| File name: | Application.exe |
| Full analysis: | https://app.any.run/tasks/69307e36-5f82-44d0-87b8-ee894b3d533d |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2021, 21:14:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 11B2945D35F844C4DEA64490499B58DE |
| SHA1: | BB5B05AF01860AC4327FD5A9EB57EDE3F365CF7B |
| SHA256: | 776BB07C4EEFDB326DA76FE0AEE3F6BABE05BEA6AE0FF741A97E712D93F347C7 |
| SSDEEP: | 6144:qqI9NpdU/P0m1e8ZP8/qyh0JZ3xdbi6r6N5dE07vKtM7P1950XuqR88jvtxh27:qdNpdU/PjXJM6ra5a0vK4P130XusVq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 2212)
Creates files in the program directory
- javaw.exe (PID: 2212)
Checks supported languages
- javaw.exe (PID: 2212)
- Application.exe (PID: 2388)
Check for Java to be installed
- Application.exe (PID: 2388)
Executes JAVA applets
- Application.exe (PID: 2388)
Executed as Windows Service
- fxssvc.exe (PID: 3640)
- fxssvc.exe (PID: 2348)
Creates files in the Windows directory
- fxssvc.exe (PID: 3640)
Executed via COM
- DeviceDisplayObjectProvider.exe (PID: 1120)
INFO
Reads the computer name
- icacls.exe (PID: 2016)
- fxssvc.exe (PID: 3640)
- regedit.exe (PID: 2548)
- fxssvc.exe (PID: 2348)
Checks supported languages
- icacls.exe (PID: 2016)
- regedit.exe (PID: 2548)
- fxssvc.exe (PID: 3640)
- fxssvc.exe (PID: 2348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| ProductVersion: | 0.1.0.0 |
|---|---|
| ProductName: | Application |
| OriginalFileName: | Application.exe |
| LegalCopyright: | 2021 |
| InternalName: | Application |
| FileVersion: | 0.1.0.0 |
| FileDescription: | Application |
| CompanyName: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 0.1.0.0 |
| FileVersionNumber: | 0.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1290 |
| UninitializedDataSize: | 36864 |
| InitializedDataSize: | 7680 |
| CodeSize: | 18432 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2021:09:07 23:14:22+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Sep-2021 21:14:22 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | Application |
| FileVersion: | 0.1.0.0 |
| InternalName: | Application |
| LegalCopyright: | 2021 |
| OriginalFilename: | Application.exe |
| ProductName: | Application |
| ProductVersion: | 0.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 07-Sep-2021 21:14:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004788 | 0x00004800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.07342 |
.data | 0x00006000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.346693 |
.rdata | 0x00007000 | 0x00000520 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06836 |
.bss | 0x00008000 | 0x00008EF0 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000A94 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.61998 |
.rsrc | 0x00012000 | 0x00000970 | 0x00000A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03255 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.98093 | 356 | UNKNOWN | Process Default Language | RT_MANIFEST |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
10 | 2.5 | 8 | UNKNOWN | Process Default Language | RT_RCDATA |
15 | 3.61687 | 17 | UNKNOWN | Process Default Language | RT_RCDATA |
16 | 3.75444 | 22 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 3.91327 | 25 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
47
Monitored processes
8
Malicious processes
0
Suspicious processes
1
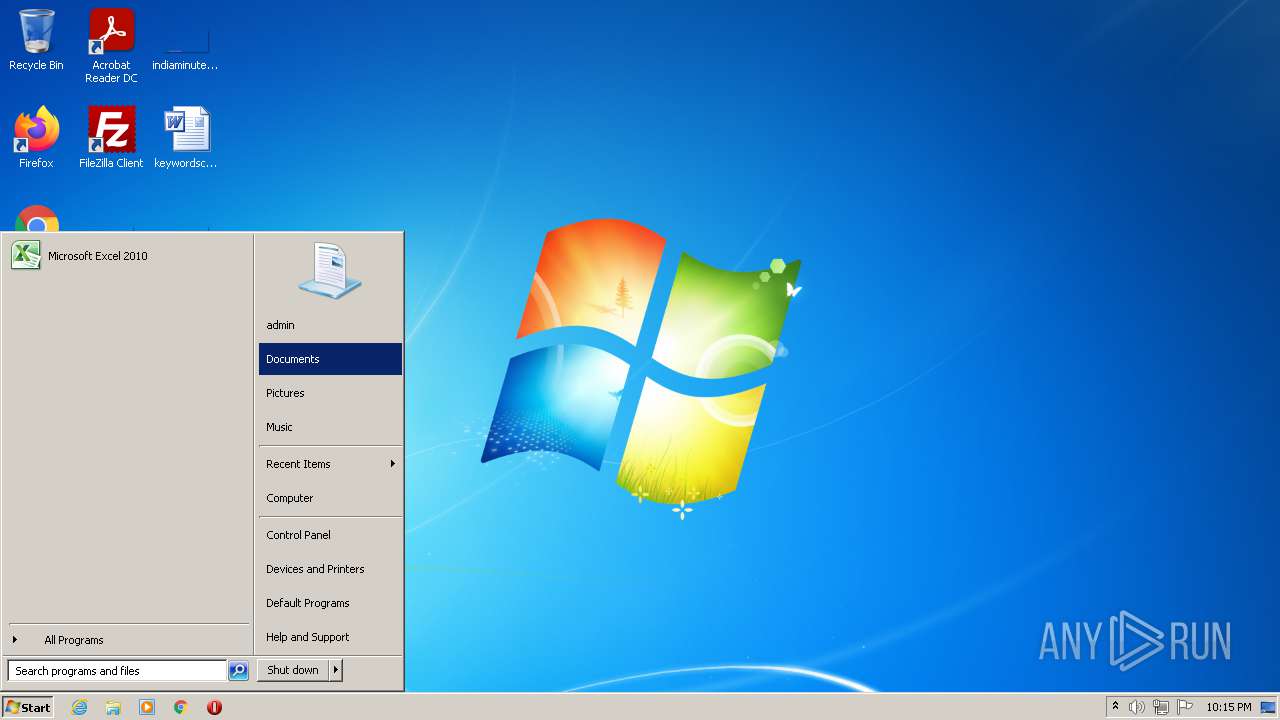
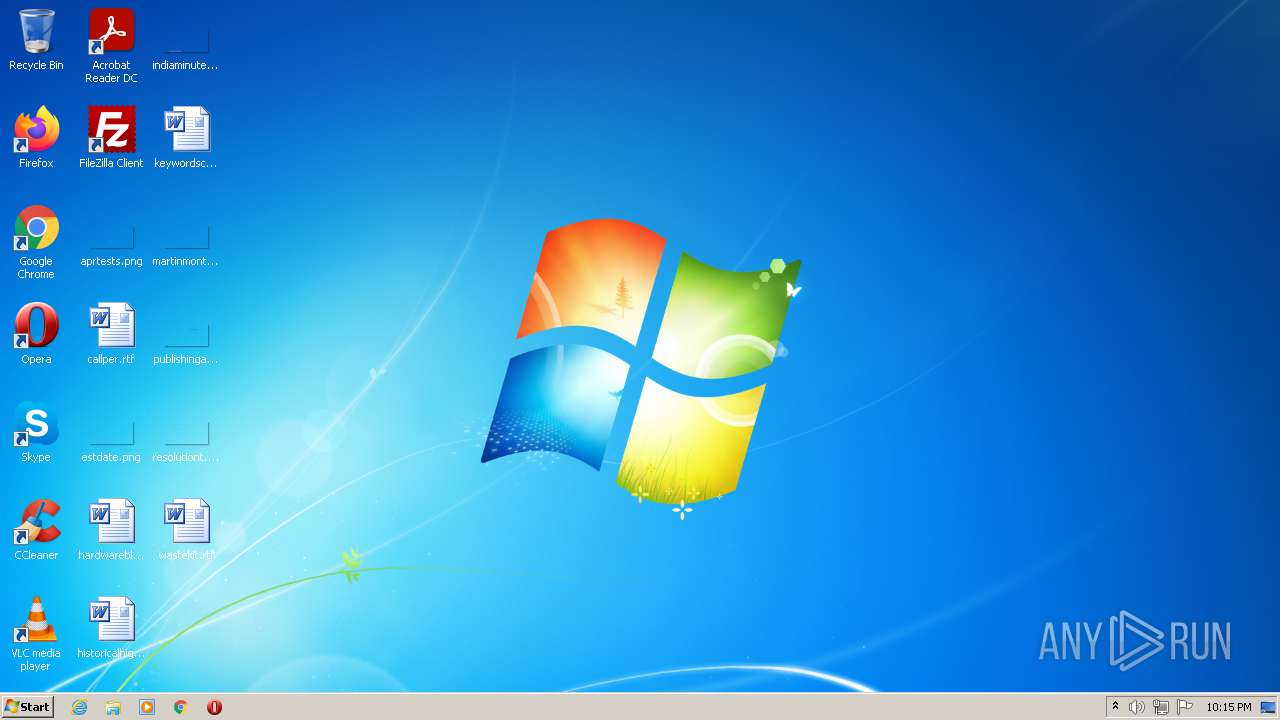
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1120 | C:\Windows\system32\DeviceDisplayObjectProvider.exe -Embedding | C:\Windows\system32\DeviceDisplayObjectProvider.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Display Object Function Discovery Provider Exit code: 3221225852 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Xms128m -Xmx1024m -classpath "C:\Users\admin\AppData\Local\Temp\Application.exe;commons-io-2.11.0.jar" com.example.Main | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | Application.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2348 | C:\Windows\system32\fxssvc.exe | C:\Windows\system32\fxssvc.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Fax Service Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
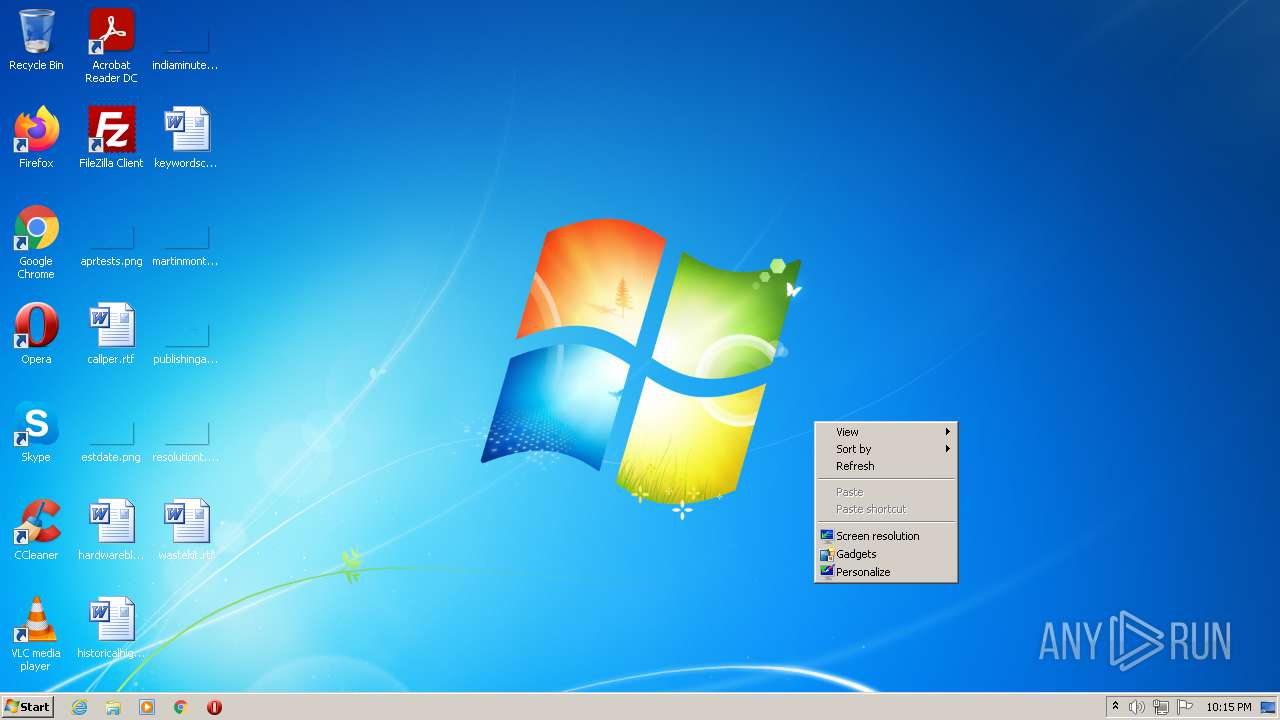
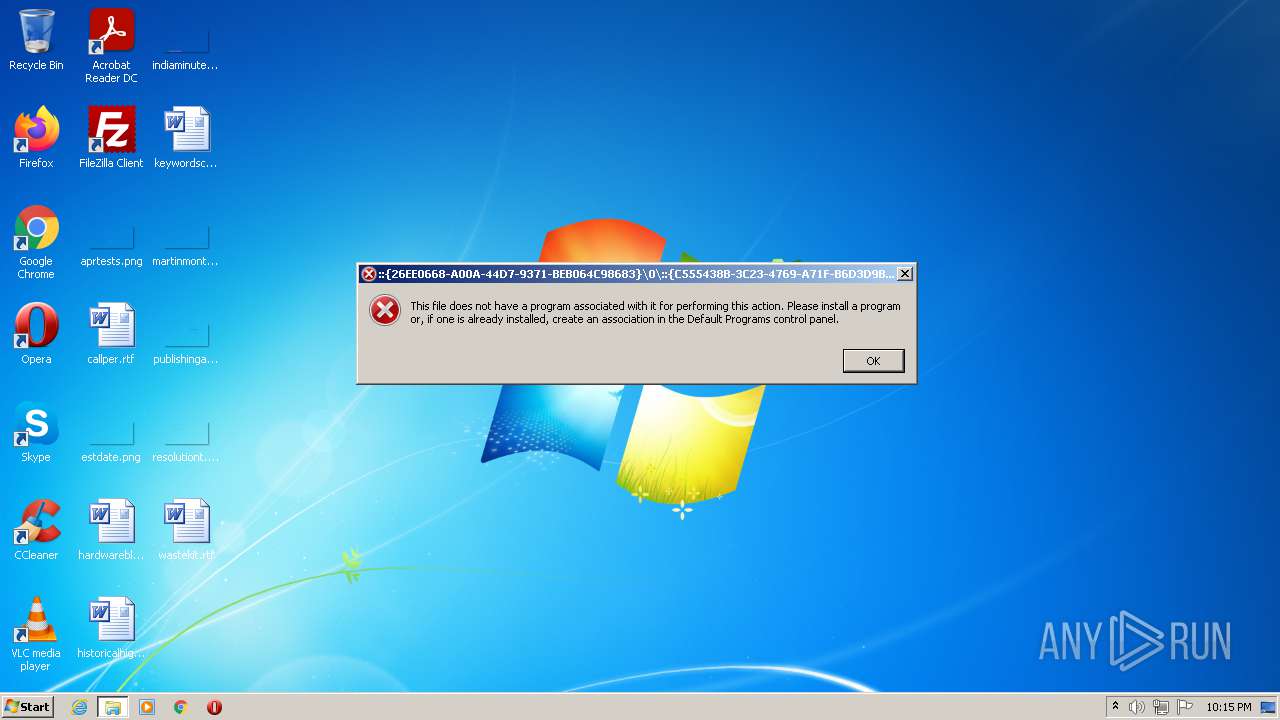
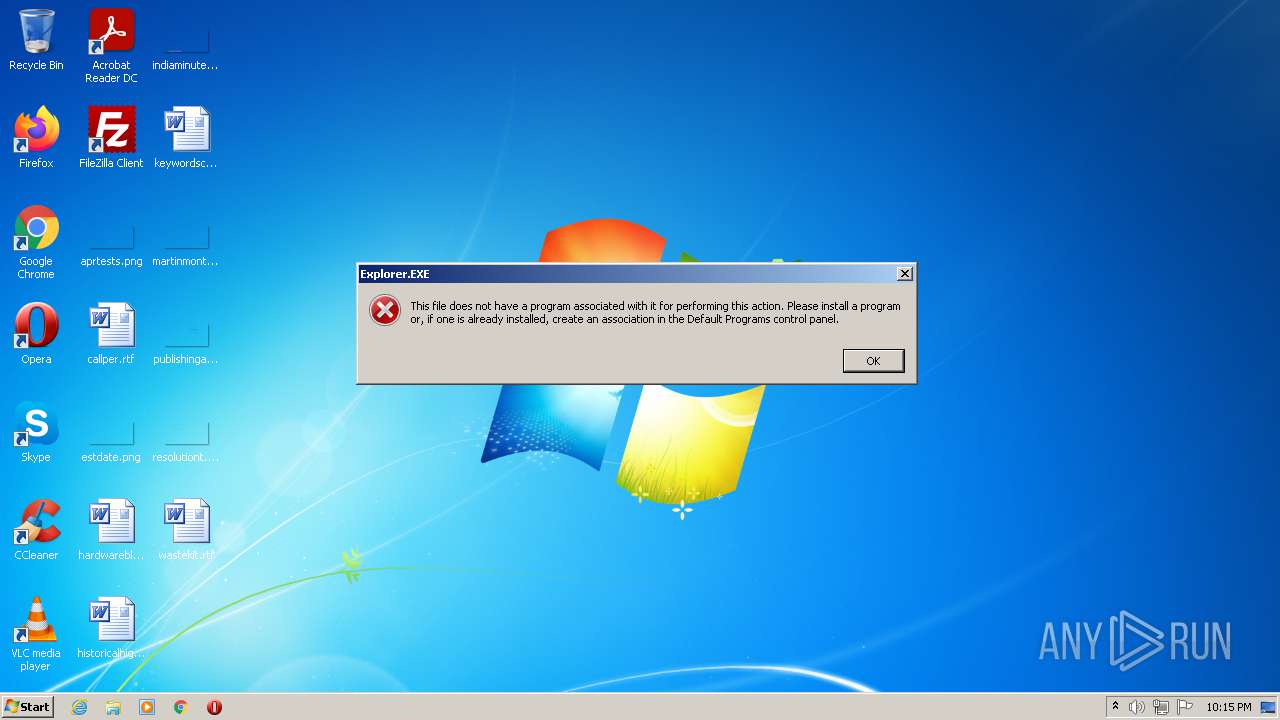
| 2388 | "C:\Users\admin\AppData\Local\Temp\Application.exe" | C:\Users\admin\AppData\Local\Temp\Application.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Application Exit code: 0 Version: 0.1.0.0 Modules
| |||||||||||||||
| 2548 | regedit /s C:\Users\admin\AppData\Local\Temp\file.reg | C:\Windows\regedit.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
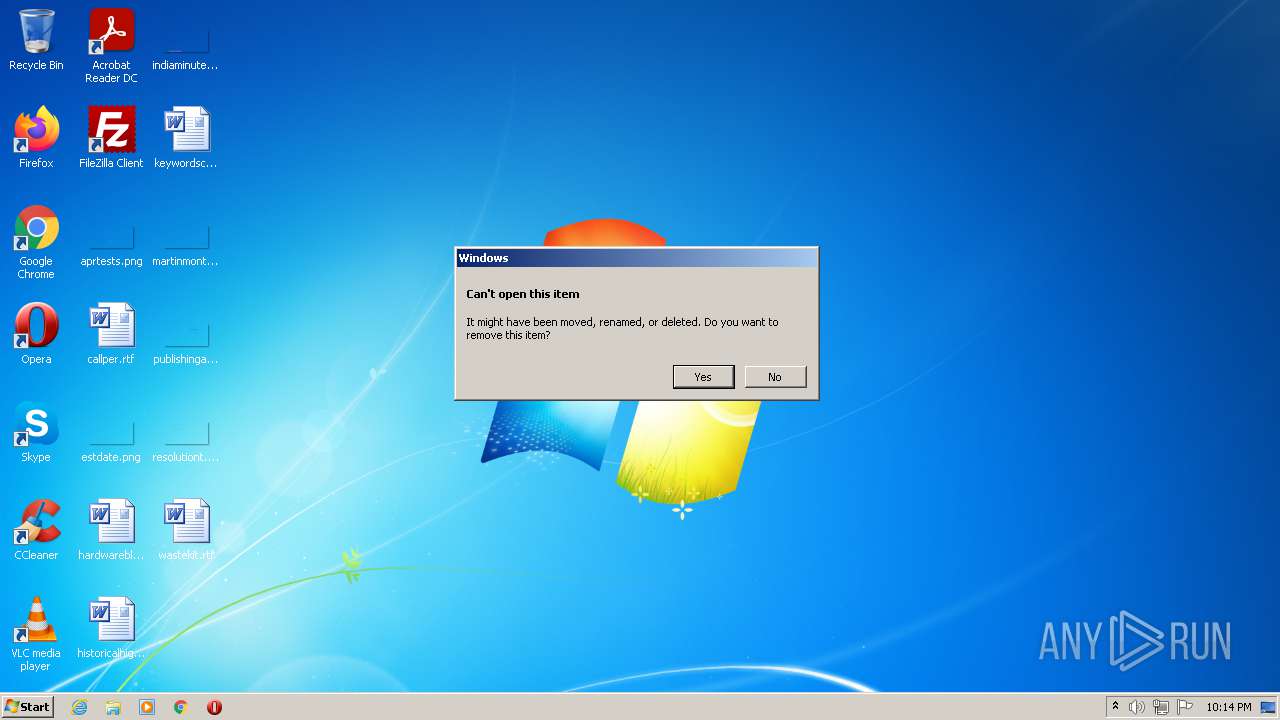
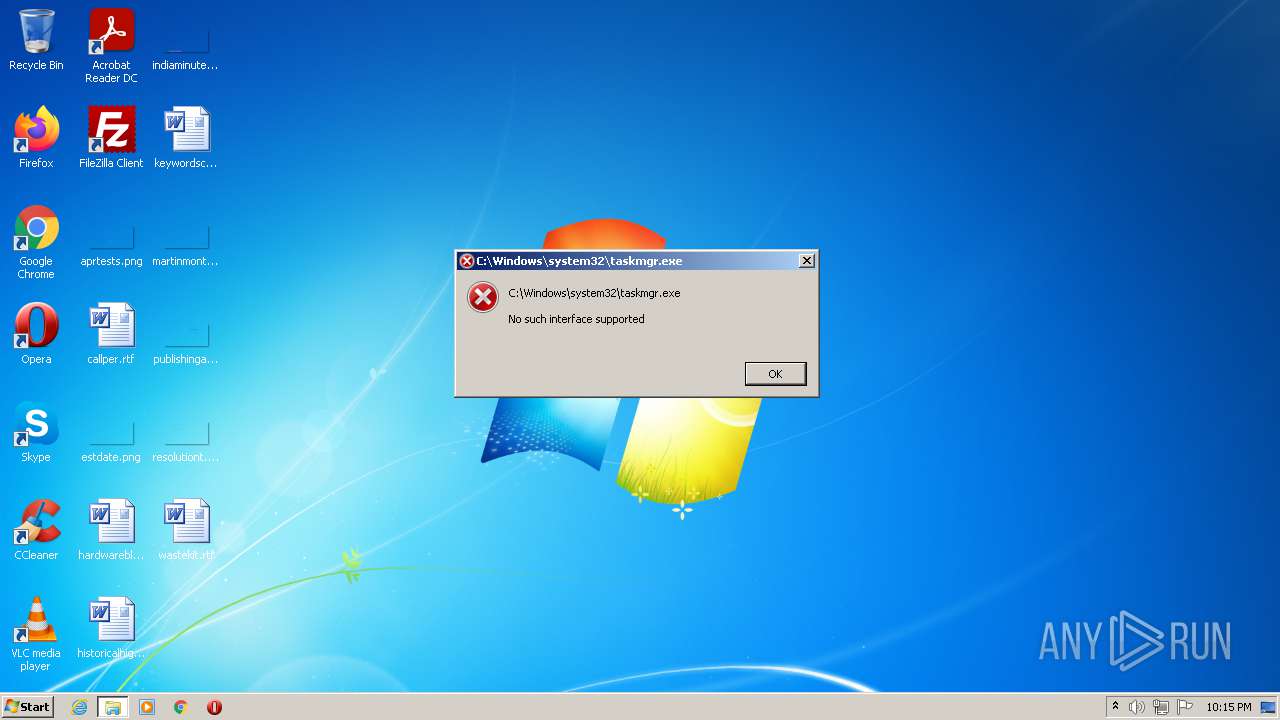
| 2732 | "C:\Users\admin\AppData\Local\Temp\Application.exe" | C:\Users\admin\AppData\Local\Temp\Application.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application Exit code: 3221226540 Version: 0.1.0.0 Modules
| |||||||||||||||
| 3640 | C:\Windows\system32\fxssvc.exe | C:\Windows\system32\fxssvc.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Fax Service Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
178 167
Read events
953
Write events
0
Delete events
177 214
Modification events
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\DSDT\DELL_\DELLDSDT\00000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\DSDT\DELL_\DELLDSDT |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\DSDT\DELL_ |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\DSDT |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\FACS |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\FADT\DELL_\DELLFACP\00000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\FADT\DELL_\DELLFACP |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\FADT\DELL_ |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\FADT |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2548) regedit.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\ACPI\RSDT\DELL_\DELLRSDT\00000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2212 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 2212 | javaw.exe | C:\Users\admin\AppData\Local\Temp\file.reg | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report