| File name: | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe |
| Full analysis: | https://app.any.run/tasks/0655fec4-c7d5-4f66-a741-20a6aebfb66f |
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2025, 01:15:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | E9FD67AF728448A36D1CB198B120B408 |
| SHA1: | 7E58280F220F530A3AD4B276611F056C52DF1D96 |
| SHA256: | 77671BBA05E63085613A299F07D6AB05503F558F844FE534FD456454A066F087 |
| SSDEEP: | 98304:3j+pzhreZxRMdREZX6ek1aBMU9VovGV7TB9czGm5N0QgMOmIz764XllNGOxUIADB:554du3Tg2gAA1yh2mqR |
MALICIOUS
Executing a file with an untrusted certificate
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7448)
- certutil.exe (PID: 3320)
- certutil.exe (PID: 5236)
Connects to the CnC server
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Changes settings of System certificates
- certmgr.exe (PID: 7620)
Changes the autorun value in the registry
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
SUSPICIOUS
Executable content was dropped or overwritten
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
The process creates files with name similar to system file names
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Process drops legitimate windows executable
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
The process drops C-runtime libraries
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Uses NETSH.EXE to add a firewall rule or allowed programs
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Reads security settings of Internet Explorer
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- I3GProc.exe (PID: 2780)
- I3GInit.exe (PID: 8020)
Contacting a server suspected of hosting an CnC
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Adds/modifies Windows certificates
- certmgr.exe (PID: 7620)
Reads the BIOS version
- I3GProc.exe (PID: 2780)
- I3GProc.exe (PID: 4452)
Non windows owned service launched
- I3GMainSvc.exe (PID: 7996)
Executes as Windows Service
- I3GMainSvc.exe (PID: 7996)
There is functionality for taking screenshot (YARA)
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- I3GMainSvc.exe (PID: 7996)
There is functionality for VM detection VirtualBox (YARA)
- I3GProc.exe (PID: 2780)
There is functionality for enable RDP (YARA)
- I3GProc.exe (PID: 2780)
There is functionality for VM detection VMWare (YARA)
- I3GProc.exe (PID: 2780)
INFO
Creates files in the program directory
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- openssl.exe (PID: 5276)
- openssl.exe (PID: 1296)
- openssl.exe (PID: 4712)
- openssl.exe (PID: 6372)
- openssl.exe (PID: 5956)
Reads Environment values
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Creates files or folders in the user directory
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- I3GInit.exe (PID: 8020)
- certutil.exe (PID: 5236)
Reads the computer name
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- certutil.exe (PID: 3320)
- certutil.exe (PID: 5236)
- I3GMainSvc.exe (PID: 6188)
- I3GMainSvc.exe (PID: 7988)
- I3GMainSvc.exe (PID: 7996)
- I3GProc.exe (PID: 2780)
- I3GInit.exe (PID: 8020)
Checks supported languages
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- certmgr.exe (PID: 1568)
- certmgr.exe (PID: 5972)
- certmgr.exe (PID: 5492)
- certmgr.exe (PID: 2124)
- openssl.exe (PID: 6372)
- openssl.exe (PID: 1296)
- certmgr.exe (PID: 7620)
- openssl.exe (PID: 5956)
- openssl.exe (PID: 5276)
- openssl.exe (PID: 4712)
- certutil.exe (PID: 3320)
- certutil.exe (PID: 5236)
- I3GMainSvc.exe (PID: 6188)
- I3GProc.exe (PID: 2780)
- I3GMainSvc.exe (PID: 7996)
- I3GMainSvc.exe (PID: 7988)
- I3GInit.exe (PID: 8020)
- I3GProc.exe (PID: 4452)
The sample compiled with english language support
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Checks proxy server information
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- I3GProc.exe (PID: 2780)
- I3GInit.exe (PID: 8020)
- slui.exe (PID: 8160)
The sample compiled with korean language support
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Creates a software uninstall entry
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Process checks computer location settings
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
- I3GProc.exe (PID: 2780)
Reads the machine GUID from the registry
- openssl.exe (PID: 5276)
- openssl.exe (PID: 6372)
- openssl.exe (PID: 1296)
- openssl.exe (PID: 5956)
- openssl.exe (PID: 4712)
- I3GProc.exe (PID: 2780)
- I3GInit.exe (PID: 8020)
- certmgr.exe (PID: 7620)
Launching a file from a Registry key
- 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe (PID: 7624)
Process checks whether UAC notifications are on
- I3GProc.exe (PID: 2780)
Manual execution by a user
- I3GProc.exe (PID: 4452)
Reads the software policy settings
- I3GInit.exe (PID: 8020)
- slui.exe (PID: 8160)
Themida protector has been detected
- I3GProc.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:02 03:01:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 1236992 |
| InitializedDataSize: | 9635328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x107d3b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.24 |
| ProductVersionNumber: | 3.0.0.24 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
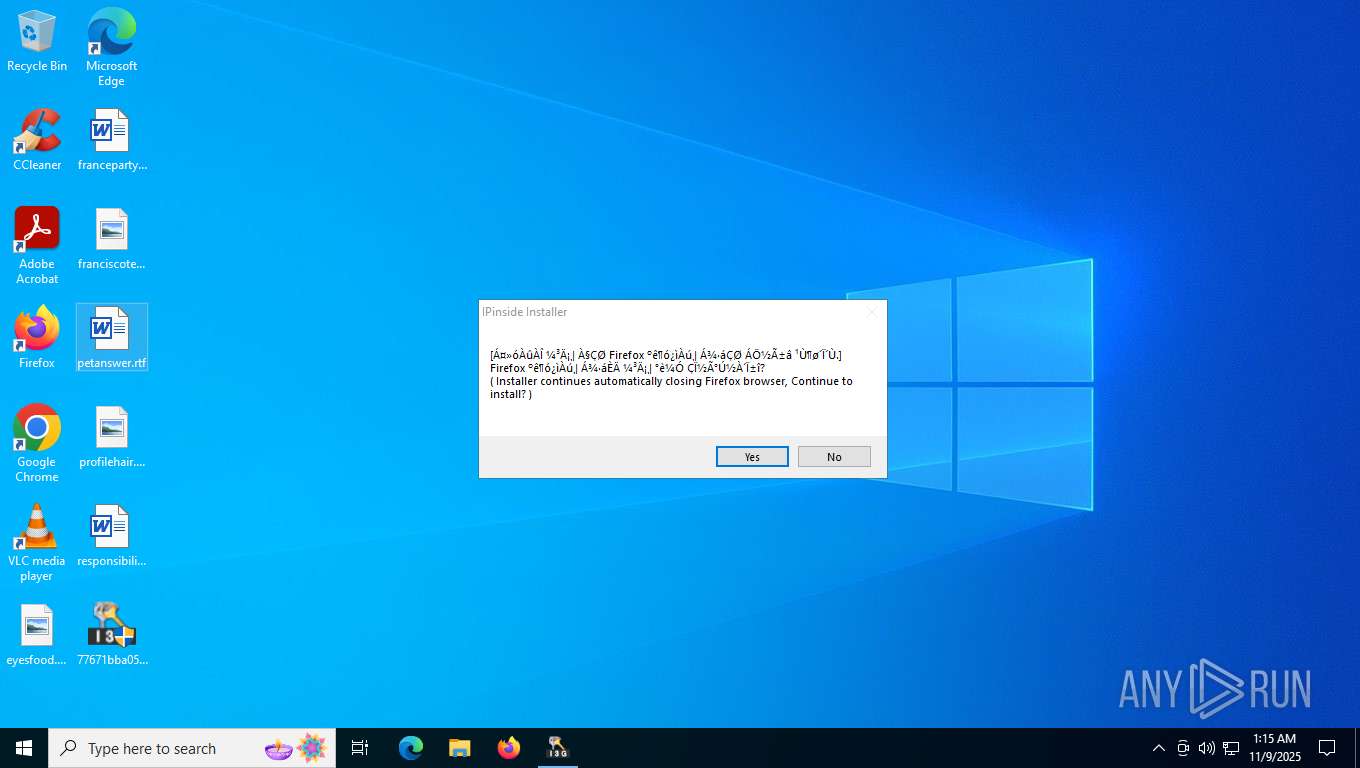
| Comments: | I3GManager LWS Module Installer |
| CompanyName: | Interezen. Co., Ltd. |
| FileDescription: | I3GManager LWS Module Installer |
| FileVersion: | 3.0.0.24 |
| InternalName: | I3GManager |
| LegalCopyright: | Interezen. Copyright ⓒ 2009 ~ |
| OriginalFileName: | I3GSvcManager.exe |
| ProductName: | I3GManager |
| ProductVersion: | 3.0.0.24 |
Total processes
181
Monitored processes
35
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\IPinside_LWS\openssl.exe" x509 -req -in "C:\Program Files (x86)\IPinside_LWS\InterezenSSLServer.csr" -CA "C:\Program Files (x86)\IPinside_LWS\interezen-rootca.crt" -CAkey "C:\Program Files (x86)\IPinside_LWS\interezen-rootca.key" -CAcreateserial -out "C:\Program Files (x86)\IPinside_LWS\interezen.opt" -sha256 -extfile "C:\Program Files (x86)\IPinside_LWS\InterezenSSLServerCert.ext" -days 7300 | C:\Program Files (x86)\IPinside_LWS\openssl.exe | — | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | |||||||||||
User: admin Company: The OpenSSL Project, https://www.openssl.org/ Integrity Level: HIGH Description: OpenSSL application Exit code: 0 Version: 3.0.7 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\IPinside_LWS\certmgr.exe" /del /c /sha1 7A852FB3EC54541E4378F3B18DC96BA2FAE08065 /s /r localMachine Root | C:\Program Files (x86)\IPinside_LWS\certmgr.exe | — | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 5.131.1863.1 Modules
| |||||||||||||||
| 2056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2124 | "C:\Program Files (x86)\IPinside_LWS\certmgr.exe" /del /c /sha1 A9A41C09E8B58DD59C97B6F0524BB48D9A15BD4F /s /r localMachine Root | C:\Program Files (x86)\IPinside_LWS\certmgr.exe | — | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 5.131.1863.1 Modules
| |||||||||||||||
| 2780 | "C:\Program Files (x86)\IPinside_LWS\I3GProc.exe" | C:\Program Files (x86)\IPinside_LWS\I3GProc.exe | — | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | |||||||||||
User: admin Company: Interezen. Co., Ltd. Integrity Level: HIGH Description: Interezen Process Version: 3.0.0.24 Modules
| |||||||||||||||
| 3032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3320 | "C:\Program Files (x86)\IPinside_LWS\certfr\certutil.exe" -D -n "Interezen CA" -d "sql:C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release" | C:\Program Files (x86)\IPinside_LWS\certfr\certutil.exe | — | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 255 Modules
| |||||||||||||||
| 4444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | openssl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 638
Read events
27 562
Write events
74
Delete events
2
Modification events
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | ipinside-mgr |
Value: | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\IPinside LWS Agent |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\IPinside_LWS\I3GSvcManager.exe | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\IPinside LWS Agent |
| Operation: | write | Name: | DisplayName |
Value: IPinside LWS Agent | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\IPinside LWS Agent |
| Operation: | write | Name: | DisplayVersion |
Value: 3.0.0.24 | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\IPinside LWS Agent |
| Operation: | write | Name: | Publisher |
Value: interezen | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\IPinside LWS Agent |
| Operation: | write | Name: | UninstallPath |
Value: C:\Program Files (x86)\IPinside_LWS\I3GSvcManager.exe | |||
| (PID) Process: | (7624) 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\IPinside LWS Agent |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\IPinside_LWS\I3GSvcManager.exe /uninstall | |||
Executable files
67
Suspicious files
5
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Users\admin\AppData\LocalLow\IPinside\I3GSetupLog.log | text | |
MD5:6AAD1682859519044B6A3A5257332A1E | SHA256:71A53077552BFC0F46390183845ECE1B14DCBEB848F552A575E14000F4FC71B9 | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:3F224766FE9B090333FDB43D5A22F9EA | SHA256:AE5E73416EB64BC18249ACE99F6847024ECEEA7CE9C343696C84196460F3A357 | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:405BB6A7CD56CBF5276C3A8DC631963D | SHA256:F654E56C4299F507BC34271B6BAA29290FD4919B853E17D7470596CAD779F063 | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:E205DE17A85B0C3352A6857EF9B3C6DD | SHA256:29B23370474BE0C459CC47863603167CC7191F58318BD29877225FCBF2454215 | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:79EE4A2FCBE24E9A65106DE834CCDA4A | SHA256:9F7BDA59FAAFC8A455F98397A63A7F7D114EFC4E8A41808C791256EBF33C7613 | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files\Common Files\System\symsrv.dll | executable | |
MD5:7574CF2C64F35161AB1292E2F532AABF | SHA256:DE055A89DE246E629A8694BDE18AF2B1605E4B9B493C7E4AEF669DD67ACF5085 | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:9A4FC3727AAF02C3285B47DF5EE56244 | SHA256:891CCFEB349116283326262C27B8894B43CDC89B8AFD5BA7D21B891814A68075 | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-memory-l1-1-0.dll | executable | |
MD5:536F07C04C316AAC61AB64A492ED9191 | SHA256:50BF87DA10AE3F442C457E42D6666993B0FCA7C5D4DF521E8CD0959995FBCDDC | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:F4604E259459F5A0D5BE6914A6D4C5FB | SHA256:BCE066193FEB60B08EDF4CBEB490AAAA5DFFEB8A63A720CADF948748A9AF4B8F | |||
| 7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | C:\Program Files (x86)\IPinside_LWS\api-ms-win-core-localization-l1-2-0.dll | executable | |
MD5:23BD405A6CFD1E38C74C5150EEC28D0A | SHA256:A7FA48DE6C06666B80184AFEE7E544C258E0FB11399AB3FE47D4E74667779F41 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5164 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | GET | 200 | 76.223.54.146:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | GET | — | 76.223.54.146:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
— | — | POST | — | 4.154.209.85:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | — | unknown |
— | — | POST | 500 | 4.154.209.85:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2972 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5164 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2972 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5164 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5524 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | 76.223.54.146:80 | www.aieov.com | AMAZON-02 | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
5isohu.com |
| whitelisted |
www.aieov.com |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
7624 | 77671bba05e63085613a299f07d6ab05503f558f844fe534fd456454a066f087.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |