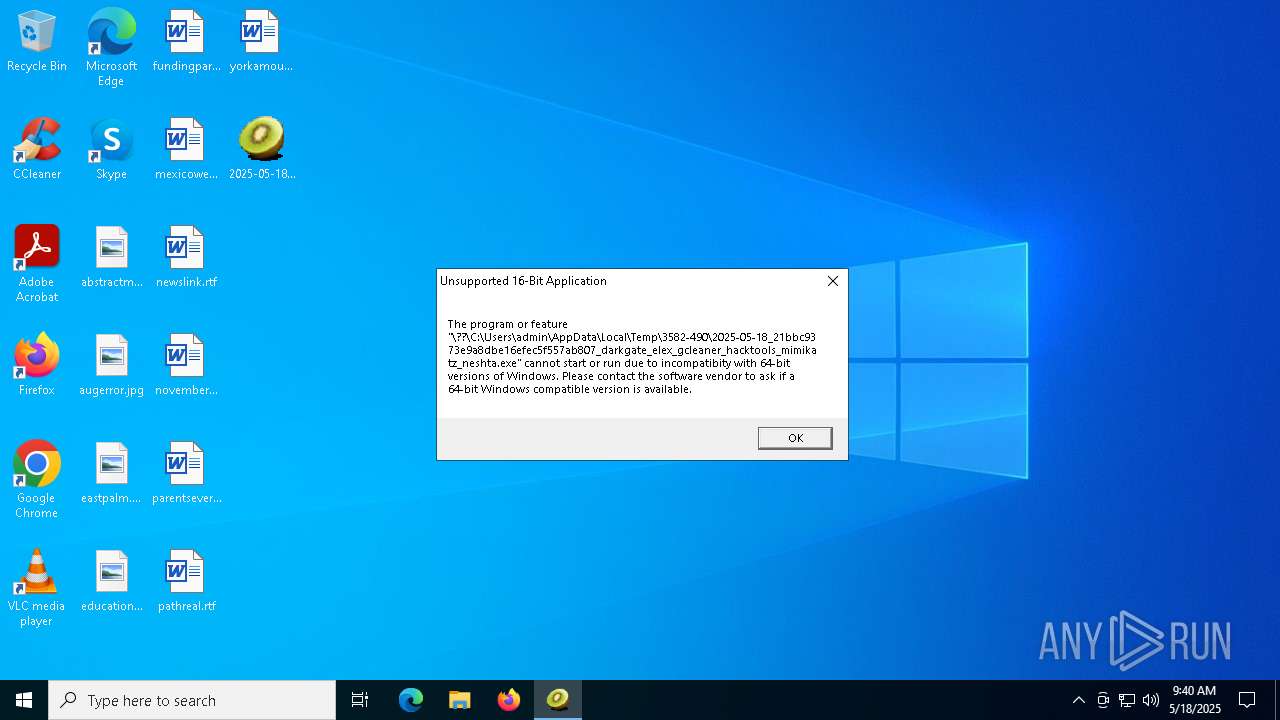
| File name: | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta |
| Full analysis: | https://app.any.run/tasks/8e8cced1-e7e3-442b-8c6b-4871f6f2705f |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 09:39:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 21BBC9373E9A8DBE16EFEC5F557AB807 |
| SHA1: | 3D2705BC7B5EB421EA9F7B596358E00F57EFF56F |
| SHA256: | 77B4790A18E90E2702AB2038E01EFE7EAB76D451DBEB8D42B98E2997D5E24F5B |
| SSDEEP: | 12288:95ak6v9P1kgEeliOPKfsEtjx/FgIzeRe6iRnFVJJcbAvV6skLGFw/wlYopTlfw6M:95Fk2gEy8XRHG6nFeb6ZY6PcRI2qq |
MALICIOUS
Executing a file with an untrusted certificate
- FileCoAuth.exe (PID: 8032)
NESHTA mutex has been found
- FileCoAuth.exe (PID: 7972)
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
SUSPICIOUS
Starts a Microsoft application from unusual location
- FileCoAuth.exe (PID: 8032)
Mutex name with non-standard characters
- FileCoAuth.exe (PID: 7972)
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
Reads security settings of Internet Explorer
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
- FileCoAuth.exe (PID: 7972)
Executable content was dropped or overwritten
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
- FileCoAuth.exe (PID: 7972)
There is functionality for taking screenshot (YARA)
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
Process drops legitimate windows executable
- FileCoAuth.exe (PID: 7972)
INFO
Create files in a temporary directory
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
- FileCoAuth.exe (PID: 8032)
Process checks computer location settings
- FileCoAuth.exe (PID: 7972)
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
Creates files or folders in the user directory
- FileCoAuth.exe (PID: 8032)
Checks supported languages
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
- FileCoAuth.exe (PID: 8032)
Reads the computer name
- 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe (PID: 7632)
- FileCoAuth.exe (PID: 8032)
Reads the machine GUID from the registry
- FileCoAuth.exe (PID: 8032)
The sample compiled with english language support
- FileCoAuth.exe (PID: 7972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (85.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (4.6) |
| .scr | | | Windows screen saver (4.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.1) |
| .exe | | | Win32 Executable (generic) (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
126
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7632 | "C:\Users\admin\Desktop\2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe" | C:\Users\admin\Desktop\2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7972 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 8032 | "C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe" -Embedding | C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe | — | FileCoAuth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 8132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 979
Read events
3 979
Write events
0
Delete events
0
Modification events
Executable files
8
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncHelper.exe | executable | |
MD5:1C0BE16E6ED8F5B6F0910650A25F4FA7 | SHA256:3028F6A6A7A10DC5D63F256FEEB8275F3818BF3371EAF8B20A2D0BF2FCD5F4A9 | |||
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\Users\admin\AppData\Local\Temp\3582-490\2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | binary | |
MD5:005C182B20A4E2AF33301EC0FFC0D106 | SHA256:B5631D31F56E56C54A111614D5F7EF10AA7D2D8019AF647BE0CE1519C2AD436D | |||
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncConfig.exe | executable | |
MD5:0C5EC1AE9A301408AF26032B445FBB08 | SHA256:3A8010F1E4E028782093877D969EB127B80AE48B7215A8D3F91E8AB9C165AC7A | |||
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDrive.exe | executable | |
MD5:178B773B3FB050FCE26E40A9E8C2EE9A | SHA256:1E03573733F25B44004049A535E7E79366FD86FE953F6DFEDAAD05513B46A6C5 | |||
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:85A67D34298E33D2D5A9EC789B6AB594 | SHA256:1DEE143B4F88F2375B85C6271A58E2E78FED081BEAE4090678CB2DD7A37FB2D4 | |||
| 8032 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2025-05-18.0940.8032.1.odl | binary | |
MD5:F2E16E49DBB5D094EC2F4DA399450618 | SHA256:7C220F95FAFE3712167479C8A62152A2D27E7F4C4715D95449743C83D844B13D | |||
| 8032 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2025-05-18.0940.8032.1.aodl | binary | |
MD5:28DCA2FF4B34B5A52A2E59DF202A6ED3 | SHA256:33BACCB7296F1ED1F995FC77A23049F261CF391AC0388F9E8DD161F8C17B7F94 | |||
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\OneDriveUpdaterService.exe | executable | |
MD5:E73AC057B2CFEF016B8199389F0DF590 | SHA256:20ABA9D6001E5CDC287CD5BD452D0F2D05980D83F851D2B309BF49E9D9A8AC4C | |||
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | executable | |
MD5:13C2D5BF03C4A2B28E930F990CCC32DB | SHA256:12D24D0BC0E7CDC902E3540A3C6F7B755094F011A8EAD49A47A00563710B8F80 | |||
| 7632 | 2025-05-18_21bbc9373e9a8dbe16efec5f557ab807_darkgate_elex_gcleaner_hacktools_mimikatz_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe | executable | |
MD5:A747FA4161FE3C00C3FBB4BF391D4D4E | SHA256:B7BA59428AF7AE08C5BF927B57E326D5259E6ED31BD4237AA6A44378177364C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
23
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.39:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.39:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7484 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8132 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |