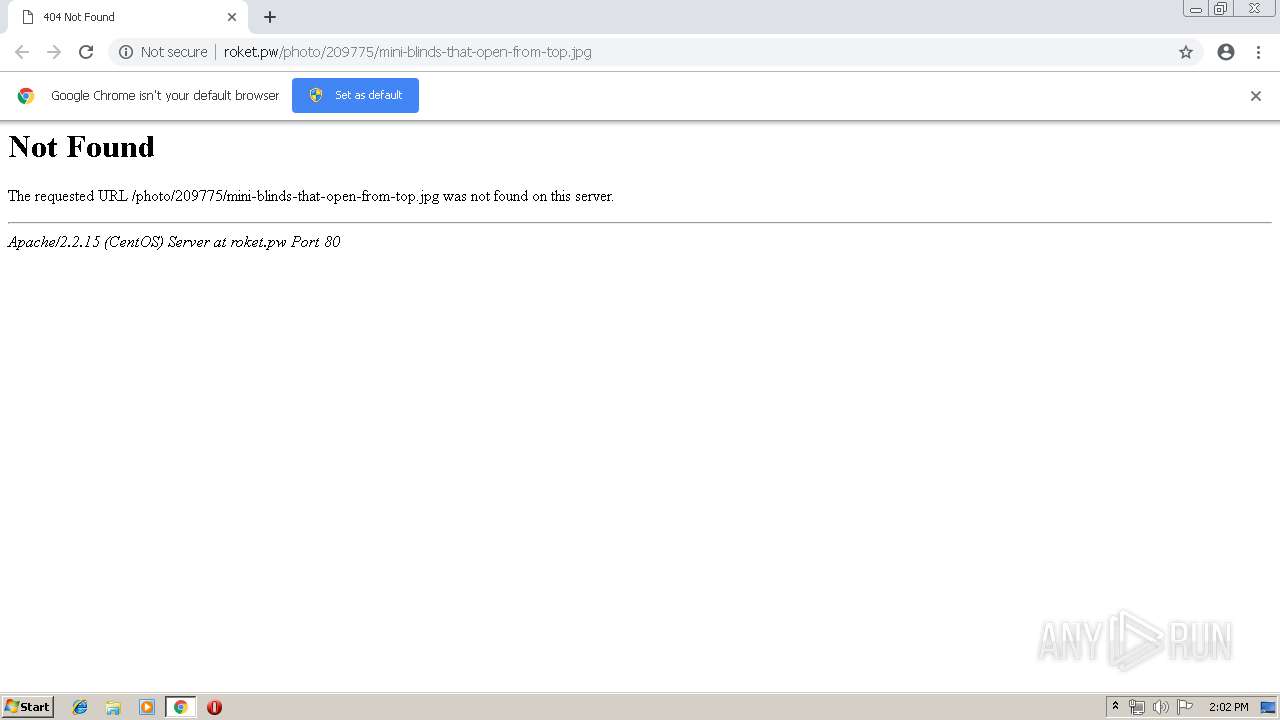
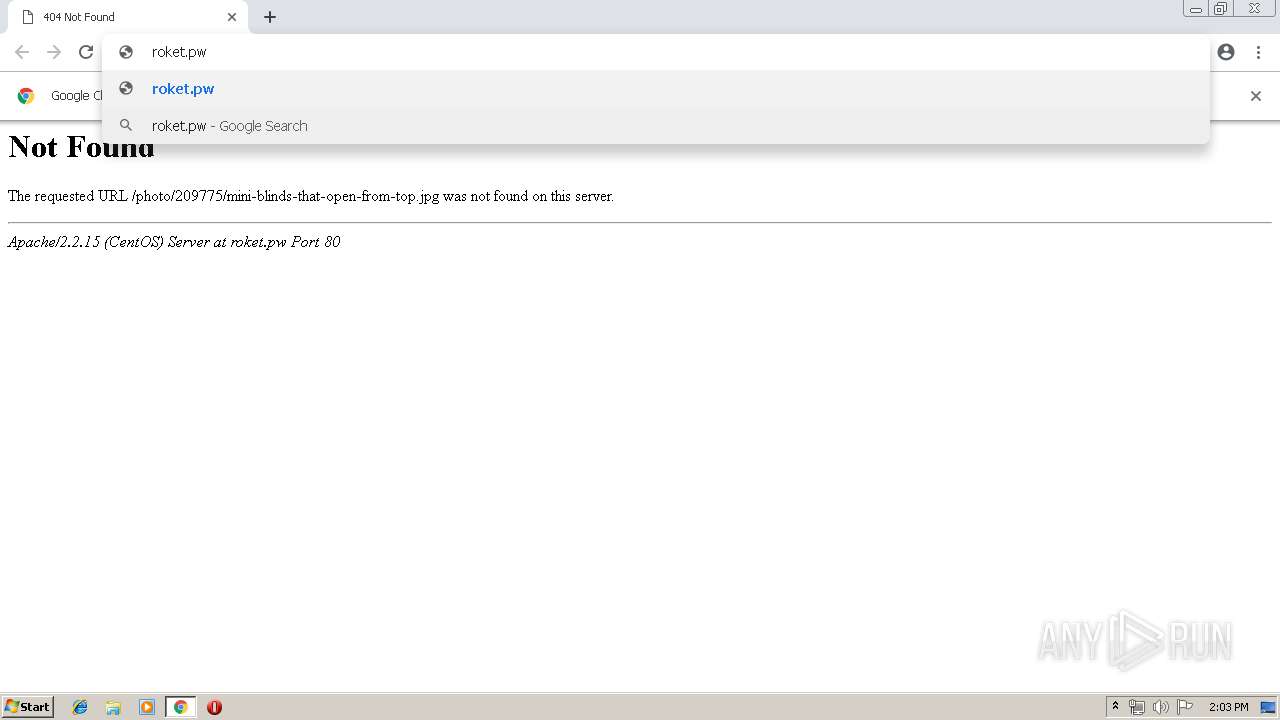
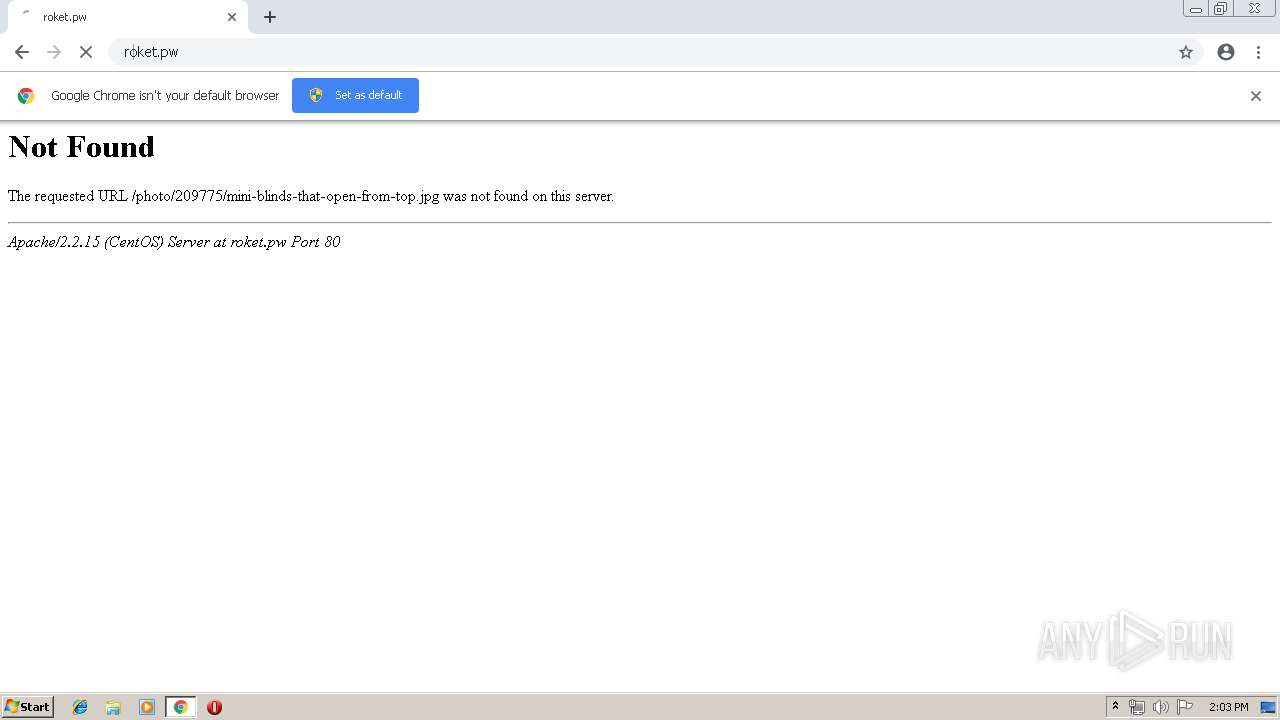
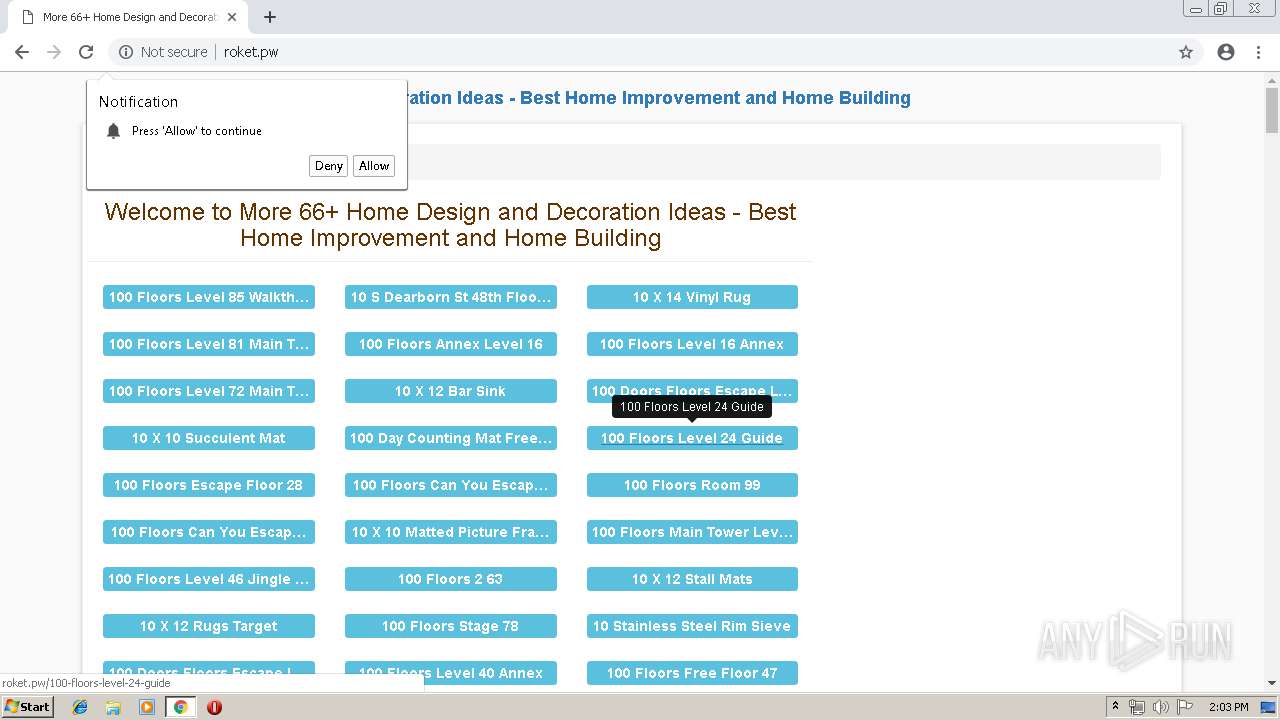
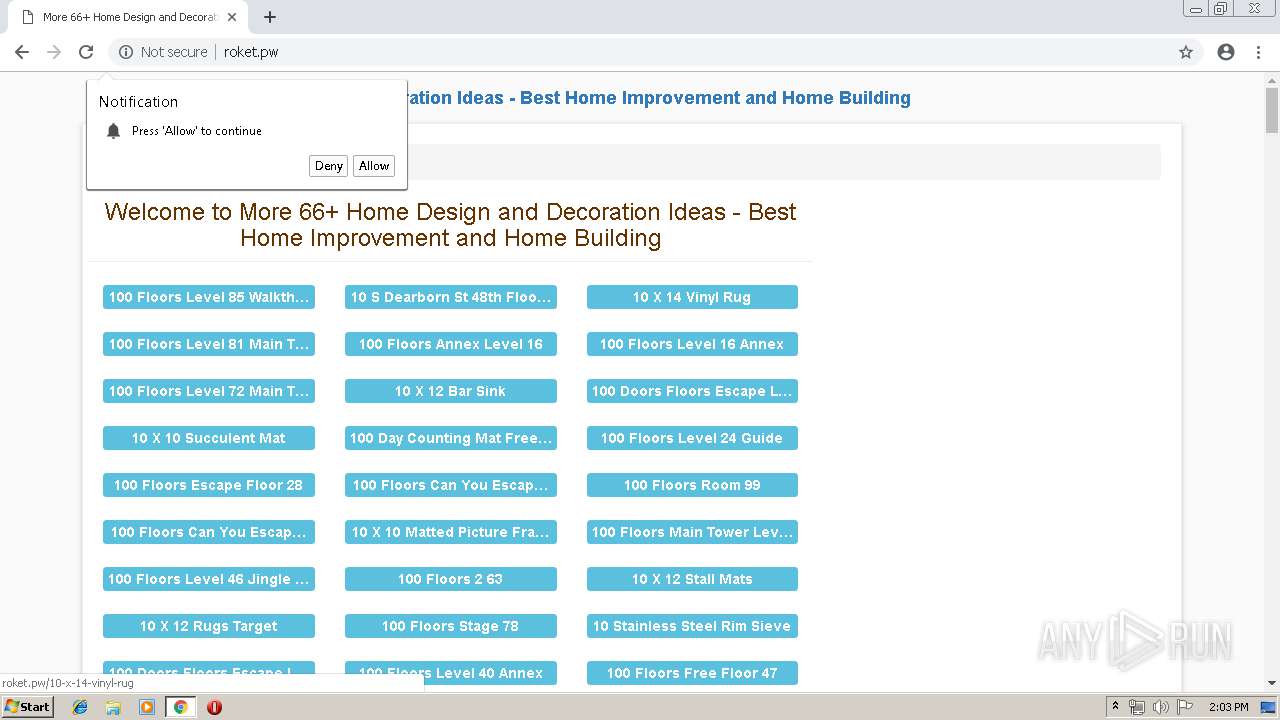
| URL: | http://roket.pw/photo/209775/mini-blinds-that-open-from-top.jpg |
| Full analysis: | https://app.any.run/tasks/1cc23093-7d33-4e3b-a4c9-188f497458bd |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 13:02:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4FD4E20B55BD4D77C52A623F4F3B3E59 |
| SHA1: | 1479DC95EBD9C5E9B76E8BF0542EFFEC92E84181 |
| SHA256: | 78241E08DBDFED51CA280B052A56803DFA2CCCC5A43759F3C62D7E64DE55E828 |
| SSDEEP: | 3:N1KMXJX2hfIMYOFVAkKIBRCn:CMZXYfLVADak |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://roket.pw/photo/209775/mini-blinds-that-open-from-top.jpg | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --service-pipe-token=953879581538579774 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=953879581538579774 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --service-pipe-token=15681485701852209054 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15681485701852209054 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5078453381817823270 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5078453381817823270 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4753481070215143674 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4753481070215143674 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=490350615579386511 --mojo-platform-channel-handle=3484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12961315274846328852 --mojo-platform-channel-handle=3992 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3914649626176237911 --mojo-platform-channel-handle=3660 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10754223863273789255 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8030672525457960087 --mojo-platform-channel-handle=3492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
546
Read events
476
Write events
66
Delete events
4
Modification events
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 584-13202830962362375 |
Value: 259 | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 584-13202830962362375 |
Value: 259 | |||
Executable files
0
Suspicious files
34
Text files
59
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\da81ad3d-0ad4-42d4-af9b-1190a0267d60.tmp | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
52
DNS requests
29
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
584 | chrome.exe | GET | 403 | 198.134.112.242:80 | http://4bb6jls06l.com/0b738a72e003d97f515717a9a8992cdd/invoke.js | US | — | — | whitelisted |
584 | chrome.exe | GET | 403 | 198.134.112.242:80 | http://4bb6jls06l.com/0b738a72e003d97f515717a9a8992cdd/invoke.js | US | — | — | whitelisted |
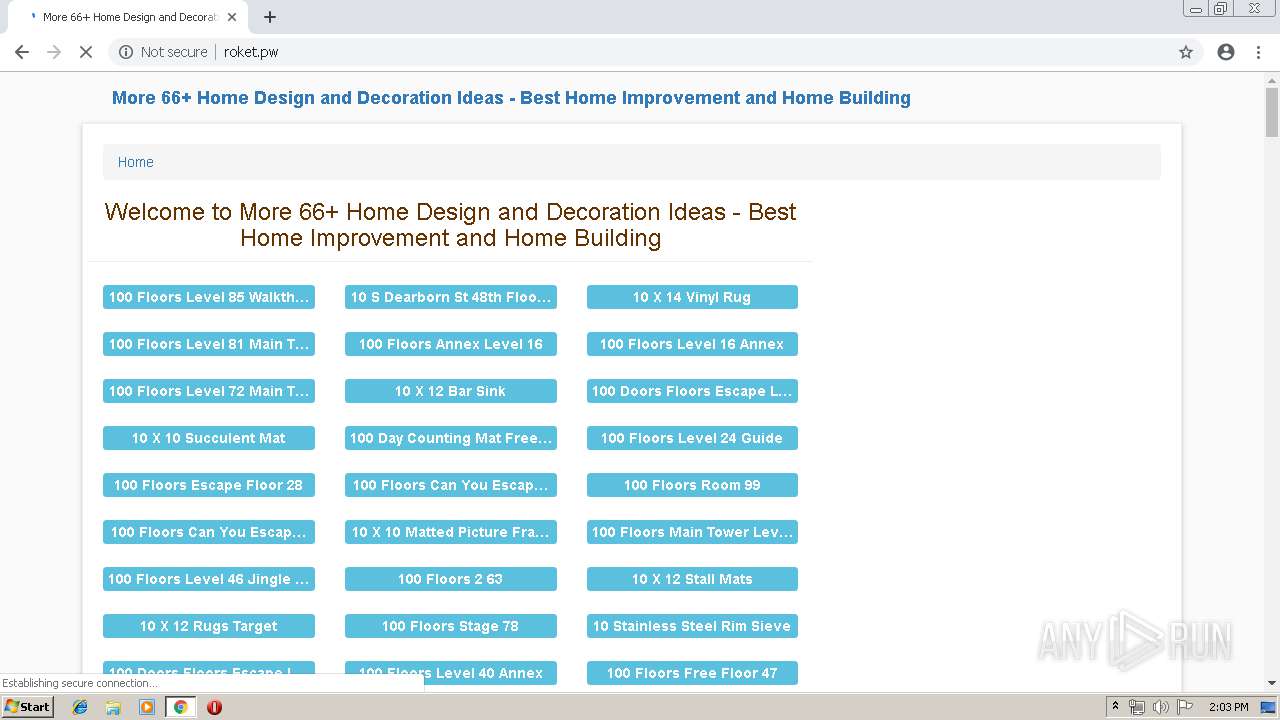
584 | chrome.exe | GET | 404 | 104.28.16.114:80 | http://roket.pw/js/css3-mediaqueries.js | US | html | 244 b | suspicious |
584 | chrome.exe | GET | 200 | 46.105.201.240:80 | http://s10.histats.com/js15_as.js | FR | html | 4.42 Kb | whitelisted |
— | — | GET | 200 | 104.28.16.114:80 | http://roket.pw/lib/css/style.css | US | text | 686 b | suspicious |
584 | chrome.exe | GET | 200 | 172.217.18.98:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 32.2 Kb | whitelisted |
584 | chrome.exe | GET | 200 | 198.27.69.19:80 | http://s4.histats.com/stats/0.php?4225920&@f16&@g0&@h2&@i1&@j1558357383190&@k5&@l2&@mMore%2066%2B%20Home%20Design%20and%20Decoration%20Ideas%20-%20Best%20Home%20Improvement%20and%20Home%20Building&@n0&@o1000&@q0&@r0&@s0&@ten-US&@u1280&@b1:-138076307&@b3:1558357383&@b4:js15_as.js&@b5:60&@a-_0.2.1&@vhttp%3A%2F%2Froket.pw%2F&@w | CA | text | 50 b | whitelisted |
— | — | GET | 200 | 198.27.69.19:80 | http://s4.histats.com/stats/0.php?4246317&@f16&@g0&@h2&@i1&@j1558357383190&@k5&@l2&@mMore%2066%2B%20Home%20Design%20and%20Decoration%20Ideas%20-%20Best%20Home%20Improvement%20and%20Home%20Building&@n0&@o1000&@q0&@r0&@s0&@ten-US&@u1280&@b1:-30738668&@b3:1558357383&@b4:js15_as.js&@b5:60&@a-_0.2.1&@vhttp%3A%2F%2Froket.pw%2F&@w | CA | text | 51 b | whitelisted |
584 | chrome.exe | GET | 204 | 35.190.50.89:80 | http://www.predictivdisplay.com/a/display.php?r=2386007 | US | — | — | whitelisted |
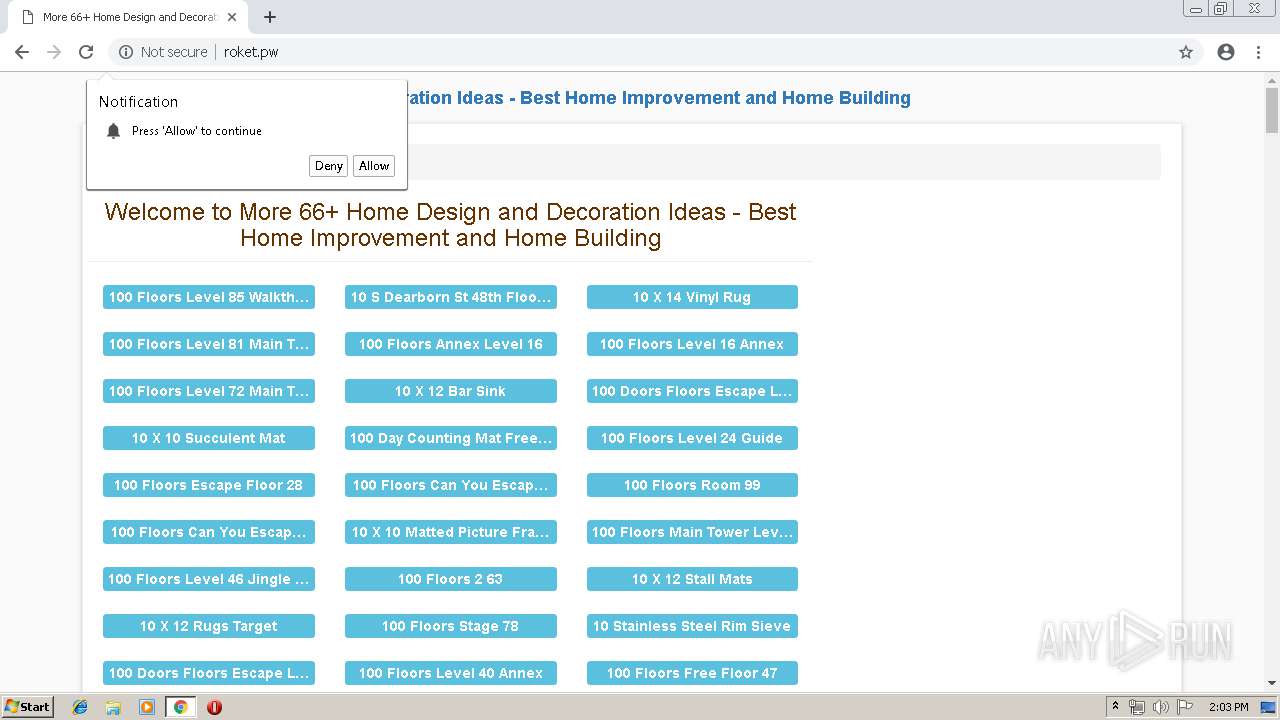
584 | chrome.exe | GET | 200 | 188.72.215.108:80 | http://nativepu.sh/ntfc.php?p=2562737 | NL | text | 4.39 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
584 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
584 | chrome.exe | 104.28.16.114:80 | roket.pw | Cloudflare Inc | US | shared |
584 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 104.28.16.114:80 | roket.pw | Cloudflare Inc | US | shared |
584 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
584 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
584 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
584 | chrome.exe | 172.217.22.67:443 | www.google.de | Google Inc. | US | whitelisted |
584 | chrome.exe | 188.72.215.108:443 | nativepu.sh | Webzilla B.V. | NL | unknown |
— | — | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
roket.pw |
| suspicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
584 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |