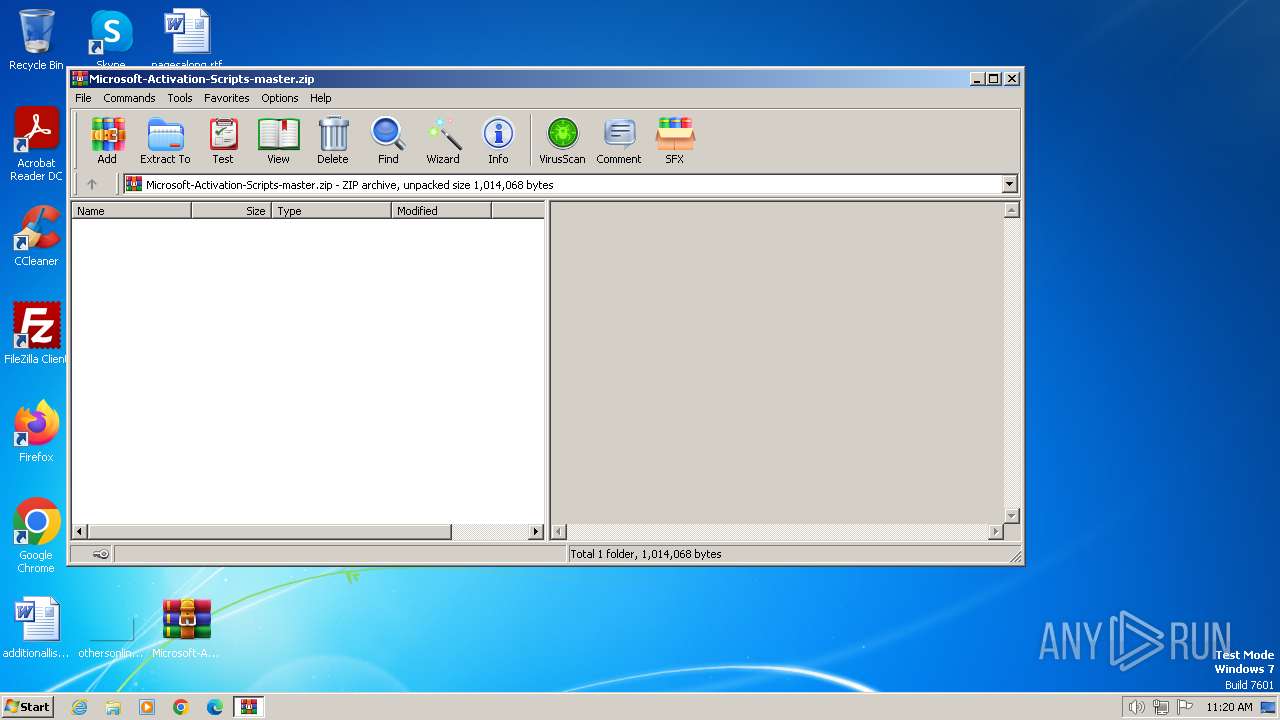
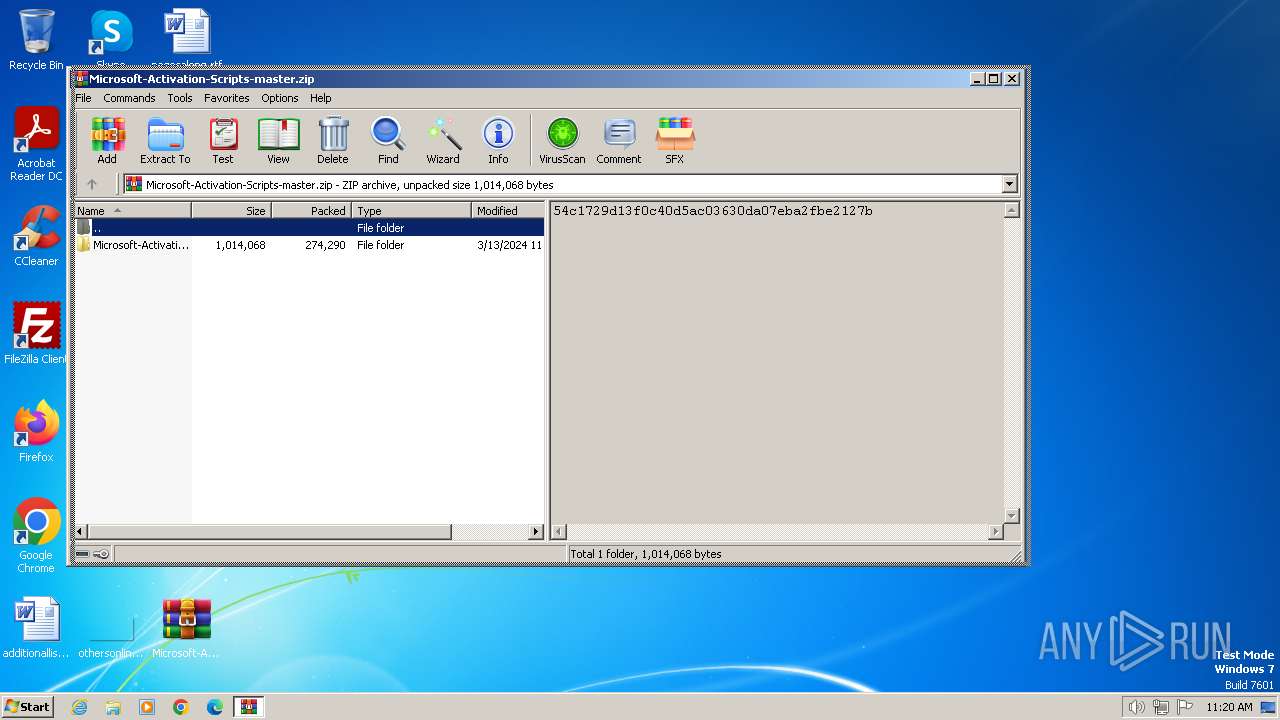
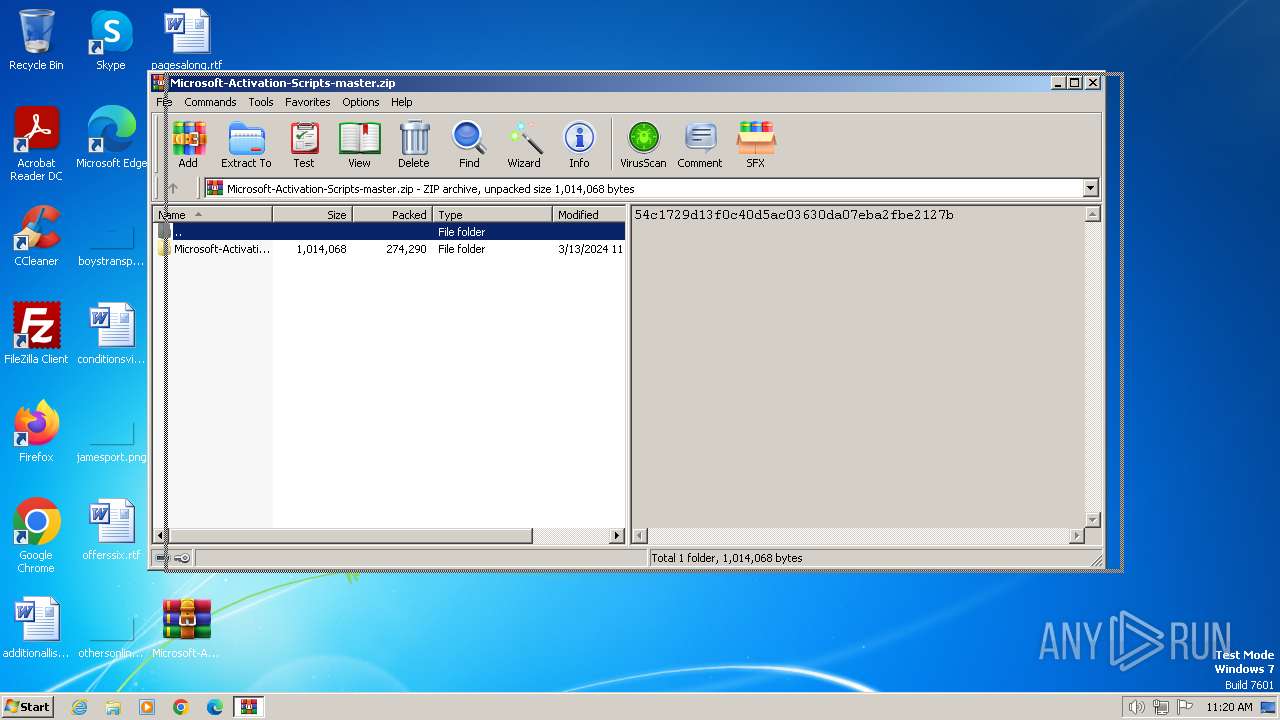
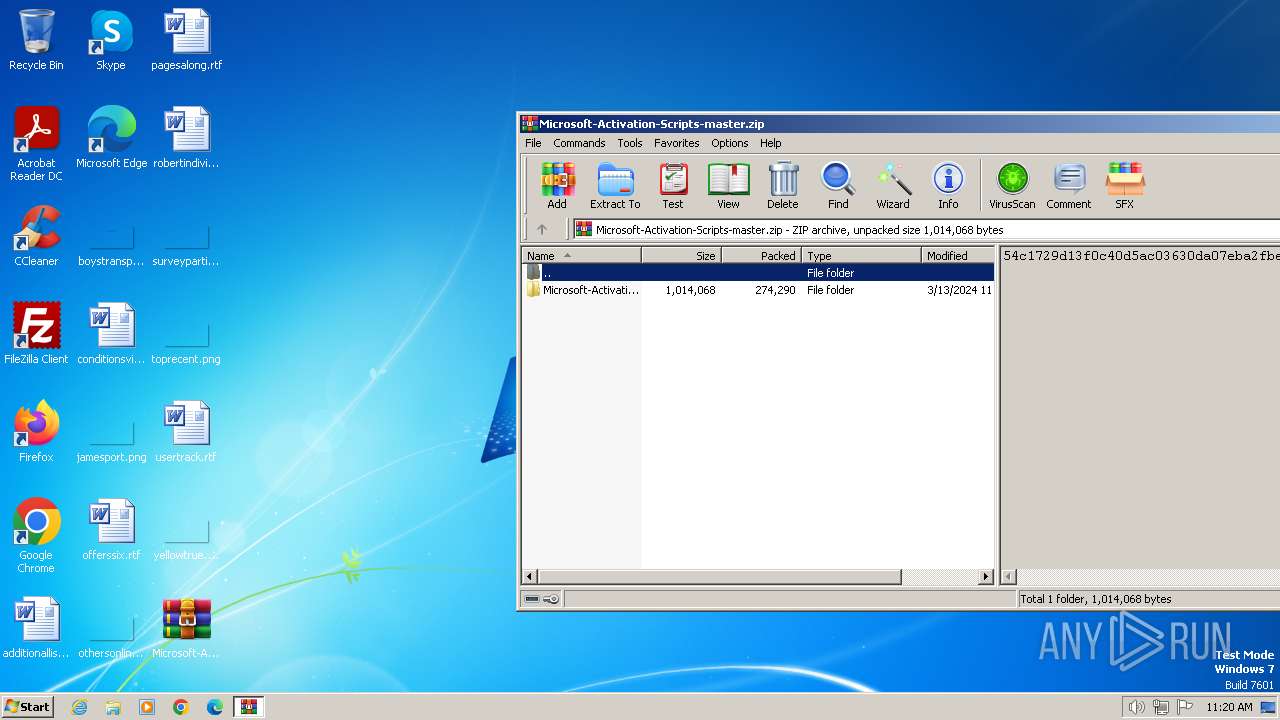
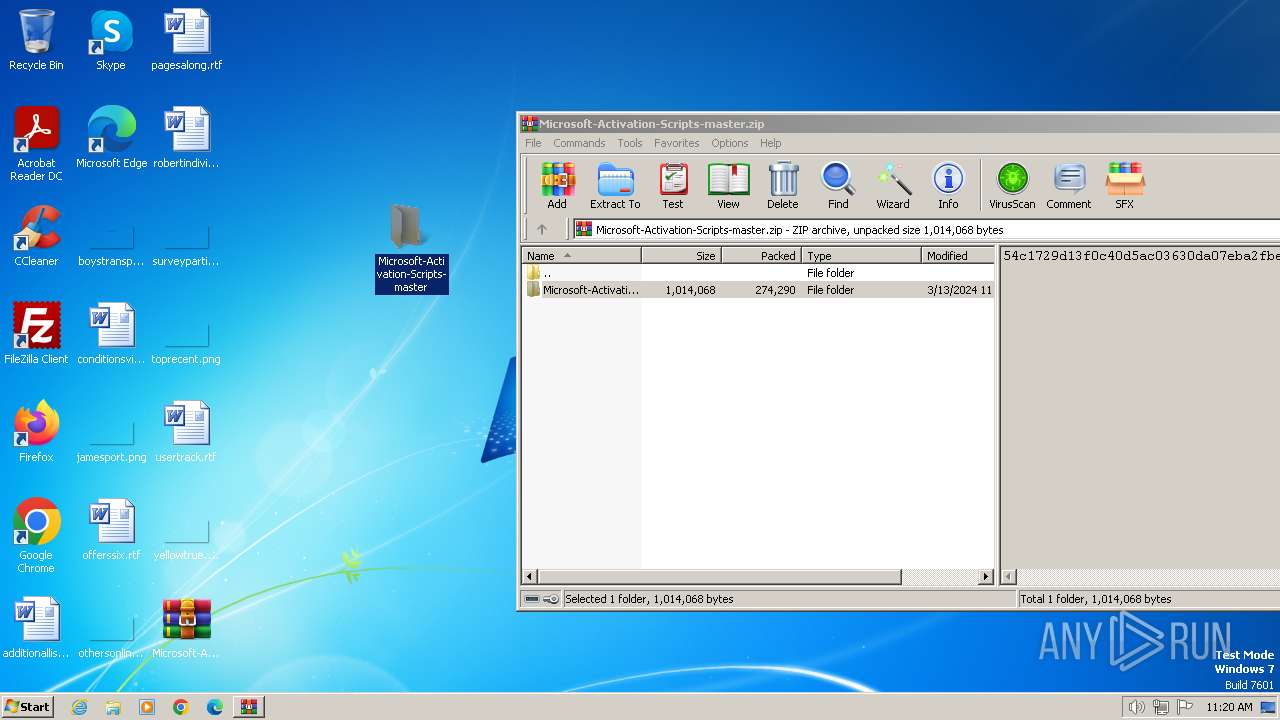
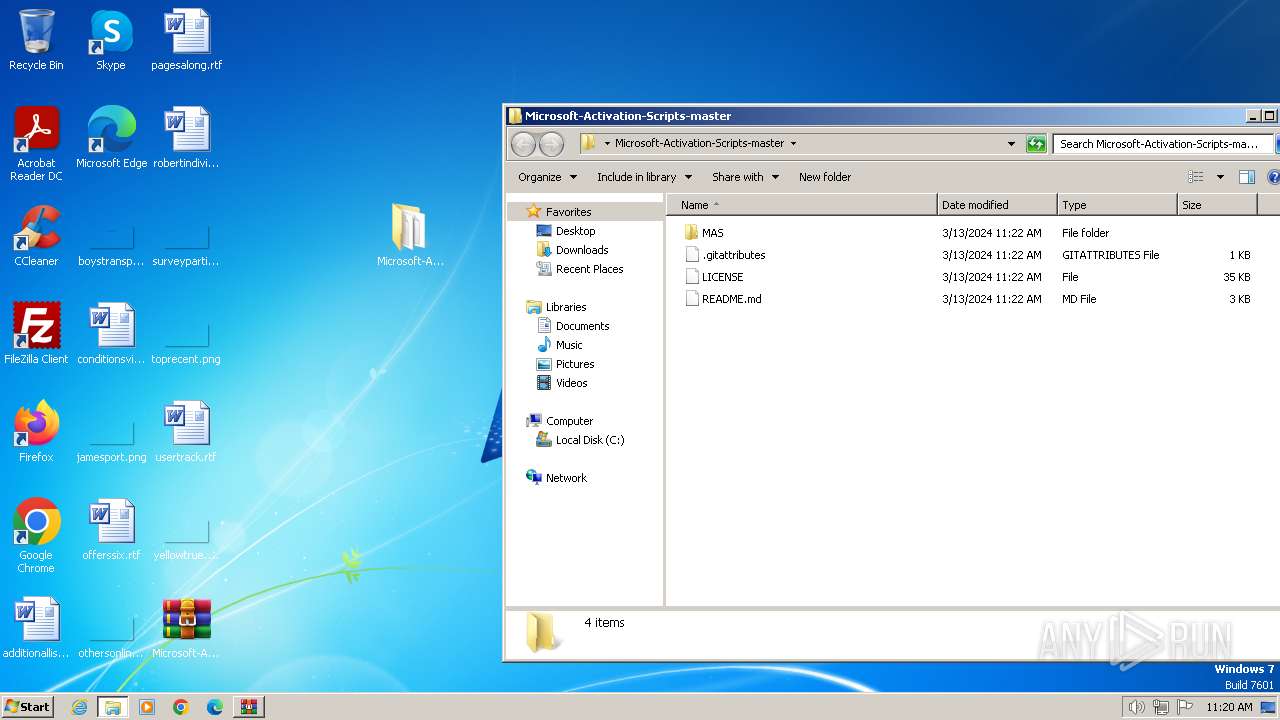
| File name: | Microsoft-Activation-Scripts-master.zip |
| Full analysis: | https://app.any.run/tasks/16763aaf-4d0b-45ef-8d15-77e210f32156 |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2024, 11:20:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | D7A74FB92A9A40D597459E86FFA12F11 |
| SHA1: | 6009E6E50EECE5B58D72976DED182E07CE221640 |
| SHA256: | 7863586F017D773B133E4CCE9814B0C8249CC629FB7265BA7C8408FA7D70A61A |
| SSDEEP: | 12288:+afOzLaRAs/u6nHcGDeXbJpFVcZiF4zYxCklr:+kOzLaRAsW6nHcGDeXbJpFVcwF4zmlr |
MALICIOUS
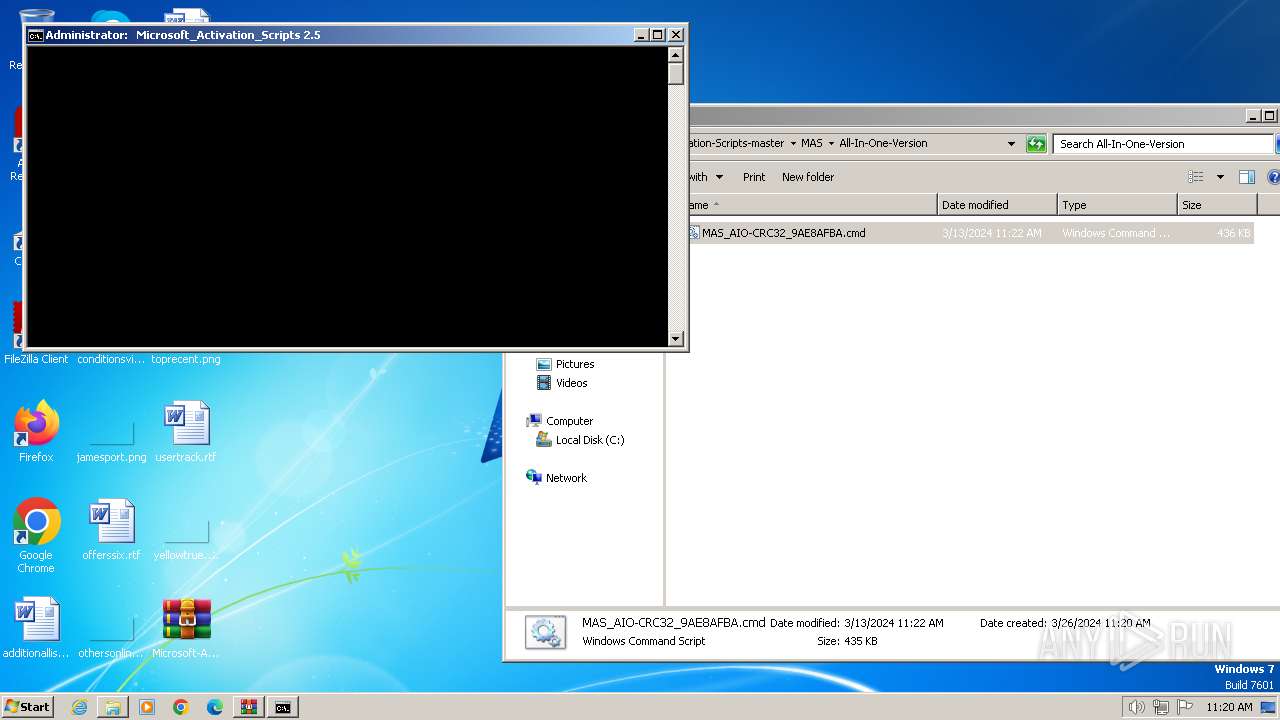
Starts NET.EXE for service management
- cmd.exe (PID: 968)
- net.exe (PID: 4060)
- net.exe (PID: 3004)
SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 1888)
- cmd.exe (PID: 968)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1888)
- powershell.exe (PID: 2744)
- cmd.exe (PID: 968)
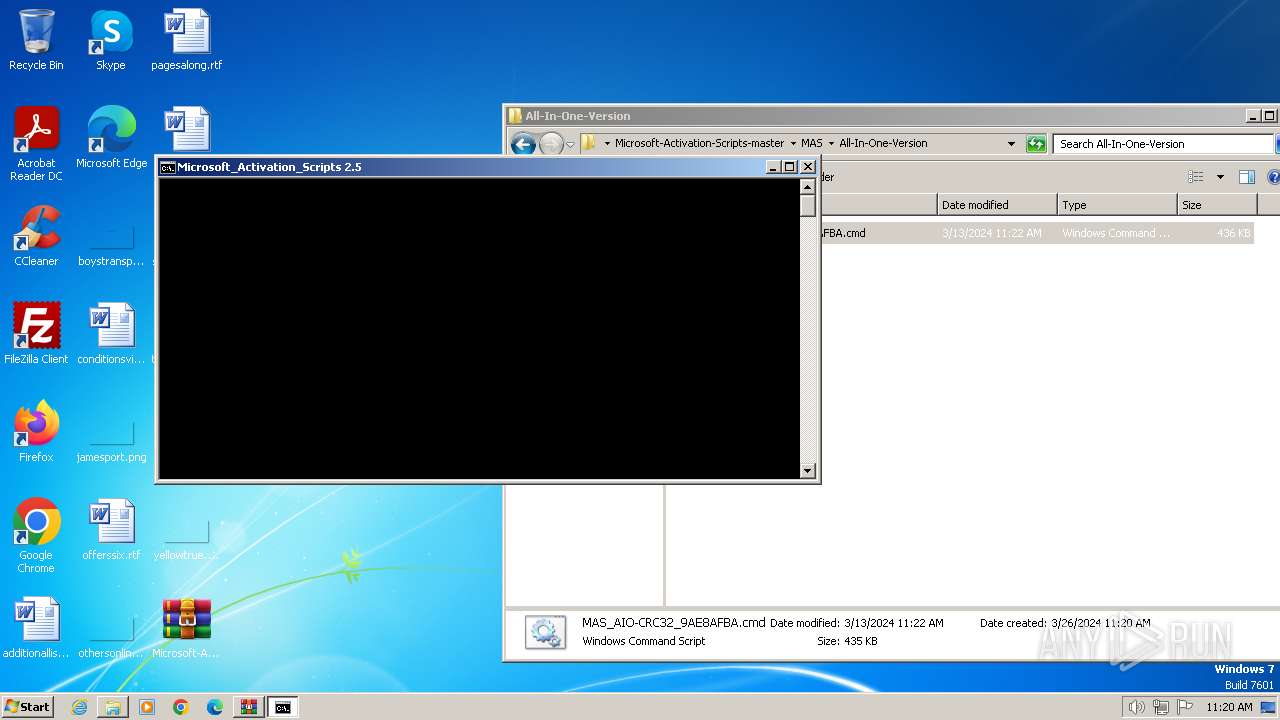
Executing commands from ".cmd" file
- cmd.exe (PID: 1888)
- powershell.exe (PID: 2744)
- cmd.exe (PID: 968)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1888)
- cmd.exe (PID: 968)
Application launched itself
- cmd.exe (PID: 1888)
- cmd.exe (PID: 968)
Reads the Internet Settings
- powershell.exe (PID: 2744)
- WMIC.exe (PID: 3784)
- WMIC.exe (PID: 3932)
- WMIC.exe (PID: 1824)
- WMIC.exe (PID: 3940)
- WMIC.exe (PID: 1740)
- WMIC.exe (PID: 2644)
- WMIC.exe (PID: 2788)
- WMIC.exe (PID: 2244)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1888)
- cmd.exe (PID: 968)
- cmd.exe (PID: 1992)
- cmd.exe (PID: 1340)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 968)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 968)
- cmd.exe (PID: 1656)
- cmd.exe (PID: 1992)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 1340)
INFO
Manual execution by a user
- cmd.exe (PID: 1888)
- wmpnscfg.exe (PID: 2032)
Checks operating system version
- cmd.exe (PID: 1888)
- cmd.exe (PID: 968)
Checks supported languages
- mode.com (PID: 2748)
- mode.com (PID: 3596)
- wmpnscfg.exe (PID: 2032)
- mode.com (PID: 3548)
- mode.com (PID: 2448)
Reads the computer name
- wmpnscfg.exe (PID: 2032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:03:13 04:22:44 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
Total processes
134
Monitored processes
88
Malicious processes
3
Suspicious processes
0
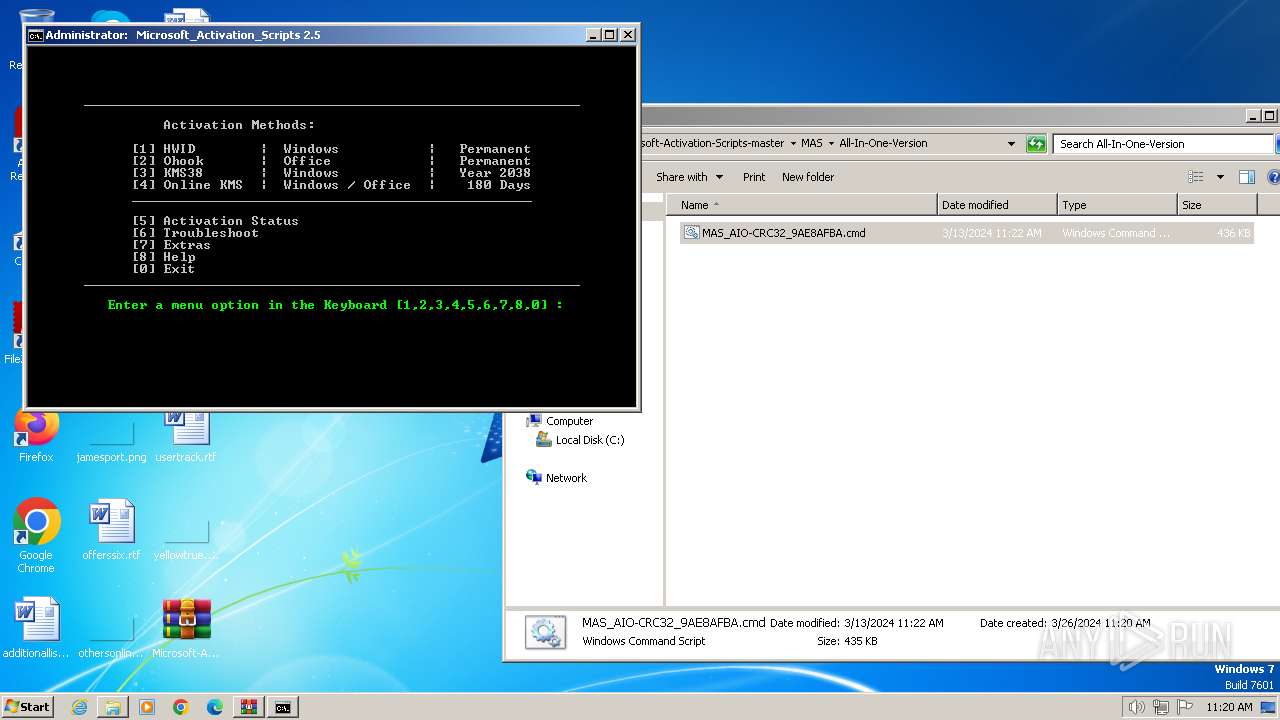
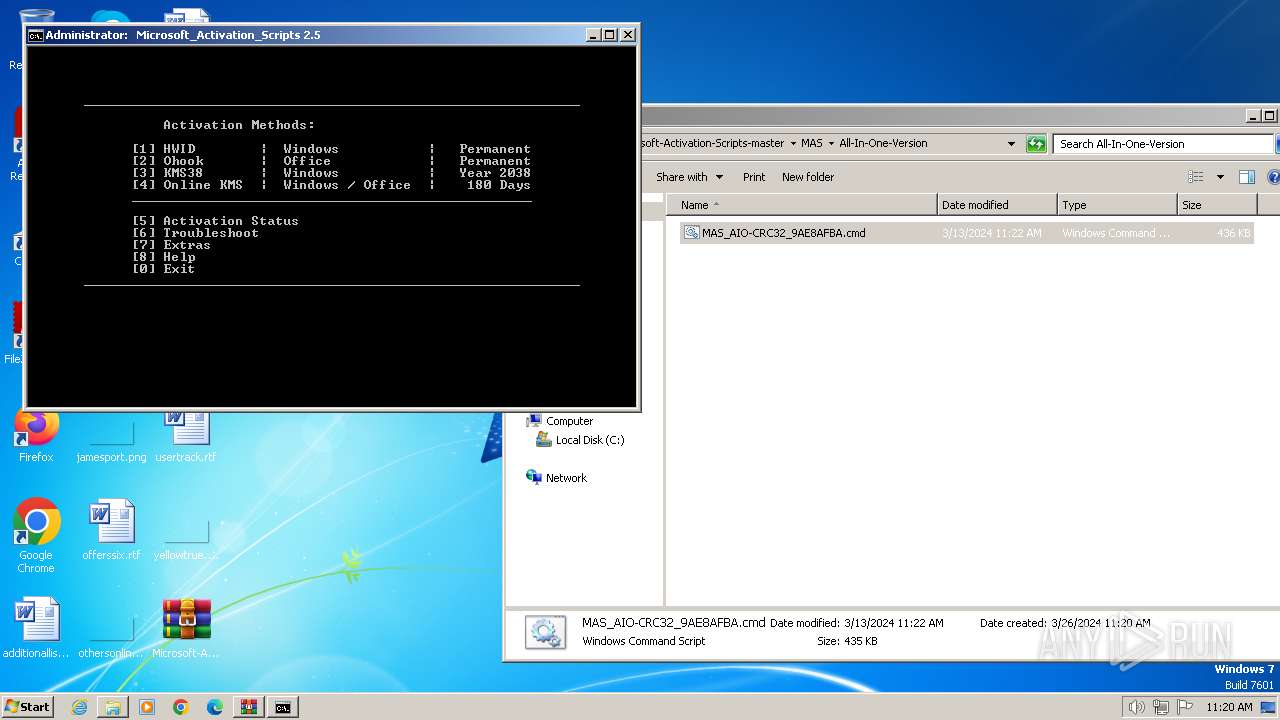
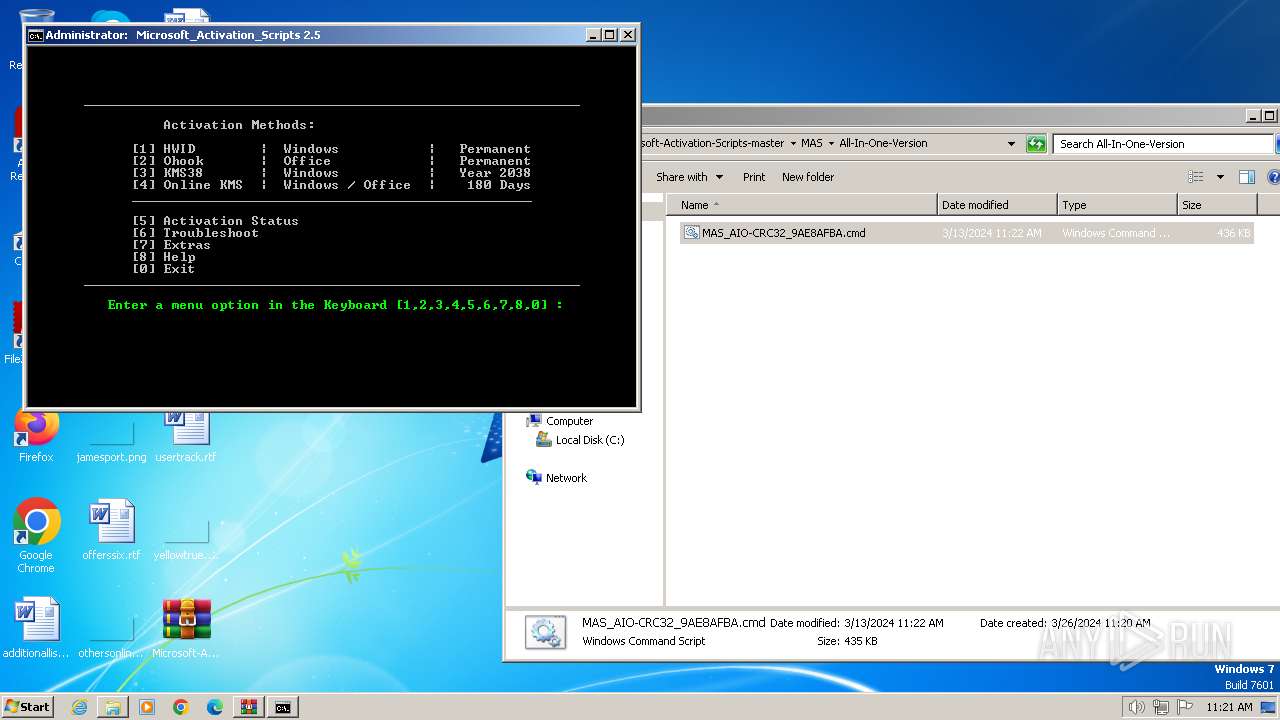
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | C:\Windows\system32\cmd.exe /S /D /c" echo "-el" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 712 | cmd /c exit /b 0 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 784 | C:\Windows\system32\cmd.exe /c reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /v Desktop | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 844 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_AIO-CRC32_9AE8AFBA.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | find "127.69.2.5" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | findstr /i ID | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "C:\Windows\System32\cmd.exe" /c ""C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\All-In-One-Version\MAS_AIO-CRC32_9AE8AFBA.cmd" -el " | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1036 | find /i "/" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 433
Read events
18 414
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master.zip | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
1
Text files
16
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
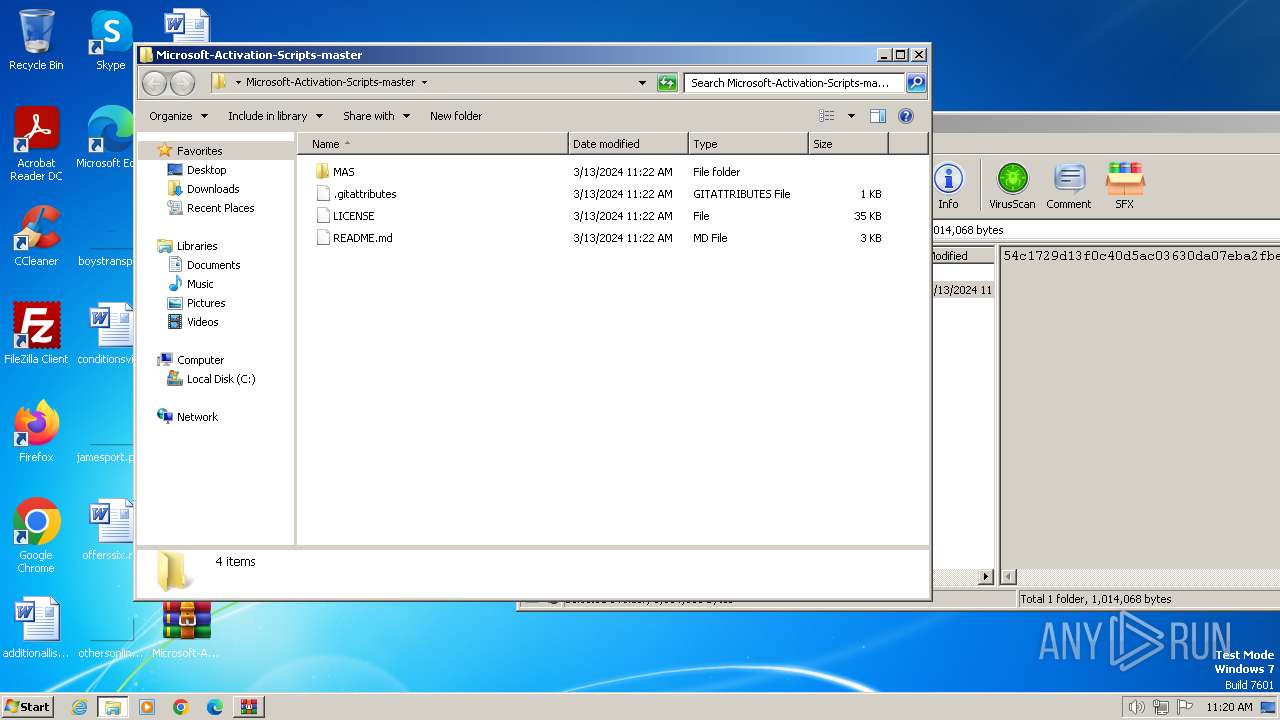
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\.gitattributes | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\LICENSE | text | |
MD5:— | SHA256:— | |||
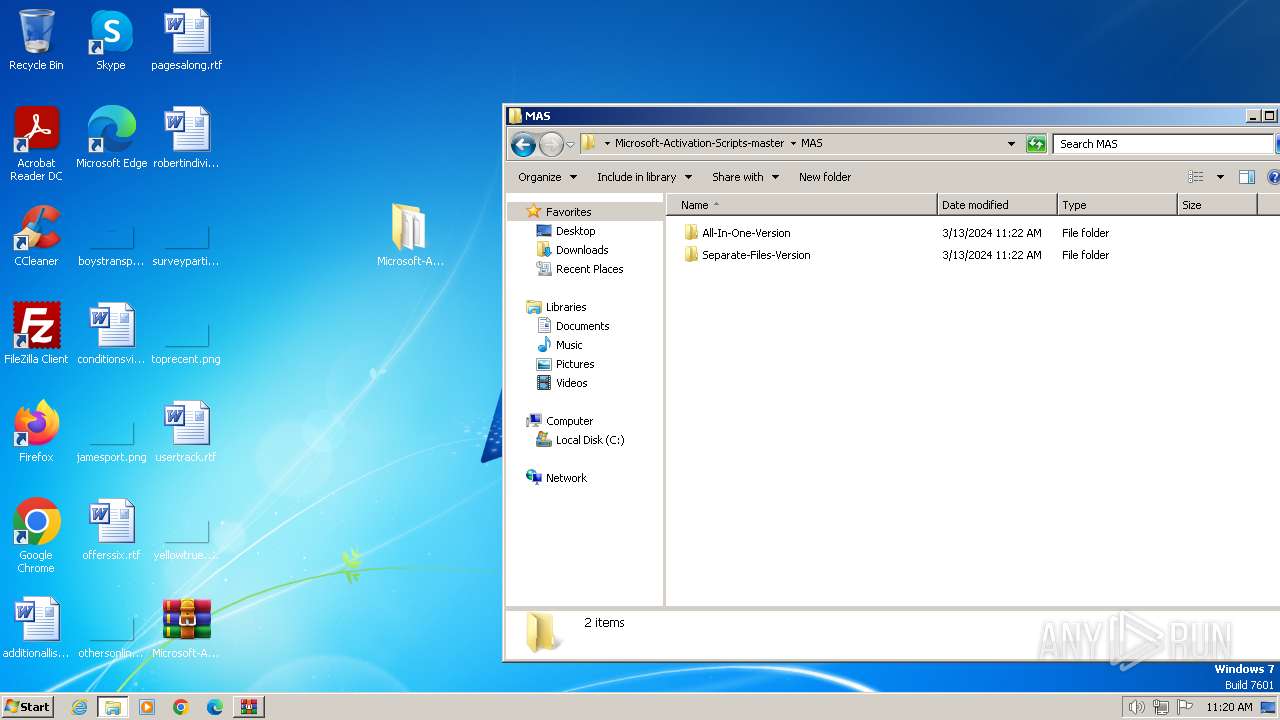
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\All-In-One-Version\MAS_AIO-CRC32_9AE8AFBA.cmd | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\HWID_Activation.cmd | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\KMS38_Activation.cmd | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\Ohook_Activation_AIO.cmd | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\Online_KMS_Activation.cmd | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\ReadMe.txt | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Change_Edition.cmd | text | |
MD5:— | SHA256:— | |||
| 3956 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3956.1042\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Check-Activation-Status-vbs.cmd | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
updatecheck.massgrave.dev |
| unknown |