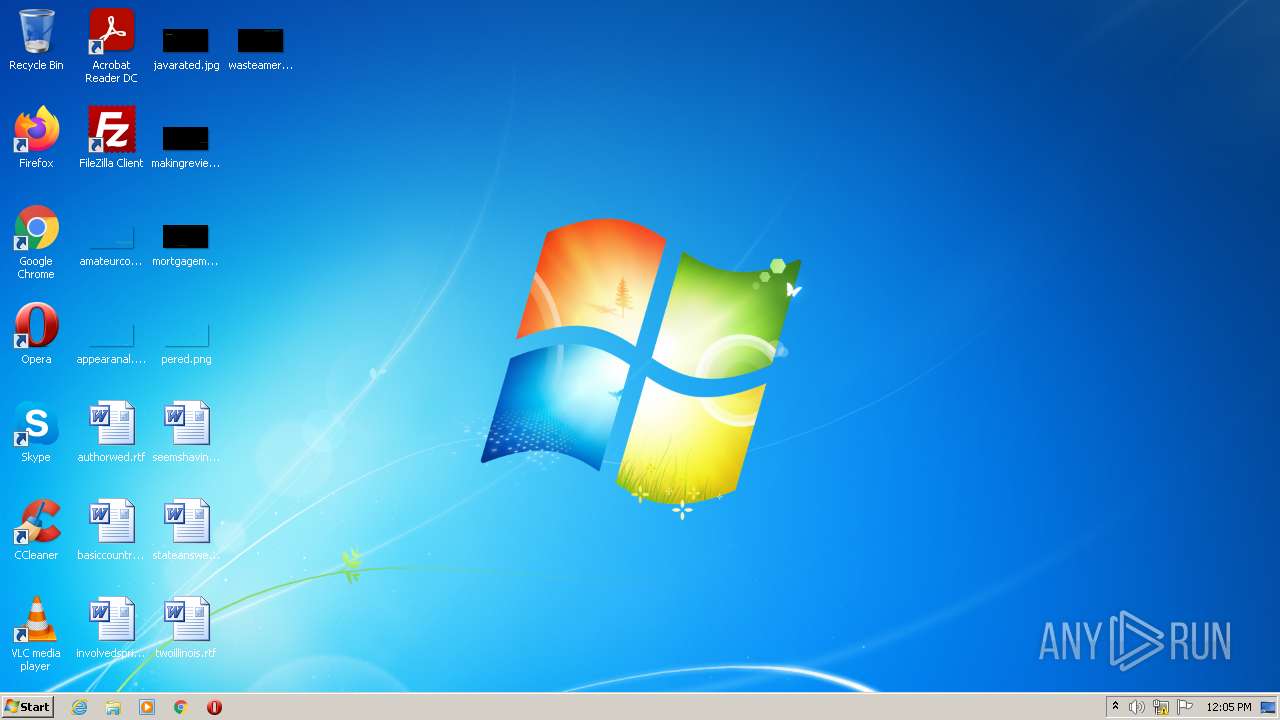
| File name: | sus.exe |
| Full analysis: | https://app.any.run/tasks/0351f52a-0bca-410f-a864-7ed5ff390bf6 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 11:05:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 759CC9814D49DE530345974B960F696B |
| SHA1: | F2582E7025834D967F09CDE24FE4773B09730907 |
| SHA256: | 7779C10C0C16791E8F51F905845CEEFE2F1C18D7DA3C41BC8FEC4F75D7322211 |
| SSDEEP: | 98304:gJ4enhMb5DzQ0bJPE94FyQByxqjae1MRuo6rF6JG:gJPhCDzQIVE9NQxGsMRuJaG |
MALICIOUS
Drops executable file immediately after starts
- sus.exe (PID: 2832)
- 1233.sfx.exe (PID: 3764)
- 1233.exe (PID: 3628)
- BrowserruntimeBroker.exe (PID: 2760)
Application was dropped or rewritten from another process
- 1233.exe (PID: 3628)
- BrowserruntimeBroker.exe (PID: 2760)
- services.exe (PID: 1384)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3136)
- schtasks.exe (PID: 2776)
- schtasks.exe (PID: 3020)
- schtasks.exe (PID: 2124)
- schtasks.exe (PID: 3596)
- schtasks.exe (PID: 2164)
- schtasks.exe (PID: 1196)
- schtasks.exe (PID: 2288)
- schtasks.exe (PID: 4032)
- schtasks.exe (PID: 2664)
- schtasks.exe (PID: 2596)
- schtasks.exe (PID: 2476)
- schtasks.exe (PID: 2764)
- schtasks.exe (PID: 2932)
- schtasks.exe (PID: 3200)
SUSPICIOUS
Executable content was dropped or overwritten
- sus.exe (PID: 2832)
- 1233.sfx.exe (PID: 3764)
- 1233.exe (PID: 3628)
- BrowserruntimeBroker.exe (PID: 2760)
Checks supported languages
- sus.exe (PID: 2832)
- 1233.sfx.exe (PID: 3764)
- 1233.exe (PID: 3628)
- WScript.exe (PID: 1808)
- cmd.exe (PID: 2728)
- BrowserruntimeBroker.exe (PID: 2760)
- services.exe (PID: 1384)
Reads the computer name
- sus.exe (PID: 2832)
- 1233.sfx.exe (PID: 3764)
- 1233.exe (PID: 3628)
- WScript.exe (PID: 1808)
- BrowserruntimeBroker.exe (PID: 2760)
- services.exe (PID: 1384)
Starts itself from another location
- sus.exe (PID: 2832)
- BrowserruntimeBroker.exe (PID: 2760)
Drops a file with a compile date too recent
- sus.exe (PID: 2832)
- 1233.sfx.exe (PID: 3764)
- 1233.exe (PID: 3628)
- BrowserruntimeBroker.exe (PID: 2760)
Creates files in the user directory
- 1233.exe (PID: 3628)
Executes scripts
- 1233.exe (PID: 3628)
Executed via WMI
- schtasks.exe (PID: 2124)
- schtasks.exe (PID: 3136)
- schtasks.exe (PID: 2776)
- schtasks.exe (PID: 3020)
- schtasks.exe (PID: 4032)
- schtasks.exe (PID: 3596)
- schtasks.exe (PID: 2164)
- schtasks.exe (PID: 1196)
- schtasks.exe (PID: 2288)
- schtasks.exe (PID: 2764)
- schtasks.exe (PID: 2932)
- schtasks.exe (PID: 2476)
- schtasks.exe (PID: 2664)
- schtasks.exe (PID: 3200)
- schtasks.exe (PID: 2596)
Reads Environment values
- BrowserruntimeBroker.exe (PID: 2760)
- services.exe (PID: 1384)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 1808)
Creates executable files which already exist in Windows
- BrowserruntimeBroker.exe (PID: 2760)
Reads the date of Windows installation
- rundll32.exe (PID: 2228)
INFO
Reads the computer name
- schtasks.exe (PID: 3136)
- schtasks.exe (PID: 3596)
- schtasks.exe (PID: 3020)
- schtasks.exe (PID: 2124)
- schtasks.exe (PID: 2776)
- schtasks.exe (PID: 2164)
- schtasks.exe (PID: 1196)
- schtasks.exe (PID: 4032)
- schtasks.exe (PID: 2288)
- schtasks.exe (PID: 2476)
- schtasks.exe (PID: 2664)
- schtasks.exe (PID: 2596)
- schtasks.exe (PID: 3200)
- schtasks.exe (PID: 2764)
- schtasks.exe (PID: 2932)
- rundll32.exe (PID: 2228)
Checks Windows Trust Settings
- WScript.exe (PID: 1808)
Checks supported languages
- schtasks.exe (PID: 2776)
- schtasks.exe (PID: 3020)
- schtasks.exe (PID: 2124)
- schtasks.exe (PID: 3596)
- schtasks.exe (PID: 2164)
- schtasks.exe (PID: 2288)
- schtasks.exe (PID: 1196)
- schtasks.exe (PID: 4032)
- schtasks.exe (PID: 2664)
- schtasks.exe (PID: 2596)
- schtasks.exe (PID: 2476)
- schtasks.exe (PID: 2764)
- schtasks.exe (PID: 3200)
- schtasks.exe (PID: 2932)
- rundll32.exe (PID: 2228)
- NOTEPAD.EXE (PID: 3304)
- schtasks.exe (PID: 3136)
Manual execution by user
- rundll32.exe (PID: 2228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x14220 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 331264 |
| CodeSize: | 156160 |
| LinkerVersion: | 14.3 |
| PEType: | PE32 |
| TimeStamp: | 2022:03:03 14:16:04+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Mar-2022 13:16:04 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-Mar-2022 13:16:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000261EC | 0x00026200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69378 |
.rdata | 0x00028000 | 0x0000A2DE | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26322 |
.data | 0x00033000 | 0x00035D60 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.07618 |
.didat | 0x00069000 | 0x00000160 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.04904 |
.rsrc | 0x0006A000 | 0x0000DFF8 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63857 |
.reloc | 0x00078000 | 0x00002878 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6547 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11236 | 440 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
59
Monitored processes
24
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1196 | schtasks.exe /create /tn "csrss" /sc ONLOGON /tr "'C:\MSOCache\All Users\{90140000-0019-041F-0000-0000000FF1CE}-C\csrss.exe'" /rl HIGHEST /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1384 | "C:\Users\admin\Desktop\services.exe" | C:\Users\admin\Desktop\services.exe | — | BrowserruntimeBroker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1808 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\WinRAR\wESs858y4EGPUPl7YBxtM1FOkU.vbe" | C:\Windows\System32\WScript.exe | — | 1233.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2124 | schtasks.exe /create /tn "smss" /sc ONLOGON /tr "'C:\MSOCache\All Users\{90140000-002C-0C0A-0000-0000000FF1CE}-C\Proof.pt-br\smss.exe'" /rl HIGHEST /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | schtasks.exe /create /tn "csrssc" /sc MINUTE /mo 14 /tr "'C:\MSOCache\All Users\{90140000-0019-041F-0000-0000000FF1CE}-C\csrss.exe'" /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
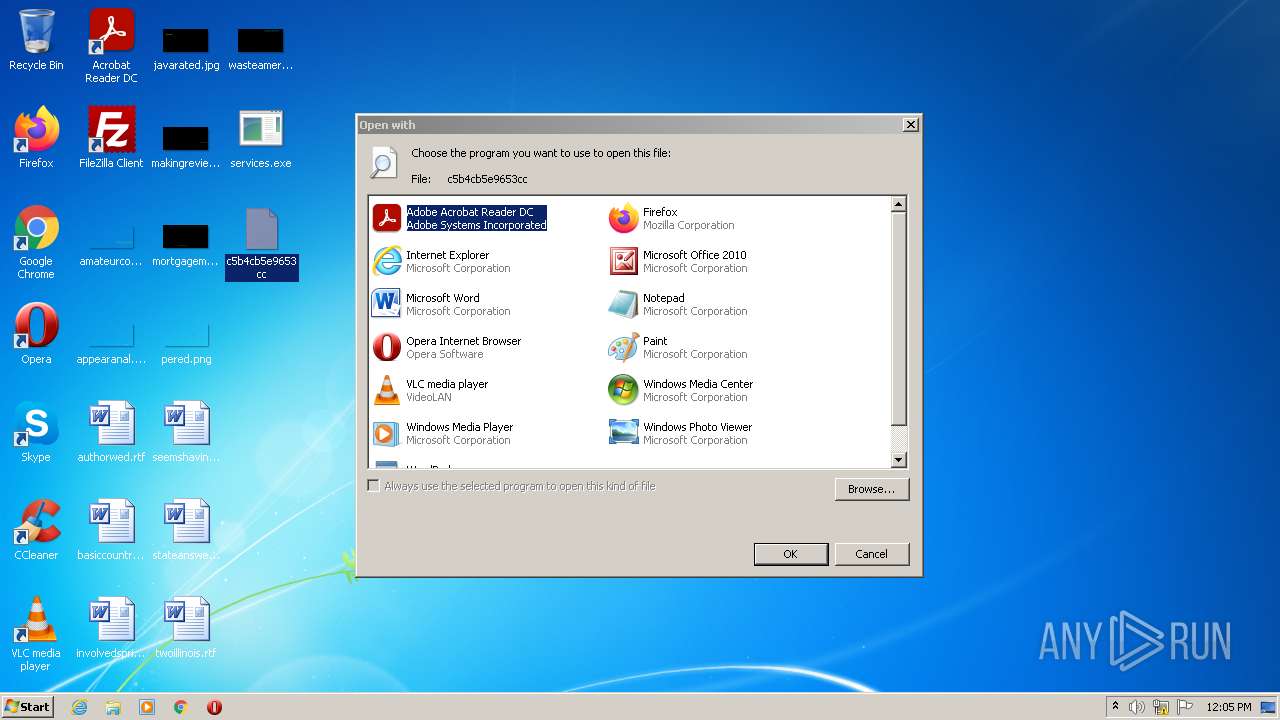
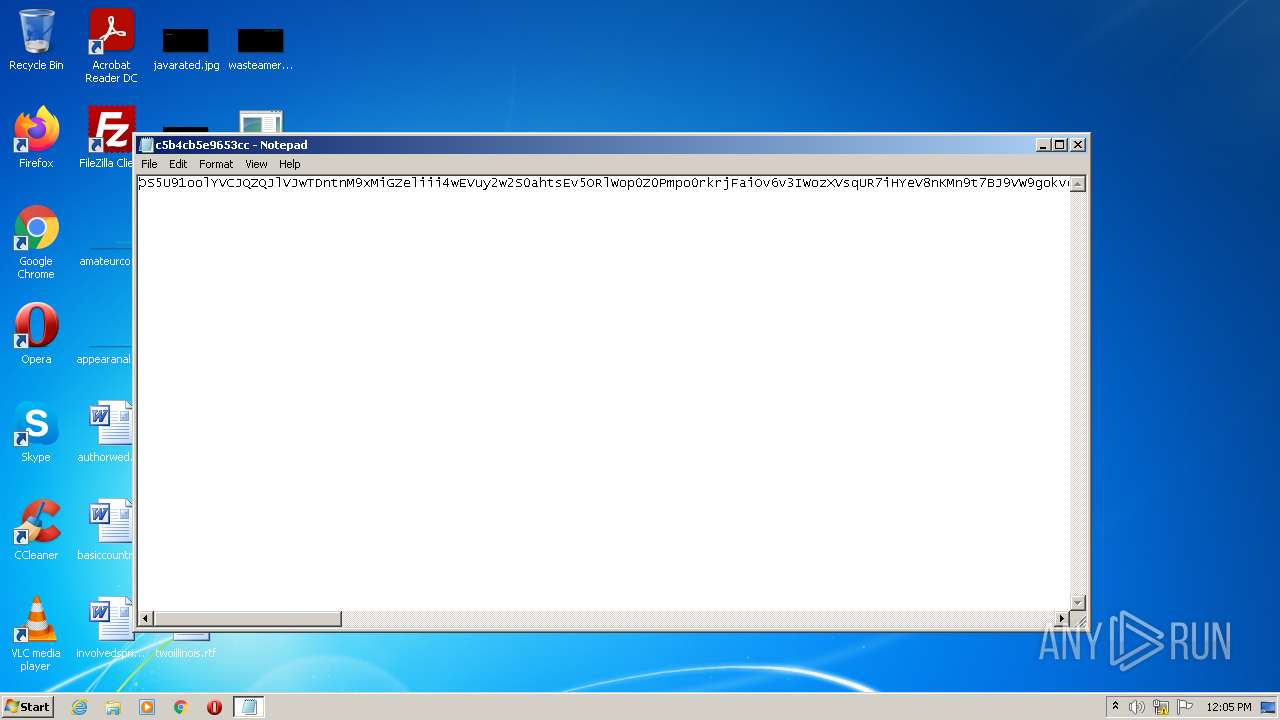
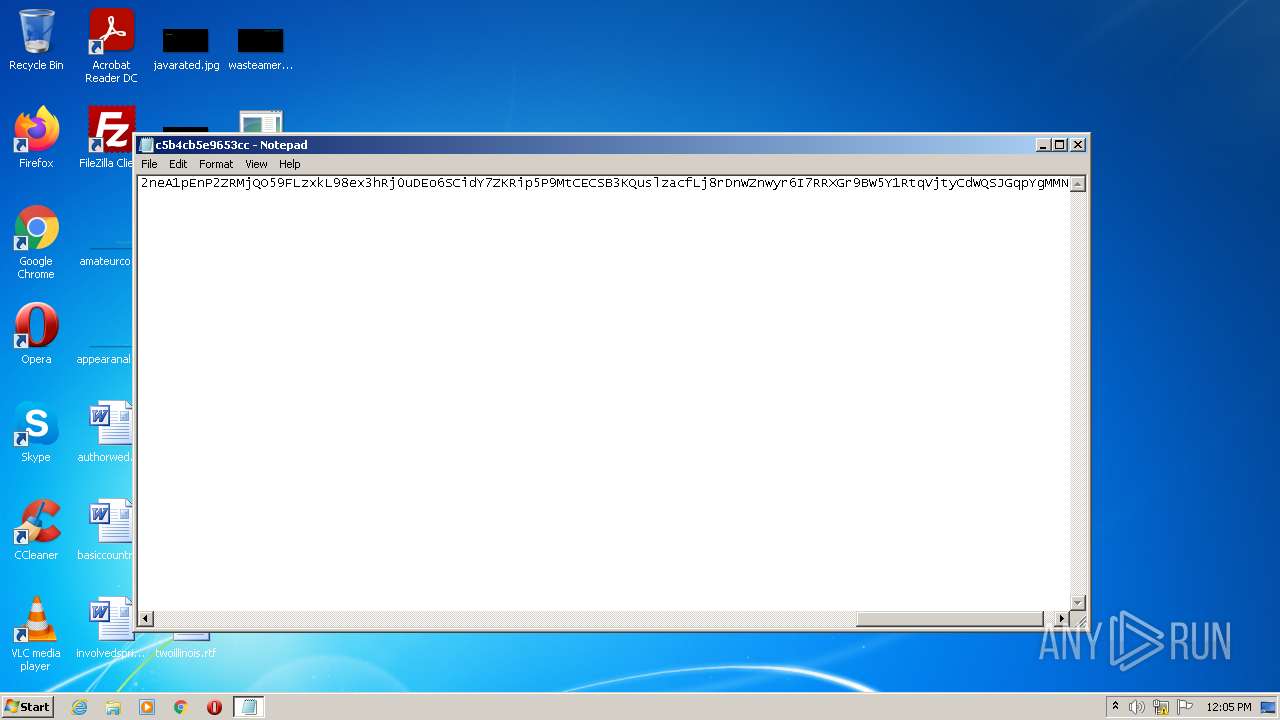
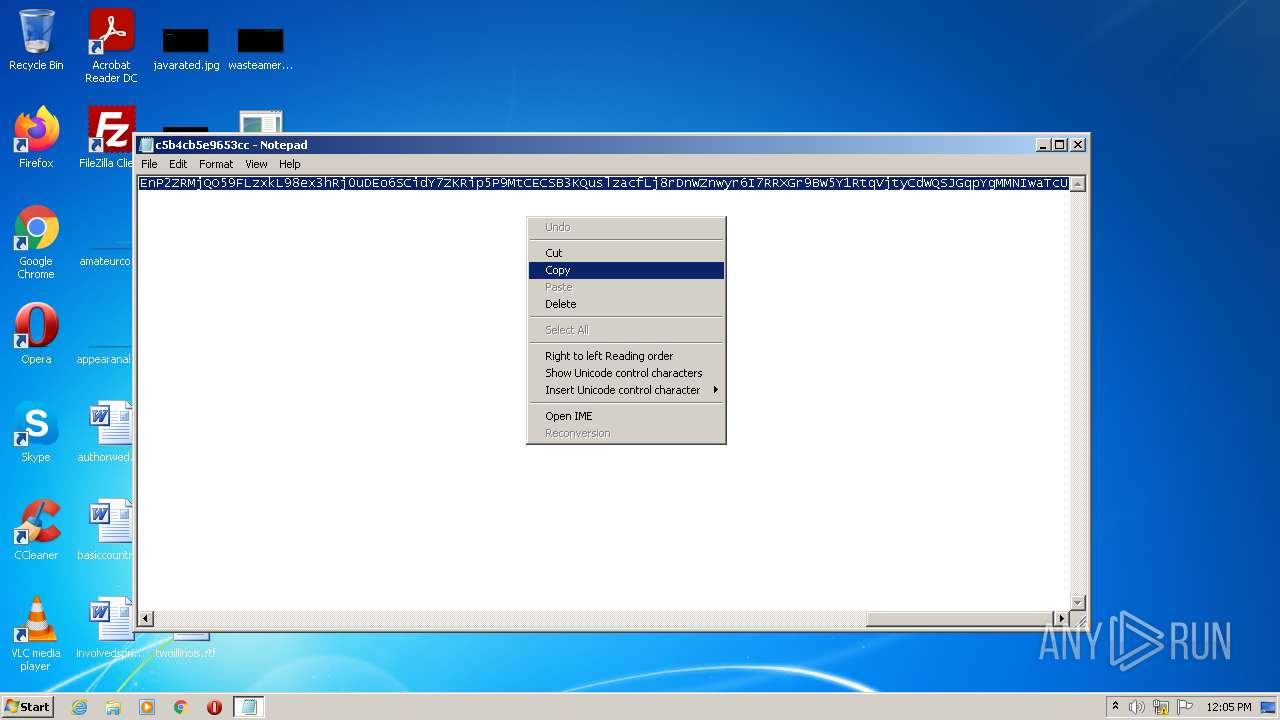
| 2228 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\c5b4cb5e9653cc | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | schtasks.exe /create /tn "csrssc" /sc MINUTE /mo 10 /tr "'C:\MSOCache\All Users\{90140000-0019-041F-0000-0000000FF1CE}-C\csrss.exe'" /rl HIGHEST /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | schtasks.exe /create /tn "cmdc" /sc MINUTE /mo 9 /tr "'C:\MSOCache\All Users\{90140000-0044-0C0A-0000-0000000FF1CE}-C\cmd.exe'" /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2596 | schtasks.exe /create /tn "cmdc" /sc MINUTE /mo 7 /tr "'C:\MSOCache\All Users\{90140000-0044-0C0A-0000-0000000FF1CE}-C\cmd.exe'" /rl HIGHEST /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | schtasks.exe /create /tn "cmd" /sc ONLOGON /tr "'C:\MSOCache\All Users\{90140000-0044-0C0A-0000-0000000FF1CE}-C\cmd.exe'" /rl HIGHEST /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 945
Read events
4 817
Write events
128
Delete events
0
Modification events
| (PID) Process: | (2832) sus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2832) sus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2832) sus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2832) sus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3764) 1233.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3764) 1233.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3764) 1233.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3764) 1233.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3628) 1233.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3628) 1233.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
9
Suspicious files
0
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3764 | 1233.sfx.exe | C:\Users\admin\AppData\Local\Temp\1233.exe | executable | |
MD5:— | SHA256:— | |||
| 3628 | 1233.exe | C:\Users\admin\AppData\Roaming\WinRAR\0fA6uq8R.bat | text | |
MD5:— | SHA256:— | |||
| 3628 | 1233.exe | C:\Users\admin\AppData\Roaming\WinRAR\BrowserruntimeBroker.exe | executable | |
MD5:— | SHA256:— | |||
| 3628 | 1233.exe | C:\Users\admin\AppData\Roaming\WinRAR\wESs858y4EGPUPl7YBxtM1FOkU.vbe | vbe | |
MD5:— | SHA256:— | |||
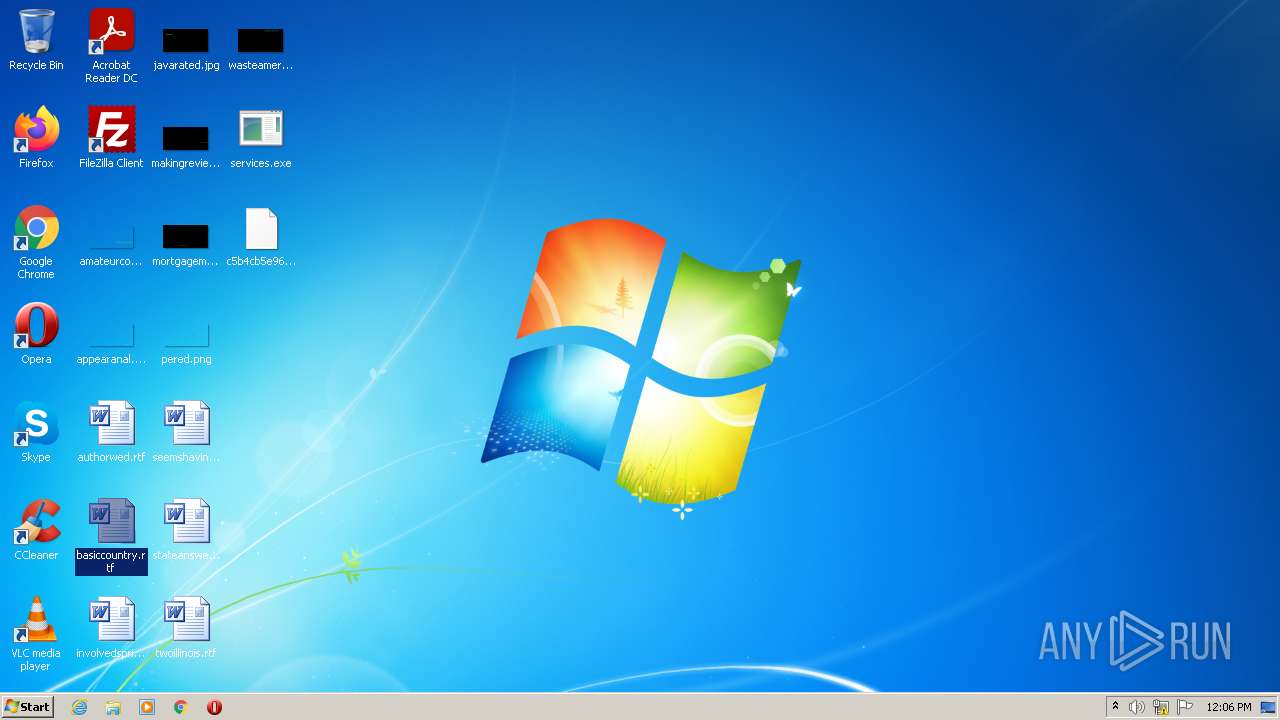
| 2760 | BrowserruntimeBroker.exe | C:\Users\admin\Desktop\services.exe | executable | |
MD5:— | SHA256:— | |||
| 2760 | BrowserruntimeBroker.exe | C:\MSOCache\All Users\{90140000-002C-0C0A-0000-0000000FF1CE}-C\Proof.pt-br\smss.exe | executable | |
MD5:— | SHA256:— | |||
| 2760 | BrowserruntimeBroker.exe | C:\MSOCache\All Users\{90140000-002C-0C0A-0000-0000000FF1CE}-C\Proof.pt-br\69ddcba757bf72 | text | |
MD5:— | SHA256:— | |||
| 2760 | BrowserruntimeBroker.exe | C:\MSOCache\All Users\{90140000-0019-041F-0000-0000000FF1CE}-C\886983d96e3d3e | text | |
MD5:— | SHA256:— | |||
| 2832 | sus.exe | C:\Users\admin\AppData\Local\Temp\1233.sfx.exe | executable | |
MD5:— | SHA256:— | |||
| 2760 | BrowserruntimeBroker.exe | C:\Users\admin\Desktop\c5b4cb5e9653cc | text | |
MD5:6746DBA6A5364B95163D4B17079182C9 | SHA256:D276EFA7EBE336C7F8739F3FA7355F6960D72DC6404FAACD661900FC568EDC8D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
gay.sytes.net |
| malicious |
Threats
1 ETPRO signatures available at the full report