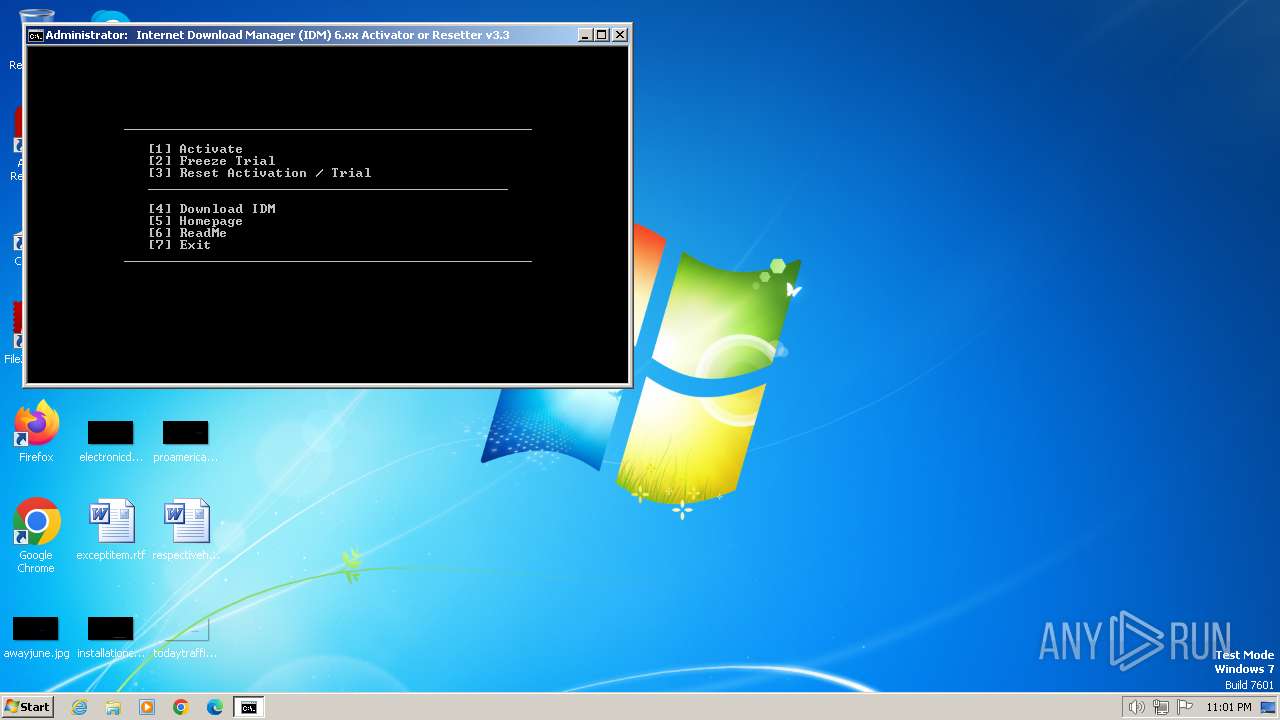
| File name: | IDM 6.xx Activator or Resetter v3.3.exe |
| Full analysis: | https://app.any.run/tasks/87234c6f-97ce-4d34-a3b8-985bf4b18f87 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2024, 22:00:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B2BB695B656DFB91E01967DE3A8BEEE3 |
| SHA1: | 30EBAC4EB84AA036BED8F8931B6493348B87108A |
| SHA256: | 7822FA6C35CBD1CFB95C780970DEEF14D8B53C62ADE3A4BCF63C494C3F2E5BBD |
| SSDEEP: | 24576:Kq2RNiQQlO14bmK/v5TX5di5mRU7sPU/R+w01DepD:Kf/iQQlO14bmK/v5TX5di5mRU7sPU/RJ |
MALICIOUS
Drops the executable file immediately after the start
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
- 7za.exe (PID: 1740)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
Reads security settings of Internet Explorer
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
Executing commands from a ".bat" file
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 956)
Reads the Internet Settings
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
- cmd.exe (PID: 1572)
Starts CMD.EXE for commands execution
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
- cmd.exe (PID: 1572)
The executable file from the user directory is run by the CMD process
- 7za.exe (PID: 2440)
- 7za.exe (PID: 696)
- 7za.exe (PID: 1740)
- 7za.exe (PID: 2184)
- 7za.exe (PID: 3508)
- NSudo86x.exe (PID: 1220)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1572)
Starts SC.EXE for service management
- cmd.exe (PID: 1572)
Application launched itself
- cmd.exe (PID: 1572)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3272)
- cmd.exe (PID: 1572)
Get information on the list of running processes
- cmd.exe (PID: 1572)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3084)
- cmd.exe (PID: 1572)
- cmd.exe (PID: 1608)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1572)
Hides command output
- cmd.exe (PID: 1608)
- cmd.exe (PID: 3272)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1572)
INFO
Checks supported languages
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
- 7za.exe (PID: 696)
- 7za.exe (PID: 2440)
- 7za.exe (PID: 1740)
- 7za.exe (PID: 3508)
- 7za.exe (PID: 2184)
- mode.com (PID: 3900)
- NSudo86x.exe (PID: 1220)
- mode.com (PID: 1172)
Reads the computer name
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
- 7za.exe (PID: 2440)
- 7za.exe (PID: 696)
- 7za.exe (PID: 1740)
- 7za.exe (PID: 2184)
- 7za.exe (PID: 3508)
- NSudo86x.exe (PID: 1220)
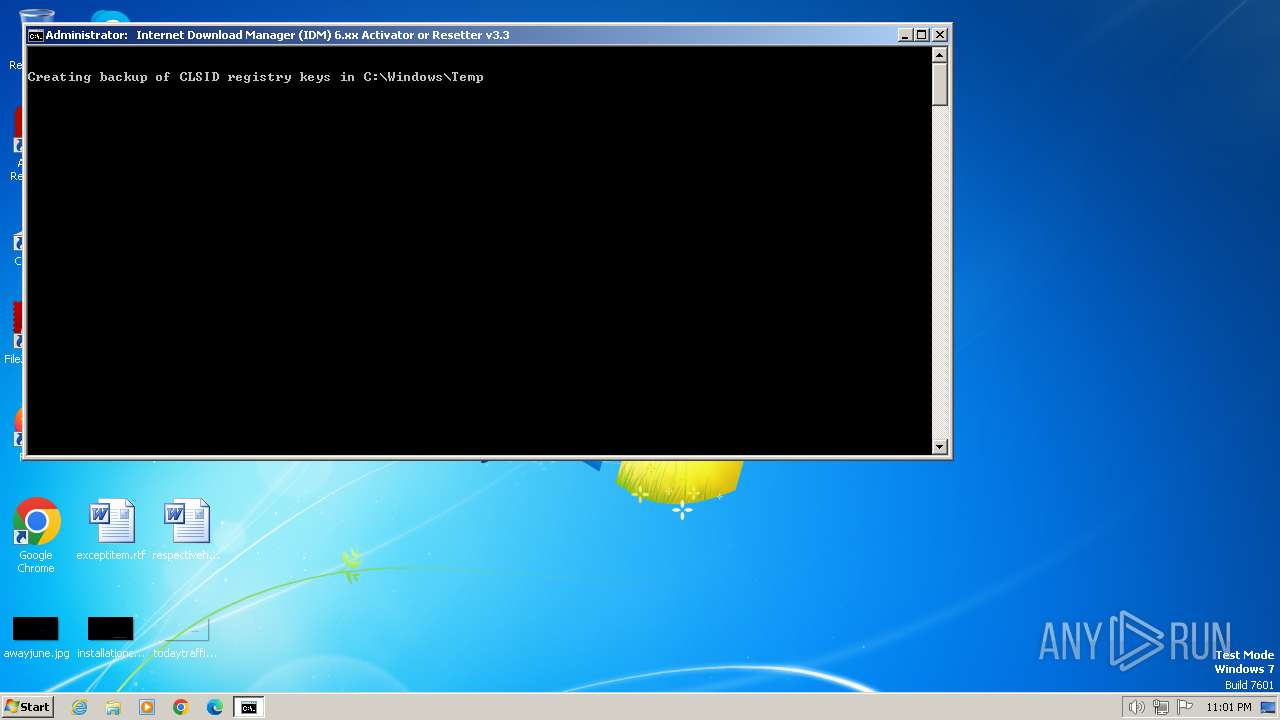
Create files in a temporary directory
- IDM 6.xx Activator or Resetter v3.3.exe (PID: 2420)
- 7za.exe (PID: 696)
- 7za.exe (PID: 2440)
- 7za.exe (PID: 1740)
- reg.exe (PID: 3376)
Checks operating system version
- cmd.exe (PID: 1572)
Application launched itself
- msedge.exe (PID: 2840)
- msedge.exe (PID: 2372)
Manual execution by a user
- msedge.exe (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:06:27 07:06:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 70656 |
| InitializedDataSize: | 110080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11def |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.0.0 |
| ProductVersionNumber: | 3.3.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | IDM 6.xx Activator or Resetter - CrackingCity.com |
| CompanyName: | CrackingCity.com |
| FileDescription: | IDM 6.xx Activator or Resetter |
| FileVersion: | 3.3.0.0 |
| InternalName: | IDM 6.xx Activator or Resetter.exe |
| LegalCopyright: | CrackingCity.com, Copyright © 2020 - 2024 |
| OriginalFileName: | IDM 6.xx Activator or Resetter.exe |
| ProductName: | IDM 6.xx Activator or Resetter |
| ProductVersion: | 3.3.0.0 |
Total processes
133
Monitored processes
91
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | reg query HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\ytmp\IDM0.bat" " | C:\Windows\System32\cmd.exe | — | IDM 6.xx Activator or Resetter v3.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 548 | powershell.exe "&{$W=$Host.UI.RawUI.WindowSize;$B=$Host.UI.RawUI.BufferSize;$W.Height=34;$B.Height=300;$Host.UI.RawUI.WindowSize=$W;$Host.UI.RawUI.BufferSize=$B;}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 584 | choice /C:1234567 /N | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | findstr /i "idman.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | 7za e files.tmp -ptmp@tmp420 -aoa IDM0.bat | C:\Users\admin\AppData\Local\Temp\ytmp\7za.exe | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
| 712 | powershell.exe "Get-WmiObject -Class Win32_ComputerSystem | Select-Object -Property CreationClassName" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 920 | reg delete HKU\S-1-5-21-1302019708-1500728564-335382590-1000\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\ytmp\main.bat" " | C:\Windows\System32\cmd.exe | — | IDM 6.xx Activator or Resetter v3.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1196 --field-trial-handle=1268,i,8806871645212700284,7773158199159743734,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
30 926
Read events
30 862
Write events
55
Delete events
9
Modification events
| (PID) Process: | (2420) IDM 6.xx Activator or Resetter v3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2420) IDM 6.xx Activator or Resetter v3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2420) IDM 6.xx Activator or Resetter v3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2420) IDM 6.xx Activator or Resetter v3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3252) reg.exe | Key: | HKEY_CURRENT_USER\IAS_TEST |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3192) reg.exe | Key: | HKEY_CLASSES_ROOT\CLSID\IAS_TEST |
| Operation: | delete key | Name: | (default) |
Value: | |||
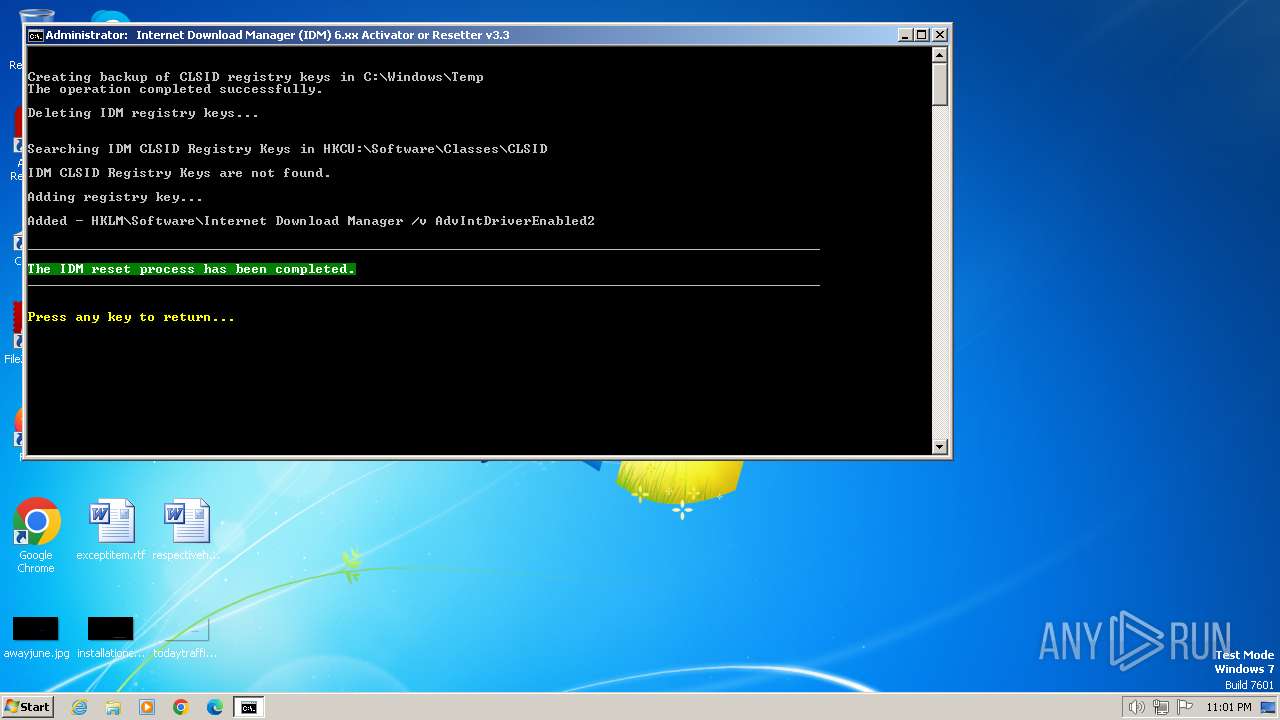
| (PID) Process: | (2360) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | AdvIntDriverEnabled2 |
Value: 1 | |||
| (PID) Process: | (2840) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2840) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2840) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
Executable files
7
Suspicious files
16
Text files
48
Unknown types
96
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | IDM 6.xx Activator or Resetter v3.3.exe | C:\Users\admin\AppData\Local\Temp\ytmp\files.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | IDM 6.xx Activator or Resetter v3.3.exe | C:\Users\admin\AppData\Local\Temp\ytmp\main.bat | text | |
MD5:— | SHA256:— | |||
| 2420 | IDM 6.xx Activator or Resetter v3.3.exe | C:\Users\admin\AppData\Local\Temp\ytmp\7za.exe | executable | |
MD5:— | SHA256:— | |||
| 696 | 7za.exe | C:\Users\admin\AppData\Local\Temp\ytmp\IDM0.bat | text | |
MD5:— | SHA256:— | |||
| 2440 | 7za.exe | C:\Users\admin\AppData\Local\Temp\ytmp\IDM.bat | text | |
MD5:— | SHA256:— | |||
| 1740 | 7za.exe | C:\Users\admin\AppData\Local\Temp\ytmp\NSudo86x.exe | executable | |
MD5:— | SHA256:— | |||
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\v4efjjjc.zu5.ps1 | binary | |
MD5:— | SHA256:— | |||
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\yi2pw1ku.0sn.psm1 | binary | |
MD5:— | SHA256:— | |||
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:— | SHA256:— | |||
| 712 | powershell.exe | C:\Users\admin\AppData\Local\Temp\e3fcxkpf.0x2.ps1 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
32
DNS requests
46
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2372 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2388 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
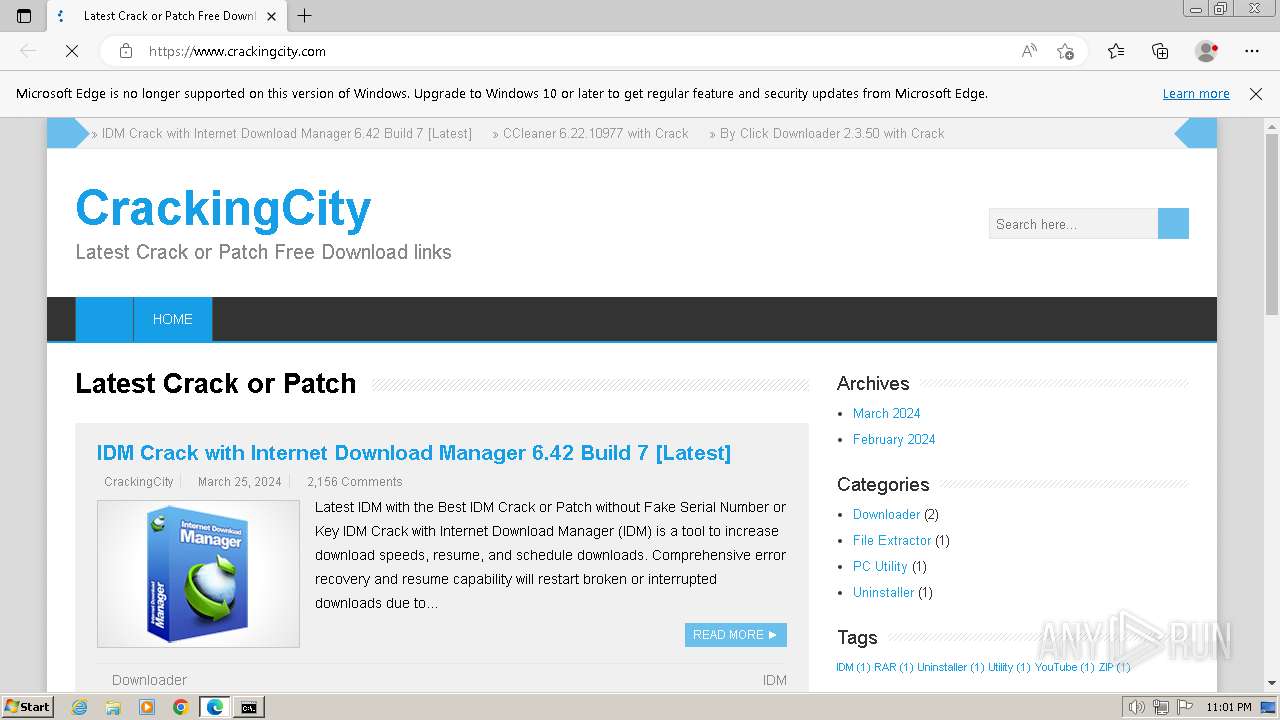
2388 | msedge.exe | 188.114.97.3:443 | www.crackingcity.com | CLOUDFLARENET | NL | unknown |
2388 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2388 | msedge.exe | 142.250.186.74:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
2388 | msedge.exe | 142.250.74.202:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
www.crackingcity.com |
| unknown |
edge.microsoft.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
i0.wp.com |
| whitelisted |
c0.wp.com |
| whitelisted |
stats.wp.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |