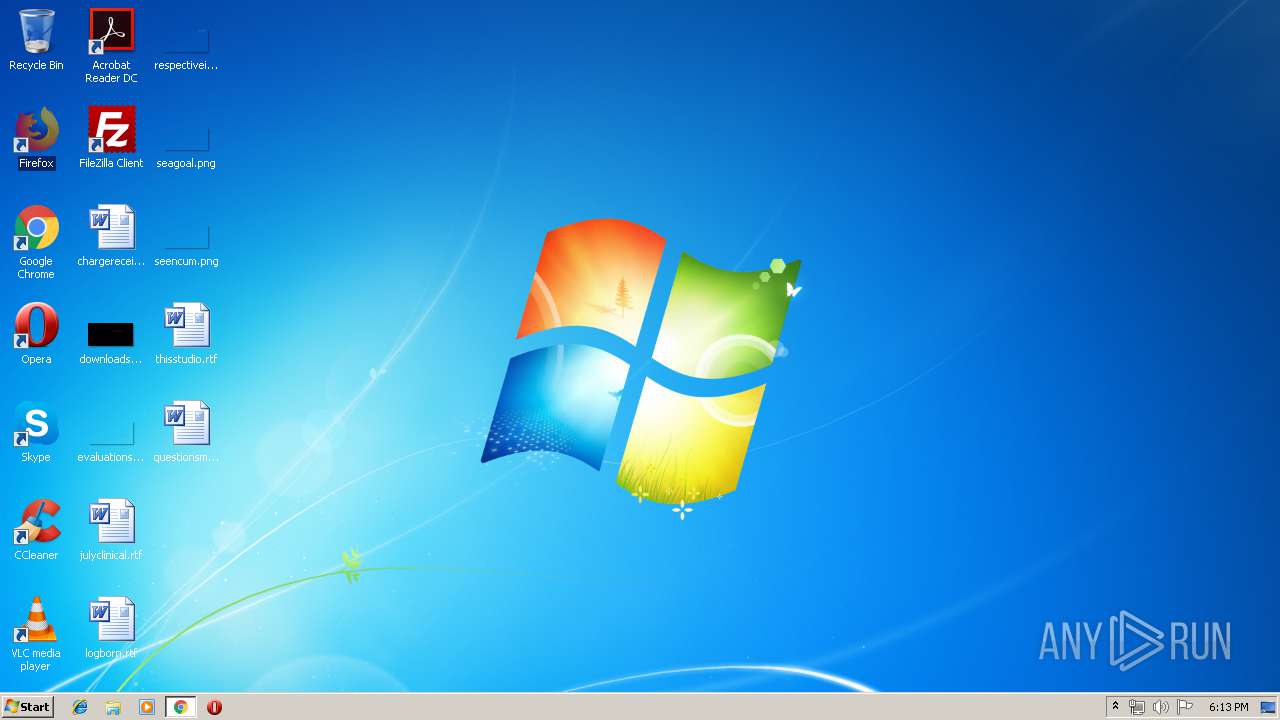
| URL: | http://lerloi.tk/ |
| Full analysis: | https://app.any.run/tasks/34a4274a-3583-4600-9d25-d6923ed8f308 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 17:13:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FD159A48BC26AA4EC0C8727AF782A76D |
| SHA1: | FC62AB21FA832F3C33865AD80FBE6CF7A5291250 |
| SHA256: | 7757352A3A7680DAFB896C06E95BA1BD27EA378479D88400A3AF3A70F0267E04 |
| SSDEEP: | 3:N1KSAl:CSa |
MALICIOUS
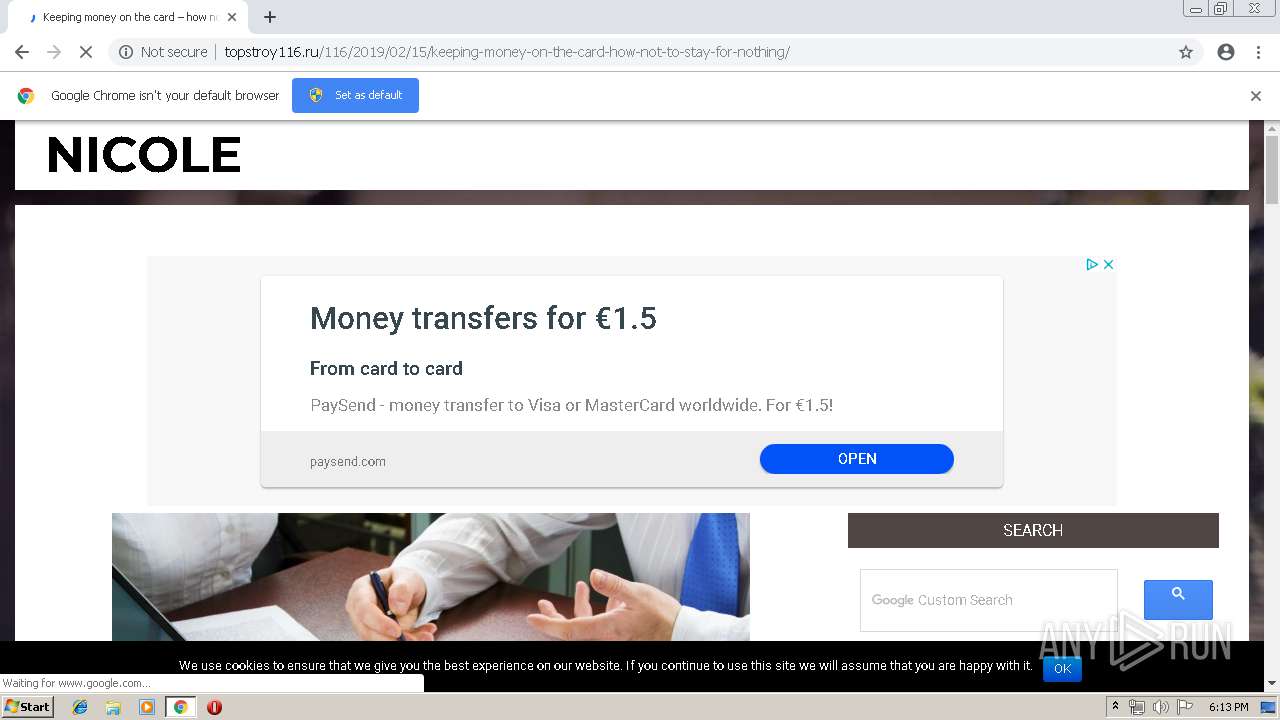
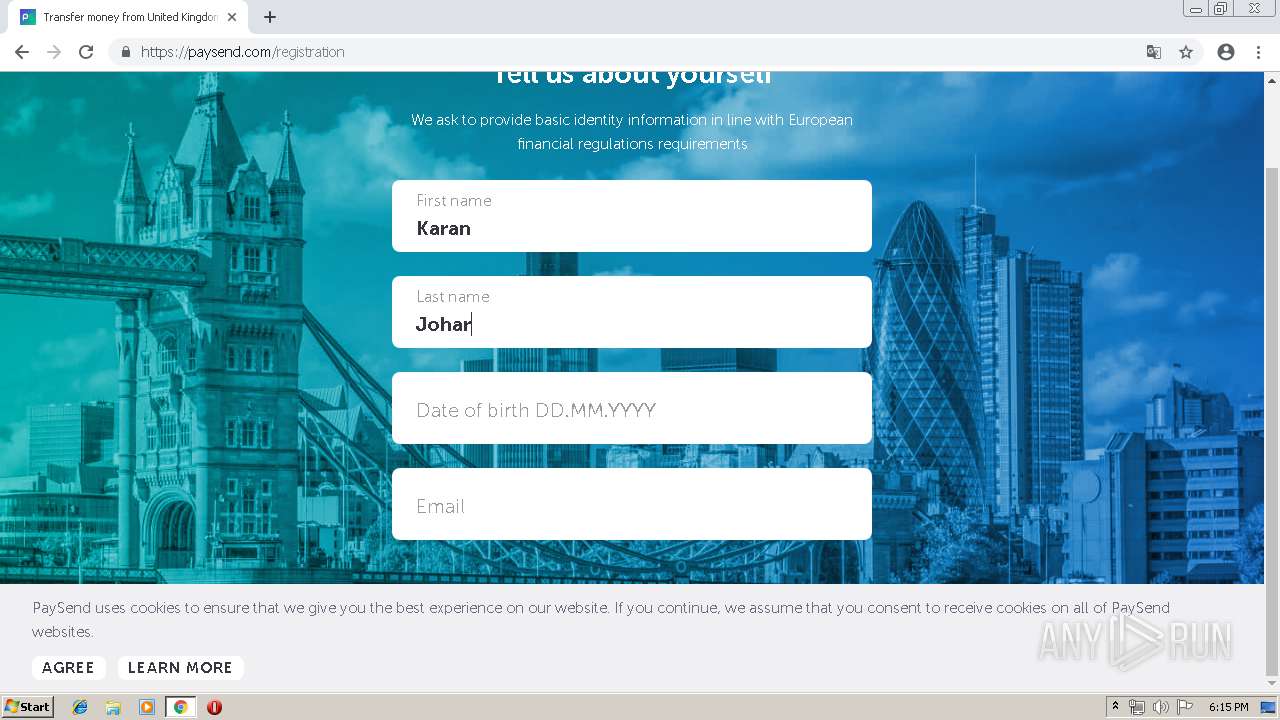
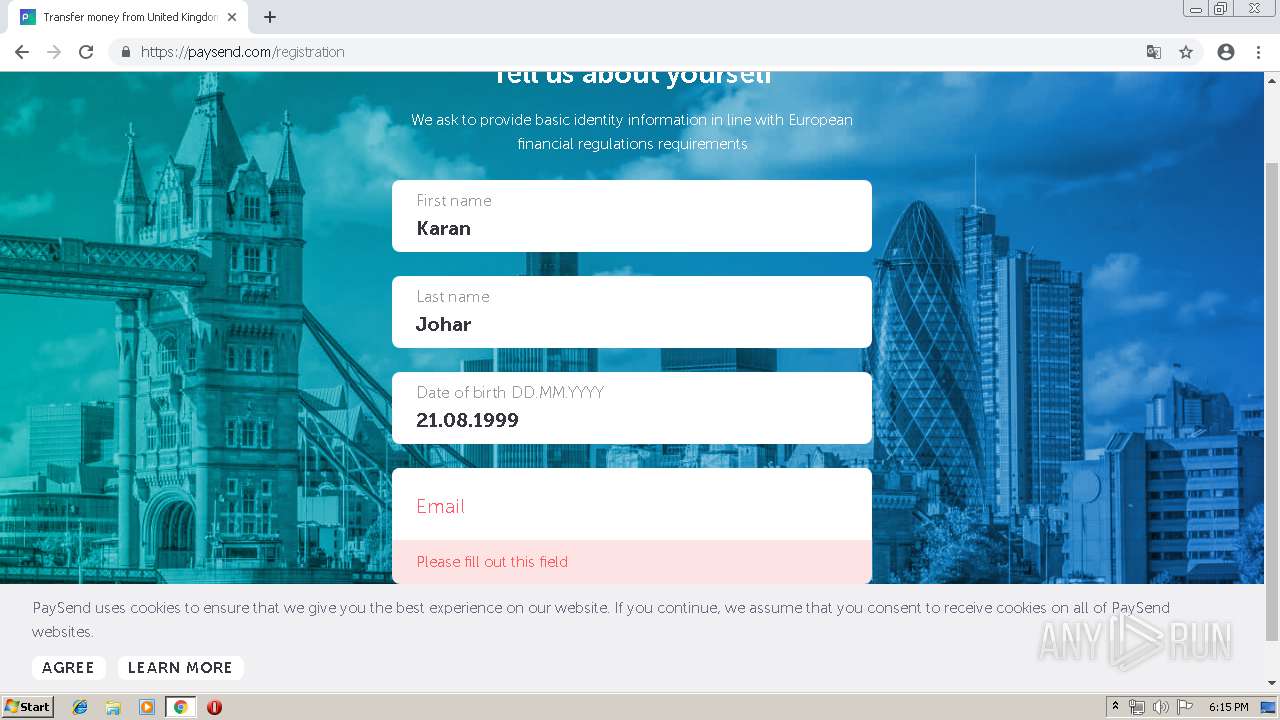
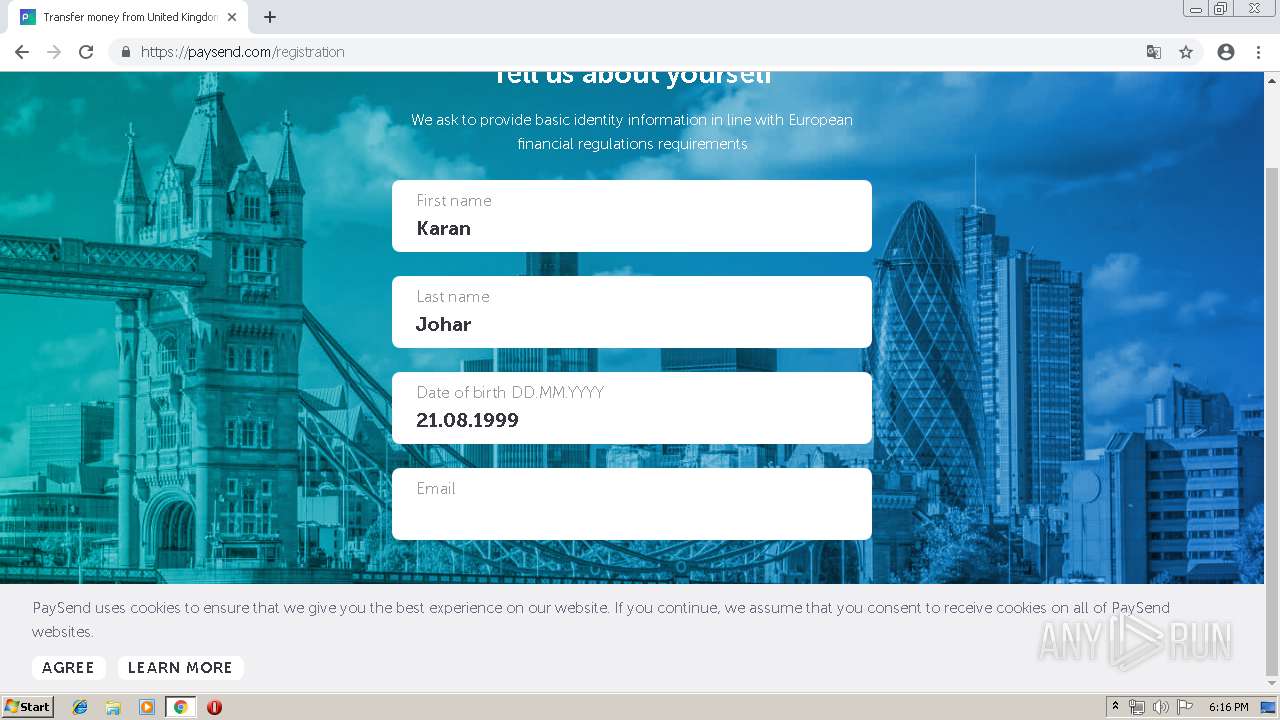
TECHSUPPORT was detected
- chrome.exe (PID: 2212)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2504)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2212)
Application launched itself
- chrome.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
25
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa10f18,0x6fa10f28,0x6fa10f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15814453535319503171 --mojo-platform-channel-handle=2732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2760 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15630622693725612843 --mojo-platform-channel-handle=3780 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9206507216376630344 --mojo-platform-channel-handle=2528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12816802753125320093 --mojo-platform-channel-handle=2696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4462502945150576442 --mojo-platform-channel-handle=2476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --service-pipe-token=2833185701234255491 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2833185701234255491 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9978436389058119908 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9978436389058119908 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=56522667435286337 --mojo-platform-channel-handle=1476 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
589
Read events
481
Write events
103
Delete events
5
Modification events
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2504-13199735612303500 |
Value: 259 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2504-13199735612303500 |
Value: 259 | |||
Executable files
0
Suspicious files
124
Text files
216
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\906d55dc-dfa3-4abd-8541-c3a1fefb6ff6.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
74
DNS requests
38
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
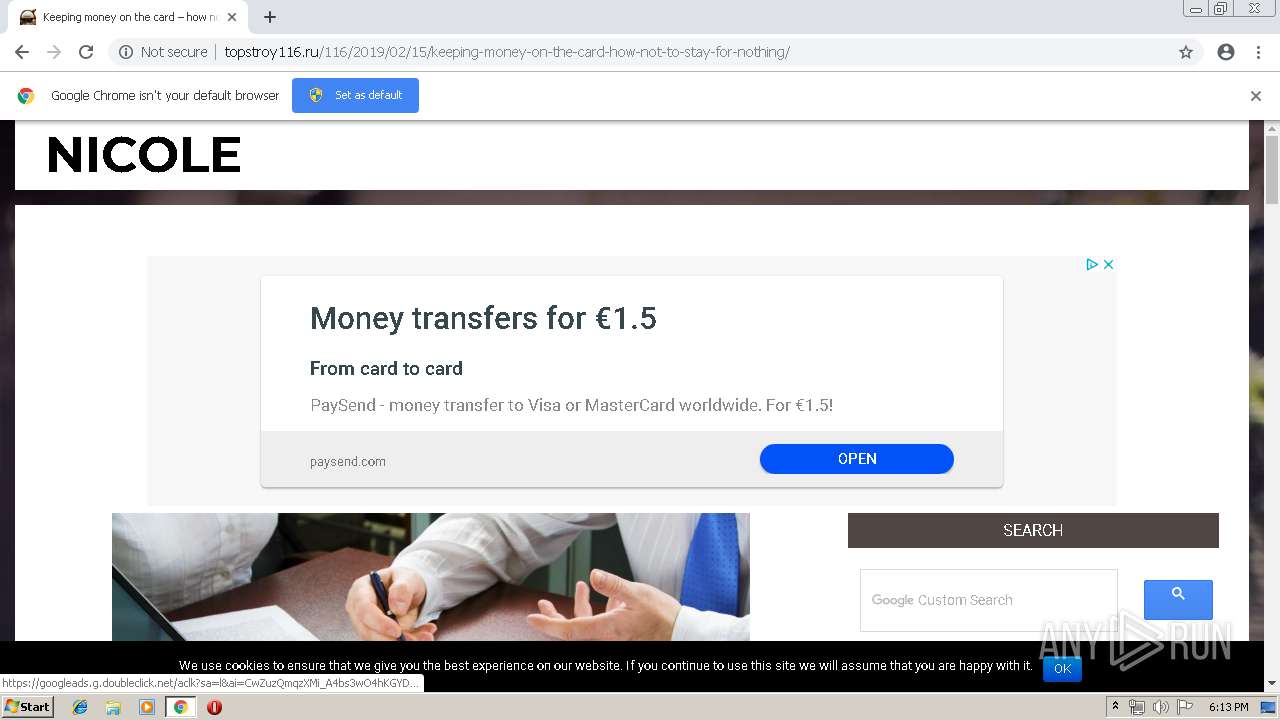
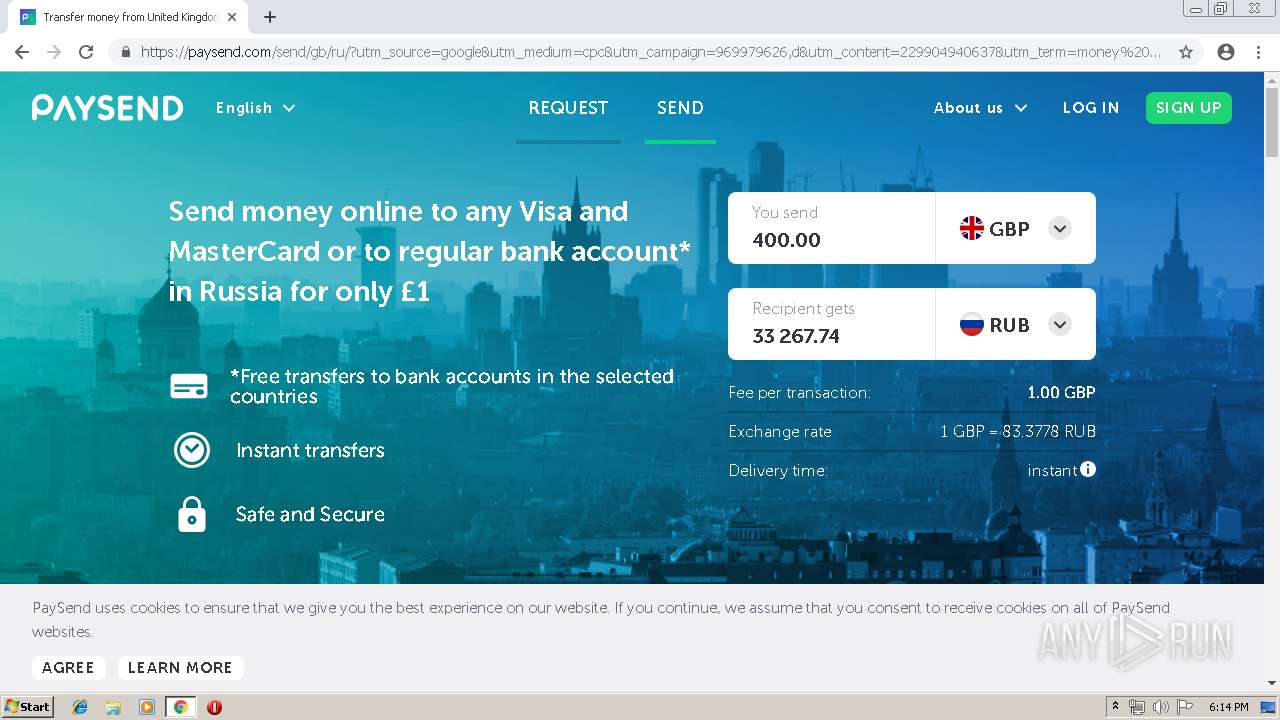
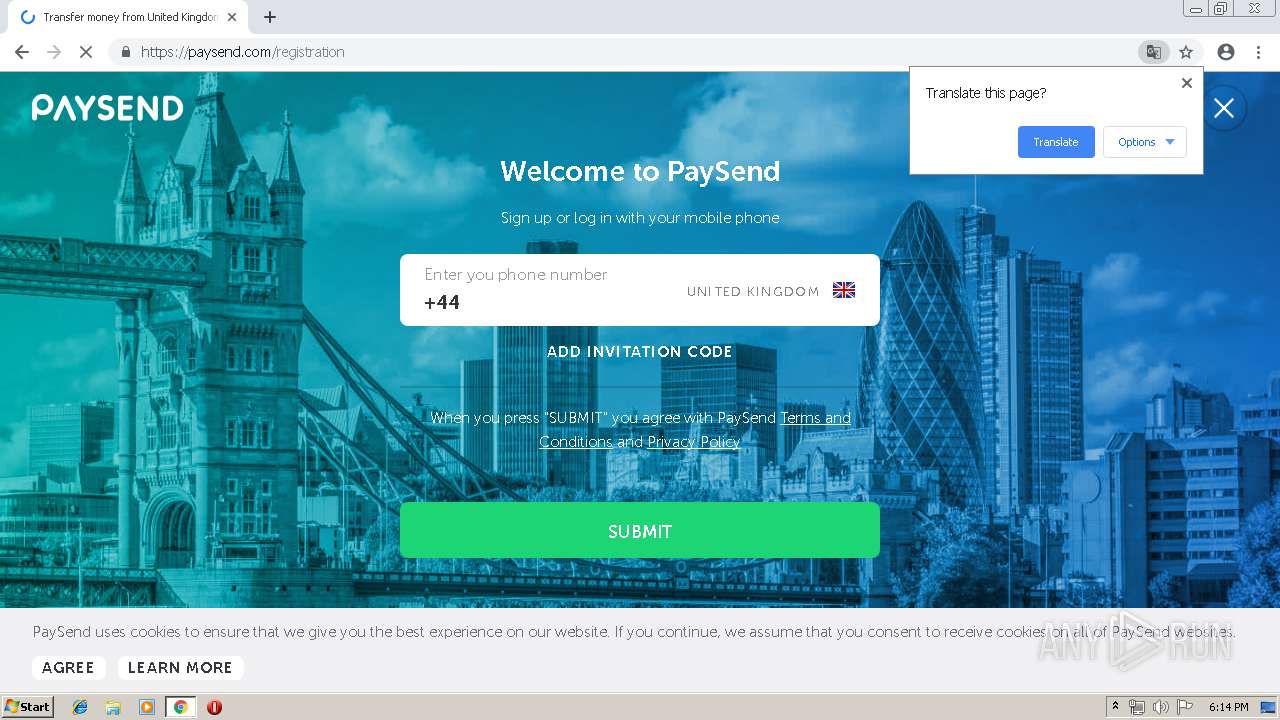
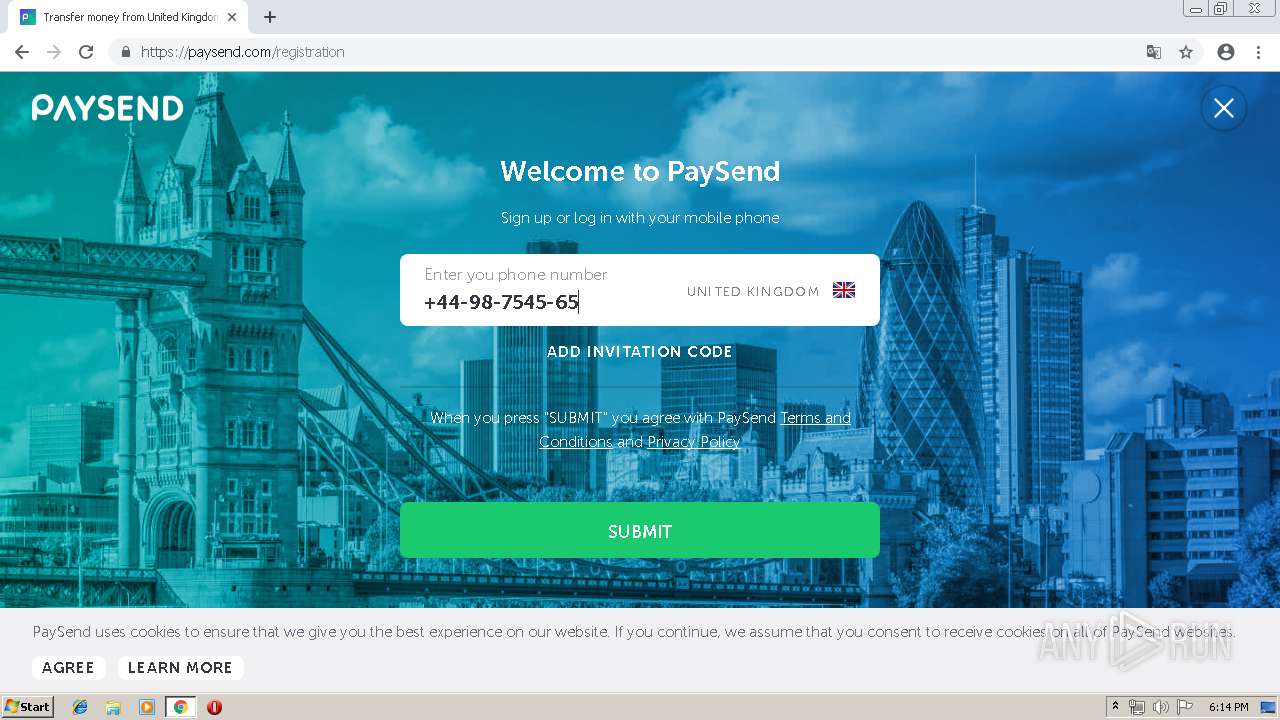
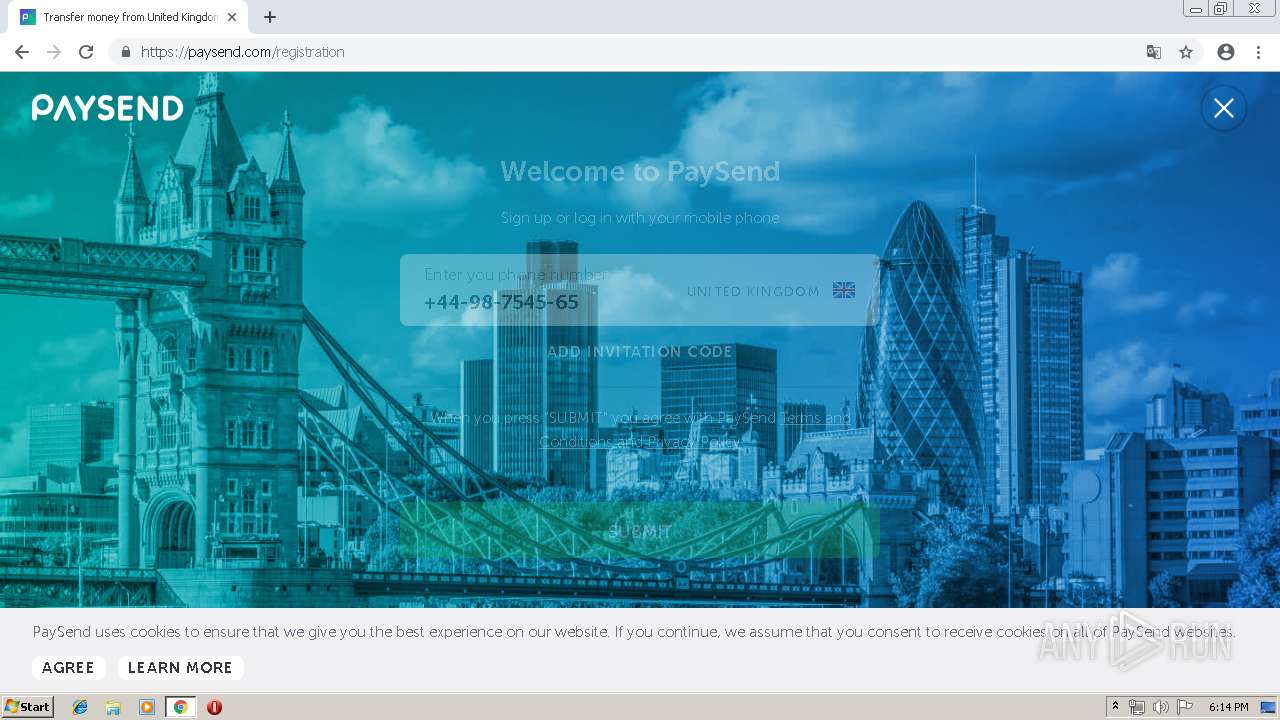
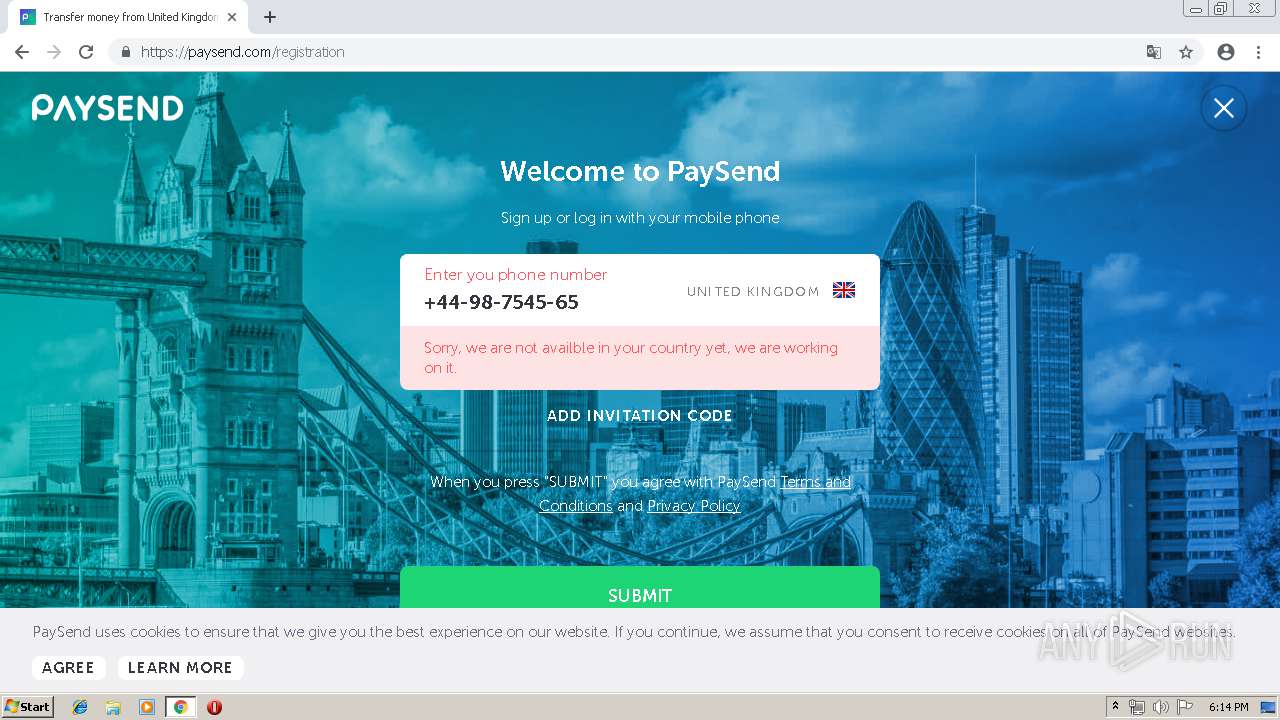
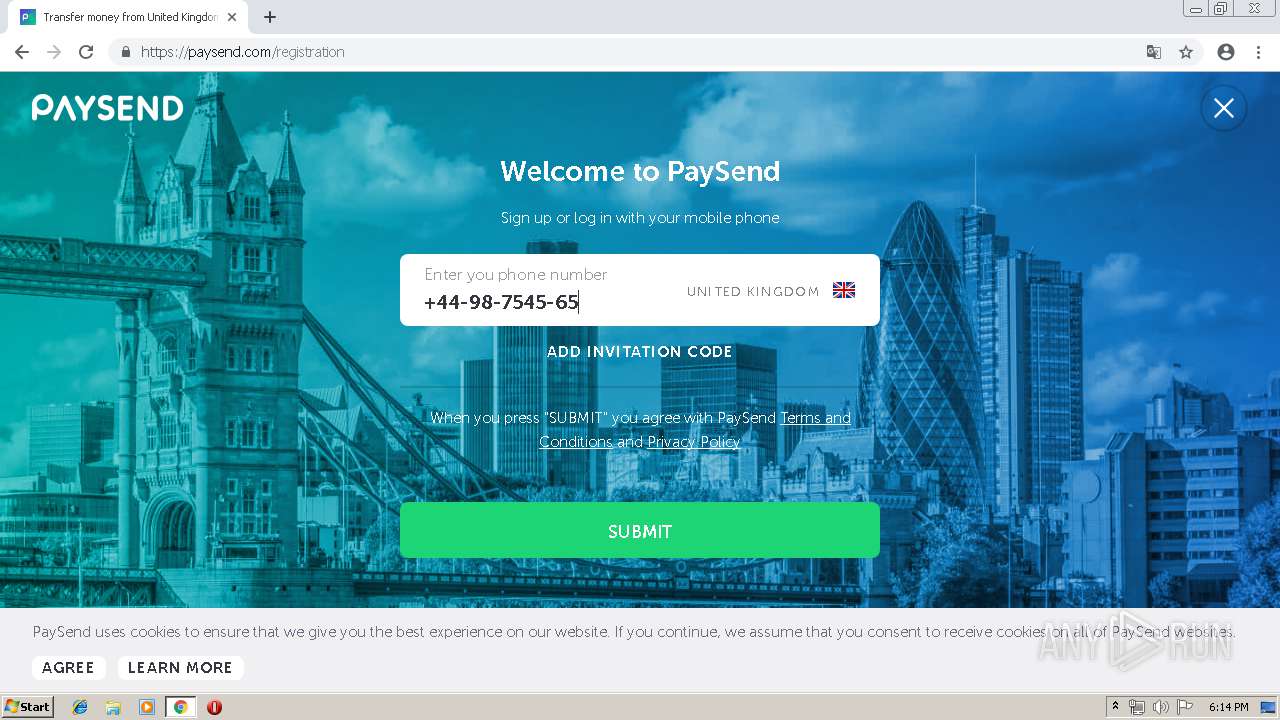
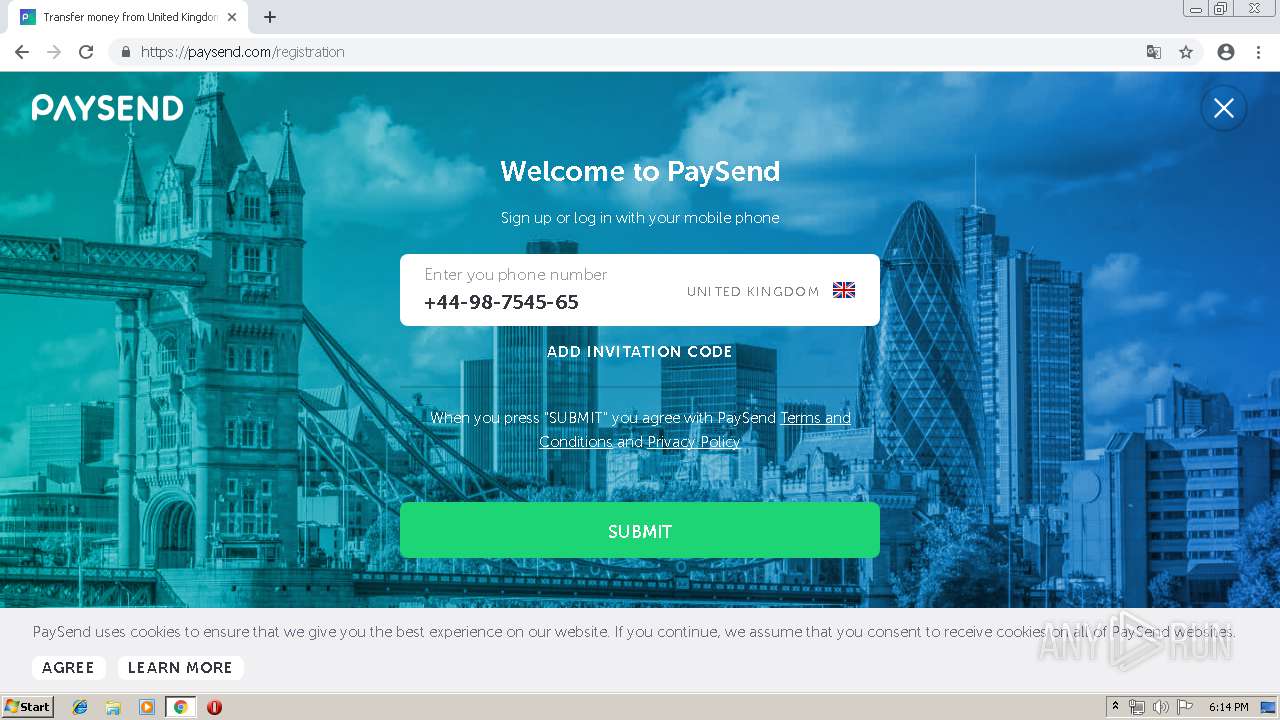
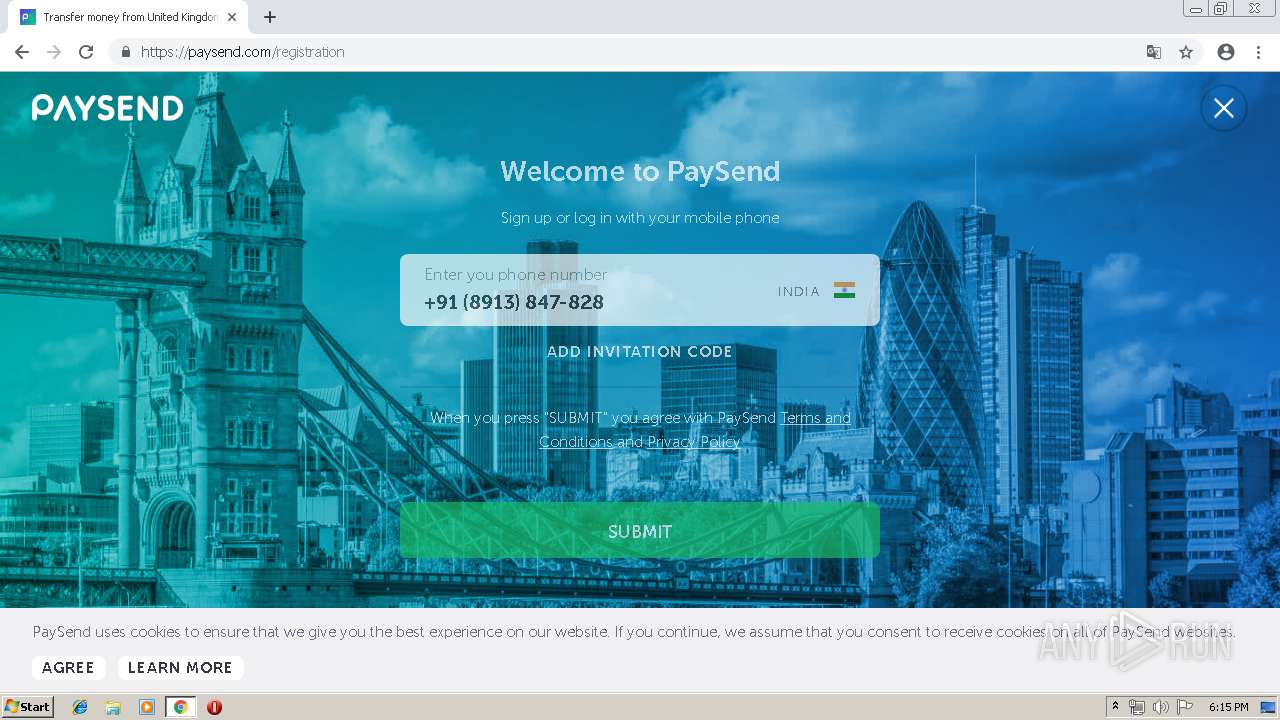
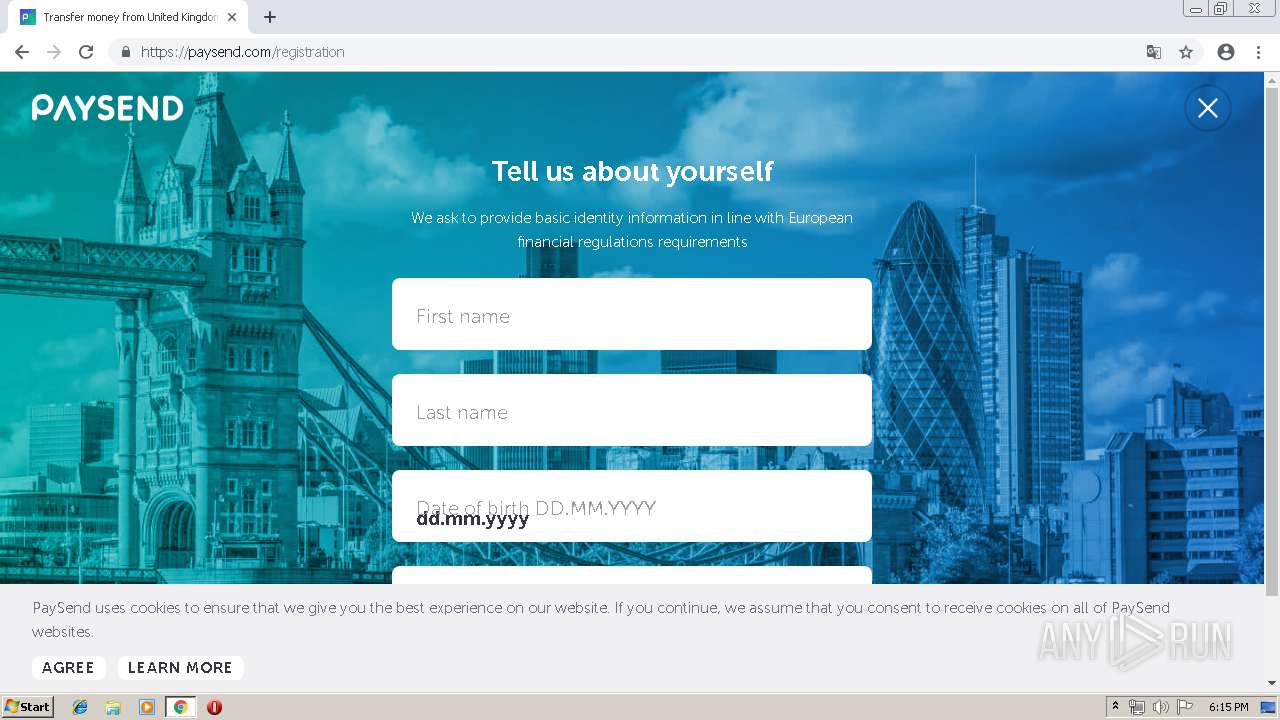
2212 | chrome.exe | GET | — | 37.230.116.105:80 | http://lerloi.tk/ | RU | — | — | suspicious |
2212 | chrome.exe | GET | 200 | 104.24.105.44:80 | http://topstroy116.ru/116/wp-content/uploads/2019/02/glavnye-oshibki-malogo-biznesa-768x512.jpg | US | image | 68.2 Kb | shared |
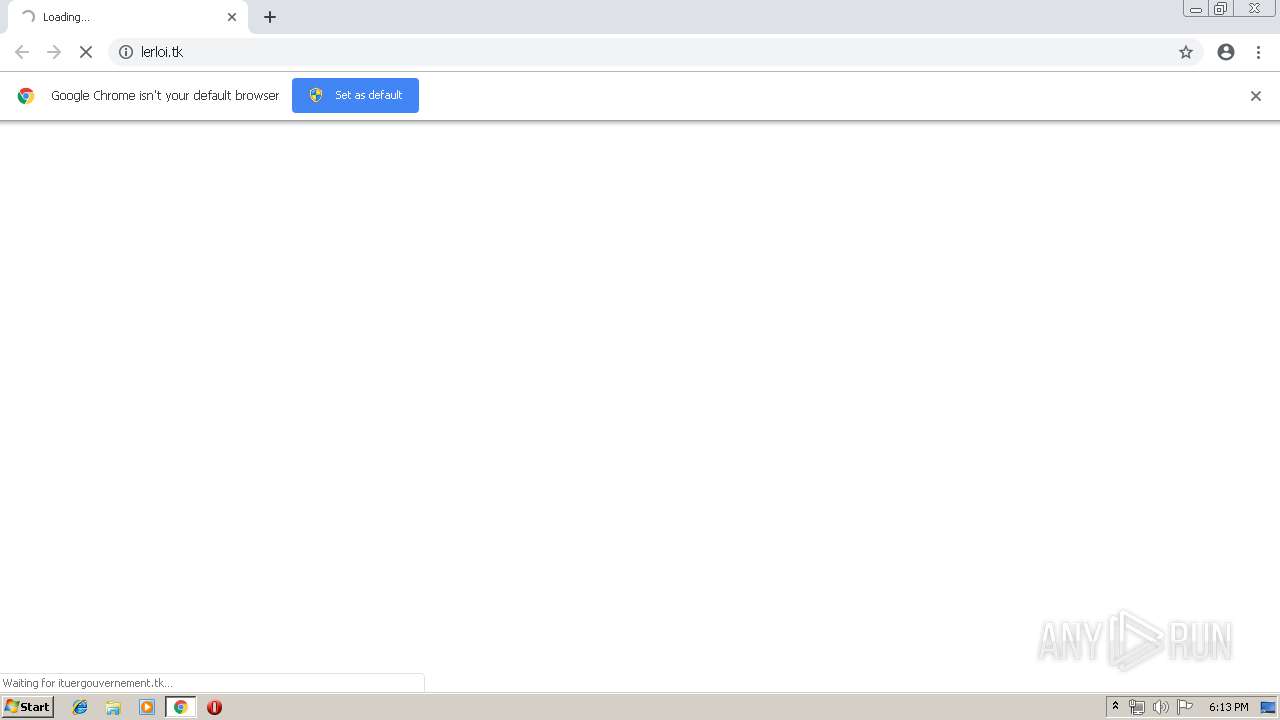
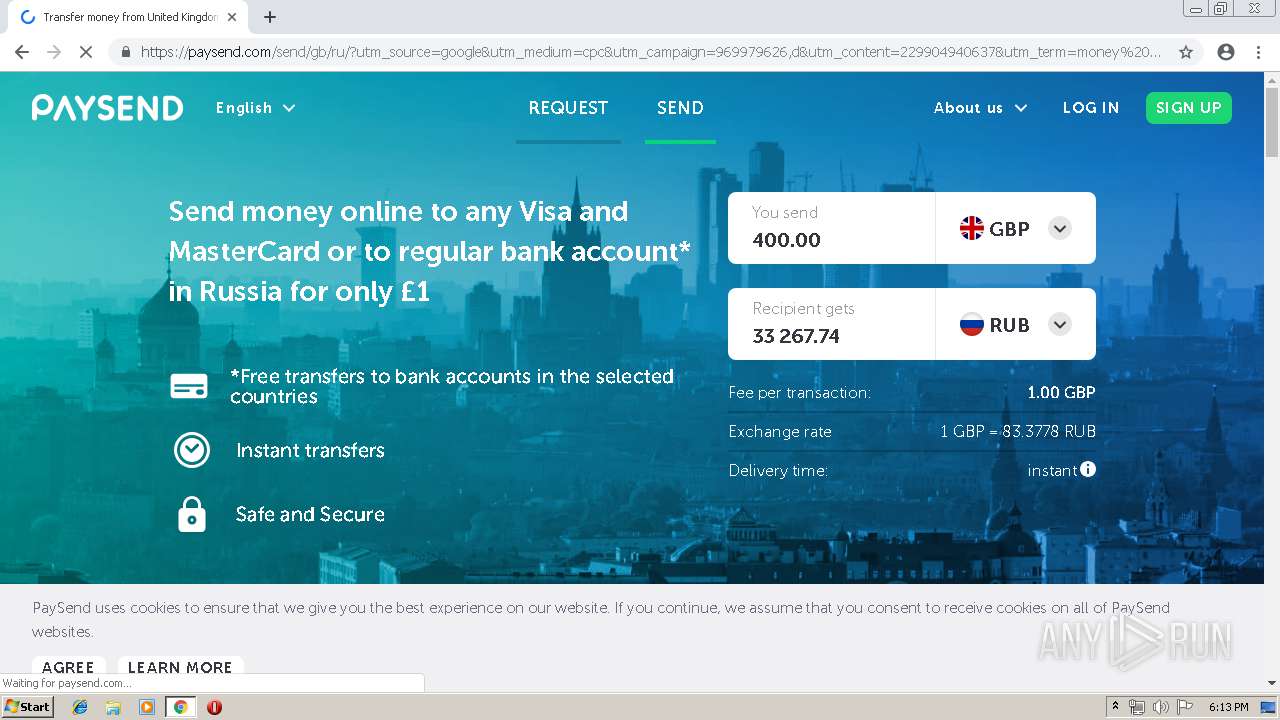
2212 | chrome.exe | GET | 200 | 37.230.116.105:80 | http://ituergouvernement.tk/index/?tS3McD | RU | html | 393 b | suspicious |
2212 | chrome.exe | POST | 200 | 104.24.105.44:80 | http://topstroy116.ru/116/1166top/ | US | html | 229 b | shared |
2212 | chrome.exe | POST | 200 | 104.24.105.44:80 | http://topstroy116.ru/116/2019/02/15/keeping-money-on-the-card-how-not-to-stay-for-nothing/ | US | html | 9.10 Kb | shared |
2212 | chrome.exe | GET | 200 | 104.24.105.44:80 | http://topstroy116.ru/116/wp-content/themes/neux/style.css?ver=2.7.3 | US | text | 15.8 Kb | shared |
2212 | chrome.exe | GET | 200 | 172.217.18.10:80 | http://fonts.googleapis.com/css?family=Roboto%3A300%2C400%2C400i%2C500%2C600%2C700%2C700i%2C800%7CComfortaa%3A400%2C700%7CMontserrat%3A400%2C400i%2C700%2C700i&subset=latin | US | text | 1.26 Kb | whitelisted |
2212 | chrome.exe | GET | 200 | 216.58.207.66:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 31.1 Kb | whitelisted |
2212 | chrome.exe | GET | 200 | 104.24.105.44:80 | http://topstroy116.ru/116/wp-includes/js/wp-emoji-release.min.js?ver=5.1.1 | US | text | 4.29 Kb | shared |
2212 | chrome.exe | GET | 404 | 37.230.116.105:80 | http://ituergouvernement.tk/favicon.ico | RU | html | 571 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2212 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 37.230.116.105:80 | lerloi.tk | JSC ISPsystem | RU | suspicious |
2212 | chrome.exe | 104.24.105.44:80 | topstroy116.ru | Cloudflare Inc | US | shared |
2212 | chrome.exe | 172.217.18.10:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 216.58.207.66:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.21.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 216.58.207.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.22.98:443 | adservice.google.es | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.22.34:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lerloi.tk |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ituergouvernement.tk |
| suspicious |
topstroy116.ru |
| unknown |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s.w.org |
| whitelisted |
adservice.google.es |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2212 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2212 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2212 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2212 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Tech Support Phone Scam Landing 2017-07-26 |