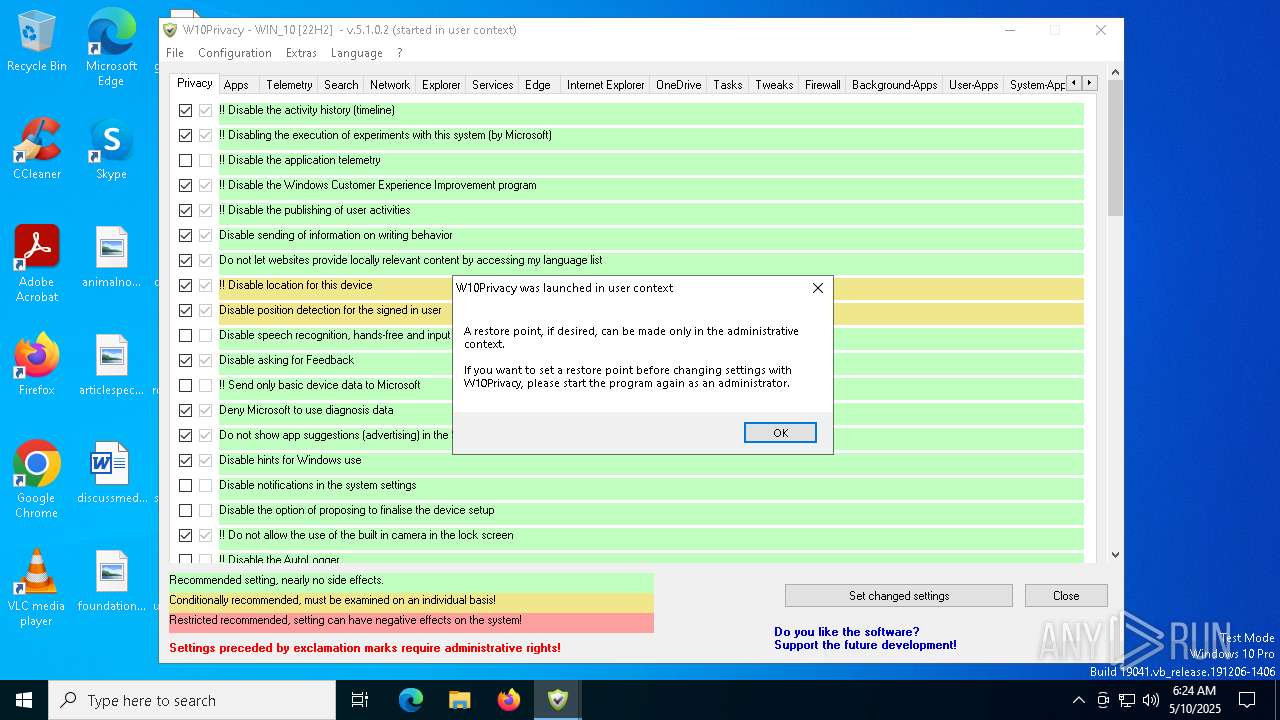
| File name: | W10Privacy.exe |
| Full analysis: | https://app.any.run/tasks/3c545904-237a-4881-8455-a1fcb60d26ea |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 06:23:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | B64E40D8D9D93A31EB533900441301F2 |
| SHA1: | 0598CD7137CECFC6F158954406CF7E1881F61D3C |
| SHA256: | 78471B1D3118E163E77E85BA6A9993ECE080AD1235C16DF7430F1C9C2F539904 |
| SSDEEP: | 98304:+5Drp5VkvdRLca1GlDCMMLIP3ueftJOS8XDblsOqmILByW+lbsNA1o9va/xmISHb:9fUR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Identifying current user with WHOAMI command
- cmd.exe (PID: 7152)
Lists all scheduled tasks in specific format
- schtasks.exe (PID: 7380)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7696)
Starts CMD.EXE for commands execution
- W10Privacy.exe (PID: 5956)
There is functionality for taking screenshot (YARA)
- W10Privacy.exe (PID: 5956)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 8120)
INFO
Checks supported languages
- W10Privacy.exe (PID: 5956)
The sample compiled with german language support
- W10Privacy.exe (PID: 5956)
Reads mouse settings
- W10Privacy.exe (PID: 5956)
Reads the computer name
- W10Privacy.exe (PID: 5956)
Create files in a temporary directory
- W10Privacy.exe (PID: 5956)
UPX packer has been detected
- W10Privacy.exe (PID: 5956)
The process uses AutoIt
- W10Privacy.exe (PID: 5956)
Reads security settings of Internet Explorer
- netsh.exe (PID: 8176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (28.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (28) |
| .exe | | | Win32 EXE Yoda's Crypter (27.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.8) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:19 07:34:02+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 356352 |
| InitializedDataSize: | 1986560 |
| UninitializedDataSize: | 2514944 |
| EntryPoint: | 0x2bd340 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.0.2 |
| ProductVersionNumber: | 3.3.14.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Unicode |
| FileVersion: | 5.1.0.2 |
| Comments: | http://www.autoitscript.com/autoit3/ |
| FileDescription: | W10Privacy |
| ProductVersion: | 3.3.14.5 |
| LegalCopyright: | Bernd Schuster |
Total processes
154
Monitored processes
27
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\WINDOWS\system32\cmd.exe /C del /s /q "C:\Users\admin\AppData\Local\Temp\rules_out.txt" | C:\Windows\SysWOW64\cmd.exe | — | W10Privacy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | whoami /ALL | C:\Windows\SysWOW64\whoami.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\cmd.exe /C del /s /q "C:\Users\admin\AppData\Local\Temp\systemapps_names.txt" | C:\Windows\SysWOW64\cmd.exe | — | W10Privacy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | C:\WINDOWS\system32\cmd.exe /C dir "C:\WINDOWS\SystemApps" /B > C:\Users\admin\AppData\Local\Temp\systemapps_names.txt | C:\Windows\SysWOW64\cmd.exe | — | W10Privacy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5956 | "C:\Users\admin\AppData\Local\Temp\W10Privacy.exe" | C:\Users\admin\AppData\Local\Temp\W10Privacy.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: W10Privacy Version: 5.1.0.2 Modules
| |||||||||||||||
| 7152 | C:\WINDOWS\system32\cmd.exe /C whoami /ALL > C:\Users\admin\AppData\Local\Temp\whoami.txt | C:\Windows\SysWOW64\cmd.exe | — | W10Privacy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 734
Read events
6 734
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
10
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5956 | W10Privacy.exe | C:\Users\admin\AppData\Local\Temp\autBD39.tmp | binary | |
MD5:EE09704A4C7C778ECC040B2A11082C95 | SHA256:A5D2FC1343B7E7EE8328C9369999FDFC6F1035AB9AE38BCA291658BF78888A14 | |||
| 5956 | W10Privacy.exe | C:\Users\admin\AppData\Local\Temp\W10Privacy.ini | text | |
MD5:A28367555FB661A98B03D27D943EF3E2 | SHA256:E9E9FC976264DA1D348B67AD496A8EB627888C4139E776DE16396C1E17F443AD | |||
| 7152 | cmd.exe | C:\Users\admin\AppData\Local\Temp\whoami.txt | text | |
MD5:46ED8955B55EF2FE721CD9F4D9DC92B9 | SHA256:57C962A0605FA1F6189375C8ECE2E72EA2A266BF8DF33D122F4556B060138661 | |||
| 7696 | cmd.exe | C:\Users\admin\AppData\Local\Temp\benutzerapps.txt | text | |
MD5:558FD48C6607826BAEAC779DA52A2510 | SHA256:CE9276D2CC1CE3A2A1596C1B2A8FAA5C29768B40EA19552C9698336FB08746F6 | |||
| 5956 | W10Privacy.exe | C:\Users\admin\AppData\Local\Temp\autBCCA.tmp | binary | |
MD5:C8BB940FE3F281D99C0C602D38A379C6 | SHA256:9808AA0E36B1639FC2E9D779E3D06728205A2DA2797BFD47F6AEBCFD9B9A1126 | |||
| 7776 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5FD8414E6CF2BB1B691134FC5279575C | SHA256:EFBBECA65D05D1B0BB7ADD37FDF22D6D5A4FB771D5BDA42175987D87EF49E2B1 | |||
| 5956 | W10Privacy.exe | C:\Users\admin\AppData\Local\Temp\aut2FBC.tmp | binary | |
MD5:BB9C5707A7872089932C7D7211038CD5 | SHA256:33468E667E8CC2A96B29B36E020FA62CDA7A609088422E3DD9BE6A8B4238E2B4 | |||
| 7260 | cmd.exe | C:\Users\admin\AppData\Local\Temp\tasks.txt | csv | |
MD5:61C4A39BE6B9E0F29561260183E4F51A | SHA256:81176A4914F816242BAE920411F2A99BD798F90E5BB87B1B3CBE797379D9E782 | |||
| 5956 | W10Privacy.exe | C:\Users\admin\AppData\Local\Temp\aut2FBB.tmp | binary | |
MD5:ABB9CC97C9C06ECFD491D28622E7652F | SHA256:DA5CF0E58DE4E2CFBA26B3D7A4726C3E50DACEE606FEB300A27D3D46521AE32C | |||
| 5956 | W10Privacy.exe | C:\Users\admin\AppData\Local\Temp\Cache.ini | text | |
MD5:1839CD193432FD66B6BEE663C3455B28 | SHA256:C0762414D431D61249D93C7424EA0E1A158BA514966A77FD111187E143A9315B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5072 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
5072 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.17:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |