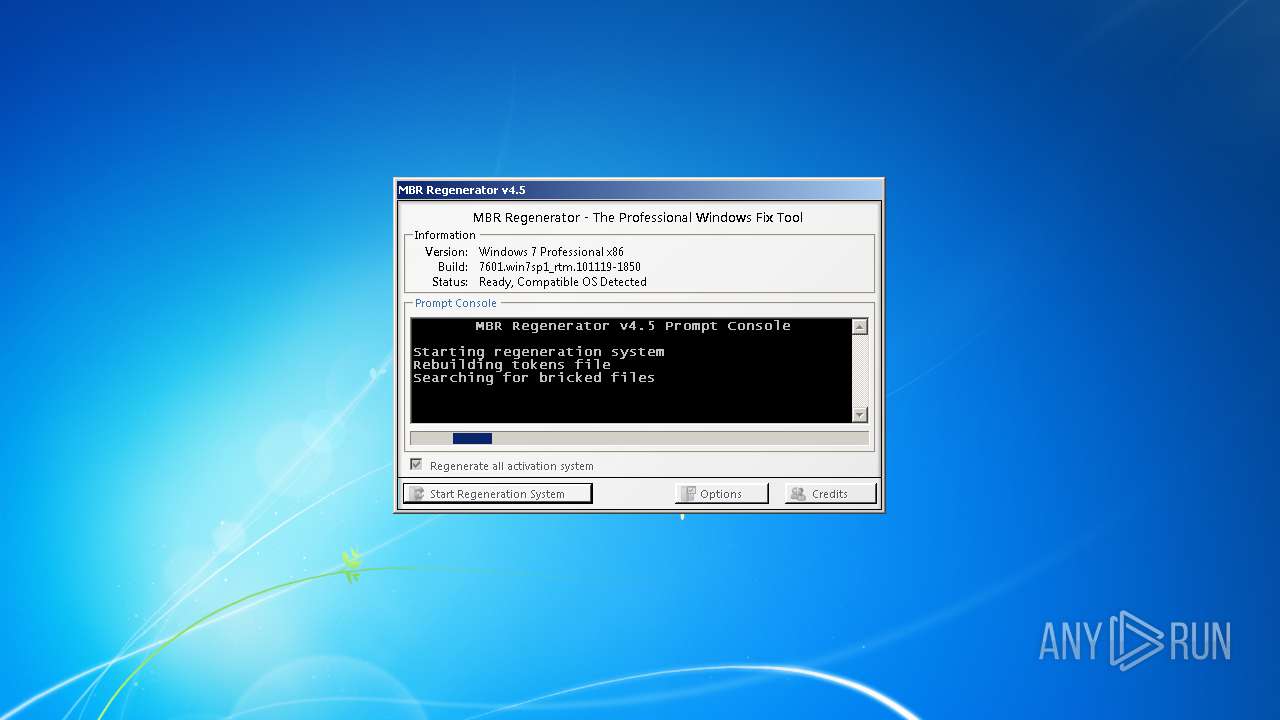
| File name: | MBR Regenerator v4.5.exe |
| Full analysis: | https://app.any.run/tasks/56da072e-e133-4dca-9679-8c3ca2e960cc |
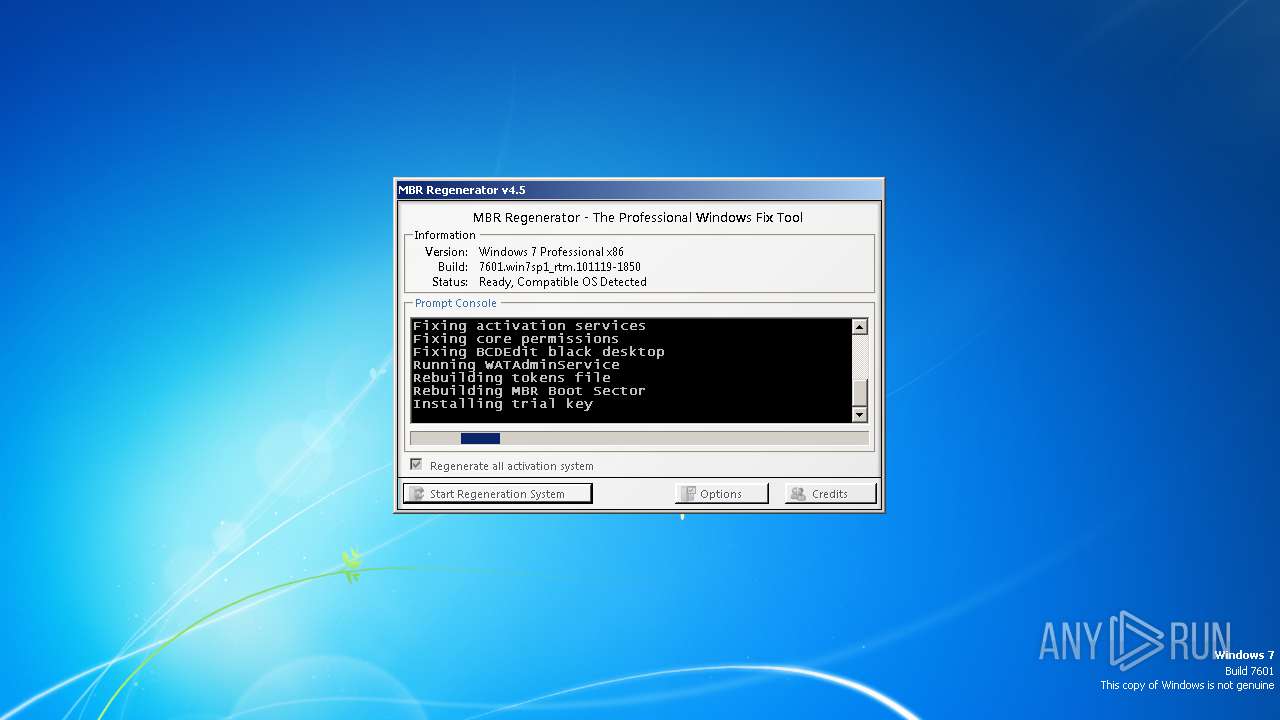
| Verdict: | Malicious activity |
| Analysis date: | January 13, 2020, 01:19:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | FCA2AA6D8039DD107AFF1A3CFBE97F7B |
| SHA1: | 7D47EB1EC59C3381CED53AF2AFE4A5C14CDF86F5 |
| SHA256: | 78729C8E1D3DCC6C70445016E36EB07D79D87033EB124598363038B7D001769F |
| SSDEEP: | 24576:VTRqE2rb1UKApqrqI9PGi0gf0zQn8qqROJH40UdSX4ovytII6:VTr0b13ApqrqI9PORO8qLYN3UI6 |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 2204)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 716)
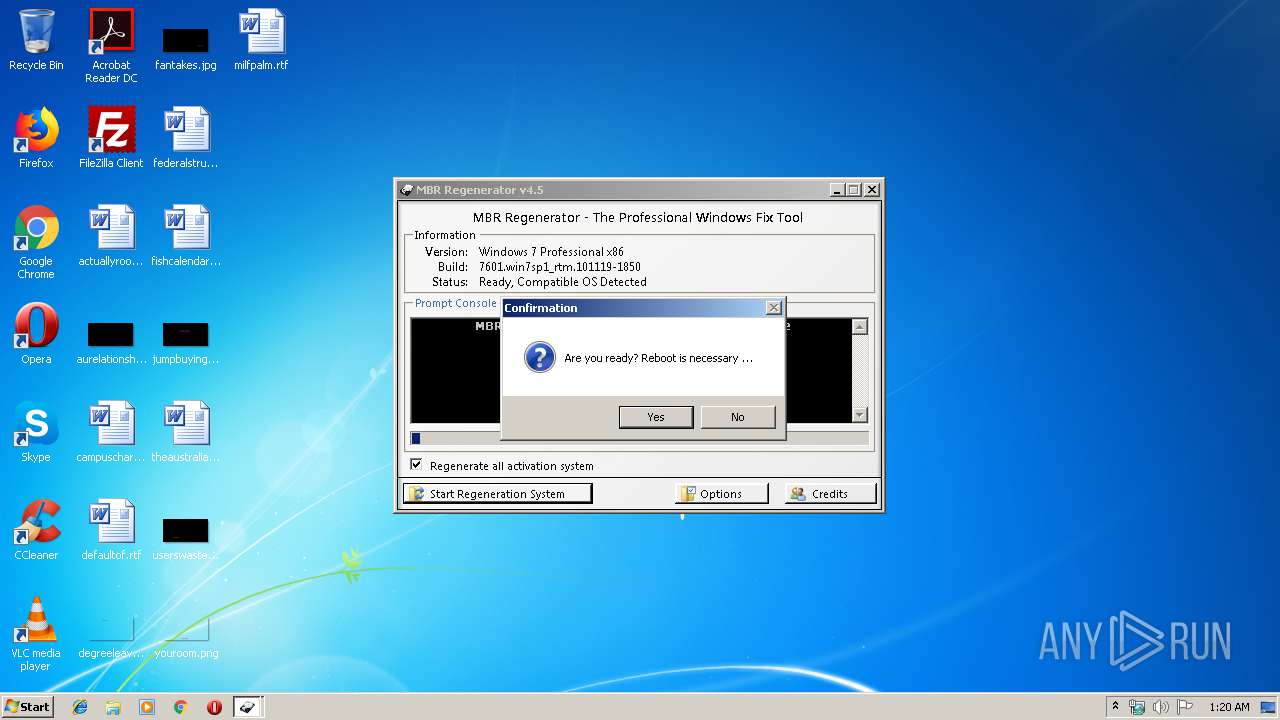
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2076)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 956)
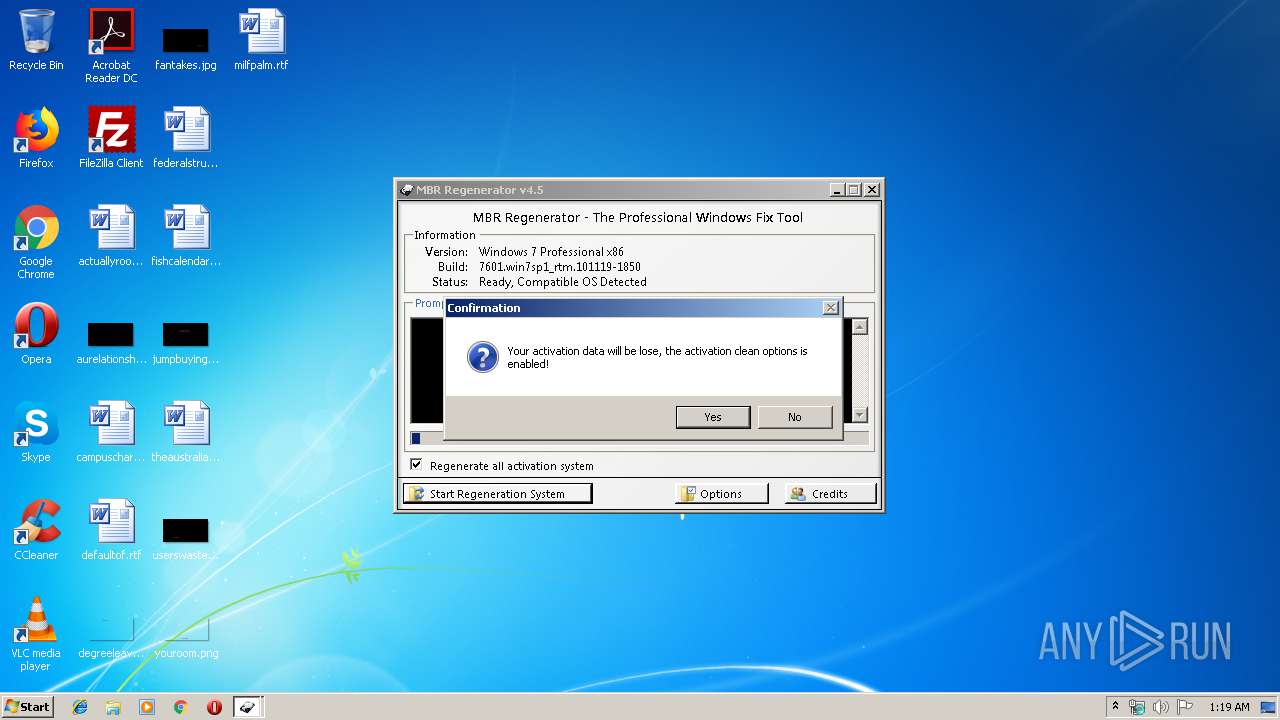
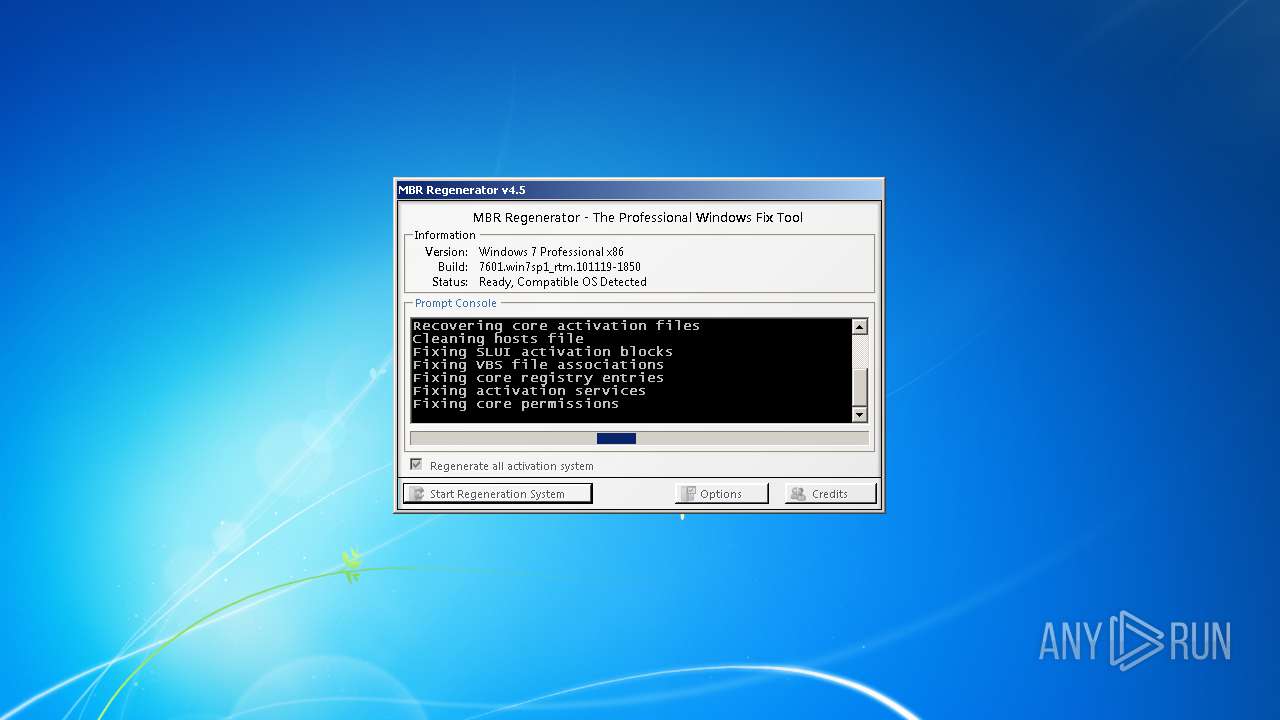
Tries to delete the host file
- cmd.exe (PID: 1336)
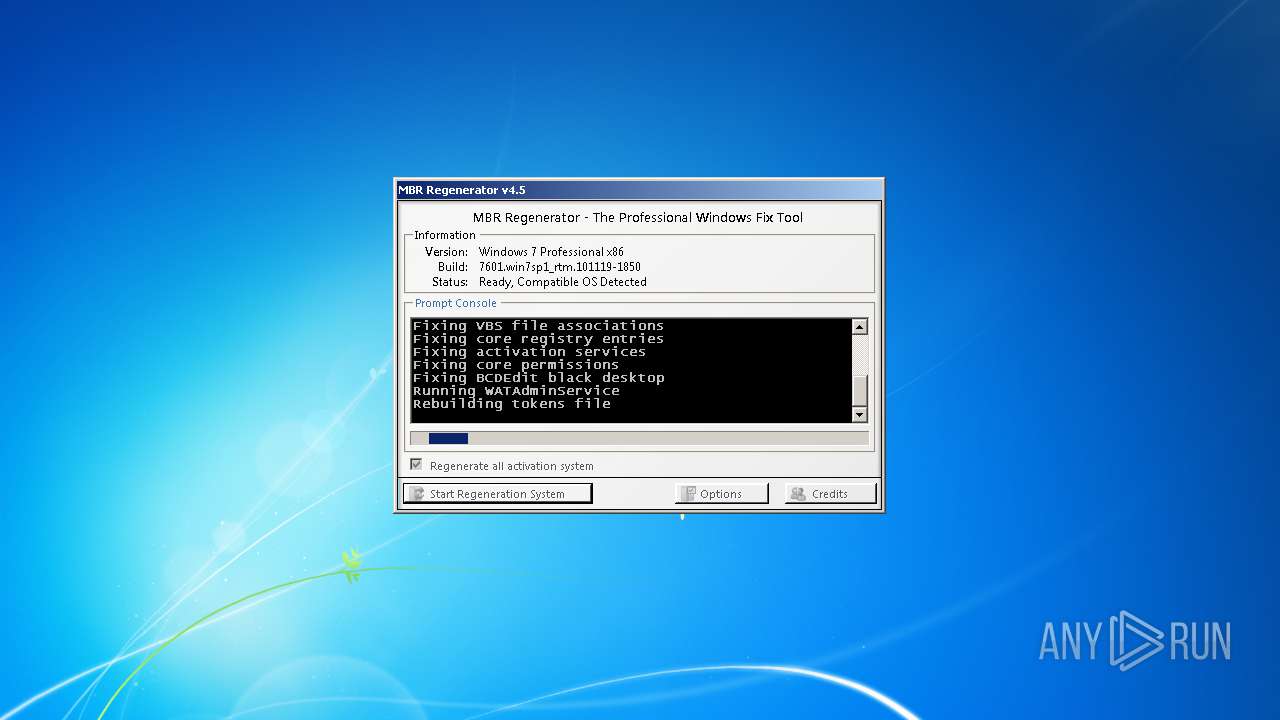
Low-level write access rights to disk partition
- bootsect.exe (PID: 3724)
SUSPICIOUS
Starts CMD.EXE for commands execution
- MBR Regenerator v4.5.exe (PID: 792)
- cmd.exe (PID: 520)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3848)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 748)
- cmd.exe (PID: 504)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3372)
- cmd.exe (PID: 3244)
