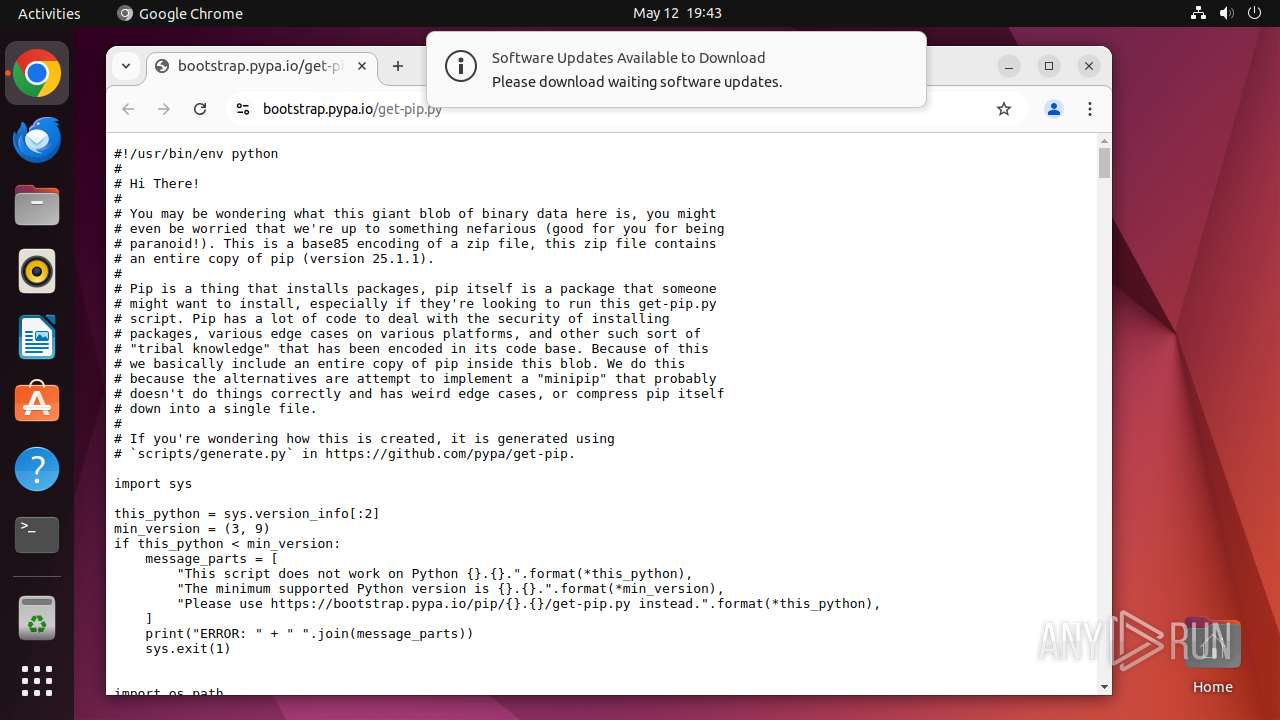
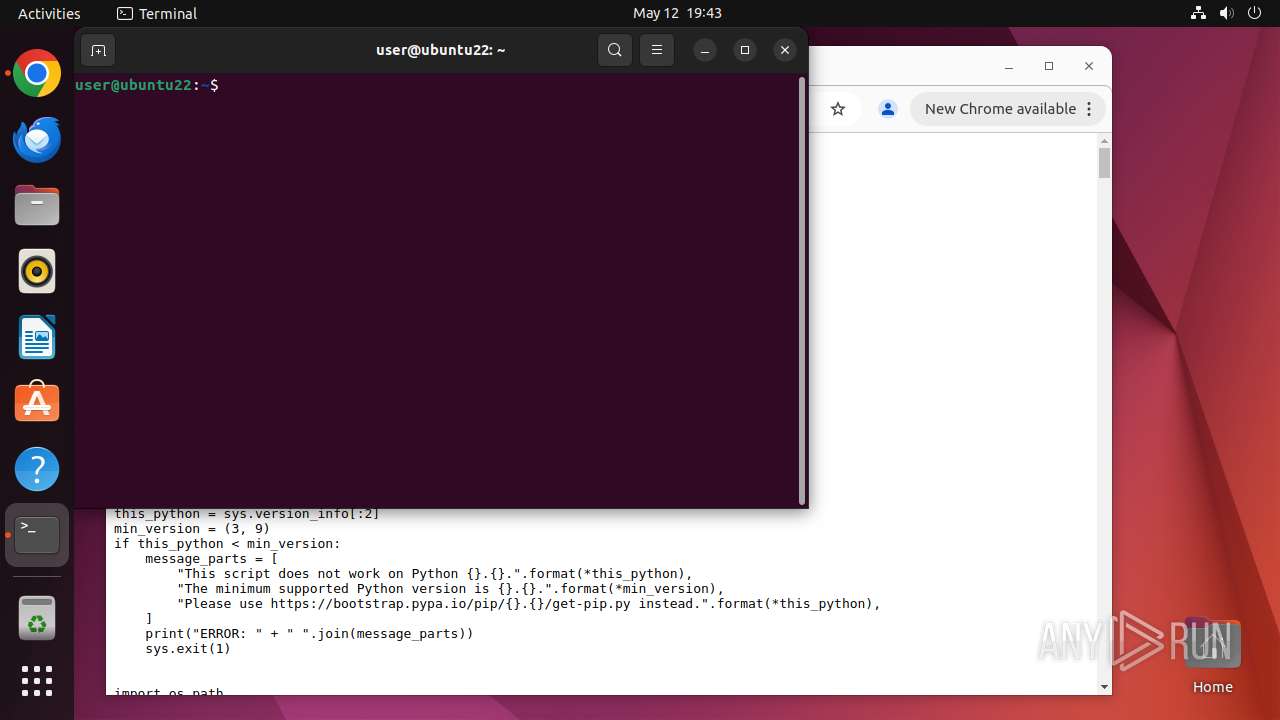
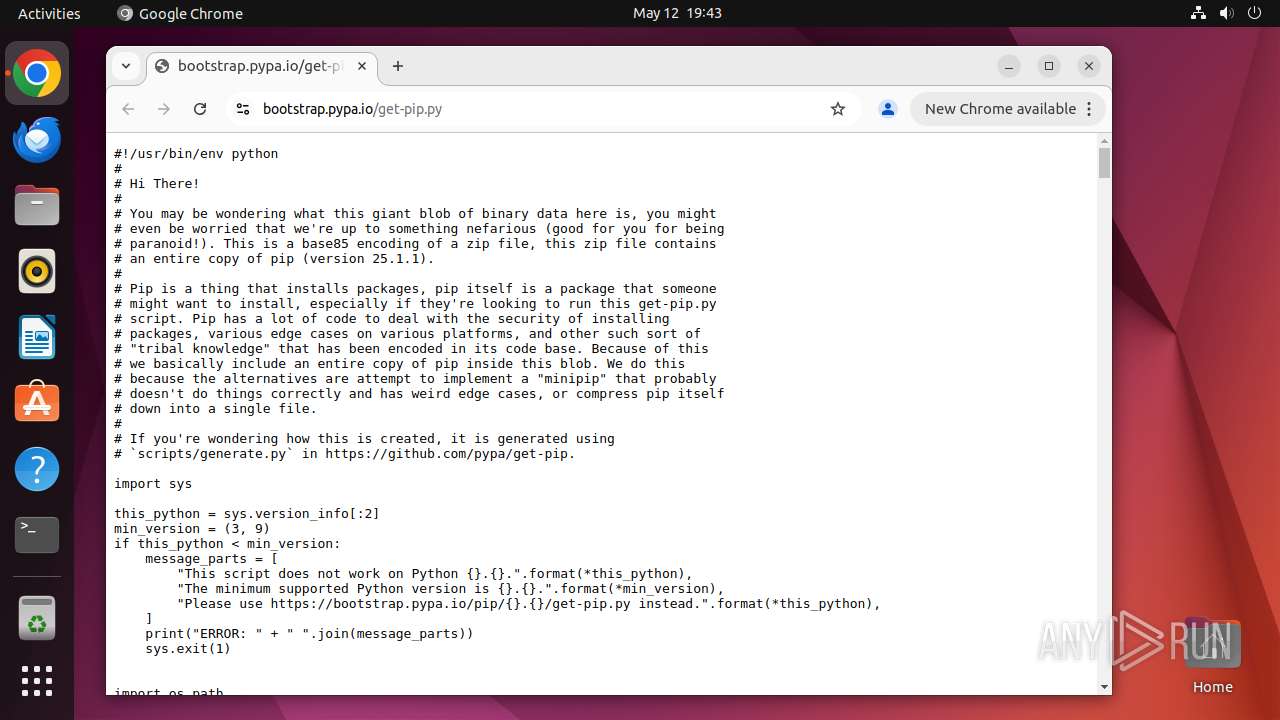
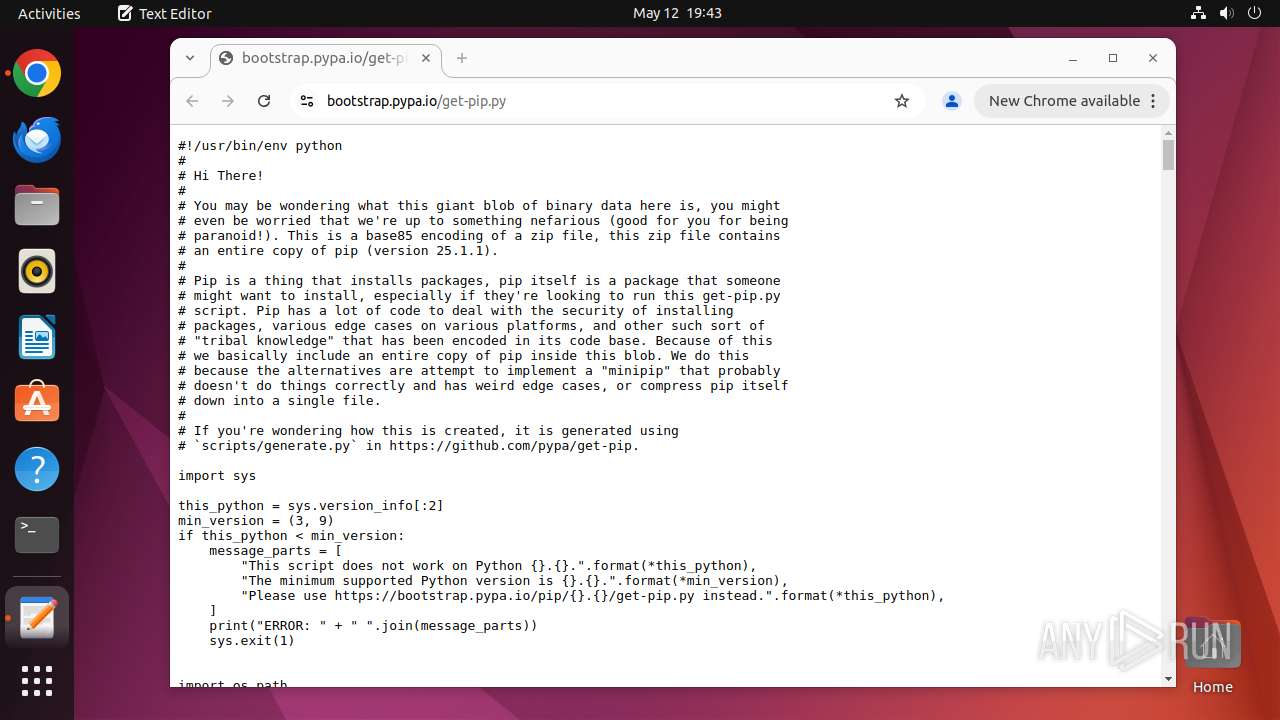
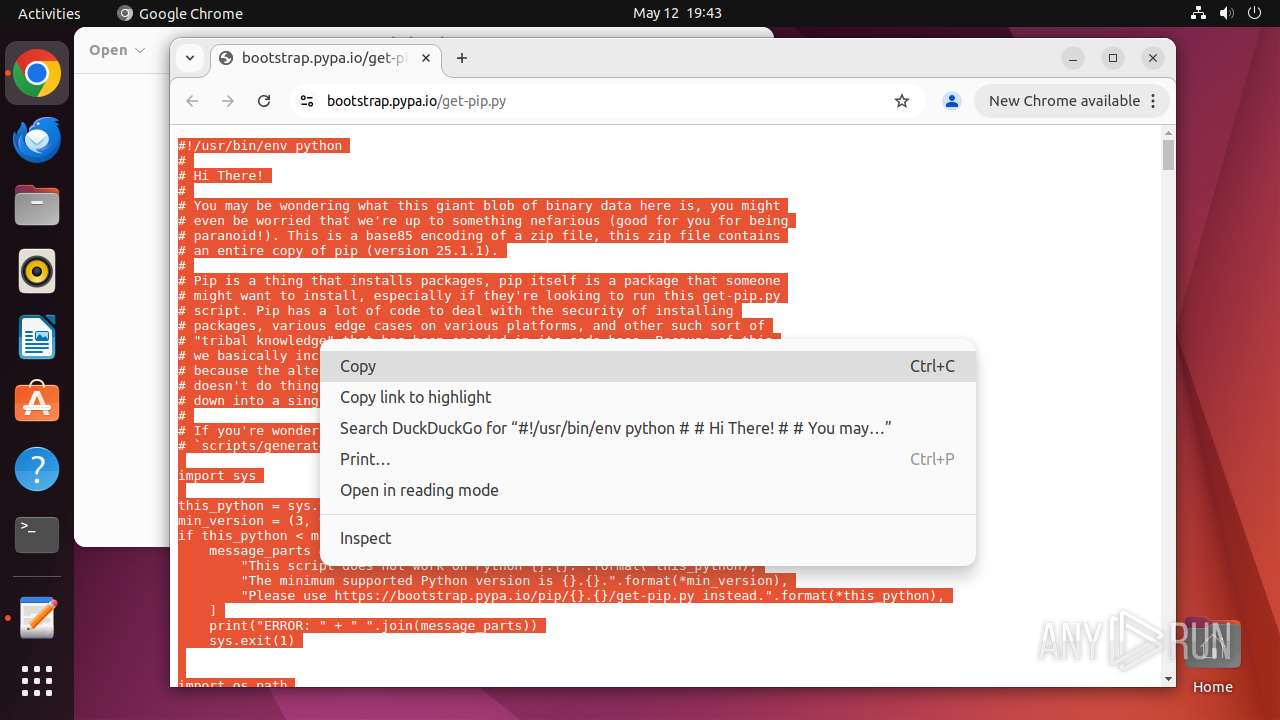
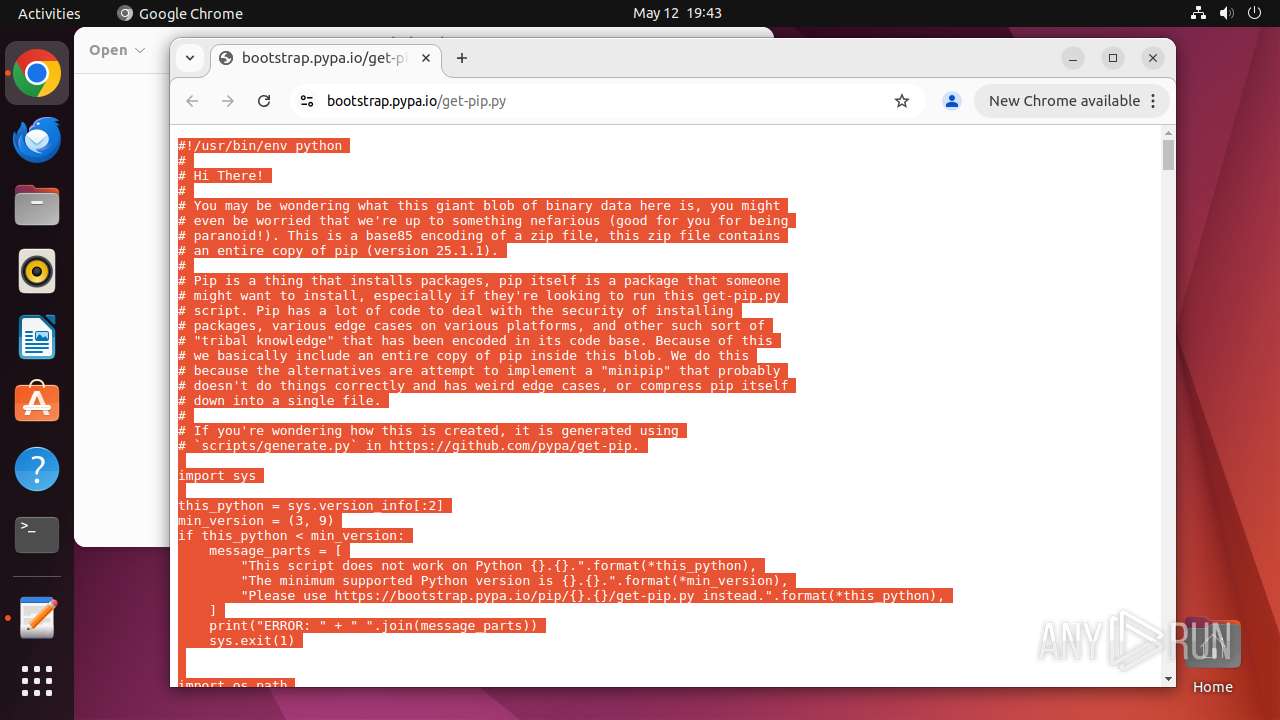
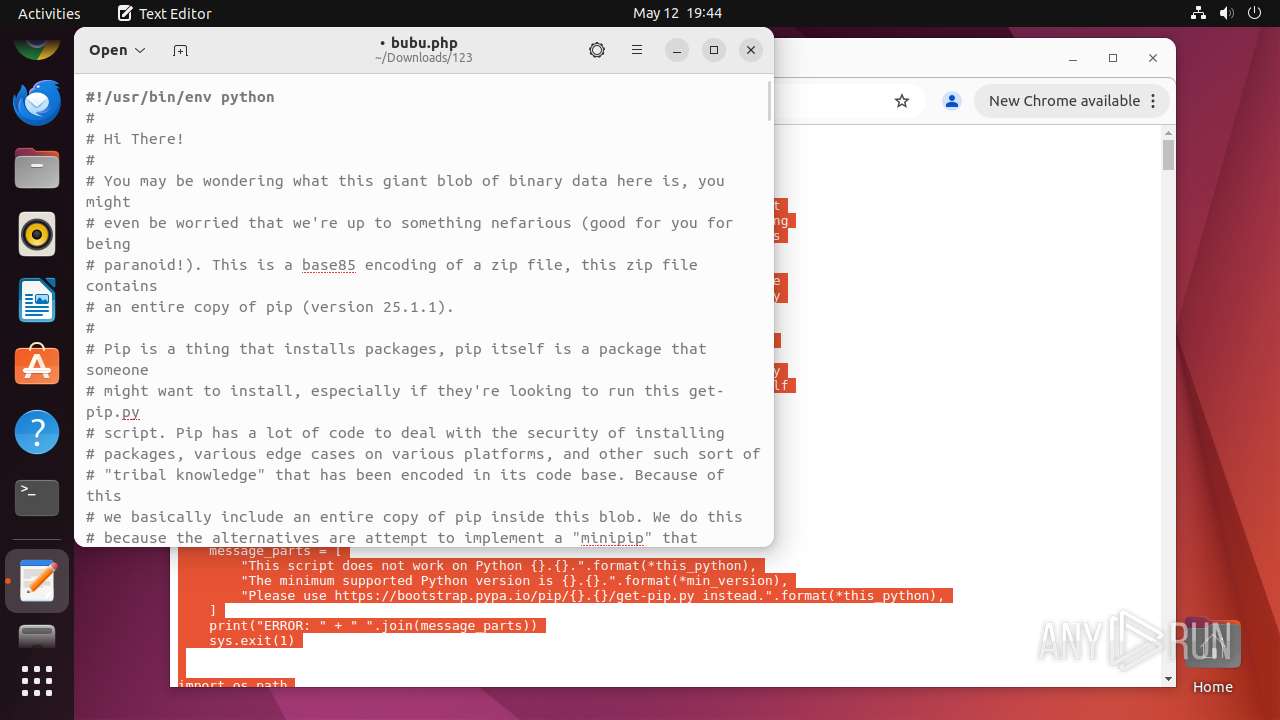
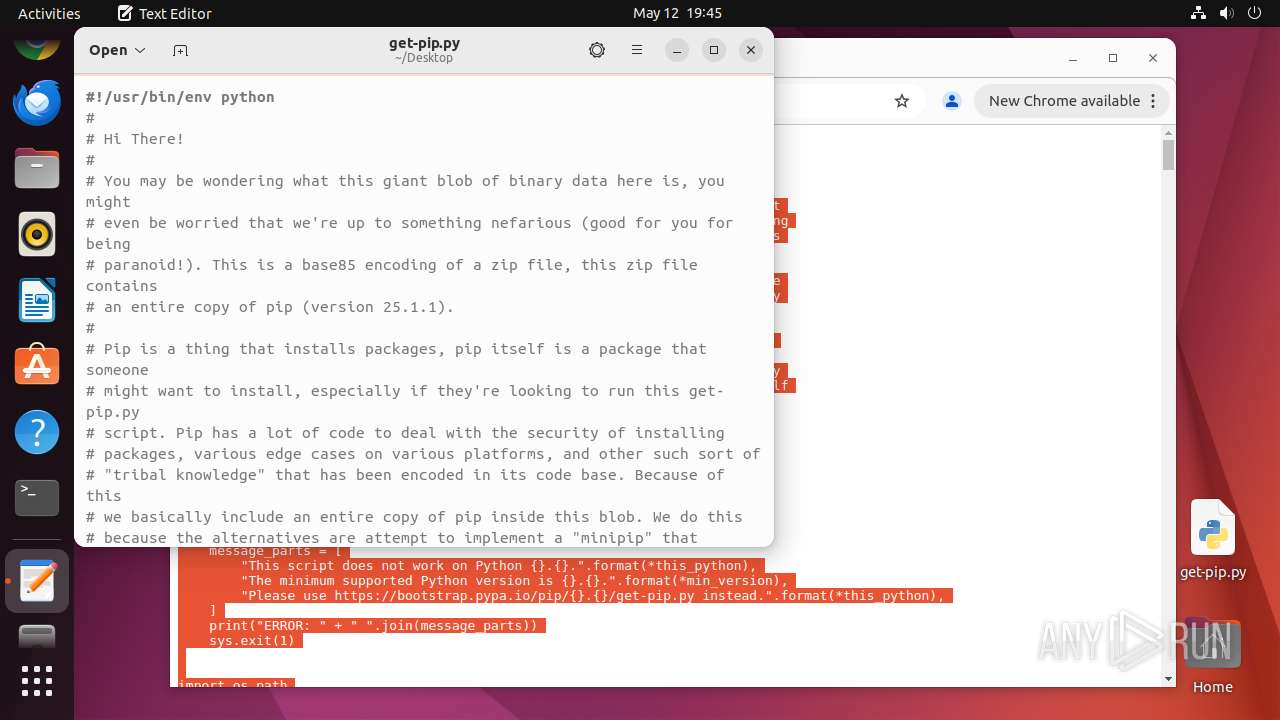
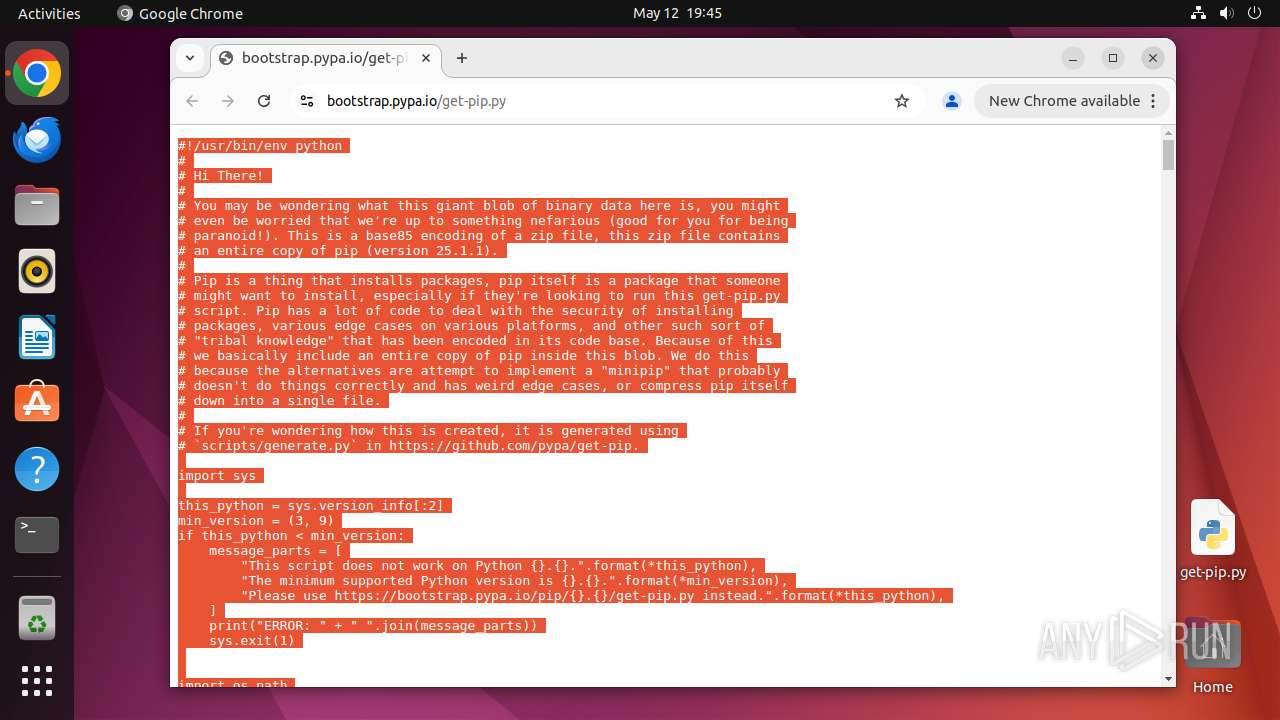
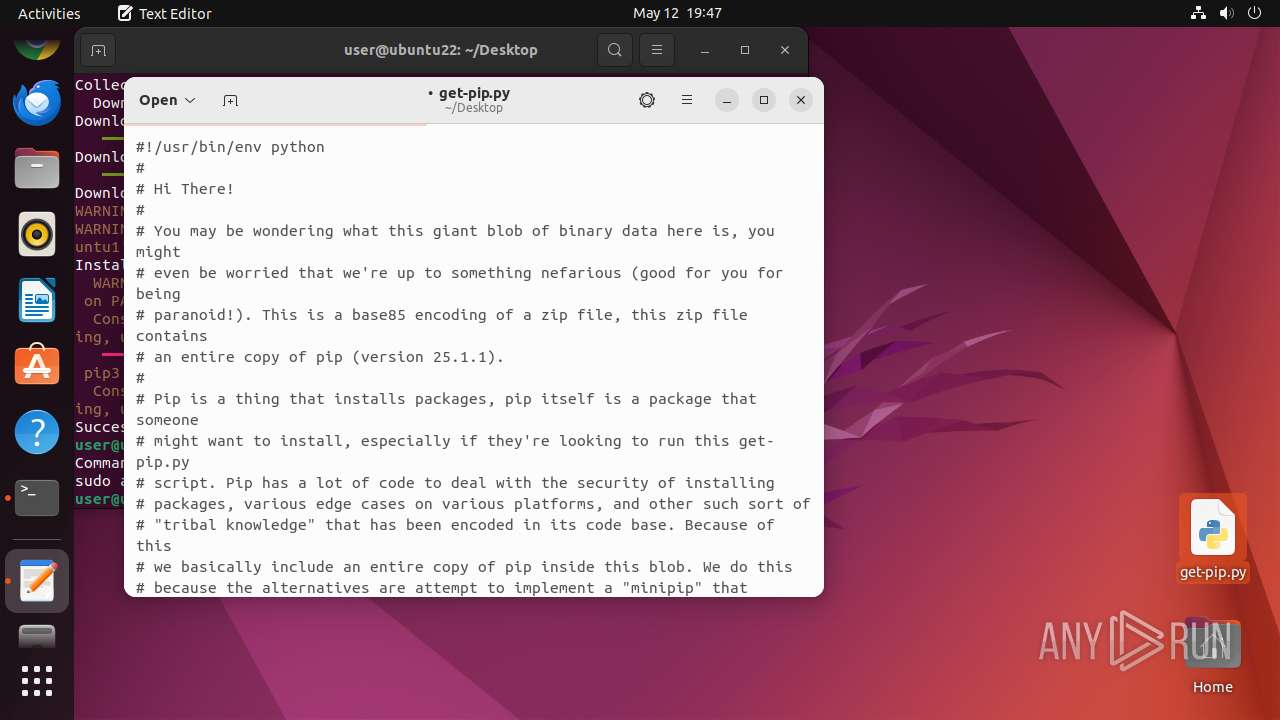
| URL: | https://bootstrap.pypa.io/get-pip.py |
| Full analysis: | https://app.any.run/tasks/9601d30b-8f29-4d37-8f54-db628a22cb11 |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 18:43:12 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | 3258A9138C93E3E173DCA6E742537F4F |
| SHA1: | 6436F6E76CFC9FDCD56541FEB910C4EE314271CA |
| SHA256: | 7857AEF9F8C57B58885CD8FE5AD4FB7872D0BBA7A1C4ABB259513039637279CF |
| SSDEEP: | 3:N8NWXEgNRVK:2aEUzK |
MALICIOUS
No malicious indicators.SUSPICIOUS
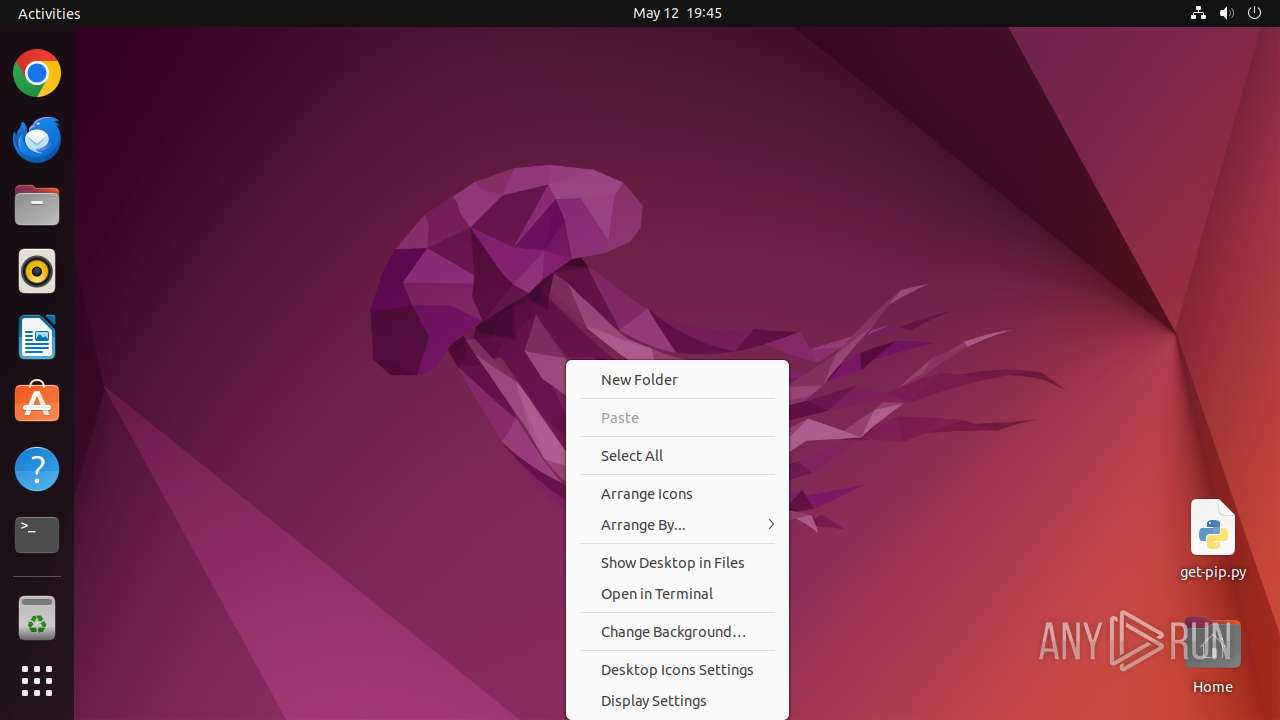
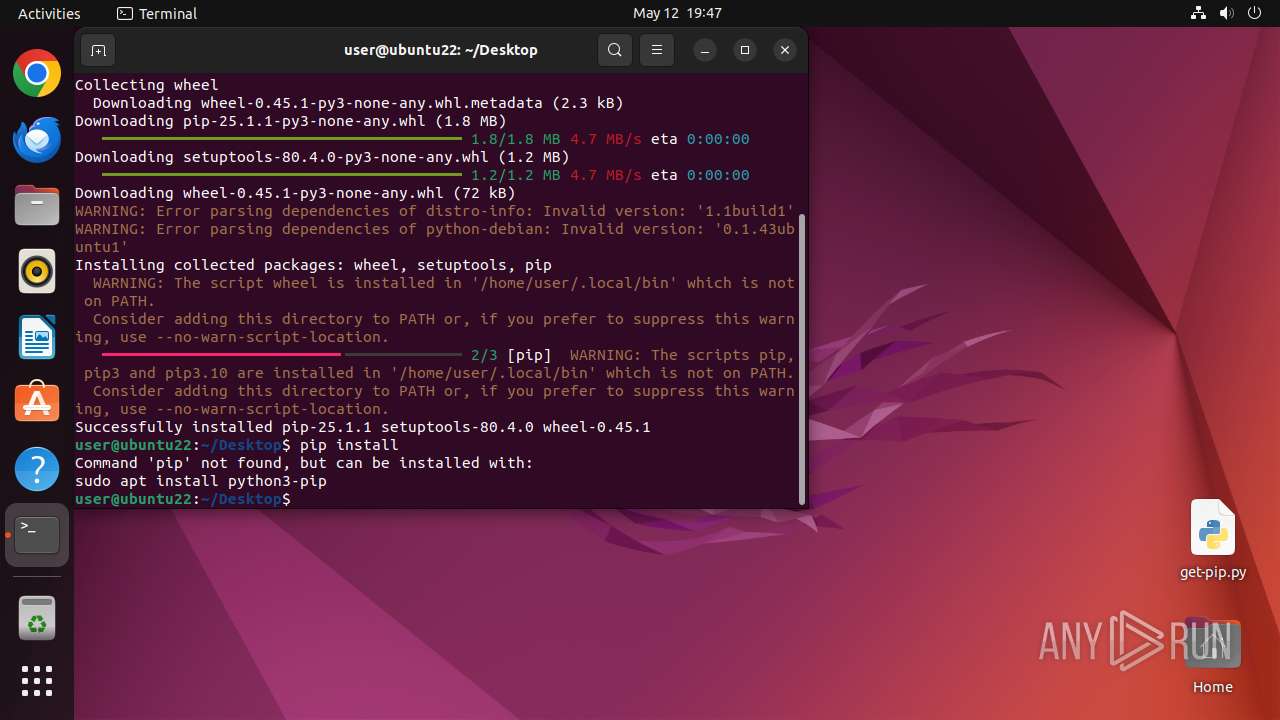
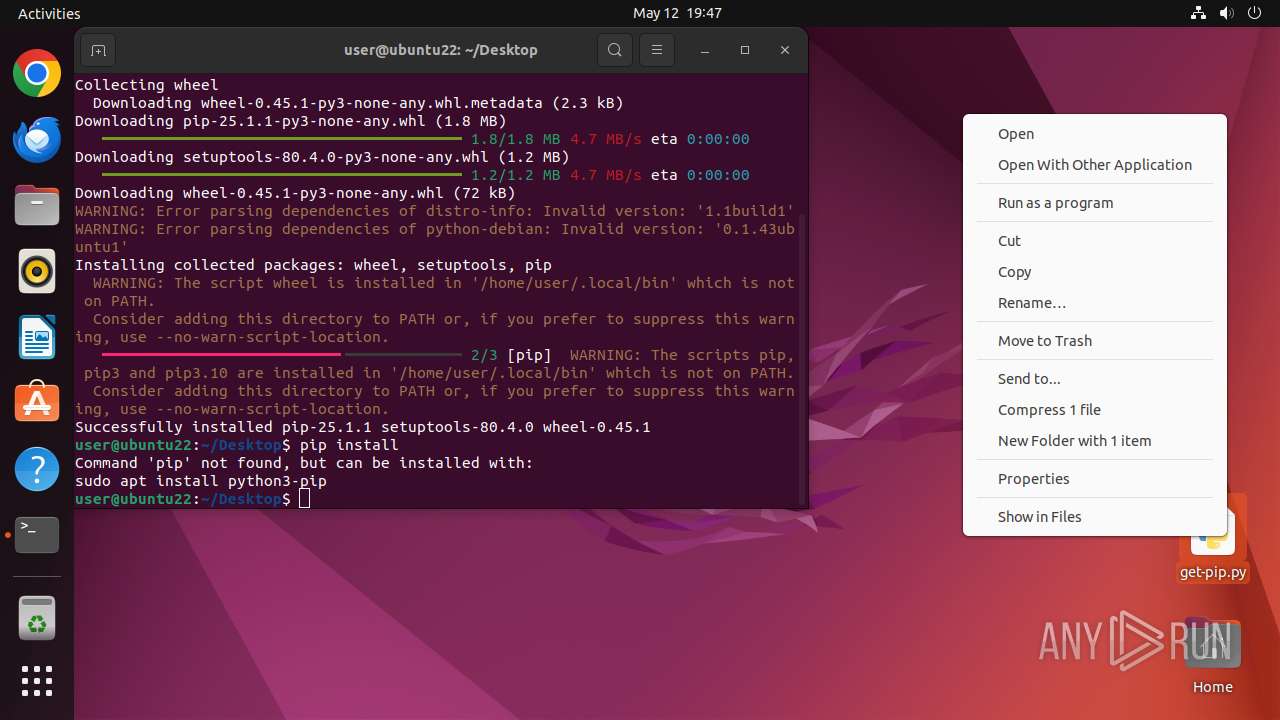
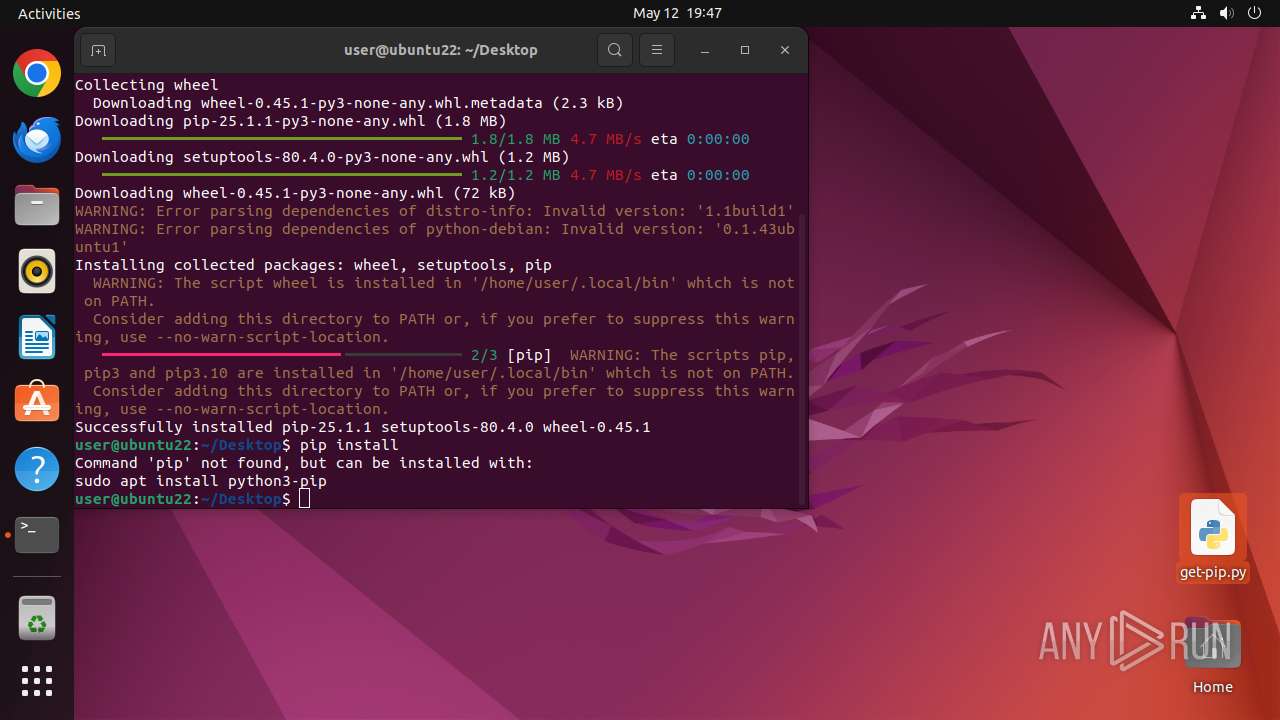
Executes commands using command-line interpreter
- chrome (PID: 40668)
- sudo (PID: 40665)
- gnome-terminal-server (PID: 40860)
- su (PID: 41211)
- gnome-terminal-server (PID: 41181)
Reads passwd file
- su (PID: 41211)
Check the Environment Variables Related to System Identification (os-release)
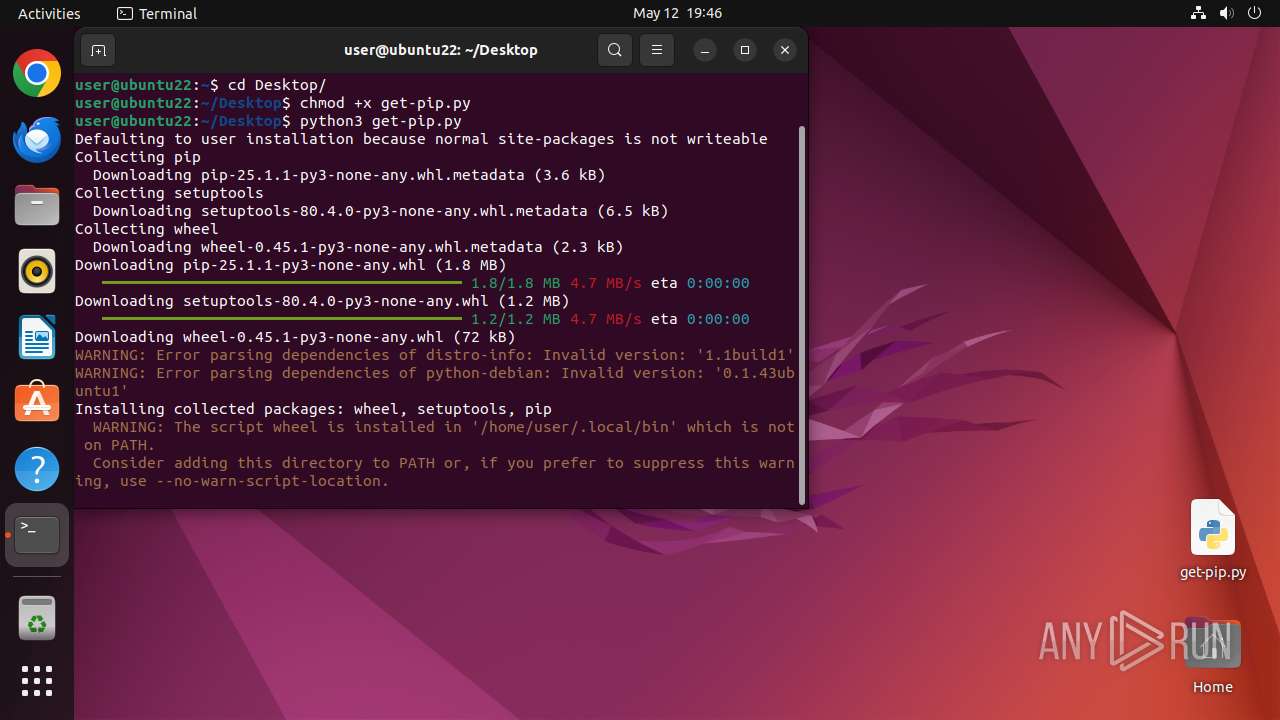
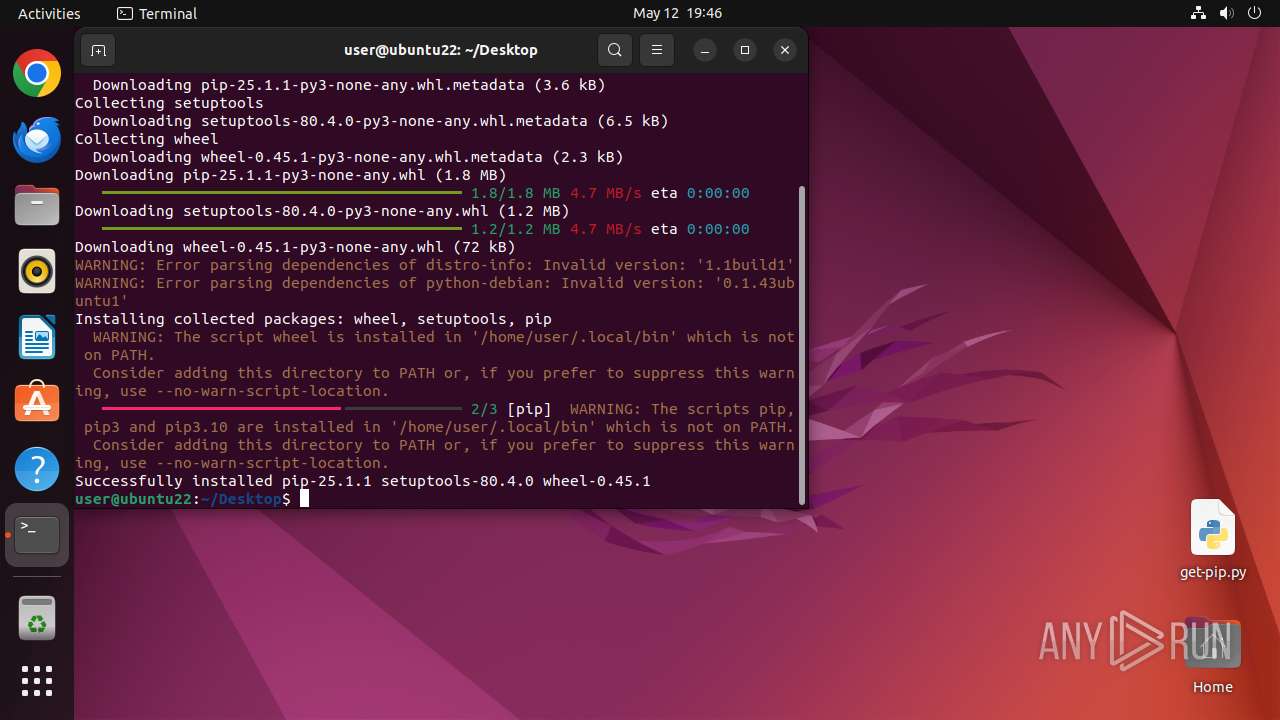
- python3.10 (PID: 41232)
- python3.10 (PID: 41231)
Checks kernel release information (uname)
- python3.10 (PID: 41231)
Executable content was dropped or overwritten
- python3.10 (PID: 41231)
INFO
Checks timezone
- chrome (PID: 40668)
- python3.10 (PID: 40852)
- python3.10 (PID: 41174)
- su (PID: 41211)
- python3.10 (PID: 41231)
- python3.10 (PID: 41232)
- python3.10 (PID: 41240)
Creates file in the temporary folder
- python3.10 (PID: 41231)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
369
Monitored processes
147
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
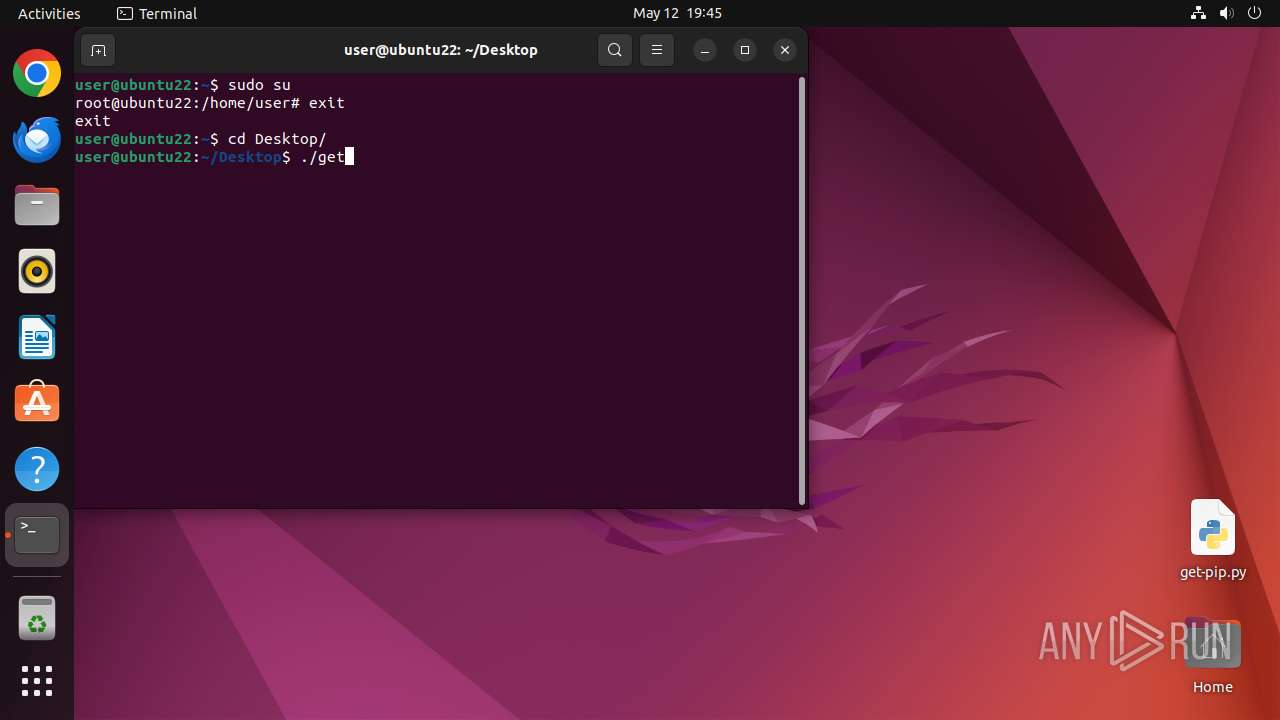
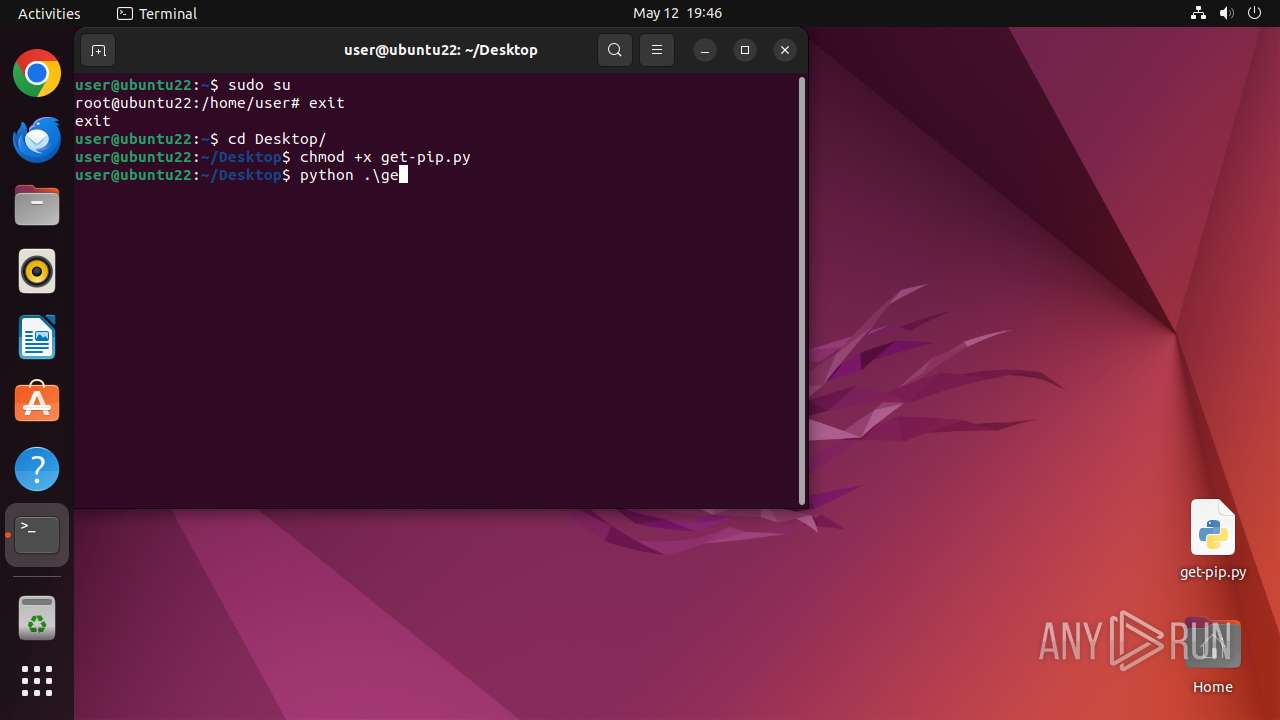
| 40664 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://bootstrap\.pypa\.io/get-pip\.py " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40665 | sudo -iu user google-chrome https://bootstrap.pypa.io/get-pip.py | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40666 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40667 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40668 | /usr/bin/google-chrome https://bootstrap.pypa.io/get-pip.py | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40669 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40670 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40671 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40672 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40673 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
21
Suspicious files
281
Text files
422
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40668 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/Extension State/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
35
DNS requests
37
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aca4j7naijrf65juvpzj5lv43una_2025.4.30.0/niikhdgajlphfehepabhhblakbdgeefj_2025.04.30.00_all_pi2vwi5t776kda42vjlunrgh5u.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclxnidwwkj5di3vduduj2gqpgpq_4.10.2891.0/oimompecagnajdejgnnjijobebaeigek_4.10.2891.0_linux_b4hin3q5s66ws2322cyyfp35lu.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/avtaypr7qxkbxa4ziskdkuquki_507/lmelglejhemejginpboagddgdfbepgmp_507_all_ZZ_acsofxfb65zjxy76u2gu7rzkbdhq.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ack5uggbk52xbbpamivut3hdp5lq_2025.5.12.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2025.05.12.01_all_acaacxxkg6wl6bml346gkcq2gtxq.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lnu3li27zsanbe2hcsfjuvm5fq_1.0.7.1744928549/laoigpblnllgcgjnjnllmfolckpjlhki_1.0.7.1744928549_all_ady56p6vtubsna6mhkx6lu2qml3a.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acosv2d45j5soyhhddhpmgg64wva_2025.5.8.1142/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.5.8.1142_all_kw4rwfqlbgg4222ufx6ttgrunm.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ktyagi2aeozubwzo2hlk3u6dni_1313/efniojlnjndmcbiieegkicadnoecjjef_1313_all_p4rv2wtycprx24knn2sn7g2ag4.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bnxx6s3k3y2e4nwiw3e7krqlhe_9779/hfnkpimlhhgieaddgfemjhofmfblmnib_9779_all_adoxx267ykskysr5rtzd5qnm5djq.crx3 | unknown | — | — | whitelisted |
40715 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adchl7wjwtq6n322xjkik2i7vfaa_20250424.754192769.14/obedbbhbpmojnkanicioggnmelmoomoc_20250424.754192769.14_all_ENGB500000_ad77ur2hlt5pkhj4pv534qpf4seq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 212.102.56.178:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40715 | chrome | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
40715 | chrome | 142.250.185.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40715 | chrome | 151.101.0.175:443 | bootstrap.pypa.io | FASTLY | US | whitelisted |
40715 | chrome | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| whitelisted |
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
bootstrap.pypa.io |
| whitelisted |
dualstack.c.ssl.global.fastly.net |
| unknown |
accounts.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40715 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |