| File name: | Covid-19 Check.exe |
| Full analysis: | https://app.any.run/tasks/a2f8fcb5-5df4-4fd5-9ebd-fd7a406abfec |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2020, 16:22:29 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 1101FCFE2845B3189C13F80CE75FF562 |
| SHA1: | CFF3B29ADC457759EF0FCF781DEEDBB8CA34A7B9 |
| SHA256: | 7871ACFC6F5E839CB764FD120EE9CEC7585EAD0D4F4E5B1C526BAA6A2B936D29 |
| SSDEEP: | 3072:i4lRkAehGfzmuqTPryFArGRrwEQI9yVi5UfPl:i4lRkAehaKuqT+FAatwN5Vi5UV |
MALICIOUS
Application was dropped or rewritten from another process
- server.sfx.exe (PID: 6136)
- server.exe (PID: 5940)
Actions looks like stealing of personal data
- server.sfx.exe (PID: 6136)
- Covid-19 Check.exe (PID: 5136)
SUSPICIOUS
Executable content was dropped or overwritten
- Covid-19 Check.exe (PID: 5136)
- server.sfx.exe (PID: 6136)
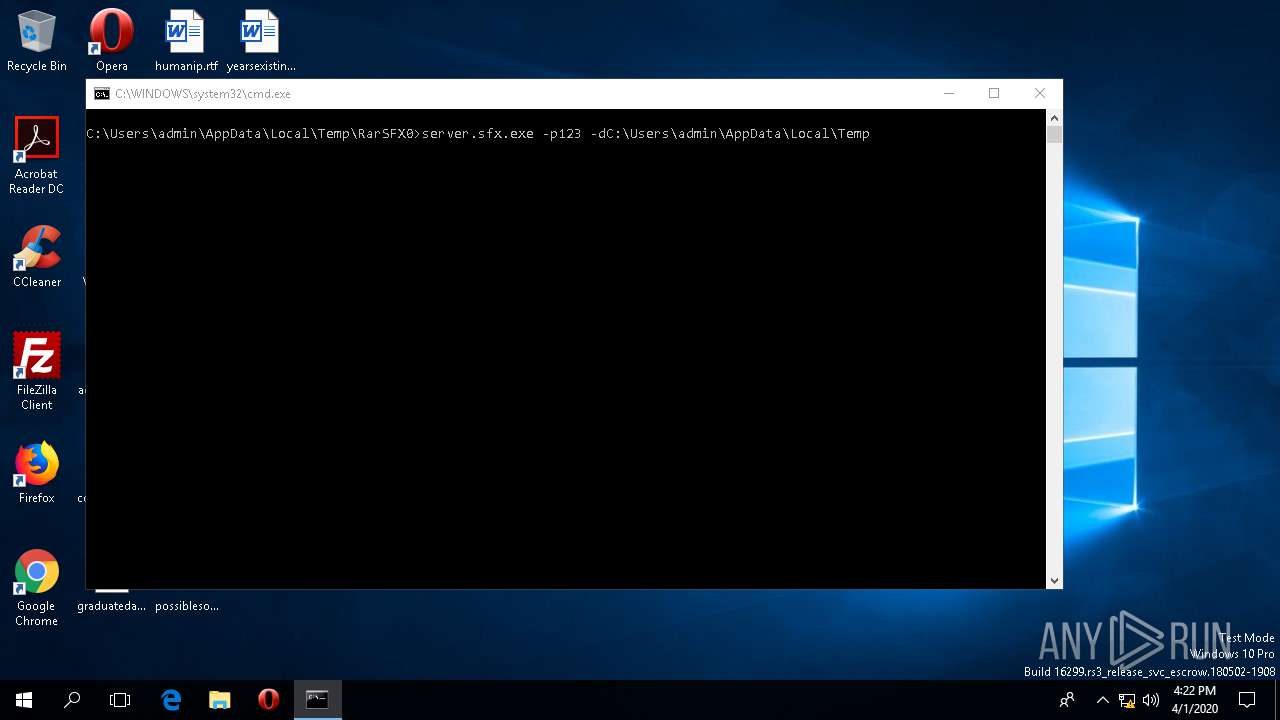
Starts CMD.EXE for commands execution
- Covid-19 Check.exe (PID: 5136)
Reads the machine GUID from the registry
- server.exe (PID: 5940)
- WerFault.exe (PID: 5688)
- backgroundTaskHost.exe (PID: 4336)
- SpeechRuntime.exe (PID: 5624)
Reads CPU info
- WerFault.exe (PID: 5688)
Creates files in the program directory
- WerFault.exe (PID: 5688)
Reads Environment values
- WerFault.exe (PID: 5688)
Executed via COM
- ApplicationFrameHost.exe (PID: 1668)
- SystemSettings.exe (PID: 2380)
- RuntimeBroker.exe (PID: 1724)
- backgroundTaskHost.exe (PID: 4336)
- SpeechRuntime.exe (PID: 5624)
Checks supported languages
- SystemSettings.exe (PID: 2380)
- backgroundTaskHost.exe (PID: 4336)
Creates files in the user directory
- SystemSettings.exe (PID: 2380)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:05:28 18:04:29+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 72192 |
| InitializedDataSize: | 80384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb480 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-May-2011 16:04:29 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-May-2011 16:04:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011998 | 0x00011A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55849 |
.rdata | 0x00013000 | 0x00001C15 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.86387 |
.data | 0x00015000 | 0x0000FF2C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.51849 |
.CRT | 0x00025000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.213101 |
.rsrc | 0x00026000 | 0x0001162C | 0x00011800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.72938 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.24143 | 556 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.26996 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.16254 | 776 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.06352 | 380 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 1.91924 | 20 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | English - United States | RT_BITMAP |
ASKNEXTVOL | 3.42597 | 646 | Latin 1 / Western European | English - United States | RT_DIALOG |
GETPASSWORD1 | 3.33944 | 314 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
102
Monitored processes
11
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1668 | C:\WINDOWS\system32\ApplicationFrameHost.exe -Embedding | C:\WINDOWS\system32\ApplicationFrameHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Frame Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1724 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | "C:\Windows\ImmersiveControlPanel\SystemSettings.exe" -ServerName:microsoft.windows.immersivecontrolpanel | C:\Windows\ImmersiveControlPanel\SystemSettings.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Settings Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3608 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\fud.bat" " | C:\WINDOWS\SysWOW64\cmd.exe | — | Covid-19 Check.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3908 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | "C:\WINDOWS\system32\backgroundTaskHost.exe" -ServerName:CortanaUI.AppXy7vb4pc2dr3kc93kfc509b1d0arkfb2x.mca | C:\WINDOWS\system32\backgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5136 | "C:\Users\admin\Desktop\Covid-19 Check.exe" | C:\Users\admin\Desktop\Covid-19 Check.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5624 | C:\Windows\System32\Speech_OneCore\Common\SpeechRuntime.exe -Embedding | C:\Windows\System32\Speech_OneCore\Common\SpeechRuntime.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Speech Runtime Executable Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5688 | C:\WINDOWS\system32\WerFault.exe -u -p 5940 -s 904 | C:\WINDOWS\system32\WerFault.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5940 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\server.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\server.exe | server.sfx.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3762504530 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
2 136
Read events
2 047
Write events
87
Delete events
2
Modification events
| (PID) Process: | (5136) Covid-19 Check.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Users%admin%AppData%Local%Temp |
Value: C:\Users\admin\AppData\Local\Temp\RarSFX0 | |||
| (PID) Process: | (5136) Covid-19 Check.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5136) Covid-19 Check.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5136) Covid-19 Check.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5136) Covid-19 Check.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6136) server.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6136) server.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6136) server.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6136) server.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1668) ApplicationFrameHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MrtCache\C:%5CWindows%5CImmersiveControlPanel%5Cresources.pri\1d33928e47e02c6\a01460c8 |
| Operation: | write | Name: | LanguageList |
Value: _en-US;en_standard_100_US_LTR_dark_Desktop | |||
Executable files
2
Suspicious files
4
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5940 | server.exe | C:\Users\admin\Desktop\coffeesource.jpg.pdf | — | |
MD5:— | SHA256:— | |||
| 5940 | server.exe | C:\Users\admin\Desktop\kingschedule.jpg.pdf | — | |
MD5:— | SHA256:— | |||
| 5940 | server.exe | C:\Users\admin\Desktop\possiblesomeone.jpg.pdf | — | |
MD5:— | SHA256:— | |||
| 5940 | server.exe | C:\Users\admin\Desktop\mbseven.png.pdf | — | |
MD5:— | SHA256:— | |||
| 5688 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\server.exe.5940.dmp | — | |
MD5:— | SHA256:— | |||
| 5688 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WAX2D04.tmp | — | |
MD5:— | SHA256:— | |||
| 2380 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SPIQRNL0ZJYMGGBC1VUZ.temp | — | |
MD5:— | SHA256:— | |||
| 5136 | Covid-19 Check.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\fud.bat | text | |
MD5:— | SHA256:— | |||
| 5940 | server.exe | C:\Users\admin\Desktop\coffeesource.jpg.pdf.pdf | binary | |
MD5:— | SHA256:— | |||
| 5940 | server.exe | C:\Users\admin\Desktop\kingschedule.jpg.pdf.pdf | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1924 | svchost.exe | GET | 304 | 20.191.48.196:443 | https://settings-win-ppe.data.microsoft.com/settings/v2.0/Storage/StorageHealthEvaluation?os=Windows&deviceClass=Windows.Desktop&appVer=1.0.0.0 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
648 | svchost.exe | 20.191.48.196:443 | settings-win-ppe.data.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win-ppe.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |