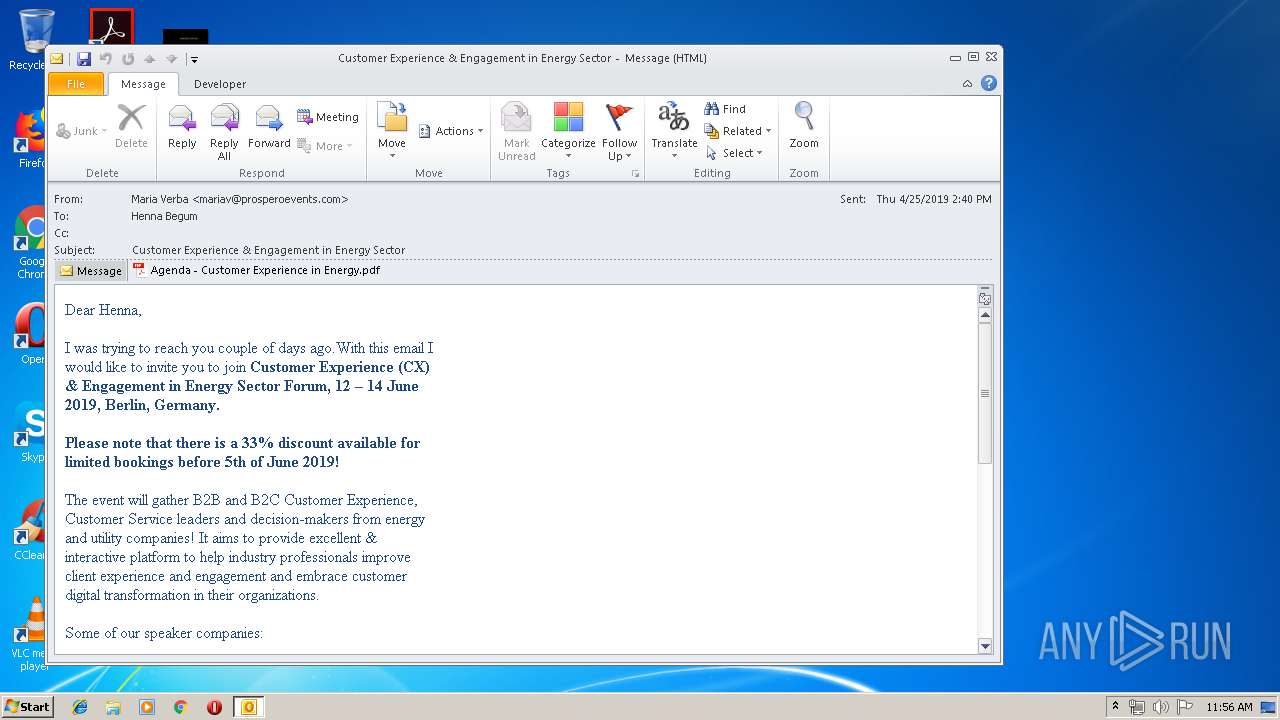
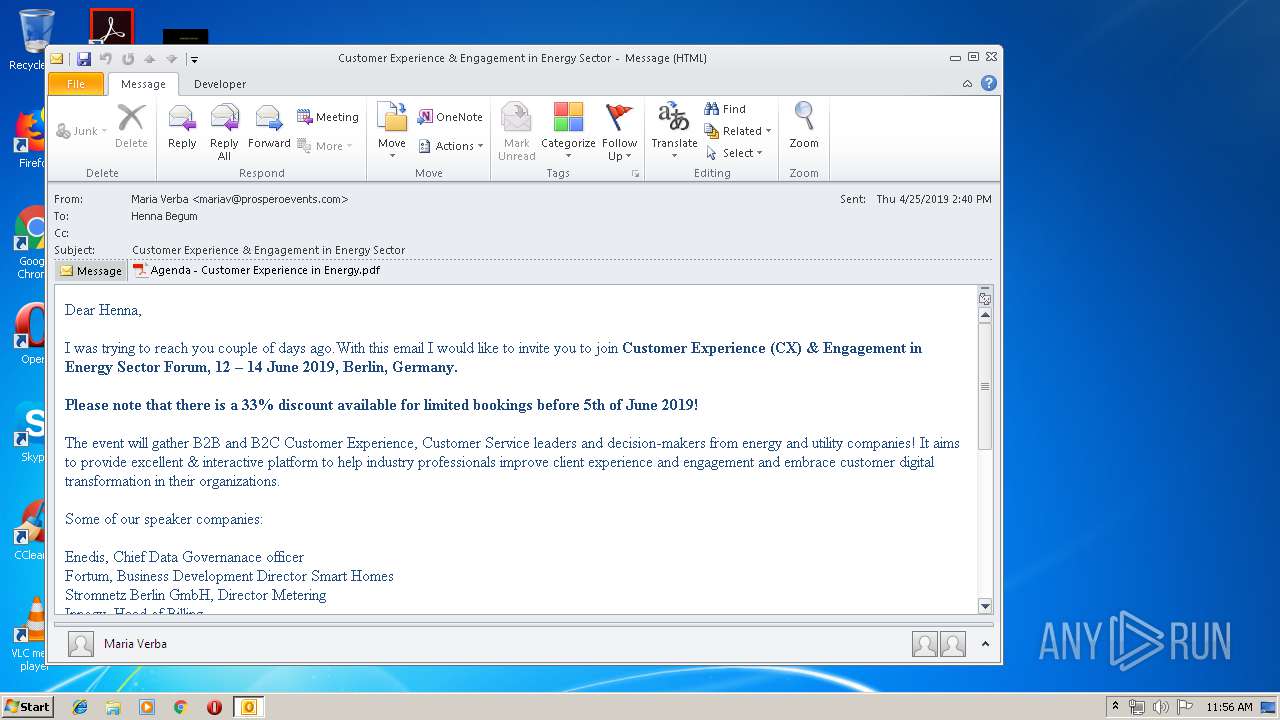
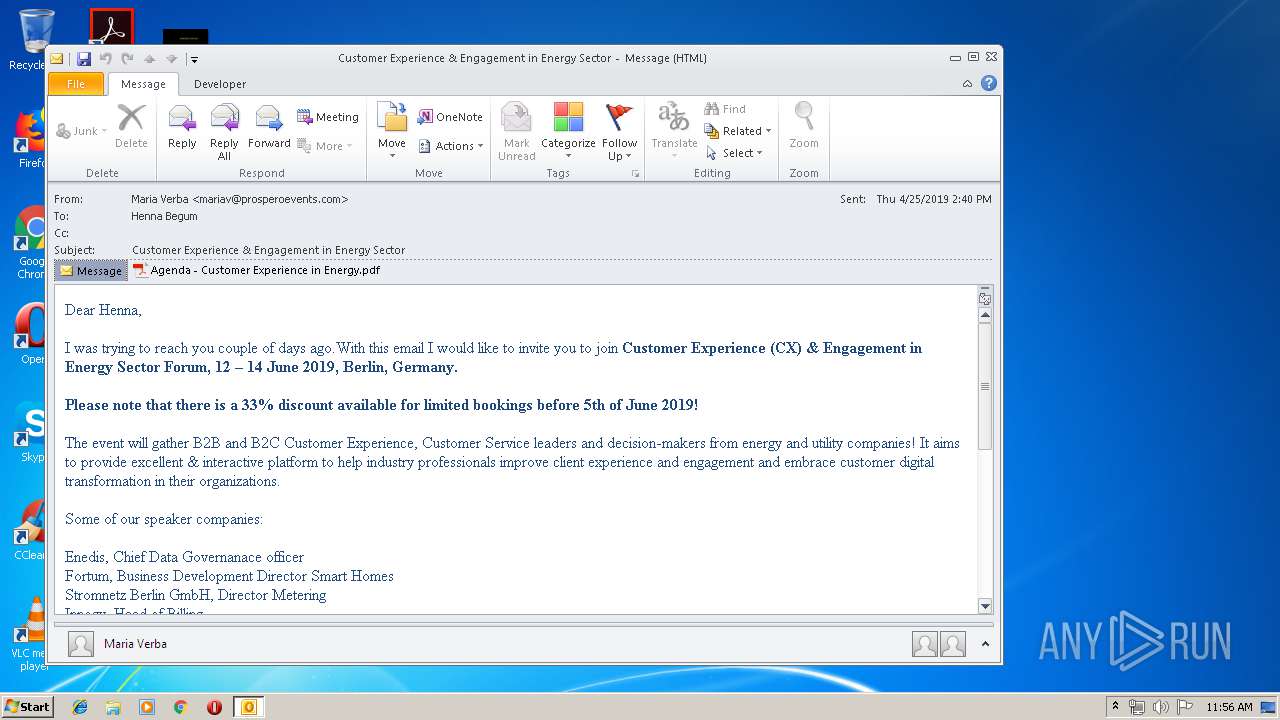
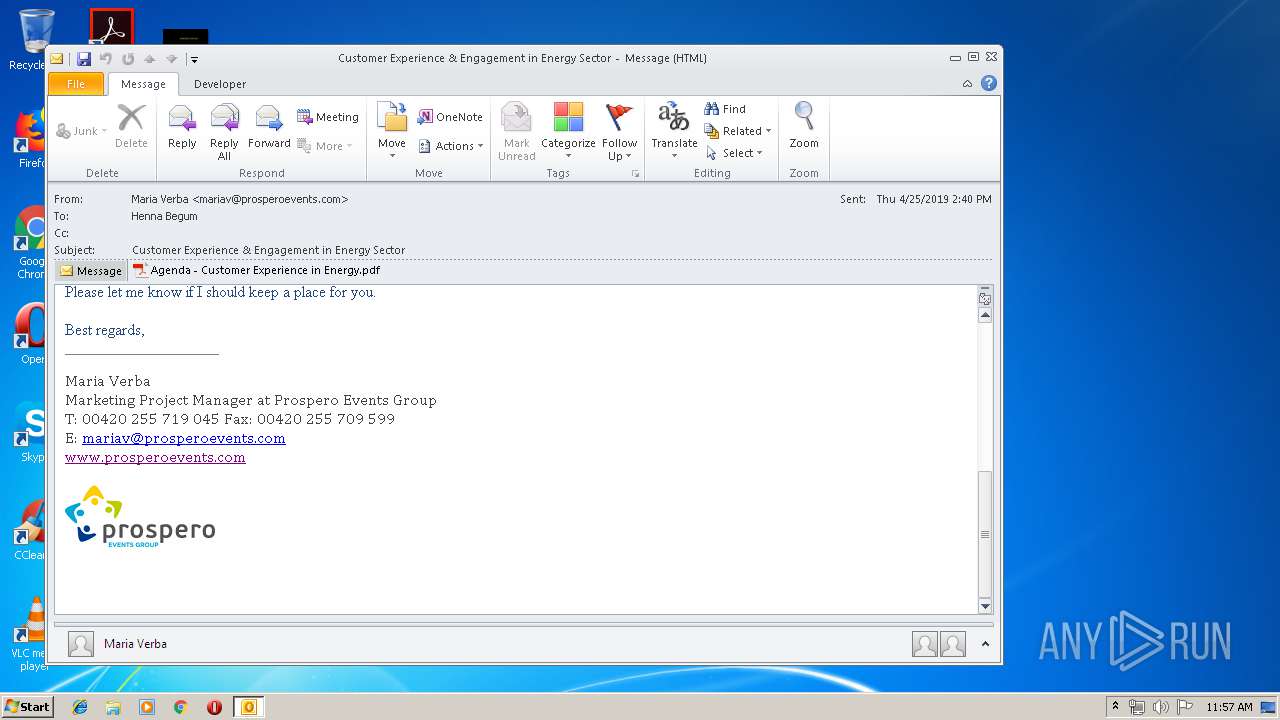
| File name: | Customer Experience Engagement in Energy Sector.msg |
| Full analysis: | https://app.any.run/tasks/3a188352-c7f4-431b-8ada-4f605714468e |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 10:56:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 130D345C219924780FC8802CB827EC69 |
| SHA1: | 77AD12E709CFDFEEBEA610D23EAD307632CBA66B |
| SHA256: | 78302C329F6FB8CBFAFFEDA3D6452B28B01041E51FBAD161E2410904589DC916 |
| SSDEEP: | 6144:oglt8V1mDpKK5SLuL+bFPd4Tf1igYBs0+0r:okyVstKHHbF6TRYBs |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3016)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3016)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3016)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3016)
INFO
Creates files in the user directory
- AcroRd32.exe (PID: 2904)
- iexplore.exe (PID: 1472)
Changes internet zones settings
- iexplore.exe (PID: 3088)
Reads internet explorer settings
- iexplore.exe (PID: 1472)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3016)
Application launched itself
- AcroRd32.exe (PID: 2904)
- RdrCEF.exe (PID: 2840)
- iexplore.exe (PID: 3088)
Reads Internet Cache Settings
- iexplore.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
43
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3088 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2840.0.2118135322\683232854" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2840.1.420495036\48542413" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RK7M3E50\Agenda - Customer Experience in Energy.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Customer Experience Engagement in Energy Sector.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
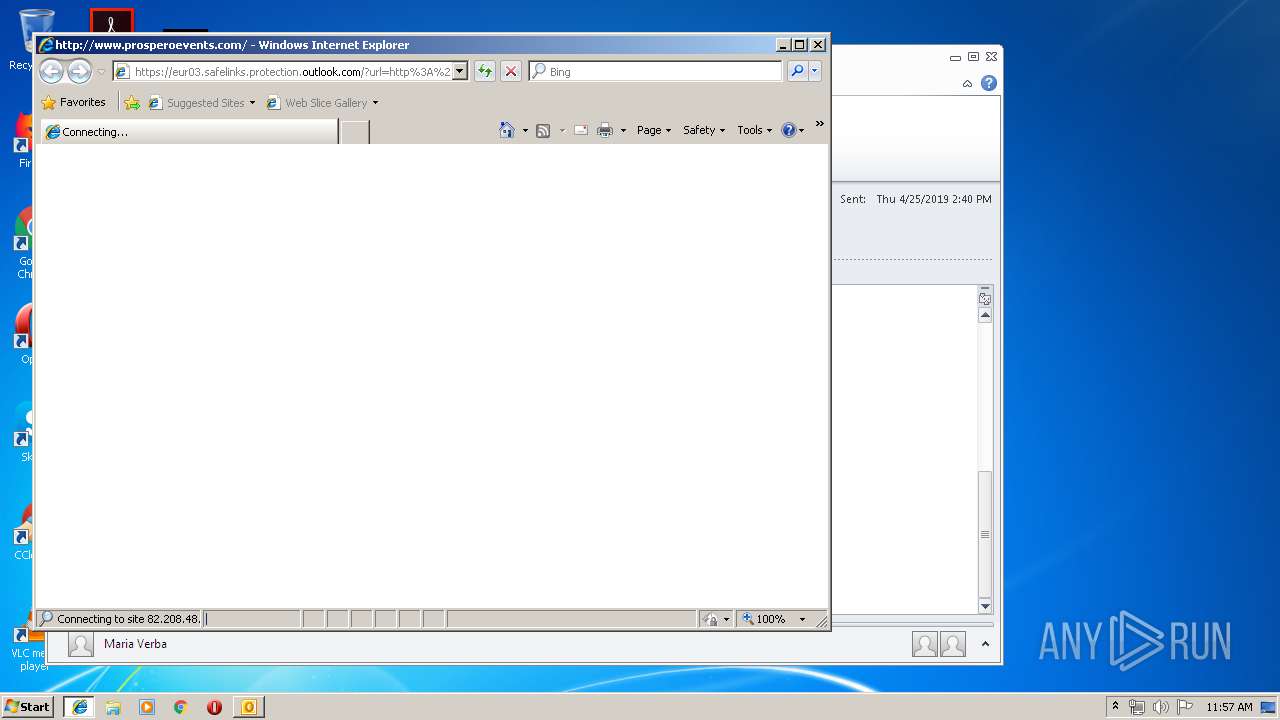
| 3088 | "C:\Program Files\Internet Explorer\iexplore.exe" https://eur03.safelinks.protection.outlook.com/?url=http%3A%2F%2Fwww.prosperoevents.com&data=02%7C01%7Chenna.begum%40havenpower.com%7C7c2d2eac3c2a4058865b08d6c98390bb%7C007c146d3d97467d849f6f4fe5a6a0f3%7C0%7C0%7C636917964450266510&sdata=PE7%2BM9mYmaqaV97vJpFP9cFWDQxz9mRsYPvlbhjxueU%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3208 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RK7M3E50\Agenda - Customer Experience in Energy.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
2 068
Read events
1 529
Write events
518
Delete events
21
Modification events
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | of? |
Value: 6F663F00C80B0000010000000000000000000000 | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C80B0000E0EA05B3FA0ED50100000000 | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220046400 | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3016) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1320419349 | |||
Executable files
0
Suspicious files
9
Text files
57
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3016 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE60.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3016 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RK7M3E50\Agenda - Customer Experience in Energy (2).pdf\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3208 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SharedDataEvents-journal | — | |
MD5:— | SHA256:— | |||
| 3208 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3208 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.3208 | — | |
MD5:— | SHA256:— | |||
| 3208 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.3208 | — | |
MD5:— | SHA256:— | |||
| 3016 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3016 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A239C97D.dat | image | |
MD5:— | SHA256:— | |||
| 3016 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_3E4CD965BD623642A94C5BE7C7209BDB.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3016 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\RK7M3E50\Agenda - Customer Experience in Energy (2).pdf | ||
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
13
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3016 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2904 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/modules/mod_news_pro_gk4/interface/css/style.portal.mode.1.css | CZ | text | 684 b | suspicious |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/modules/mod_image_show_gk4/styles/gk_financial_business/style.css | CZ | text | 637 b | suspicious |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/templates/gk_appsite/css/template12.css | CZ | text | 10.3 Kb | suspicious |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/templates/gk_appsite/css/k2.css | CZ | compressed | 9.65 Kb | suspicious |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/templates/gk_appsite/js/gk.scripts.js | CZ | text | 1.12 Kb | suspicious |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/templates/gk_appsite/js/gk.video.js | CZ | text | 7.12 Kb | suspicious |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/components/com_k2store/js/k2store.js | CZ | text | 2.28 Kb | suspicious |
1472 | iexplore.exe | GET | 200 | 82.208.48.93:80 | http://www.prosperoevents.com/templates/gk_appsite/css/menu.gkmenu.css | CZ | text | 196 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2904 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3016 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1472 | iexplore.exe | 13.90.95.14:80 | www.ape78cn2.com | Microsoft Corporation | US | whitelisted |
2904 | AcroRd32.exe | 2.16.186.33:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
3088 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1472 | iexplore.exe | 216.58.207.42:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1472 | iexplore.exe | 104.47.10.28:443 | eur03.safelinks.protection.outlook.com | Microsoft Corporation | IE | whitelisted |
1472 | iexplore.exe | 82.208.48.93:80 | www.prosperoevents.com | Casablanca INT | CZ | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
eur03.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.prosperoevents.com |
| suspicious |
ajax.googleapis.com |
| whitelisted |
www.ape78cn2.com |
| malicious |
dns.msftncsi.com |
| shared |