| File name: | s5(1).exe |
| Full analysis: | https://app.any.run/tasks/3ae96029-6a81-40f8-ad67-921c6afcc6f8 |
| Verdict: | No threats detected |
| Analysis date: | January 22, 2019, 16:31:58 |
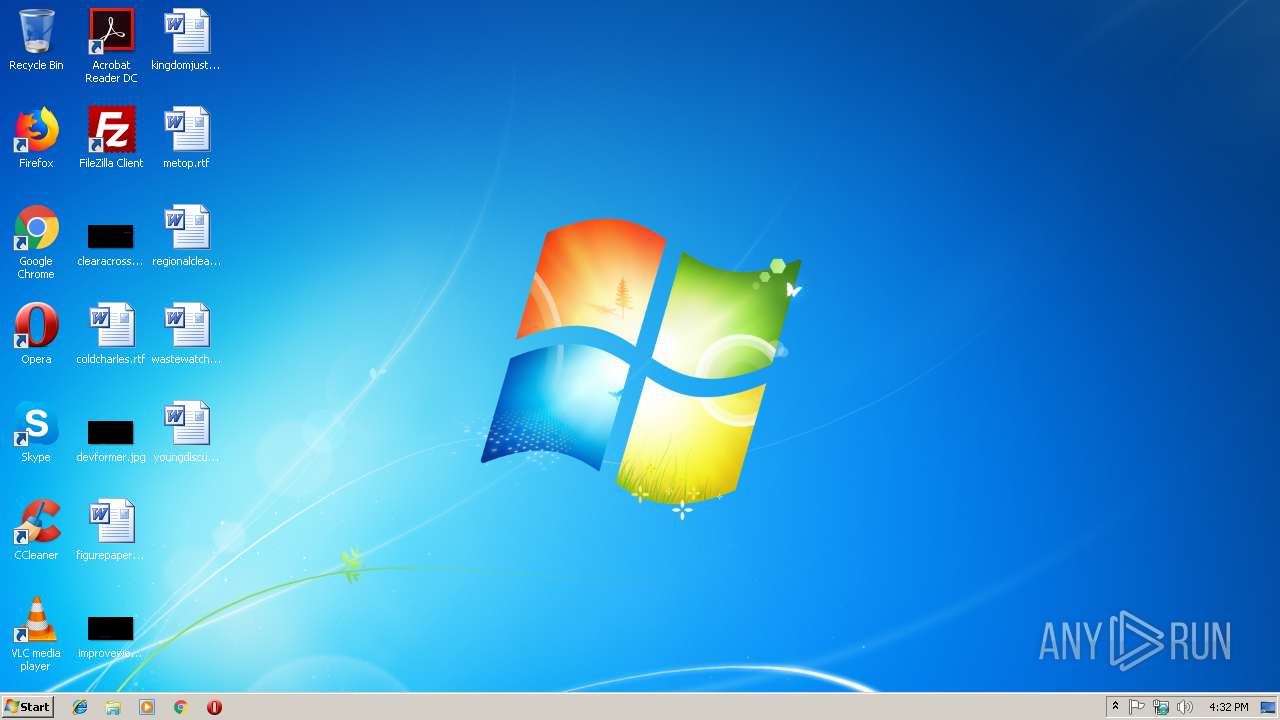
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9571D8E305446268A043C34B3B91DBD0 |
| SHA1: | 259B20B24CC878307FFA88E337F163310757AFE3 |
| SHA256: | 7755CE0CC13A4ABE3C222BCBDC203E720D4262D953686E6BE8B8813052E10E9D |
| SSDEEP: | 768:N54d6JA9IIy54d6JA9II1APNsa6w5Pk91sjWbAbLb8osV:M6aCS6aCZNs7qPk91sjdbLb8o |
MALICIOUS
Loads the Task Scheduler DLL interface
- s5(1).exe (PID: 2852)
SUSPICIOUS
Executable content was dropped or overwritten
- s5(1).exe (PID: 2852)
Creates files in the program directory
- s5(1).exe (PID: 2852)
Creates files in the Windows directory
- s5(1).exe (PID: 2852)
Connects to unusual port
- upmuisg.exe (PID: 2844)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:04:08 01:02:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 18944 |
| InitializedDataSize: | 33792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Apr-2015 23:02:24 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 07-Apr-2015 23:02:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x00004921 | 0x00004A00 | IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.1987 |
.ari | 0x00006000 | 0x00008368 | 0x00008400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.2269 |
Imports
advapi32.dll |
eappcfg.dll |
kernel32.dll |
nddeapi.dll |
resutils.dll |
shell32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
jaik | 1 | 0x000012F6 |
Total processes
33
Monitored processes
3
Malicious processes
0
Suspicious processes
0
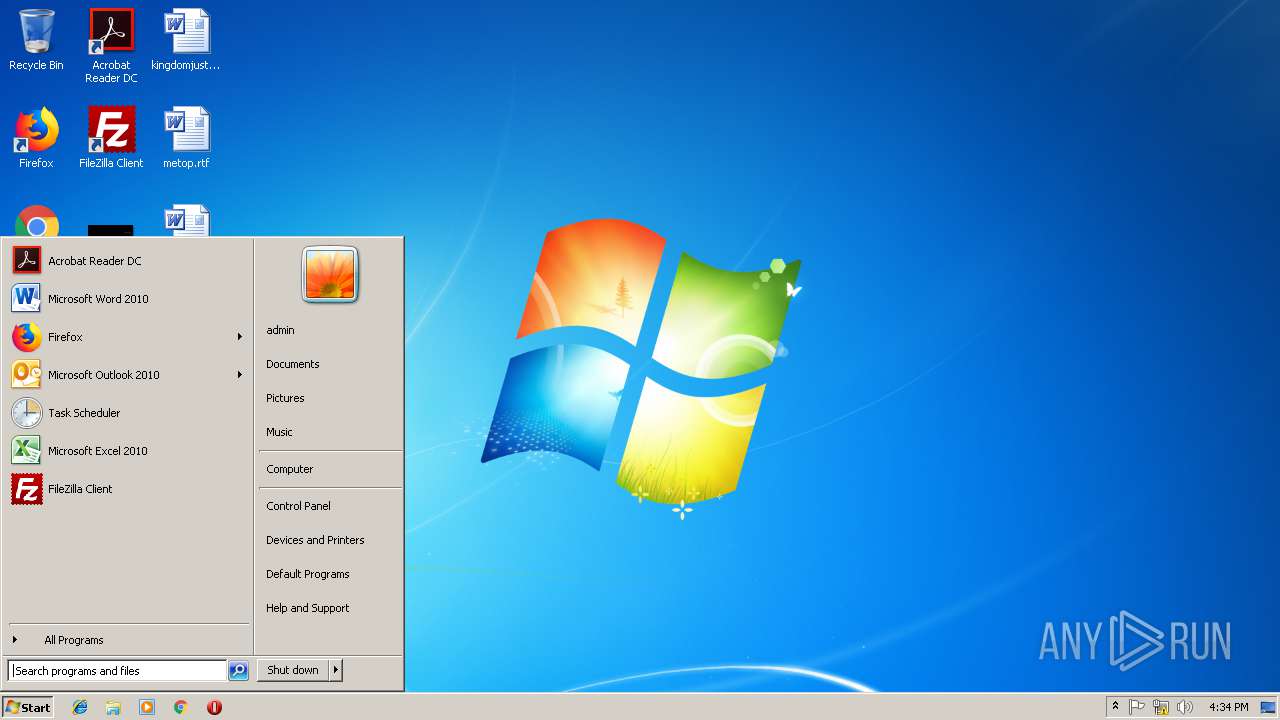
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2844 | C:\ProgramData\qehss\upmuisg.exe start2 | C:\ProgramData\qehss\upmuisg.exe | taskeng.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\s5(1).exe" | C:\Users\admin\AppData\Local\Temp\s5(1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3436 | C:\ProgramData\qehss\upmuisg.exe start2 | C:\ProgramData\qehss\upmuisg.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
9
Read events
9
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | s5(1).exe | C:\Windows\Tasks\corolina17.job | binary | |
MD5:— | SHA256:— | |||
| 2852 | s5(1).exe | C:\ProgramData\qehss\upmuisg.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | upmuisg.exe | 210.16.100.39:4000 | golgame.com | Psychz Networks | IN | unknown |
2844 | upmuisg.exe | 210.16.100.39:8458 | golgame.com | Psychz Networks | IN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
golgame.com |
| unknown |