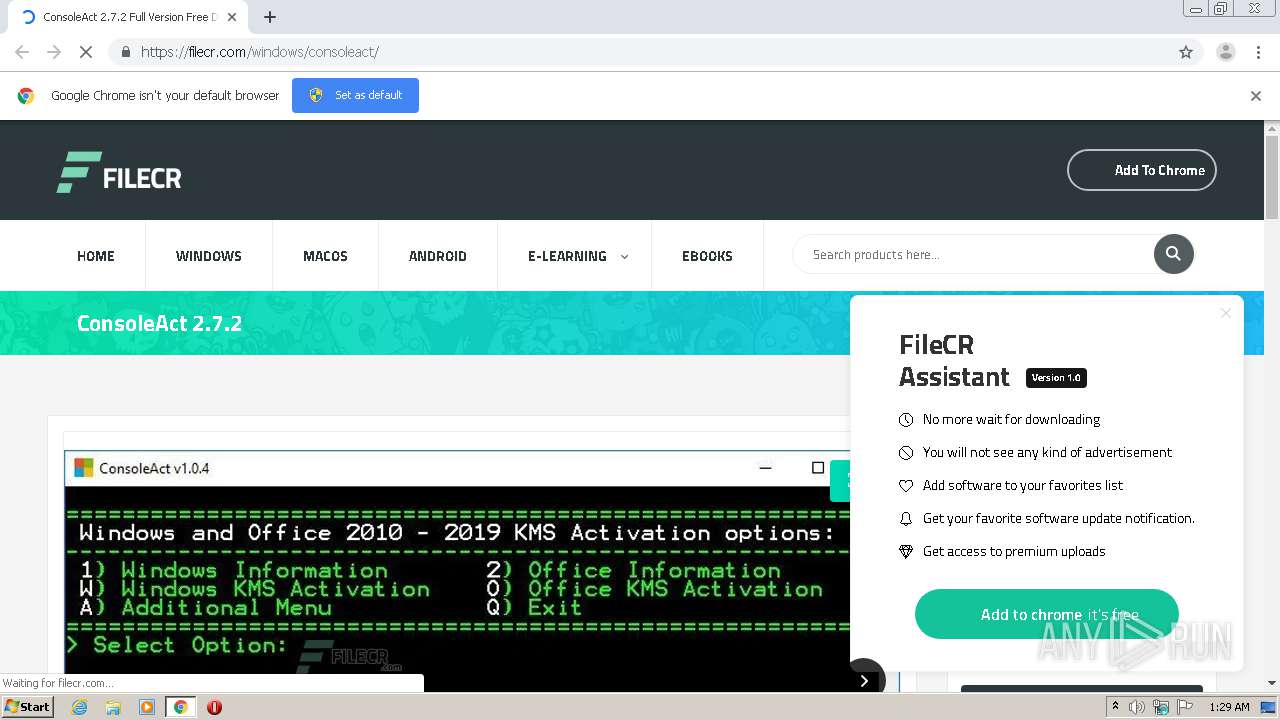
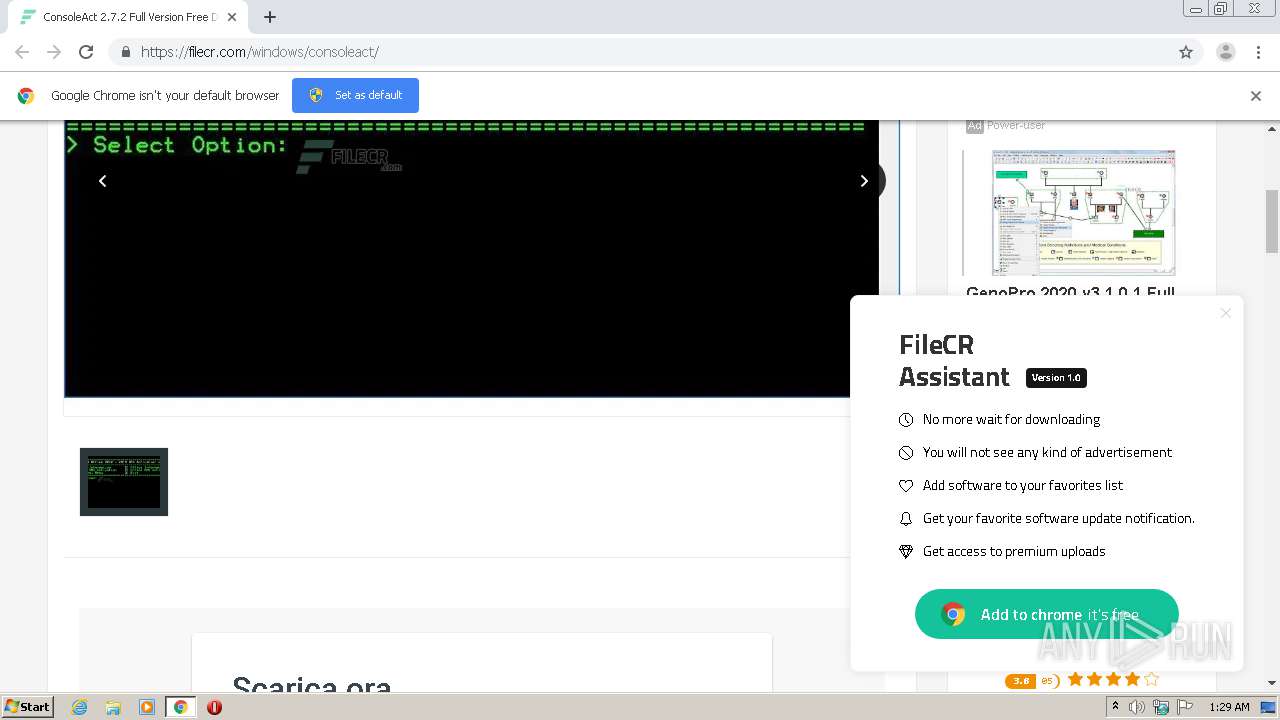
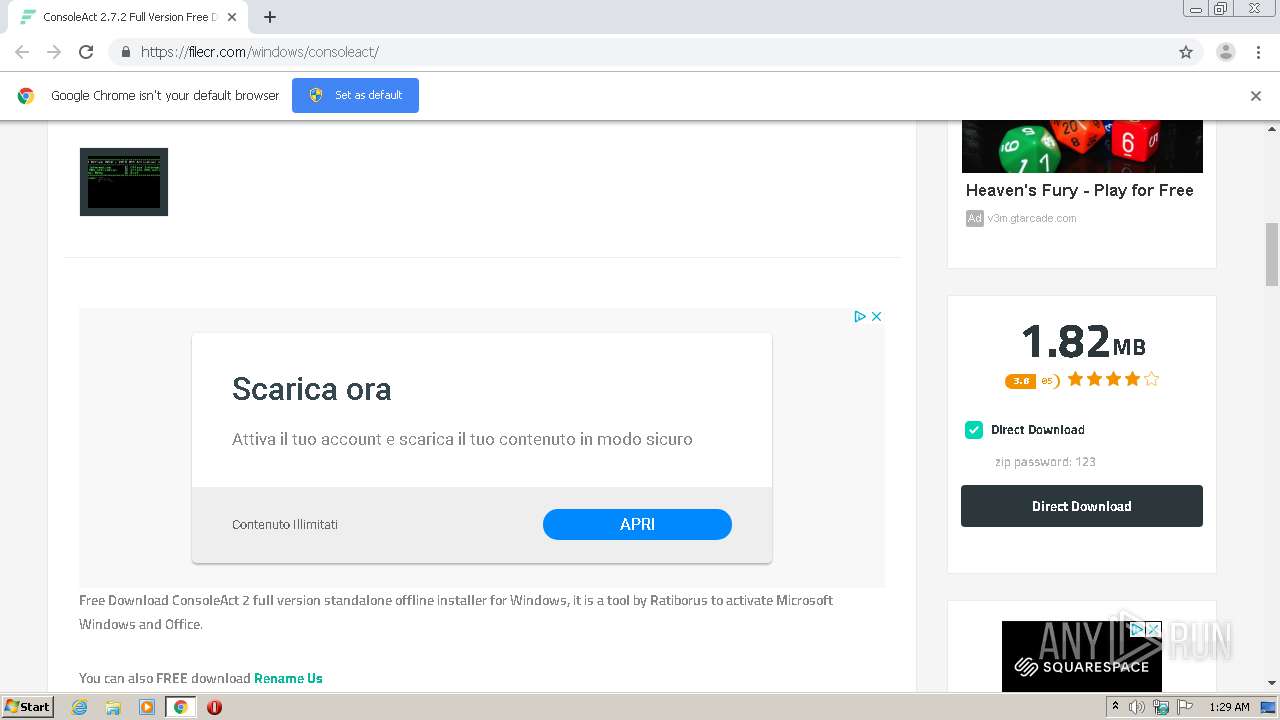
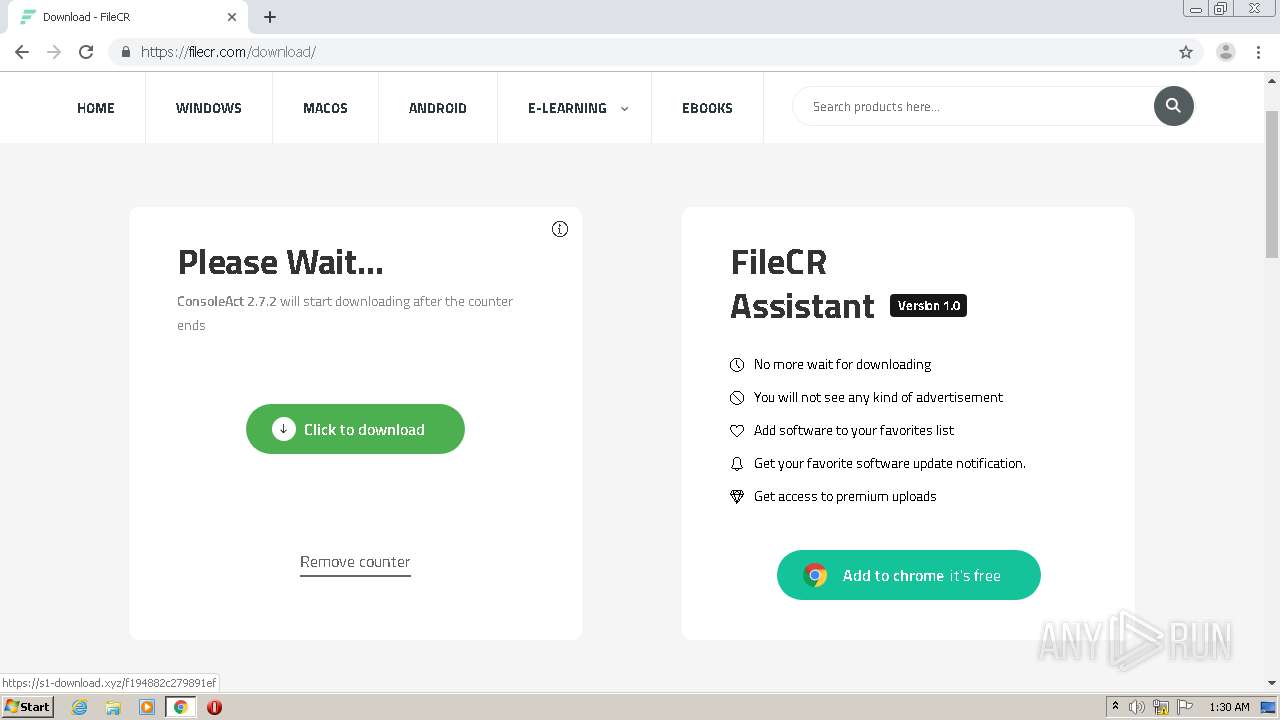
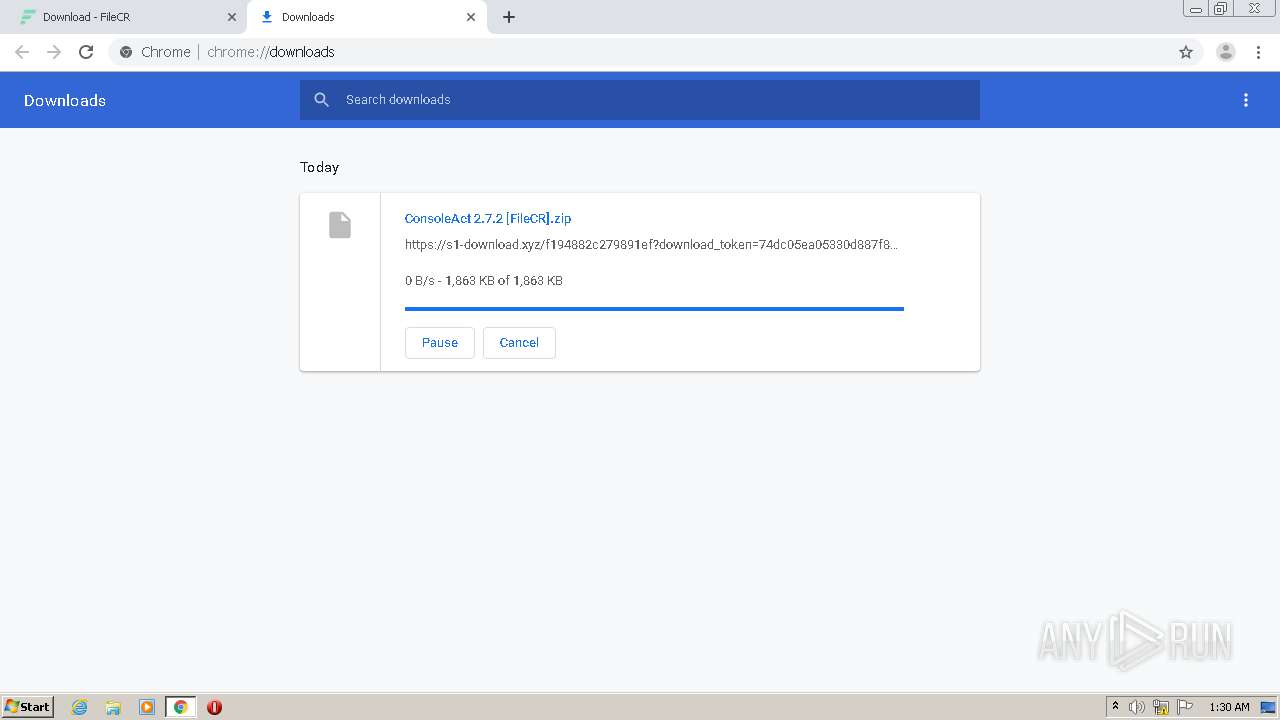
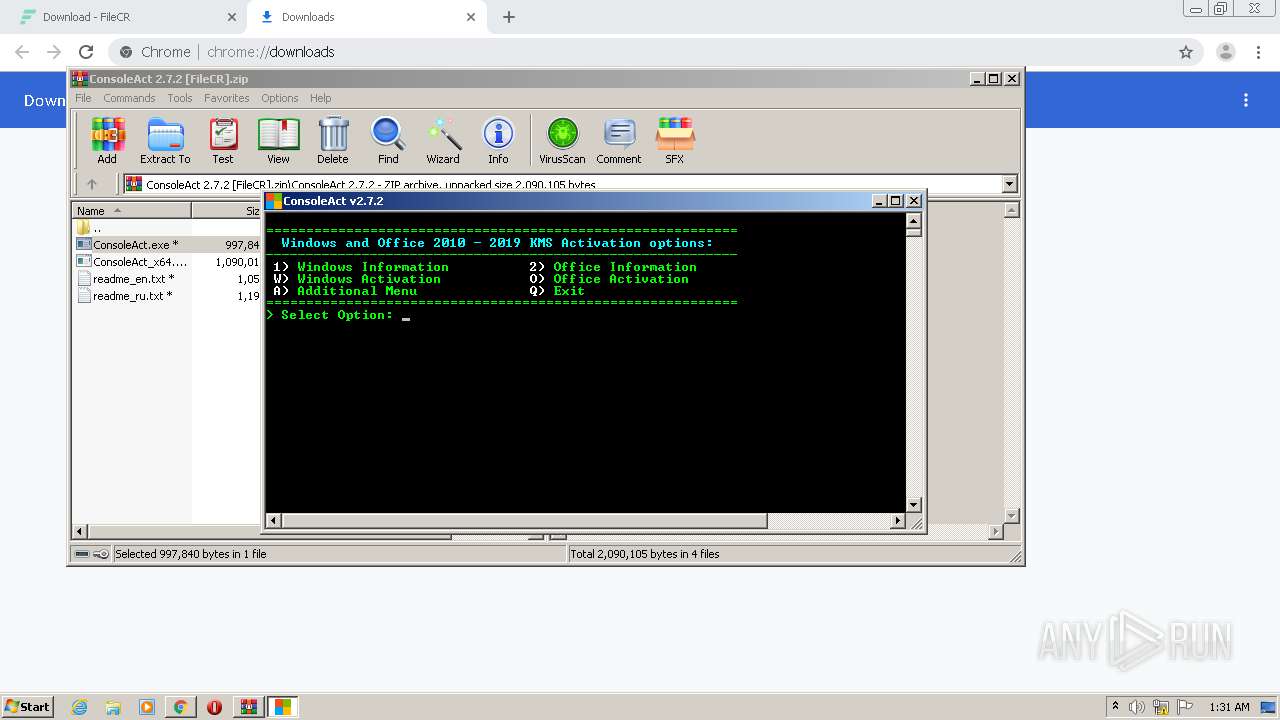
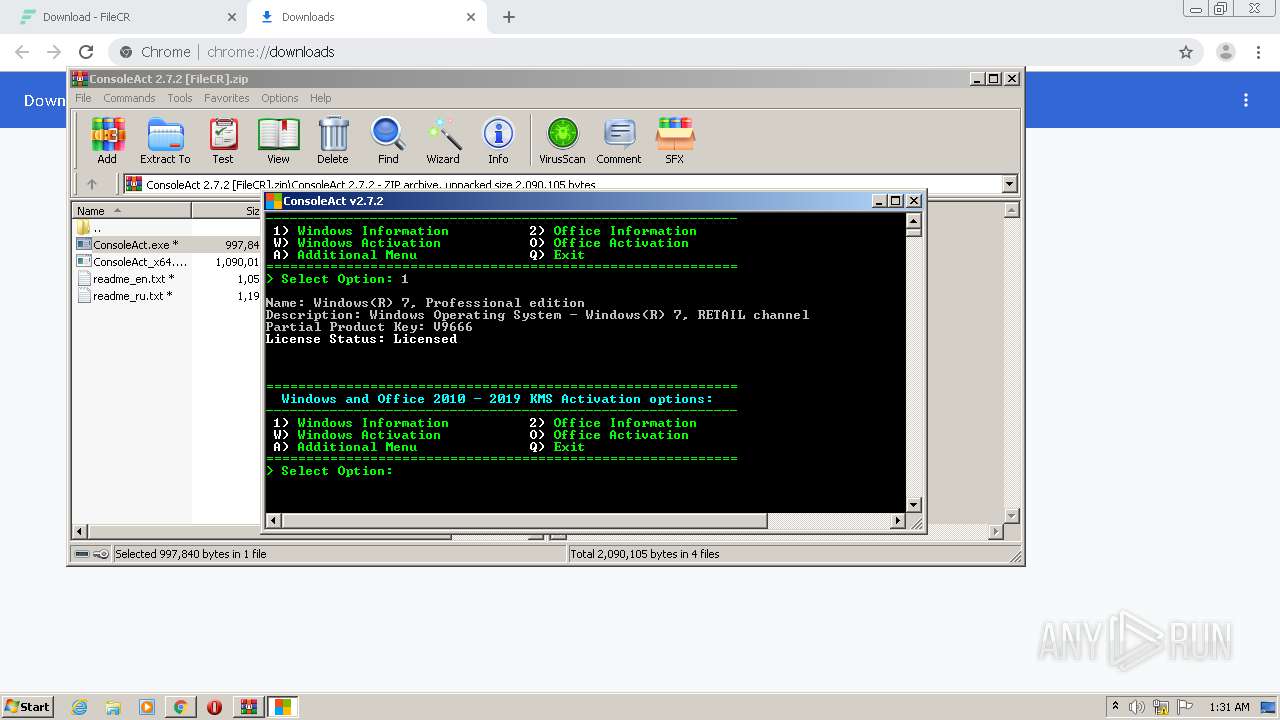
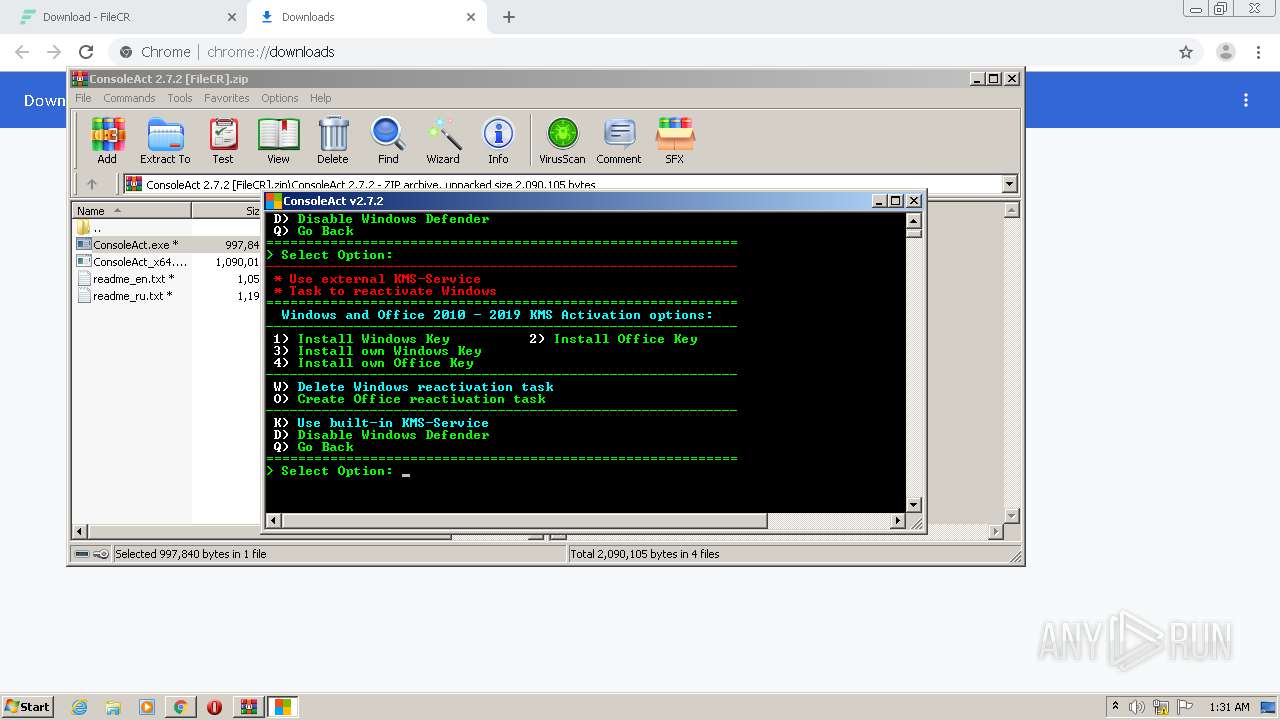
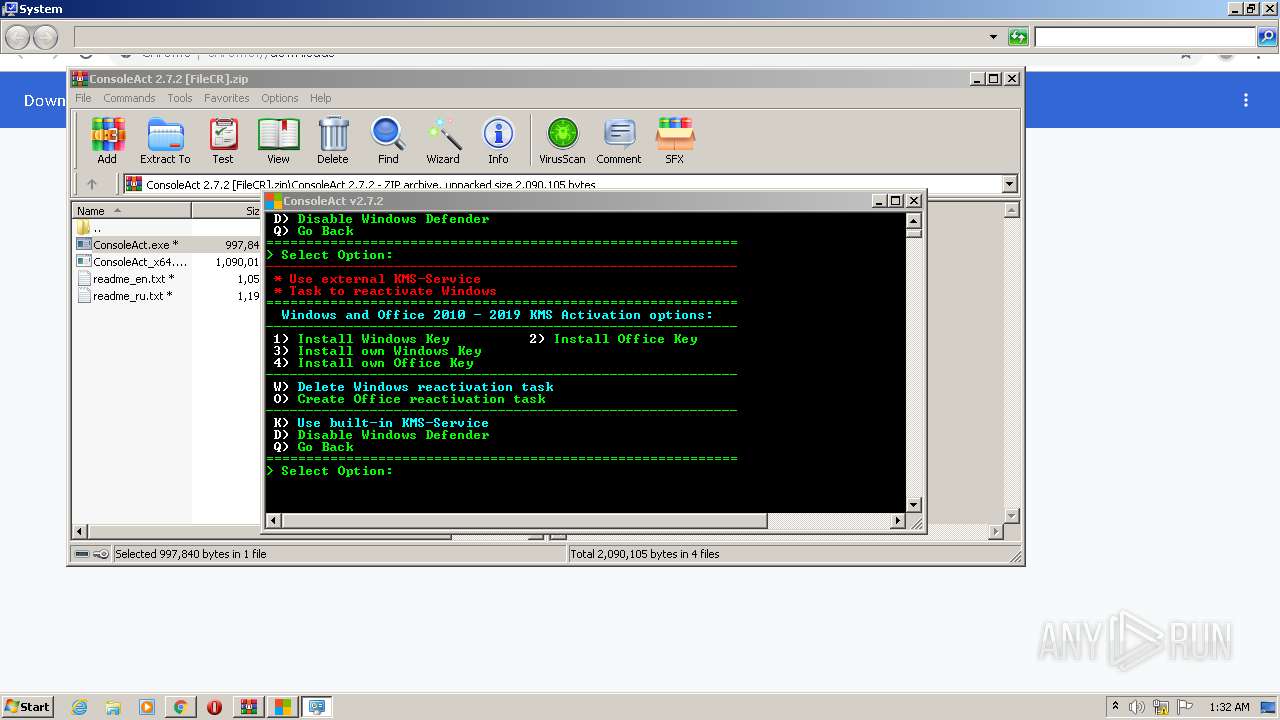
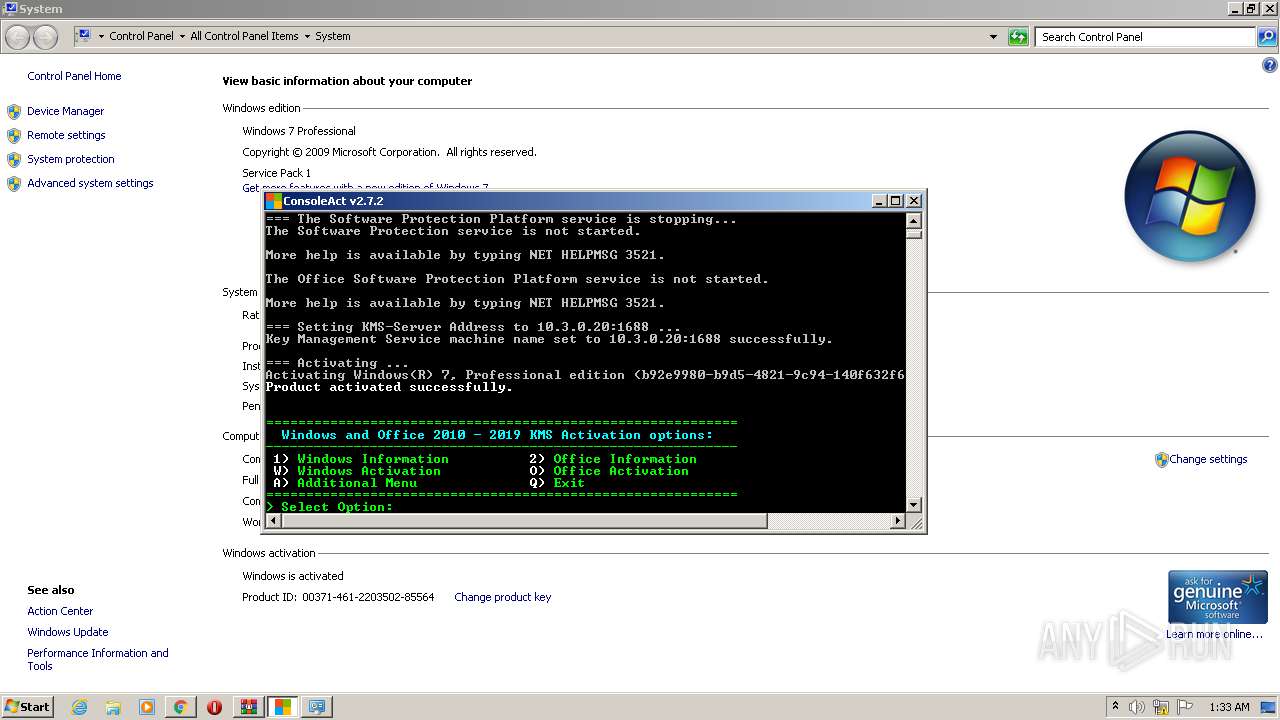
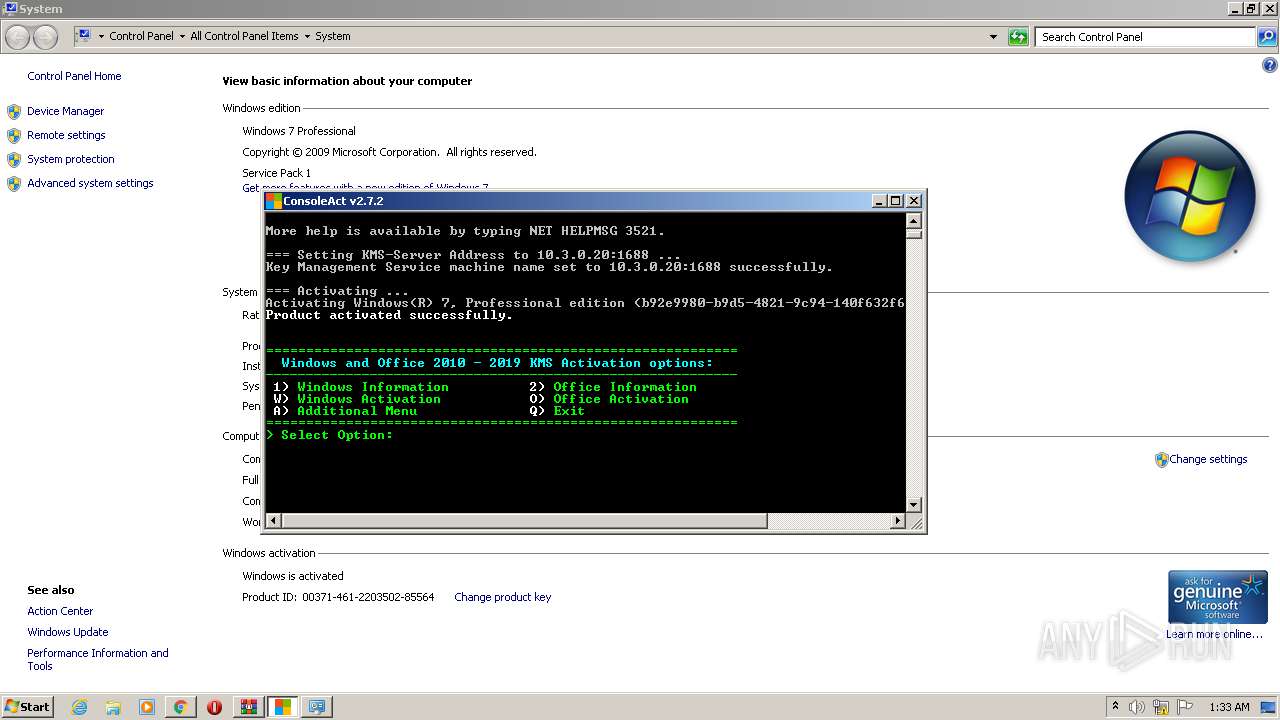
| URL: | https://filecr.com/windows/consoleact/ |
| Full analysis: | https://app.any.run/tasks/39b6bbe2-542d-424b-b73e-de9d7ca7d41c |
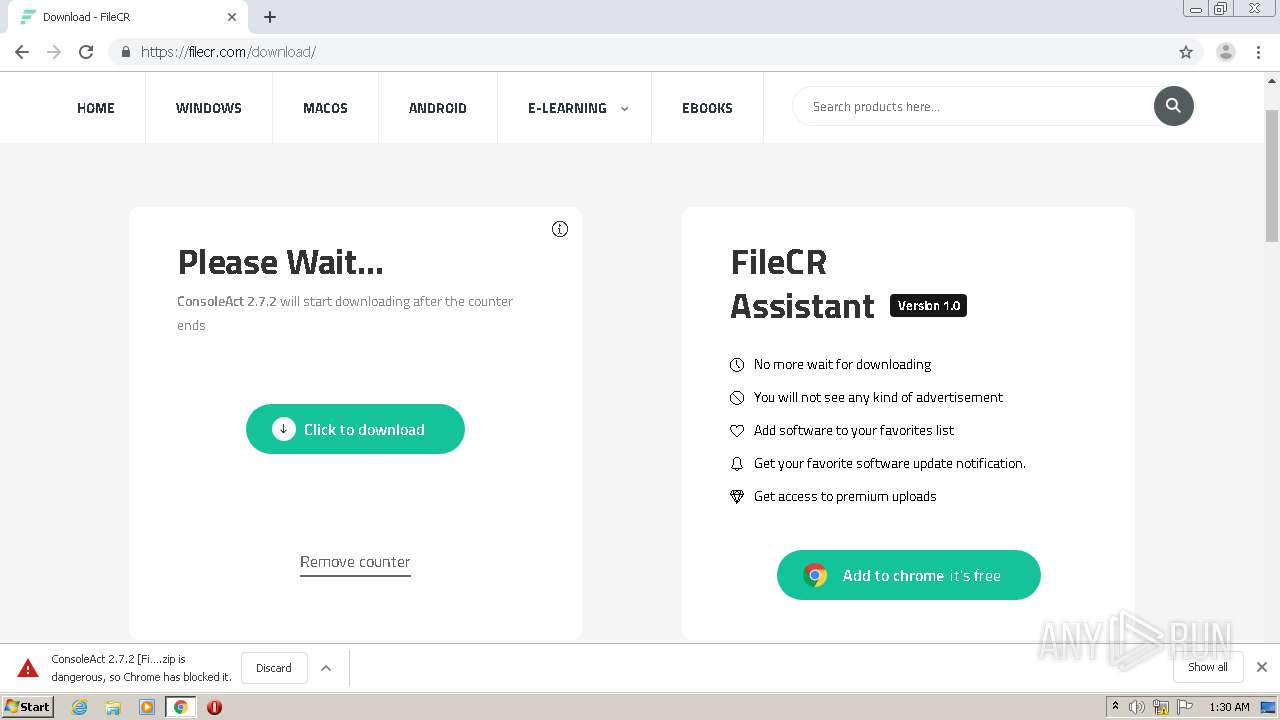
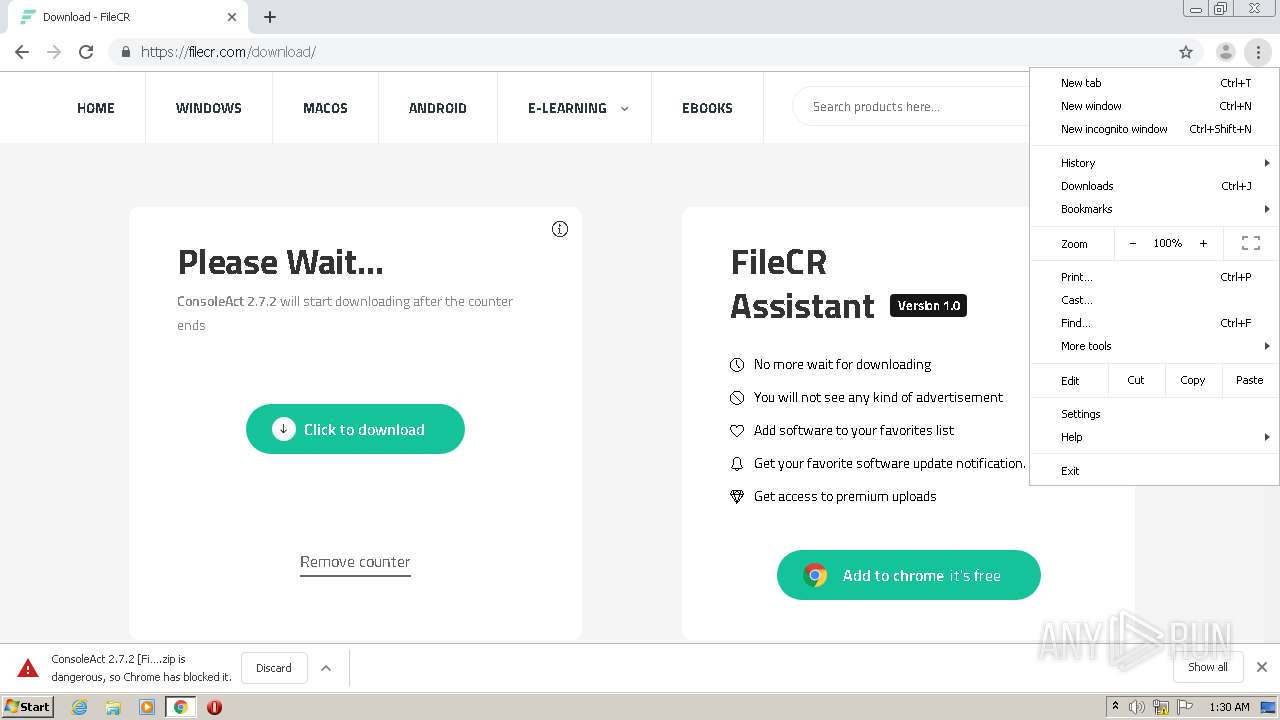
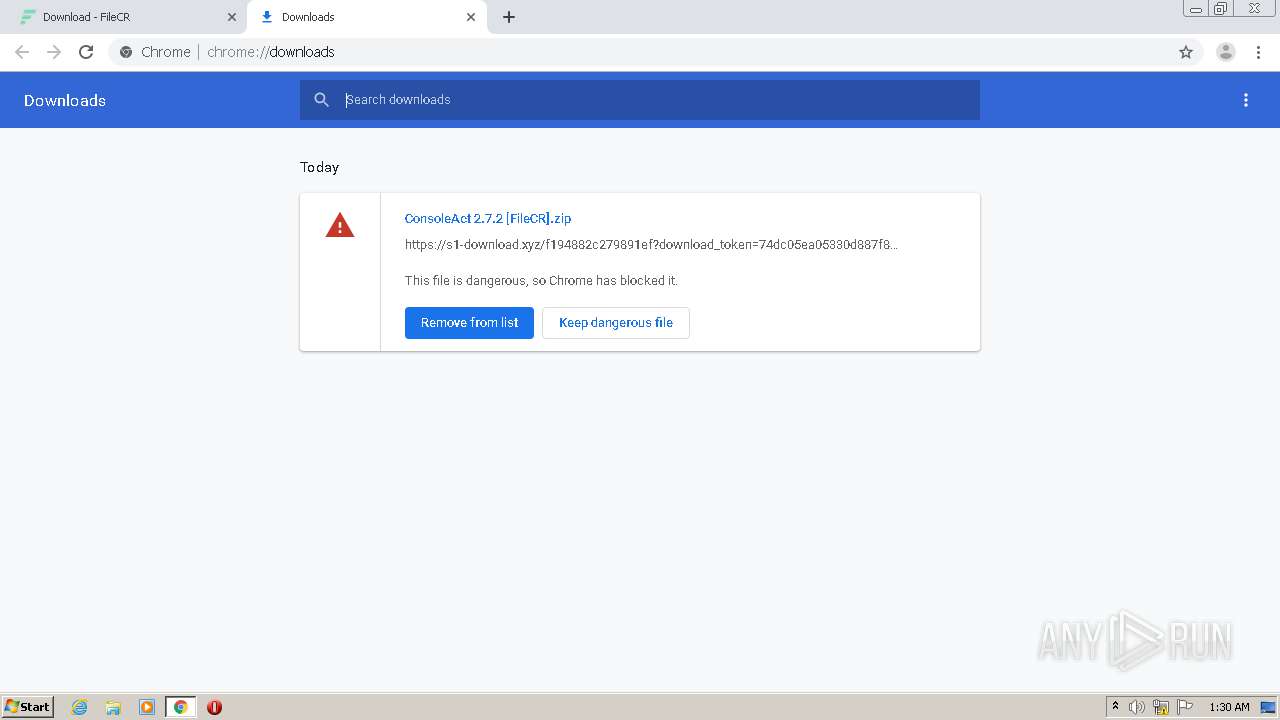
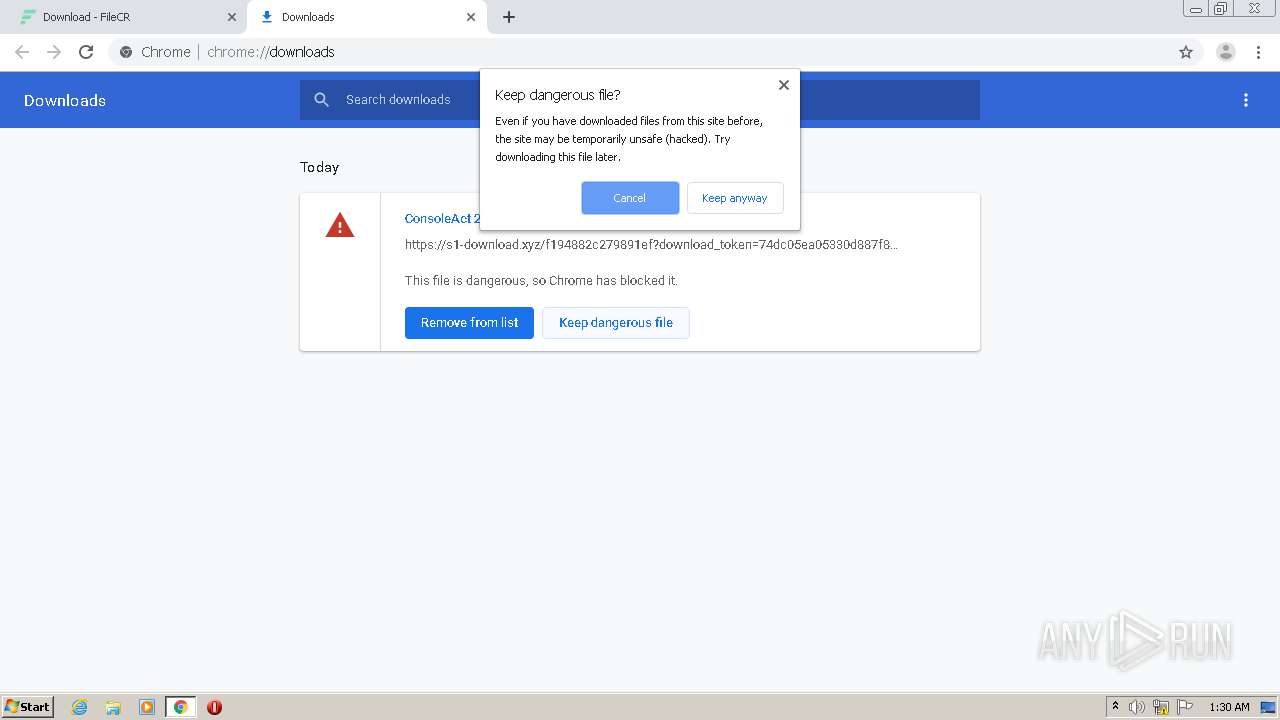
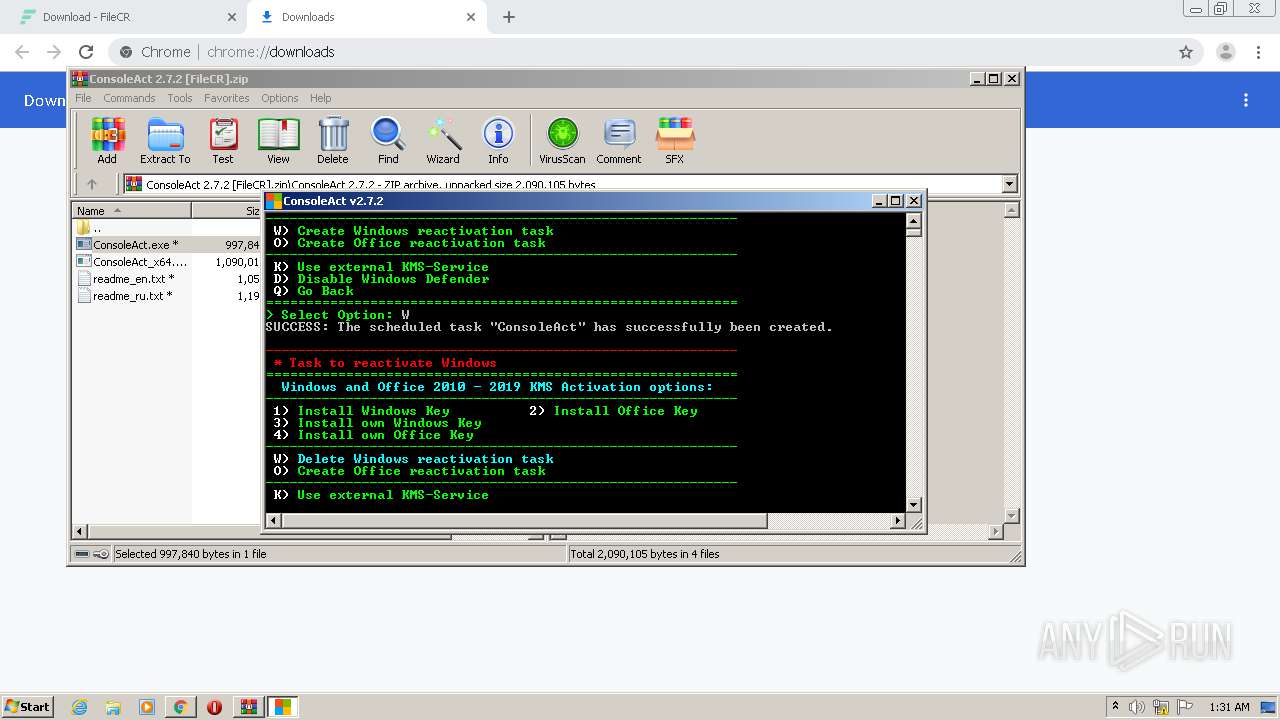
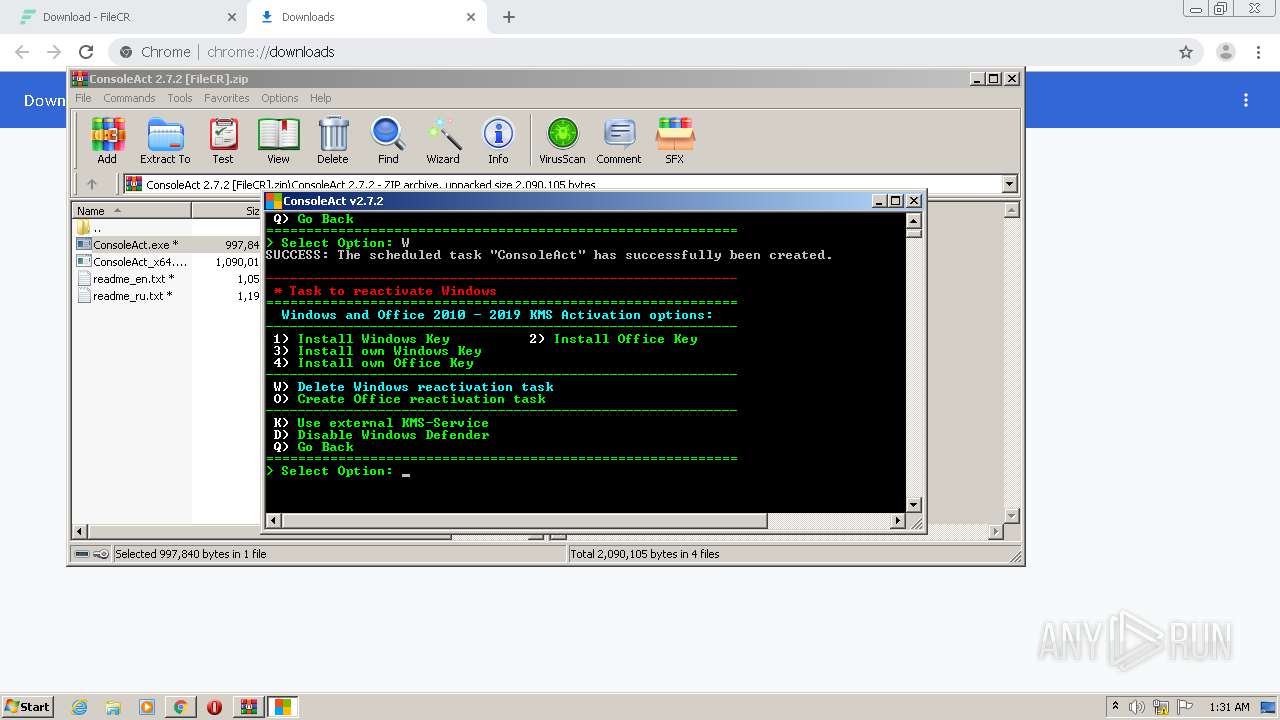
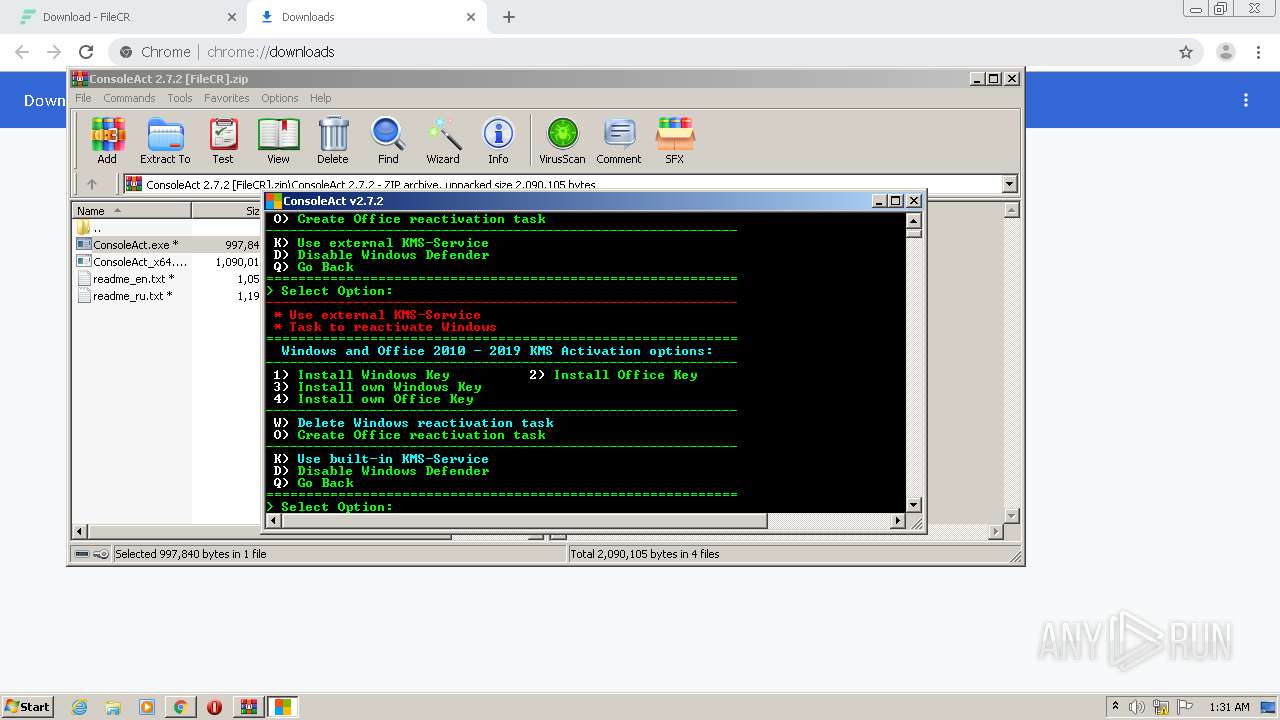
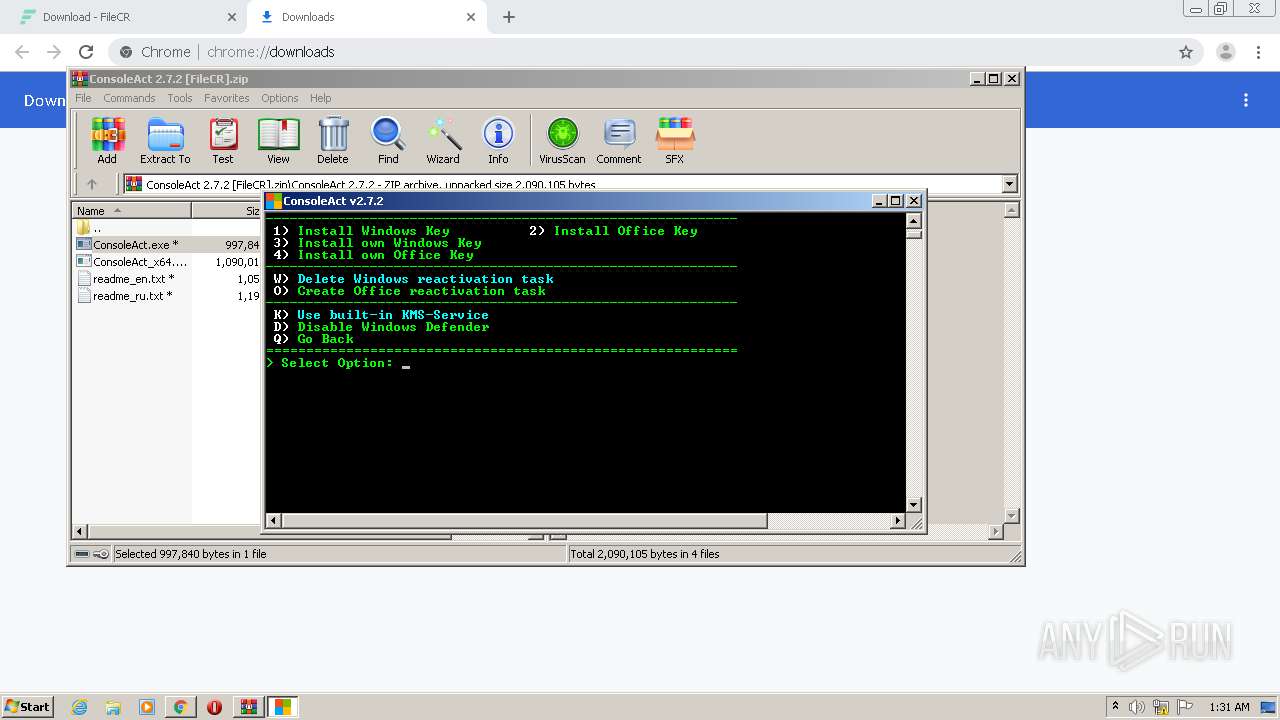
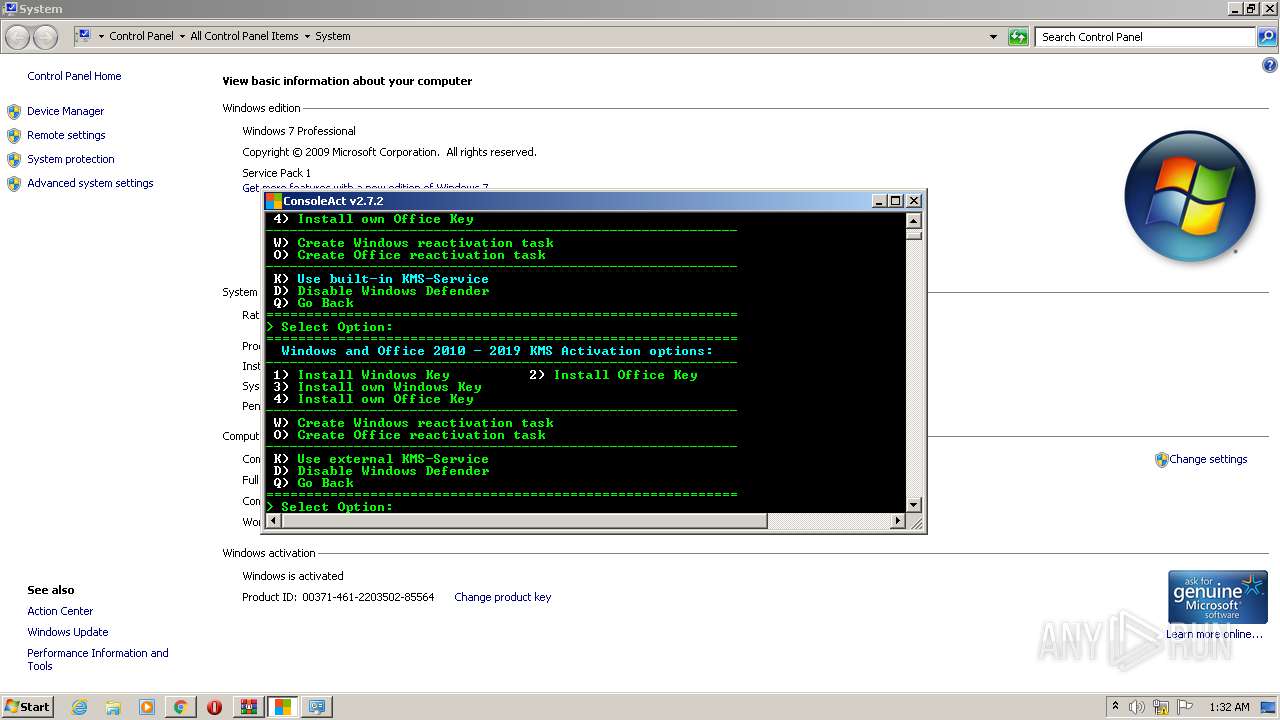
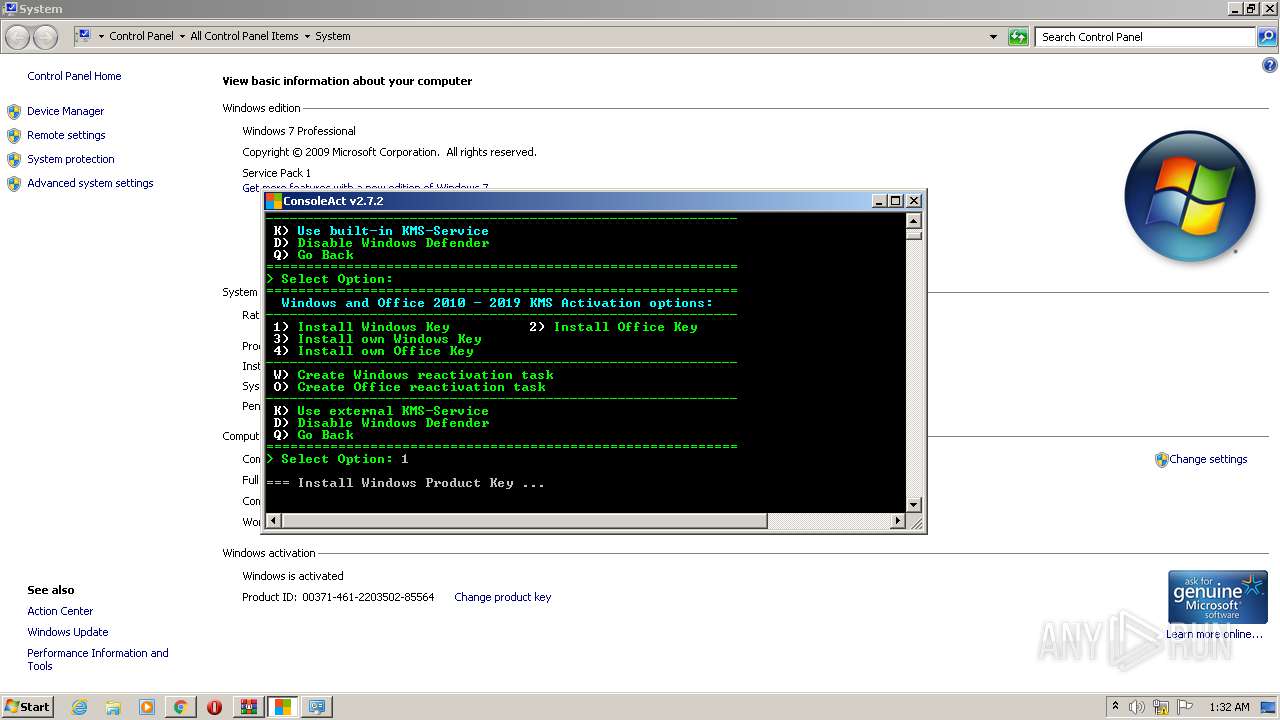
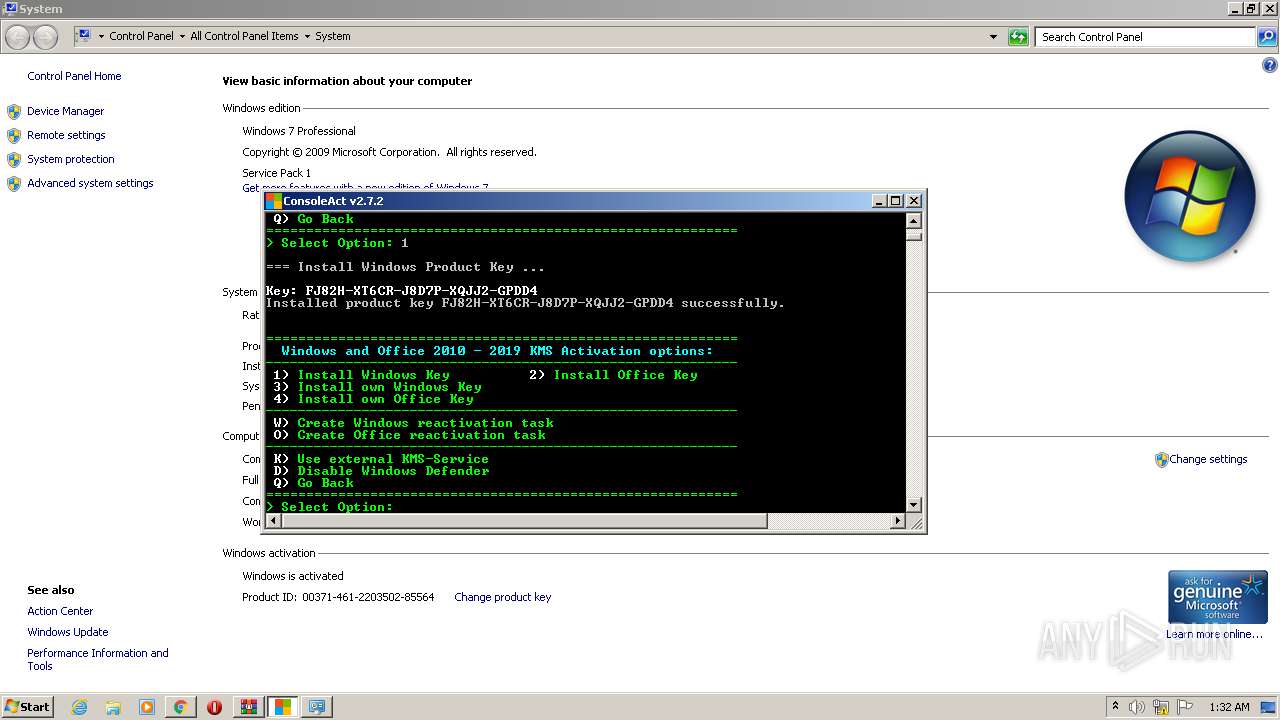
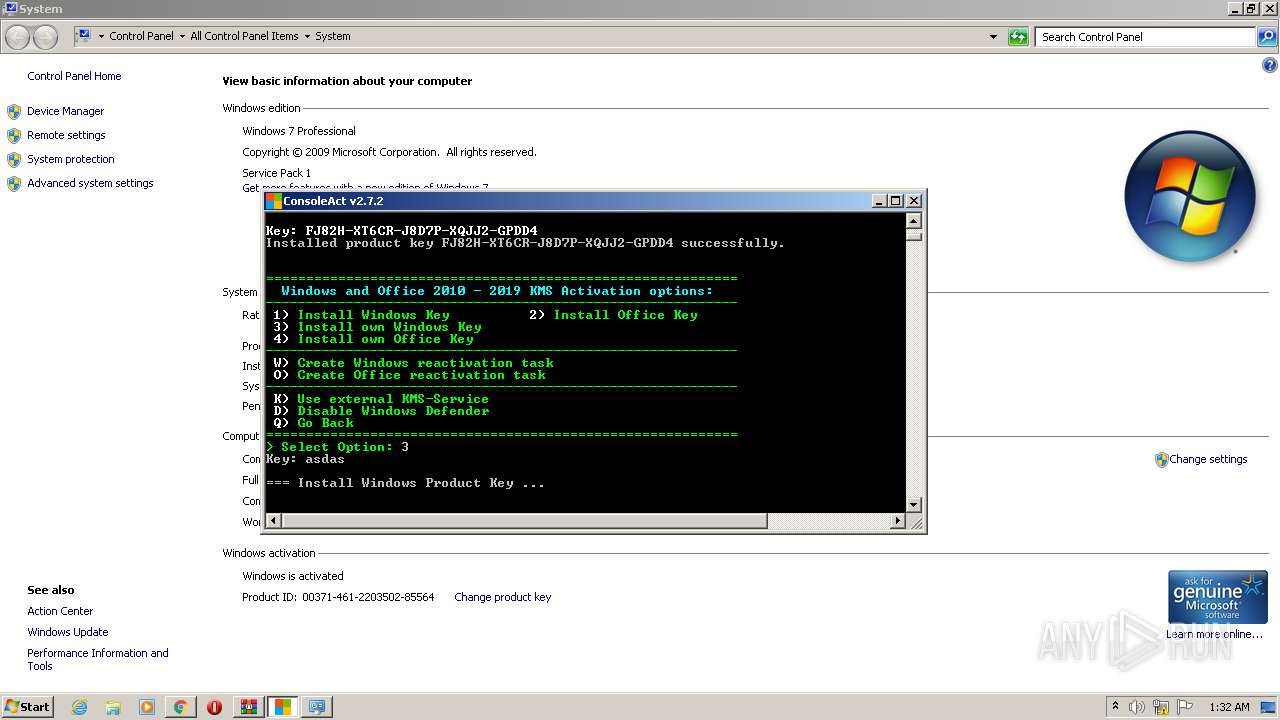
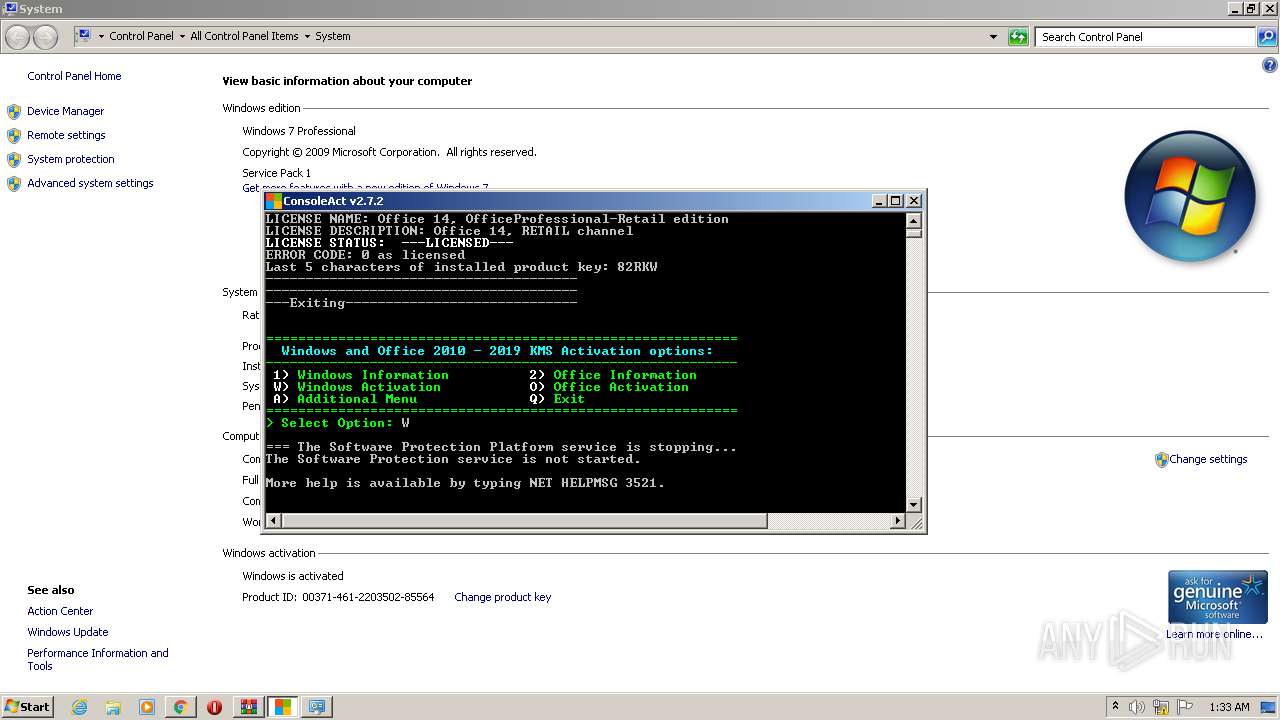
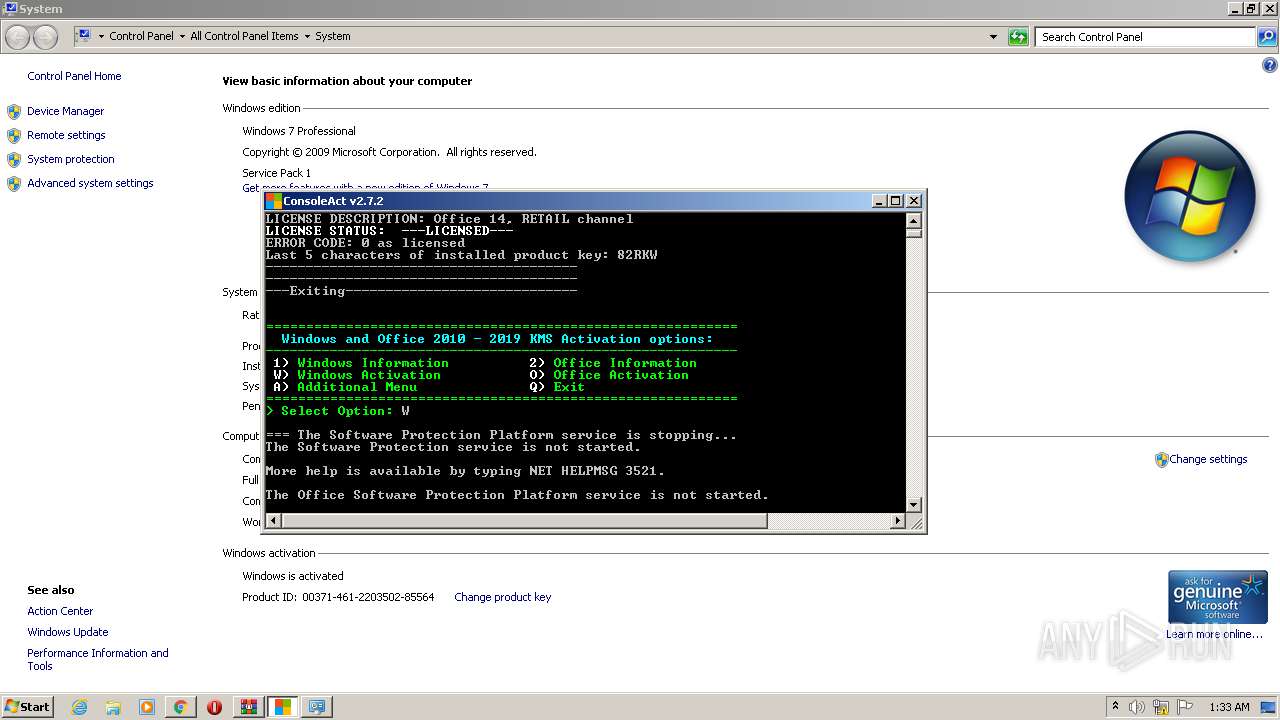
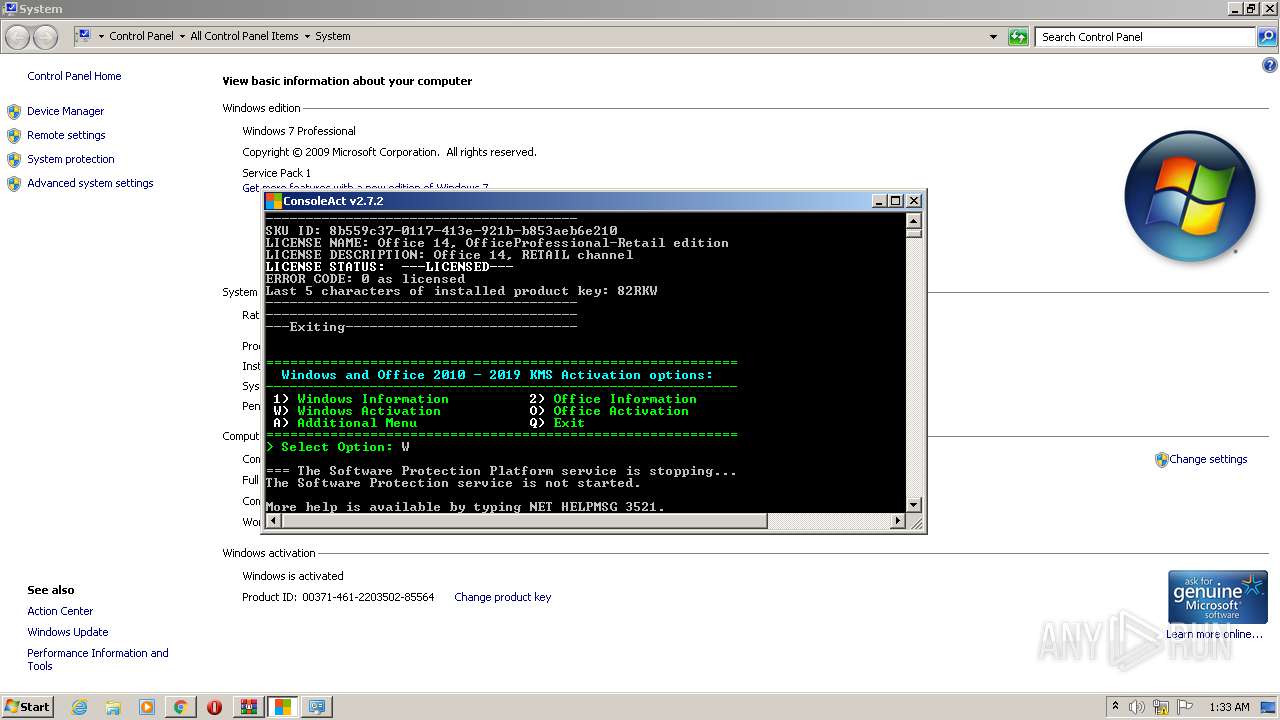
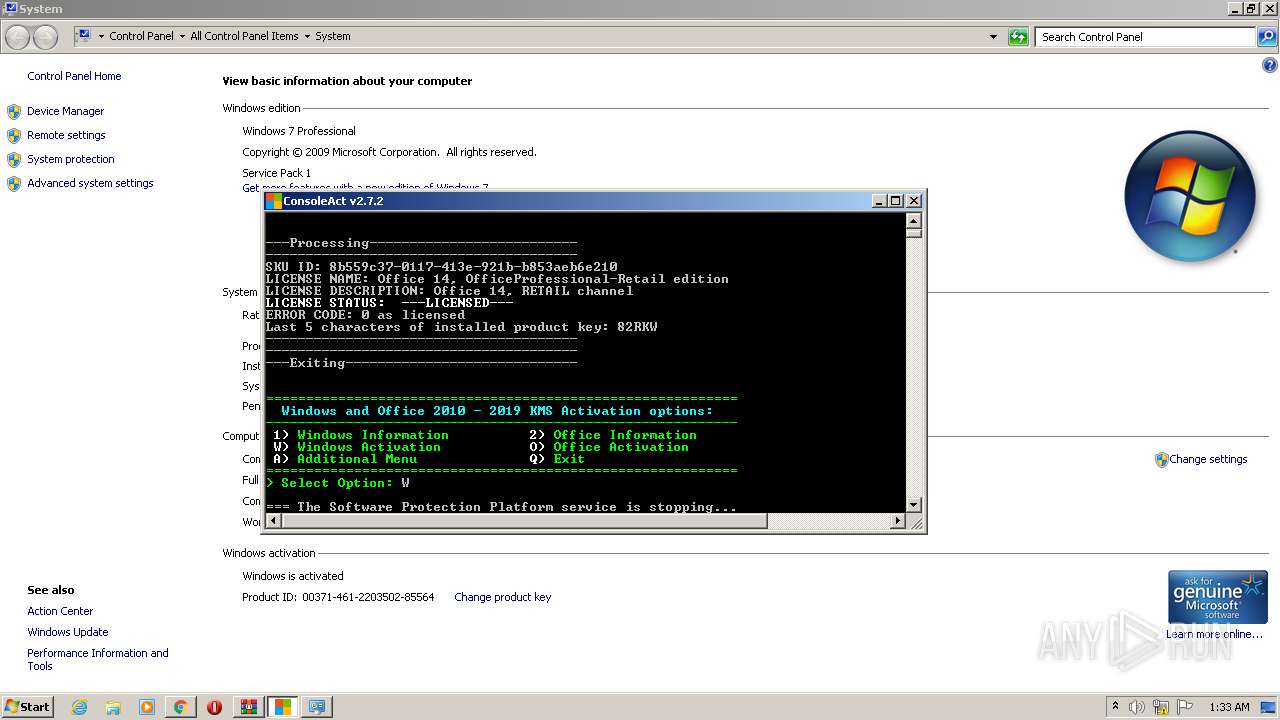
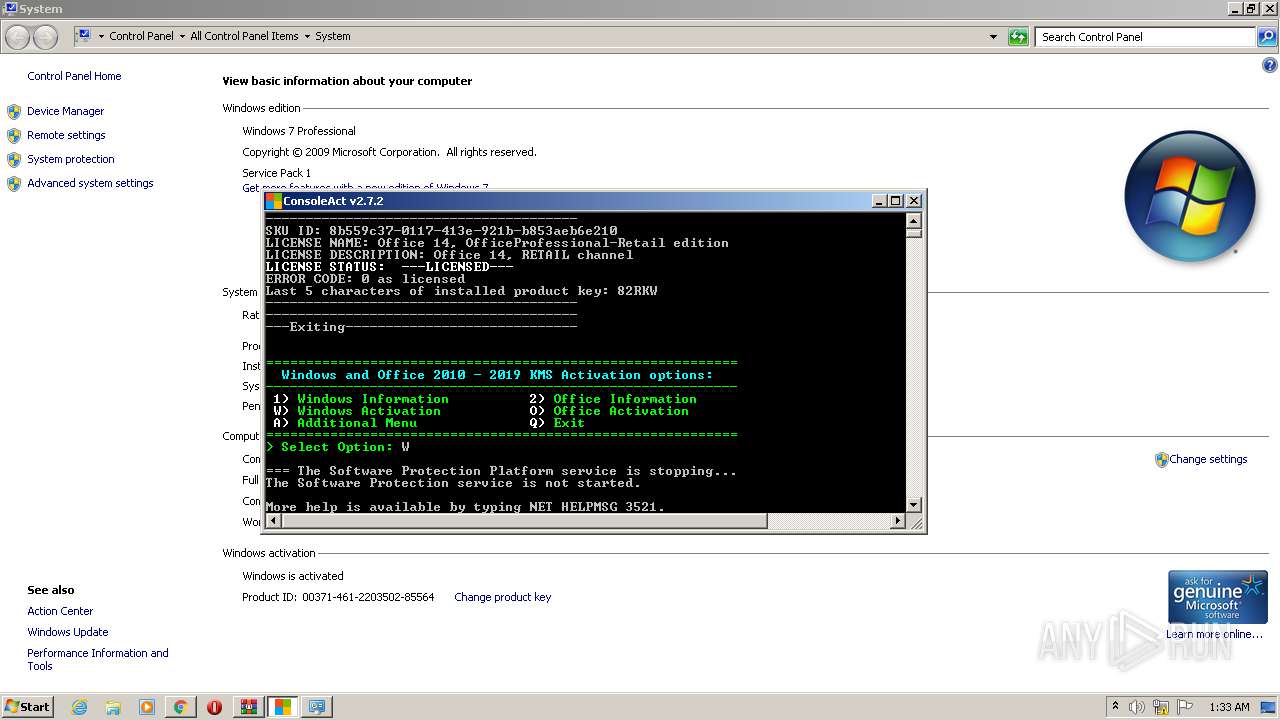
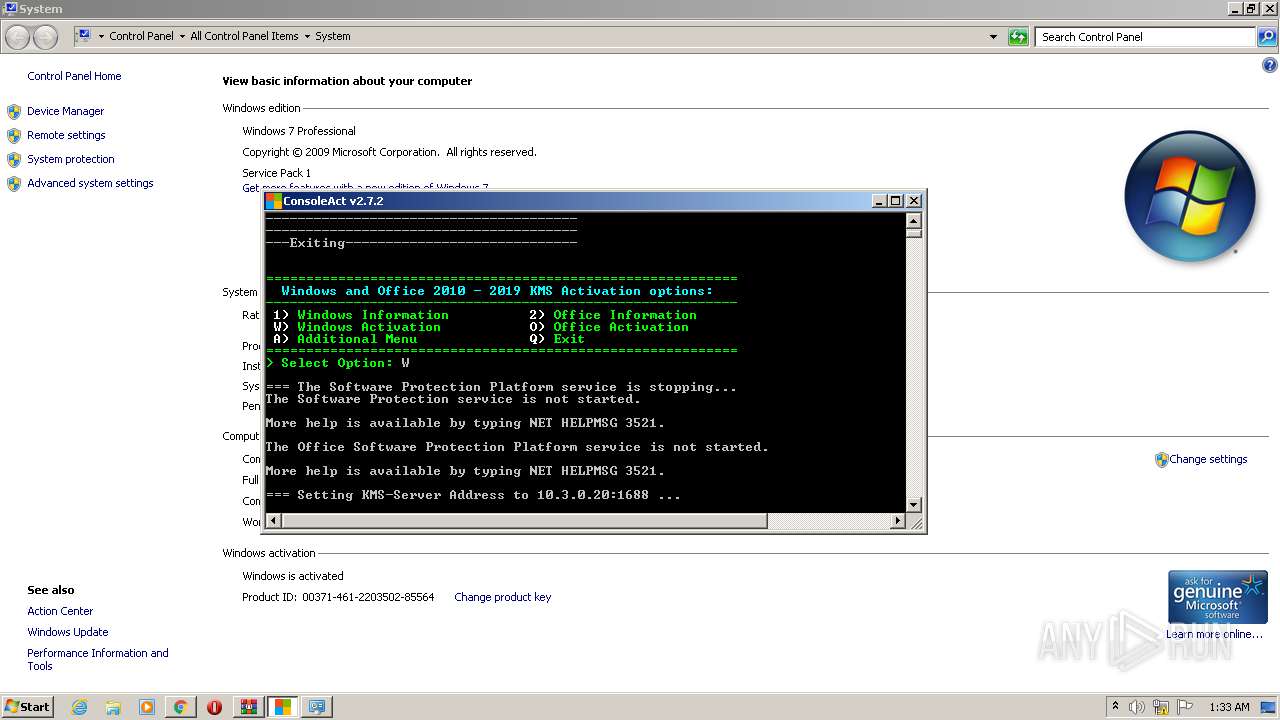
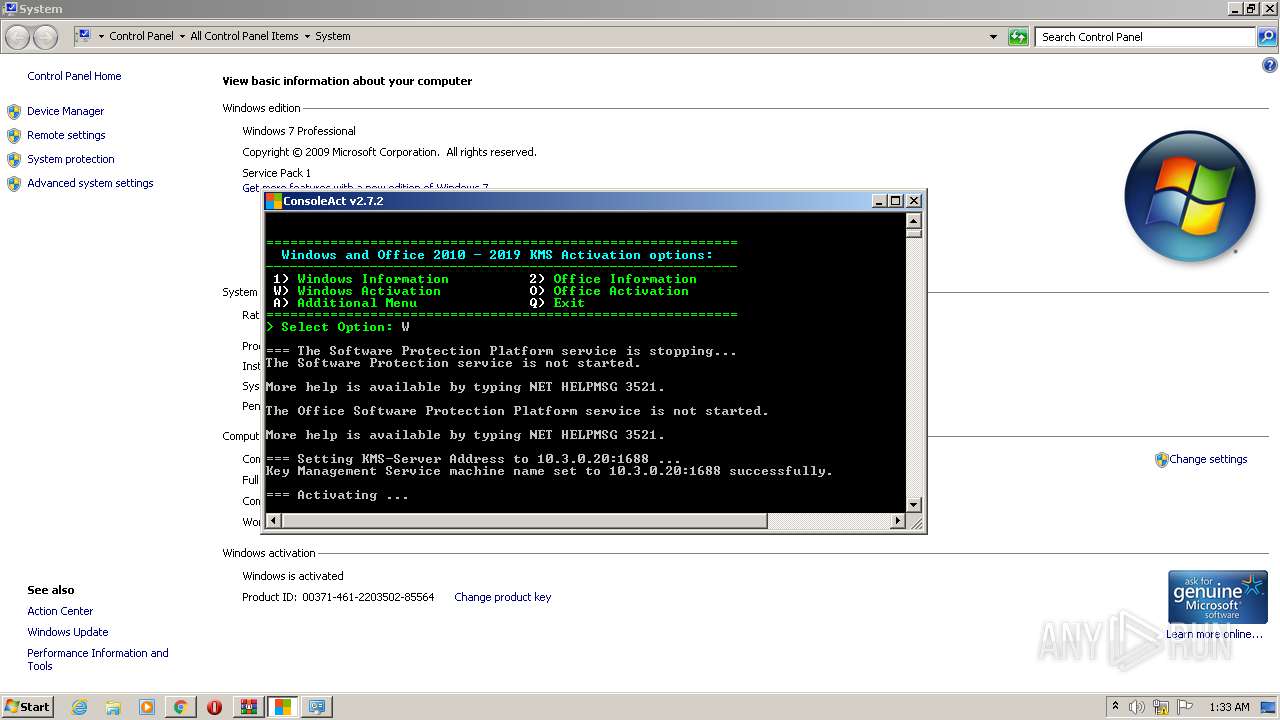
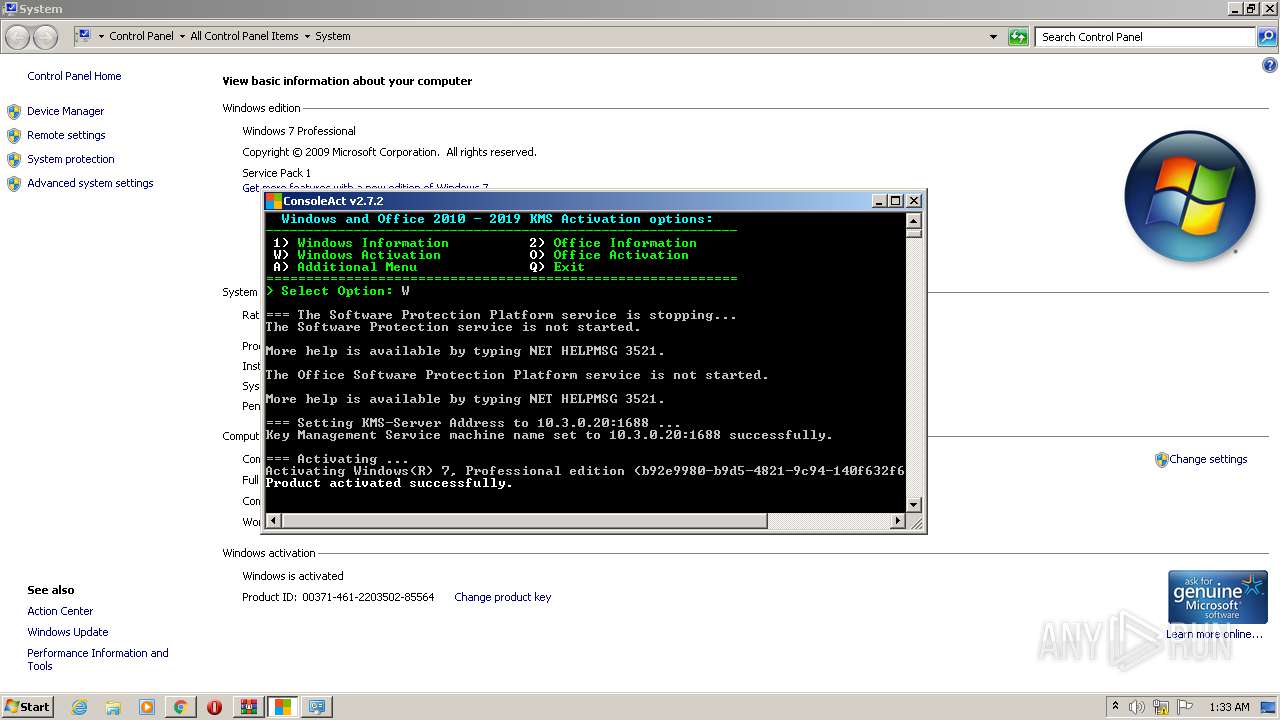
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2020, 00:28:59 |
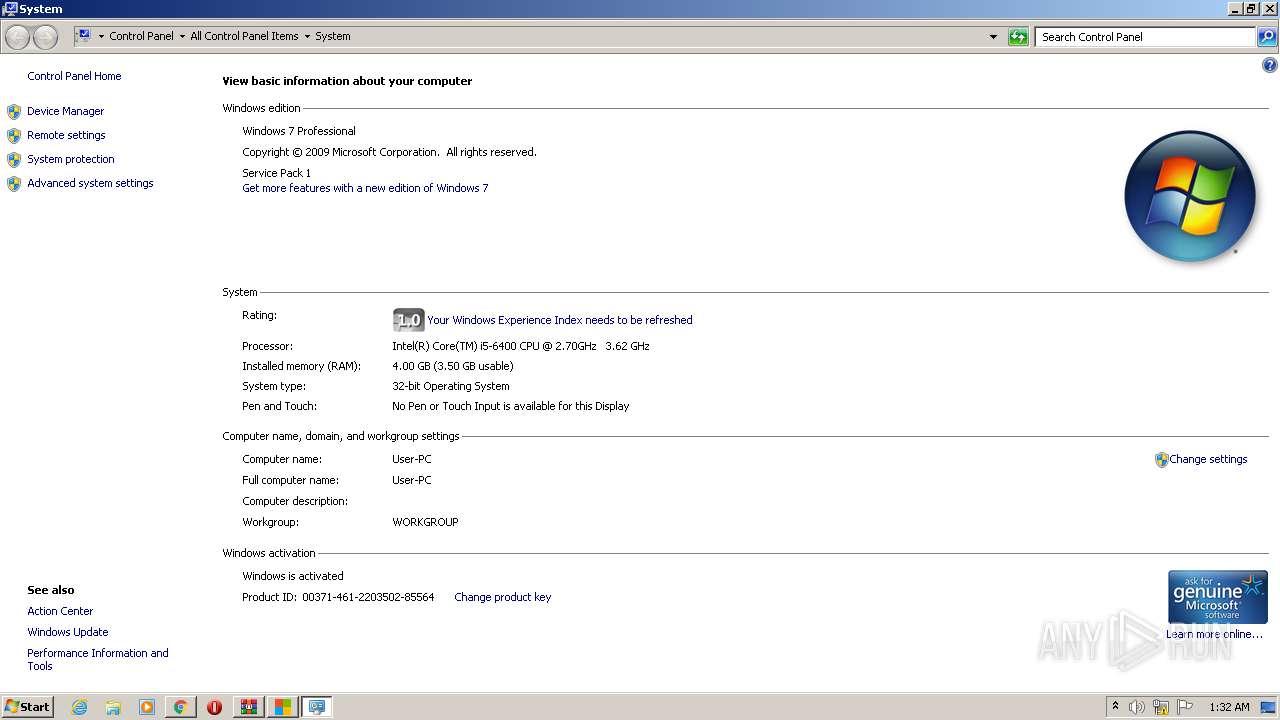
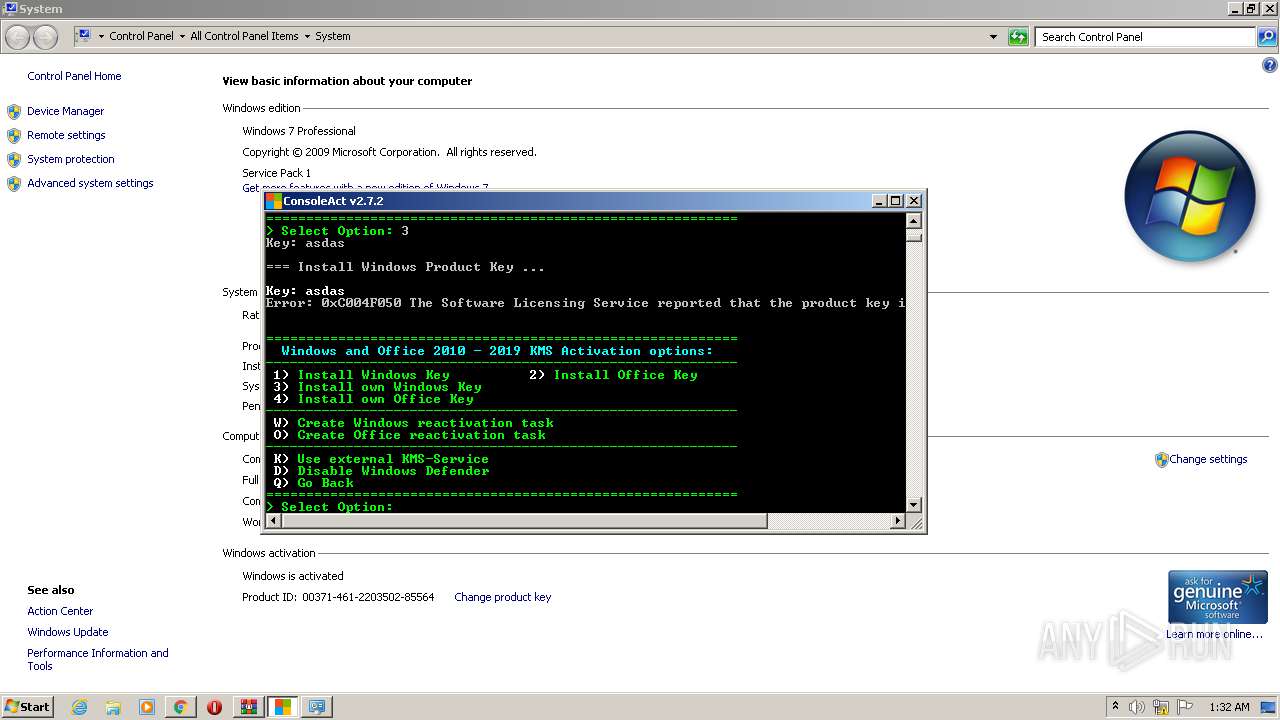
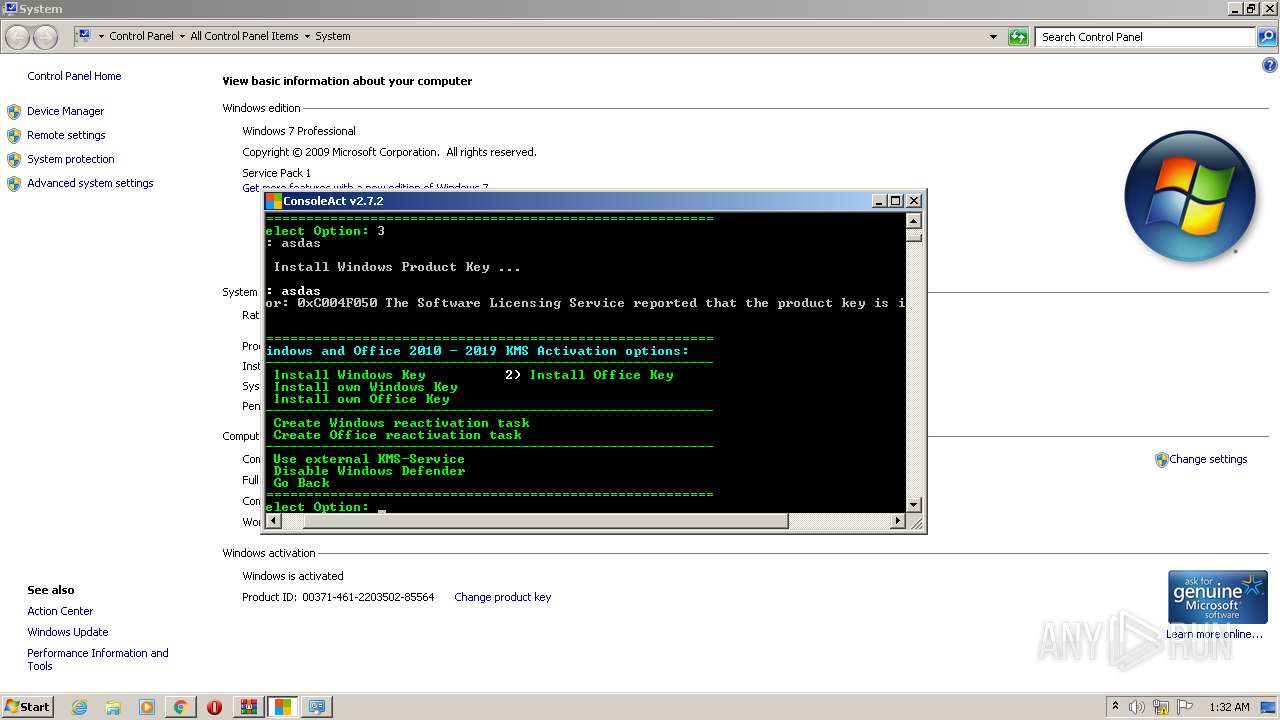
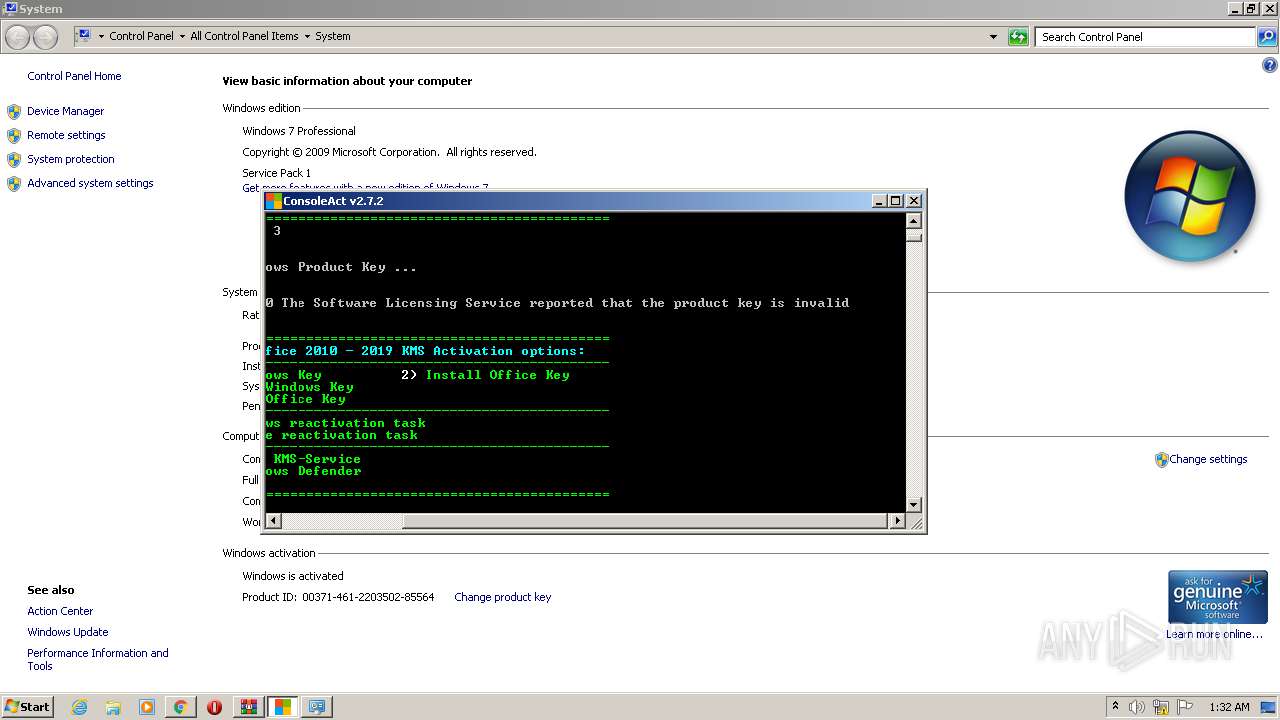
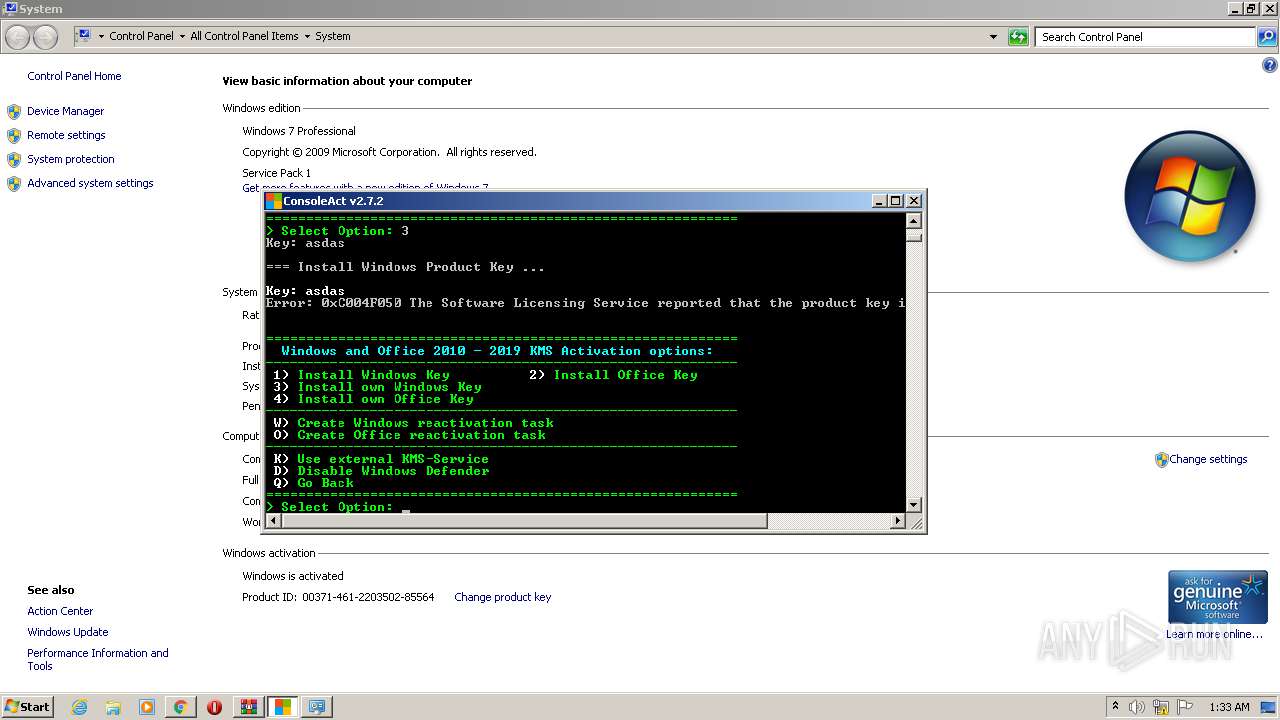
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B304BA52F999B7464C913B06A4AAA41B |
| SHA1: | 0485EC6E287D65BC50FB97871DF467E2C96BE493 |
| SHA256: | 77914081754A4CCCDEE73084ACBE7AFC5578E8398B65487A5948BBCF540891D1 |
| SSDEEP: | 3:N8JTCkKpJEKn:2hHhK |
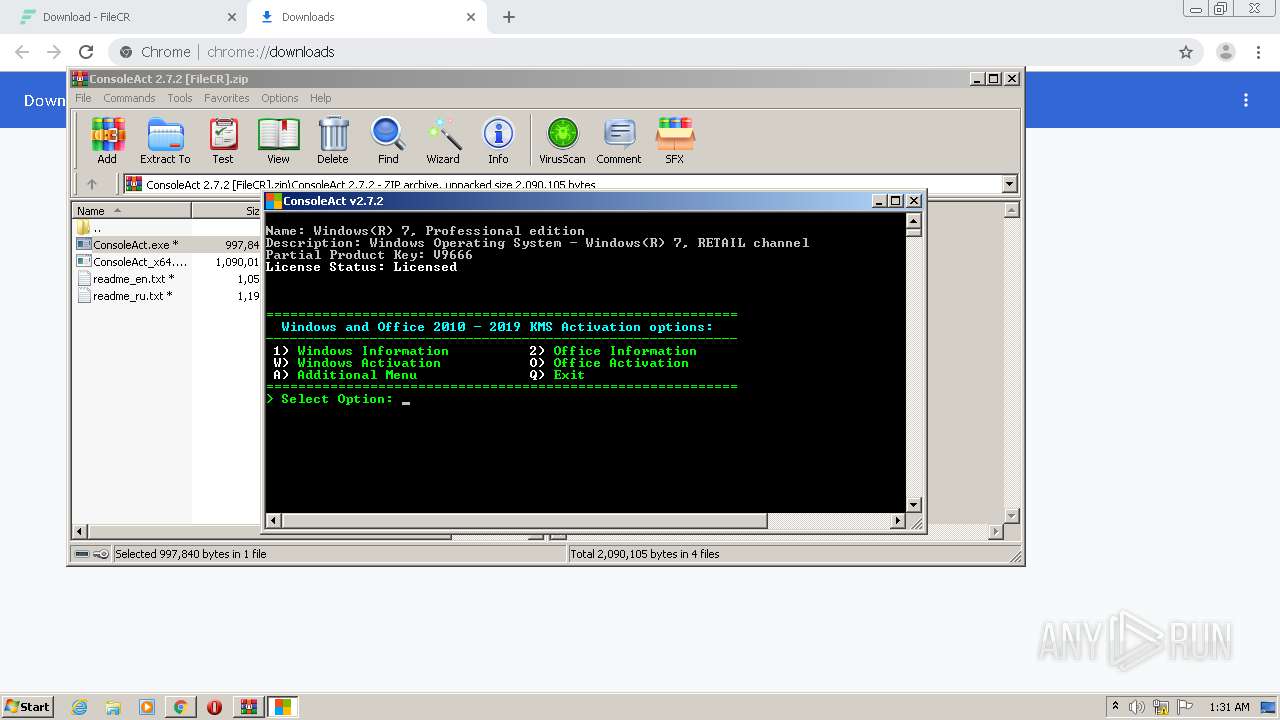
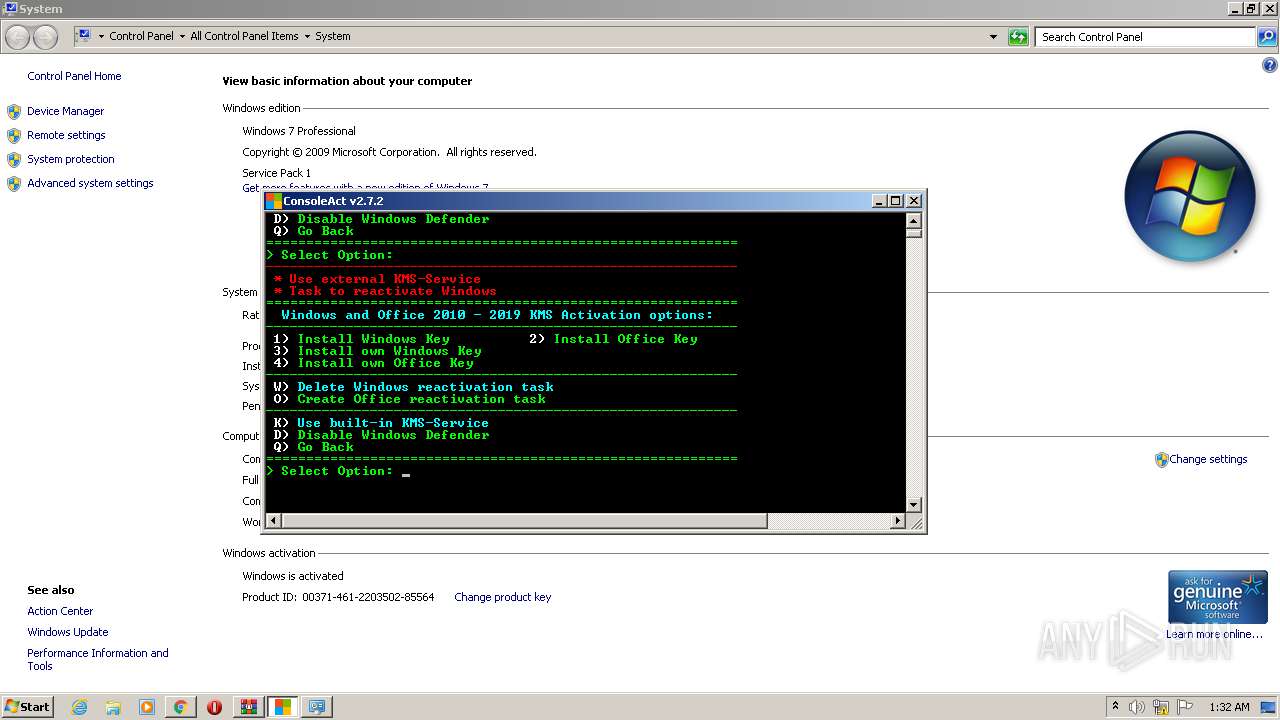
MALICIOUS
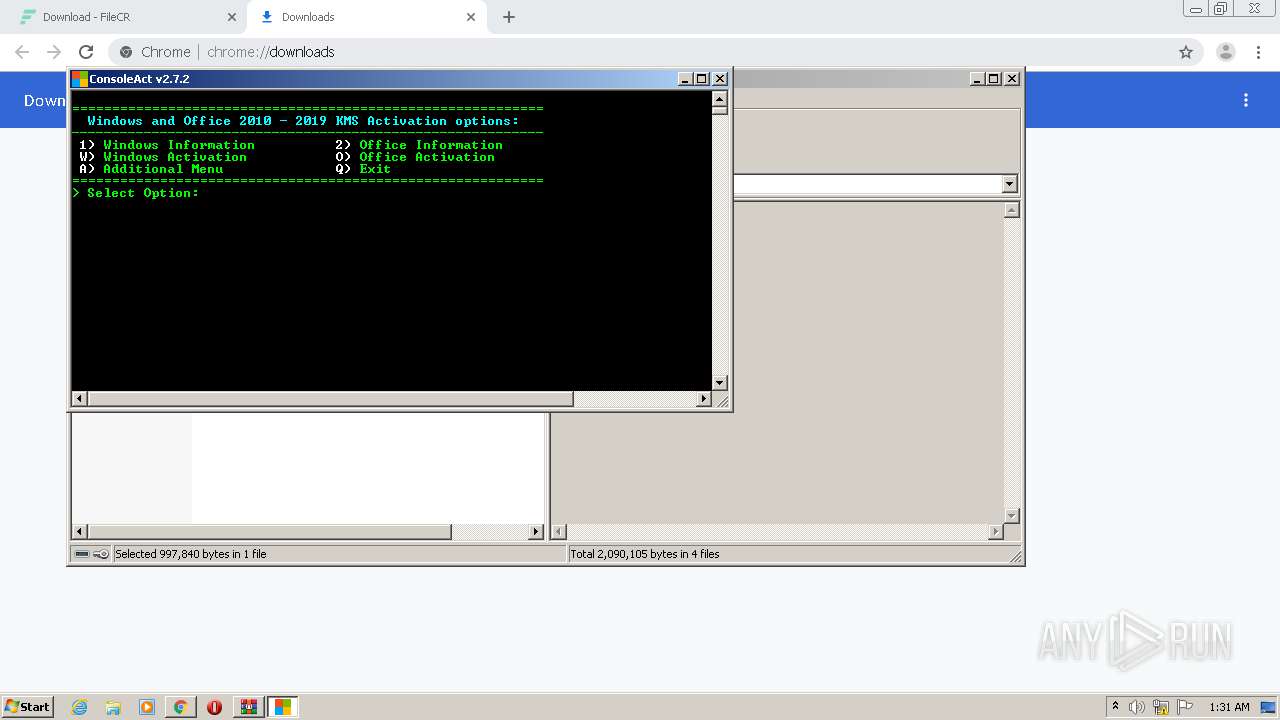
Application was dropped or rewritten from another process
- ConsoleAct.exe (PID: 2756)
- ConsoleAct.exe (PID: 3376)
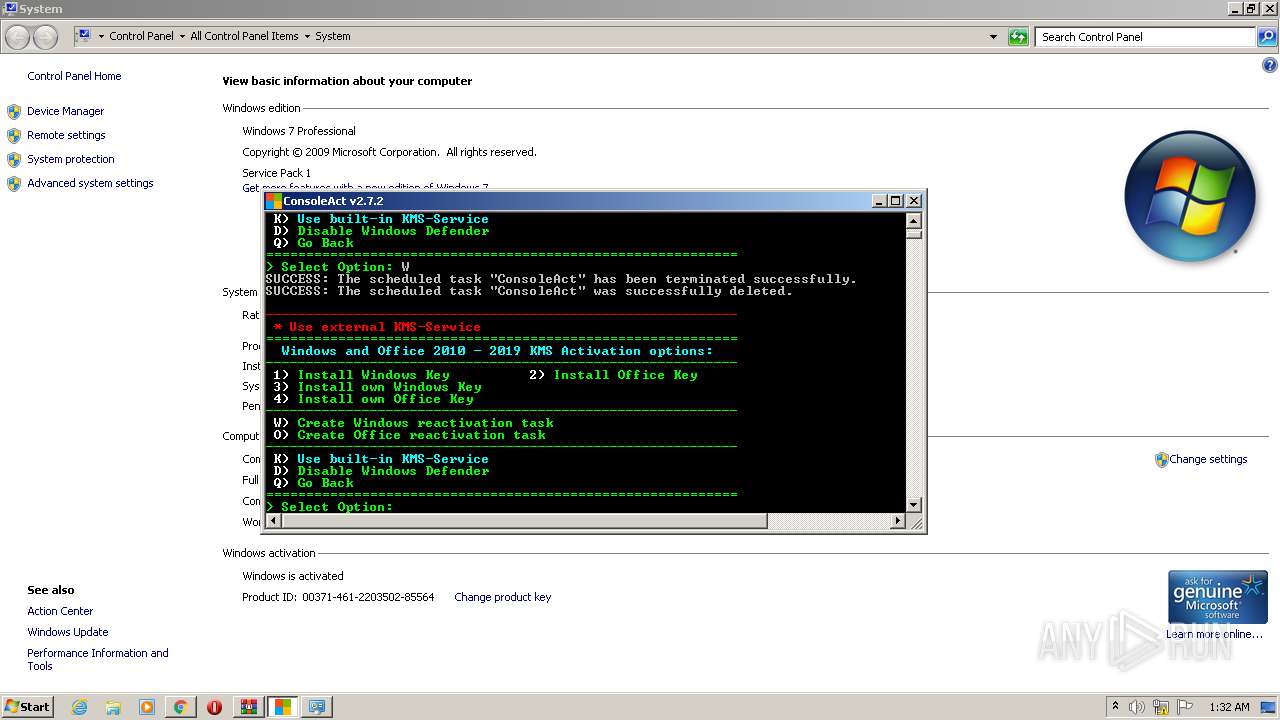
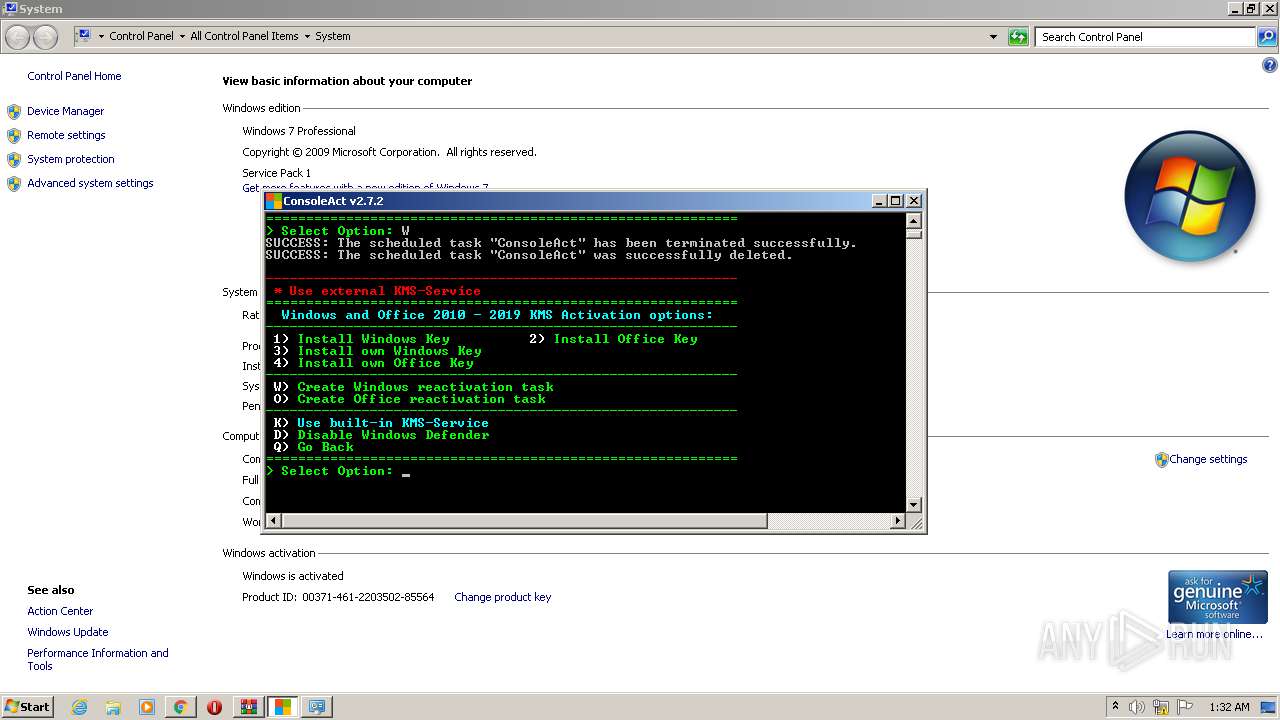
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3120)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 4072)
- cmd.exe (PID: 3160)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3772)
- schtasks.exe (PID: 3332)
- schtasks.exe (PID: 3144)
- schtasks.exe (PID: 2688)
- sppsvc.exe (PID: 3304)
Starts NET.EXE for service management
- cmd.exe (PID: 2260)
- cmd.exe (PID: 2300)
- cmd.exe (PID: 3568)
Loads dropped or rewritten executable
- sppsvc.exe (PID: 3304)
SUSPICIOUS
Starts CMD.EXE for commands execution
- ConsoleAct.exe (PID: 3376)
Creates files in the Windows directory
- ConsoleAct.exe (PID: 3376)
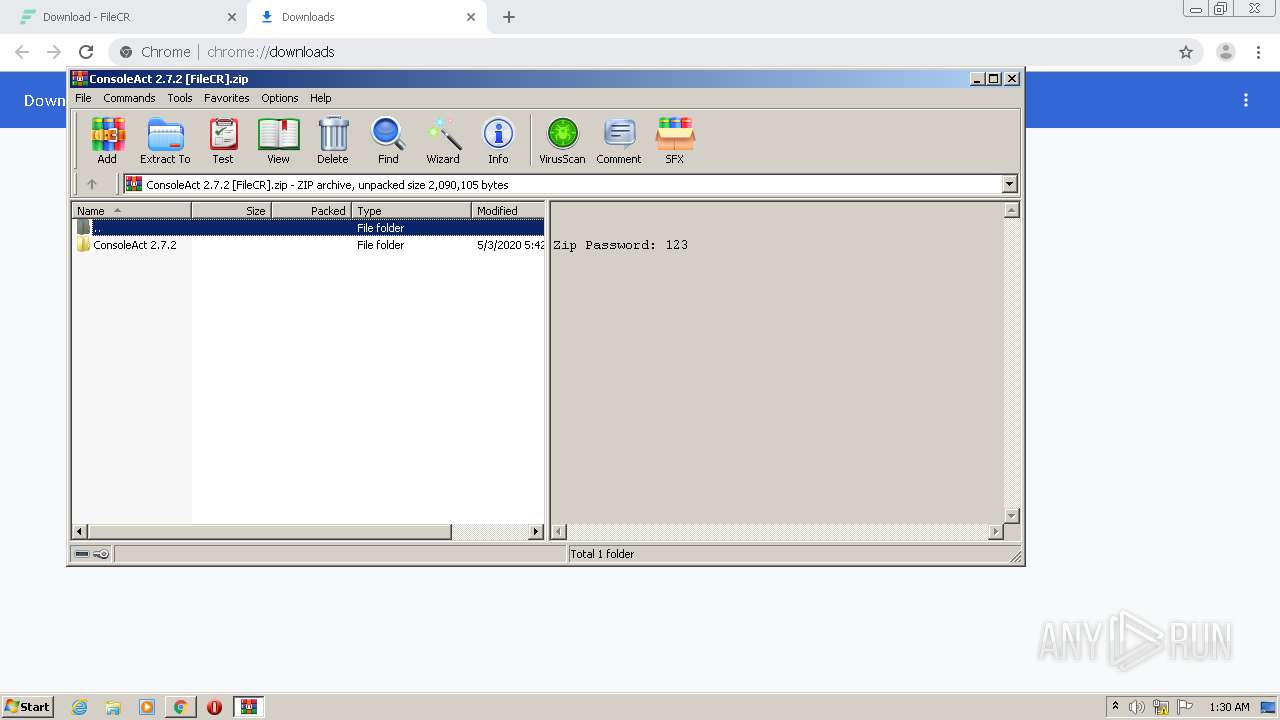
Executable content was dropped or overwritten
- WinRAR.exe (PID: 276)
- ConsoleAct.exe (PID: 3376)
Executes scripts
- cmd.exe (PID: 1932)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 3196)
- cmd.exe (PID: 3264)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 2784)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 3052)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 3088)
- cmd.exe (PID: 2764)
Removes files from Windows directory
- ConsoleAct.exe (PID: 3376)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3640)
- cmd.exe (PID: 380)
- cmd.exe (PID: 2936)
- cmd.exe (PID: 3800)
- cmd.exe (PID: 552)
- cmd.exe (PID: 3852)
- cmd.exe (PID: 2864)
- cmd.exe (PID: 1752)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 2648)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 2744)
- cmd.exe (PID: 2212)
- cmd.exe (PID: 2888)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 2704)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 4072)
- cmd.exe (PID: 796)
- cmd.exe (PID: 3648)
- ConsoleAct.exe (PID: 3376)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 764)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 3116)
Starts SC.EXE for service management
- cmd.exe (PID: 992)
- cmd.exe (PID: 3228)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2272)
- cmd.exe (PID: 3596)
INFO
Application launched itself
- chrome.exe (PID: 2636)
Reads the hosts file
- chrome.exe (PID: 2908)
- chrome.exe (PID: 2636)
Reads Internet Cache Settings
- chrome.exe (PID: 2636)
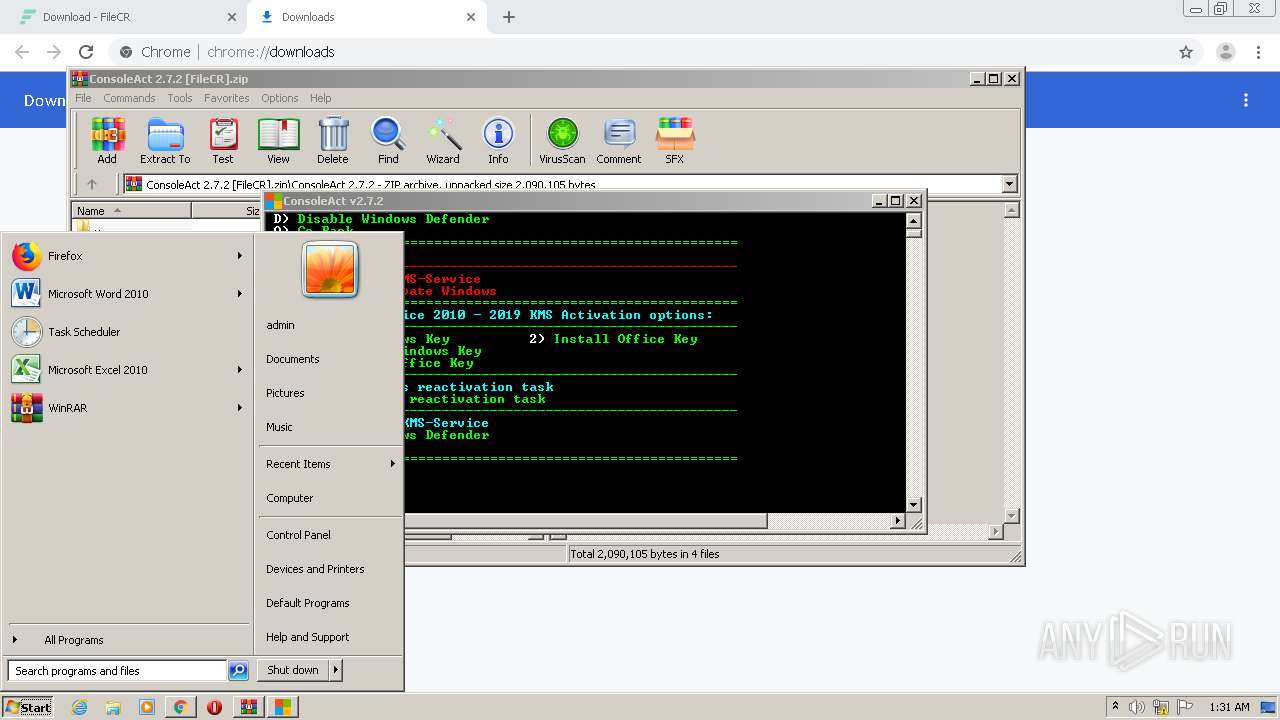
Manual execution by user
- control.exe (PID: 2556)
Reads Microsoft Office registry keys
- reg.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
161
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Windows\System32\cmd.exe" /c copy C:\Windows\System32\Tasks\ConsoleAct "C:\Users\admin\AppData\Local\Temp\ConsoleAct.tmp" /Y 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
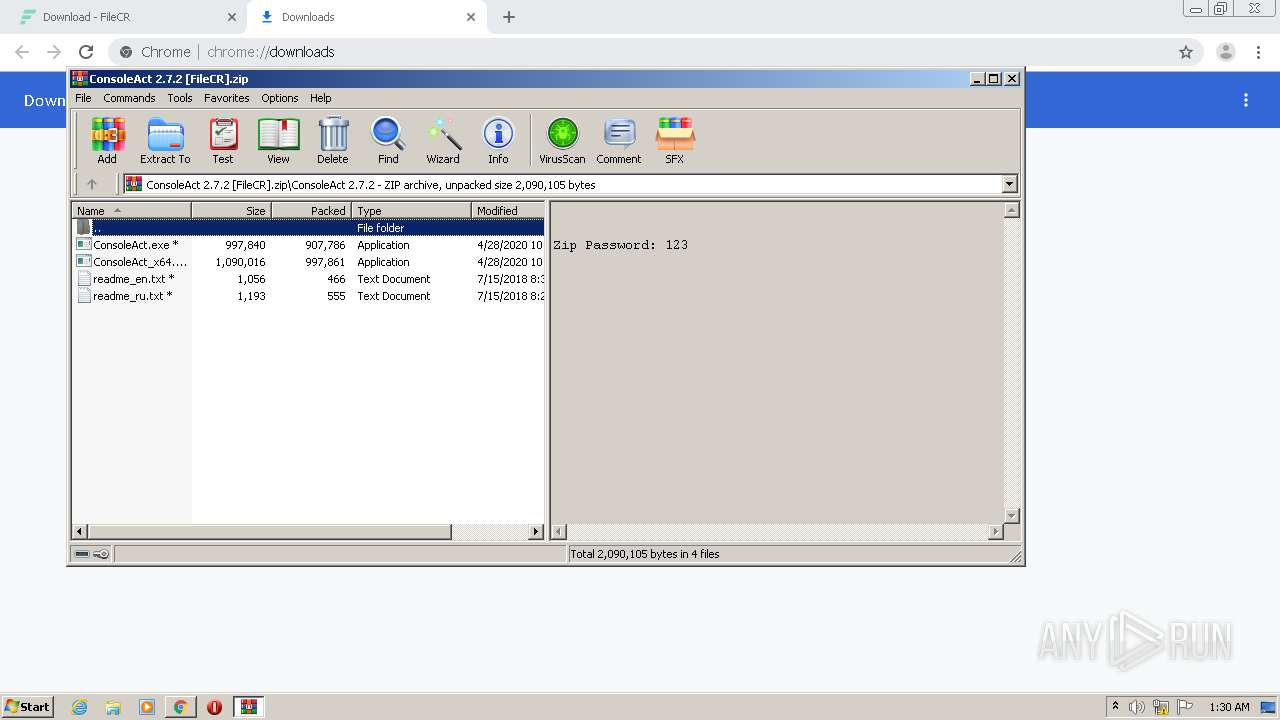
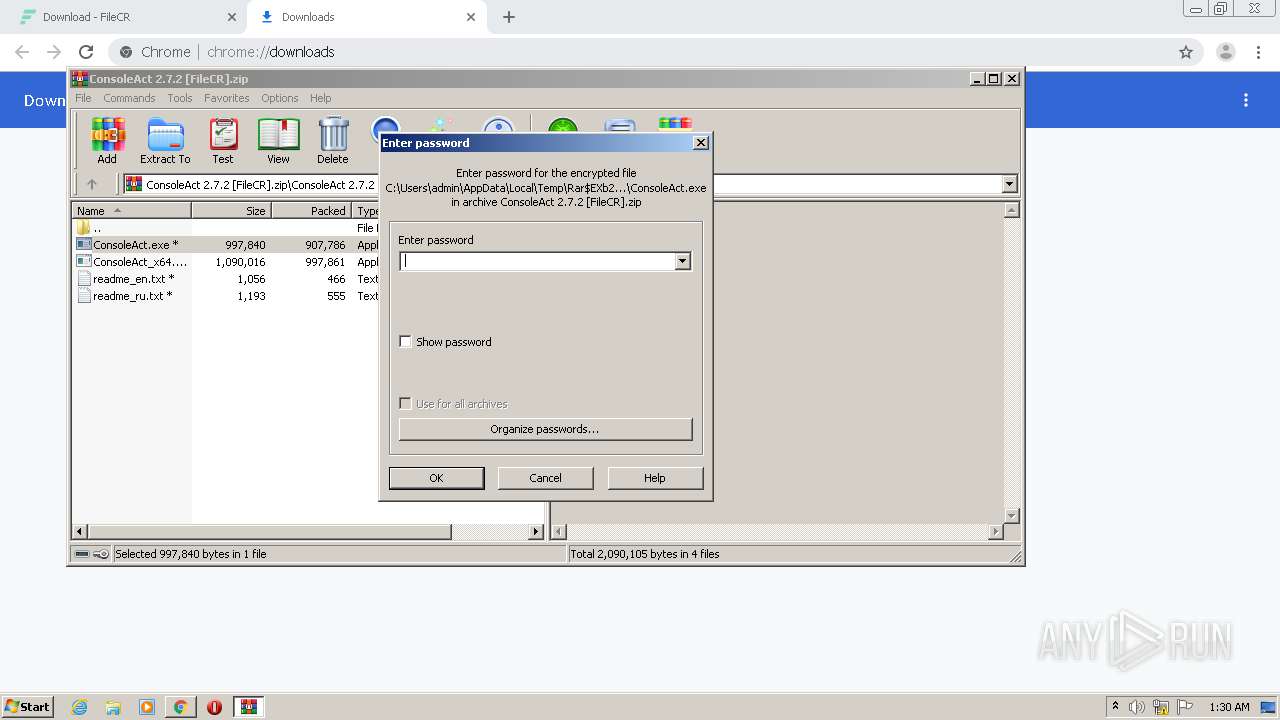
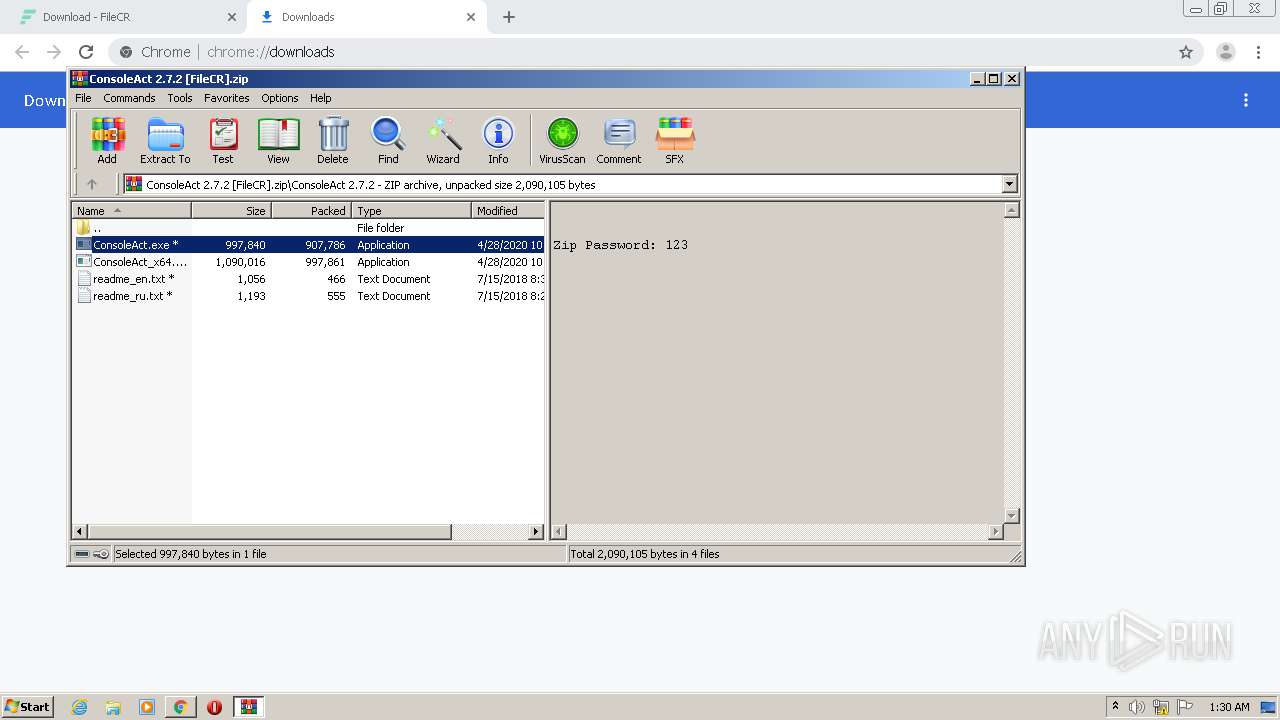
| 276 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ConsoleAct 2.7.2 [FileCR].zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 380 | "C:\Windows\System32\cmd.exe" /c reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v AllowFastServiceStartup 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 448 | "C:\Windows\System32\cmd.exe" /c copy C:\Windows\System32\Tasks\ConsoleAct "C:\Users\admin\AppData\Local\Temp\ConsoleAct.tmp" /Y 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 552 | "C:\Windows\System32\cmd.exe" /c reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v AllowFastServiceStartup 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 600 | cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /ckms-domain | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,3463710556587069967,8371031829741584657,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6627467239320280858 --mojo-platform-channel-handle=1060 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Windows\System32\cmd.exe" /c reg.exe delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v "Debugger" 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 764 | reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v AllowFastServiceStartup | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 796 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" /f /v "KeyManagementServicePort" /t REG_SZ /d 1688 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 374
Read events
2 137
Write events
229
Delete events
8
Modification events
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2636-13242702552859375 |
Value: 259 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
4
Suspicious files
152
Text files
96
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFe319b.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\48959136-c23f-4dea-b002-aaf03442f469.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe314d.TMP | text | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe3350.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe316c.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
65
DNS requests
44
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2908 | chrome.exe | 192.0.73.2:443 | secure.gravatar.com | Automattic, Inc | US | whitelisted |
2908 | chrome.exe | 216.58.212.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2908 | chrome.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
2908 | chrome.exe | 172.217.16.162:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
2908 | chrome.exe | 172.217.22.98:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
2908 | chrome.exe | 104.24.119.207:443 | filecrx.com | Cloudflare Inc | US | suspicious |
2908 | chrome.exe | 157.240.27.18:443 | graph.facebook.com | Facebook, Inc. | US | suspicious |
2908 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2908 | chrome.exe | 172.67.189.233:443 | filecr.com | — | US | unknown |
2908 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filecr.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
contextual.media.net |
| shared |
www.googletagmanager.com |
| whitelisted |
i0.wp.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
i1.wp.com |
| whitelisted |