| File name: | C:\Users\admin\AppData\Local\Temp\564_840383999\_platform_specific\win_x86\widevinecdm.dll |
| Full analysis: | https://app.any.run/tasks/600fe760-2531-4856-8744-3bbbea234353 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2021, 00:51:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (console) Intel 80386, for MS Windows |
| MD5: | 7A59D939F28964955AC301DB8518861C |
| SHA1: | E00C28F3490484CFF2F27C0ACEA36791173E0A0F |
| SHA256: | 787294FD7FE47F7FA7F735403928EAF96E04724207891FD6DB727B2A5B58D340 |
| SSDEEP: | 196608:SvzfCpdfdOiwEV525gxykVP5twd+FmYpcumk2s2s1M6vQ7QJxWuveJMjJ:SYxNBtwiJtmk2sH2oQ7QJxpeY |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 656)
- svchost.exe (PID: 884)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 656)
Application launched itself
- explorer.exe (PID: 656)
Executed as Windows Service
- PresentationFontCache.exe (PID: 3644)
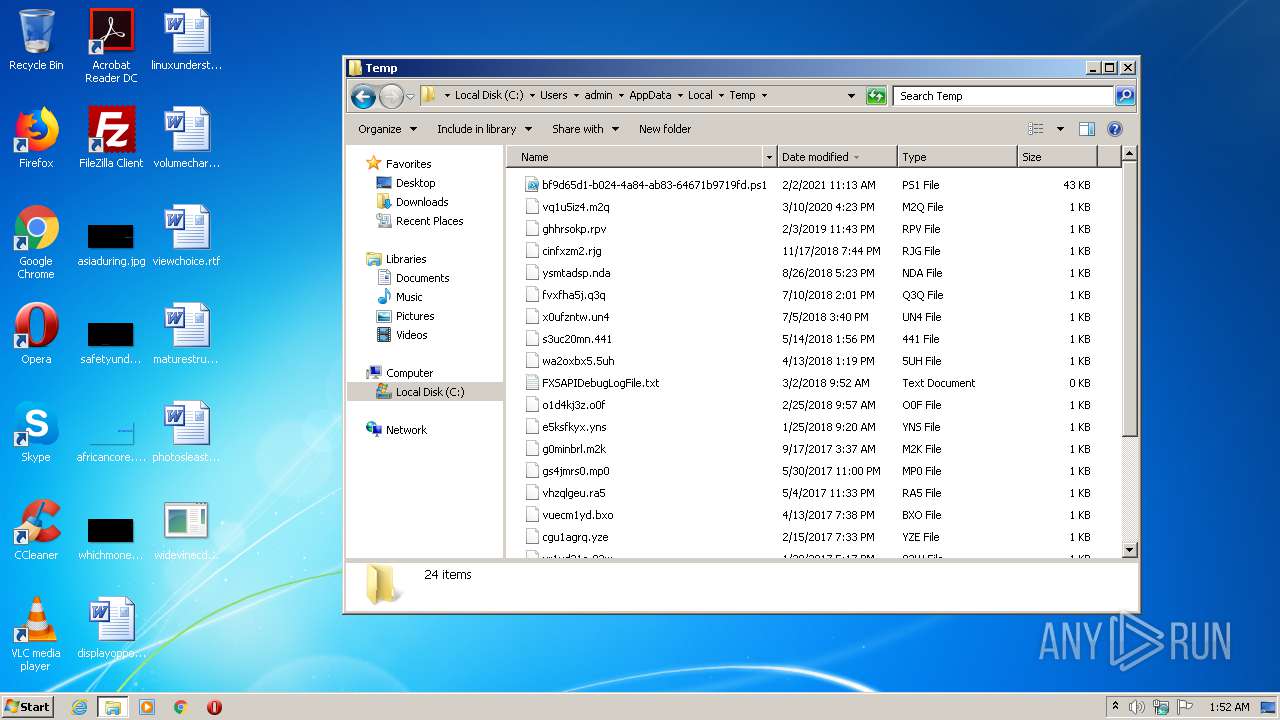
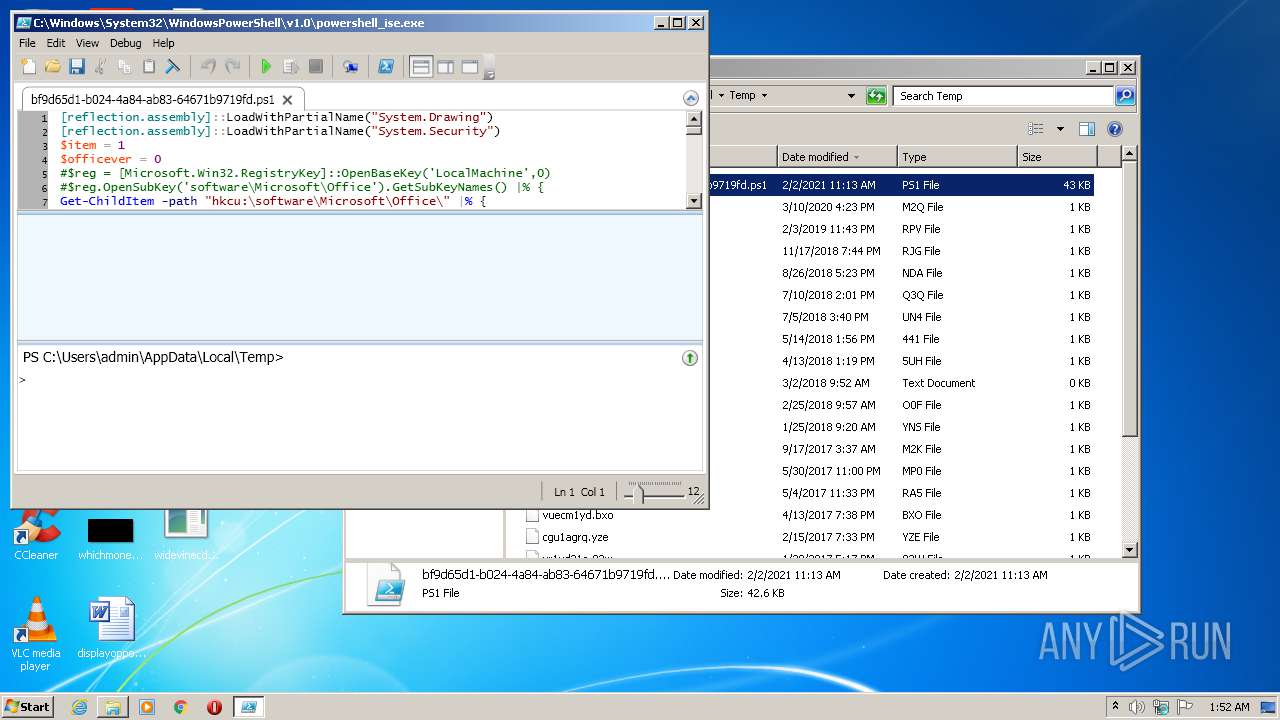
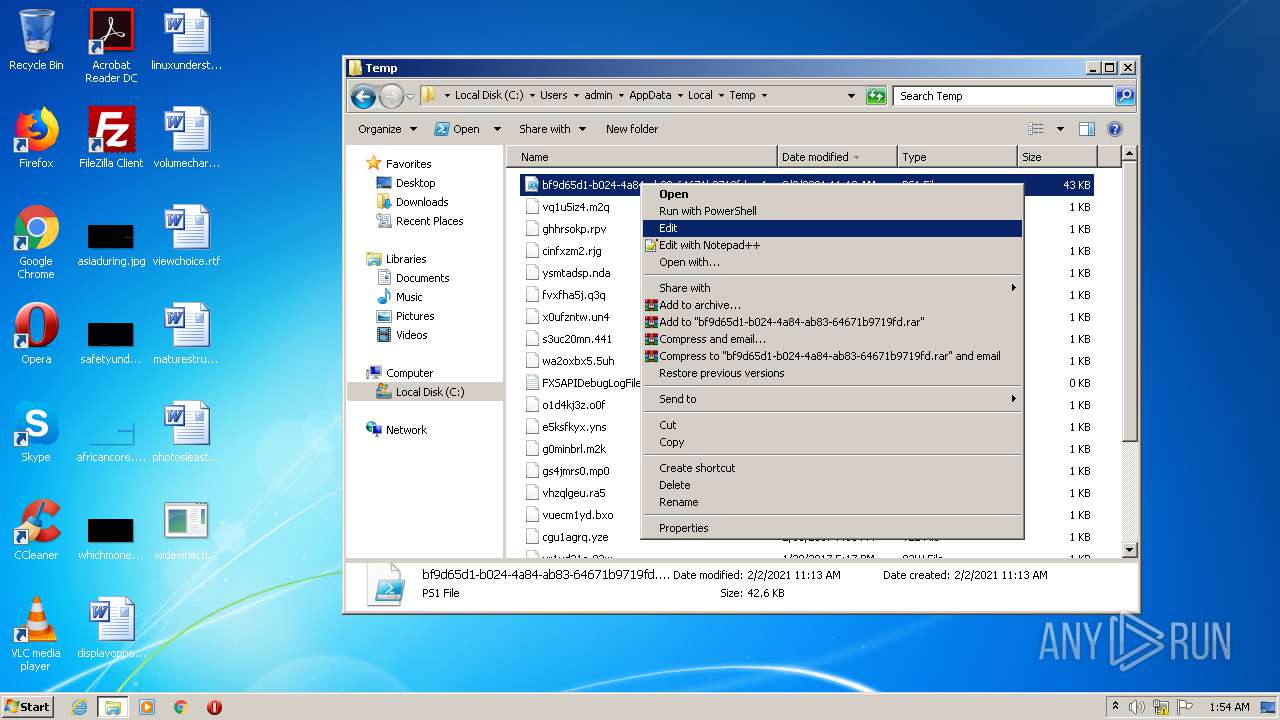
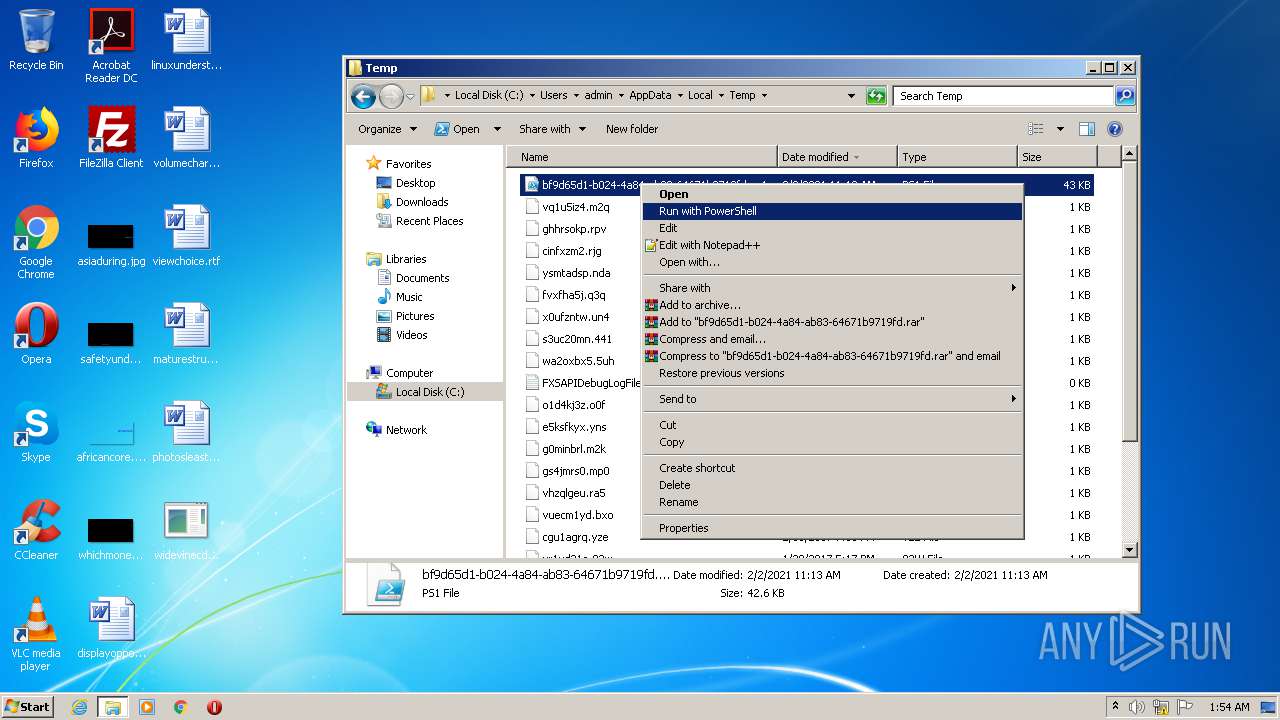
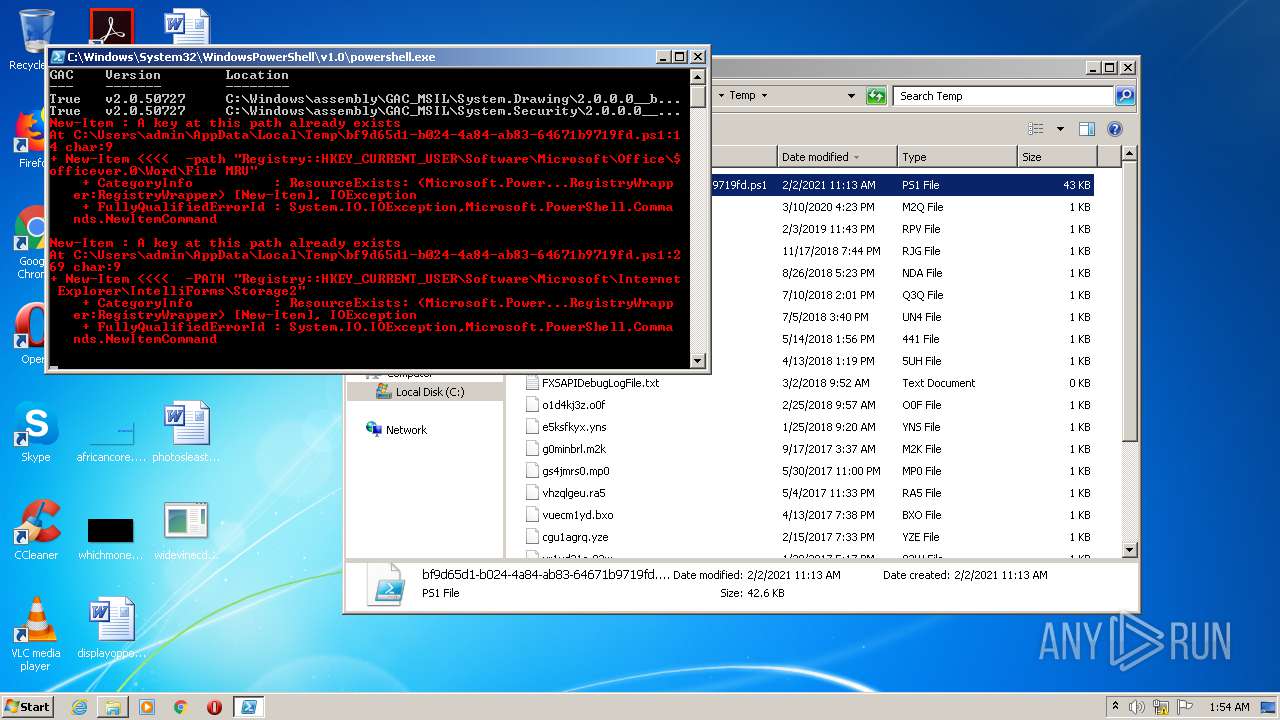
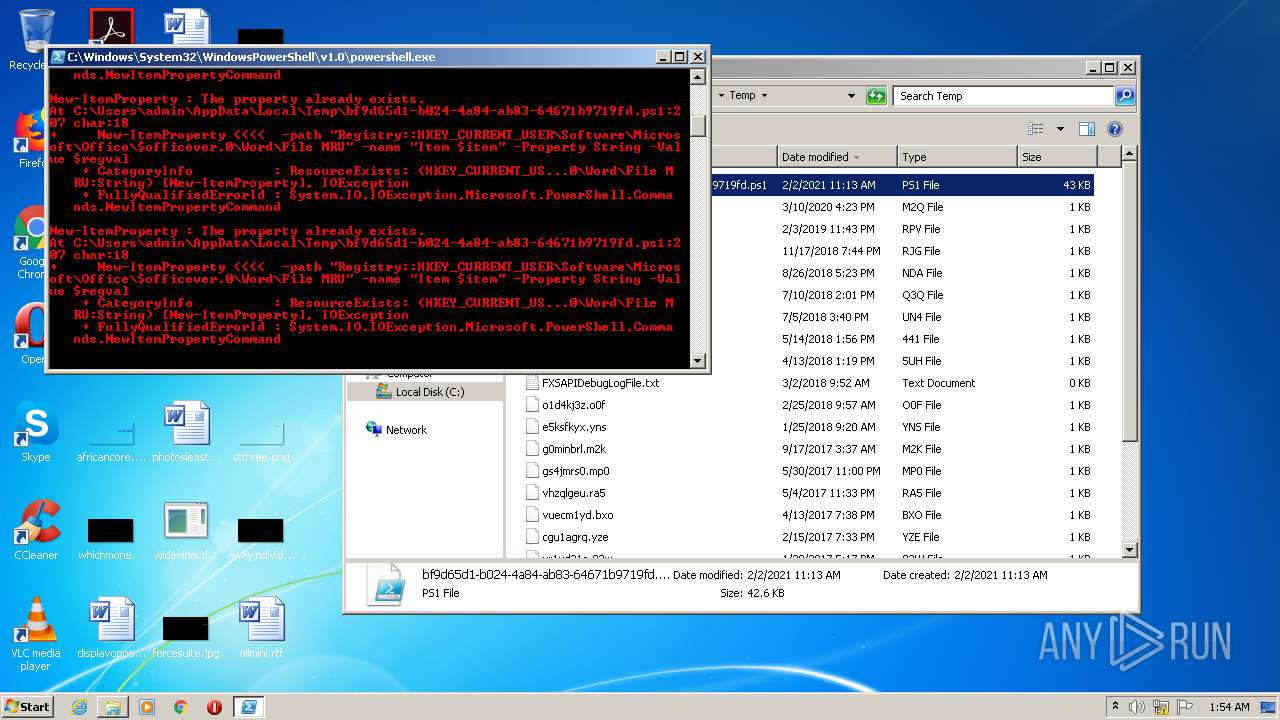
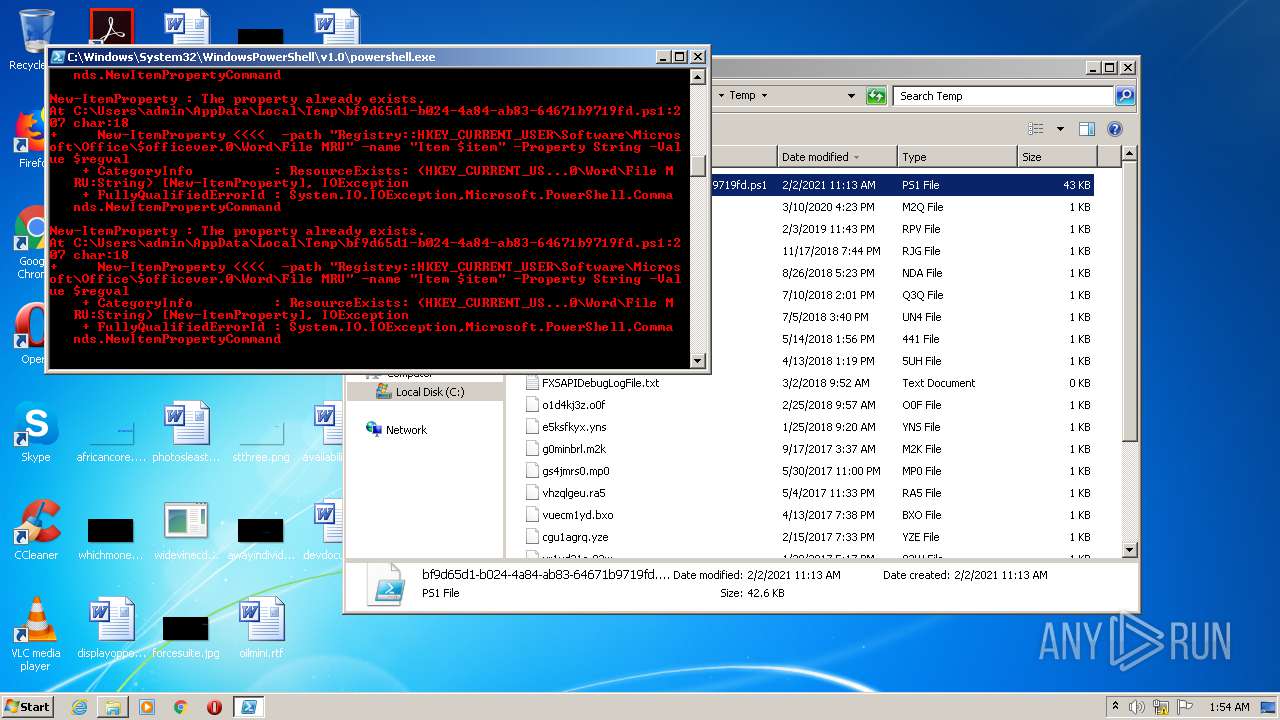
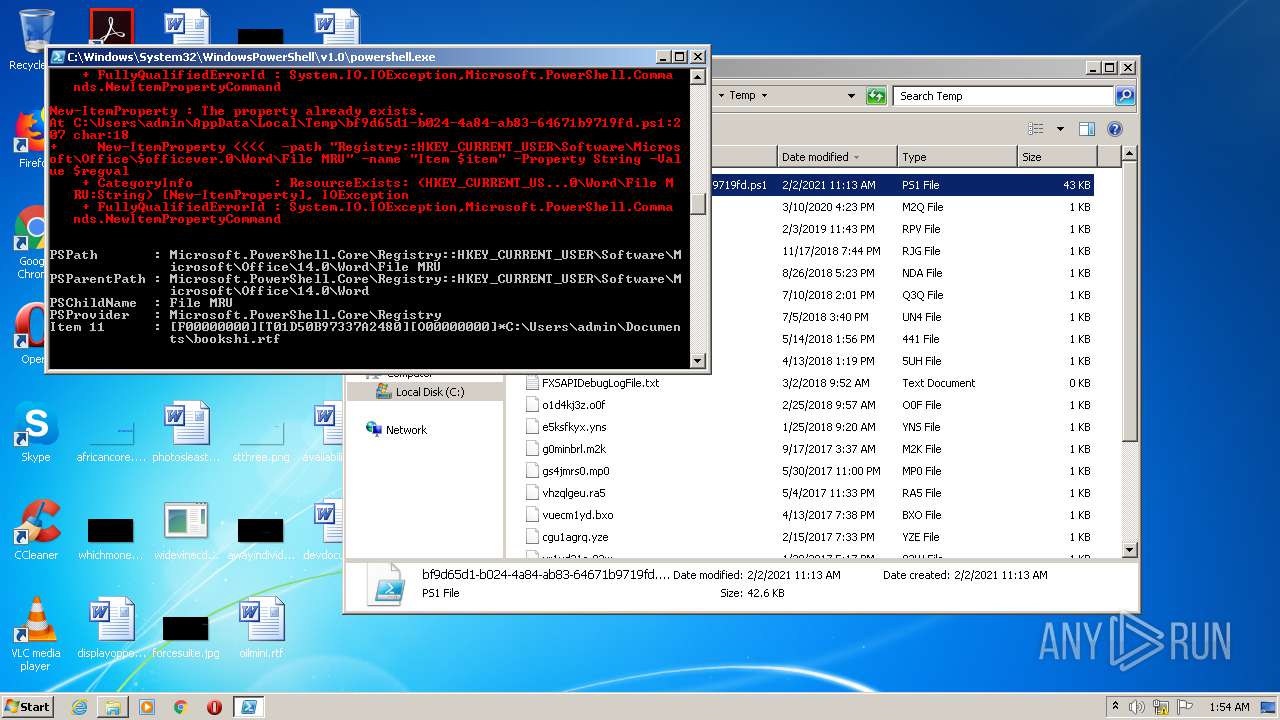
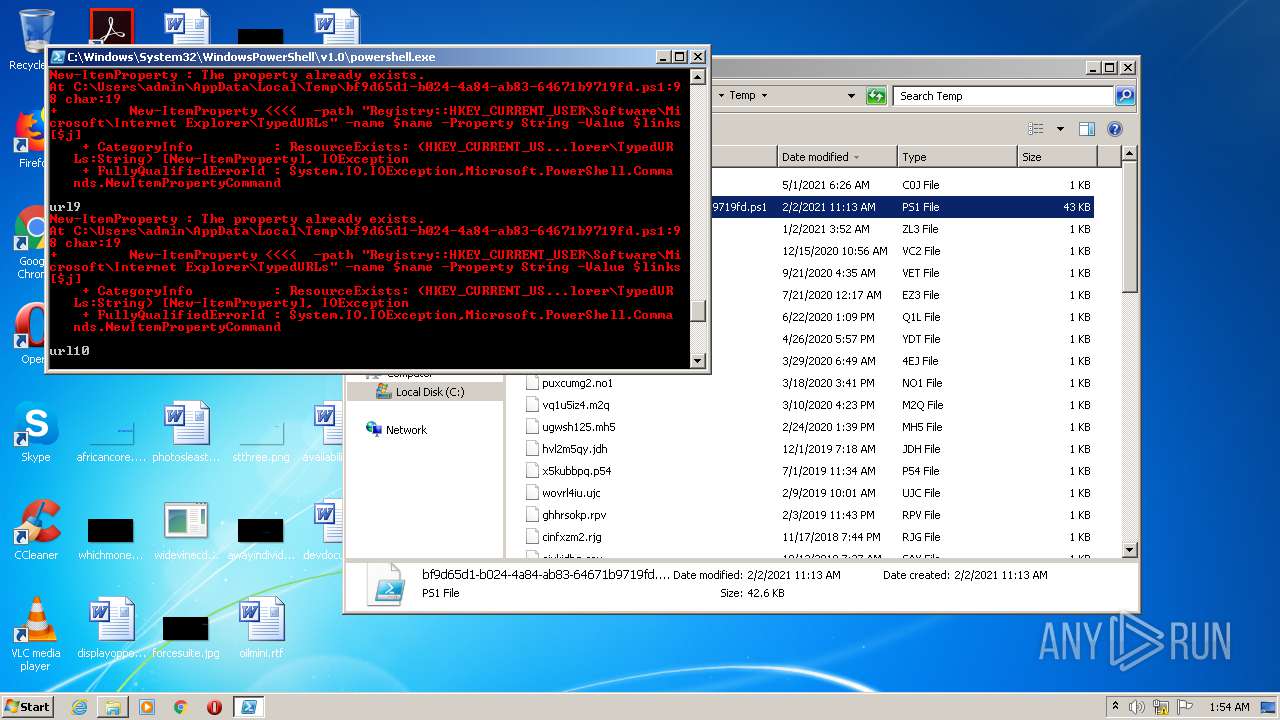
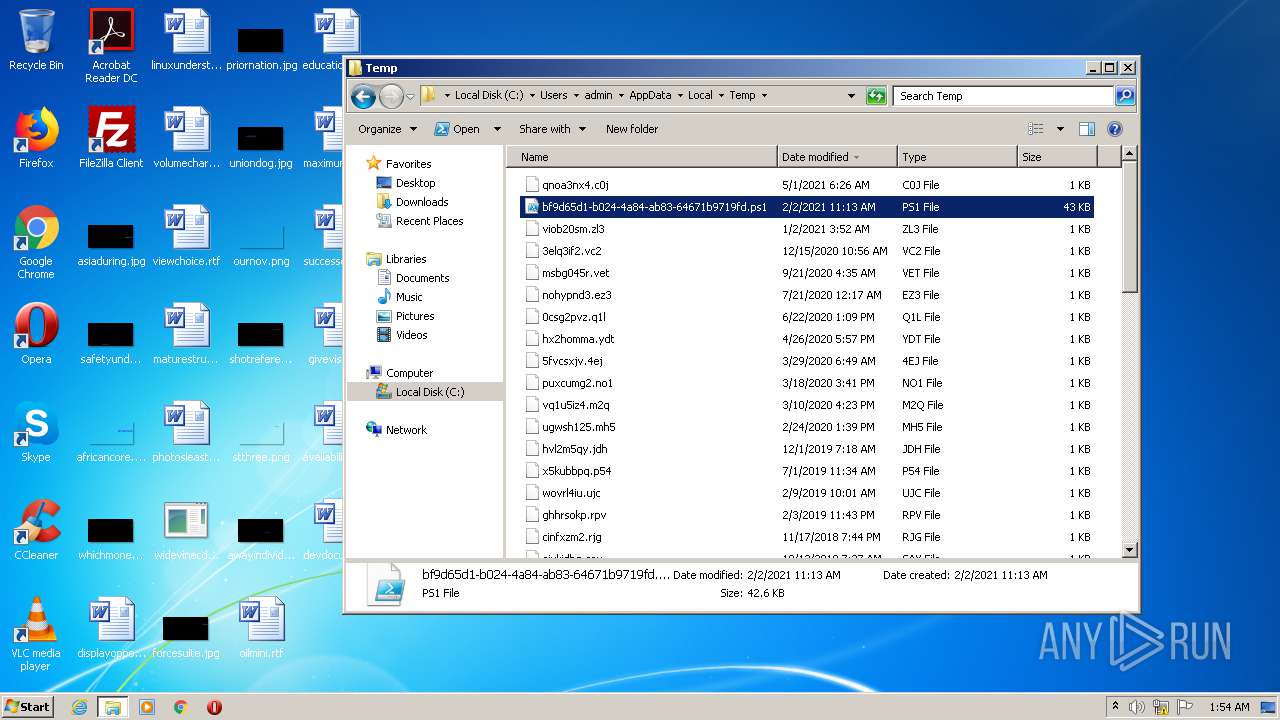
Executes PowerShell scripts
- explorer.exe (PID: 656)
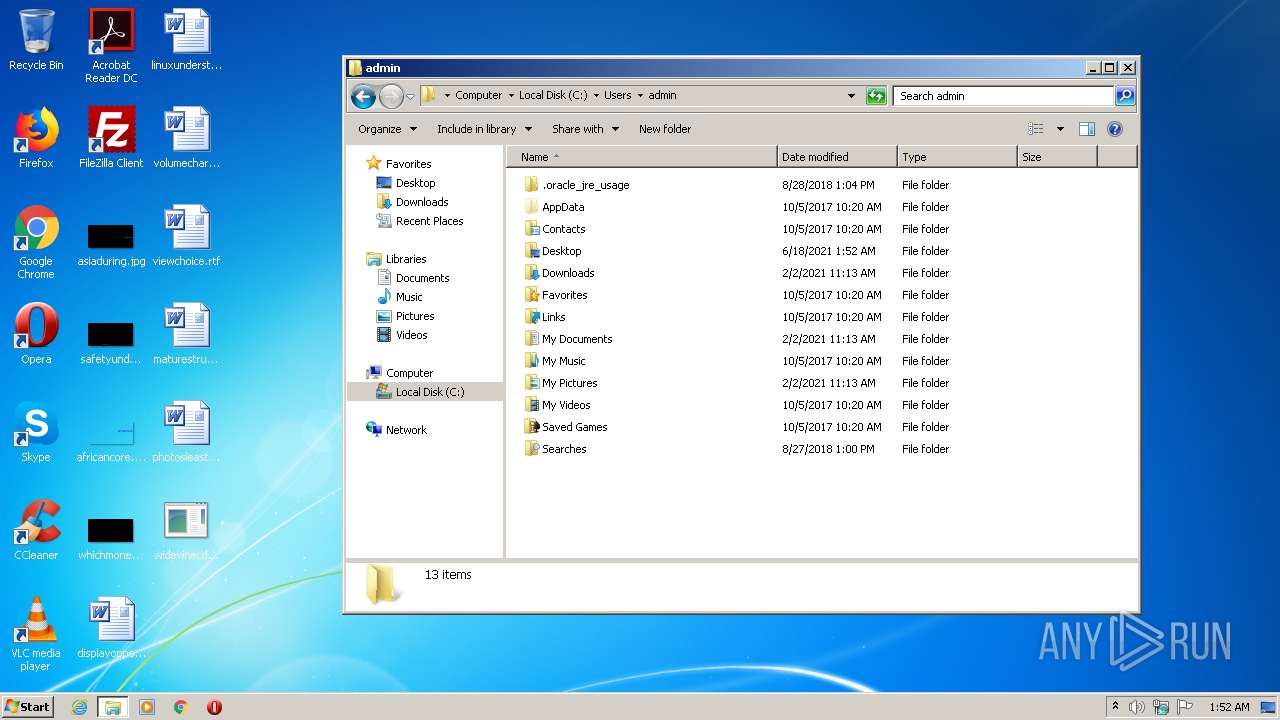
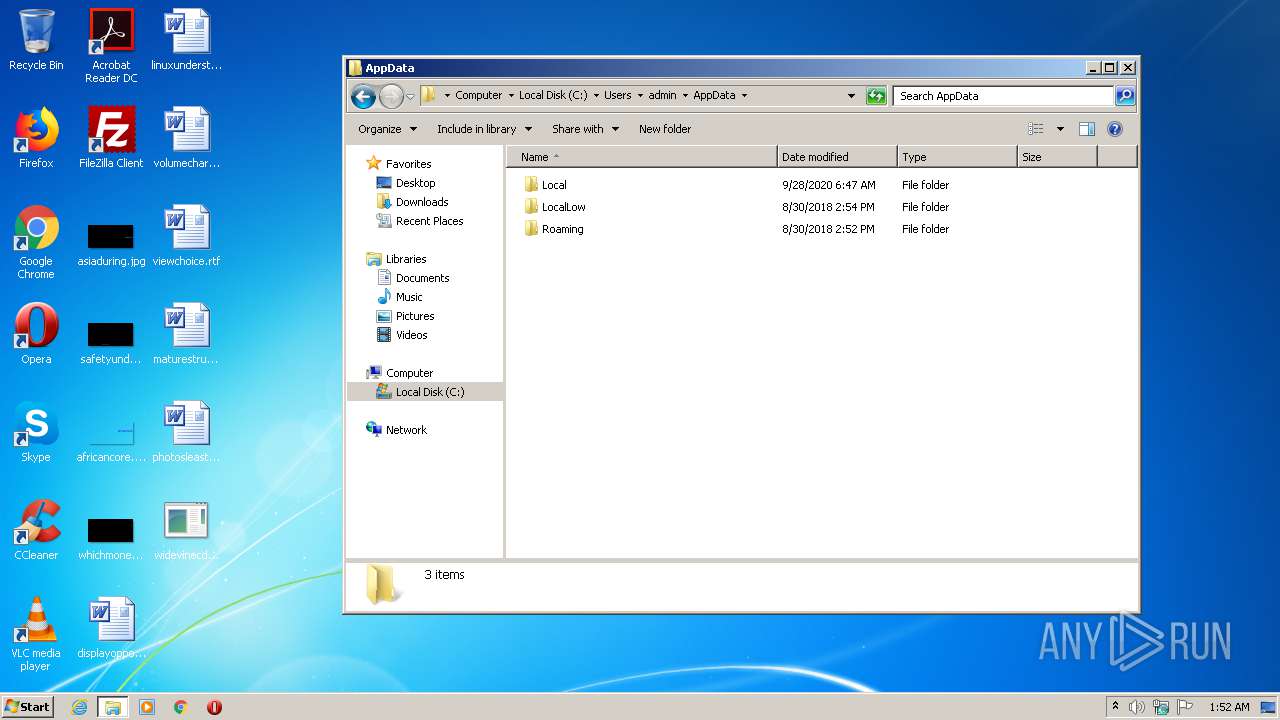
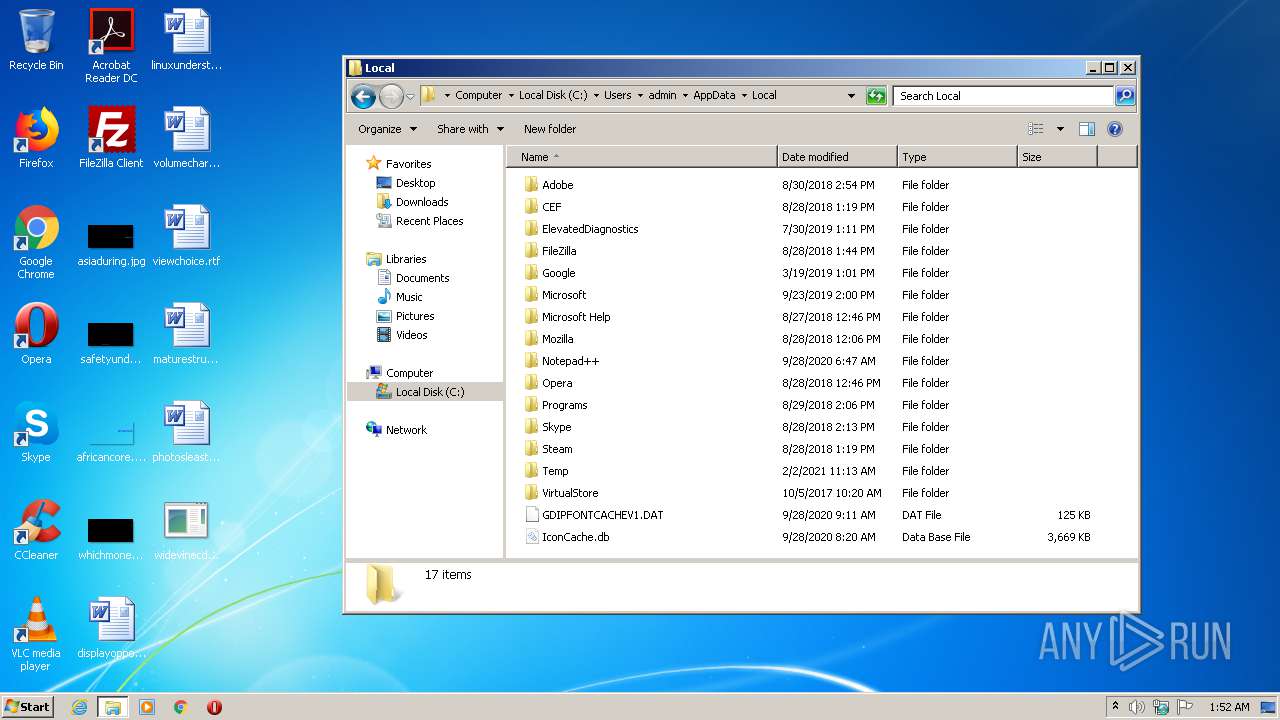
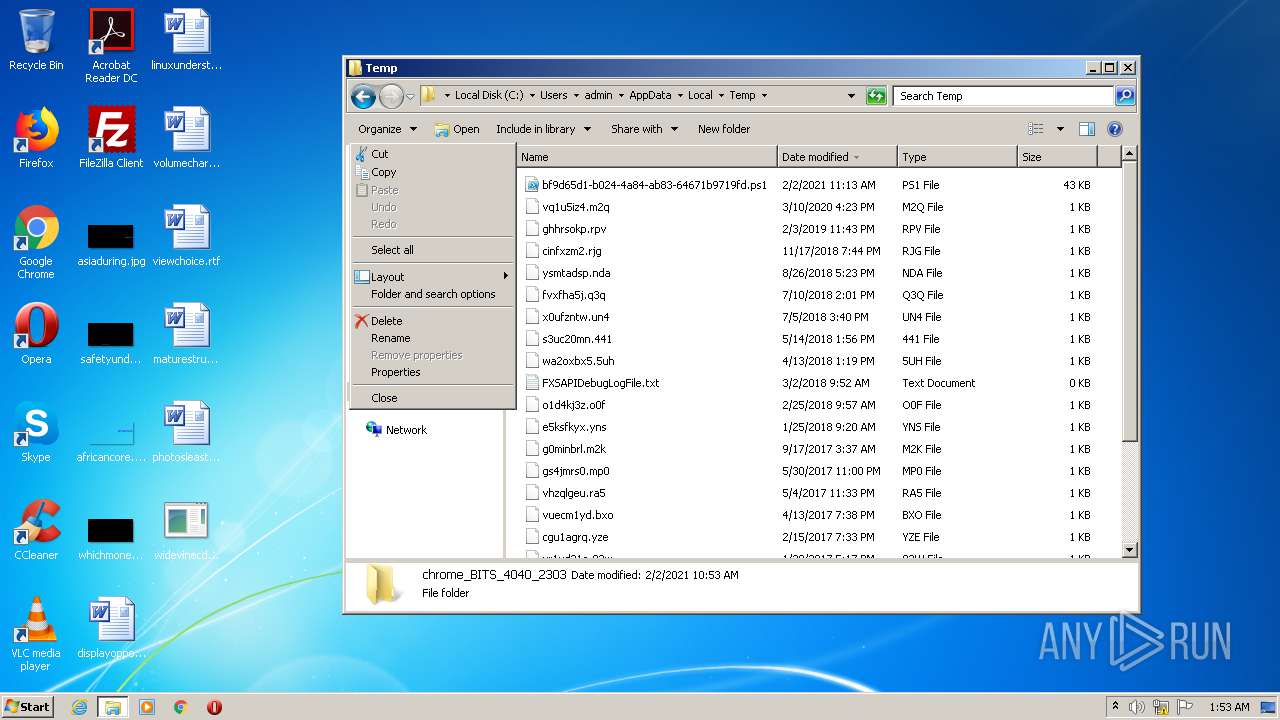
Creates files in the user directory
- powershell.exe (PID: 2976)
INFO
Loads main object executable
- rundll32.exe (PID: 2156)
Reads Microsoft Office registry keys
- powershell.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| OfficialBuild: | - |
|---|---|
| LastChange: | - |
| ProductShortName: | Widevine CDM |
| CompanyShortName: | |
| ProductVersion: | 4.10.2209.0 |
| ProductName: | Widevine Content Decryption Module |
| OriginalFileName: | widevinecdm.dll |
| LegalCopyright: | Copyright 2012 Google LLC. All rights reserved. |
| InternalName: | widevinecdm |
| FileVersion: | 4.10.2209.0 |
| FileDescription: | Widevine Content Decryption Module |
| CompanyName: | Google LLC |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 4.10.2209.0 |
| FileVersionNumber: | 4.10.2209.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x46a1d0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4968448 |
| CodeSize: | 4777472 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:01:26 21:40:51+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 26-Jan-2021 20:40:51 |
| Detected languages: |
|
| TLS Callbacks: | 3 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Google LLC |
| FileDescription: | Widevine Content Decryption Module |
| FileVersion: | 4.10.2209.0 |
| InternalName: | widevinecdm |
| LegalCopyright: | Copyright 2012 Google LLC. All rights reserved. |
| OriginalFilename: | widevinecdm.dll |
| ProductName: | Widevine Content Decryption Module |
| ProductVersion: | 4.10.2209.0 |
| CompanyShortName: | |
| ProductShortName: | Widevine CDM |
| LastChange: | 0 |
| Official Build: | 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 26-Jan-2021 20:40:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0048E49C | 0x0048E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.81708 |
.rdata | 0x00490000 | 0x004945BC | 0x00494600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.93688 |
.data | 0x00925000 | 0x00ABF3B4 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.66771 |
.00cfg | 0x013E5000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0815394 |
.rodata | 0x013E6000 | 0x00000740 | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.22321 |
.tls | 0x013E7000 | 0x000000A9 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.136464 |
.voltbl | 0x013E8000 | 0x000000F0 | 0x00000200 | 3.73746 | |
.rsrc | 0x013E9000 | 0x00000488 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.69675 |
.reloc | 0x013EA000 | 0x00024BC4 | 0x00024C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.50319 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.44838 | 1064 | UNKNOWN | English - United States | RT_VERSION |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
WINMM.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
0 | 0x00000000 | |
CreateCdmInstance | 1 | 0x00001080 |
DeinitializeCdmModule | 2 | 0x00001060 |
GetCdmVersion | 3 | 0x00001200 |
GetHandleVerifier | 4 | 0x00333800 |
InitializeCdmModule_4 | 5 | 0x00001030 |
VerifyCdmHost_0 | 6 | 0x00001210 |
Total processes
52
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 884 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\widevinecdm.dll.exe", CreateCdmInstance | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
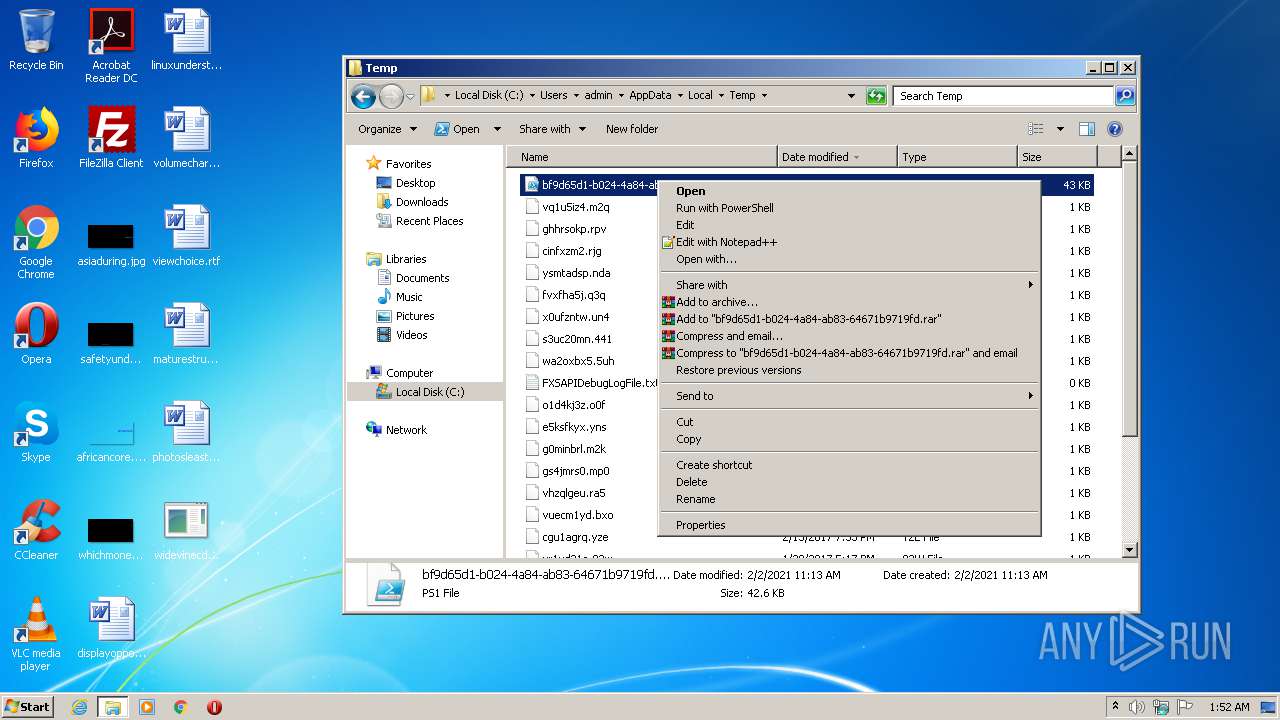
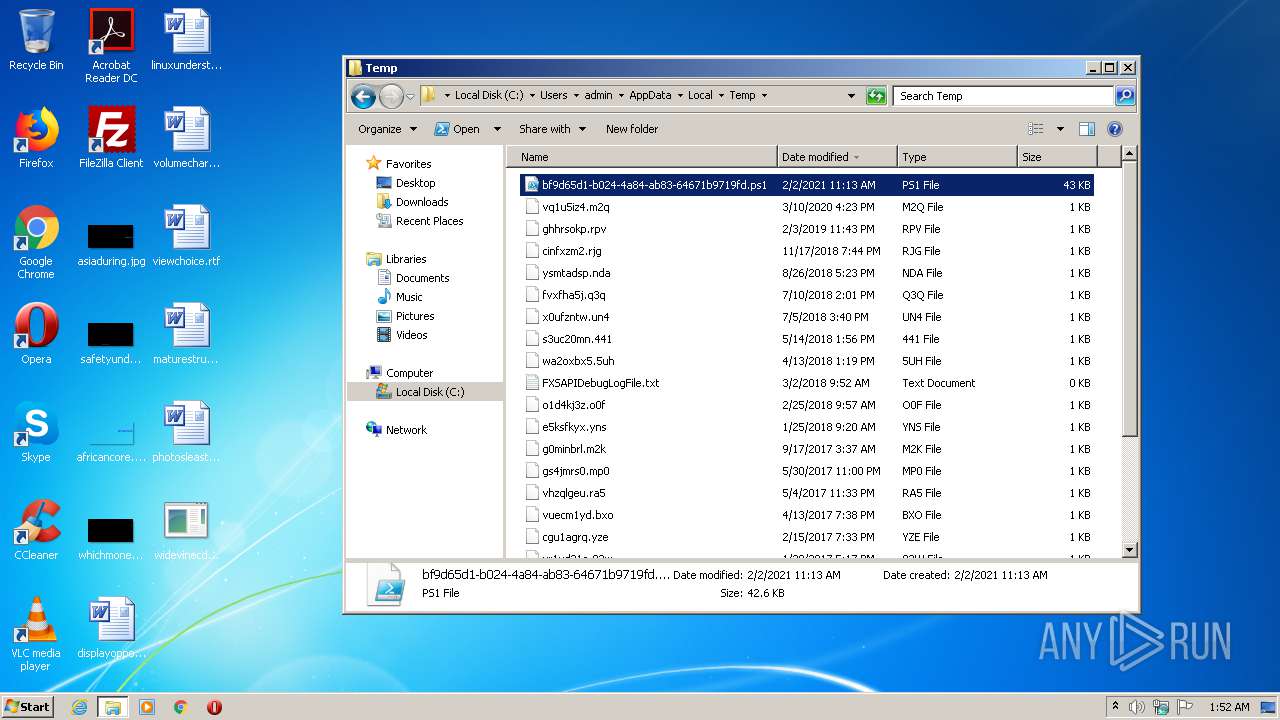
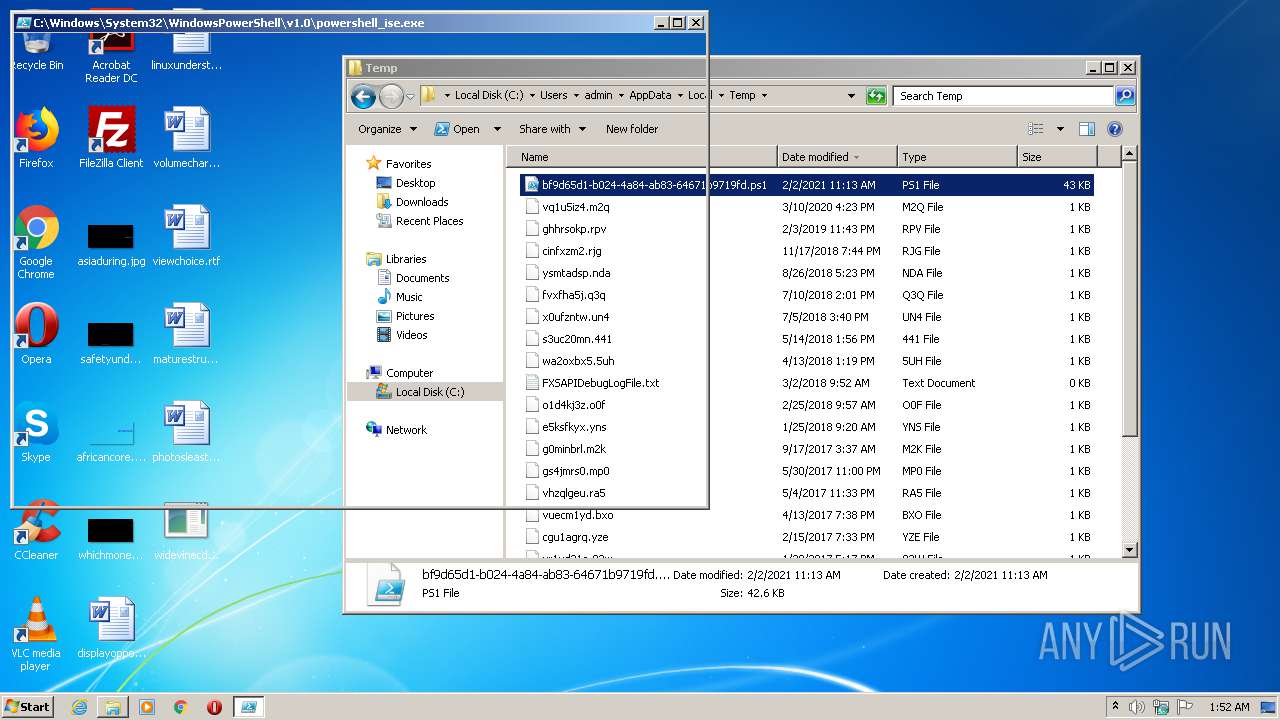
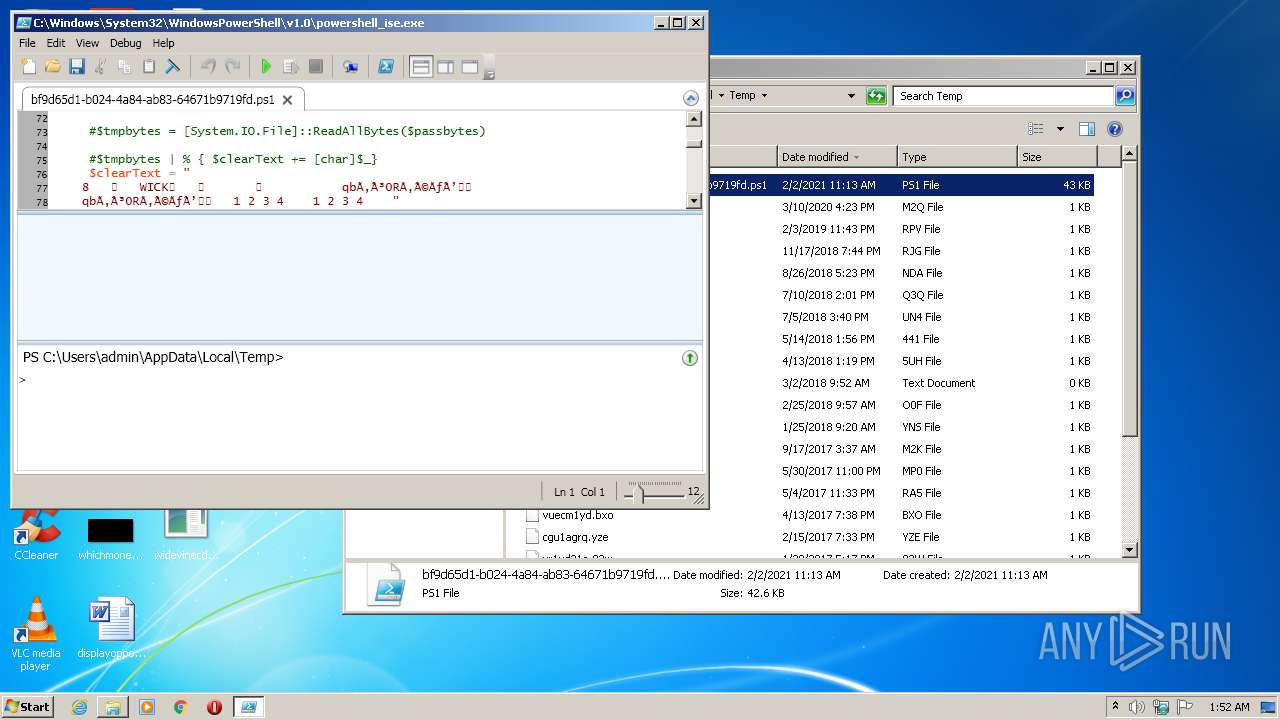
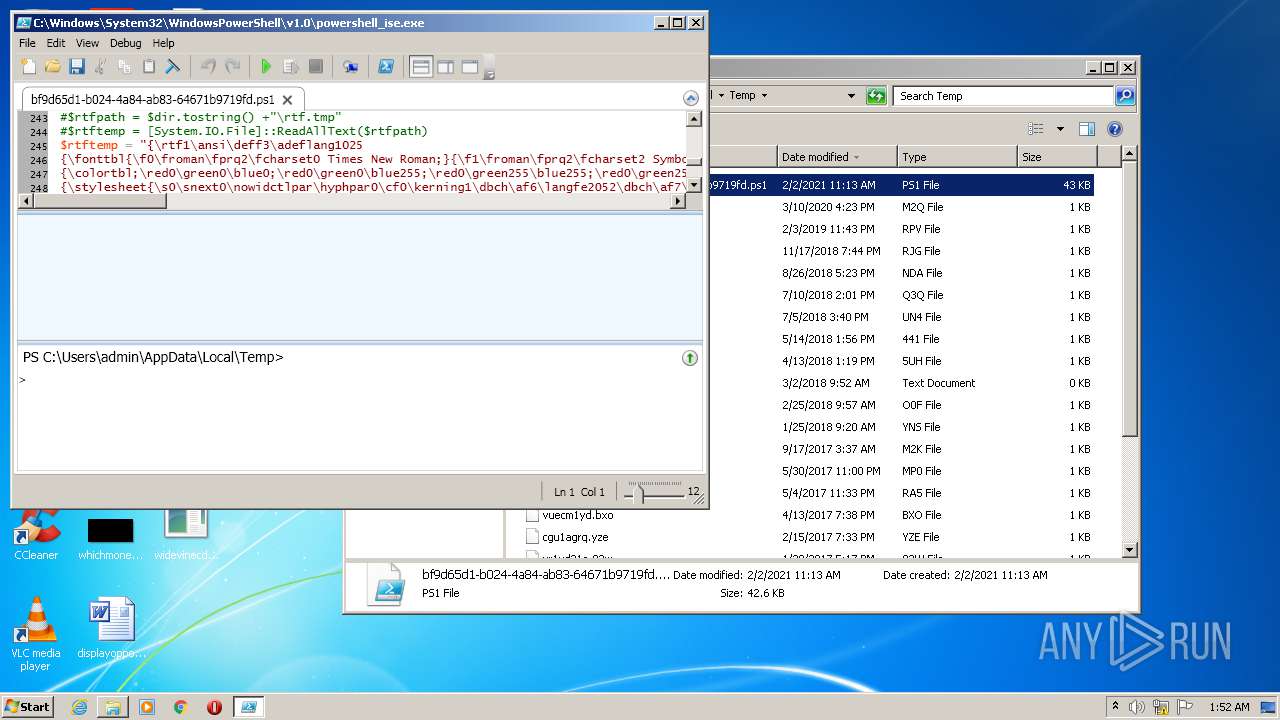
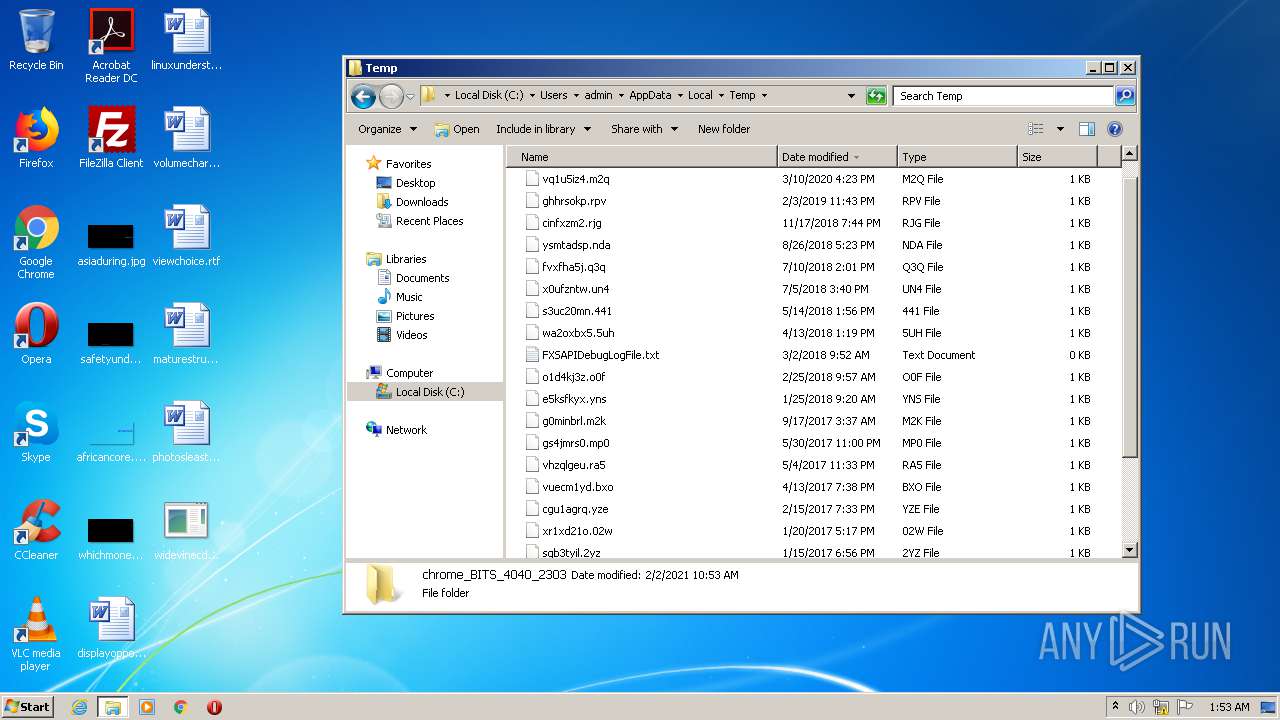
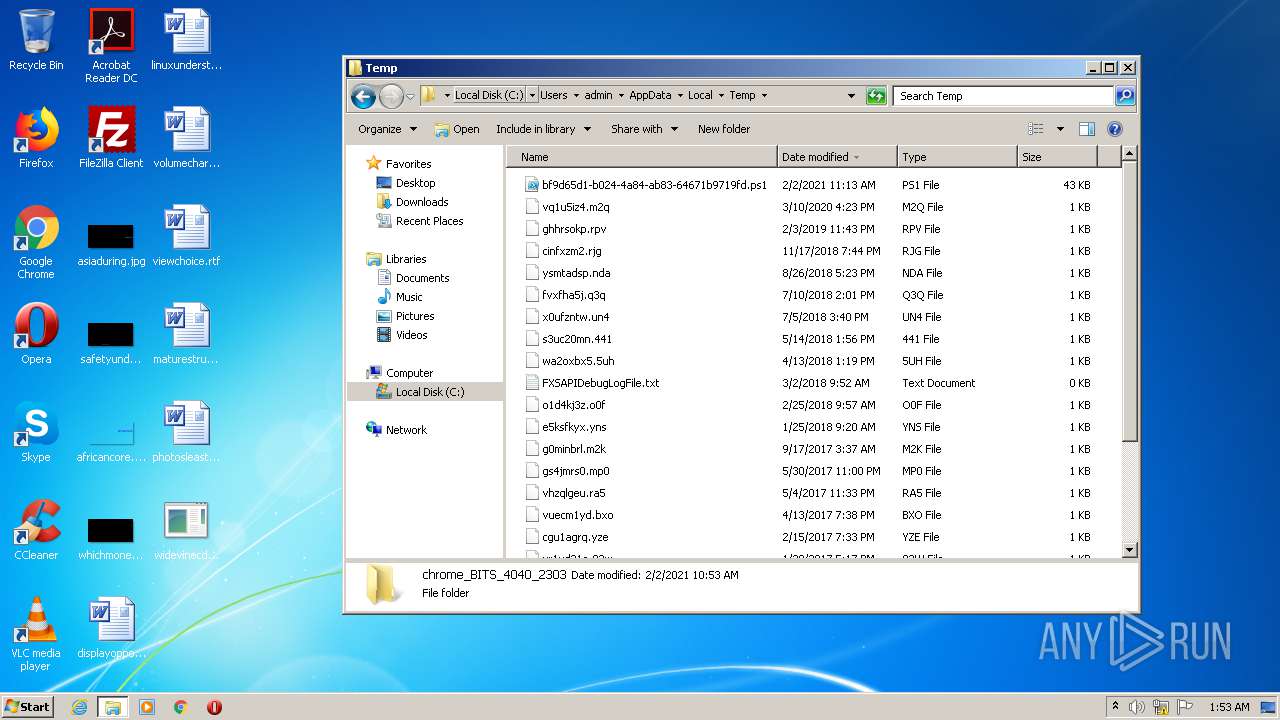
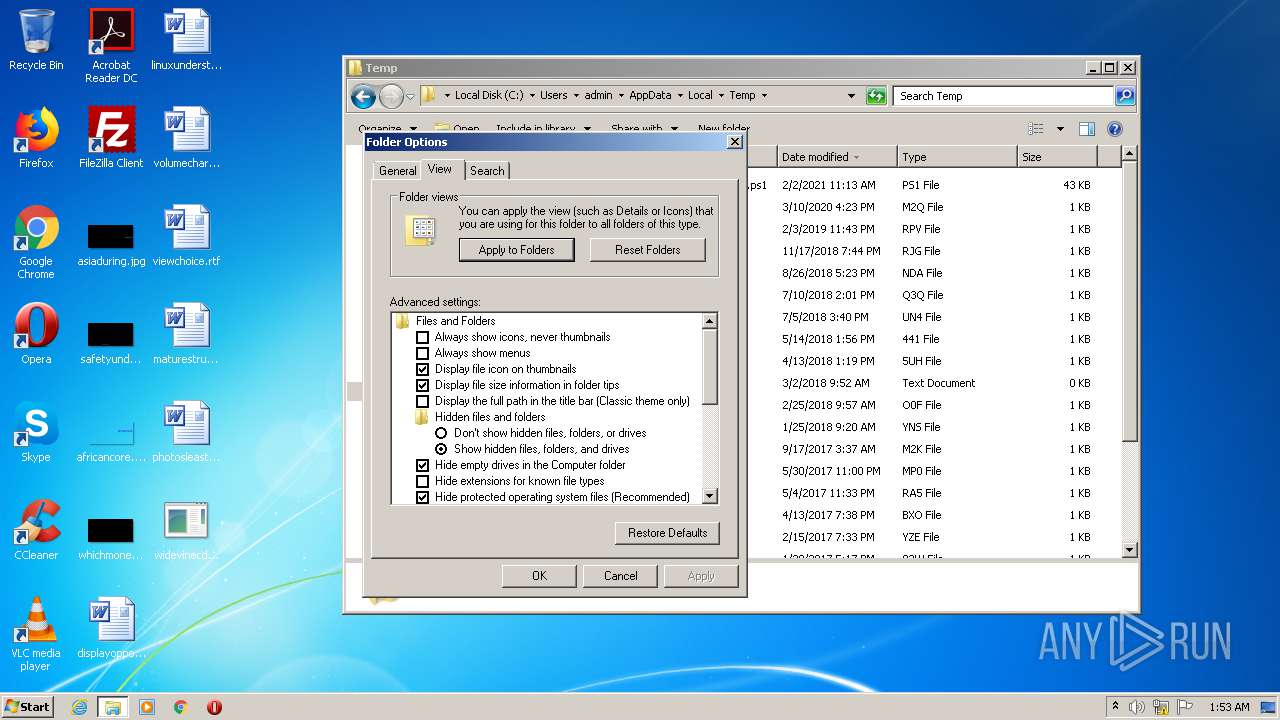
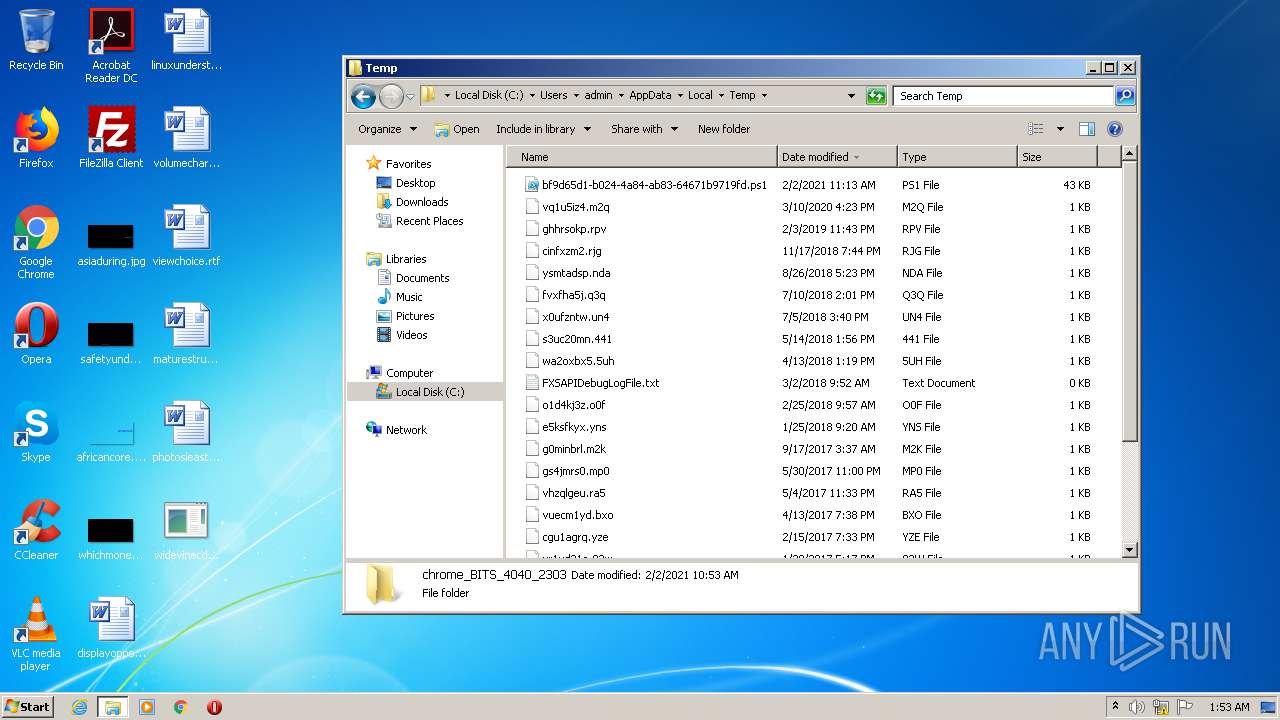
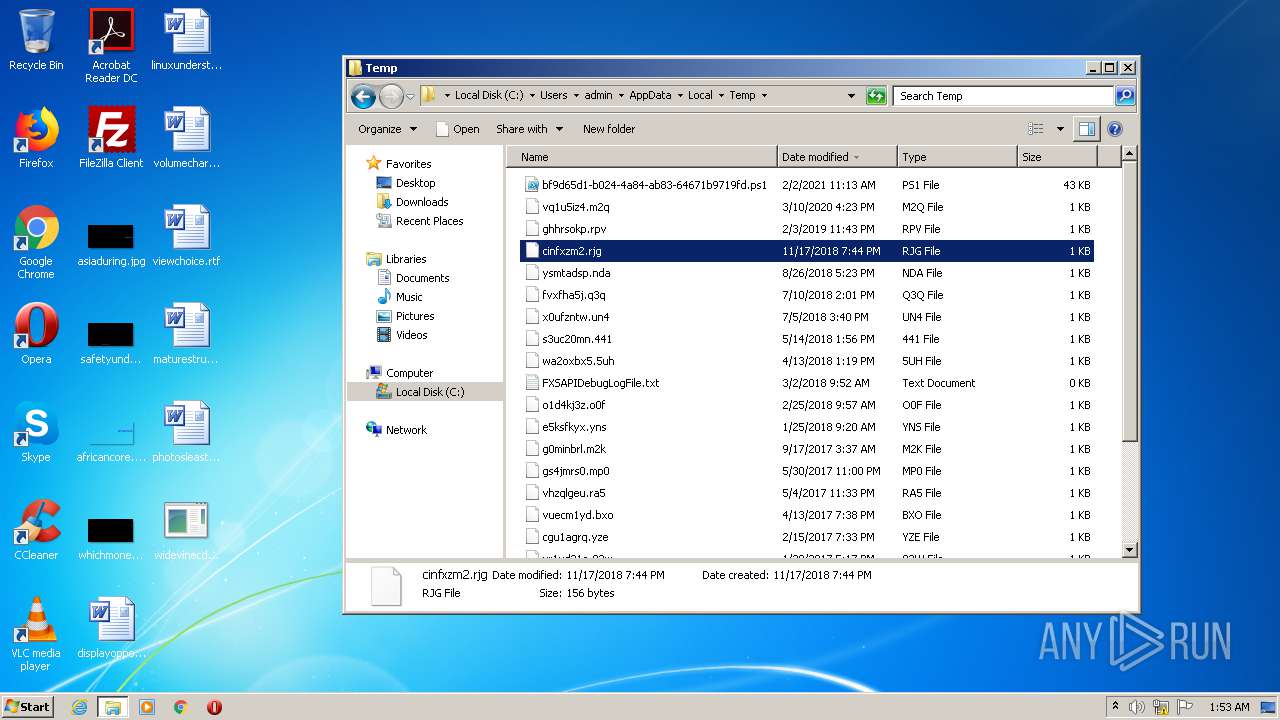
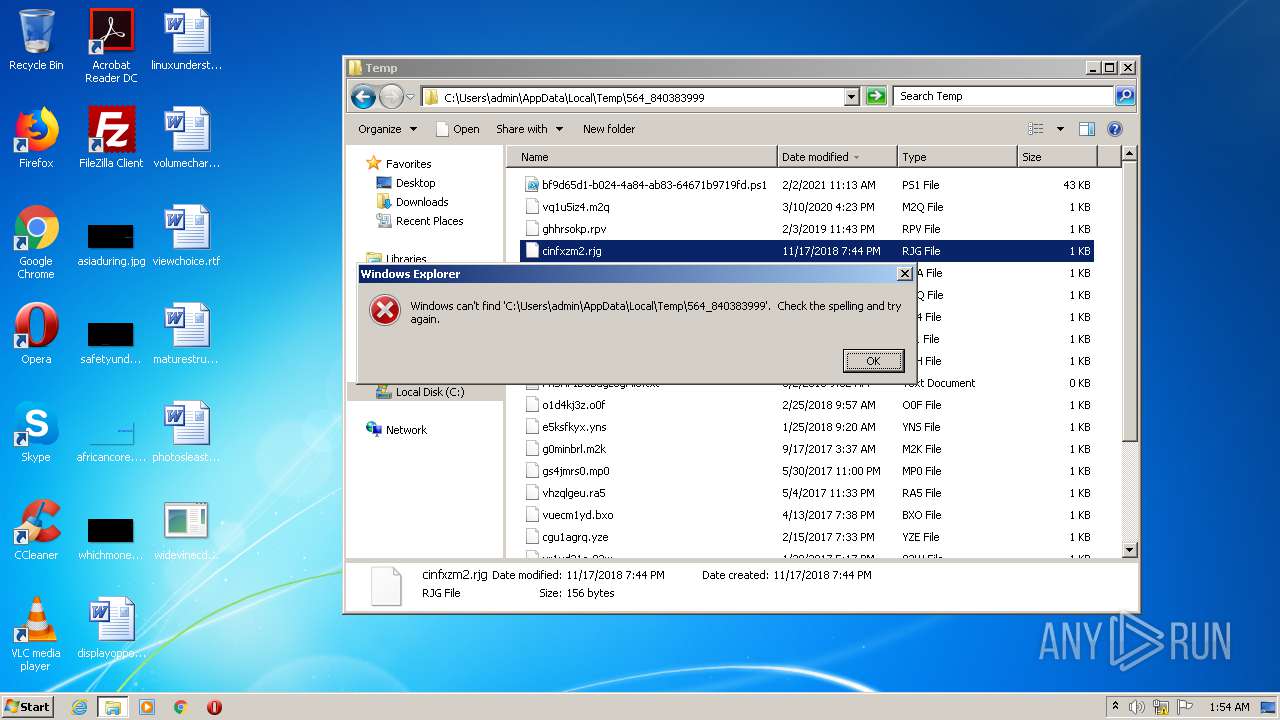
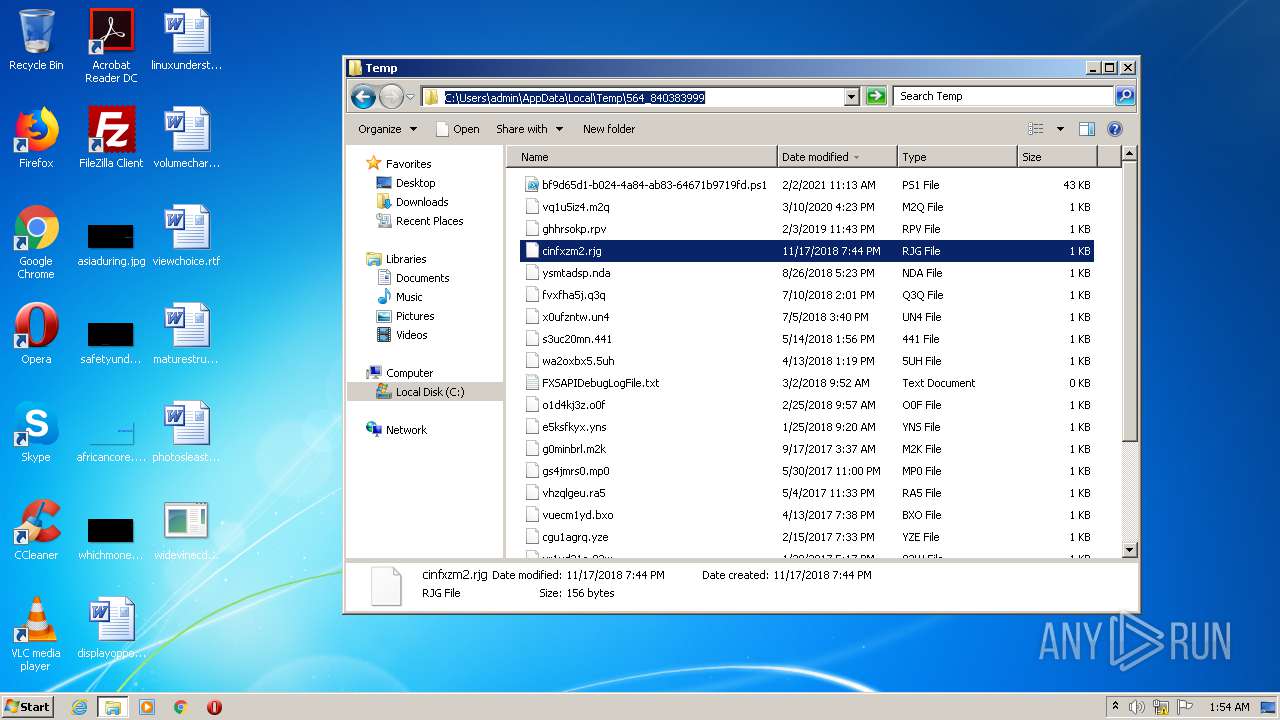
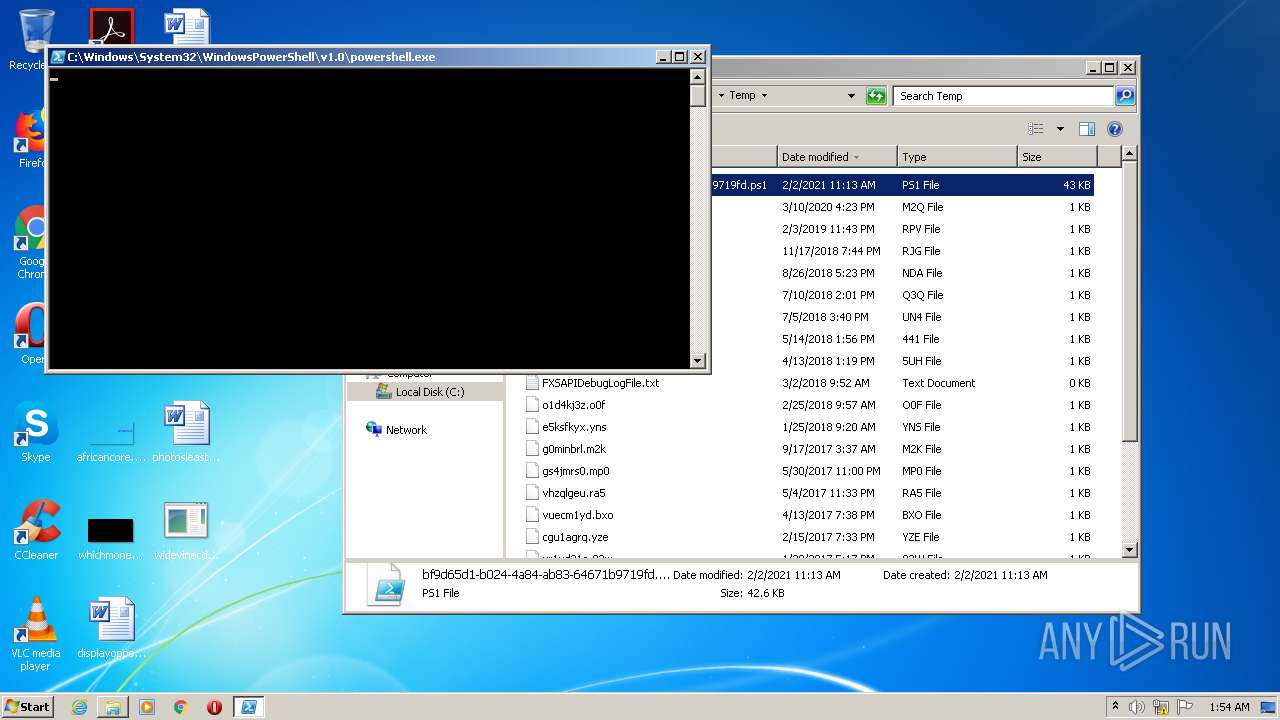
| 2976 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\bf9d65d1-b024-4a84-ab83-64671b9719fd.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3644 | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: PresentationFontCache.exe Exit code: 0 Version: 3.0.6920.4902 built by: NetFXw7 Modules
| |||||||||||||||
| 3648 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" "C:\Users\admin\AppData\Local\Temp\bf9d65d1-b024-4a84-ab83-64671b9719fd.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 255
Read events
7 750
Write events
505
Delete events
0
Modification events
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 00000000110000003400000086971600000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFD0FE3730DC63D70100000000 | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000006E0000009D000000398A46001100000034000000869716007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000FAA41C03F8A41C03B8F9187651020000600000000000000003000000000000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00003DE32F0014D3D70333ABD1773D1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702003DE32F0068D3D703D082C202E8D3D70300000000A50100006D01000012000000340000000A00000070D3D703FDE1F275E507000068D3D703E507060012000000340012006D011200D0FE3730DC63D70198D3D70357C11C7684D3D703E8D3D70362C11C76E5070600050012001100000034000000869716007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000FAA41C03F8A41C03B8F9187651020000600000000000000003000000000000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00003DE32F0014D3D70333ABD1773D1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702003DE32F0068D3D703D082C202E8D3D70300000000A50100006D01000012000000340000000A00000070D3D703FDE1F275E507000068D3D703E507060012000000340012006D011200D0FE3730DC63D70198D3D70357C11C7684D3D703E8D3D70362C11C76E5070600050012001100000034000000869716007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000FAA41C03F8A41C03B8F9187651020000600000000000000003000000000000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00003DE32F0014D3D70333ABD1773D1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702003DE32F0068D3D703D082C202E8D3D70300000000A50100006D01000012000000340000000A00000070D3D703FDE1F275E507000068D3D703E507060012000000340012006D011200D0FE3730DC63D70198D3D70357C11C7684D3D703E8D3D70362C11C76E507060005001200 | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000110000000000000010000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFC0483A30DC63D70100000000 | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003300000000000000320000001100000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00004CE32F0014D3D70333ABD1774C1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702004CE32F0068D3D703B88DC202E8D3D70300000000A50100007C01000012000000340000000A00000070D3D703FDE1F275E507000068D3D703E507060012000000340012007C011200C0483A30DC63D70198D3D70357C11C7684D3D703E8D3D70362C11C76E5070600050012001100000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00004CE32F0014D3D70333ABD1774C1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702004CE32F0068D3D703B88DC202E8D3D70300000000A50100007C01000012000000340000000A00000070D3D703FDE1F275E507000068D3D703E507060012000000340012007C011200C0483A30DC63D70198D3D70357C11C7684D3D703E8D3D70362C11C76E5070600050012001100000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00004CE32F0014D3D70333ABD1774C1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702004CE32F0068D3D703B88DC202E8D3D70300000000A50100007C01000012000000340000000A00000070D3D703FDE1F275E507000068D3D703E507060012000000340012007C011200C0483A30DC63D70198D3D70357C11C7684D3D703E8D3D70362C11C76E507060005001200 | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000110000000000000011000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFC0483A30DC63D70100000000 | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003300000000000000330000001100000000000000110000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00004CE32F0014D3D70333ABD1774C1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702004CE32F0068D3D703B88DC202E8D3D70300000000A5010000A8D300001526115958D3D70382911976A8D3D7035CD3D70327951976000000004492C20284D3D703CD9419764492C20230D4D703B88DC202E194197600000000B88DC20230D4D7038CD3D7031100000000000000110000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00004CE32F0014D3D70333ABD1774C1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702004CE32F0068D3D703B88DC202E8D3D70300000000A5010000A8D300001526115958D3D70382911976A8D3D7035CD3D70327951976000000004492C20284D3D703CD9419764492C20230D4D703B88DC202E194197600000000B88DC20230D4D7038CD3D7031100000000000000110000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000030D2D703399CFF7500A51C0300030000000000000D00000000A81C03AF02000000A51C0360D2D70343191976AFA71C03385E0D035E00000000A51C03C8462703AF020000B8F91876602627036026270370D2D70364191976C8462703385E0D0308D7D703BF431976C84627030000000000000000FFFFFFFF000000000000000000000000385E0D03505E0D03385E0D037A5E0D0300000000000000000000000000001976904B2103A05E0D0354D7D703BF431976904B21030000000000000000FFFFFFFF000000000000000000000000A05E0D03B85E0D03A05E0D03E25E0D03CC0B00004CE32F0014D3D70333ABD1774C1B514D110C00001027000011000000E257020048D3D703F8AAD177E25702004CE32F0068D3D703B88DC202E8D3D70300000000A5010000A8D300001526115958D3D70382911976A8D3D7035CD3D70327951976000000004492C20284D3D703CD9419764492C20230D4D703B88DC202E194197600000000B88DC20230D4D7038CD3D703 | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000B000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
Executable files
0
Suspicious files
29
Text files
32
Unknown types
16
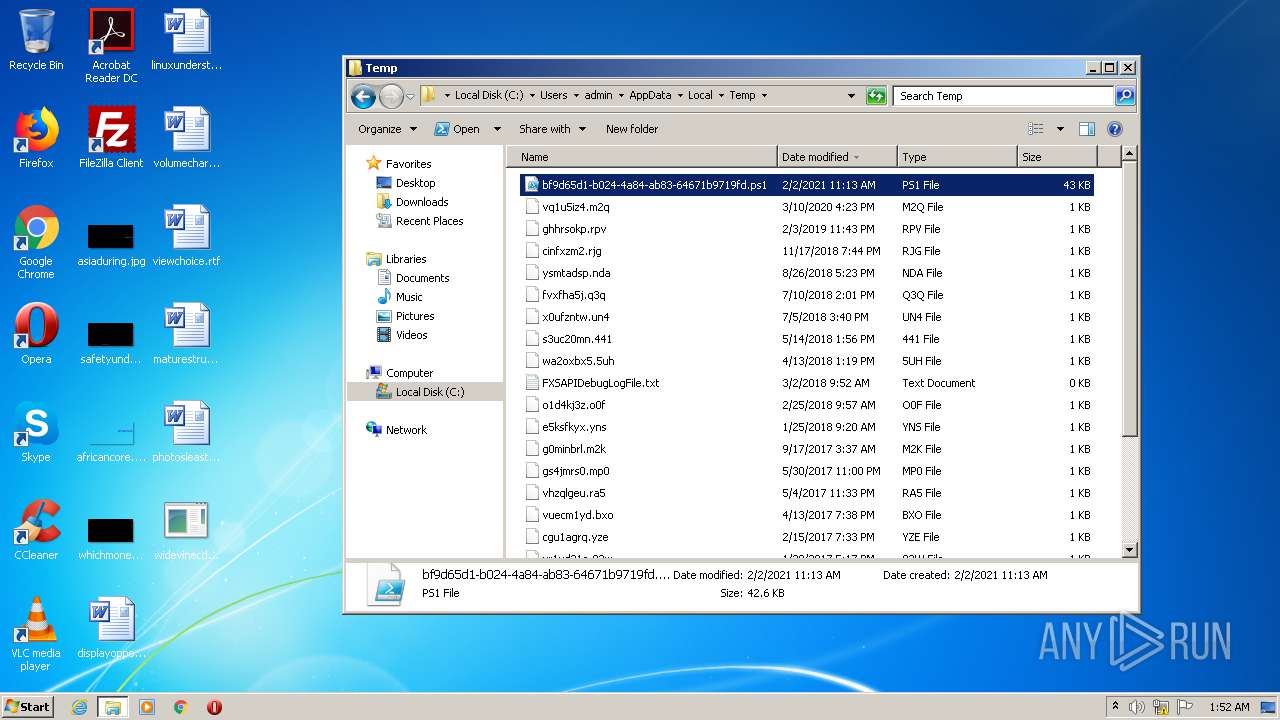
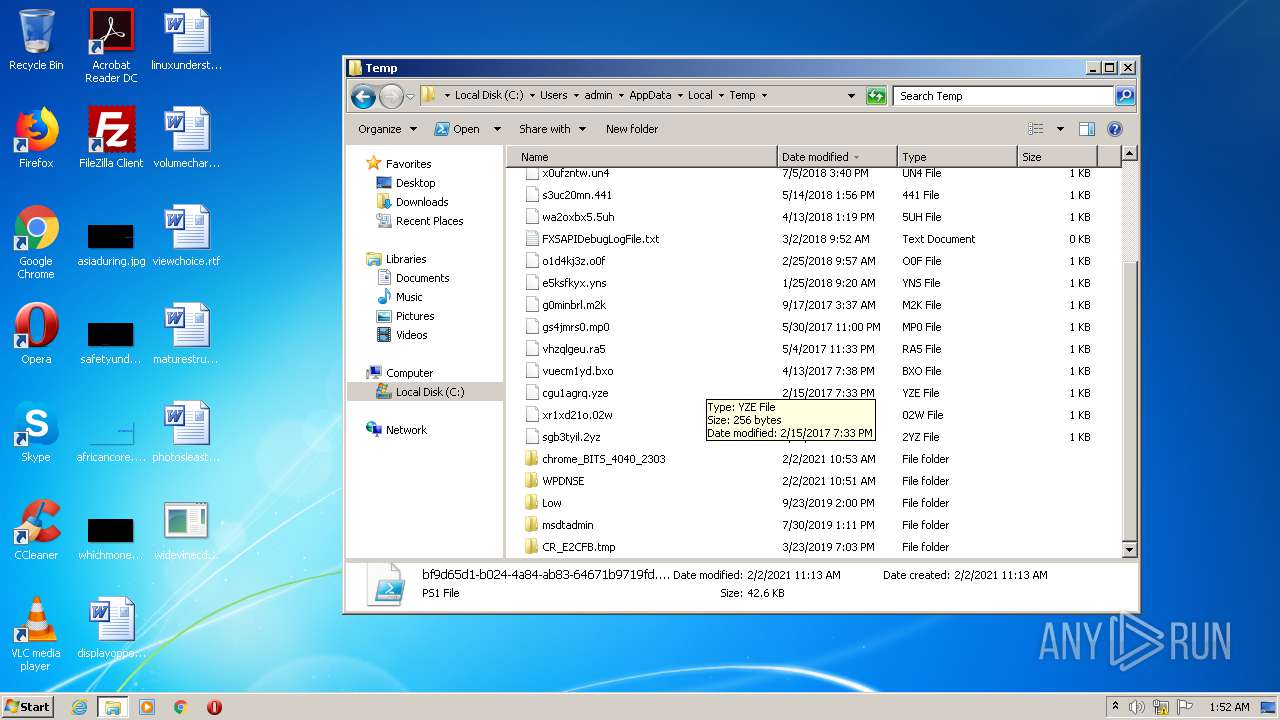
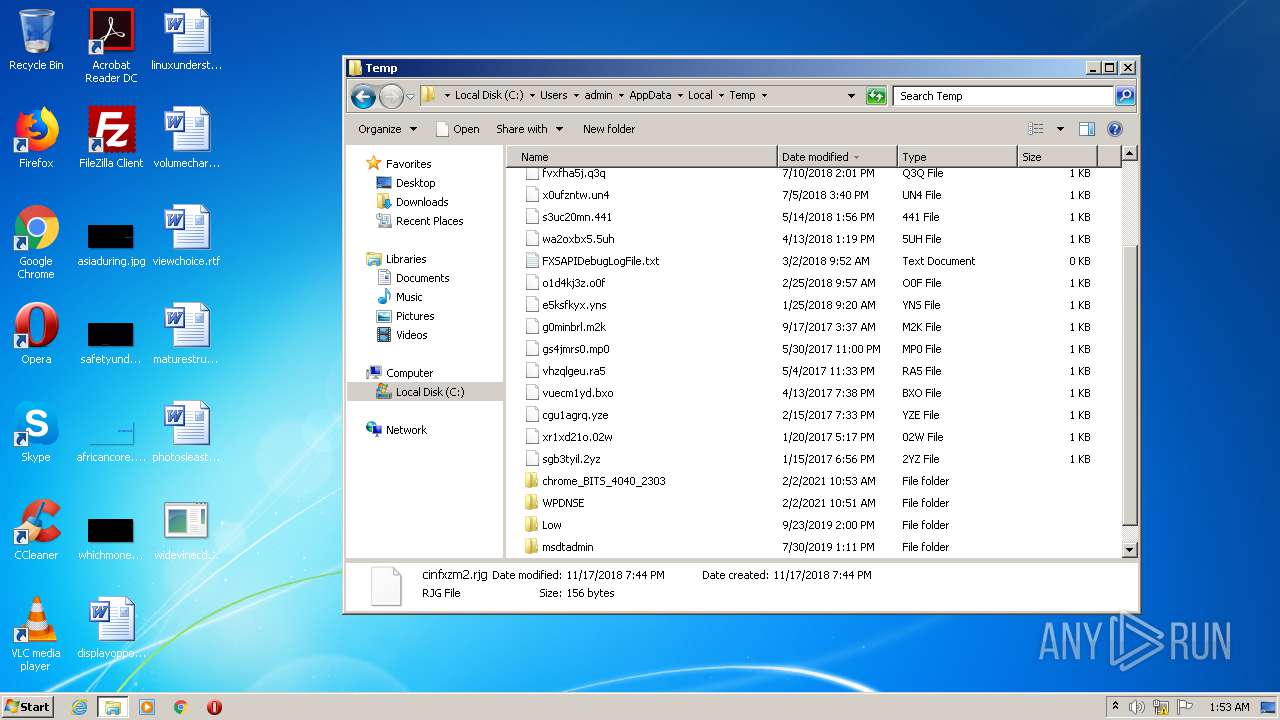
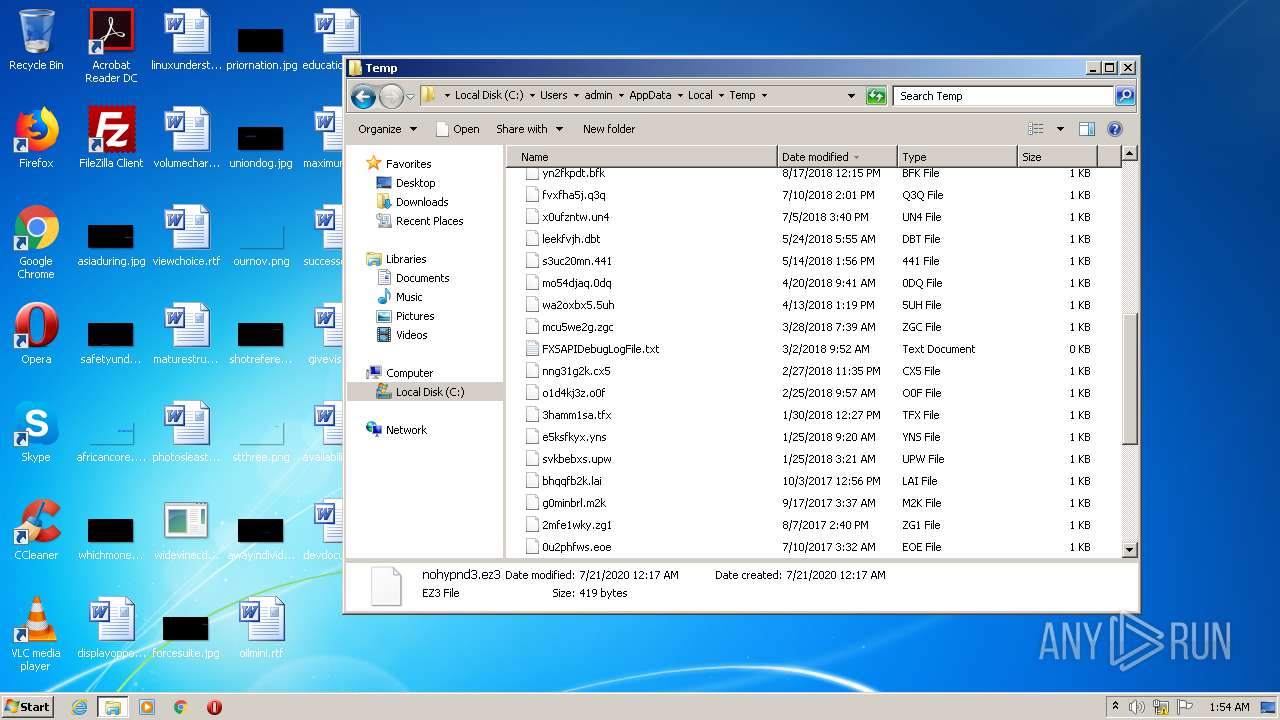
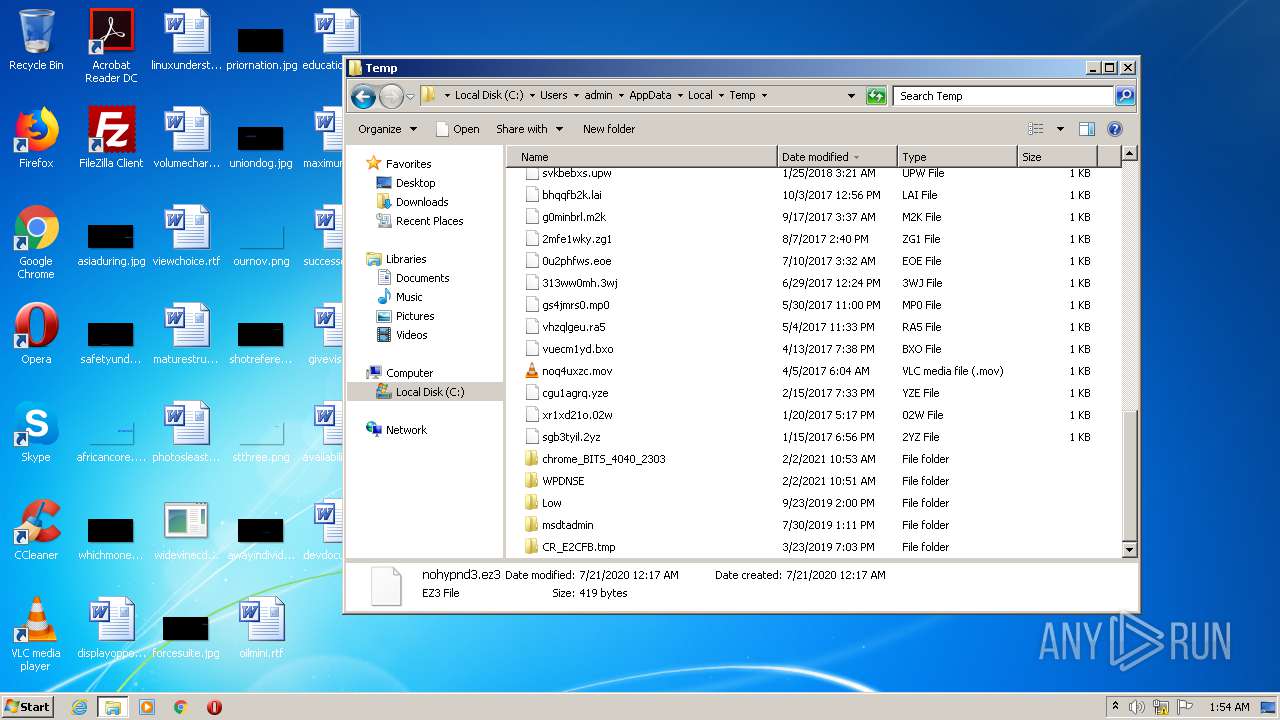
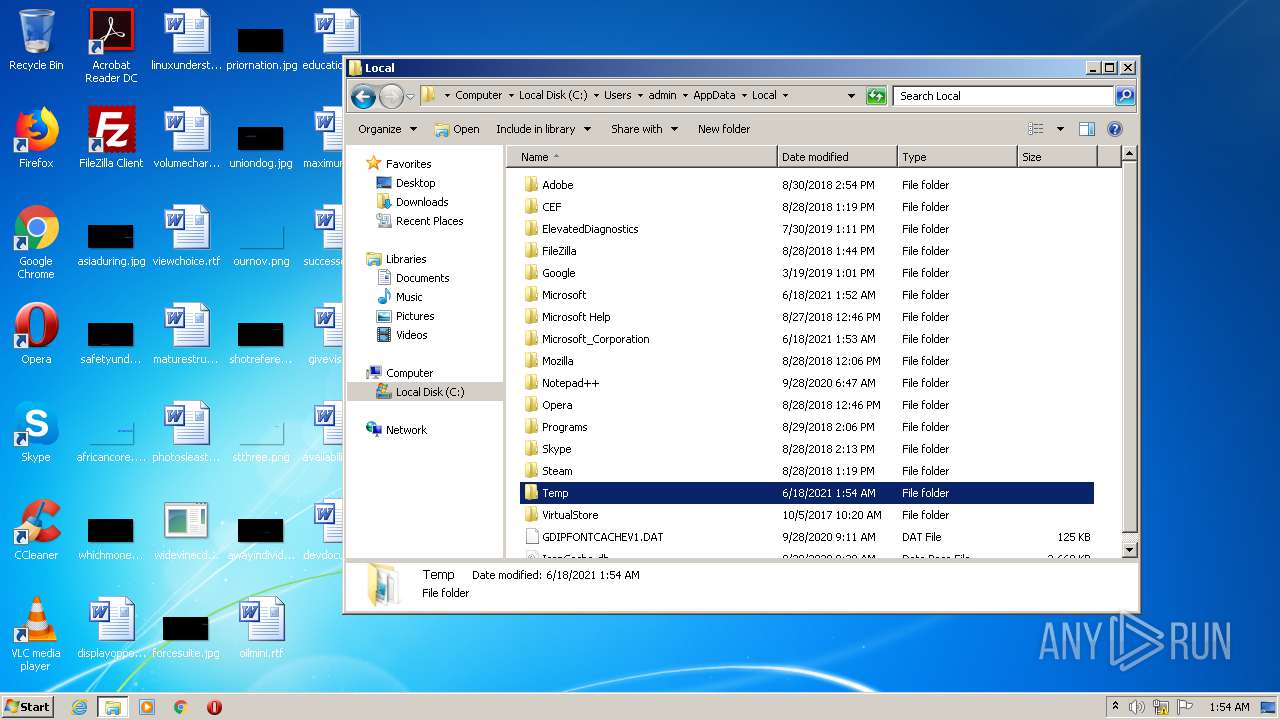
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft_Corporation\powershell_ise.exe_StrongName_lw2v2vm3wmtzzpebq33gybmeoxukb04w\1.0.0.0\m_jwd9yl.newcfg | — | |
MD5:— | SHA256:— | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6X4PMKCY348F6PWJ15KP.temp | — | |
MD5:— | SHA256:— | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF161d12.TMP | binary | |
MD5:16BD098831F20CBD5DE206703F60E498 | SHA256:65C997DE988ABFB0EFF06B2C6027D8DB64ECDF5500139FA84D310FBDDFE4E19E | |||
| 2976 | powershell.exe | C:\Users\admin\Desktop\uniondog.jpg | image | |
MD5:201E721D9C31FD298648056E3E4869F4 | SHA256:C739C819A627E11FAF33883B190ED546A7E0F4AF141079E580E90F4823777B01 | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16BD098831F20CBD5DE206703F60E498 | SHA256:65C997DE988ABFB0EFF06B2C6027D8DB64ECDF5500139FA84D310FBDDFE4E19E | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\forcesuite.jpg.lnk | lnk | |
MD5:677A9CCCD576C9255744EC9CFED7ECB2 | SHA256:5B13AD66C140DDA51979FBF1DE6F49D7A36BD7E38C635F49C3DC6694FFB10869 | |||
| 2976 | powershell.exe | C:\Users\admin\Desktop\priornation.jpg | image | |
MD5:1A27C8F5E432E508C30A72D9D64EF439 | SHA256:24CC4B4B5B9ADEF5ABA374B20E52DF96975FBF9FDCF5599585A18D5F08935127 | |||
| 2976 | powershell.exe | C:\Users\admin\Desktop\forcesuite.jpg | image | |
MD5:37066C50B4ADB169CCD6AF555CEA1C93 | SHA256:13DF6A4168B325E127841FBBCAAEAEA24F30DB44C7360B548438046A9122BB62 | |||
| 2976 | powershell.exe | C:\Users\admin\Desktop\educationald.rtf | text | |
MD5:A9F7C3C464901A85CEE29167FC2ECD5D | SHA256:D6823526CE35C87A7FE03853806055A238746645654BDAA96CFCBD9A39E97900 | |||
| 2976 | powershell.exe | C:\Users\admin\Desktop\shotreferences.jpg | image | |
MD5:CEFCABF55337E973B4B46FEC0612D7C9 | SHA256:C4A9DB9E357FE46AECB8EF67D635FDDE7A034AAD3ED0A26EE69251698B07D4F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report