Removes files from Windows directory
- MBR Regenerator v4.5.exe (PID: 792)
- cmd.exe (PID: 1336)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 4044)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 2504)
Starts CMD.EXE for self-deleting
- MBR Regenerator v4.5.exe (PID: 792)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2304)
- cmd.exe (PID: 2432)
Creates files in the Windows directory
- cmd.exe (PID: 520)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3848)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 504)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 748)
- cmd.exe (PID: 3428)
Creates files in the driver directory
- cmd.exe (PID: 520)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3848)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 504)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 748)
Application launched itself
- cmd.exe (PID: 3100)
Starts SC.EXE for service management
- cmd.exe (PID: 1596)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 520)
Changes the desktop background image
- regedit.exe (PID: 3600)
Modifies the open verb of a shell class
- regedit.exe (PID: 3600)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 516)
- cmd.exe (PID: 996)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 3004)
- cmd.exe (PID: 2532)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 1584)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 2536)
Low-level read access rights to disk partition
- bootsect.exe (PID: 3724)
Executes scripts
- cmd.exe (PID: 3000)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 1148)
INFO
Reads the hosts file
- cmd.exe (PID: 1600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:09:26 16:51:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1049088 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2cb1c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5.0.0 |
| ProductVersionNumber: | 4.5.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | MBR Regenerator - The Professional Windows Fix Tool |
| CompanyName: | Josh Cell Softwares |
| FileDescription: | MBR Regenerator - The Professional Windows Fix Tool |
| FileVersion: | 4.5.0.0 |
| InternalName: | MBR.exe |
| LegalCopyright: | Copyright © 2011 Josh Cell, All Rights Reserved |
| LegalTrademarks: | Josh Cell Softwares |
| OriginalFileName: | MBR.exe |
| ProductName: | MBR Regenerator |
| ProductVersion: | 4.5.0.0 |
| AssemblyVersion: | 4.5.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Sep-2011 14:51:51 |
| Comments: | MBR Regenerator - The Professional Windows Fix Tool |
| CompanyName: | Josh Cell Softwares |
| FileDescription: | MBR Regenerator - The Professional Windows Fix Tool |
| FileVersion: | 4.5.0.0 |
| InternalName: | MBR.exe |
| LegalCopyright: | Copyright © 2011 Josh Cell, All Rights Reserved |
| LegalTrademarks: | Josh Cell Softwares |
| OriginalFilename: | MBR.exe |
| ProductName: | MBR Regenerator |
| ProductVersion: | 4.5.0.0 |
| Assembly Version: | 4.5.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Sep-2011 14:51:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.rsrc | 0x00002000 | 0x00021F38 | 0x00022000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.53367 |
.text | 0x00024000 | 0x00100070 | 0x00100200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96638 |
.reloc | 0x00126000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.11837 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.029 | 861 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.41231 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.60594 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.41879 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.57351 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.37713 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.88636 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
186
Monitored processes
100
Malicious processes
4
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "cmd.exe" /C %WINDIR%\\System32\\bcdedit.exe -set loadoptions ENABLE_INTEGRITY_CHECKS | C:\Windows\system32\cmd.exe | — | MBR Regenerator v4.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 332 | icacls "C:\Windows\\System32\\Wat\\WatUX.exe" /grant *S-1-1-0:F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 496 | findstr /I /V /C:"27.0.0.1 genuine.microsoft.com" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 504 | "cmd.exe" /C Type "%WINDIR%\\System32\\drivers\\etc\\hosts.7" | findstr /I /V /C:"127.0.0.1 catalog.microsoft.com" >>%WINDIR%\\System32\\drivers\\etc\\hosts.8 | C:\Windows\system32\cmd.exe | — | MBR Regenerator v4.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 516 | "cmd.exe" /C icacls "%WINDIR%\\System32\\Wat\\npWatWeb.dll" /grant *S-1-1-0:F | C:\Windows\system32\cmd.exe | — | MBR Regenerator v4.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 520 | "cmd.exe" /C sc config sppuinotify start= demand | C:\Windows\system32\cmd.exe | — | MBR Regenerator v4.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 520 | "cmd.exe" /C Type "%WINDIR%\\System32\\drivers\\etc\\hosts" | findstr /I /V /C:"127.0.0.1 mpa.one.microsoft.com" >>%WINDIR%\\System32\\drivers\\etc\\hosts.1 | C:\Windows\system32\cmd.exe | — | MBR Regenerator v4.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 532 | cscript "C:\Windows\\System32\\slmgr.vbs" -ipk HYF8J-CVRMY-CM74G-RPHKF-PW487 | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 716 | "cmd.exe" /C net start sppsvc | C:\Windows\system32\cmd.exe | — | MBR Regenerator v4.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 748 | "cmd.exe" /C Type "%WINDIR%\\System32\\drivers\\etc\\hosts.6" | findstr /I /V /C:"127.0.0.1 wutrack.windows.com" >>%WINDIR%\\System32\\drivers\\etc\\hosts.7 | C:\Windows\system32\cmd.exe | — | MBR Regenerator v4.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
487
Read events
416
Write events
71
Delete events
0
Modification events
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: %windir%\web\wallpaper\windows\img0.jpg | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.vbs |
| Operation: | write | Name: | |
Value: VBSFile | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.vbs\PersistentHandler |
| Operation: | write | Name: | |
Value: {5e941d80-bf96-11cd-b579-08002b30bfeb} | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile |
| Operation: | write | Name: | |
Value: VBScript Script File | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile |
| Operation: | write | Name: | FriendlyTypeName |
Value: @%SystemRoot%\System32\wshext.dll,-4802 | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile\DefaultIcon |
| Operation: | write | Name: | |
Value: %SystemRoot%\System32\WScript.exe,2 | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile\ScriptEngine |
| Operation: | write | Name: | |
Value: VBScript | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile\ScriptHostEncode |
| Operation: | write | Name: | |
Value: {85131631-480C-11D2-B1F9-00C04F86C324} | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile\Shell\Edit |
| Operation: | write | Name: | |
Value: &Edit | |||
| (PID) Process: | (3600) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VBSFile\Shell\Edit\Command |
| Operation: | write | Name: | |
Value: %SystemRoot%\System32\Notepad.exe %1 | |||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | findstr.exe | C:\Windows\System32\drivers\etc\hosts.6 | — | |
MD5:— | SHA256:— | |||
| 3232 | findstr.exe | C:\Windows\System32\drivers\etc\hosts.7 | — | |
MD5:— | SHA256:— | |||
| 3624 | findstr.exe | C:\Windows\System32\drivers\etc\hosts.8 | — | |
MD5:— | SHA256:— | |||
| 3452 | findstr.exe | C:\Windows\System32\drivers\etc\master.mbr | — | |
MD5:— | SHA256:— | |||
| 792 | MBR Regenerator v4.5.exe | C:\Users\admin\AppData\Local\Temp\MBR.tmp\tweak.reg | — | |
MD5:— | SHA256:— | |||
| 792 | MBR Regenerator v4.5.exe | C:\Users\admin\AppData\Local\Temp\MBR.tmp\bootsect.exe | — | |
MD5:— | SHA256:— | |||
| 3724 | bootsect.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 2328 | findstr.exe | C:\Windows\System32\drivers\etc\hosts.5 | text | |
MD5:3688374325B992DEF12793500307566D | SHA256:2D6BDFB341BE3A6234B24742377F93AA7C7CFB0D9FD64EFA9282C87852E57085 | |||
| 2528 | findstr.exe | C:\Windows\System32\drivers\etc\hosts.4 | text | |
MD5:3688374325B992DEF12793500307566D | SHA256:2D6BDFB341BE3A6234B24742377F93AA7C7CFB0D9FD64EFA9282C87852E57085 | |||
| 1788 | cmd.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:3688374325B992DEF12793500307566D | SHA256:2D6BDFB341BE3A6234B24742377F93AA7C7CFB0D9FD64EFA9282C87852E57085 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report