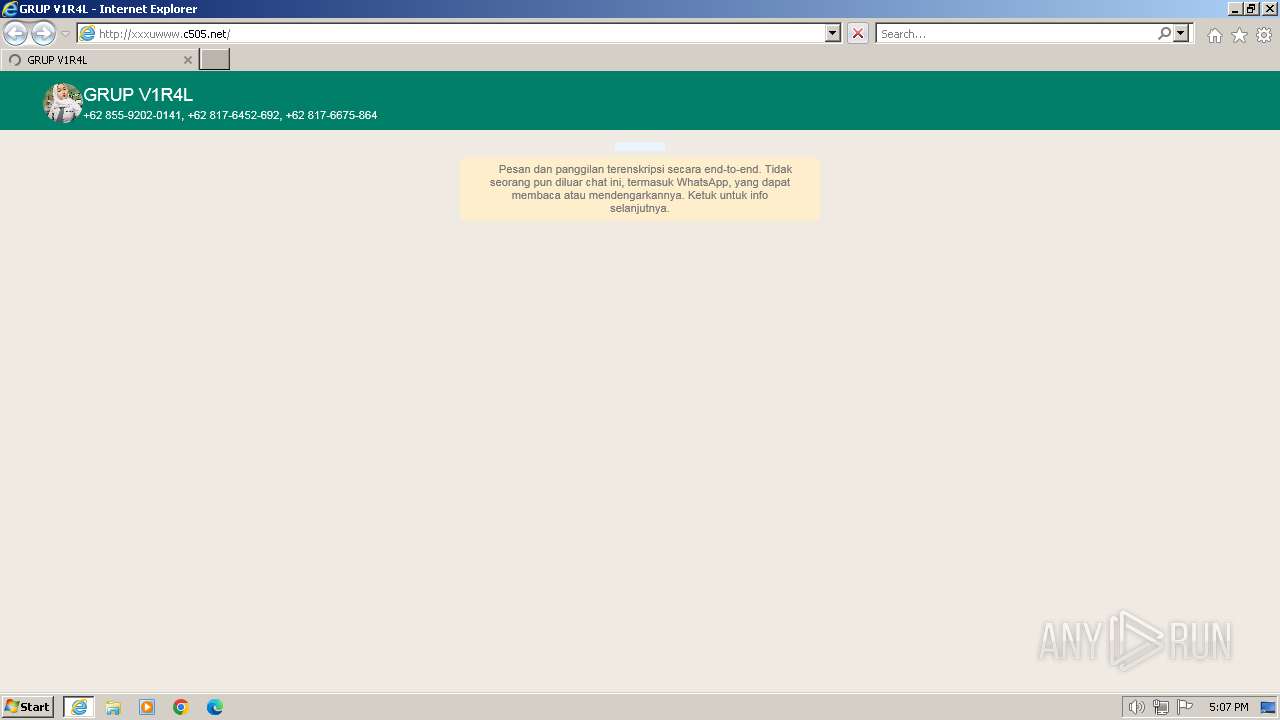
| URL: | http://xxxuwww.c505.net/ |
| Full analysis: | https://app.any.run/tasks/bec3b5b1-b879-4aa1-a42e-e4a252d0f572 |
| Verdict: | Malicious activity |
| Analysis date: | December 23, 2023, 17:07:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 00B3C4000C9F1B4726B6FBE23D705515 |
| SHA1: | D58EC9764FDF8F4336D55E977372A0491A5C4A74 |
| SHA256: | 7756452BC8E435C566D0E193258ACB67904B9CD71938B81C6BFF9EC676E4D19C |
| SSDEEP: | 3:N1KGddQSSJz:CGddHIz |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1492 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://xxxuwww.c505.net/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 375
Read events
20 305
Write events
68
Delete events
2
Modification events
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
50
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\3XG1DOXF.htm | html | |
MD5:7C0B88802F243A228B833E0053CCA0C2 | SHA256:C01E8A320A1F742B2964238CB8E13A848DBE63A719D6AC86605D4563635466F2 | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bagas[1].css | text | |
MD5:AE8F5EAC80C514B6CCFFCE75DE1D2D70 | SHA256:A9510C5B947EEDFA3D84FEF078A623EBB72CD26A8ACF9855A15521DFFC430D62 | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3B.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:C34ABF6557208BB2A2AAB2336217D006 | SHA256:1618ACC7AB318F4563C8919F73BB7F053D523F28FC31ACABDAA7645ABF8FA382 | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:BA919E04536E5E5F9761EC0EC65E82CC | SHA256:BE7E963483C7572DD07DF657D04B59FF55572C9595B19360F3F27C4A68110F59 | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:13FE4F617CD4B038E4093DE17EF5741C | SHA256:C1D48657089D5823E42433D43CD67E16D5F62CA87E594B25ADEFCF27EBBEB13A | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | der | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:4E0E8F5BB04ADFFEF570649DE85FB289 | SHA256:71610A1495C3545F61DC700F0A629E38CF6CB00A030CAA3FB46EDB05250ADA9B | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:AC76D6AE798898BF86EC657A103452A6 | SHA256:39E1FF9DC197150A00E3CCFDB7895A9A9C936B93B1217E047B76C3478DC75EA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
88
DNS requests
30
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1404 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://xxxuwww.c505.net/ | unknown | html | 3.86 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://xxxuwww.c505.net/bagas/bagas.css | unknown | compressed | 1.03 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://xxxuwww.c505.net/coreAlex/asaykjwdawldkha.css | unknown | compressed | 1.91 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?abd5acd1b79ce636 | unknown | compressed | 4.66 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b67bf06f0904ddf9 | unknown | compressed | 4.66 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c418ab72d5642389 | unknown | compressed | 4.66 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0c822da62e5e3988 | unknown | compressed | 4.66 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?11d6e8c45e20e052 | unknown | compressed | 4.66 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9bccf30d7241ea4f | unknown | compressed | 4.66 Kb | unknown |
1404 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c4089af522faeb39 | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1404 | iexplore.exe | 188.114.97.3:80 | xxxuwww.c505.net | CLOUDFLARENET | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1404 | iexplore.exe | 142.250.185.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
1404 | iexplore.exe | 104.18.40.68:443 | site-assets.fontawesome.com | CLOUDFLARENET | — | unknown |
1404 | iexplore.exe | 104.21.234.230:443 | rawcdn.githack.com | CLOUDFLARENET | — | unknown |
1404 | iexplore.exe | 162.19.58.160:443 | i.ibb.co | OVH SAS | FR | unknown |
1404 | iexplore.exe | 51.159.59.190:443 | g.top4top.io | Online S.a.s. | FR | unknown |
1404 | iexplore.exe | 162.19.61.80:443 | i.postimg.cc | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xxxuwww.c505.net |
| malicious |
site-assets.fontawesome.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
i.ibb.co |
| shared |
i.postimg.cc |
| whitelisted |
rawcdn.githack.com |
| whitelisted |
g.top4top.io |
| unknown |
bagasarya.xyz |
| unknown |
f.top4top.io |
| malicious |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Misc activity | AV INFO Observed DNS Request to Filesharing Service (top5top. io) |
1080 | svchost.exe | Misc activity | AV INFO Observed DNS Request to Filesharing Service (top5top. io) |
1404 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
1404 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
1404 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
1404 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
1404 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
1404 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
1404 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |