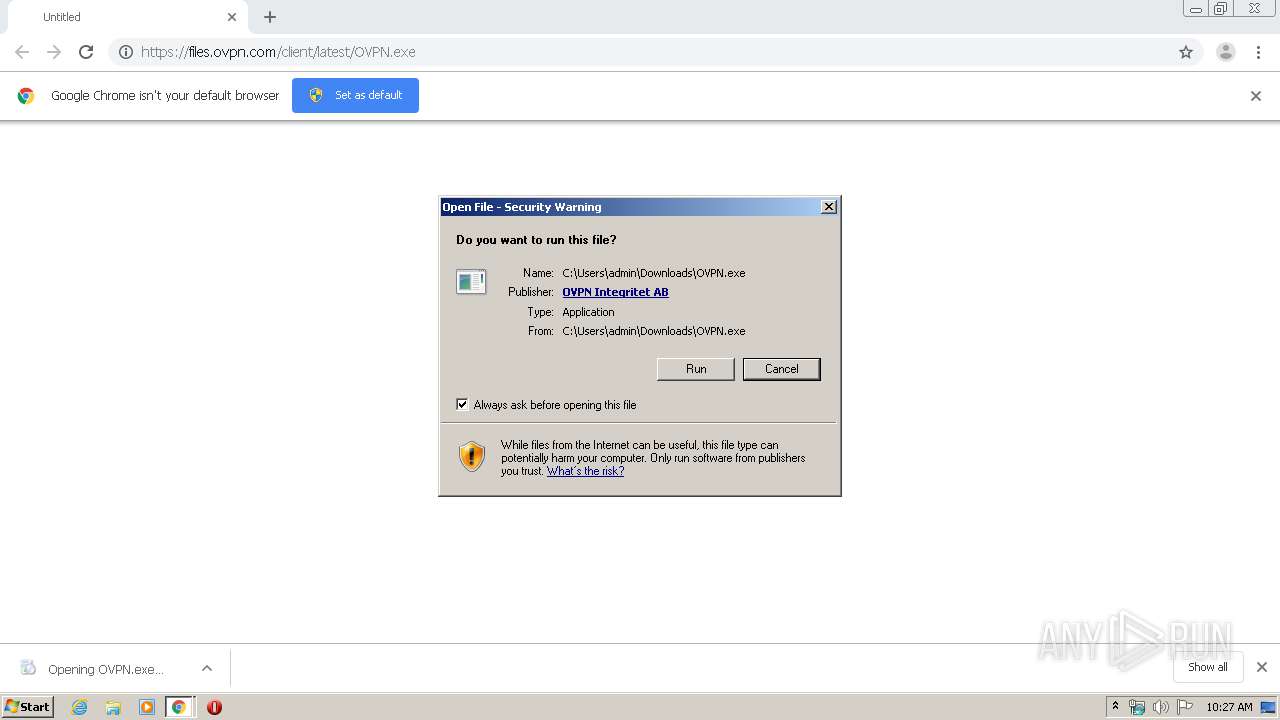
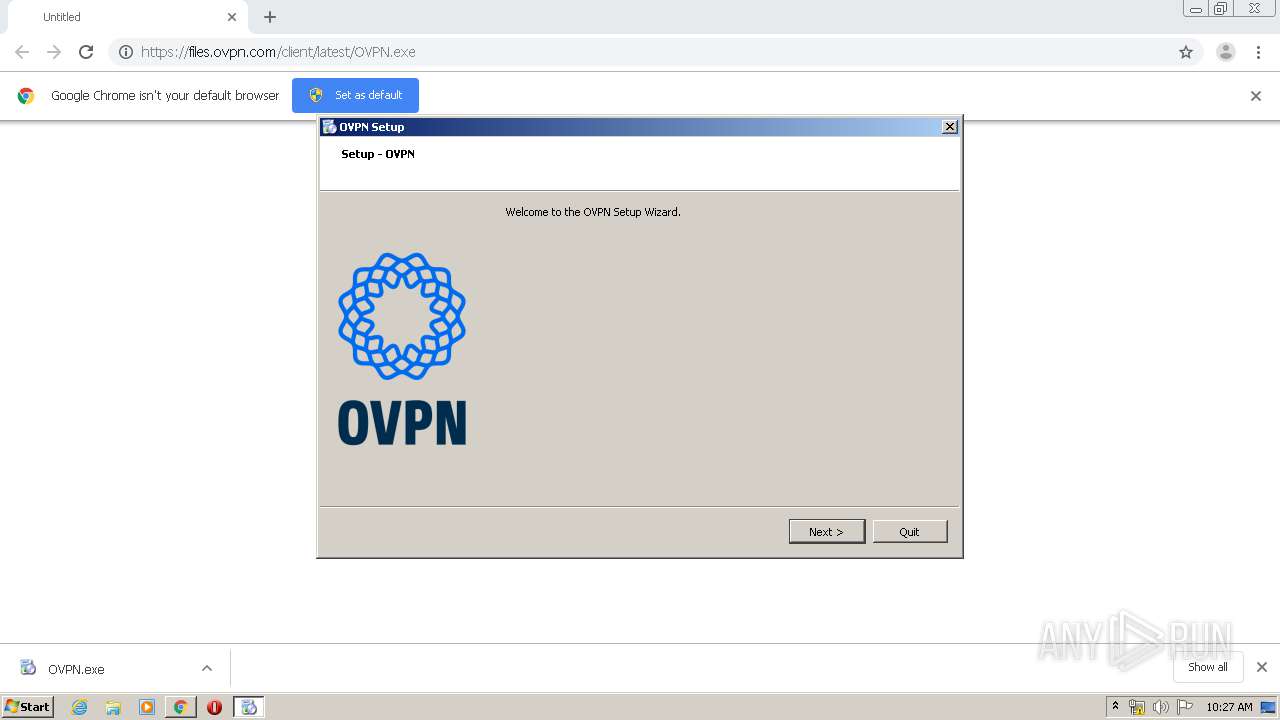
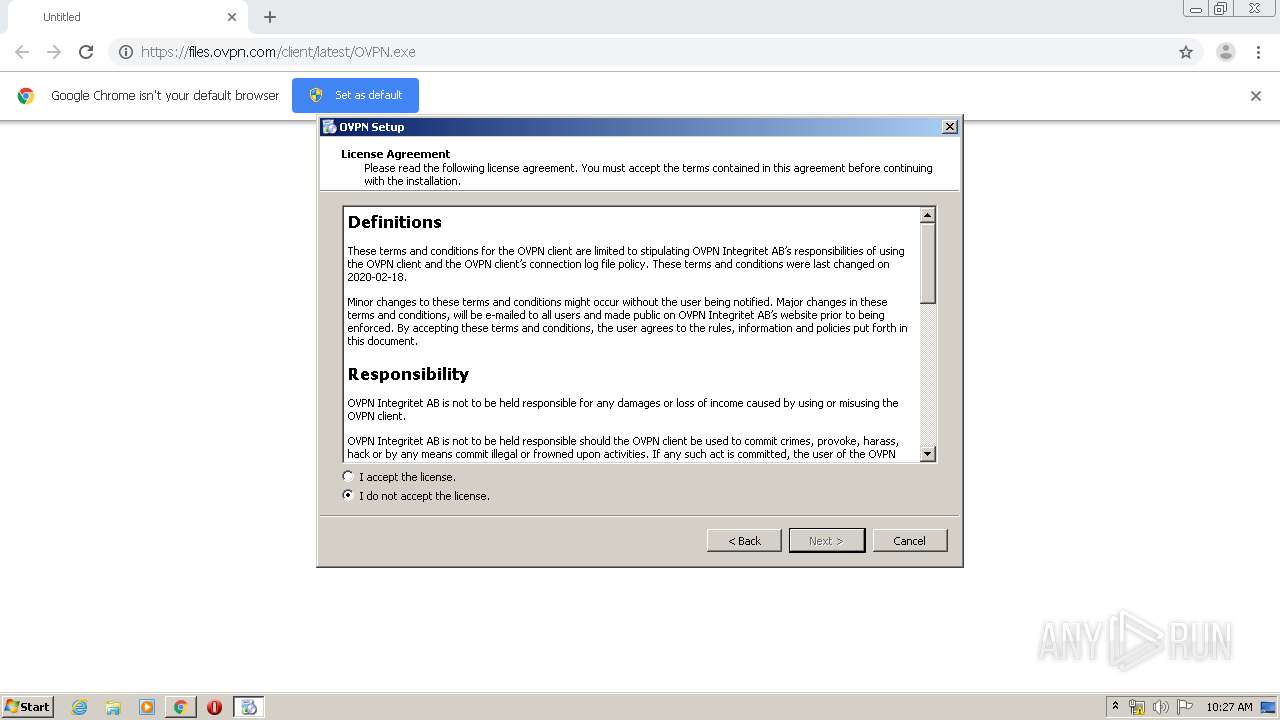
| URL: | https://files.ovpn.com/client/latest/OVPN.exe |
| Full analysis: | https://app.any.run/tasks/f9c43124-054b-4c3a-80ba-0cb092debdb8 |
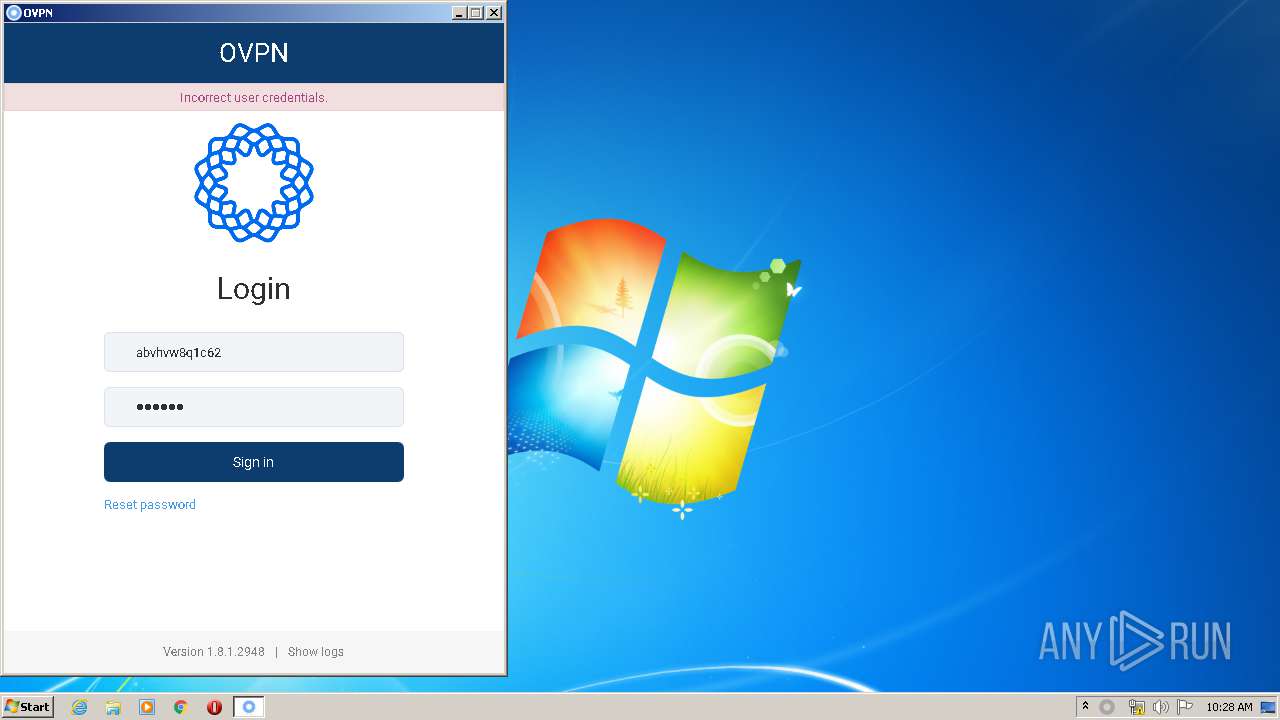
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 09:26:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 71B805A643CDB307E0EC1B6D8B1A0029 |
| SHA1: | 93A54B8A0D9697719E20B2754FB6046F80BFE4ED |
| SHA256: | 778EA1877E9BD2027AC584A1DDD1E9EE6BC54F504F88B514CE97B0CF7ABE2705 |
| SSDEEP: | 3:N8MWyTdJMuvLn:2MxJMWLn |
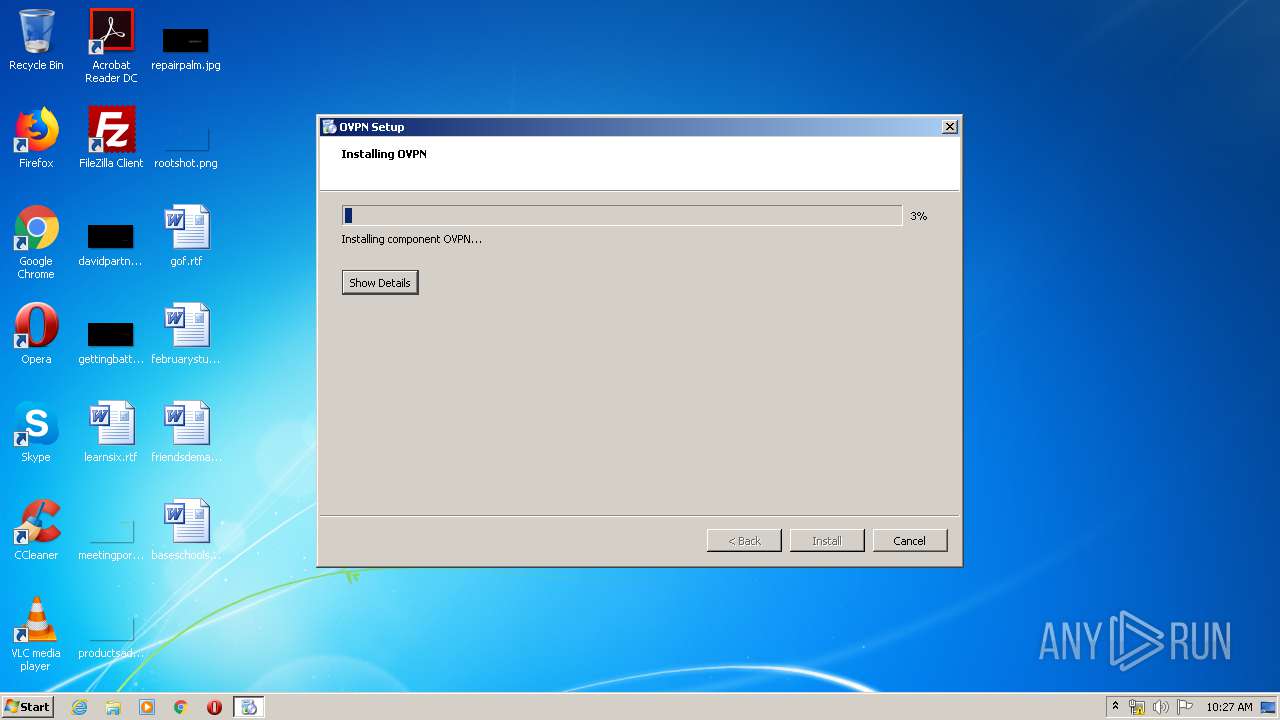
MALICIOUS
Application was dropped or rewritten from another process
- OVPN.exe (PID: 3716)
- OVPN.exe (PID: 4008)
- ovpn-controller.exe (PID: 1944)
- sed.exe (PID: 1516)
- tapinstall.exe (PID: 3204)
- sed.exe (PID: 4056)
- tapinstall.exe (PID: 1672)
- tapinstall.exe (PID: 2432)
- openvpn.exe (PID: 2952)
- tapinstall.exe (PID: 3860)
- tapinstall.exe (PID: 308)
- tapinstall.exe (PID: 3996)
- tapinstall.exe (PID: 3604)
- tapinstall.exe (PID: 3240)
- tapinstall.exe (PID: 3664)
- ovpn-daemon.exe (PID: 528)
- tapinstall.exe (PID: 1024)
- ovpn-controller.exe (PID: 3164)
- nvspbind.exe (PID: 3988)
- killswitch.exe (PID: 2396)
- openvpn.exe (PID: 2400)
- OVPNUninstaller.exe (PID: 580)
- tapinstall.exe (PID: 1440)
- killswitch.exe (PID: 1168)
- OVPN.exe (PID: 2652)
- tapinstall.exe (PID: 392)
- tapinstall.exe (PID: 2568)
Loads dropped or rewritten executable
- openvpn.exe (PID: 2952)
- sed.exe (PID: 4056)
- sed.exe (PID: 1516)
- ovpn-controller.exe (PID: 1944)
- ovpn-controller.exe (PID: 3164)
- openvpn.exe (PID: 2400)
- OVPN.exe (PID: 2652)
Starts NET.EXE for service management
- OVPN.exe (PID: 4008)
Changes the autorun value in the registry
- OVPN.exe (PID: 2652)
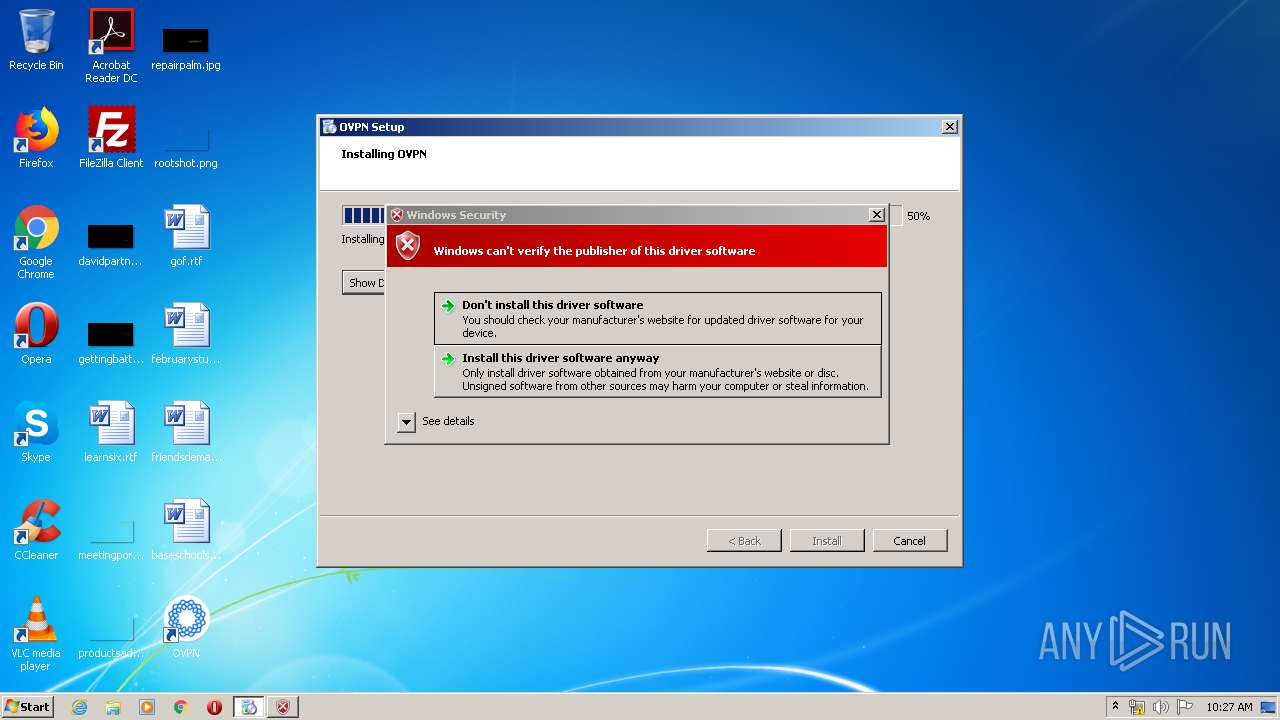
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2784)
- OVPN.exe (PID: 4008)
- DrvInst.exe (PID: 1520)
- tapinstall.exe (PID: 3204)
- DrvInst.exe (PID: 2896)
- cscript.exe (PID: 580)
Application launched itself
- OVPN.exe (PID: 3716)
Starts CMD.EXE for commands execution
- OVPN.exe (PID: 4008)
Executed via COM
- DrvInst.exe (PID: 2896)
- DrvInst.exe (PID: 1520)
Creates files in the program directory
- ovpn-controller.exe (PID: 1944)
- ovpn-daemon.exe (PID: 528)
- OVPN.exe (PID: 4008)
Creates files in the Windows directory
- certutil.exe (PID: 2496)
- DrvInst.exe (PID: 1520)
- DrvInst.exe (PID: 2896)
Removes files from Windows directory
- certutil.exe (PID: 2496)
- DrvInst.exe (PID: 1520)
- DrvInst.exe (PID: 2896)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2896)
Executed as Windows Service
- vssvc.exe (PID: 2764)
- ovpn-daemon.exe (PID: 528)
Creates files in the driver directory
- DrvInst.exe (PID: 1520)
- DrvInst.exe (PID: 2896)
Uses NETSH.EXE for network configuration
- ovpn-controller.exe (PID: 1944)
Starts SC.EXE for service management
- OVPN.exe (PID: 4008)
Creates a software uninstall entry
- OVPN.exe (PID: 4008)
Executes scripts
- OVPN.exe (PID: 4008)
Uses TASKLIST.EXE to query information about running processes
- OVPN.exe (PID: 3716)
- OVPN.exe (PID: 2652)
Creates files in the user directory
- OVPN.exe (PID: 2652)
Uses WMIC.EXE to obtain a system information
- OVPN.exe (PID: 2652)
INFO
Reads the hosts file
- chrome.exe (PID: 3880)
- chrome.exe (PID: 2784)
Reads settings of System Certificates
- chrome.exe (PID: 3880)
- tapinstall.exe (PID: 3204)
- DrvInst.exe (PID: 1520)
- tapinstall.exe (PID: 3996)
- tapinstall.exe (PID: 3604)
- tapinstall.exe (PID: 1440)
- tapinstall.exe (PID: 392)
Reads Internet Cache Settings
- chrome.exe (PID: 2784)
Application launched itself
- chrome.exe (PID: 2784)
Dropped object may contain Bitcoin addresses
- OVPN.exe (PID: 4008)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2764)
Searches for installed software
- DrvInst.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
54
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe" find tap0901 | C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe | — | ovpn-controller.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 392 | "C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe" driverfiles @ROOT\NET\0000 | C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe | — | ovpn-controller.exe | |||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 528 | "C:\Program Files\OVPN\ovpn-daemon.exe" | C:\Program Files\OVPN\ovpn-daemon.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 1.8.1.2948 Modules
| |||||||||||||||
| 580 | "C:\Program Files\OVPN\OVPNUninstaller.exe" --checkupdates | C:\Program Files\OVPN\OVPNUninstaller.exe | OVPN.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 580 | cscript //Nologo C:\Users\admin\AppData\Local\Temp\deferredrenameRm3716.vbs | C:\Windows\system32\cscript.exe | OVPN.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1344918207105440434,7727677917971419389,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9383586115470717365 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe" find tap0901 | C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe | — | ovpn-controller.exe | |||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\OVPN/killswitch.exe" | C:\Program Files\OVPN\killswitch.exe | — | ovpn-daemon.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1356 | C:\Windows\system32\net1 start OVPNService | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1440 | "C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe" drivernodes @ROOT\NET\0000 | C:\Program Files\OVPN\openvpn\x86\bin\tapinstall.exe | — | ovpn-controller.exe | |||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
Total events
2 730
Read events
2 001
Write events
676
Delete events
53
Modification events
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2784-13230120389519375 |
Value: 259 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
90
Suspicious files
351
Text files
839
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E830CC5-AE0.pma | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e1416586-9137-4d5e-941b-a44ffc46c608.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66bd2.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66be1.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66db6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
18
DNS requests
10
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3880 | chrome.exe | 217.64.148.10:443 | files.ovpn.com | — | IR | unknown |
3880 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3880 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 172.217.22.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
580 | OVPNUninstaller.exe | 217.64.148.10:443 | files.ovpn.com | — | IR | unknown |
2652 | OVPN.exe | 217.64.148.10:443 | files.ovpn.com | — | IR | unknown |
3880 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
files.ovpn.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.ovpn.com |
| unknown |
Threats
Process | Message |
|---|---|
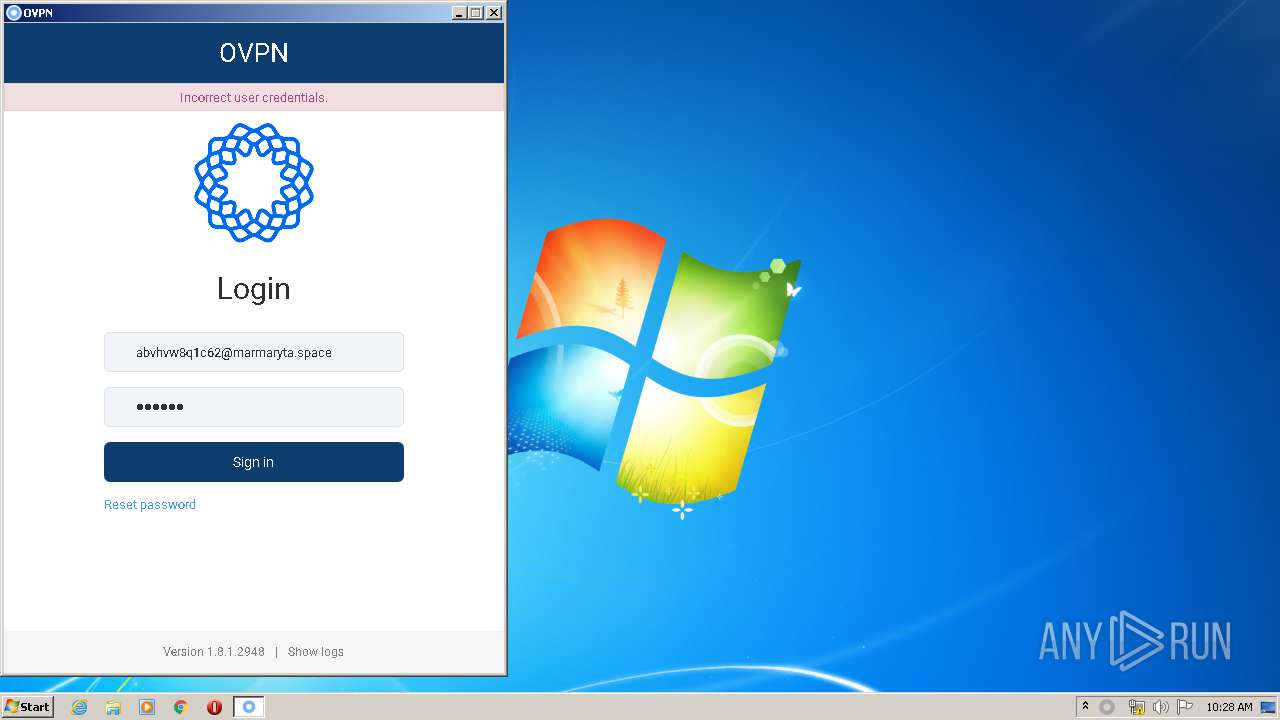
OVPN.exe | Keychain: Restoring data failed for account "https://www.ovpn.com", error text: Password entry not found
|