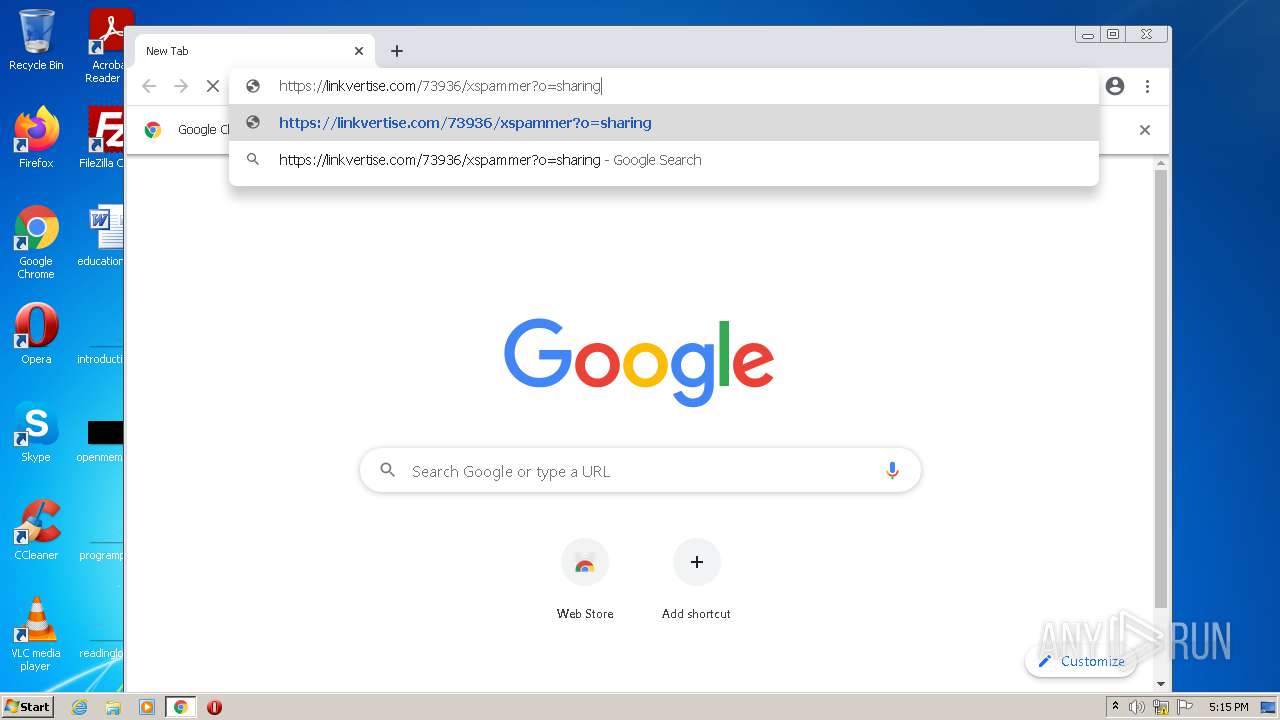
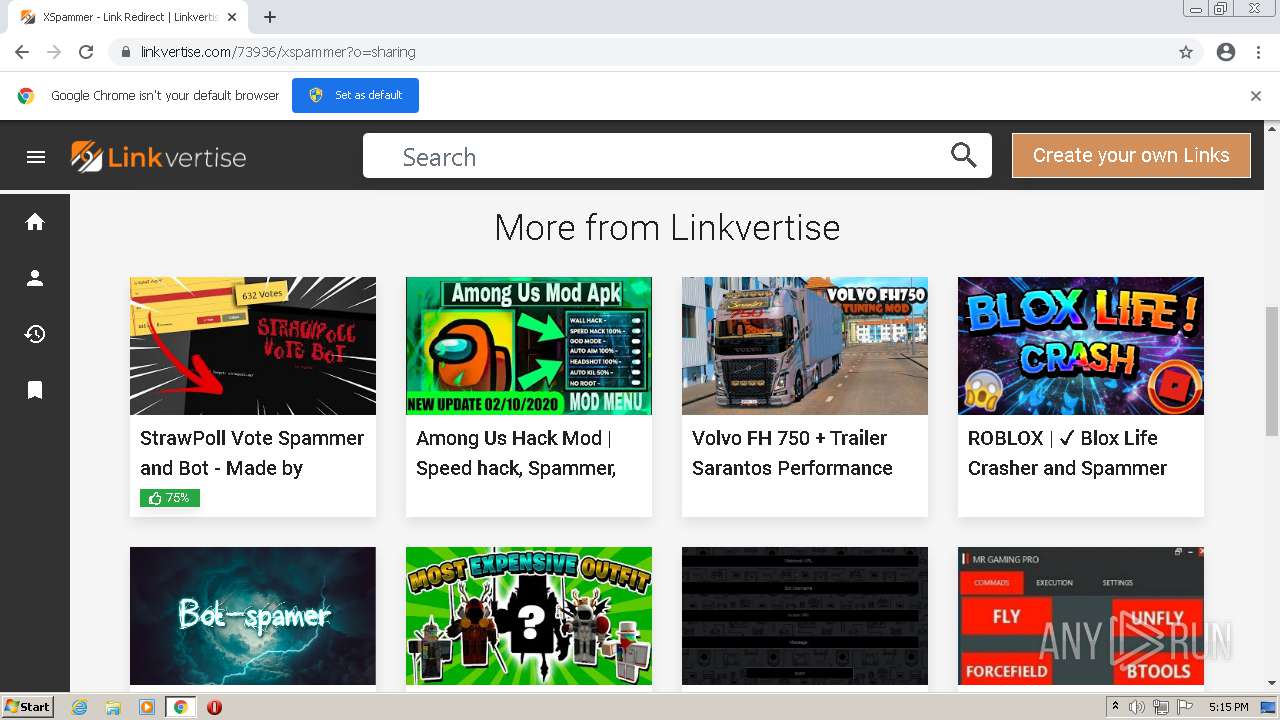
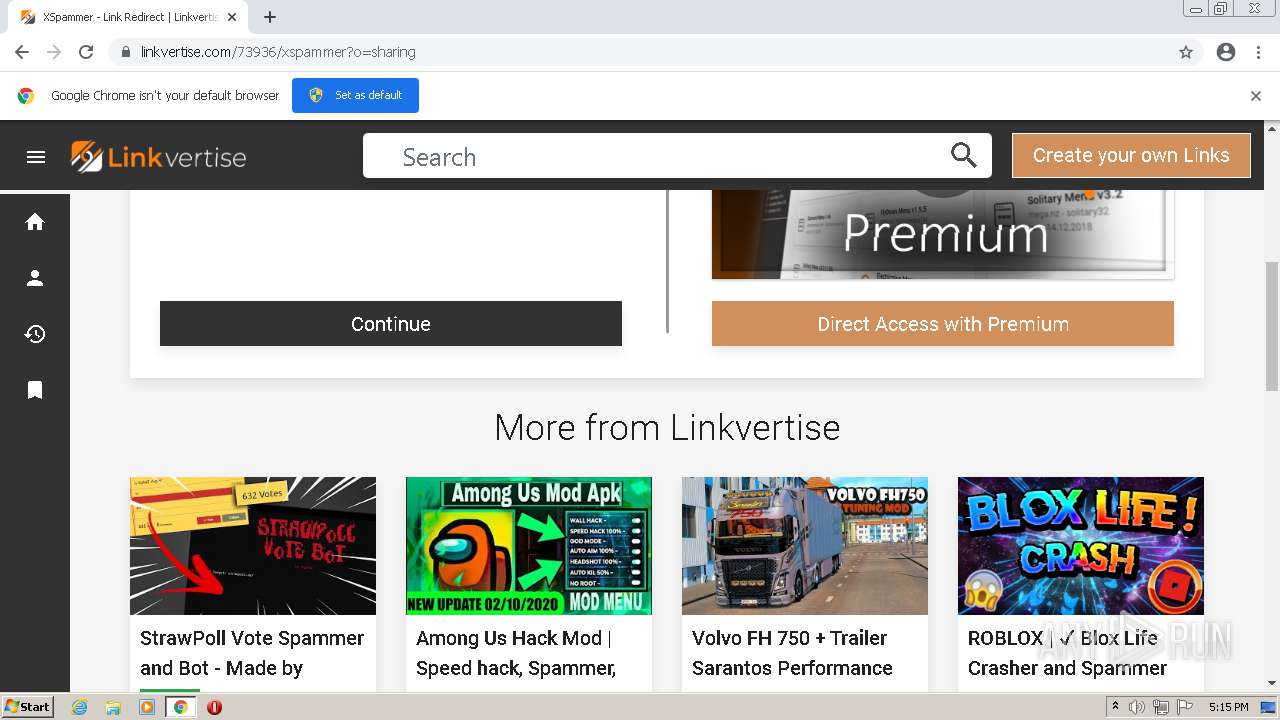
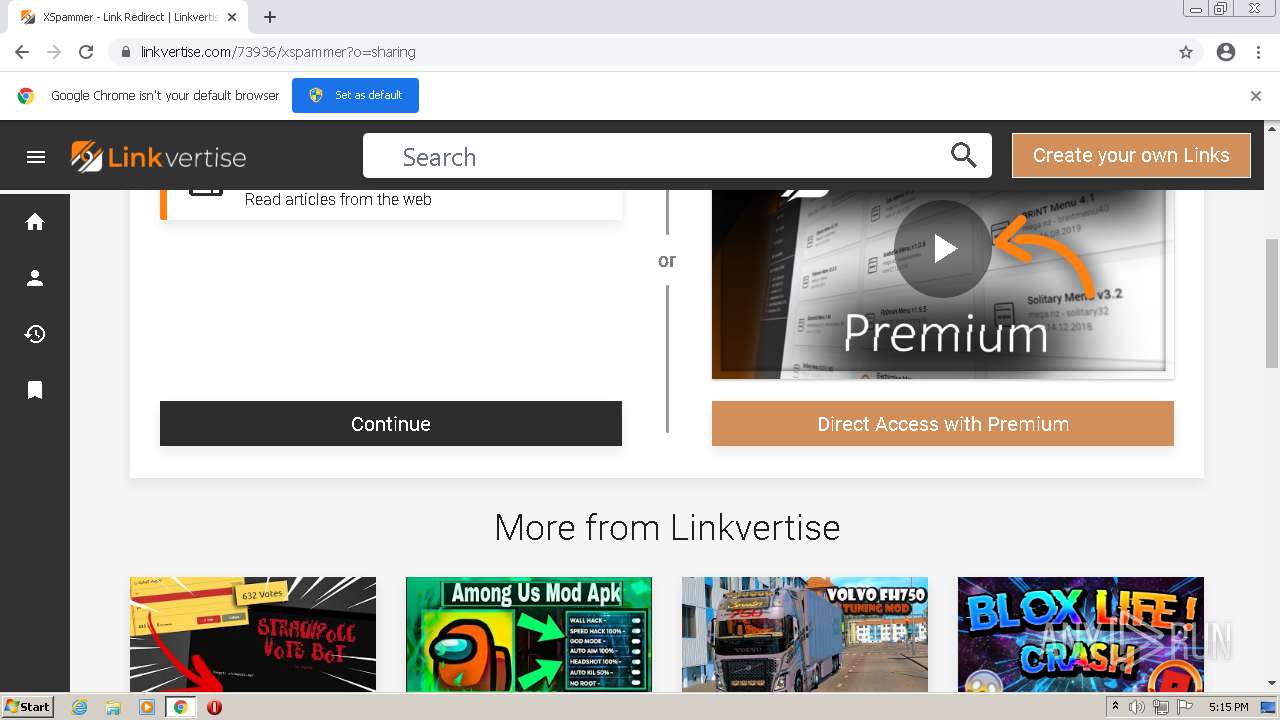
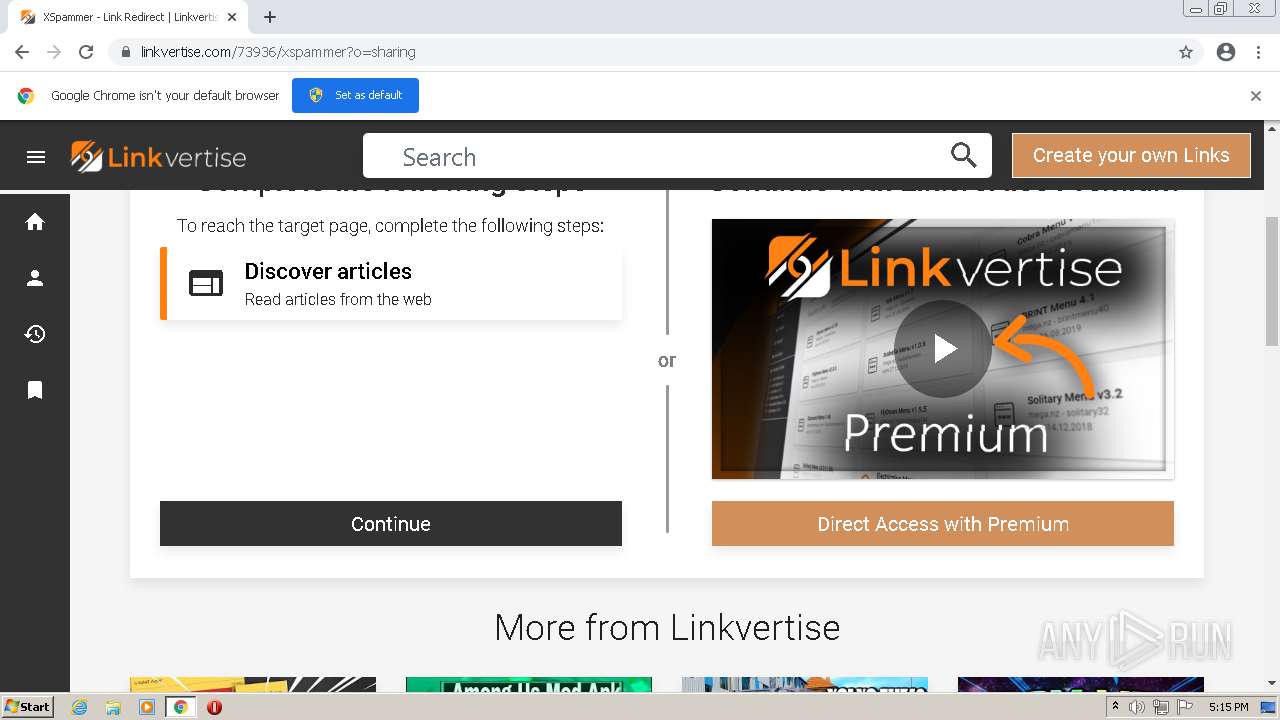
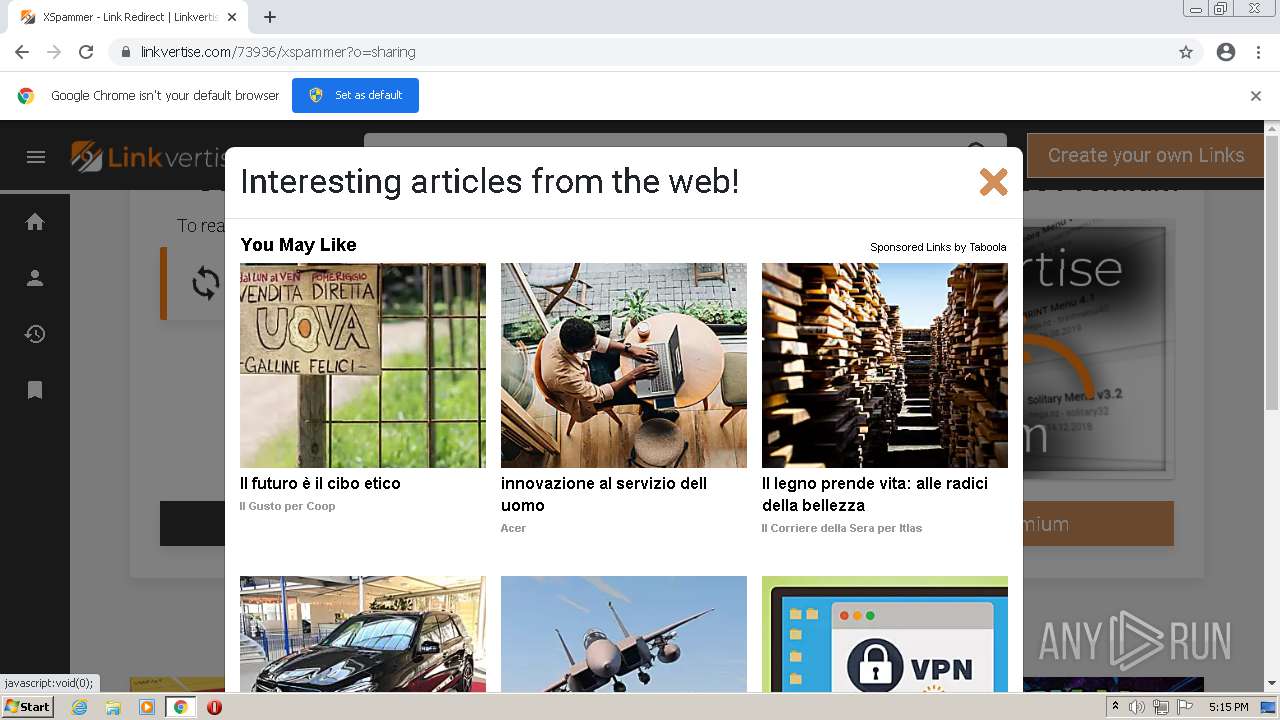
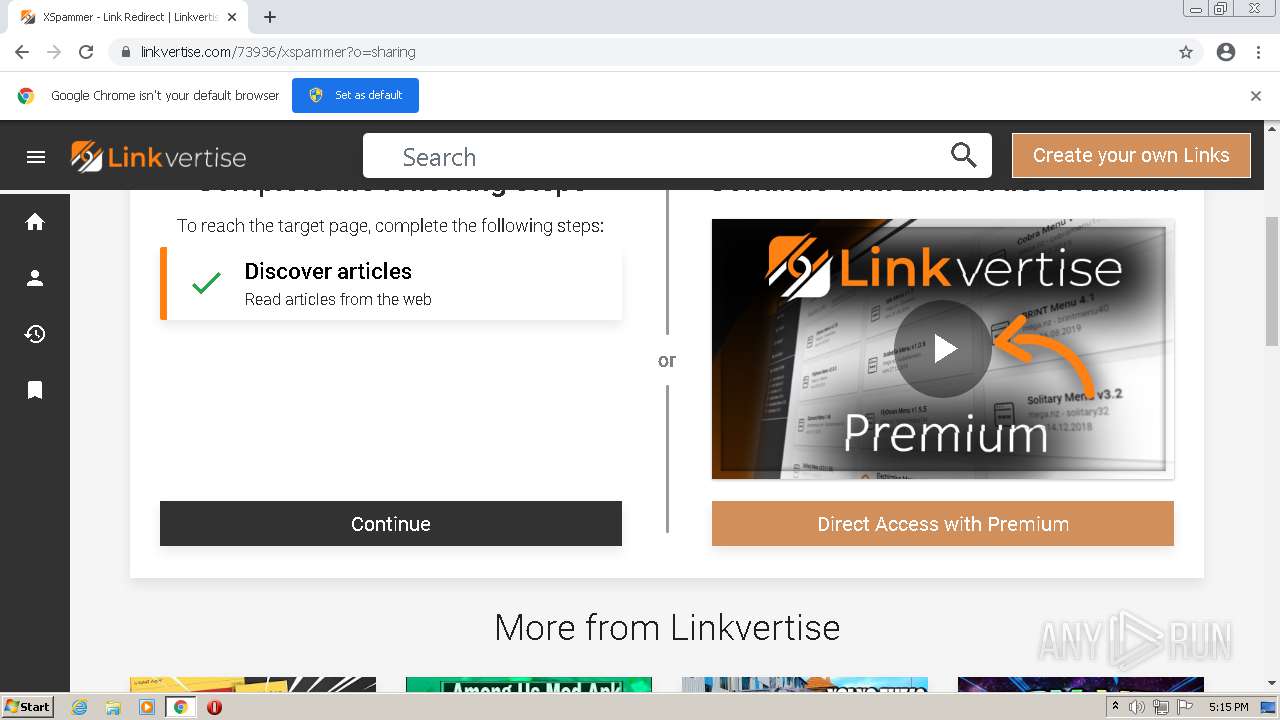
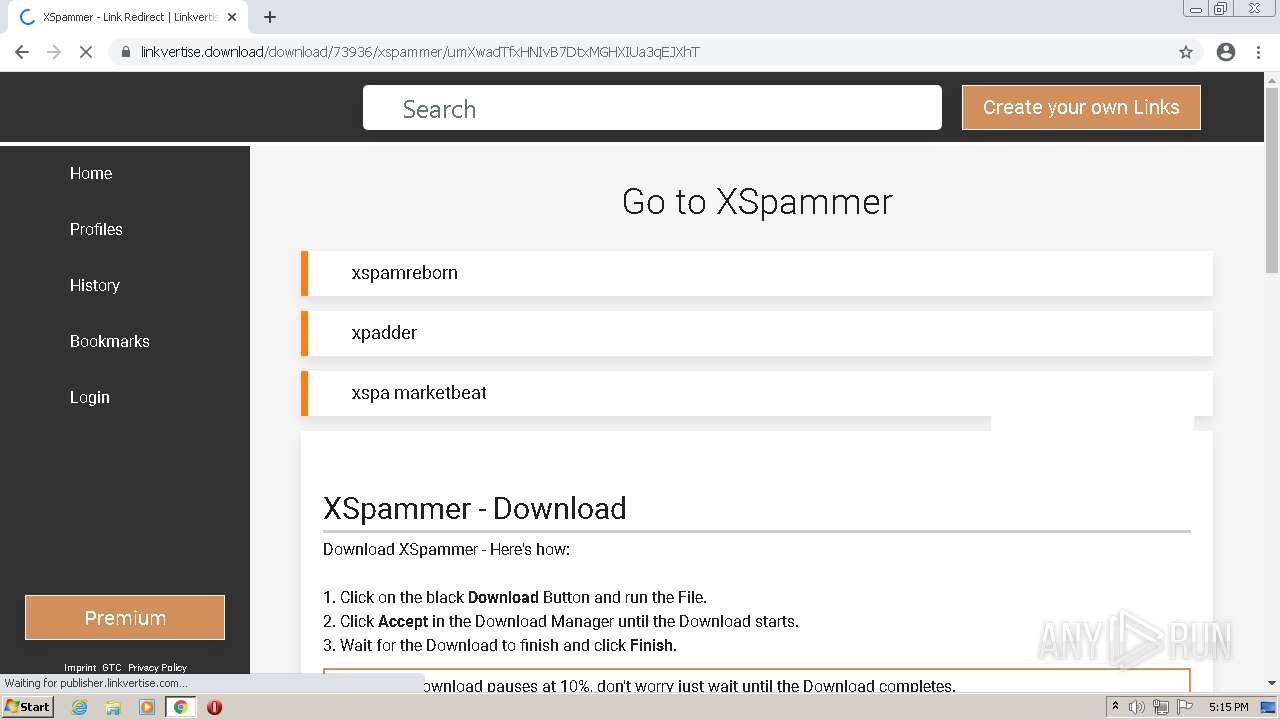
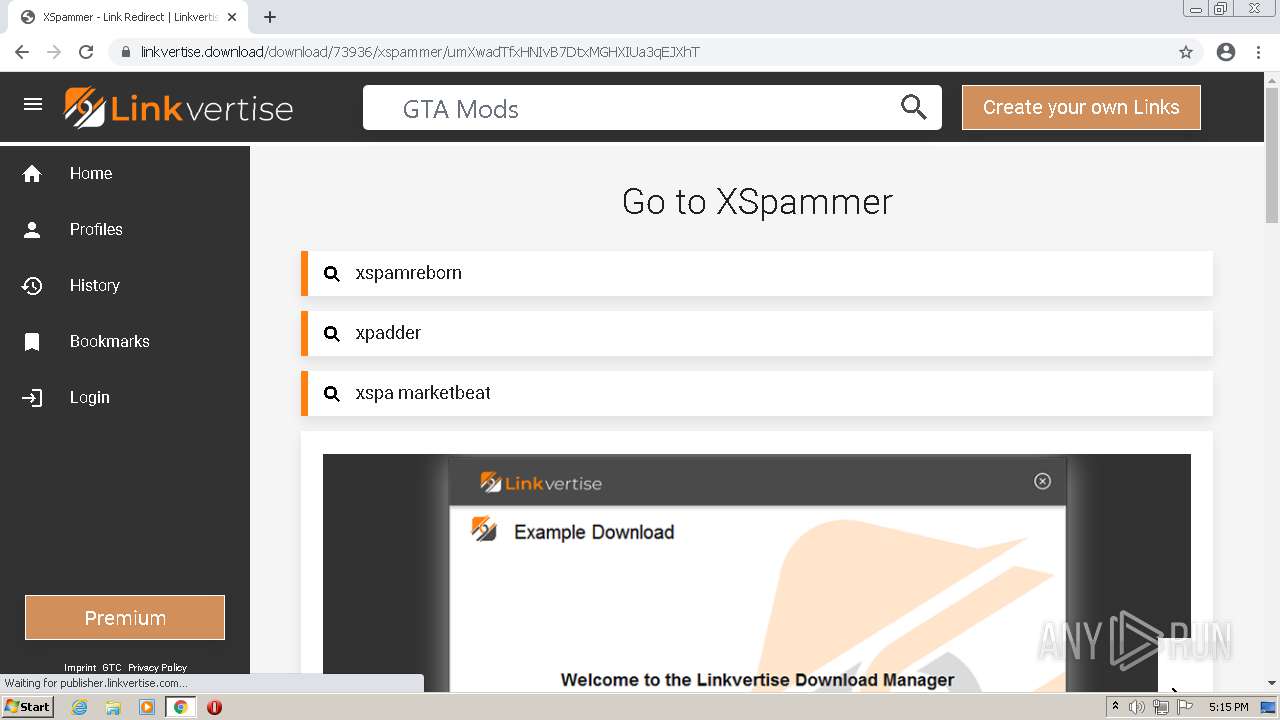
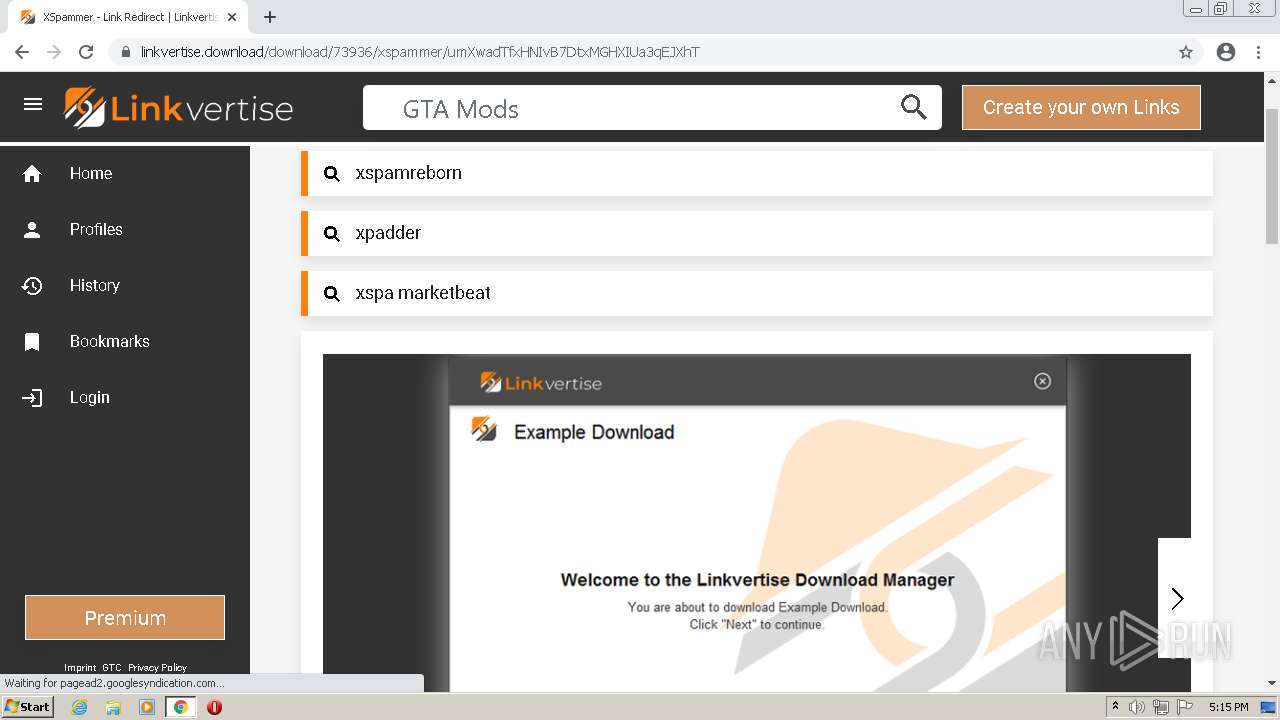
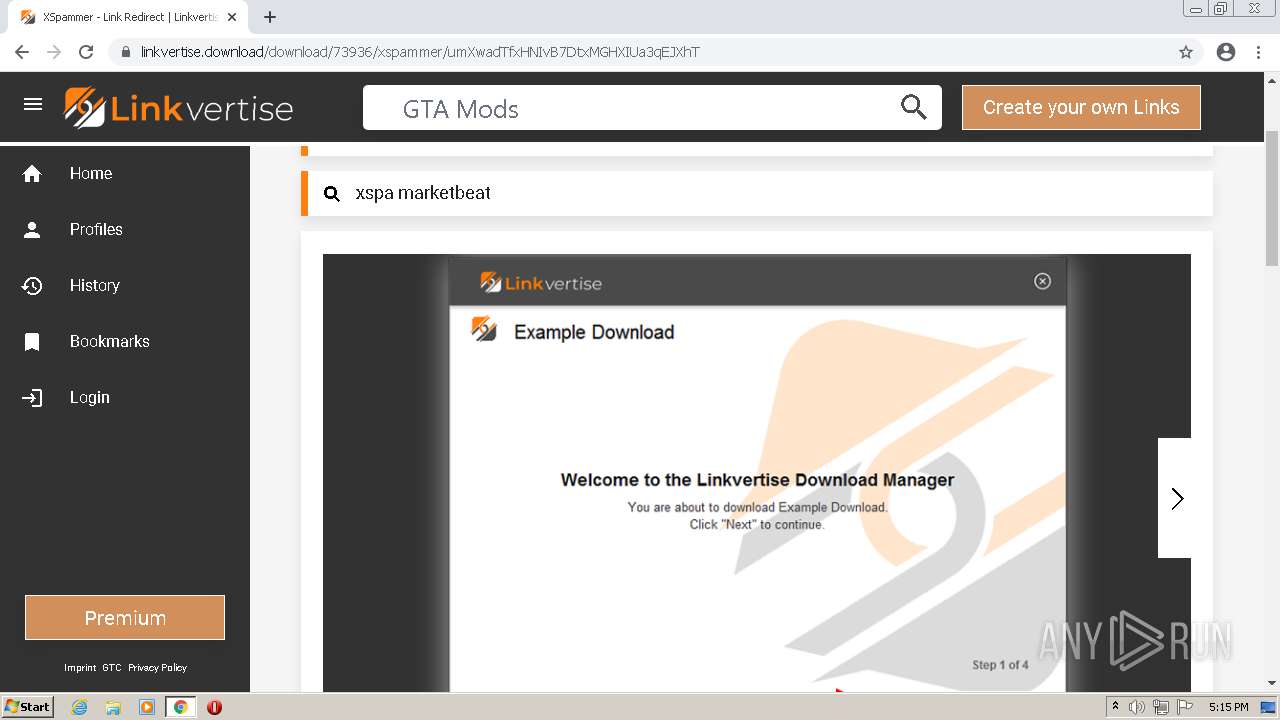
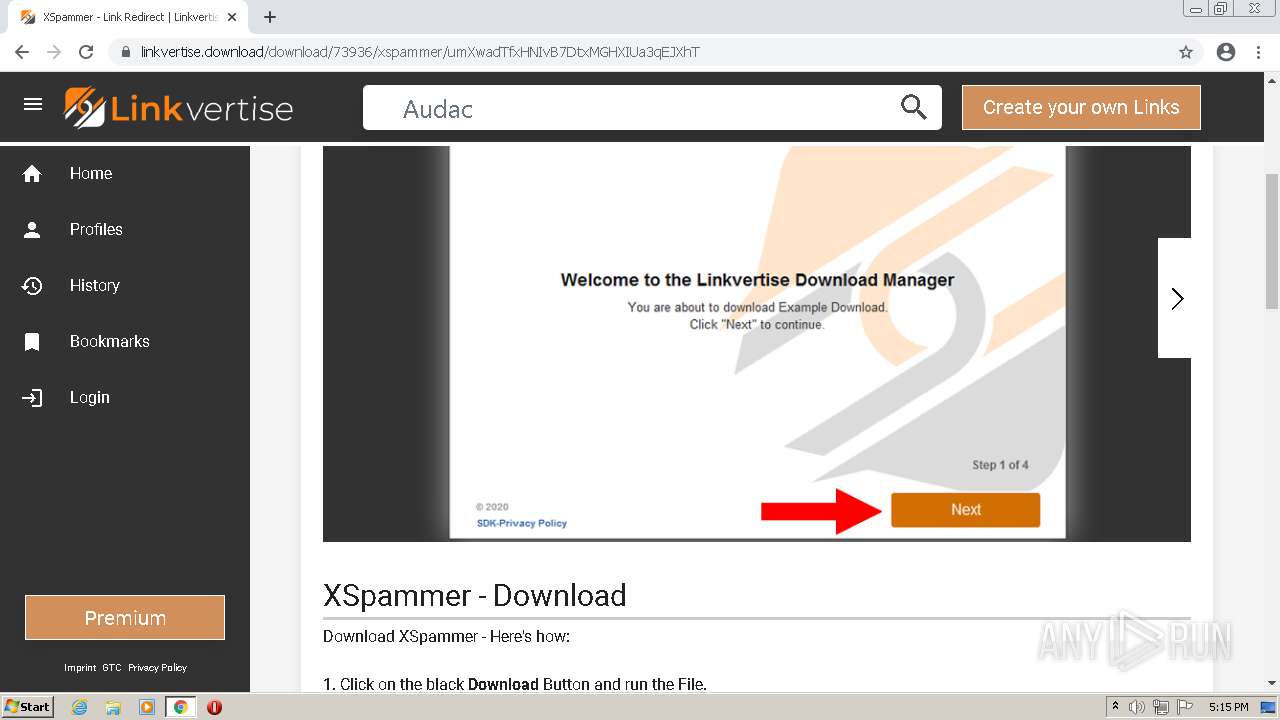
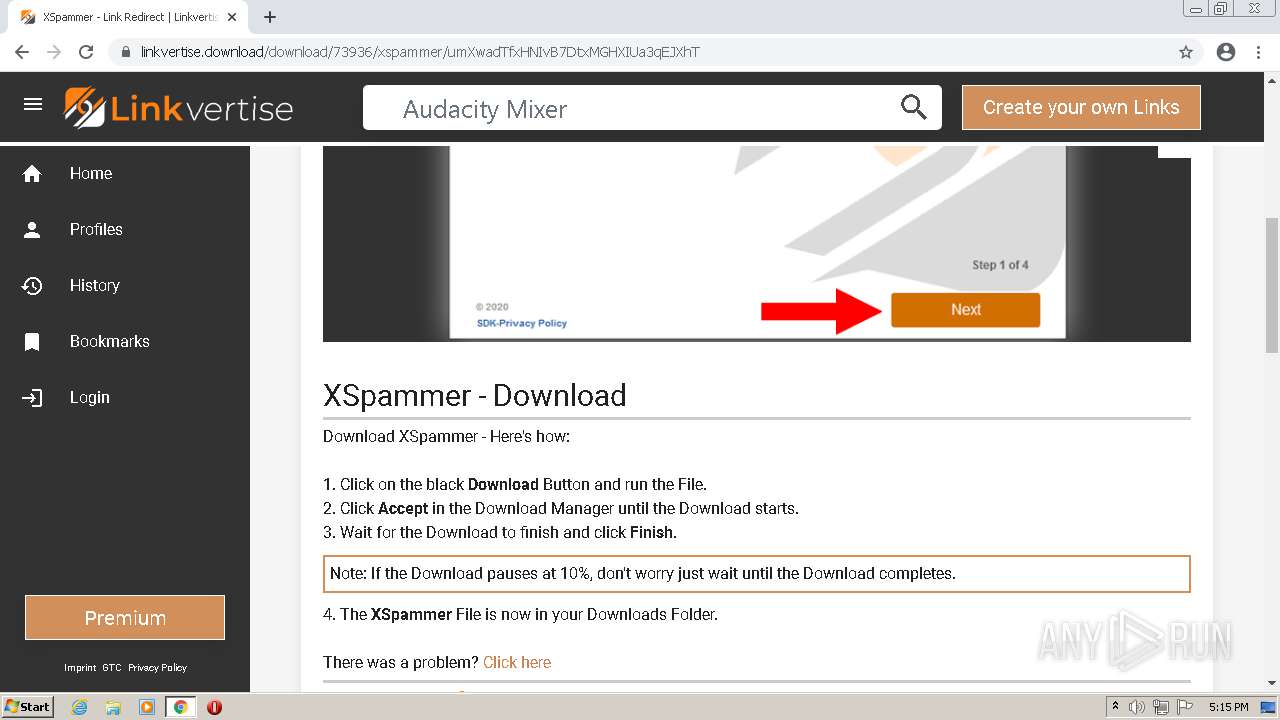
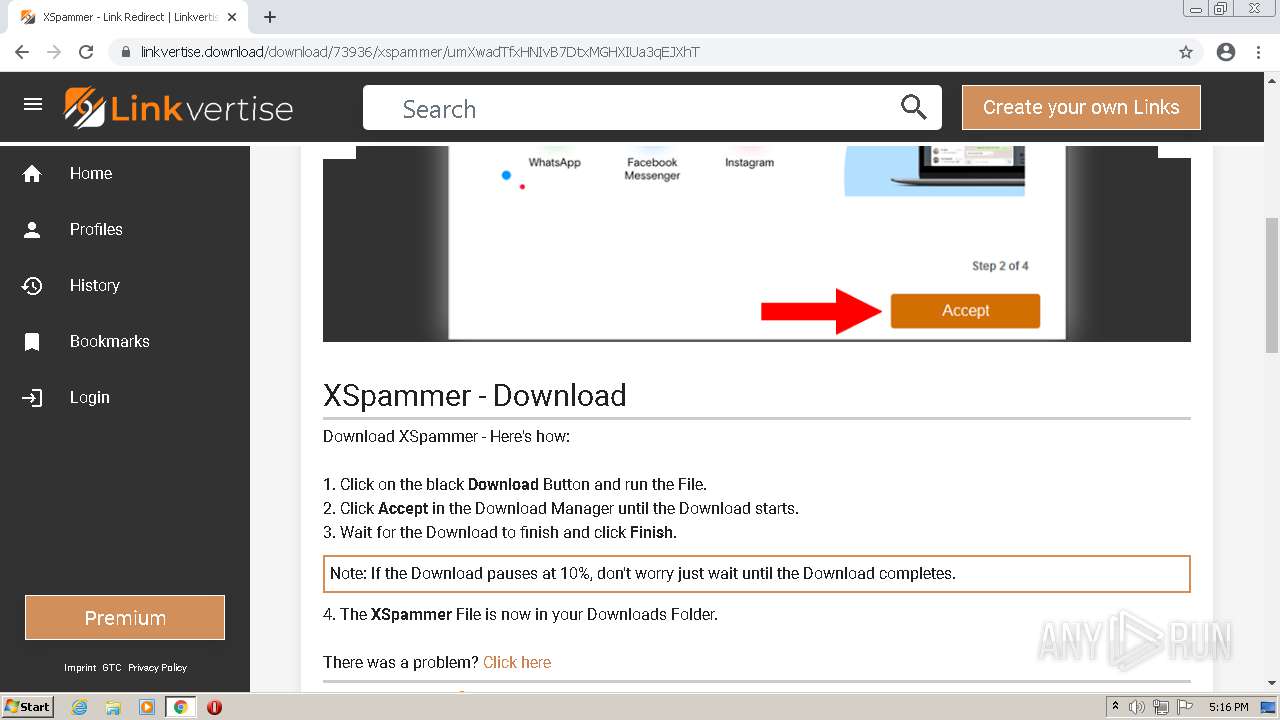
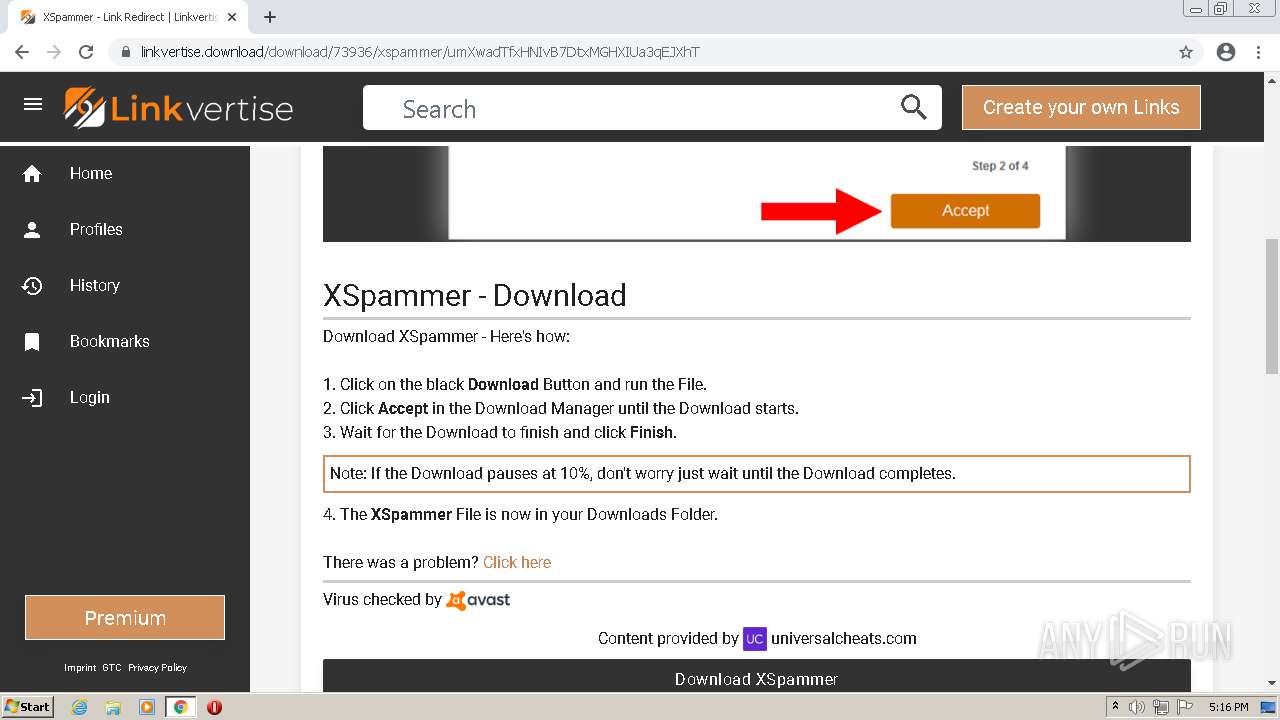
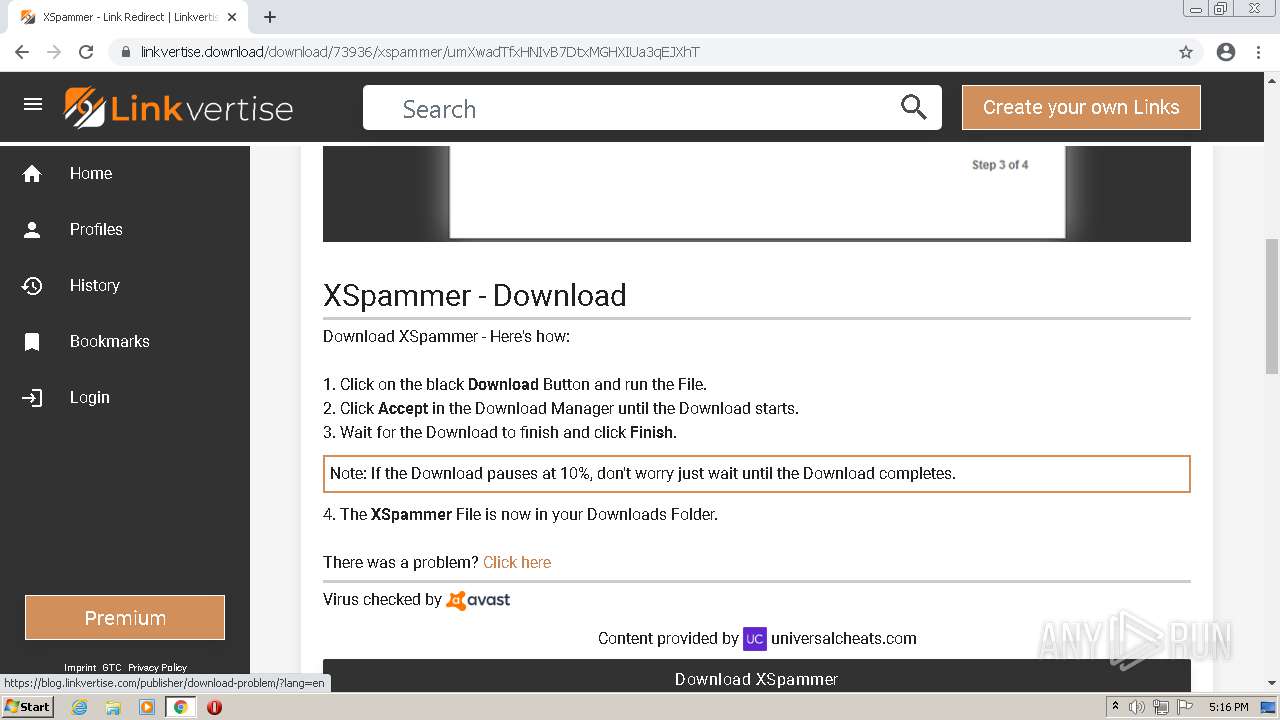
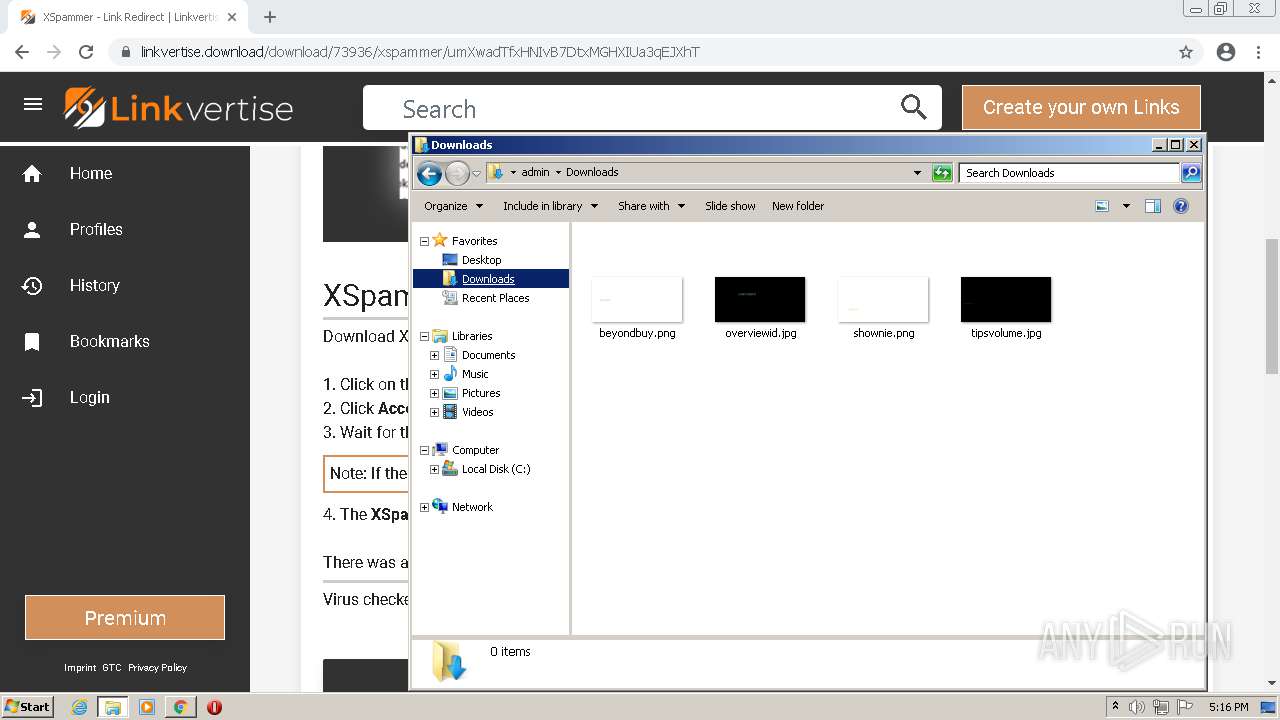
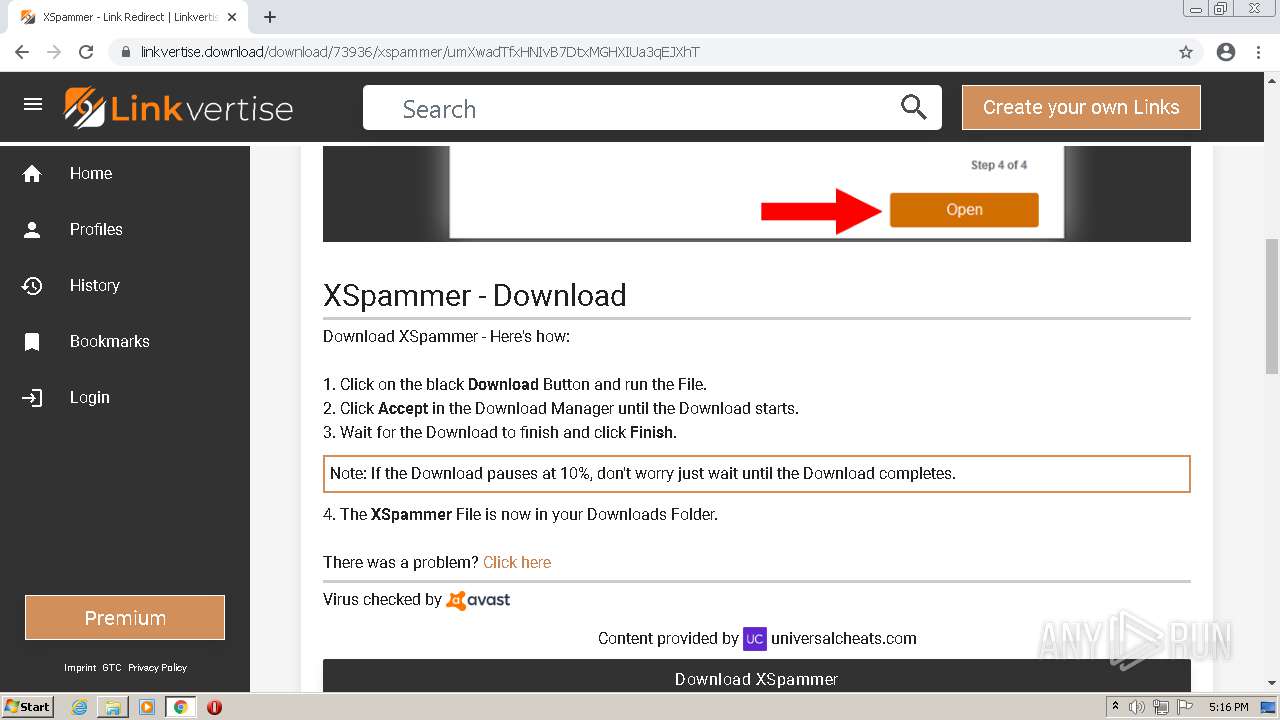
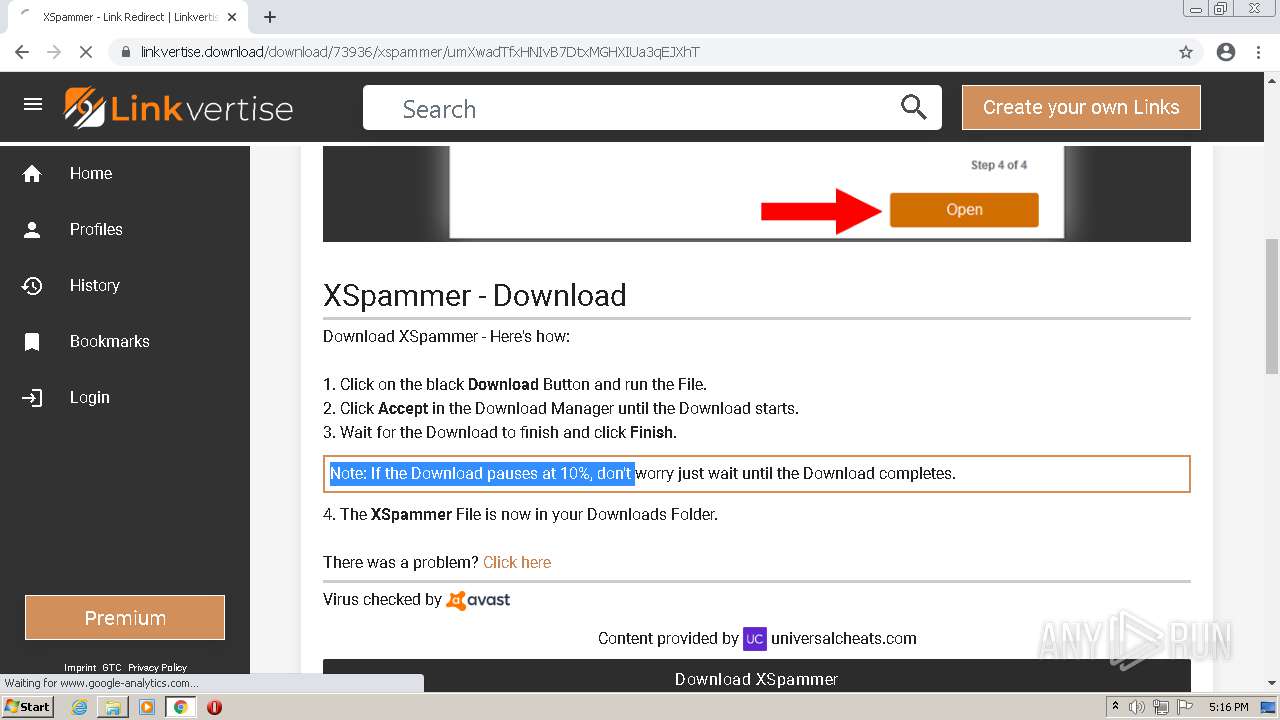
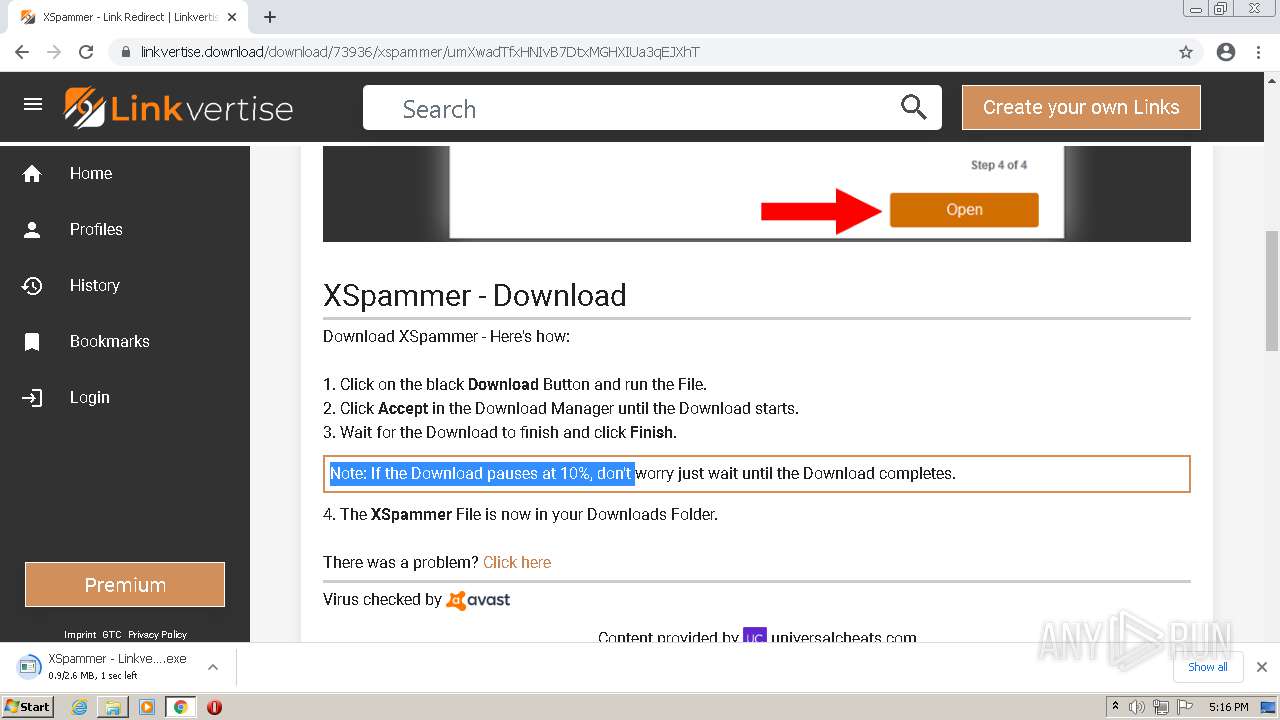
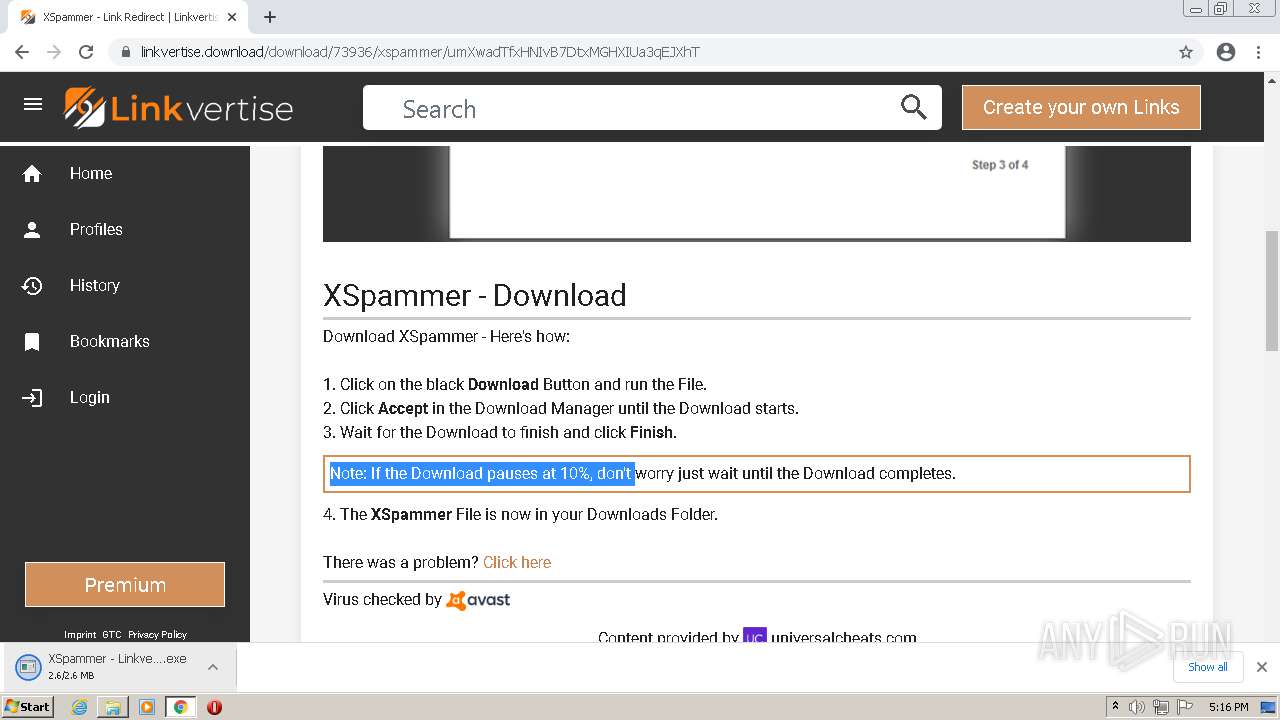
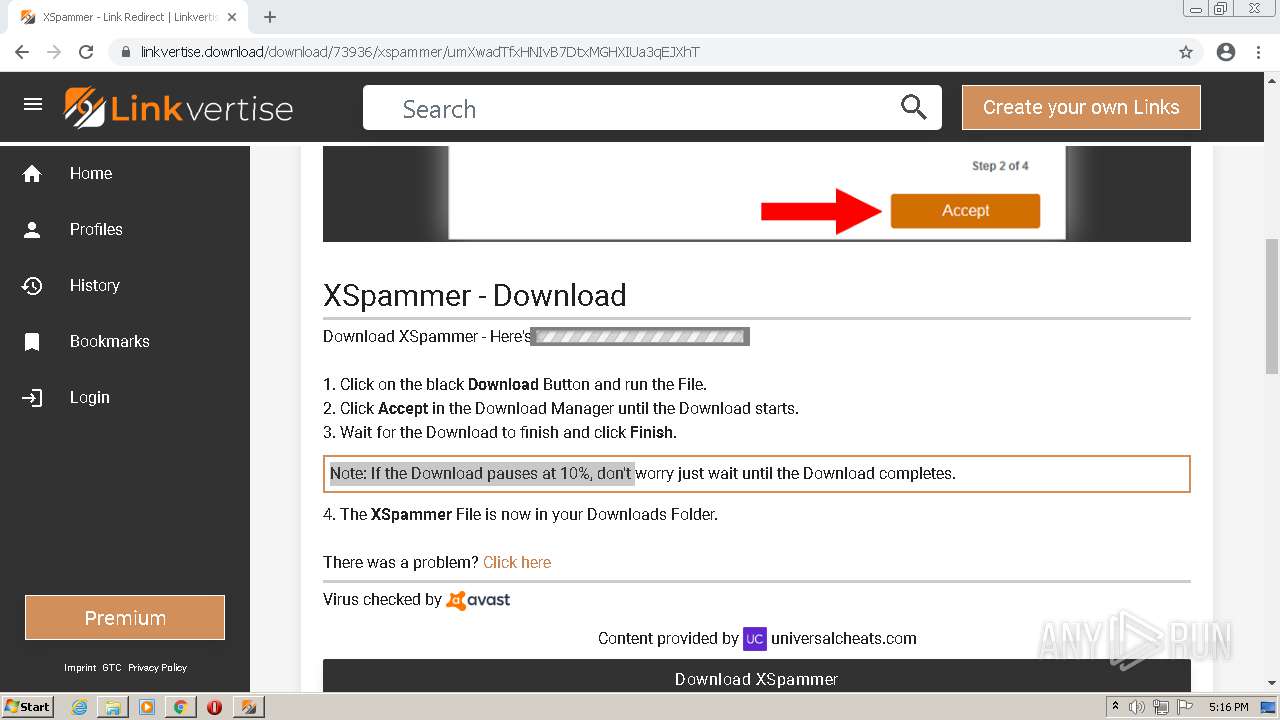
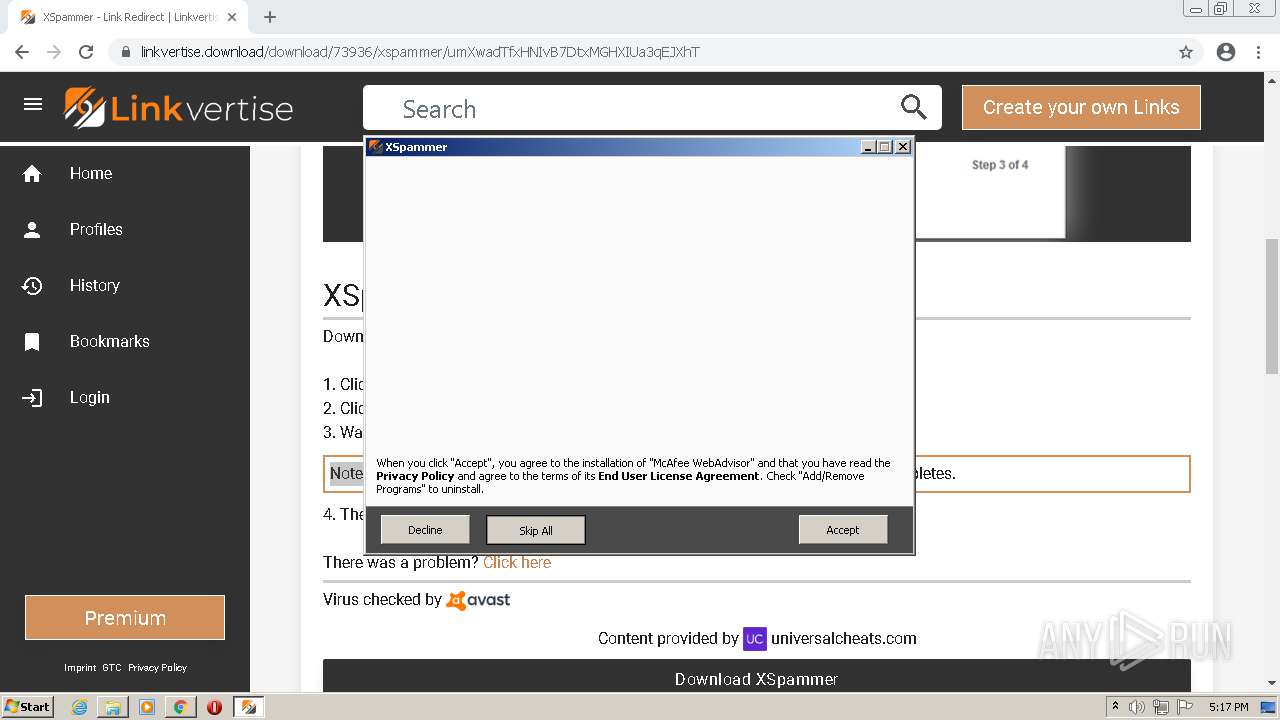
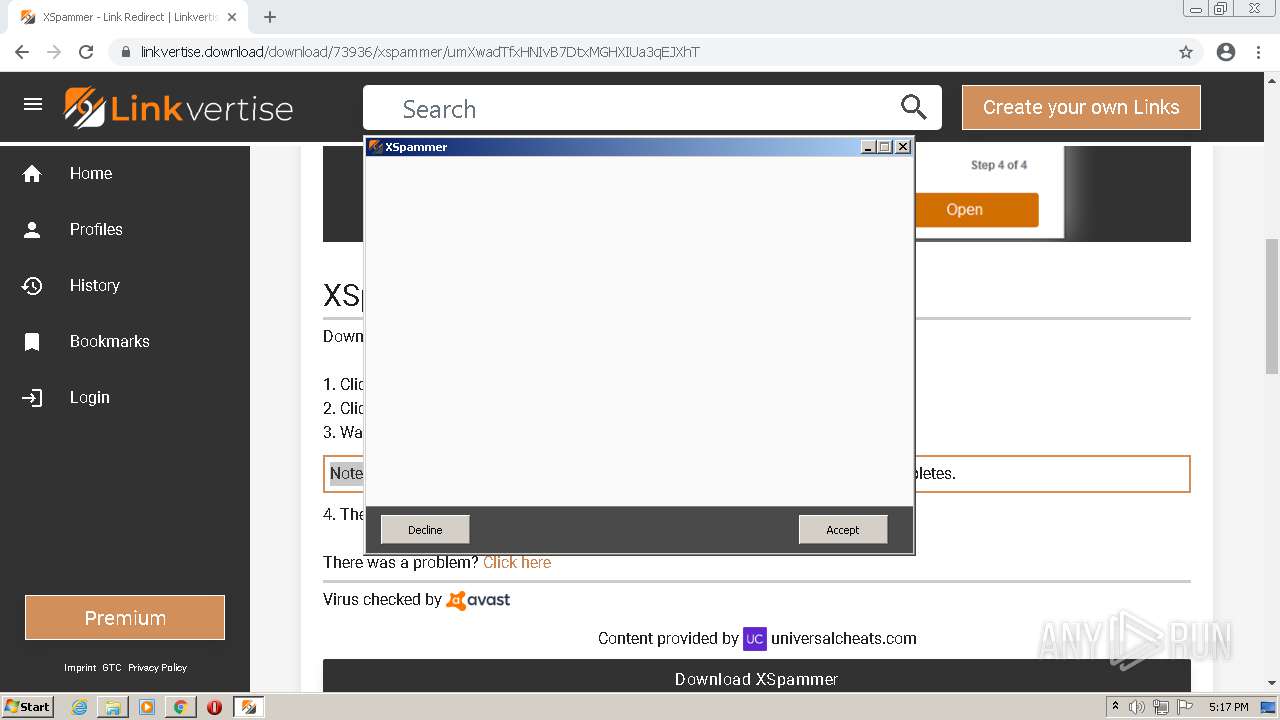
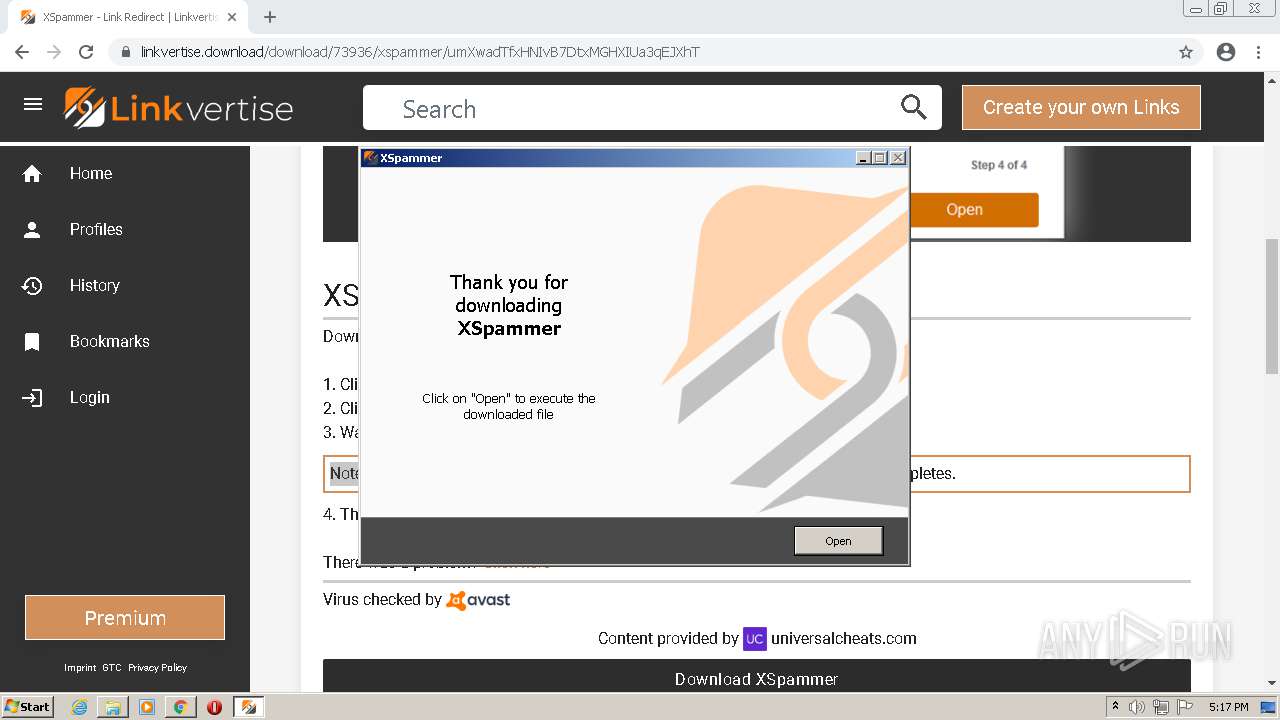
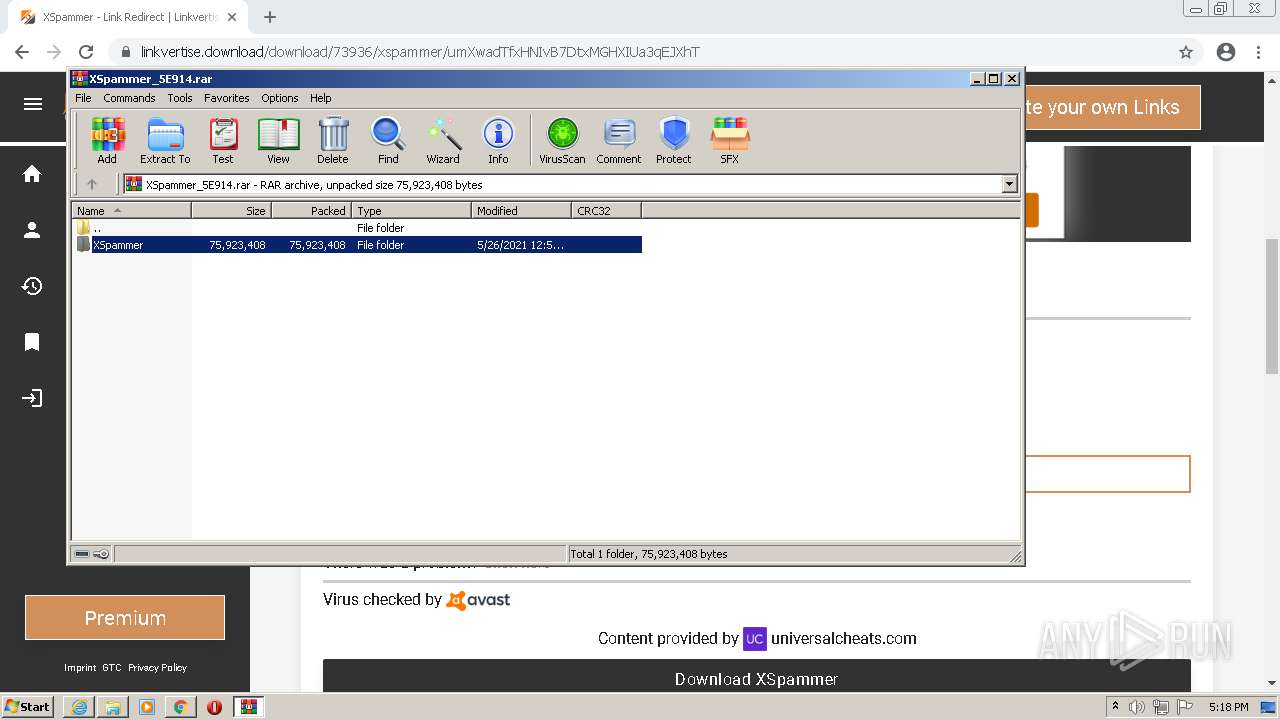
| URL: | https://linkvertise.com/73936/xspammer?o=sharing |
| Full analysis: | https://app.any.run/tasks/ab2bfe40-0070-4ee6-a9d8-d2f1cc207d6f |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2021, 16:14:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DF061CF396FE6CAA5649E210D5407080 |
| SHA1: | DEFF1BA48D466C536255534A509E5EC0A783842C |
| SHA256: | 77A7327397CE6BF529413A2A5D4F1A079BDAFC98199DEB41CD991992FB866F7B |
| SSDEEP: | 3:N8MLRBXAyTKlcRFAXbC:2MNi2fiC |
MALICIOUS
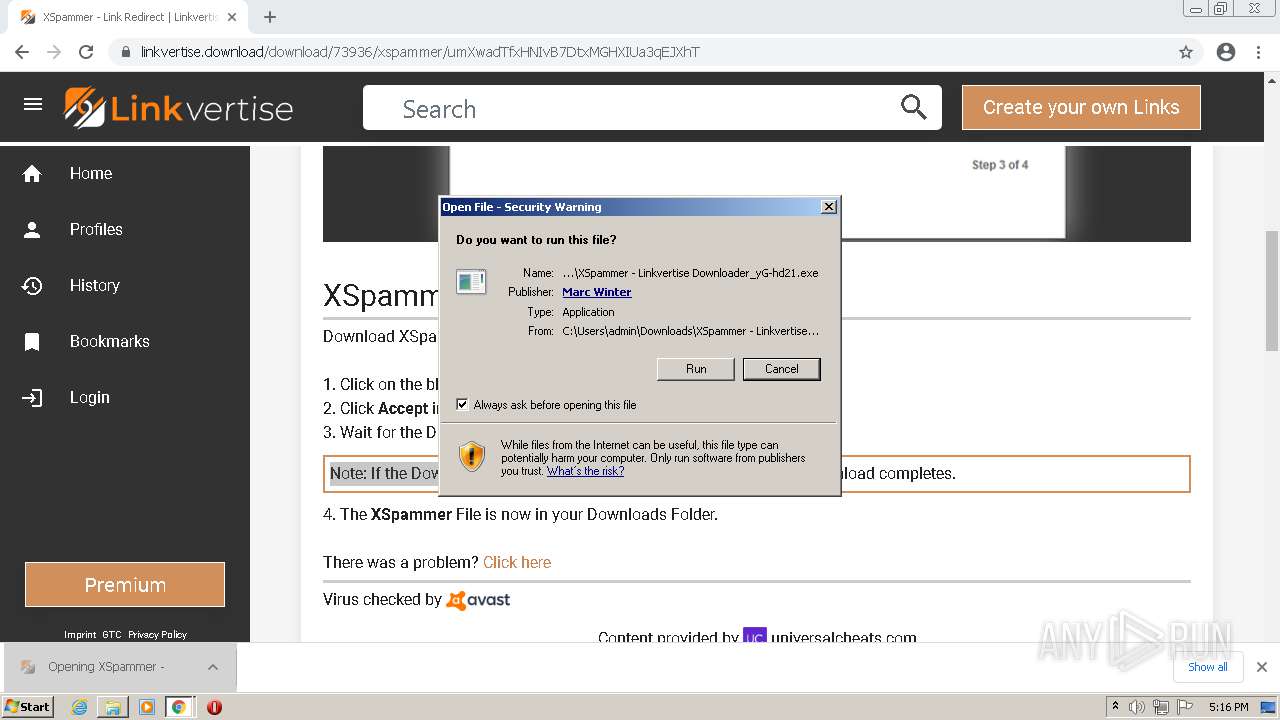
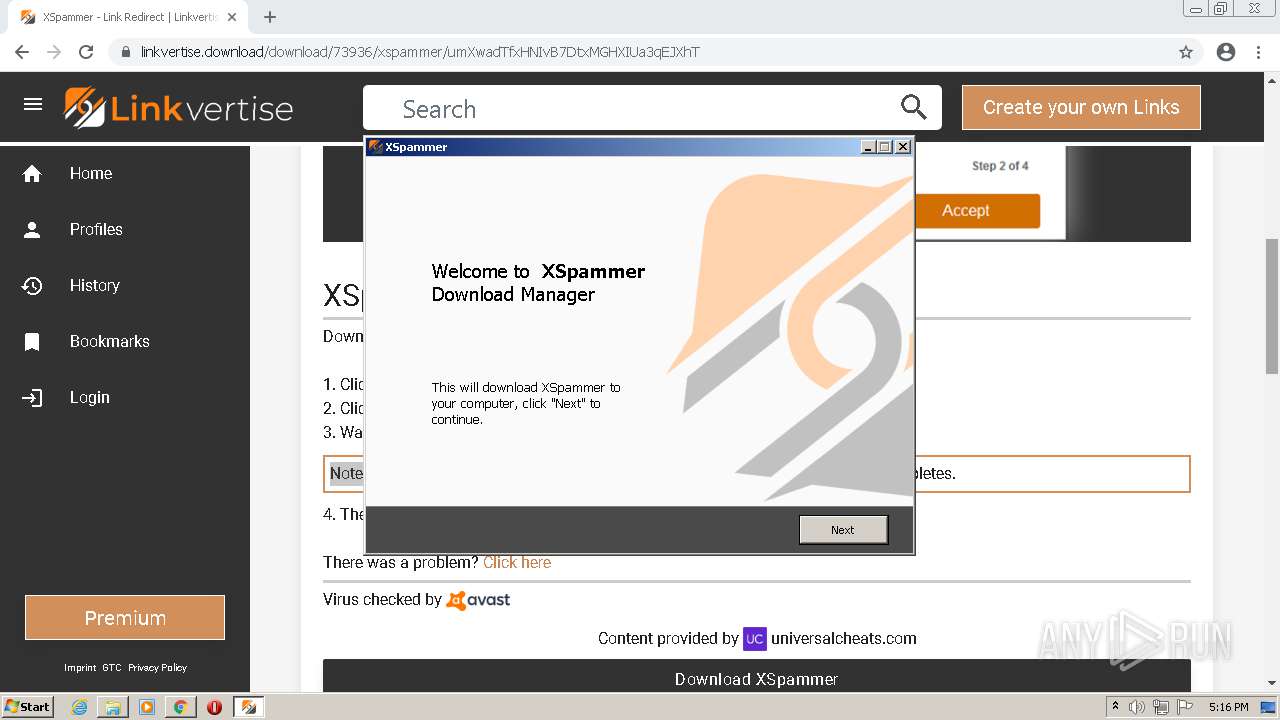
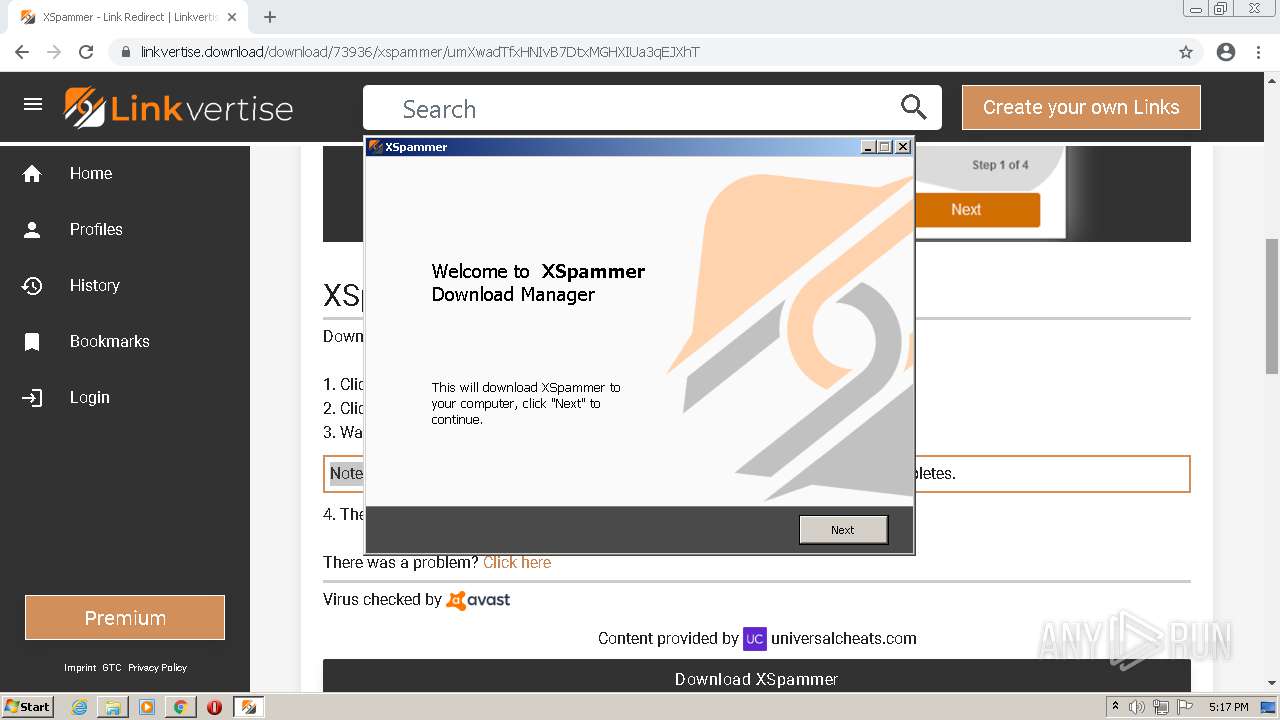
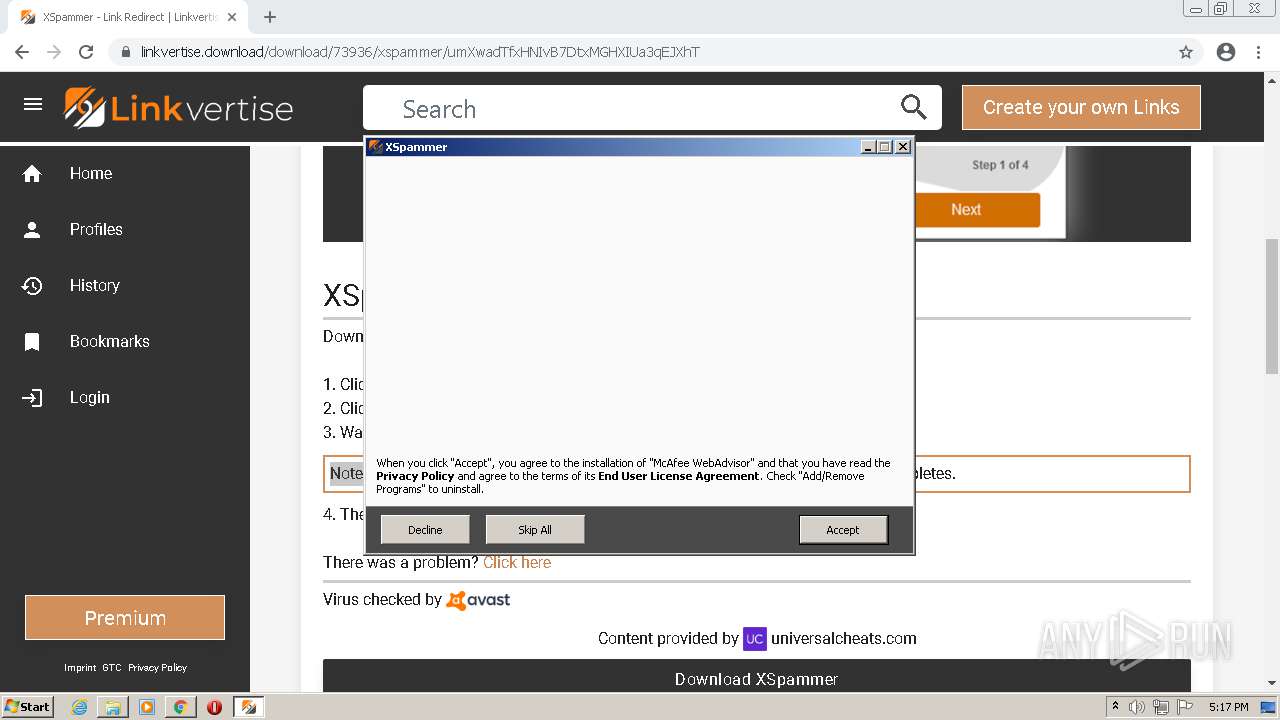
Application was dropped or rewritten from another process
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 592)
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 2576)
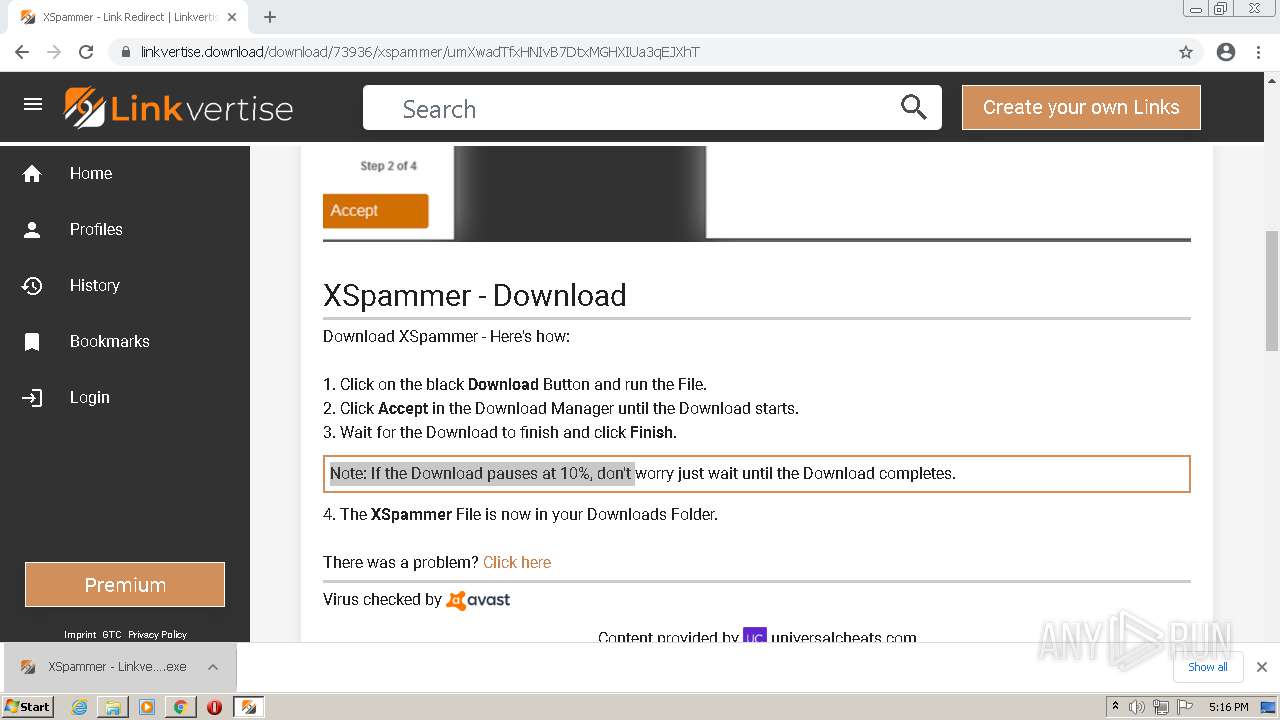
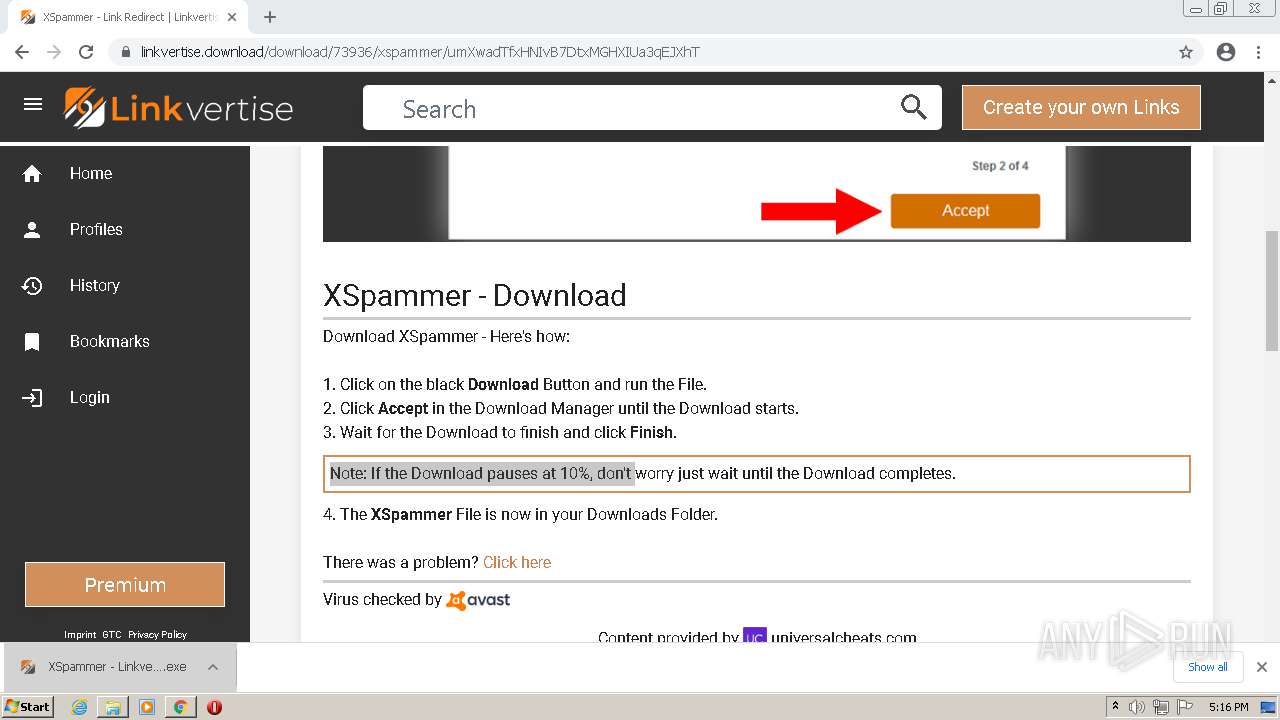
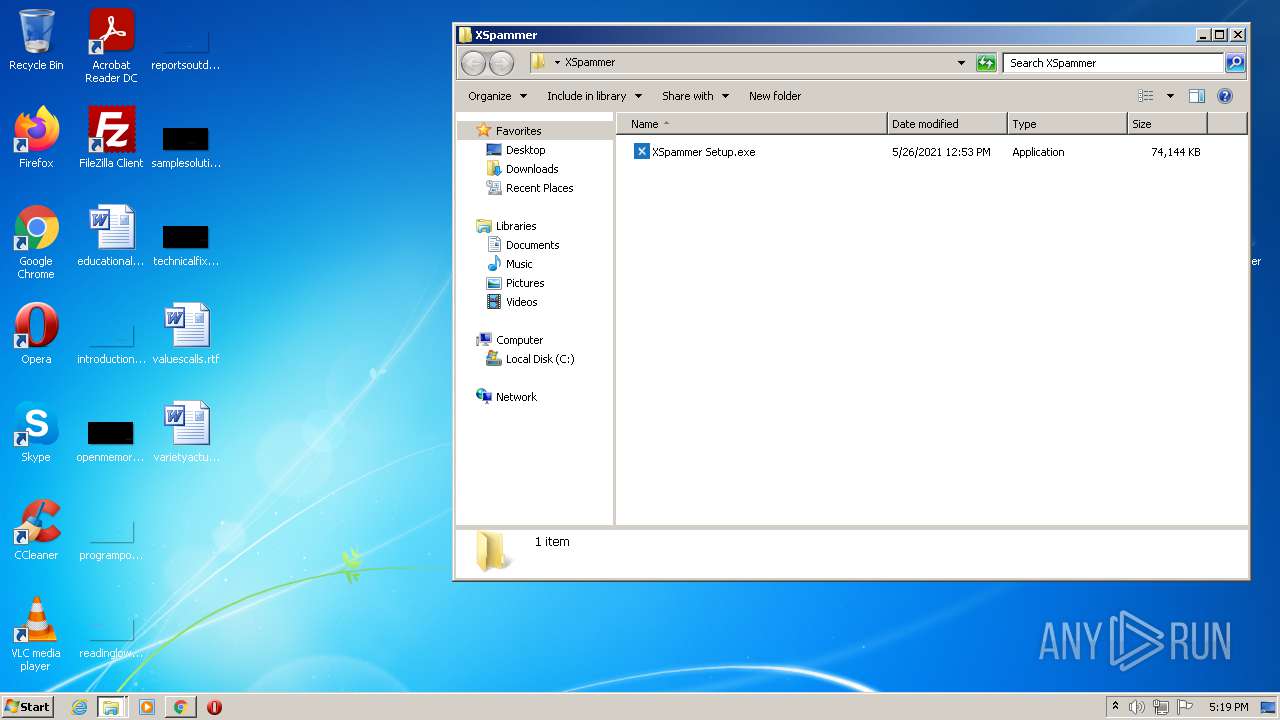
Drops executable file immediately after starts
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 592)
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 2576)
- XSpammer Setup.exe (PID: 1060)
Loads dropped or rewritten executable
- XSpammer Setup.exe (PID: 1060)
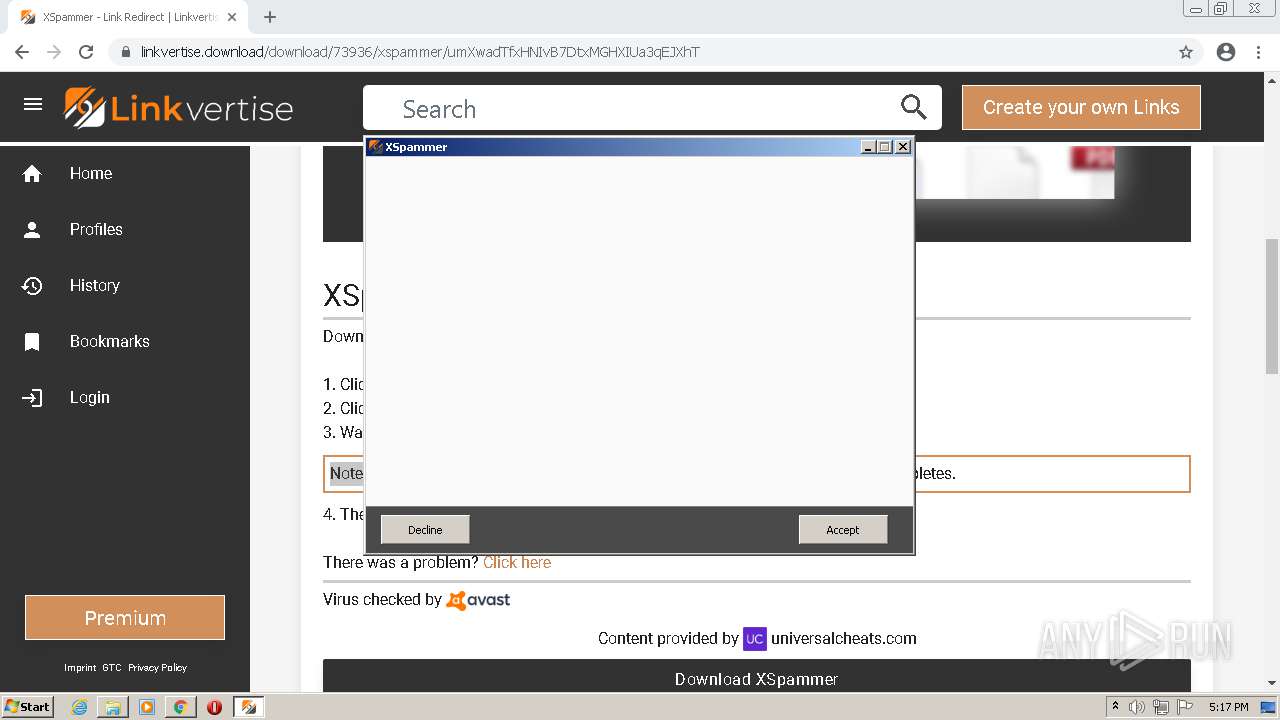
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4036)
- iexplore.exe (PID: 504)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2728)
Executable content was dropped or overwritten
- chrome.exe (PID: 2728)
- chrome.exe (PID: 544)
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 592)
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 2576)
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
- XSpammer Setup.exe (PID: 1060)
Checks supported languages
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 592)
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 3056)
- XSpammer - Linkvertise Downloader_yG-hd21.exe (PID: 2576)
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
- WinRAR.exe (PID: 268)
- XSpammer Setup.exe (PID: 1060)
Reads the computer name
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 3056)
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
- WinRAR.exe (PID: 268)
- XSpammer Setup.exe (PID: 1060)
Reads Windows owner or organization settings
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
Drops a file with too old compile date
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
Reads the Windows organization settings
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
Drops a file that was compiled in debug mode
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
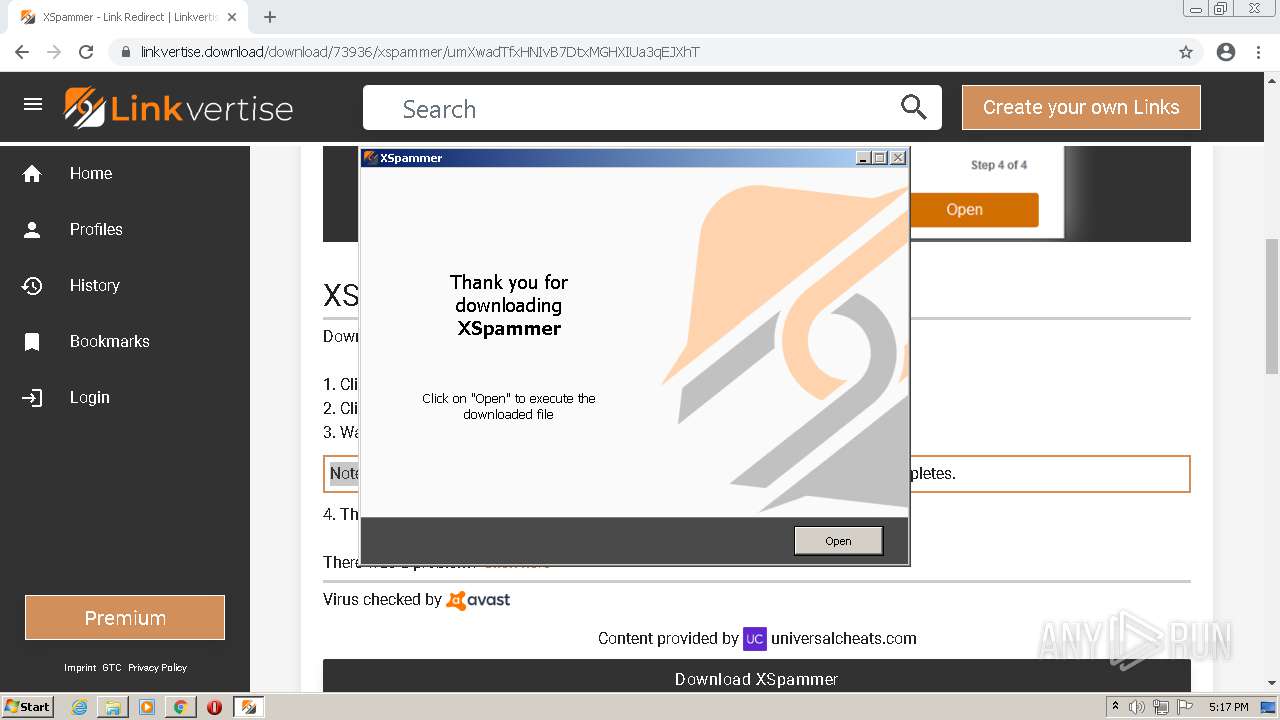
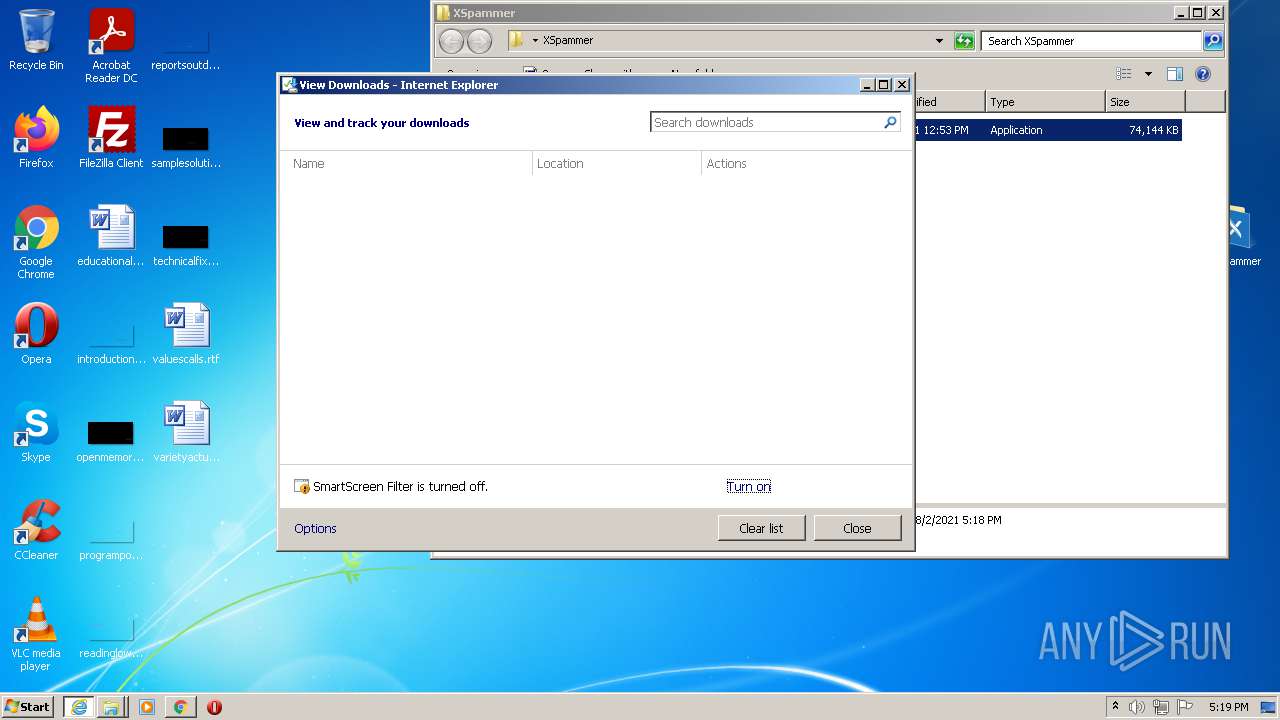
Starts Internet Explorer
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
INFO
Checks supported languages
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 4036)
- chrome.exe (PID: 544)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 648)
- chrome.exe (PID: 2804)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 280)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 740)
- chrome.exe (PID: 3684)
- explorer.exe (PID: 4084)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 1496)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2396)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 364)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 504)
- chrome.exe (PID: 2460)
- taskmgr.exe (PID: 2060)
Changes internet zones settings
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 2060)
Reads the computer name
- iexplore.exe (PID: 4036)
- iexplore.exe (PID: 2608)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 544)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 2804)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3932)
- explorer.exe (PID: 4084)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2396)
- chrome.exe (PID: 2824)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 504)
- taskmgr.exe (PID: 2060)
Application launched itself
- iexplore.exe (PID: 2608)
- chrome.exe (PID: 2728)
- iexplore.exe (PID: 2060)
Reads settings of System Certificates
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 4036)
- chrome.exe (PID: 544)
- chrome.exe (PID: 2728)
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 504)
Checks Windows Trust Settings
- iexplore.exe (PID: 4036)
- iexplore.exe (PID: 2608)
- chrome.exe (PID: 2728)
- iexplore.exe (PID: 504)
- iexplore.exe (PID: 2060)
Reads the date of Windows installation
- iexplore.exe (PID: 2608)
- chrome.exe (PID: 2092)
- iexplore.exe (PID: 2060)
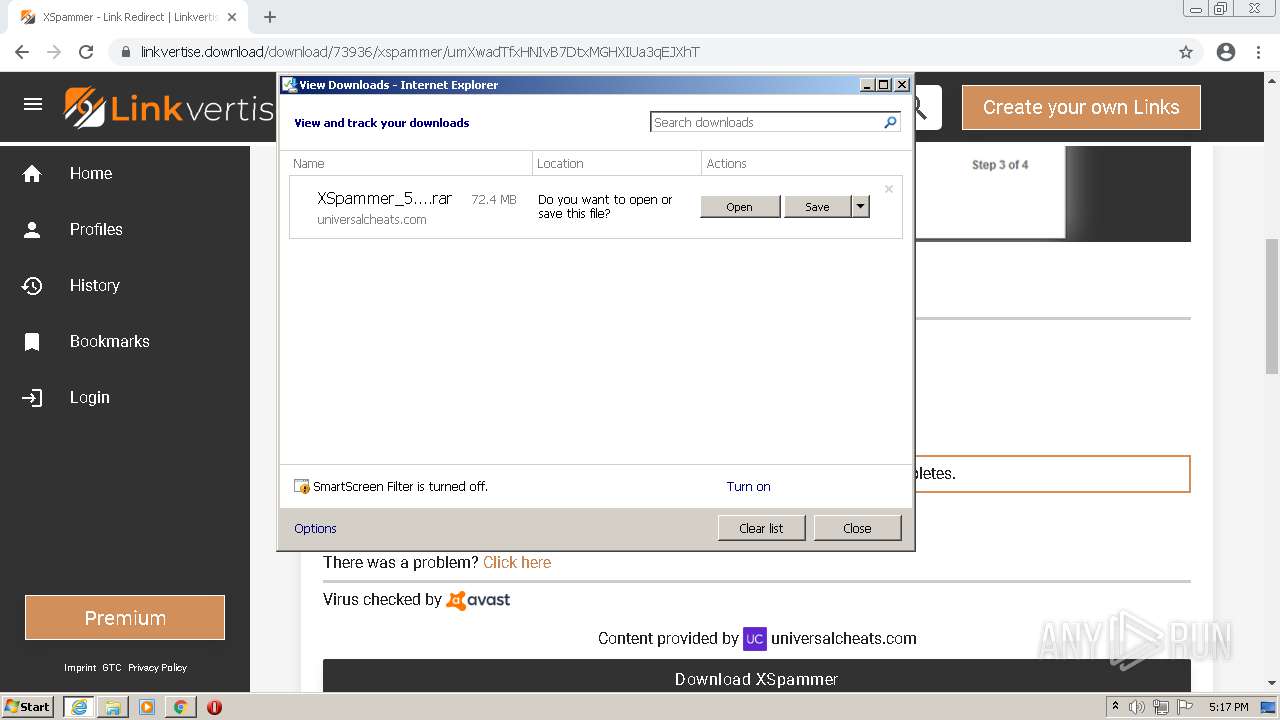
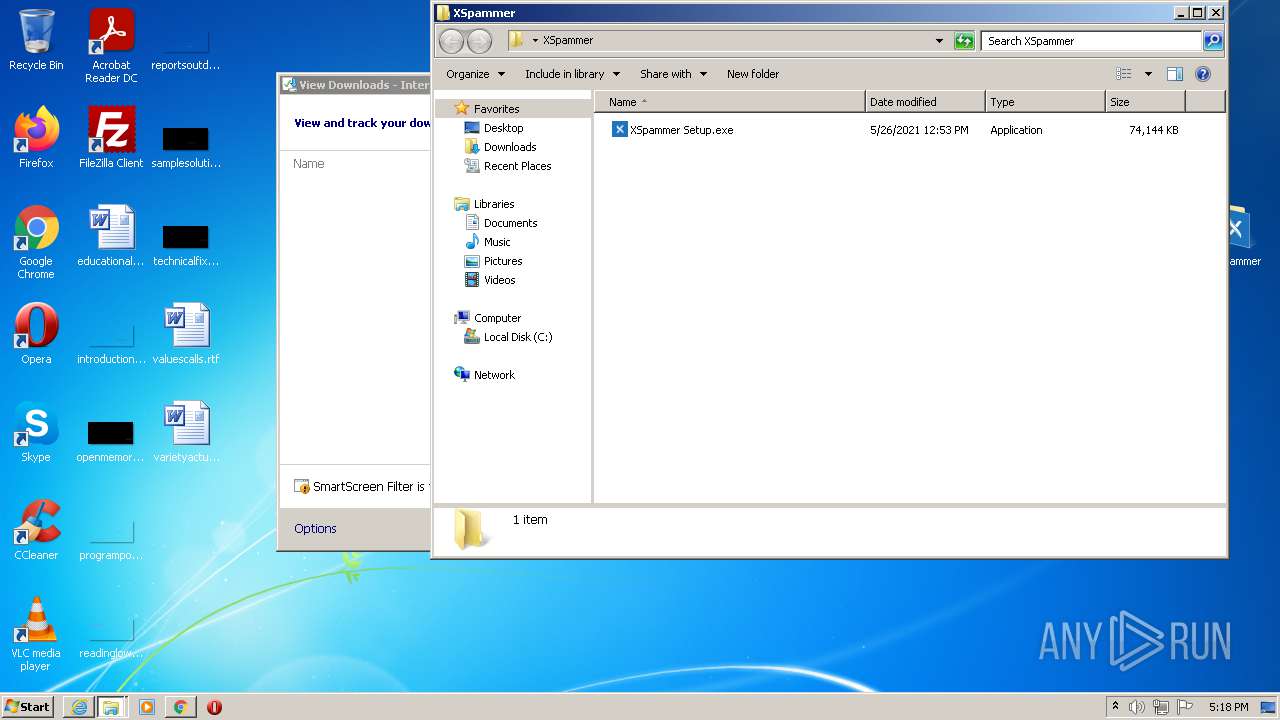
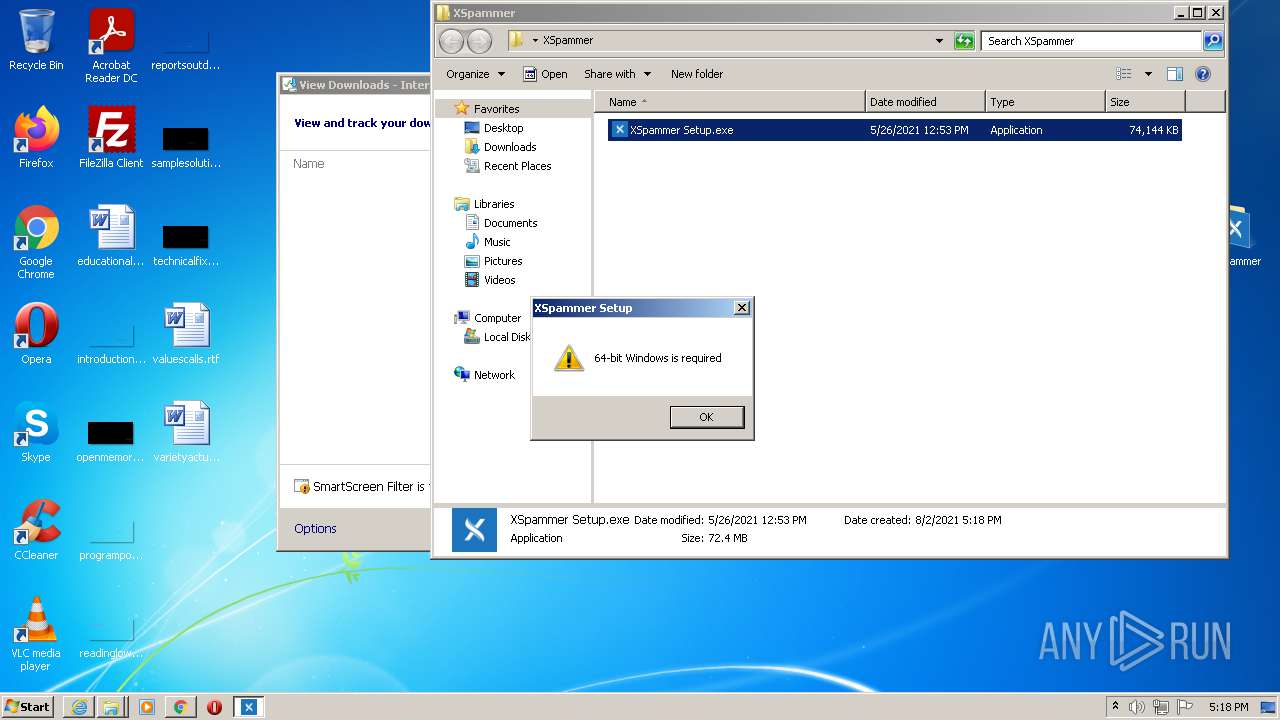
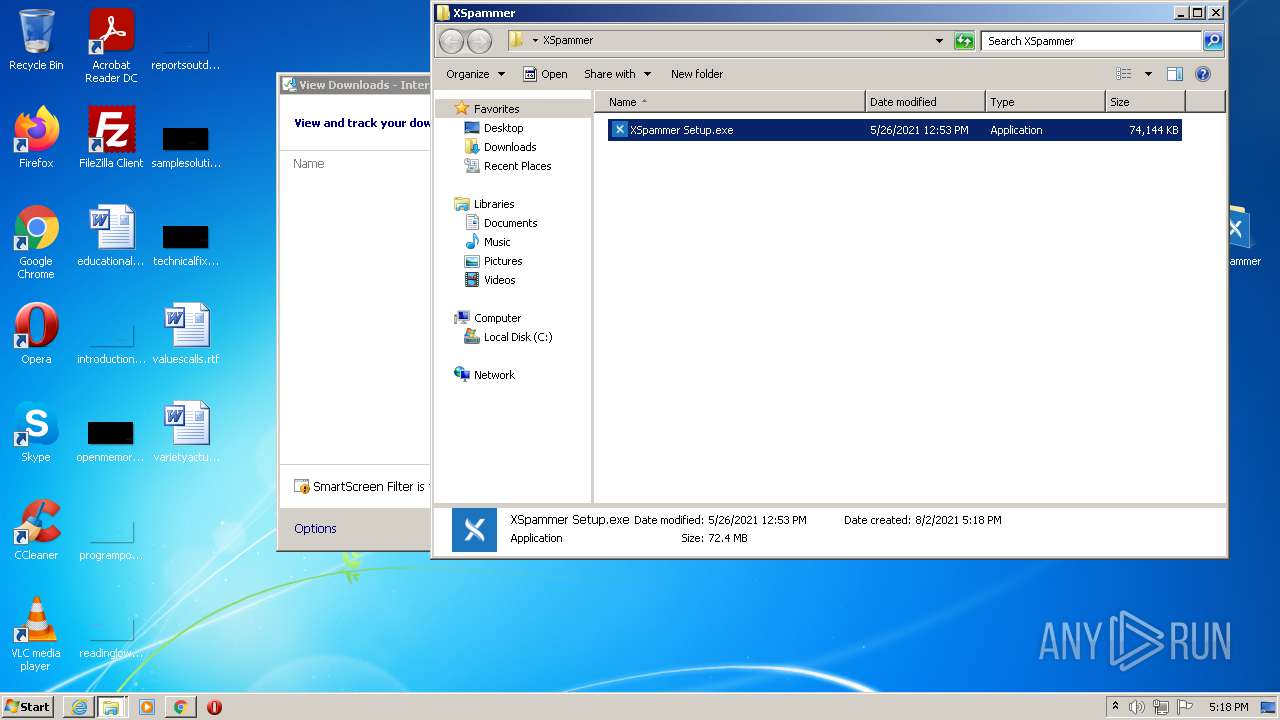
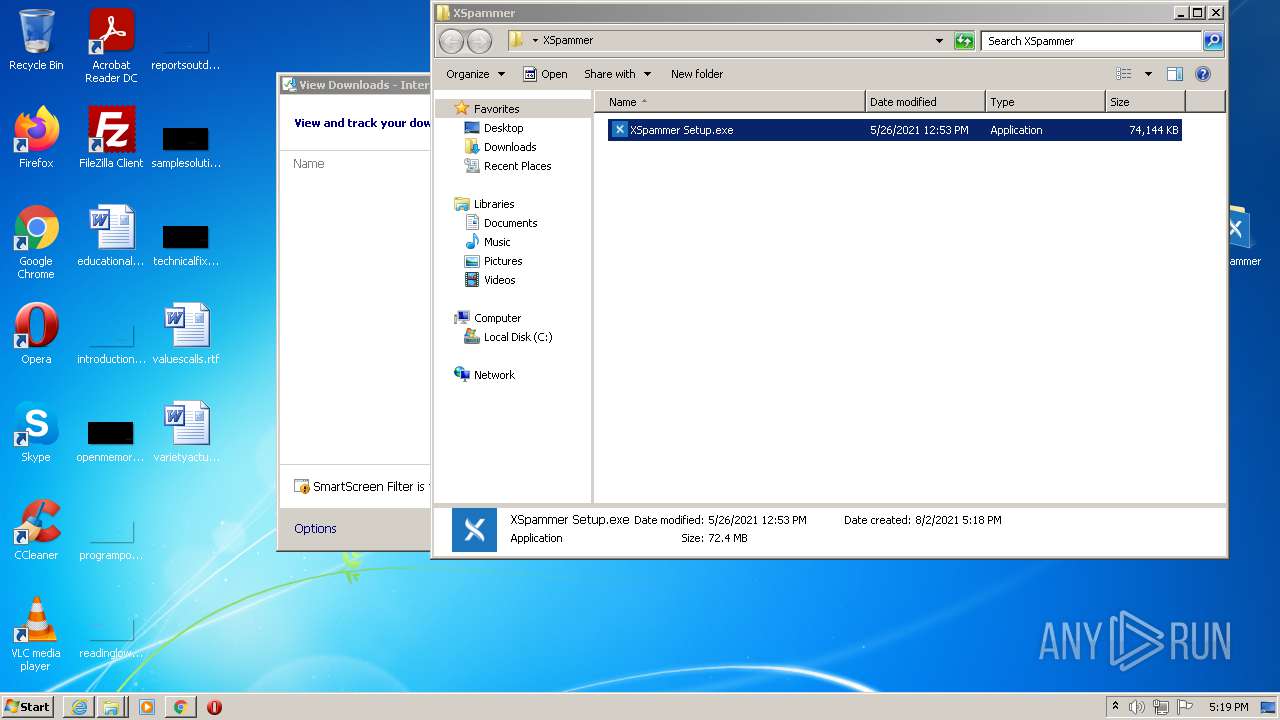
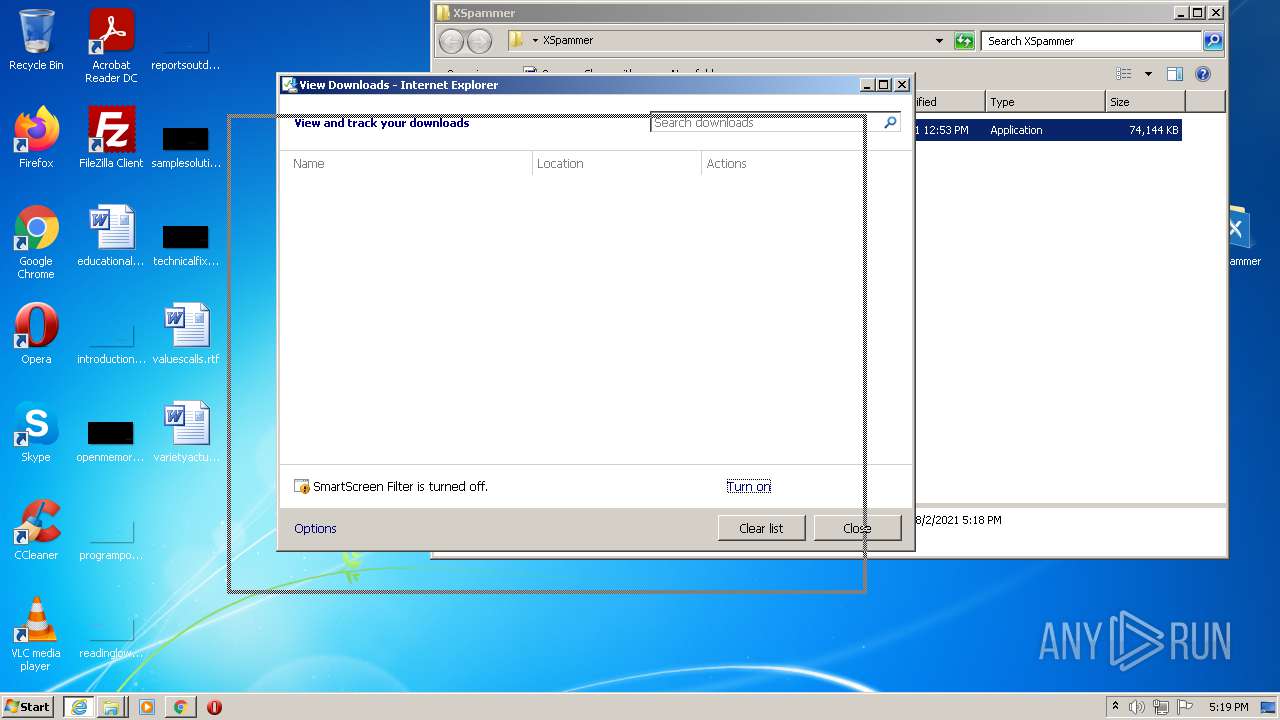
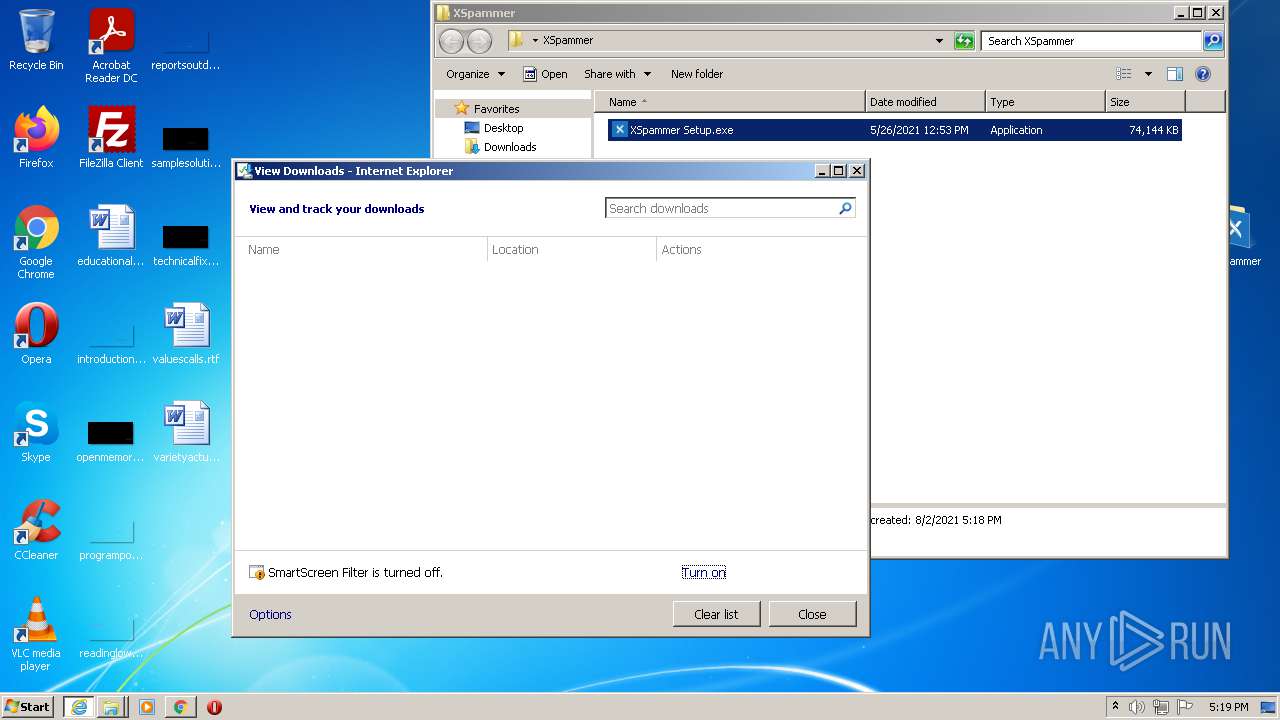
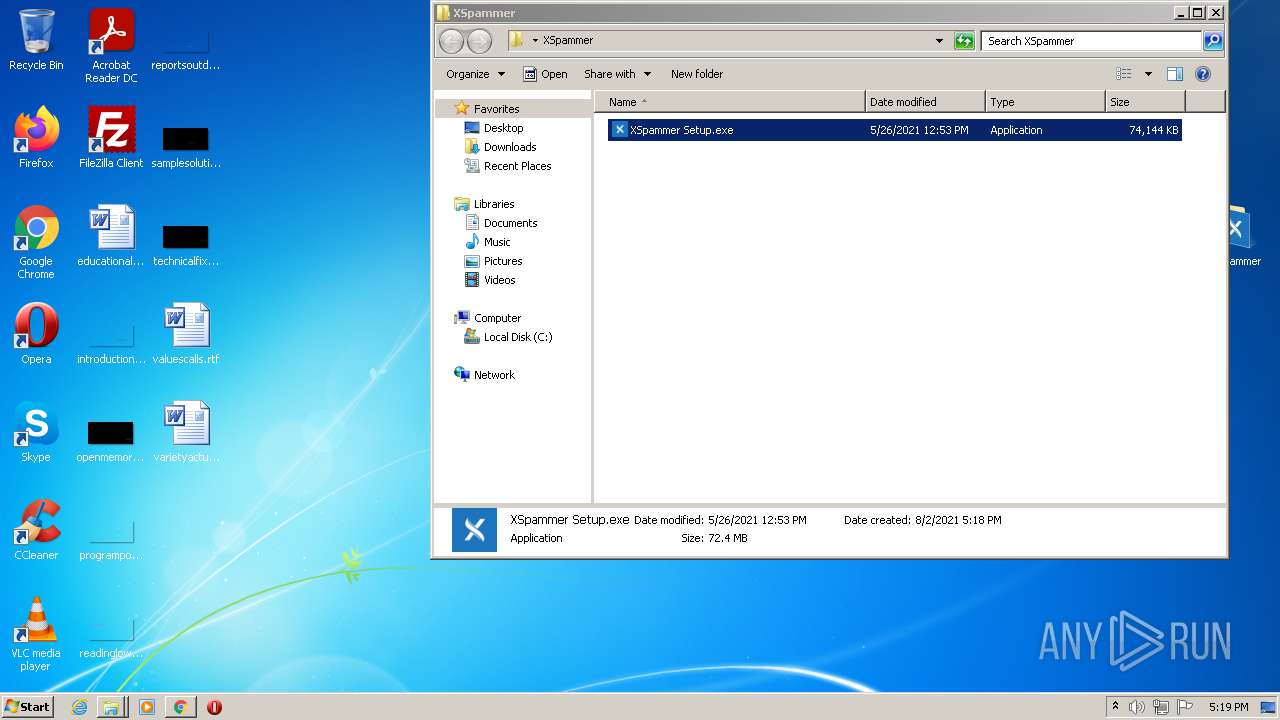
Manual execution by user
- chrome.exe (PID: 2728)
- explorer.exe (PID: 4084)
- XSpammer Setup.exe (PID: 1060)
- taskmgr.exe (PID: 2060)
Reads the hosts file
- chrome.exe (PID: 2728)
- chrome.exe (PID: 544)
Changes settings of System certificates
- chrome.exe (PID: 544)
- iexplore.exe (PID: 2060)
Application was dropped or rewritten from another process
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 3056)
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
Loads dropped or rewritten executable
- XSpammer - Linkvertise Downloader_yG-hd21.tmp (PID: 2540)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2060)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2060)
Creates files in the user directory
- iexplore.exe (PID: 2060)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
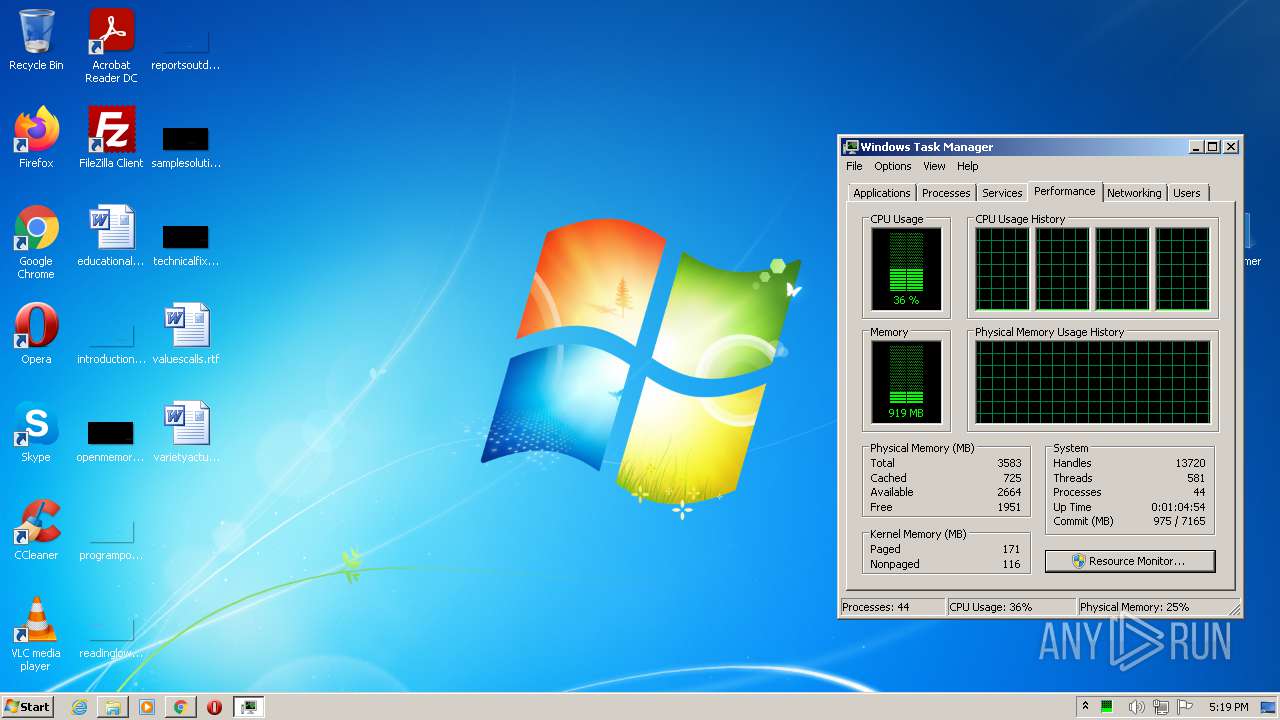
Total processes
97
Monitored processes
51
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
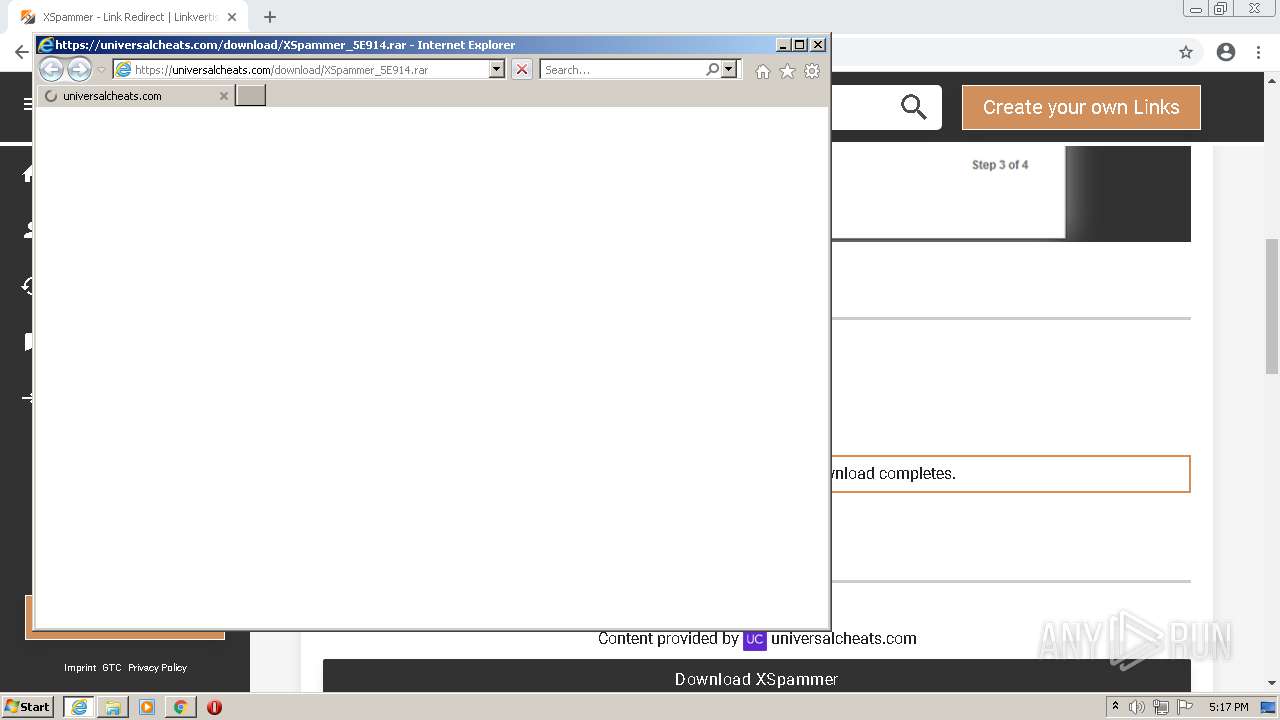
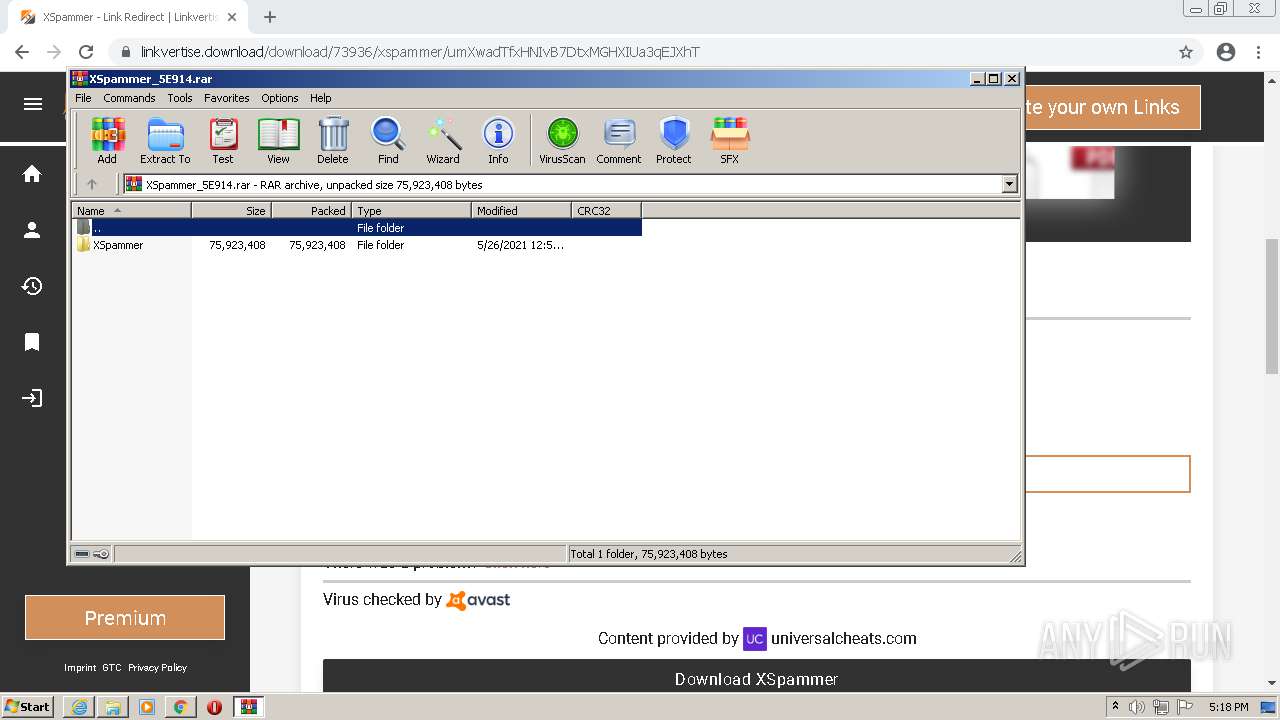
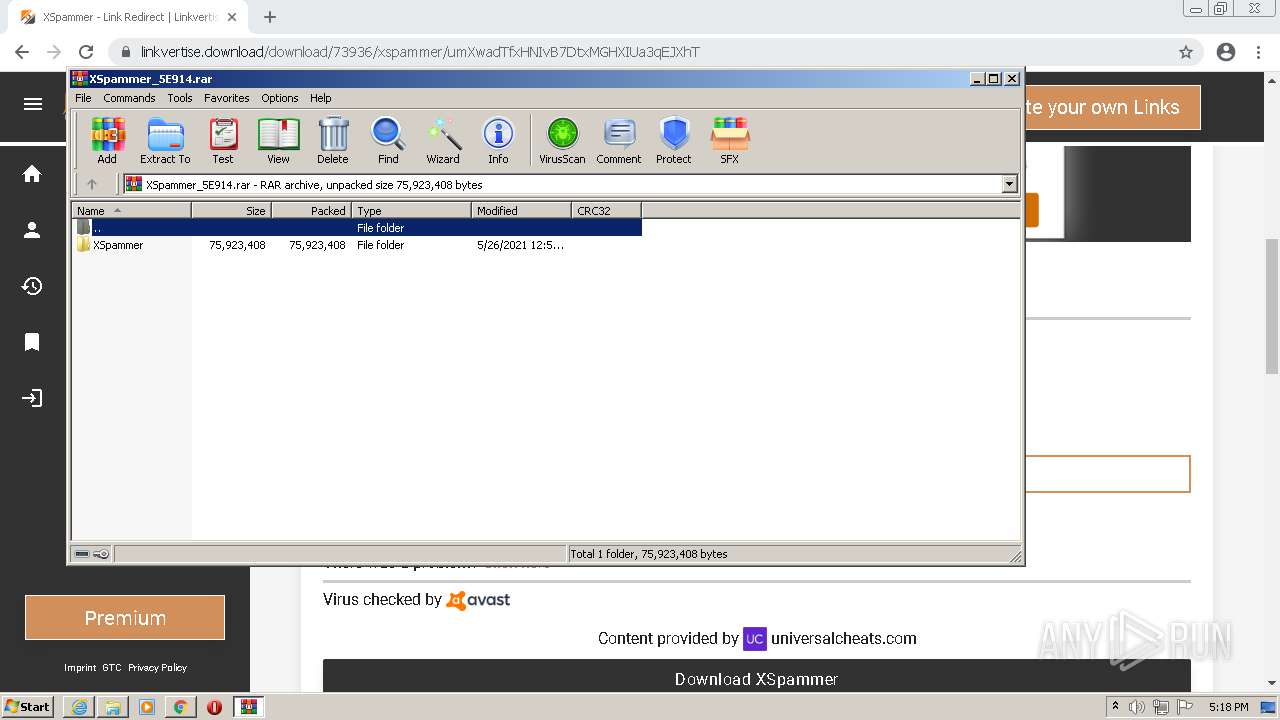
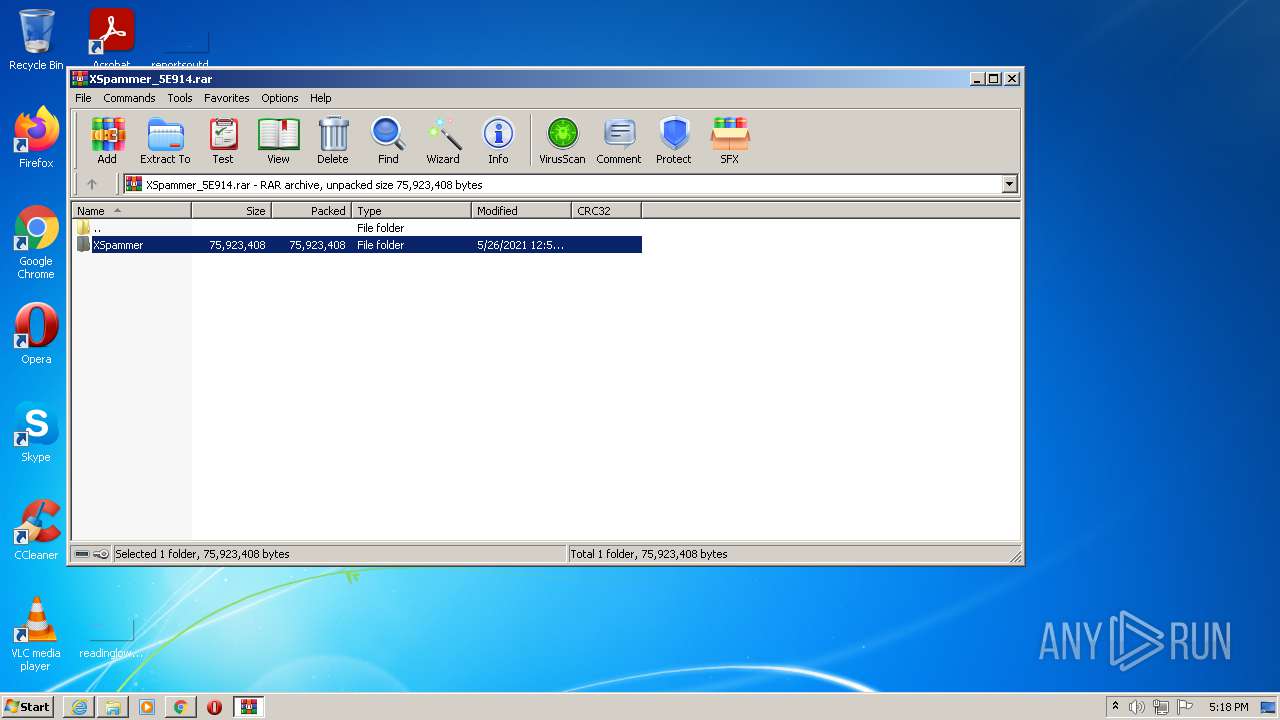
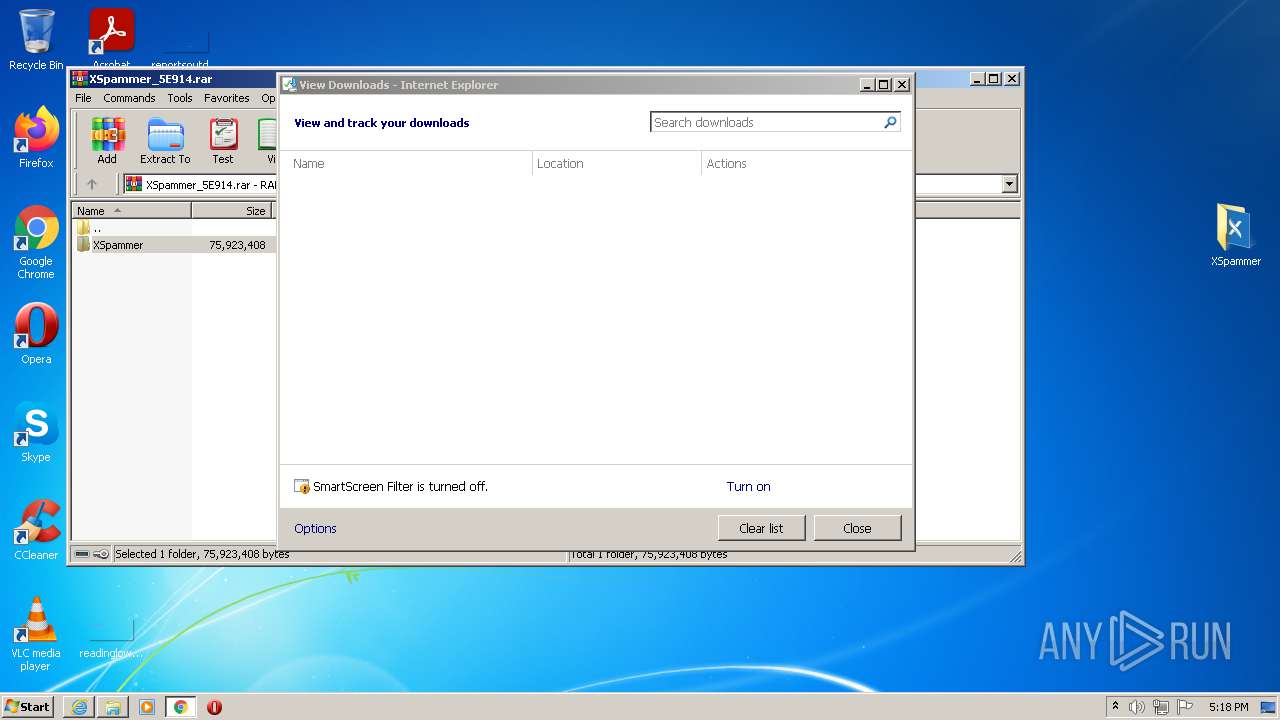
| 268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\XSpammer_5E914.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,4404791895560796337,12992134674830711863,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,4404791895560796337,12992134674830711863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2060 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1036,4404791895560796337,12992134674830711863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 592 | "C:\Users\admin\Downloads\XSpammer - Linkvertise Downloader_yG-hd21.exe" | C:\Users\admin\Downloads\XSpammer - Linkvertise Downloader_yG-hd21.exe | chrome.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Marc Winter Exit code: 0 Version: 1.4.1 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,4404791895560796337,12992134674830711863,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,4404791895560796337,12992134674830711863,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1060 | "C:\Users\admin\Desktop\XSpammer\XSpammer Setup.exe" | C:\Users\admin\Desktop\XSpammer\XSpammer Setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: Indxgo Development Integrity Level: MEDIUM Description: A feature-packed nuke bot with a slick and modern user-interface. Exit code: 2 Version: 1.0.0 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,4404791895560796337,12992134674830711863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4140 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
57 792
Read events
57 340
Write events
436
Delete events
16
Modification events
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902201 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902201 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
9
Suspicious files
199
Text files
295
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61081A02-AA8.pma | — | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{BD34BA32-F3AC-11EB-8F0C-18C4897E77EE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF36A5EE36AA4834DF.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA5AA2867F235EBA4.TMP | gmc | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF3F0E51D9A429267.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{C5D6DE17-F3AC-11EB-8F0C-18C4897E77EE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA2ADBAB6EABDCE6A.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
236
DNS requests
146
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
904 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
904 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/deblni2wo6646pqyb633d2jvlm_2021.7.19.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2021.7.19.1143_all_bjn6q745zymzjliphpkxmd63hu.crx3 | US | — | — | whitelisted |
904 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 2.85 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 7.50 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 10.0 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 21.0 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 43.5 Kb | whitelisted |
504 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2608 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 88.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4036 | iexplore.exe | 104.21.21.174:443 | linkvertise.com | Cloudflare Inc | US | unknown |
4036 | iexplore.exe | 8.248.135.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2608 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4036 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2608 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
544 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
544 | chrome.exe | 142.250.74.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
544 | chrome.exe | 142.250.185.164:443 | www.google.com | Google Inc. | US | whitelisted |
544 | chrome.exe | 172.67.199.168:443 | linkvertise.com | — | US | malicious |
544 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
linkvertise.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |