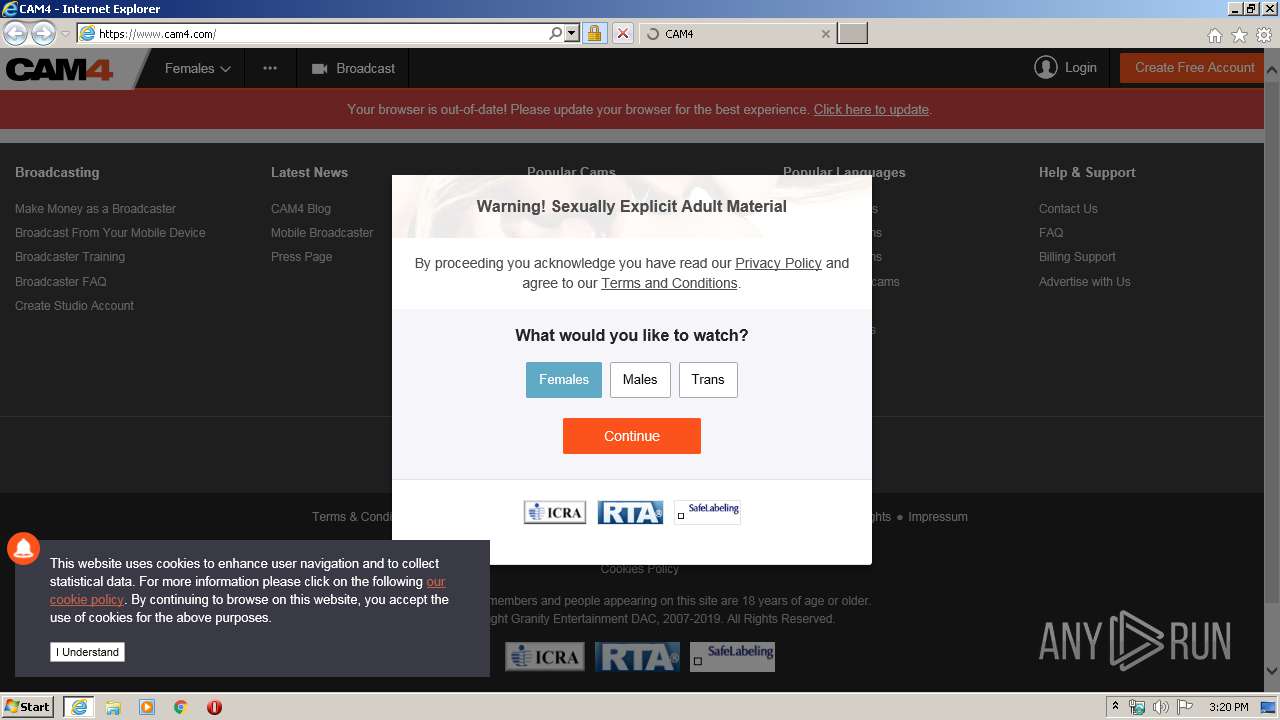
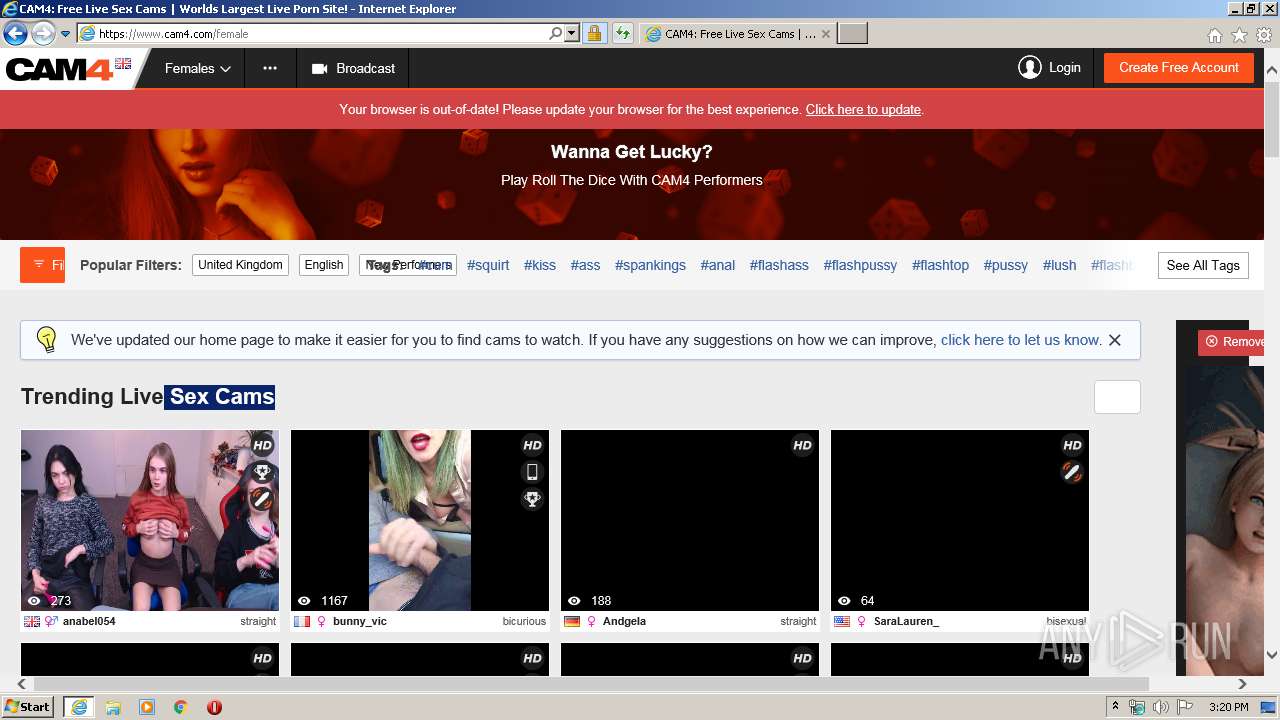
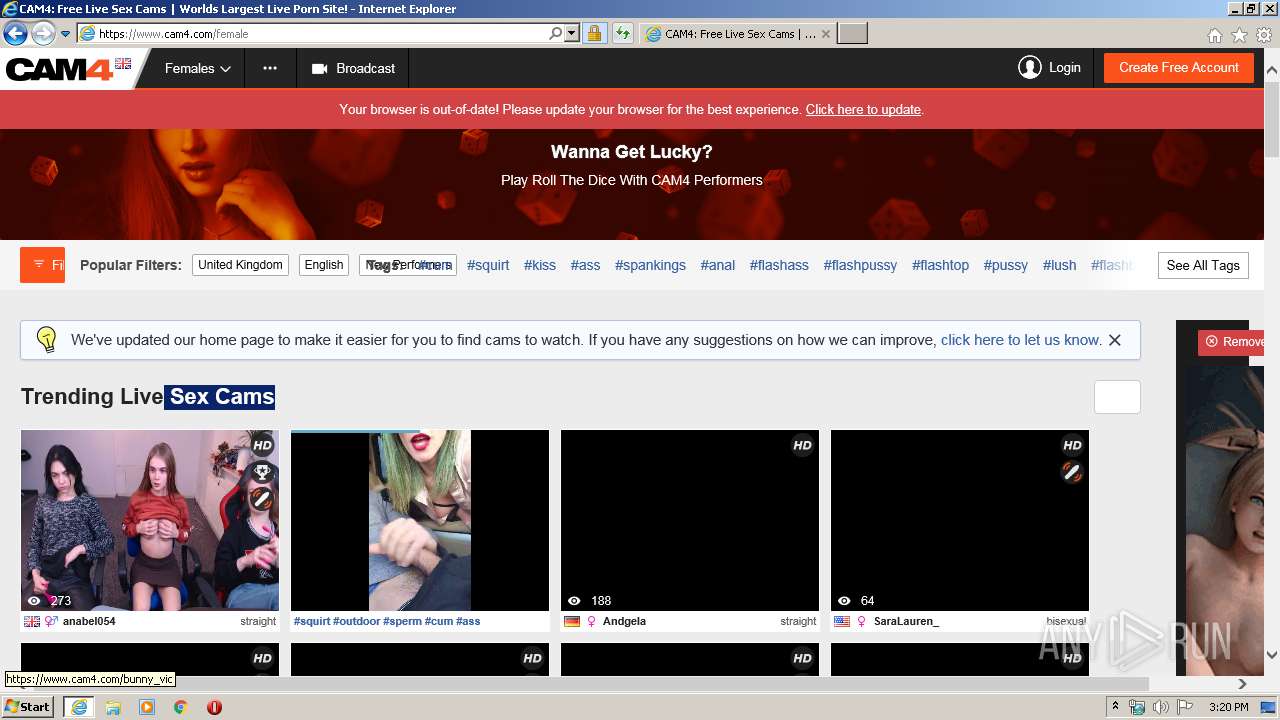
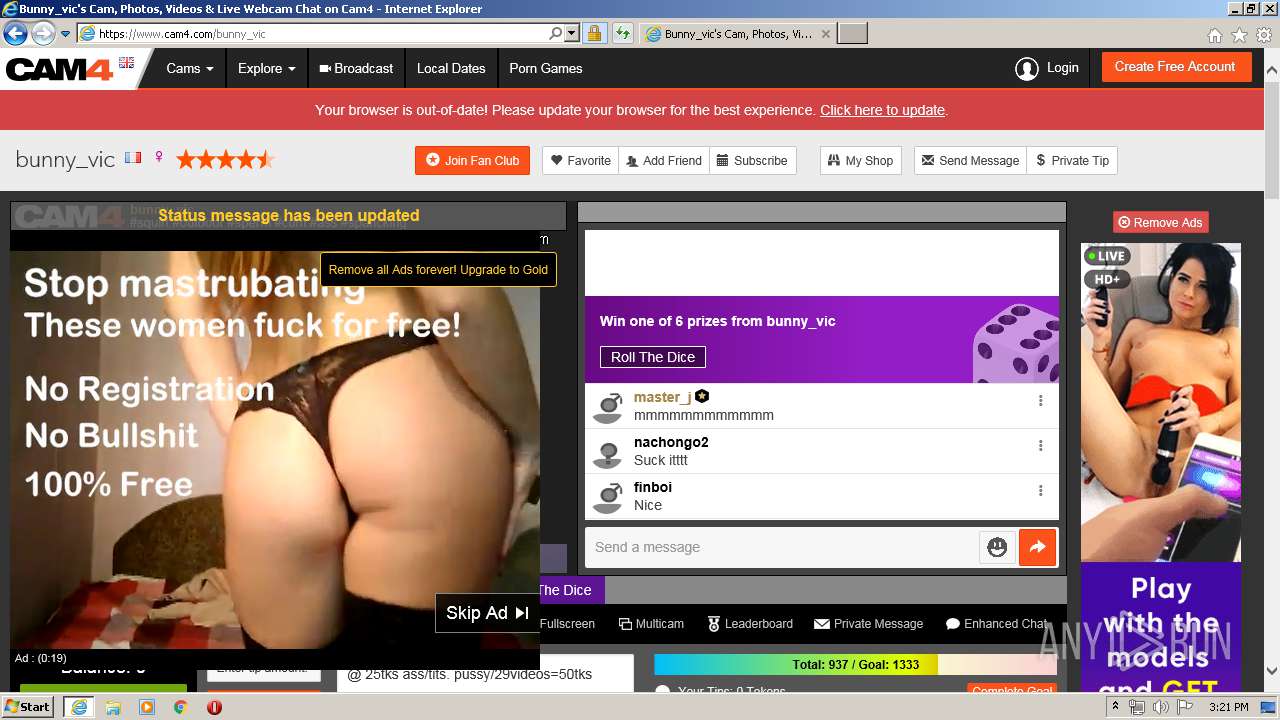
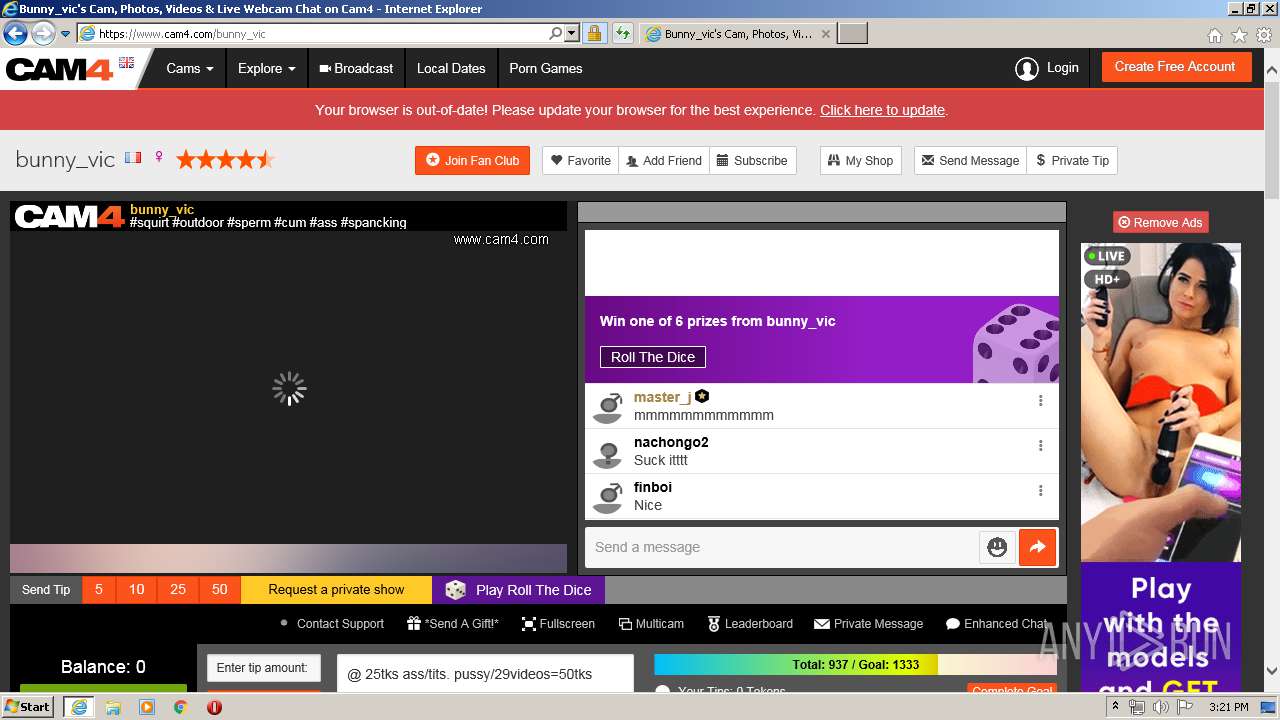
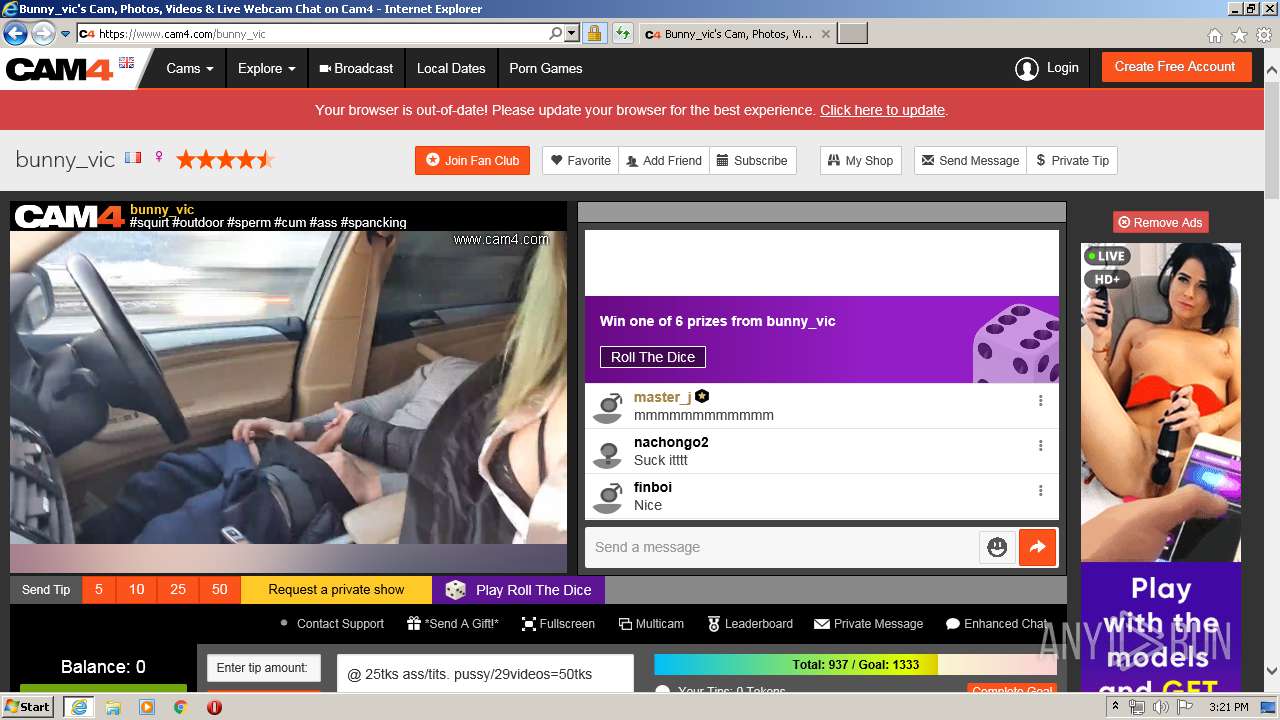
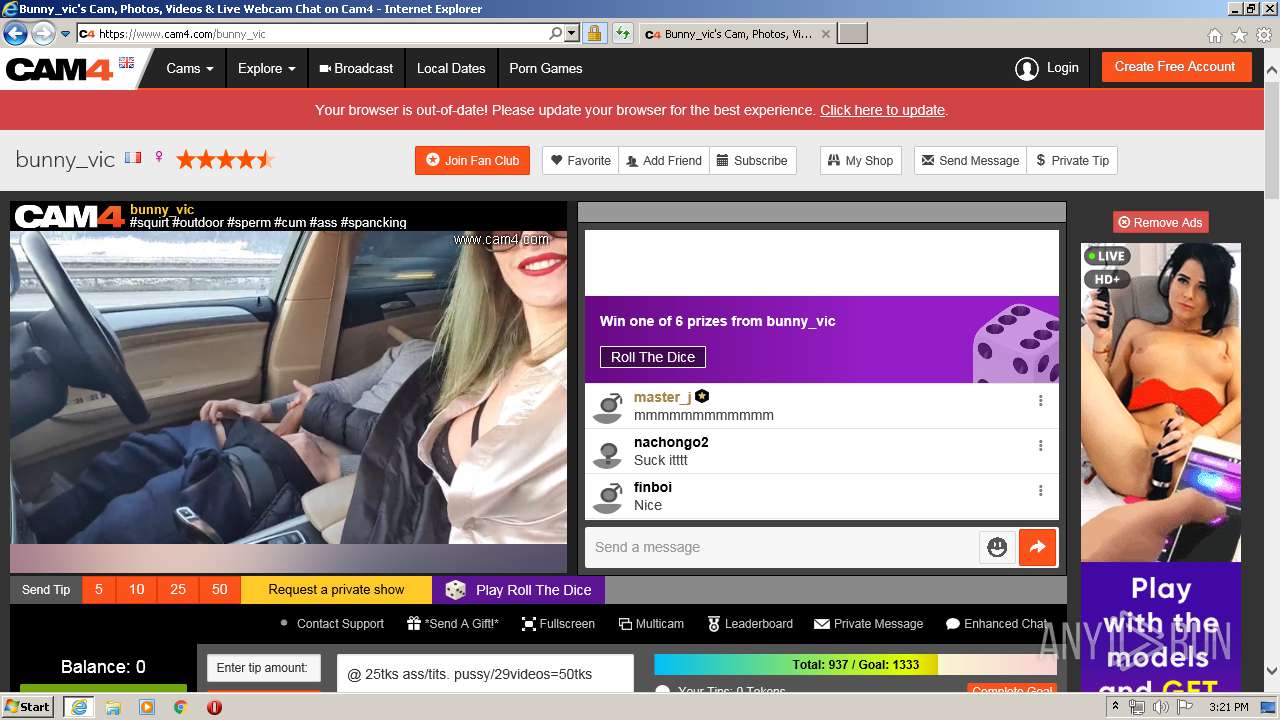
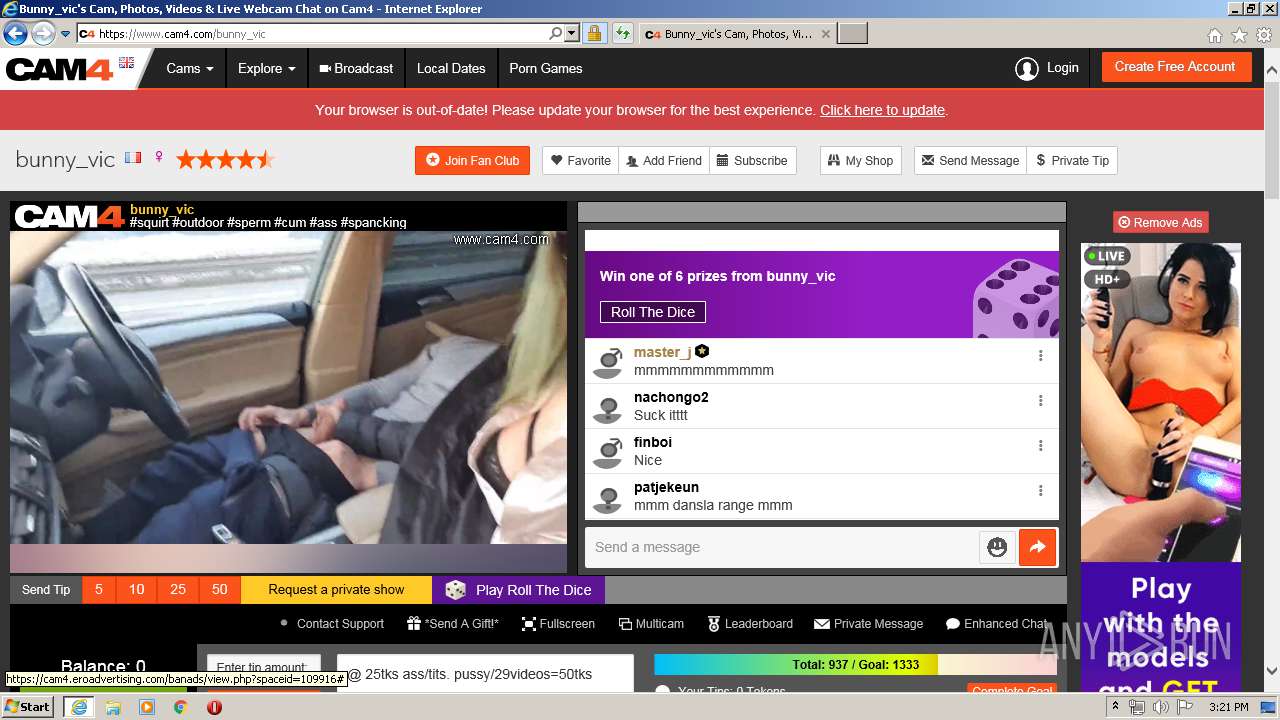
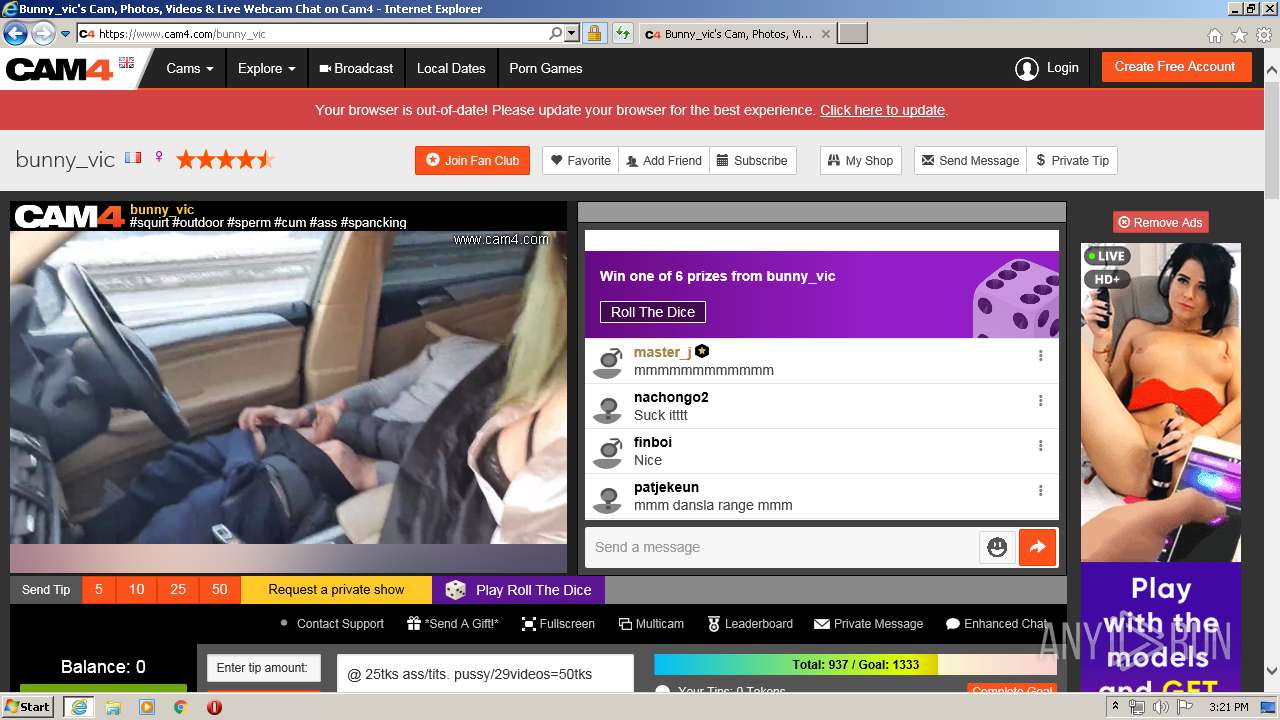
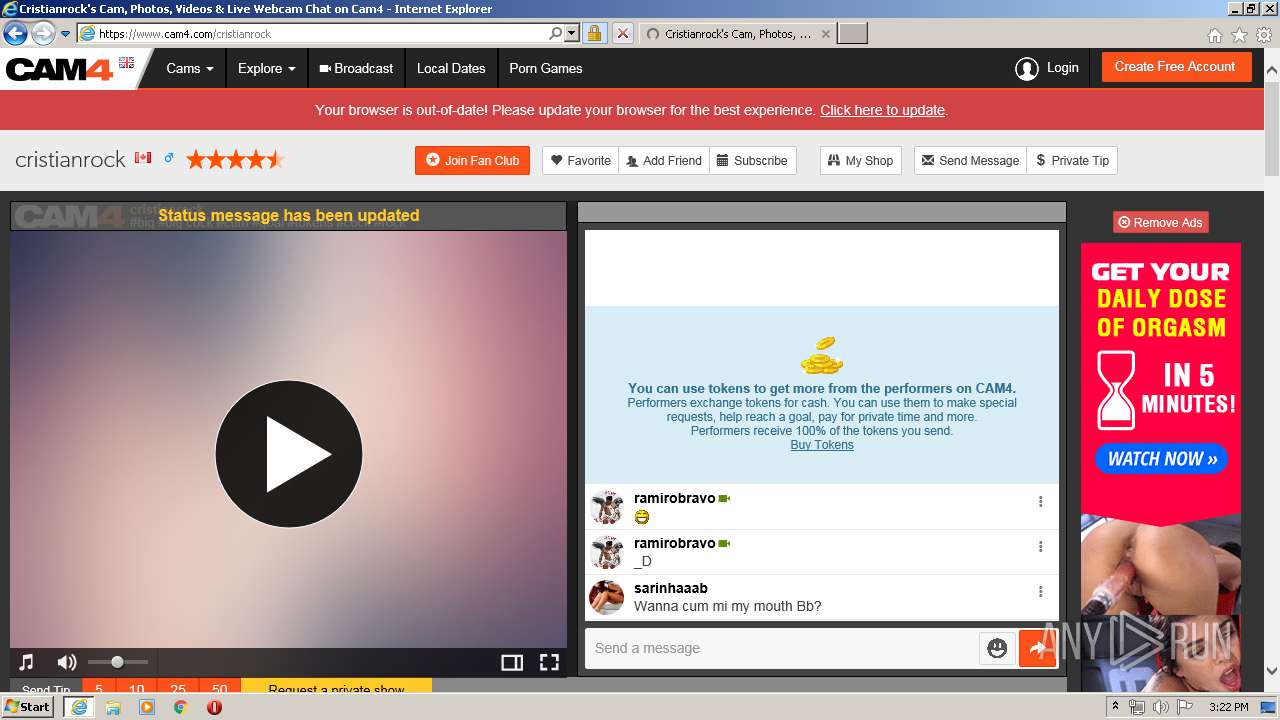
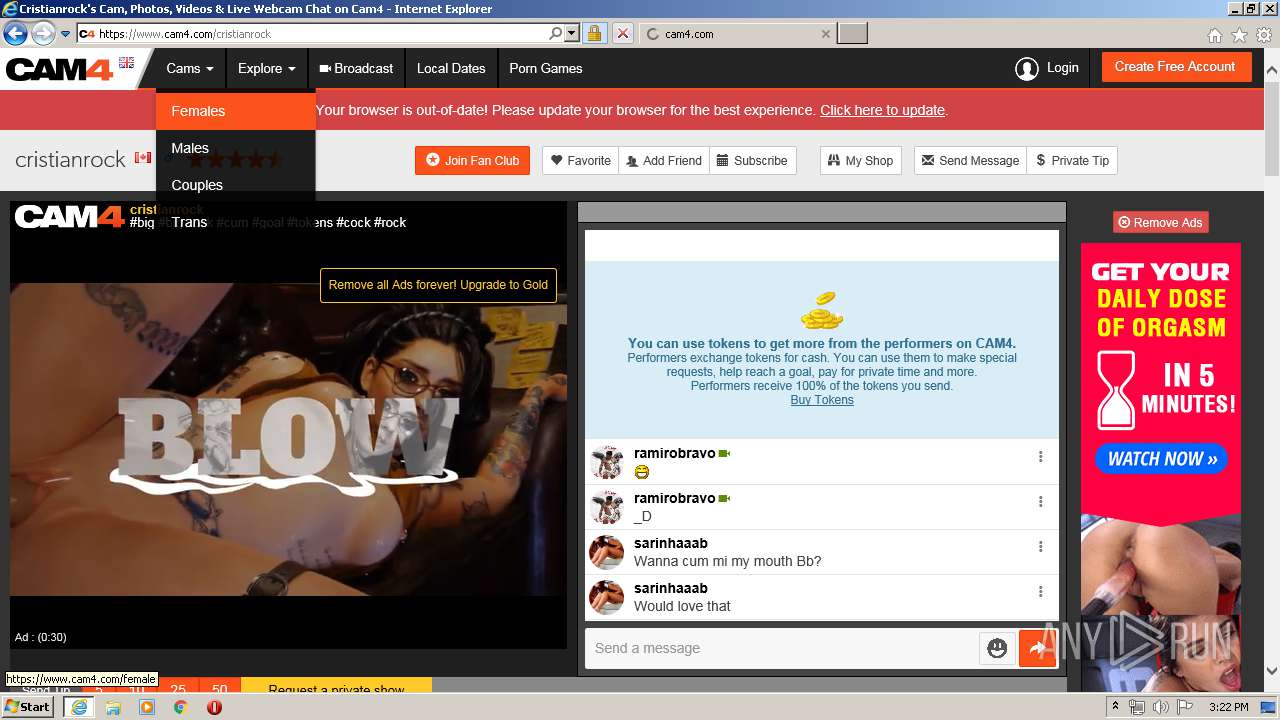
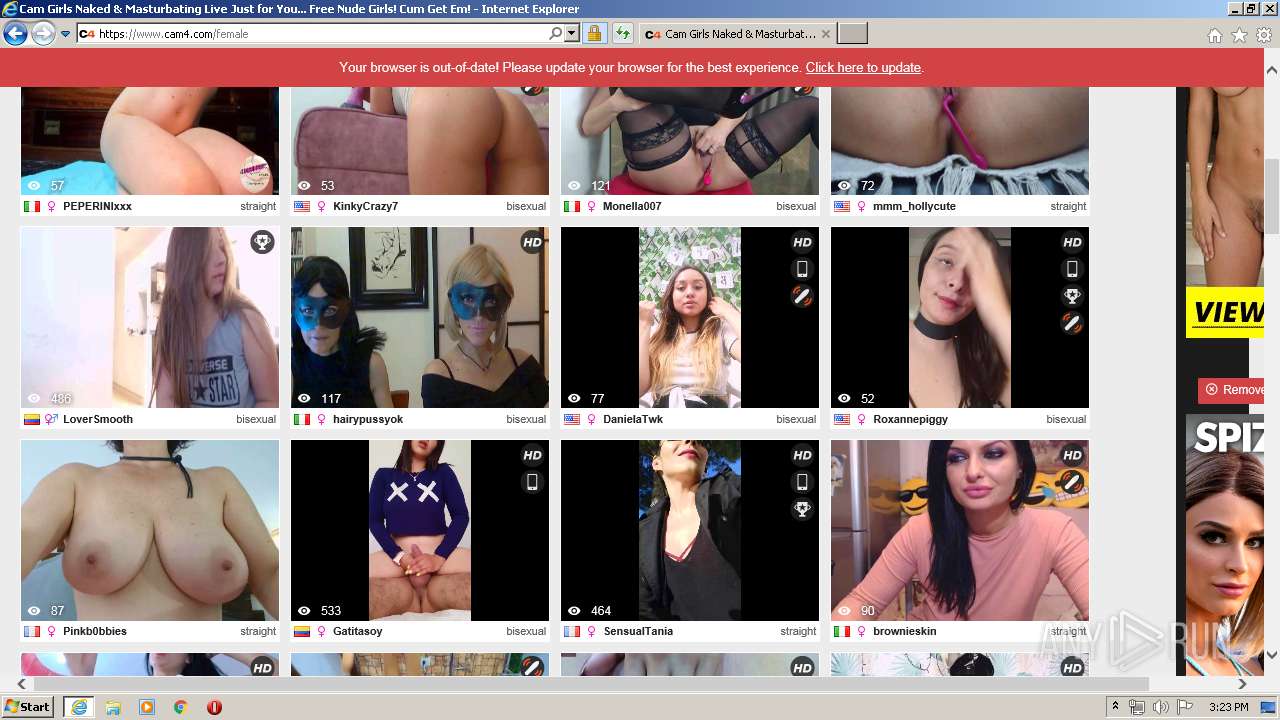
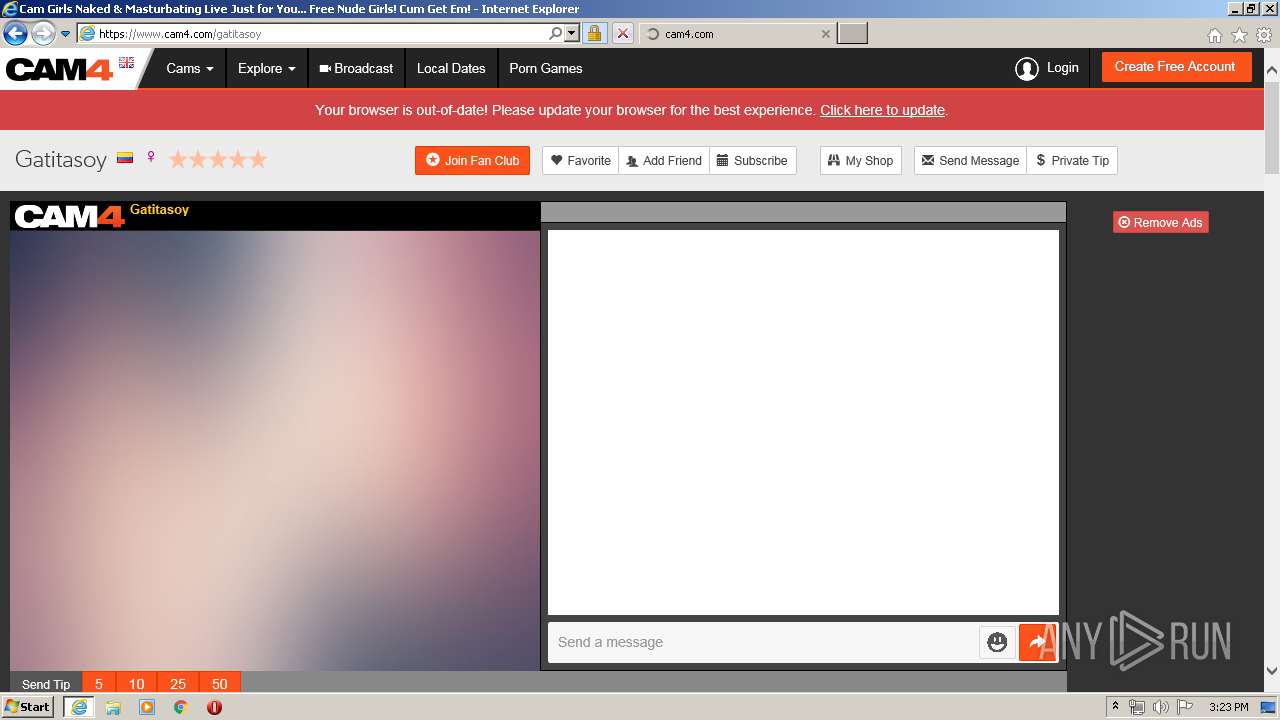
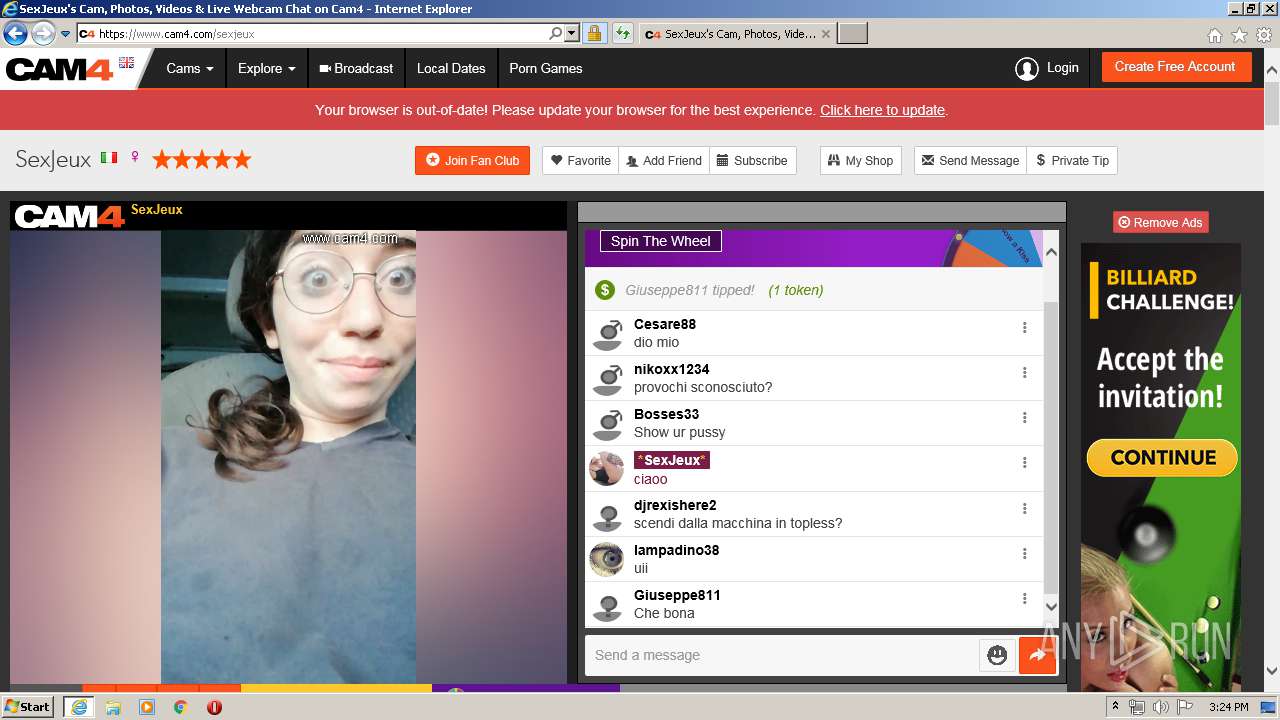
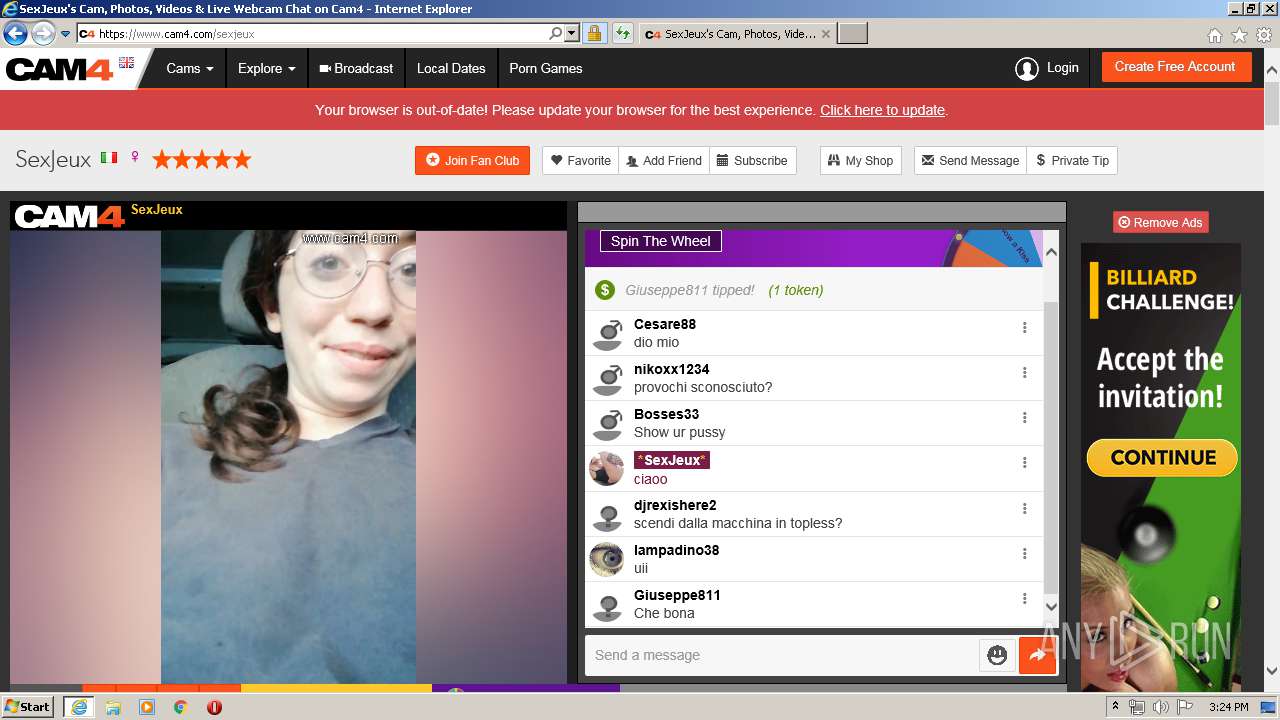
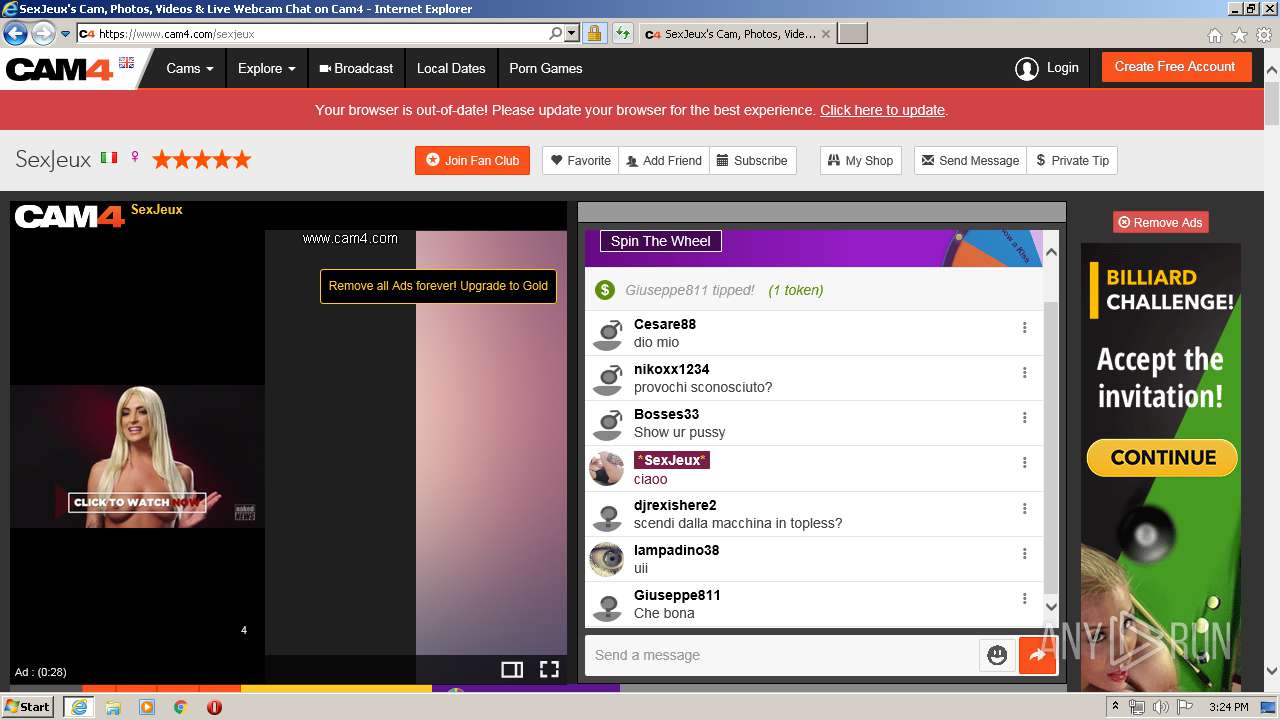
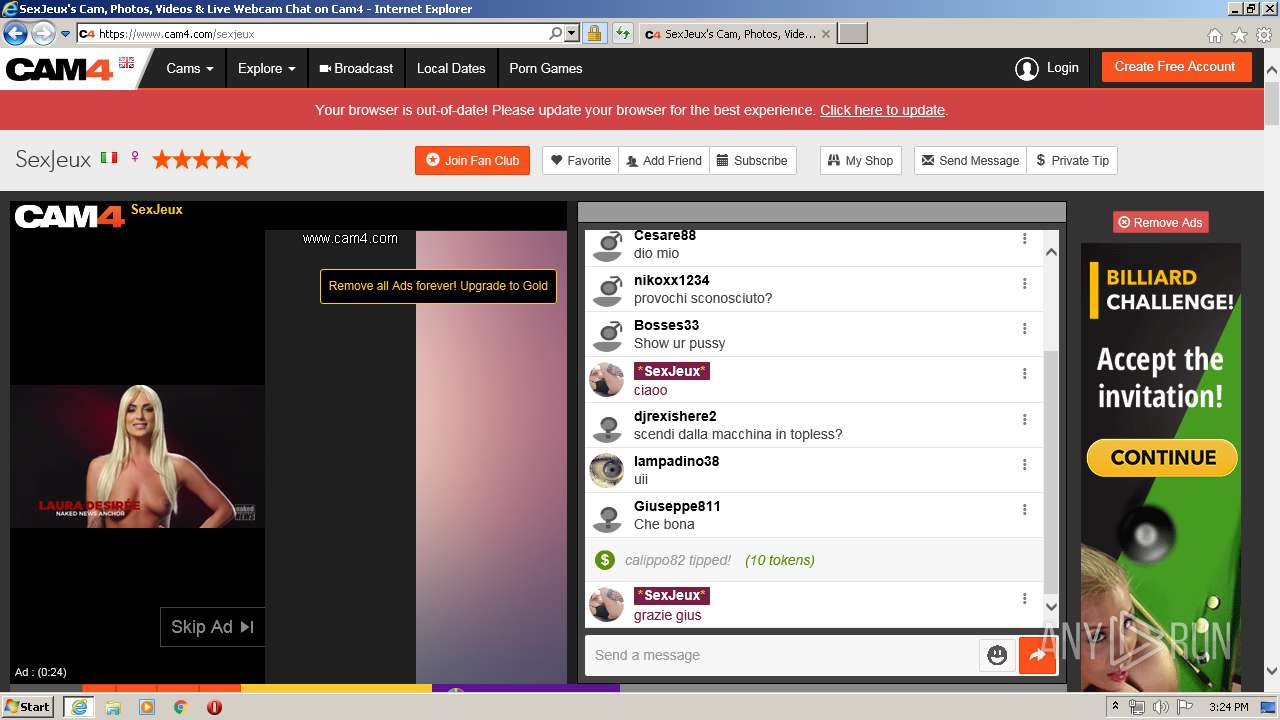
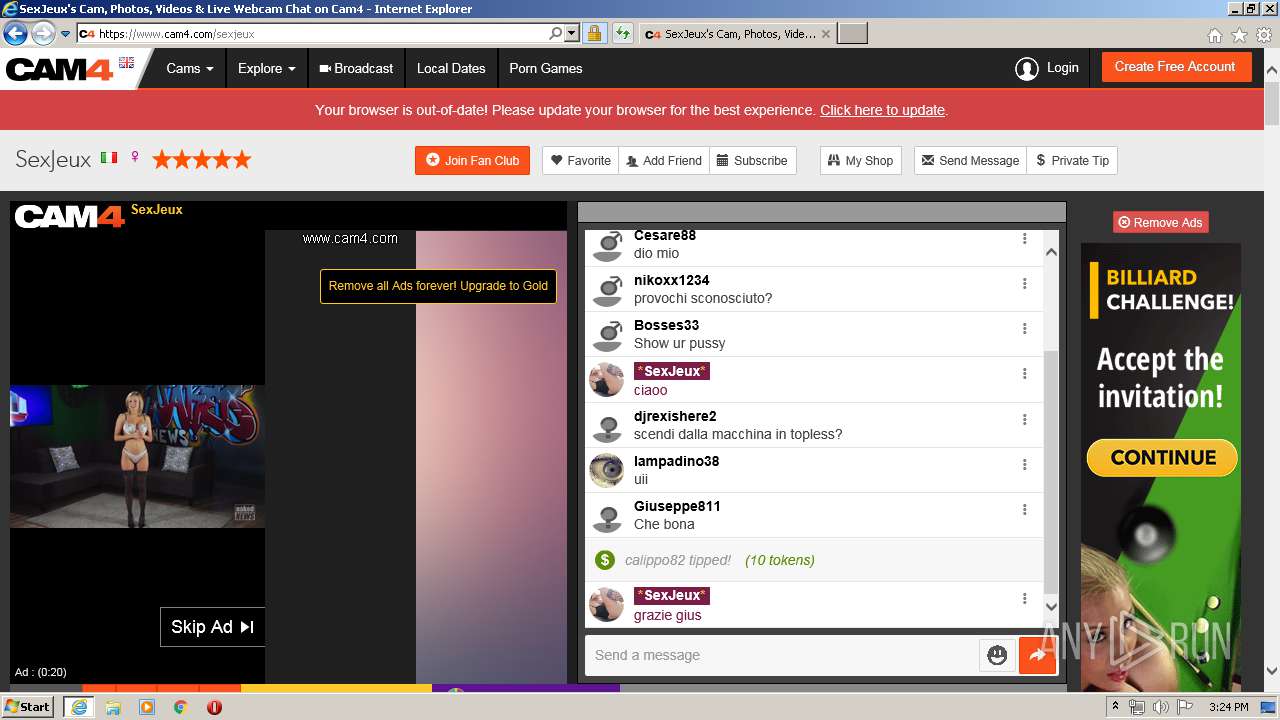
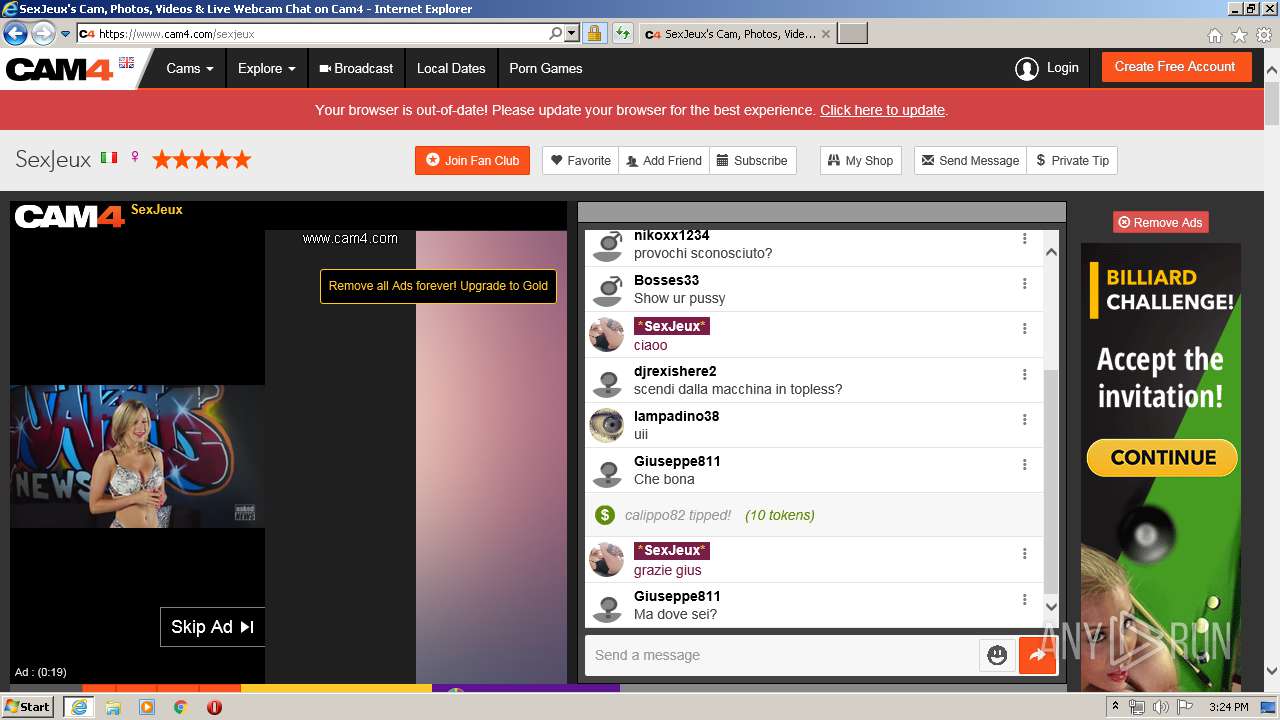
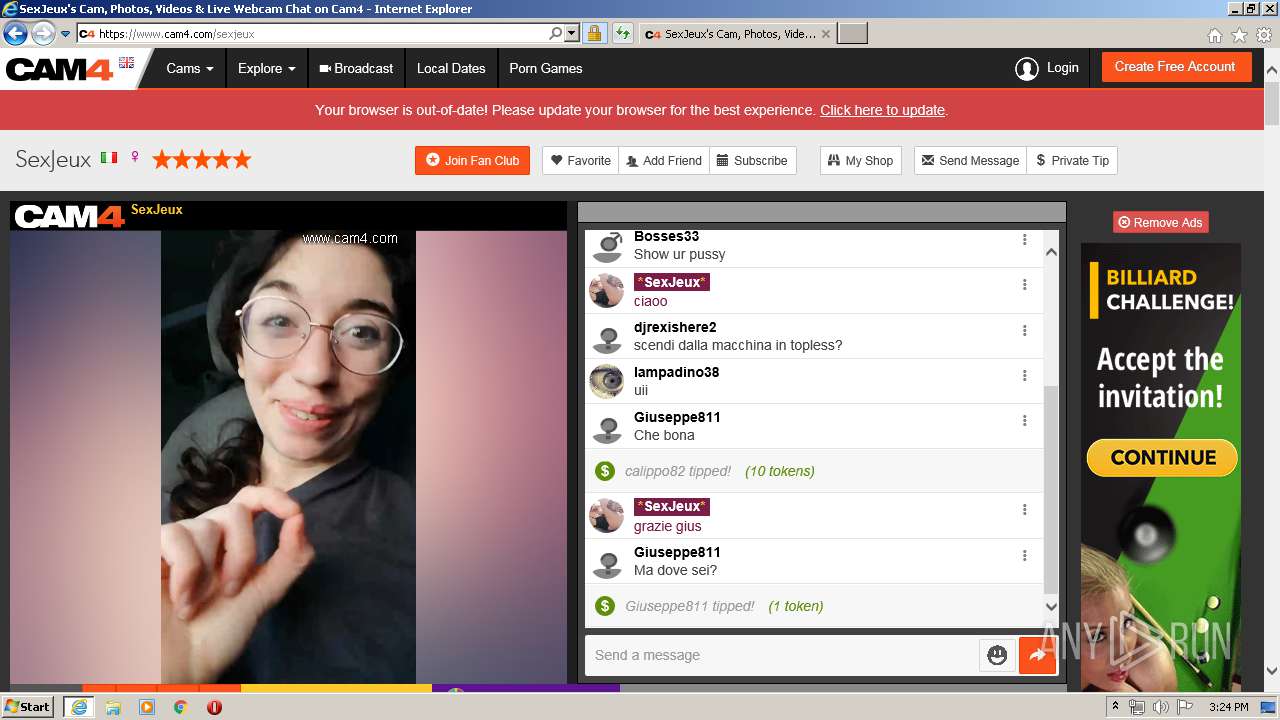
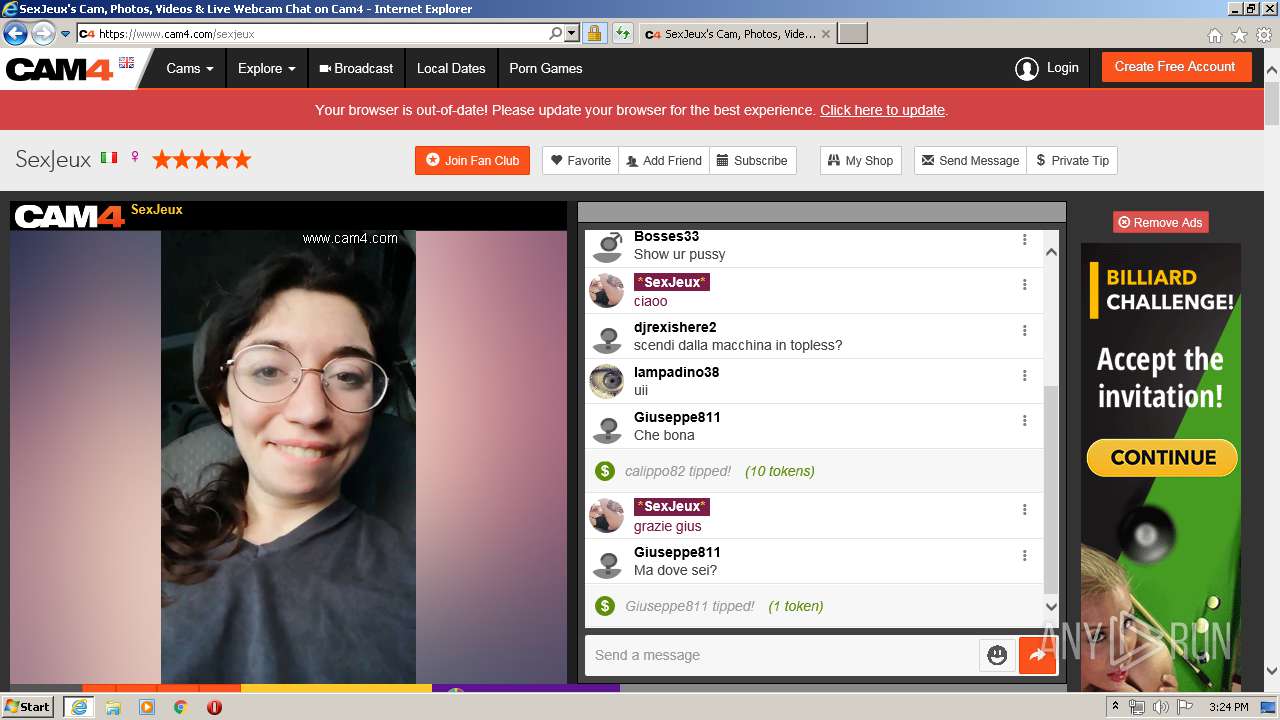
| URL: | https://www.cam4.com |
| Full analysis: | https://app.any.run/tasks/54478dbe-0dd2-4603-b5d4-0c0154f54c08 |
| Verdict: | No threats detected |
| Analysis date: | February 10, 2020, 15:20:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E16553580CD9C0C393DA335EF656943F |
| SHA1: | 92A7793055FC0456189323F7C3BB87DF356BF287 |
| SHA256: | 77BED4BD0A8A9405A1A727C22CD38C022B6584DAA3577623CD924A9087B9DBC9 |
| SSDEEP: | 3:N8DSLE0KI:2OLE0KI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2560)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3996)
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 2896)
Changes internet zones settings
- iexplore.exe (PID: 2556)
Application launched itself
- iexplore.exe (PID: 2556)
Reads internet explorer settings
- iexplore.exe (PID: 3996)
- iexplore.exe (PID: 2896)
Creates files in the user directory
- iexplore.exe (PID: 2556)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2560)
- iexplore.exe (PID: 3996)
Reads settings of System Certificates
- iexplore.exe (PID: 3996)
- iexplore.exe (PID: 2896)
- iexplore.exe (PID: 2556)
Changes settings of System certificates
- iexplore.exe (PID: 2556)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2556 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.cam4.com | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2560 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2556 CREDAT:1381649 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2556 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 182
Read events
1 709
Write events
4 756
Delete events
1 717
Modification events
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3038055560 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30793765 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
167
Text files
828
Unknown types
149
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7027.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7028.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\vendors~application-f5d9694adcf46084b8fa[1].js | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\i18n-51c4985e39e4d0afb7491daacc79dd5699a16a5ffa827dd97e7060b10b386cc8[1].htm | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1E11E75149C17A93653DA7DC0B8CF53F_42726E15C42F9DC480BCD9056A1779F9 | der | |
MD5:0C6757475F0E31125FDAD9F40883036A | SHA256:3CA274274B9AFF73147DF6F685477C3FEF3F00A9AB6BCF33202F4CAD4E412C70 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\application-e30a0aadad148317e4c1[1].js | text | |
MD5:F0BE59013321E73B9057A0DBD9766912 | SHA256:4E565202CB3B773655CDB7CD1887F9A6296A52B9053FF092DAFAF47B4DDAF59F | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:C056598304ED9DA4CCC3FDAE82B66061 | SHA256:175B79EB4DE20873DDB7BADA4CD1705DDAD0736C6B010CA2F9413890B9224250 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\vendors~application.app-902a88ac4c754610607b[1].css | text | |
MD5:BEEE2BA3DB414B9672EE961BE9B993AD | SHA256:A421FC847B854BCD52F8D730BAAB16C1A4D747315DC3BCA54E63E5DAA9EAD22E | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\i18n-51c4985e39e4d0afb7491daacc79dd5699a16a5ffa827dd97e7060b10b386cc8[1].json | text | |
MD5:2D2666AC07B99FDEC67B95B326B49406 | SHA256:51C4985E39E4D0AFB7491DAACC79DD5699A16A5FFA827DD97E7060B10B386CC8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
410
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAgAgw2cyAQJ5KilM%2ByXDgI%3D | US | der | 471 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
3996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAmZDgKxrtTc3Pz7HospRE0%3D | US | der | 279 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAa5MHPVElPavOriTJYsNCw%3D | US | der | 471 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 2.21.242.236:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgM305kqab6wLTv770Y3MnK7Ig%3D%3D | NL | der | 527 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 2.21.242.236:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgNE5N4UburLPPFYZf73gwTbfQ%3D%3D | NL | der | 527 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3996 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3996 | iexplore.exe | 66.254.122.104:443 | cam4-static.xcdnpro.com | Reflected Networks, Inc. | US | suspicious |
2556 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3996 | iexplore.exe | 172.217.16.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3996 | iexplore.exe | 216.58.207.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
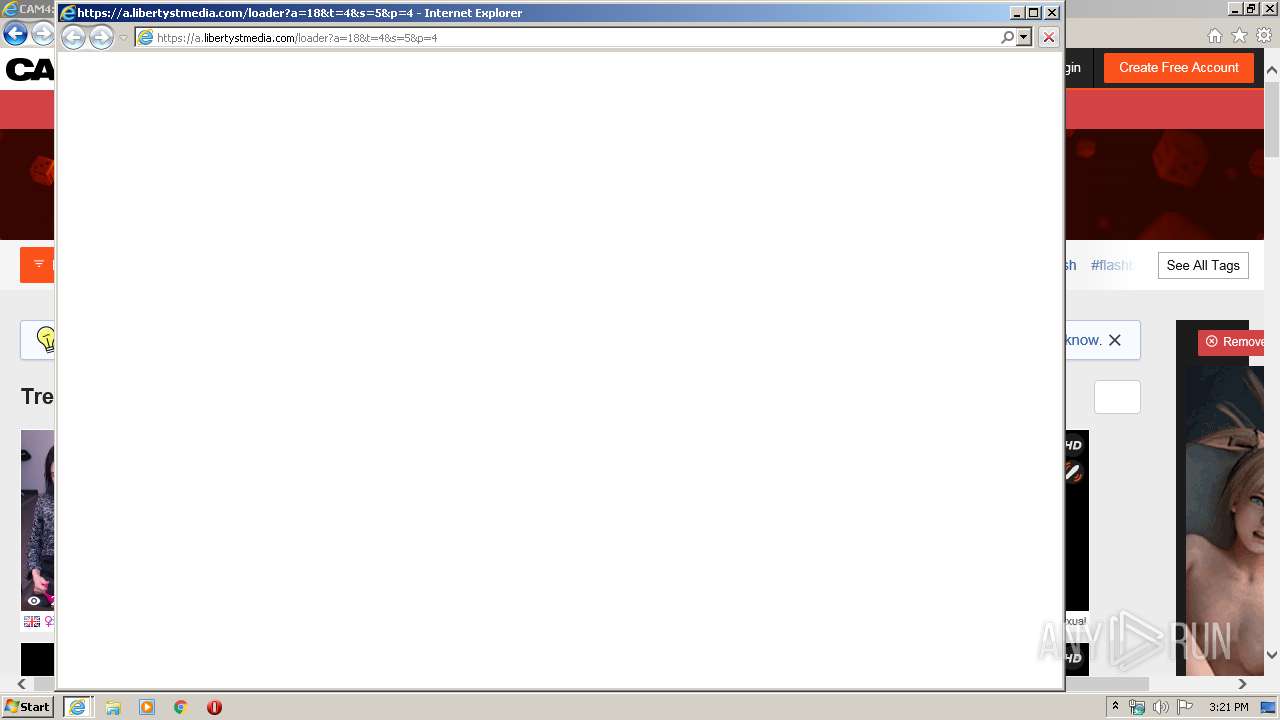
3996 | iexplore.exe | 172.64.99.17:443 | a.libertystmedia.com | Cloudflare Inc | US | shared |
3996 | iexplore.exe | 147.75.32.13:443 | static.hotjar.com | Packet Host, Inc. | US | unknown |
3996 | iexplore.exe | 52.222.149.165:443 | d2as12kgjg8gw5.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
3996 | iexplore.exe | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
3996 | iexplore.exe | 172.217.18.98:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cam4.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
cam4-static.xcdnpro.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
snapshots.xcdnpro.com |
| suspicious |
a.libertystmedia.com |
| malicious |
i.libertystmedia.com |
| malicious |