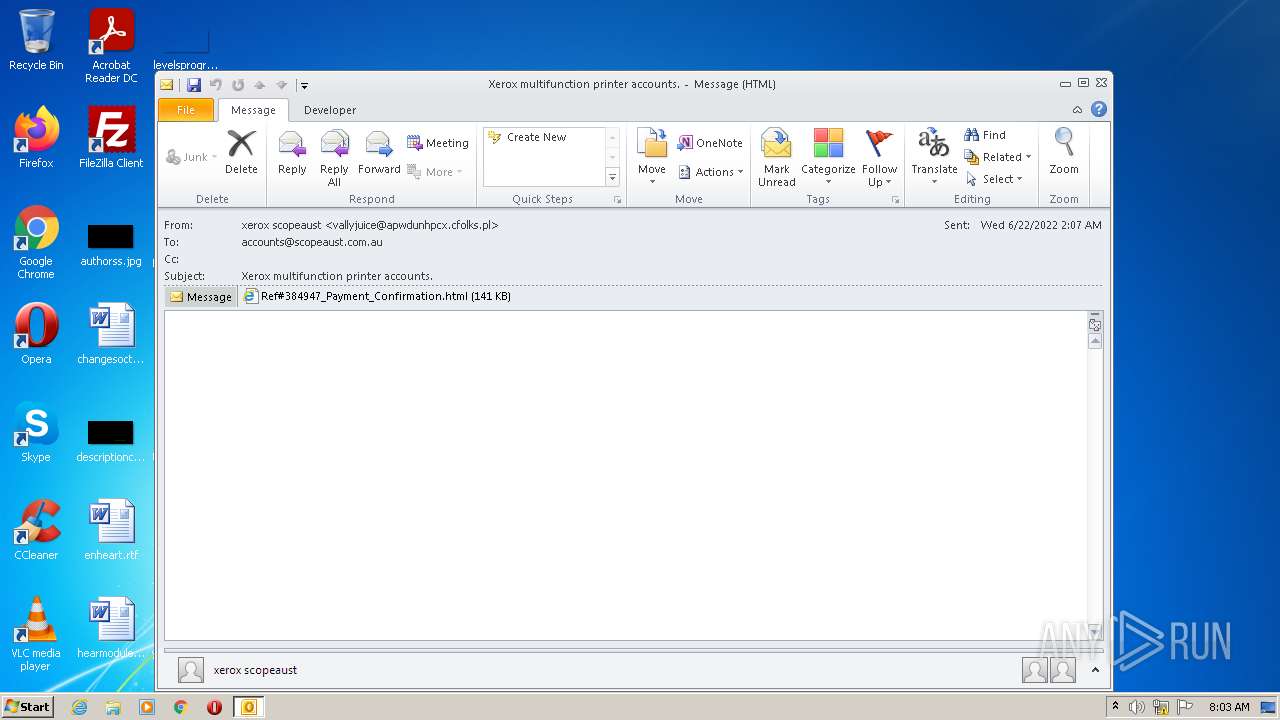
| File name: | 6e6b16de-7b88-4929-868d-08da53eb8024_d57630f1-fd39-1b31-860b-e792f55786d2.eml |
| Full analysis: | https://app.any.run/tasks/cc4e53da-16be-416b-afc2-6ced9eedc9cd |
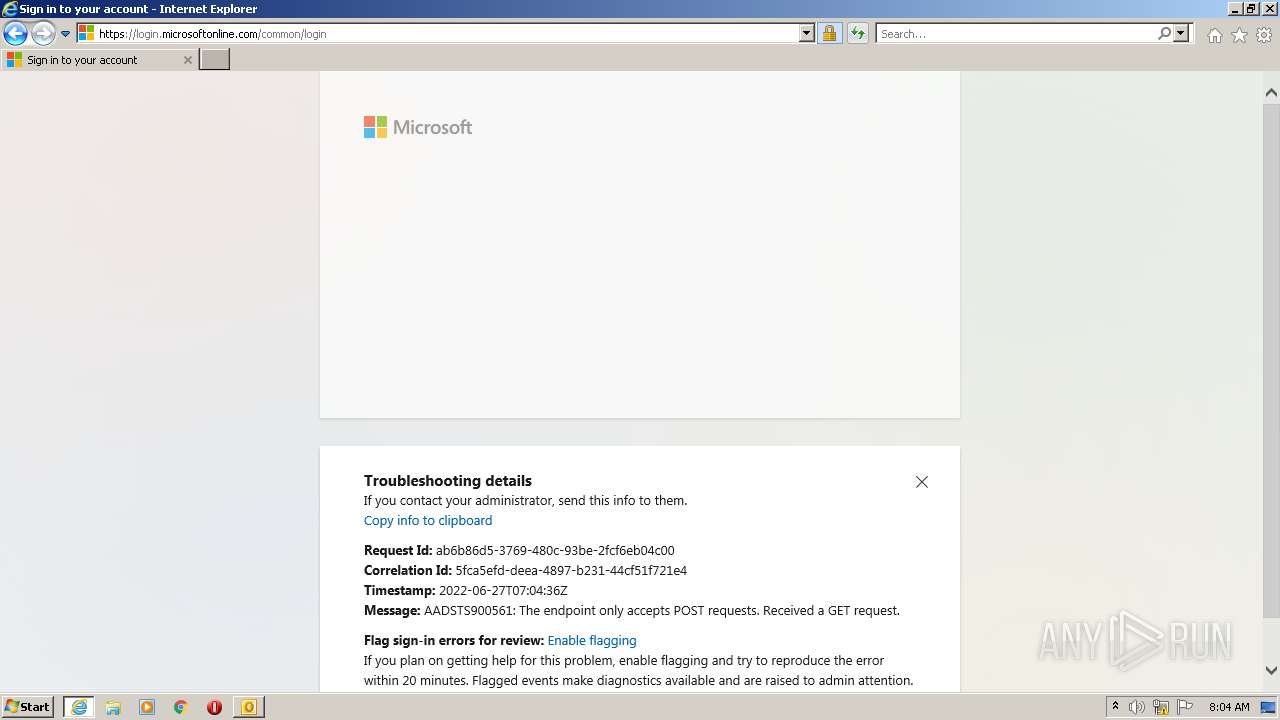
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 07:03:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | D9F93B0BF64B528EE666A279746E8297 |
| SHA1: | 3A651B76A760E04FA28D3B72051E13B48454D9CA |
| SHA256: | 7823779CF03EAA6B81B786C3396BC7510F30F36CD1CF1C44738700A4655B764E |
| SSDEEP: | 3072:o1YoGcHPUfchYj0mqn/SlFVs2oQz2d5oaipXz3KIyAfPdvbk8x9iDNsO6nfwkPGO:yh/Pn/CxjHKaWXG7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 1928)
Searches for installed software
- OUTLOOK.EXE (PID: 1928)
Reads the computer name
- OUTLOOK.EXE (PID: 1928)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1928)
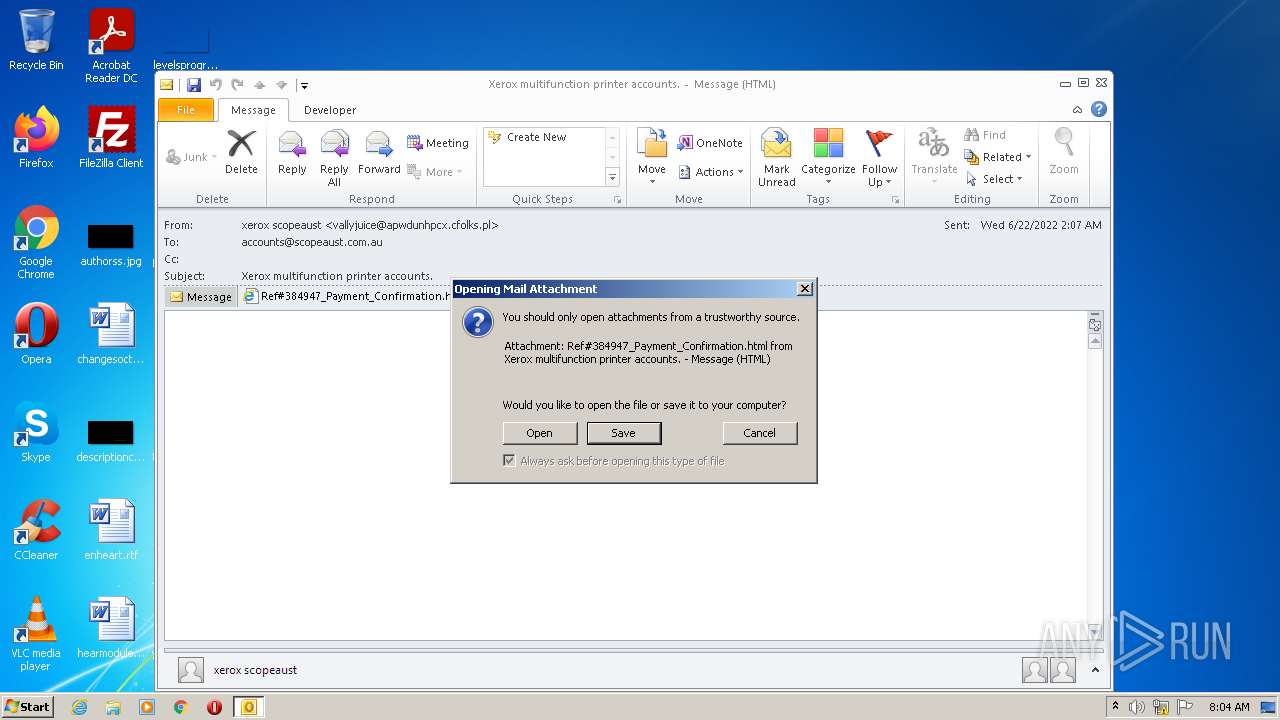
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1928)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 888)
INFO
Checks supported languages
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 888)
Reads the computer name
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 888)
Application launched itself
- iexplore.exe (PID: 1964)
Changes internet zones settings
- iexplore.exe (PID: 1964)
Reads internet explorer settings
- iexplore.exe (PID: 888)
Checks Windows Trust Settings
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 888)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1964)
Reads settings of System Certificates
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 888)
Creates files in the user directory
- iexplore.exe (PID: 888)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
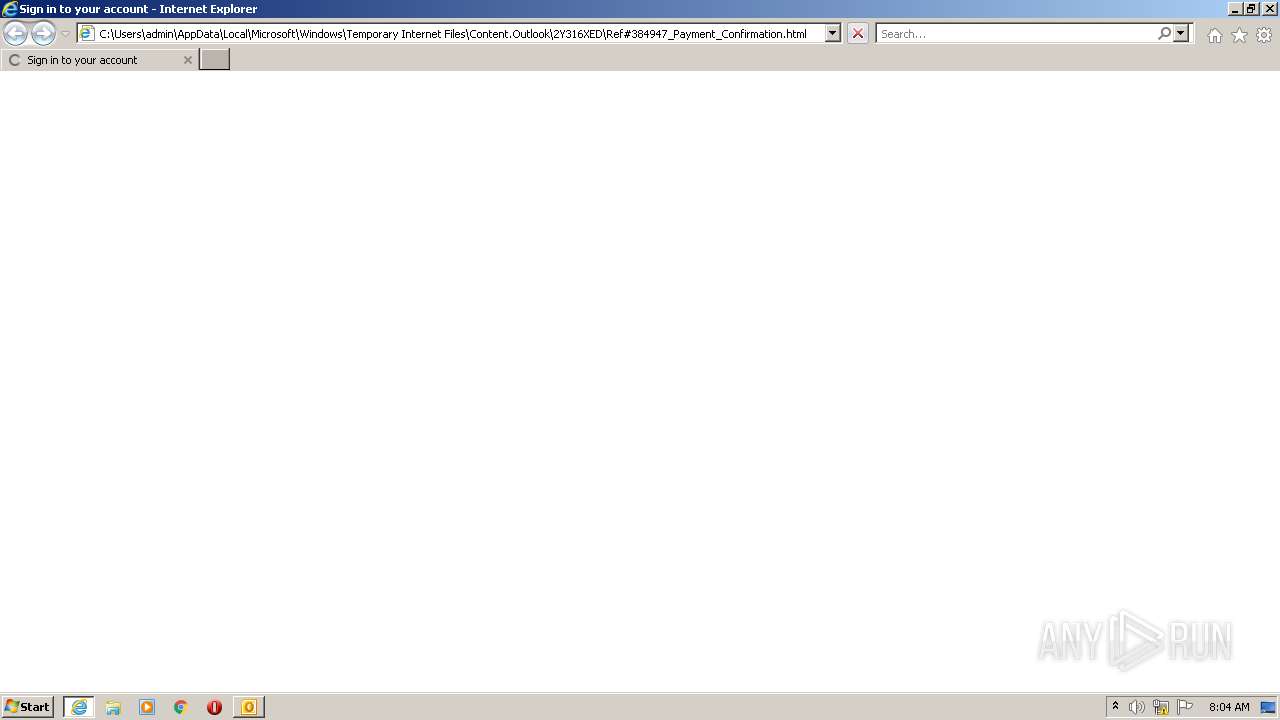
| 888 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1964 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1928 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\6e6b16de-7b88-4929-868d-08da53eb8024_d57630f1-fd39-1b31-860b-e792f55786d2.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
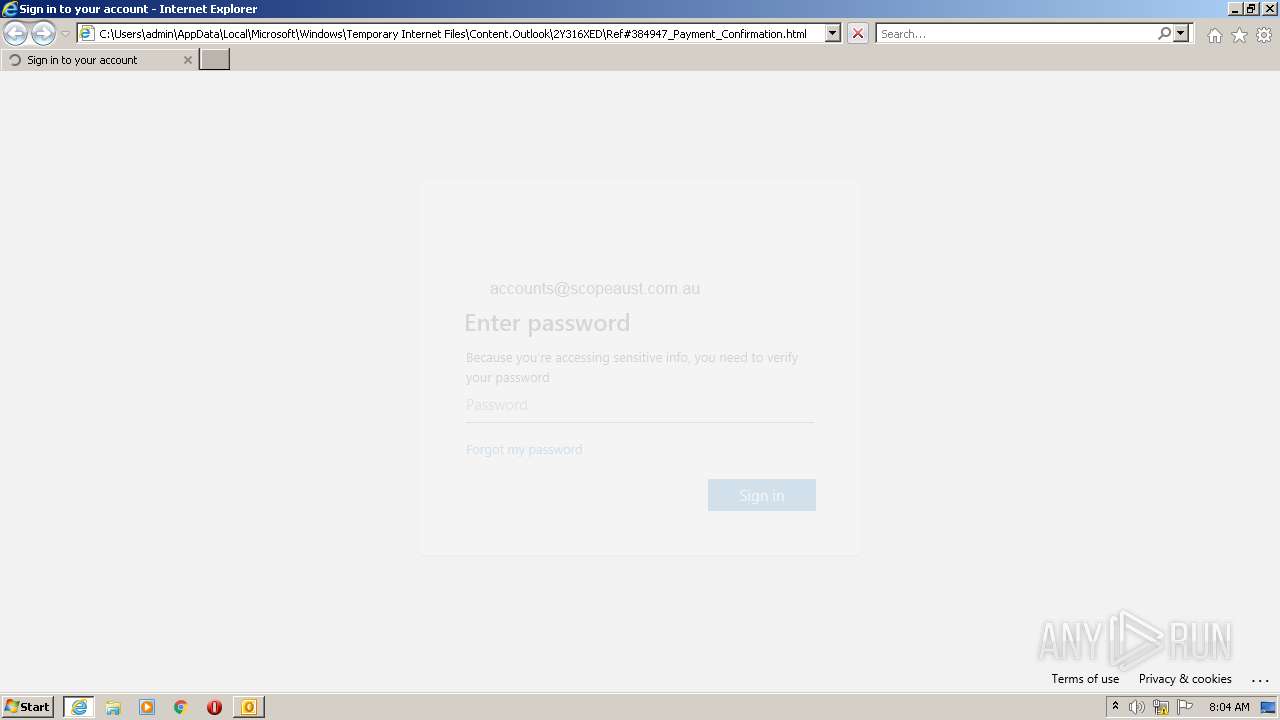
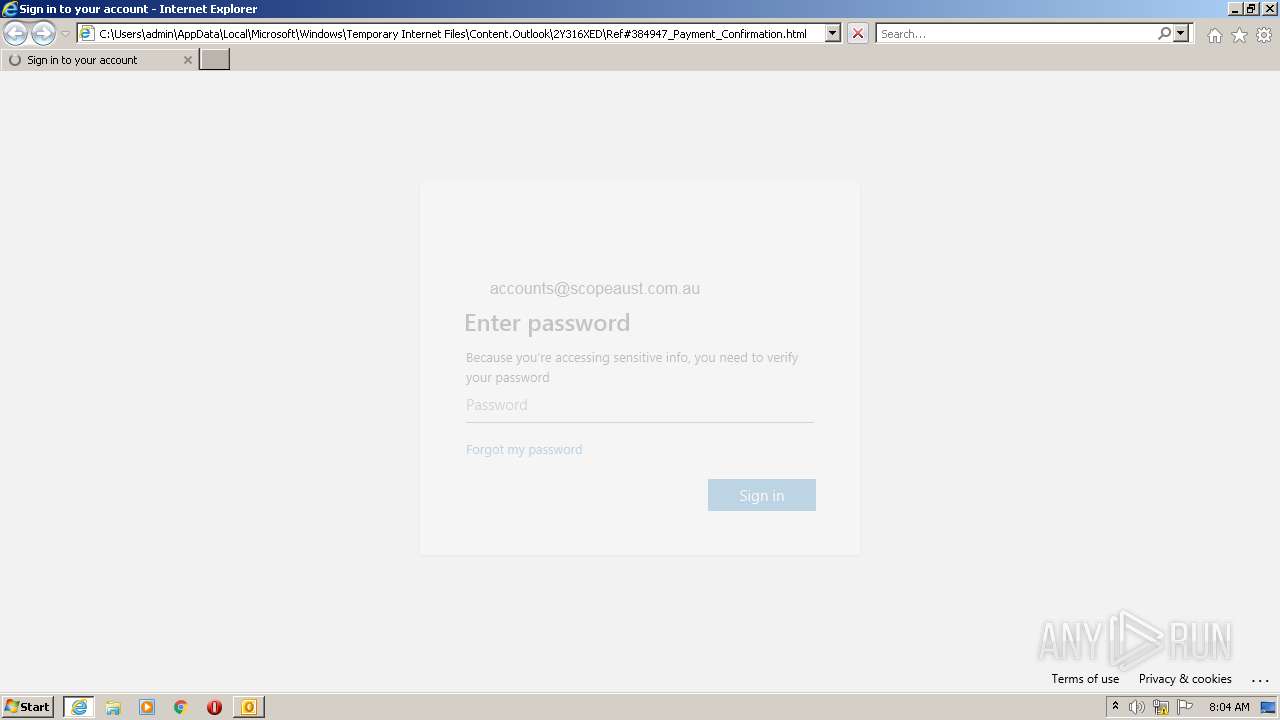
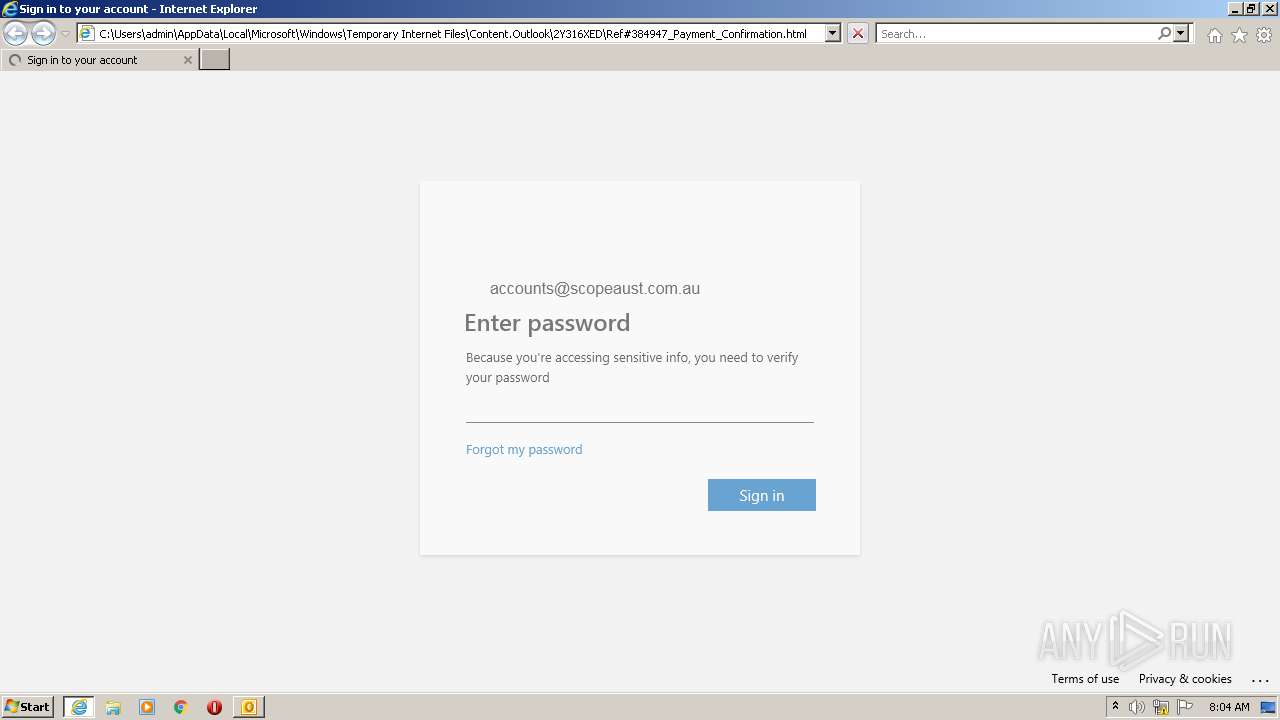
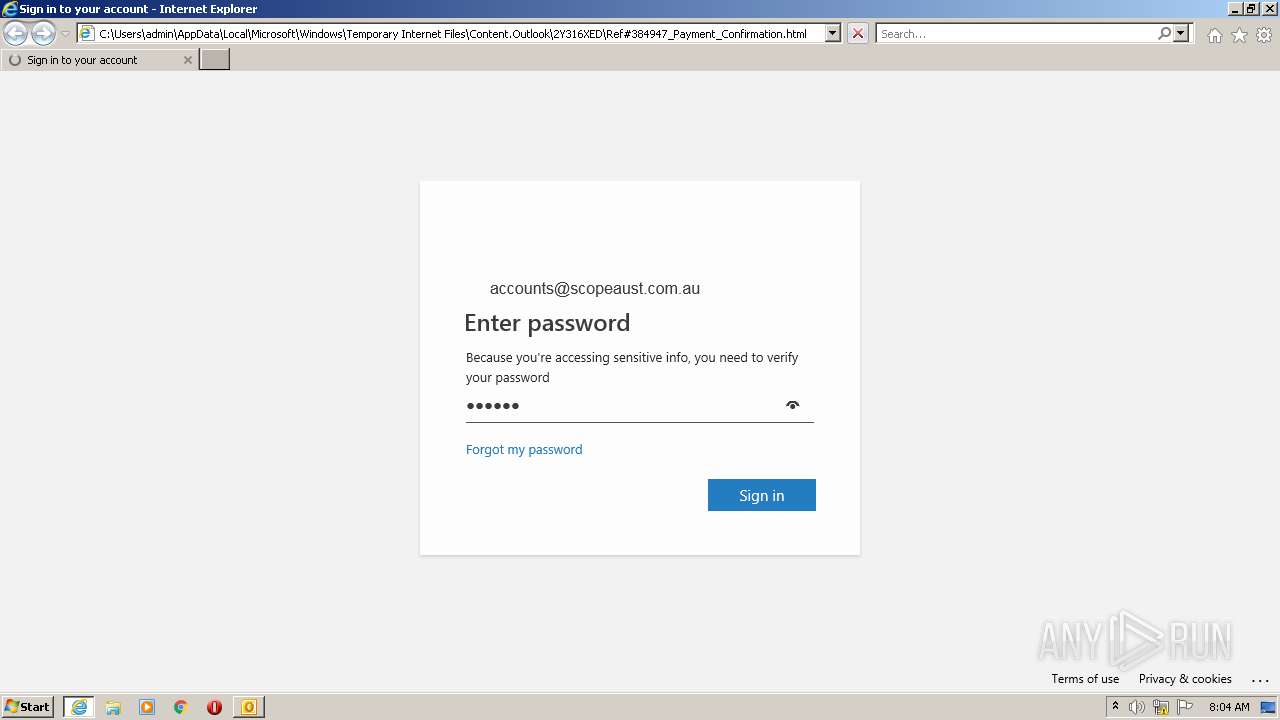
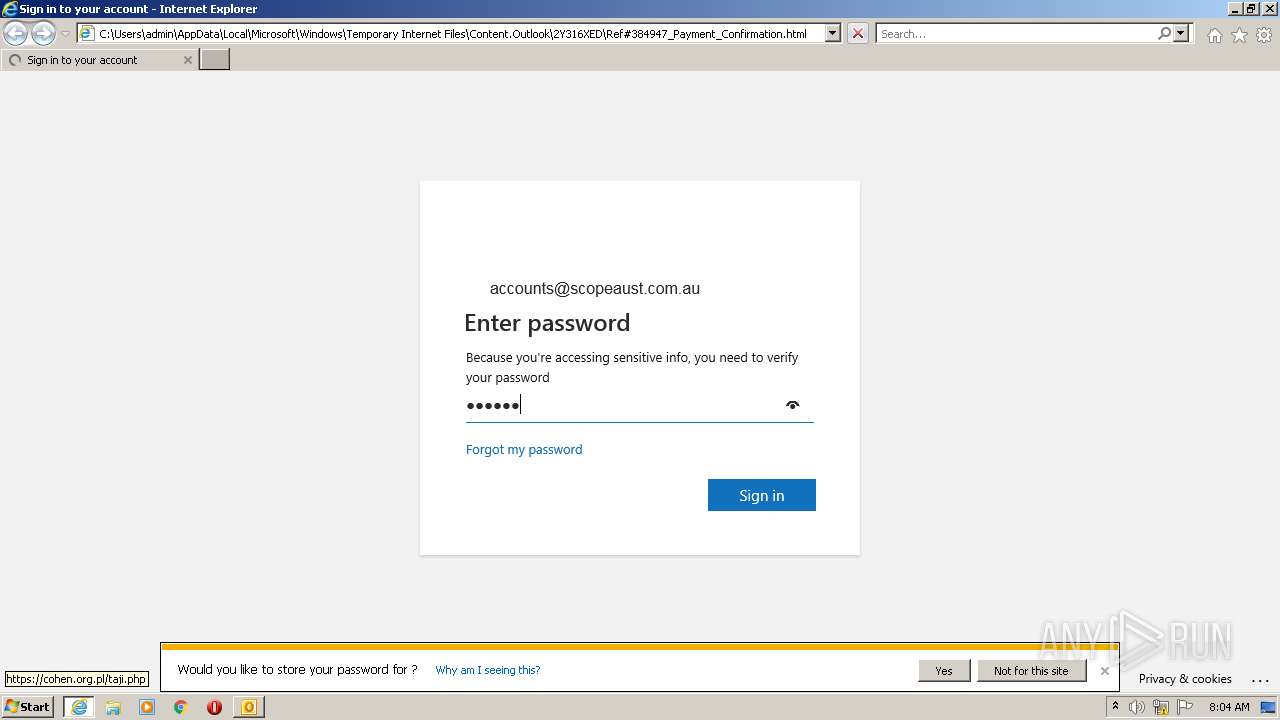
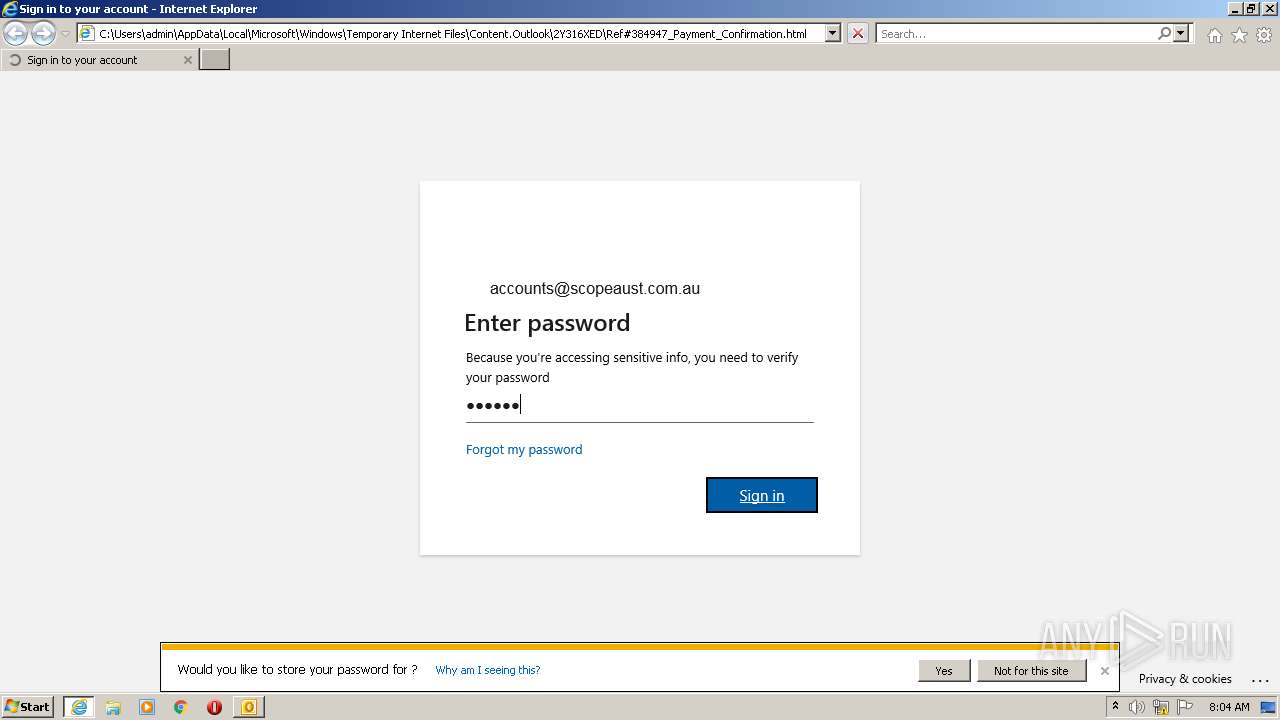
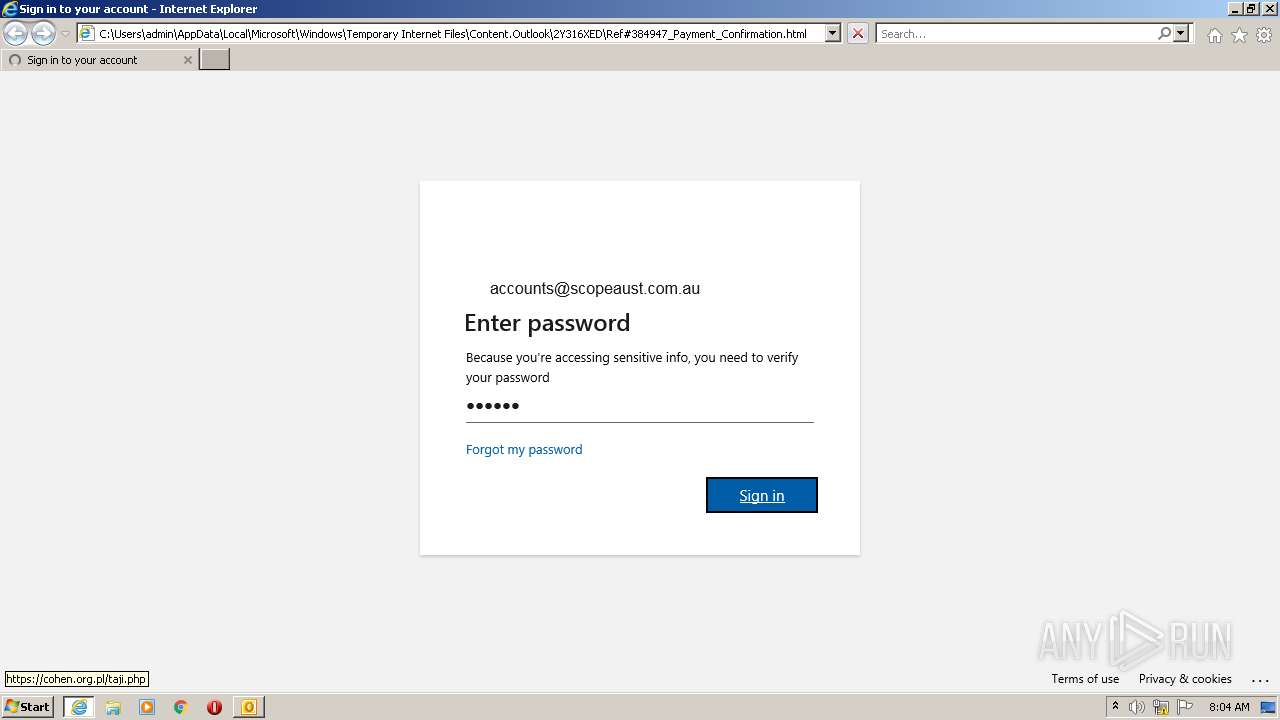
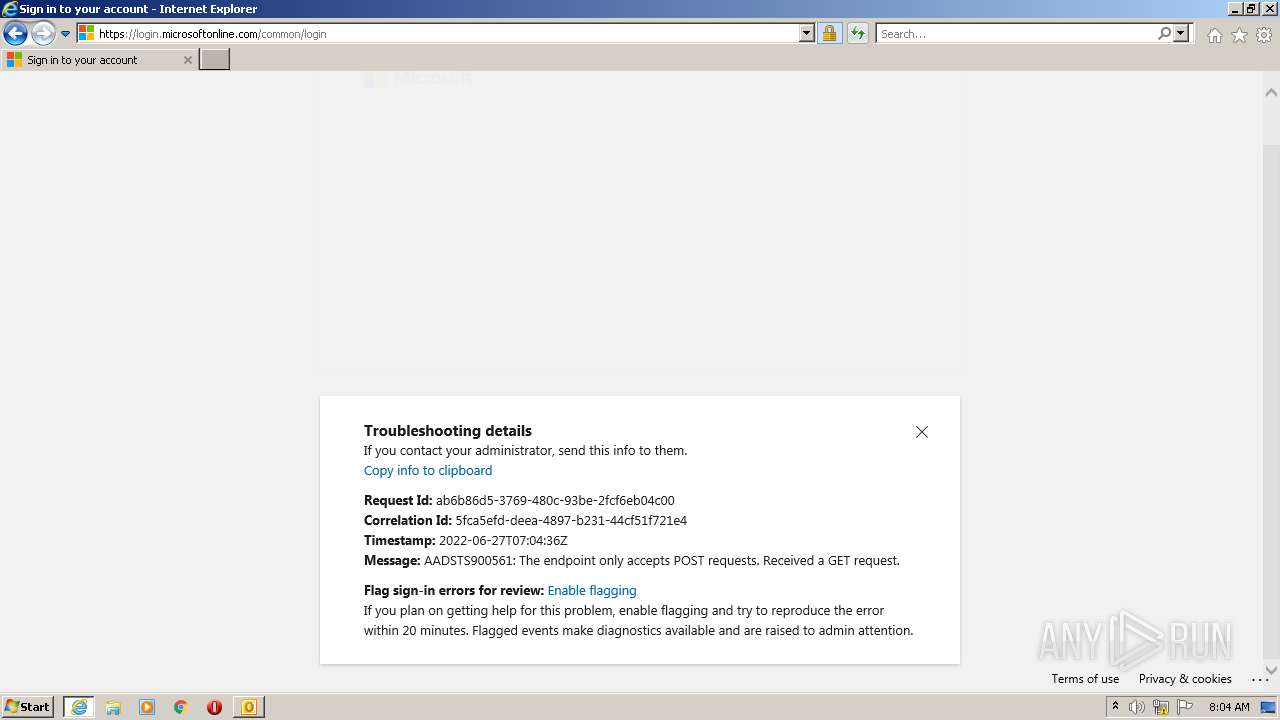
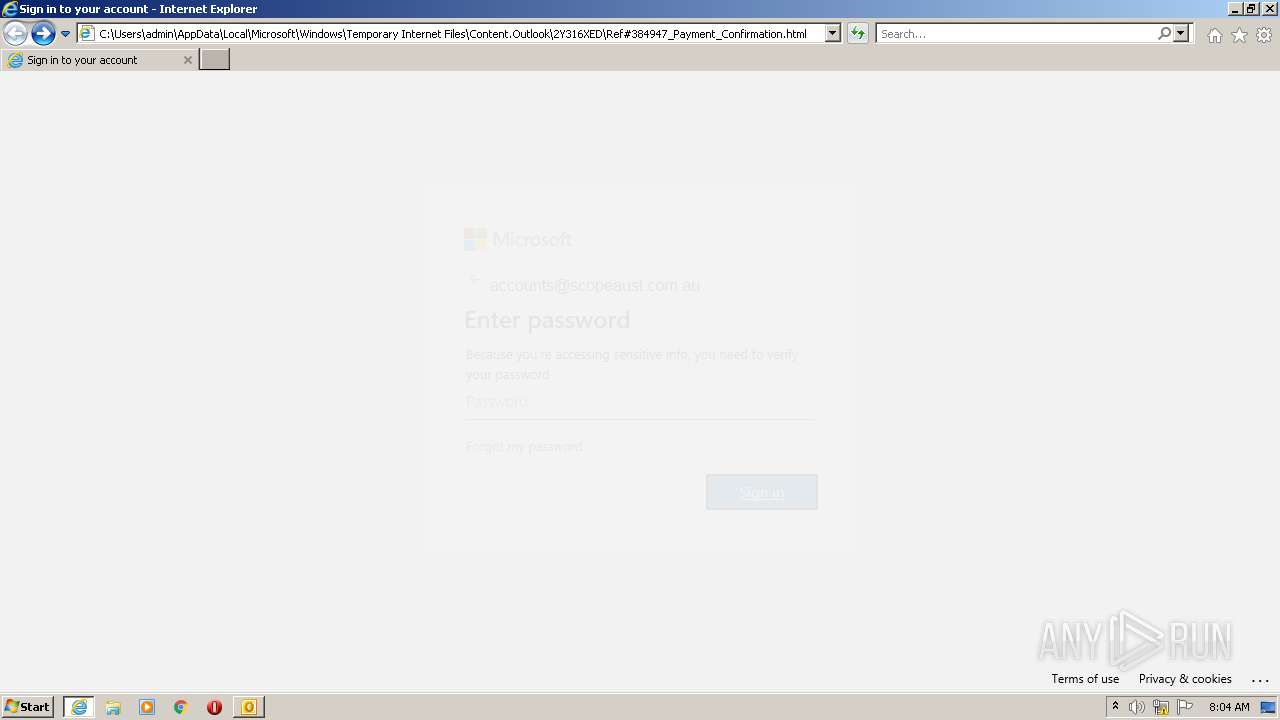
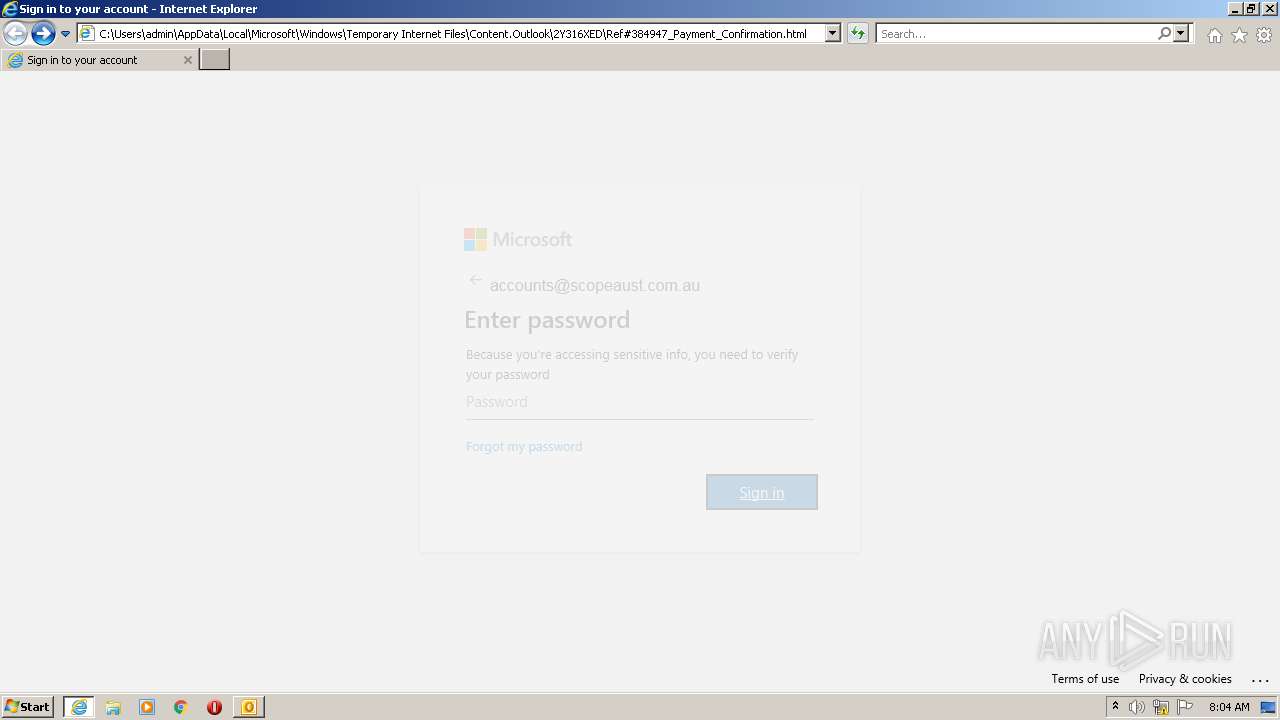
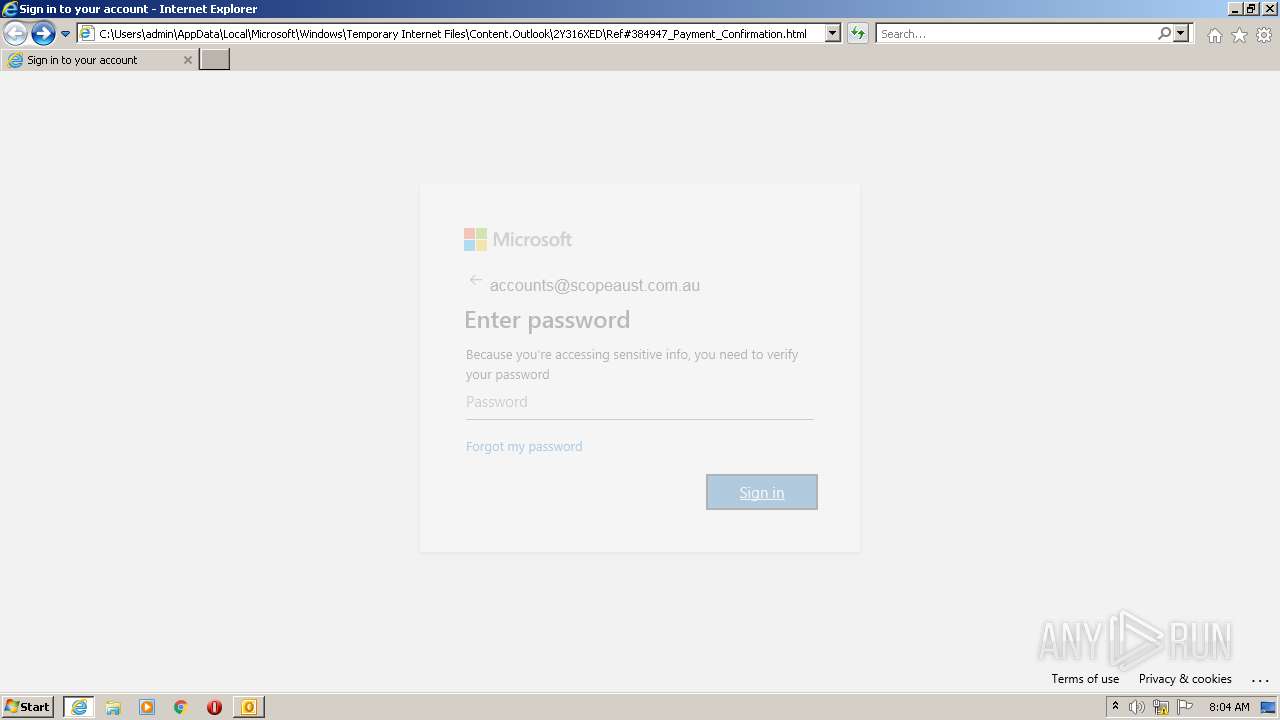
| 1964 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\2Y316XED\Ref#384947_Payment_Confirmation.html | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 021
Read events
18 307
Write events
694
Delete events
20
Modification events
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
10
Text files
35
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9136.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1928 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1928 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp92BD.tmp | html | |
MD5:— | SHA256:— | |||
| 1928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\2Y316XED\Ref#384947_Payment_Confirmation.html | html | |
MD5:— | SHA256:— | |||
| 888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\2Y316XED\Ref#384947_Payment_Confirmation (2).html | html | |
MD5:— | SHA256:— | |||
| 888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
38
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
888 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
888 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
888 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
888 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMCpKC%2BcP0uPPKD6eA%2Fhu%2F4XQ%3D%3D | unknown | der | 503 b | shared |
1964 | iexplore.exe | GET | 200 | 8.252.73.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e9887bdb0a0564b2 | US | compressed | 4.70 Kb | whitelisted |
1964 | iexplore.exe | GET | 200 | 8.252.73.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?62b1254740bd738a | US | compressed | 4.70 Kb | whitelisted |
888 | iexplore.exe | GET | 200 | 8.252.73.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?140e2bd8ee61cb44 | US | compressed | 4.70 Kb | whitelisted |
888 | iexplore.exe | GET | 200 | 23.45.105.185:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
1964 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 69.16.175.42:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
1928 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
888 | iexplore.exe | 69.16.175.10:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
888 | iexplore.exe | 8.252.73.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1964 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1964 | iexplore.exe | 8.252.73.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1964 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
888 | iexplore.exe | 2.16.186.11:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
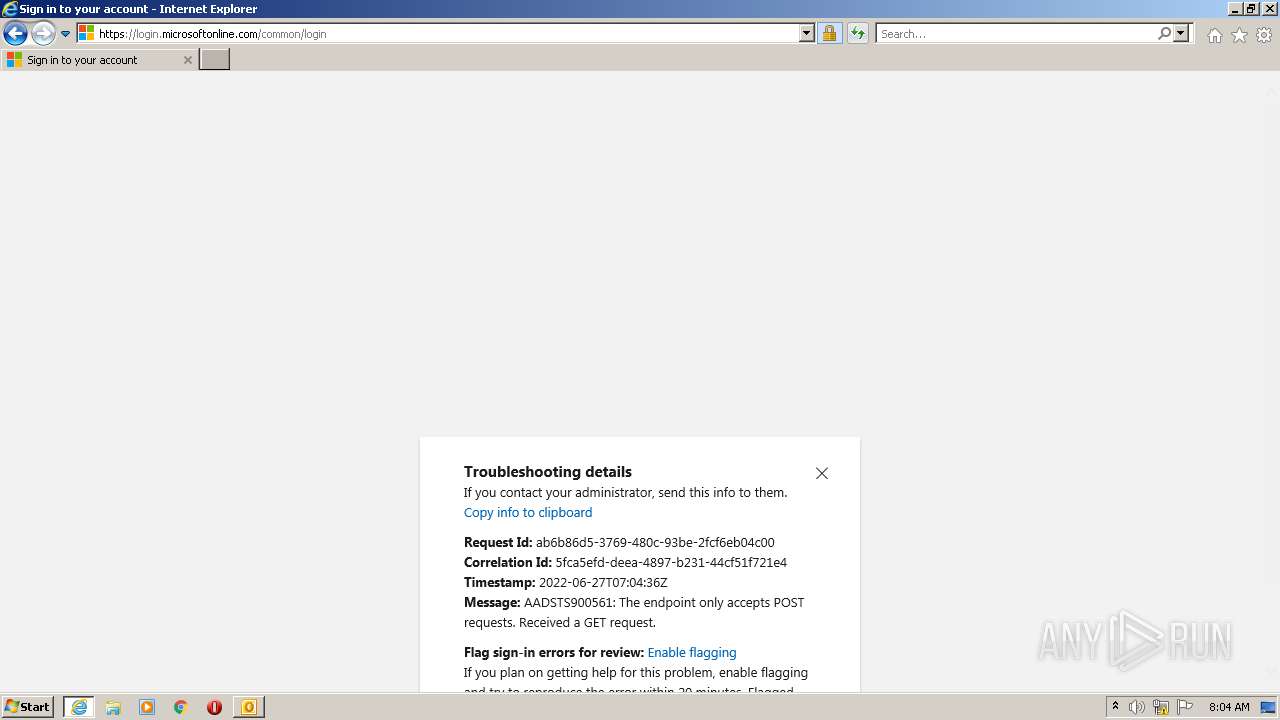
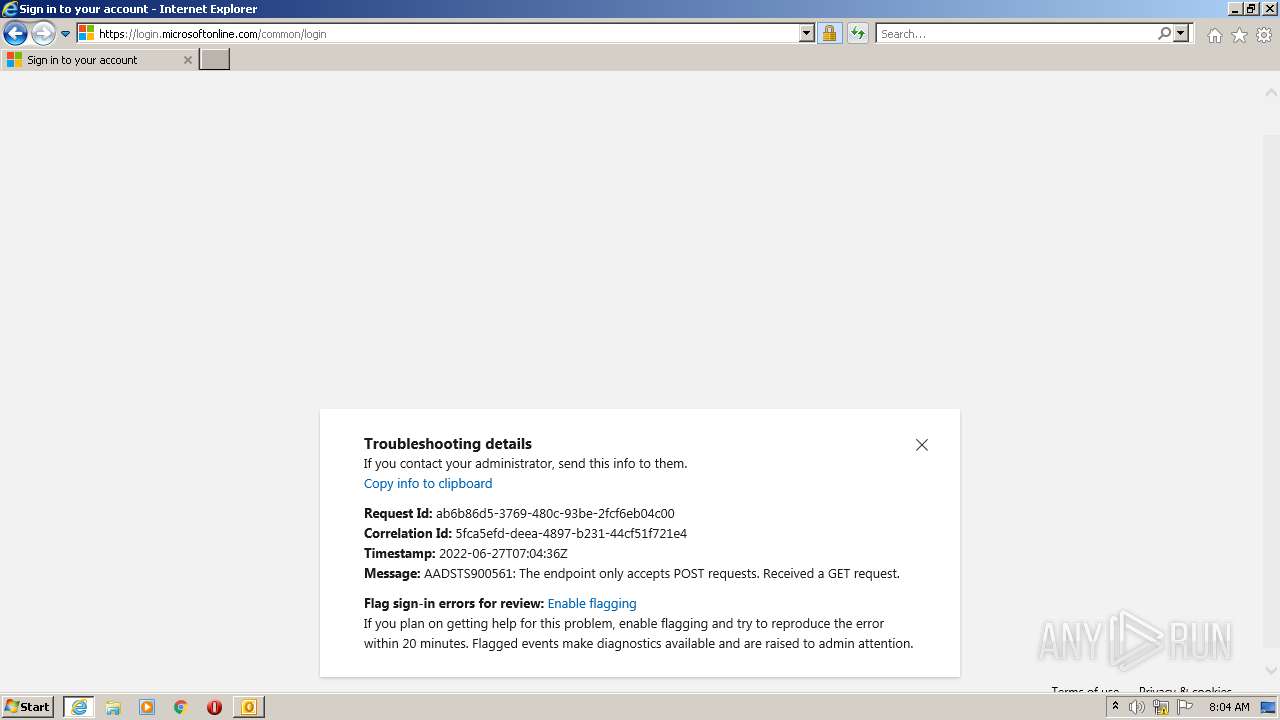
888 | iexplore.exe | 40.126.32.76:443 | login.microsoftonline.com | Microsoft Corporation | US | whitelisted |
1964 | iexplore.exe | 13.107.219.45:443 | aadcdn.msauth.net | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
code.jquery.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
aadcdn.msftauth.net |
| whitelisted |
crl3.digicert.com |
| whitelisted |