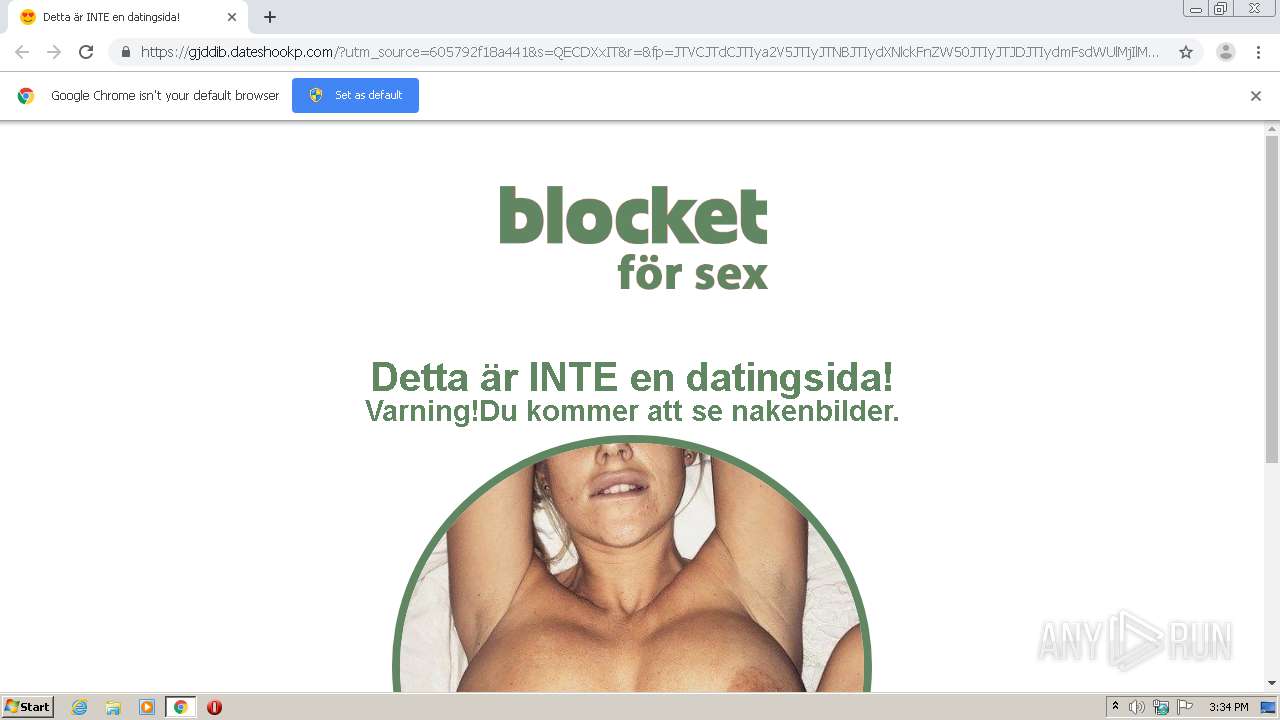
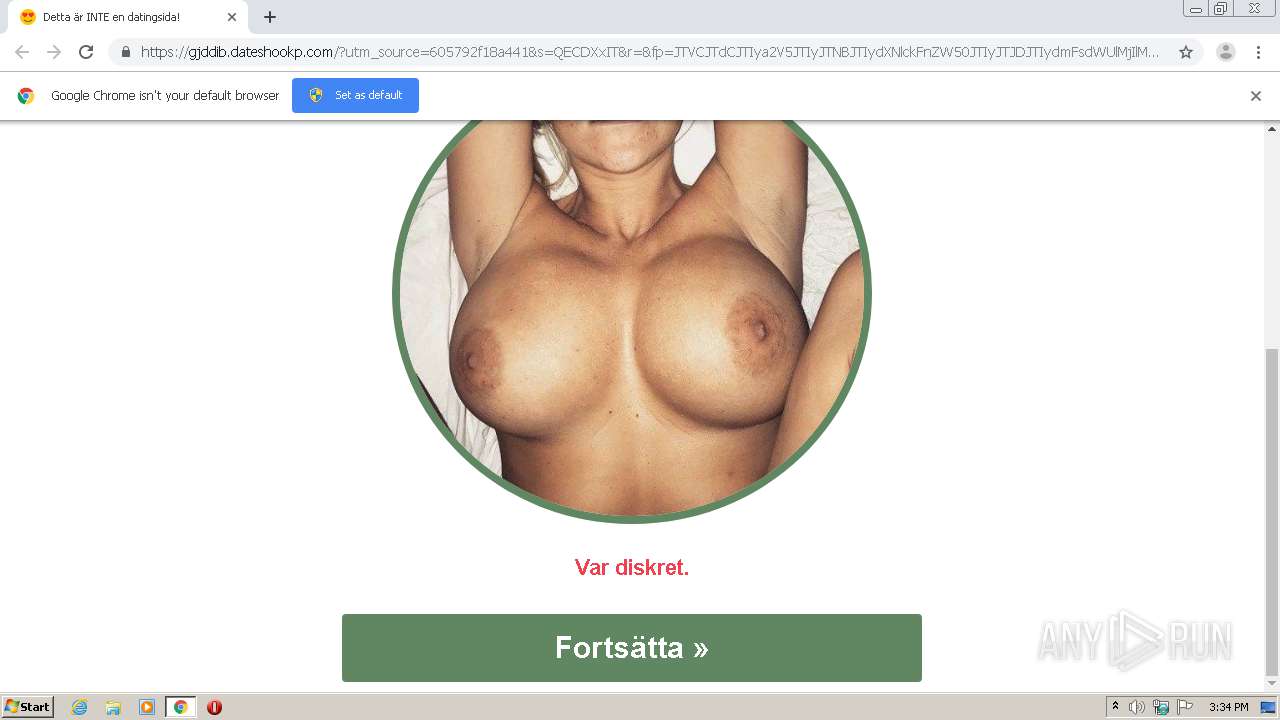
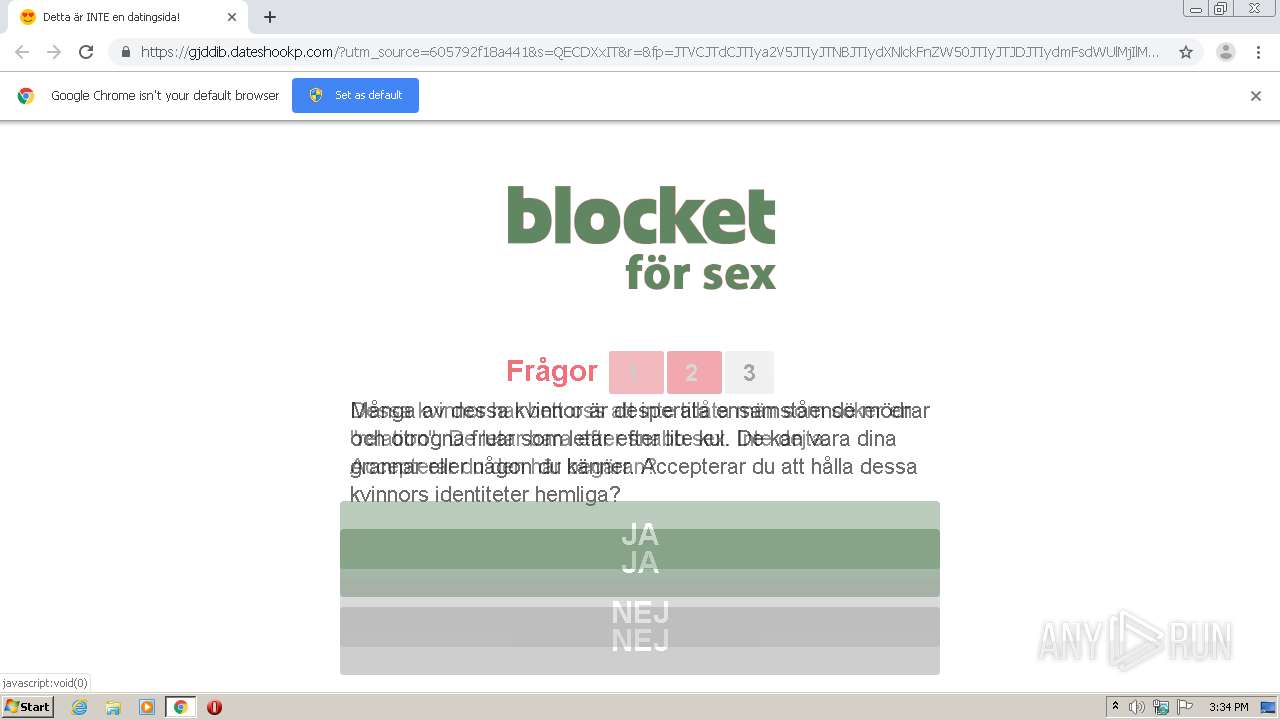
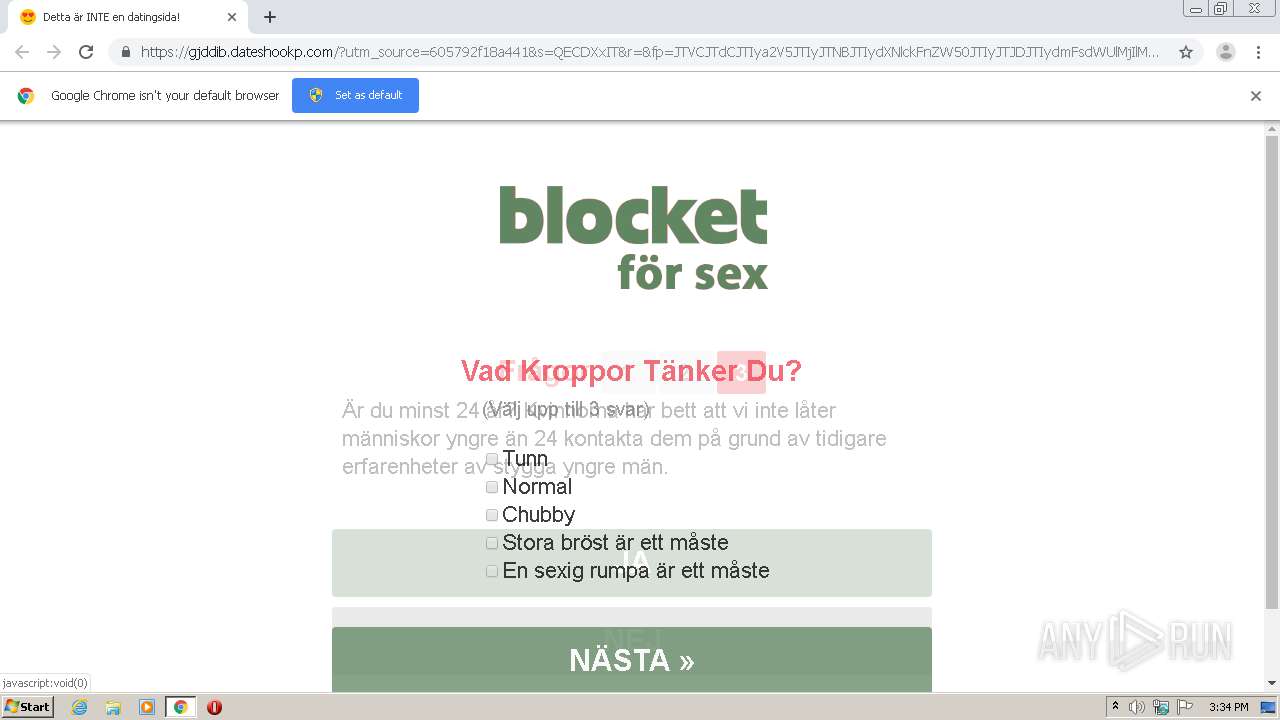
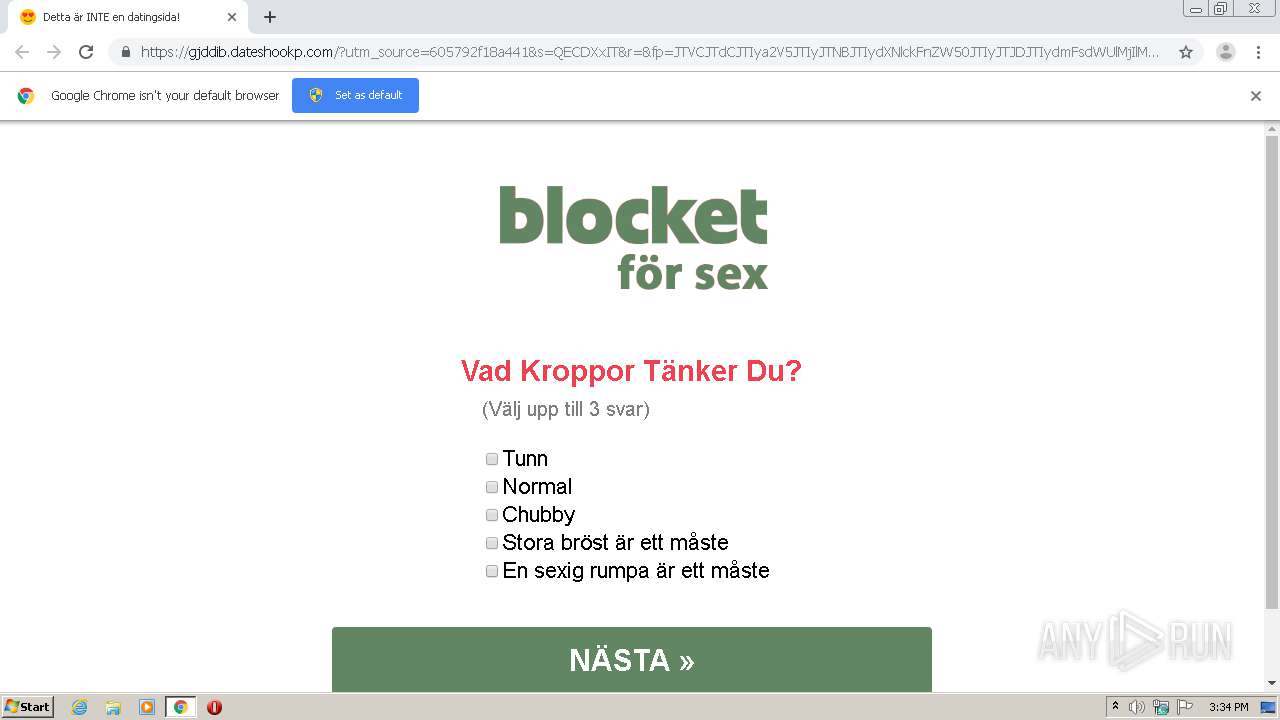
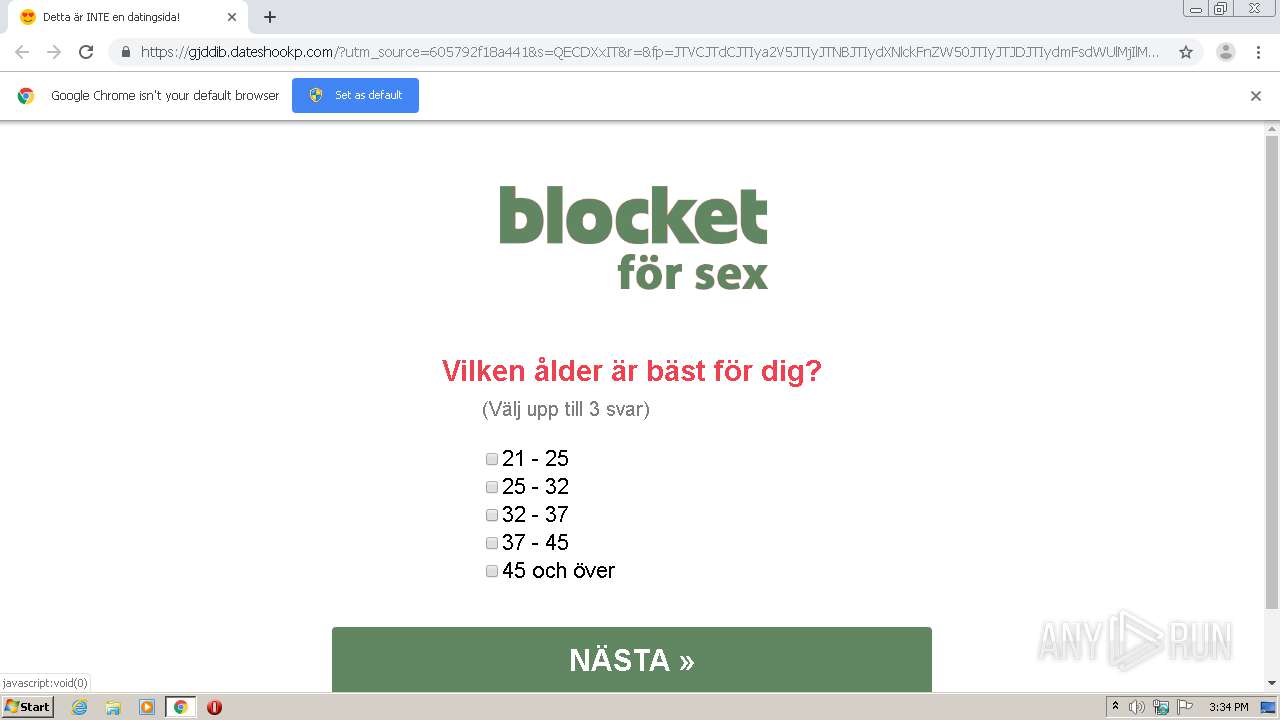
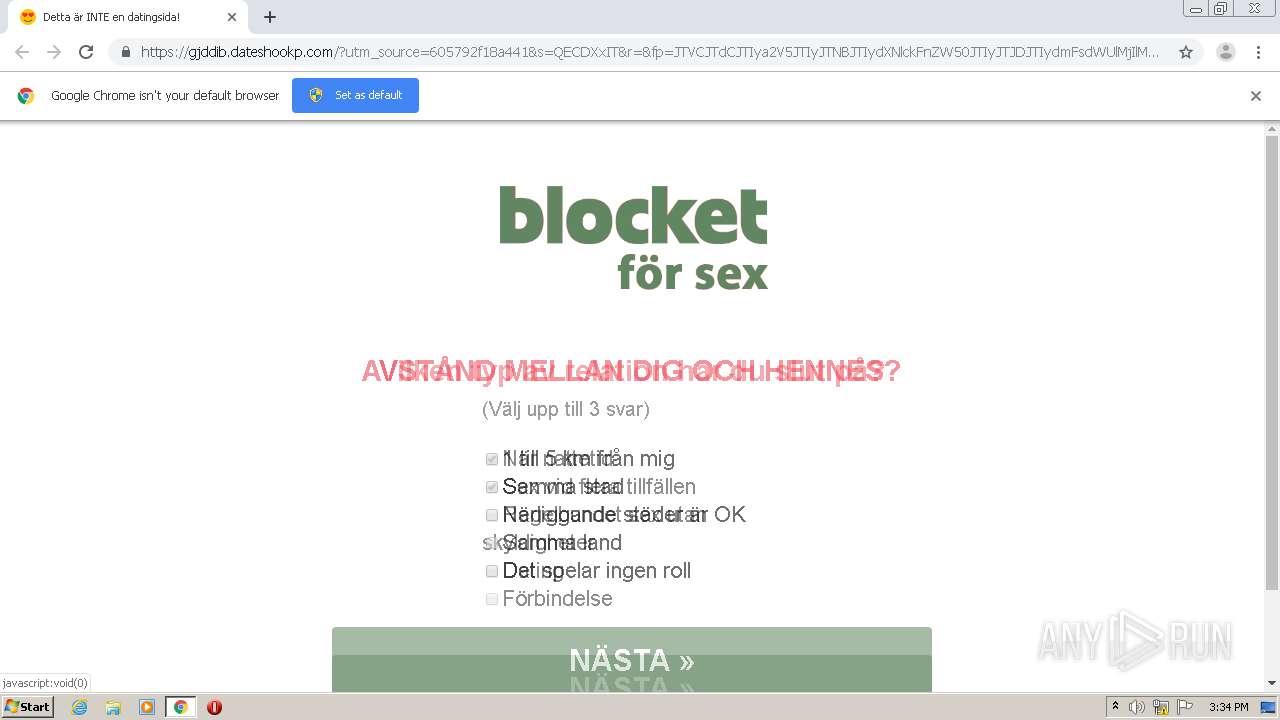
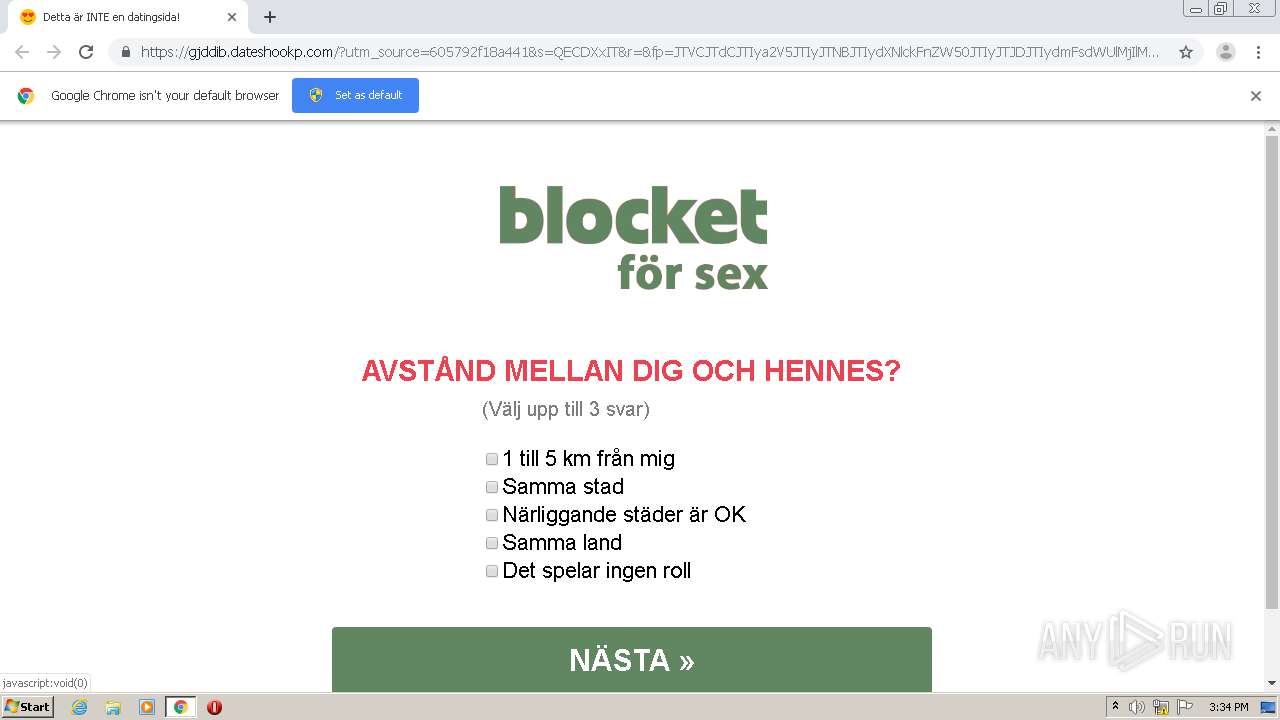
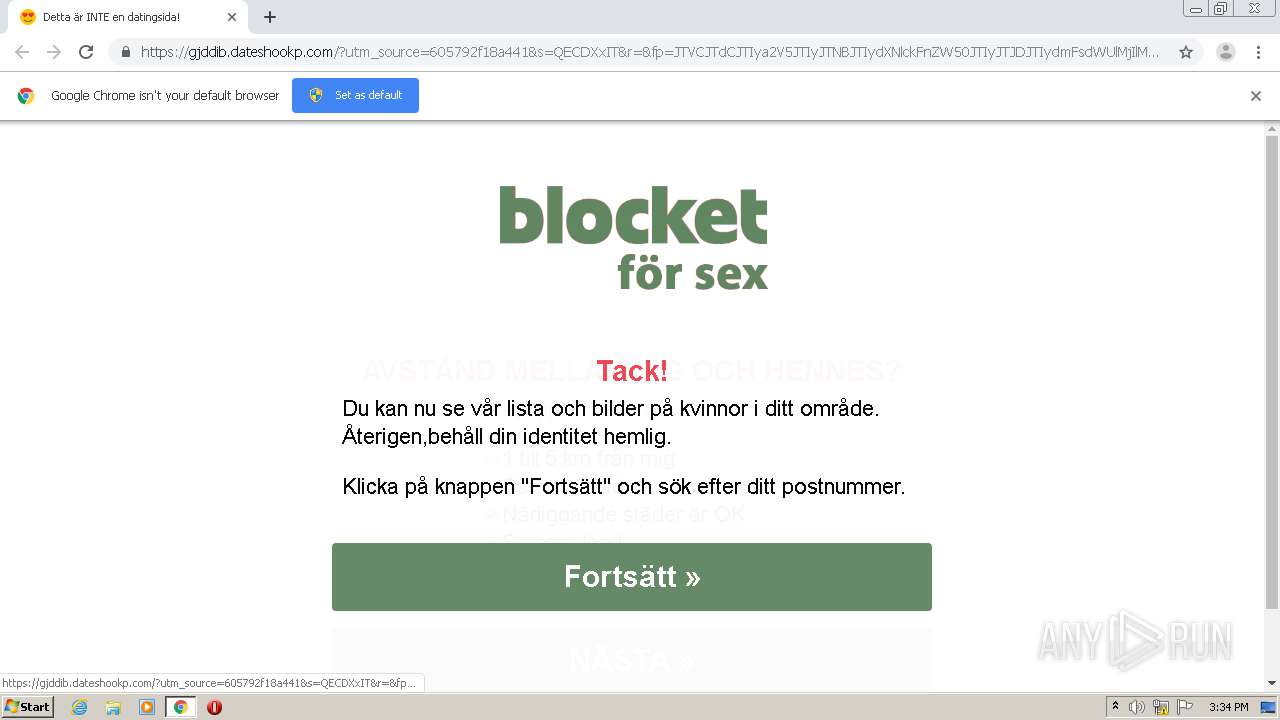
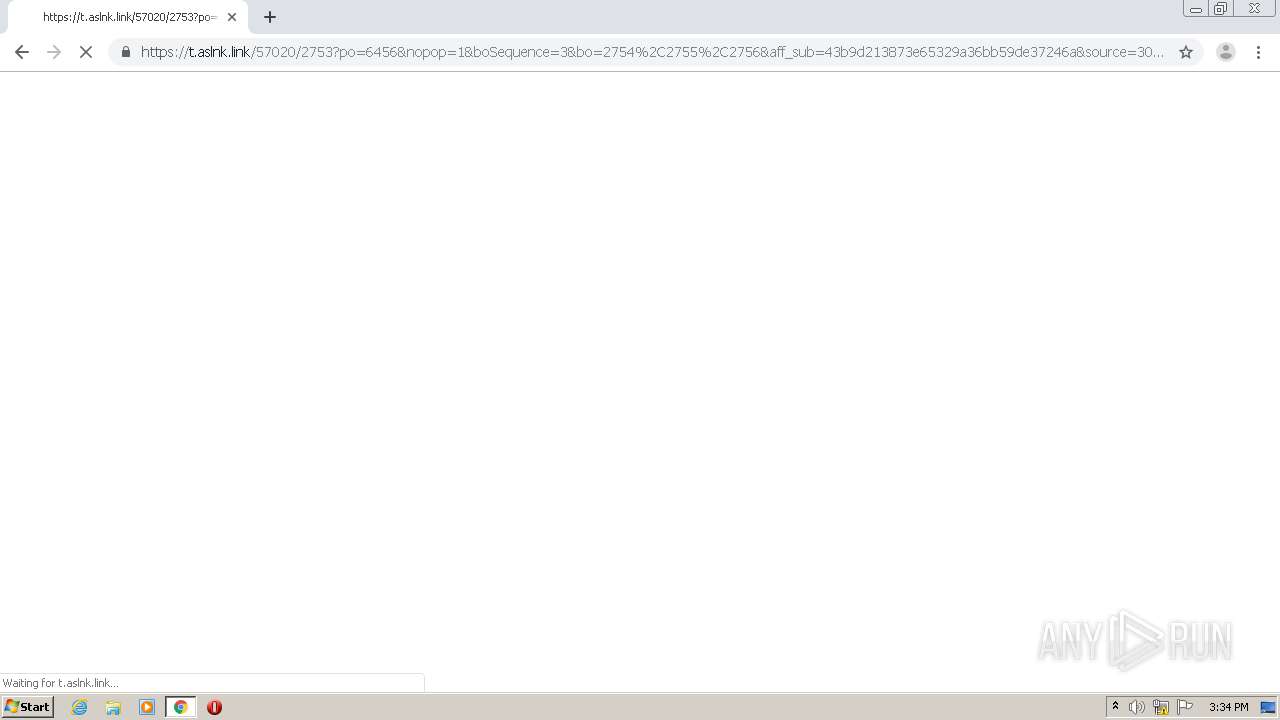
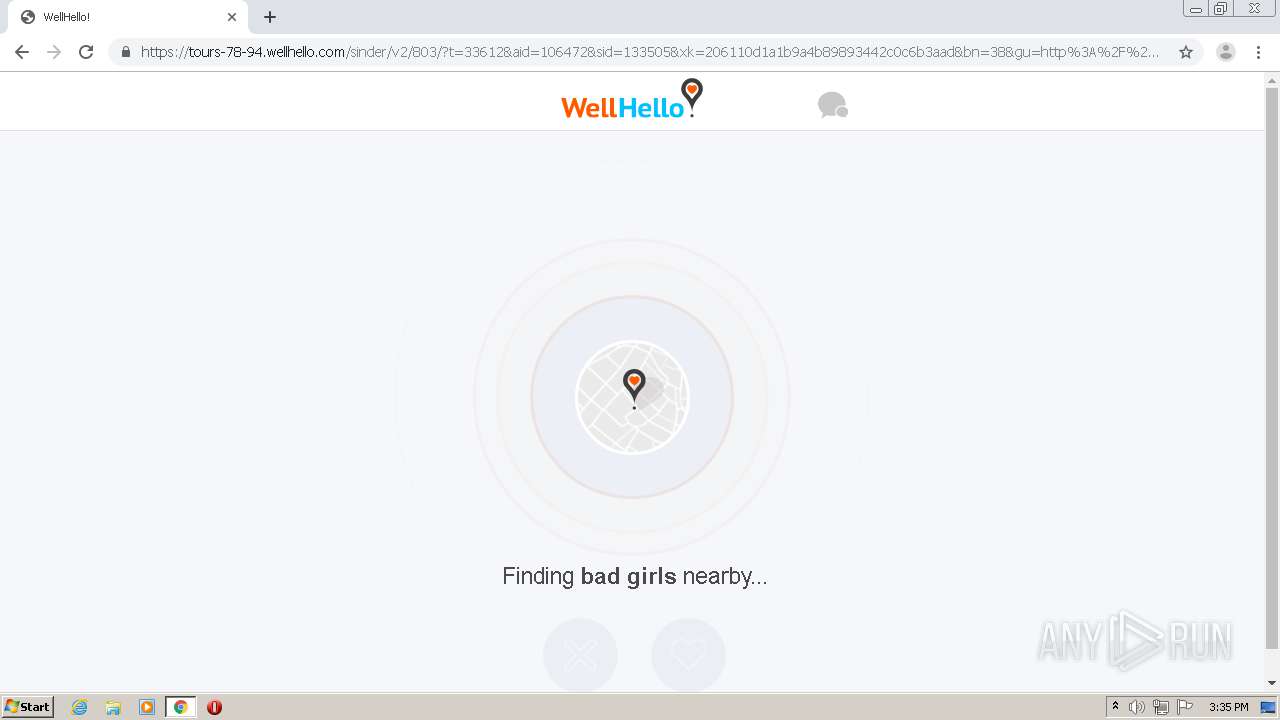
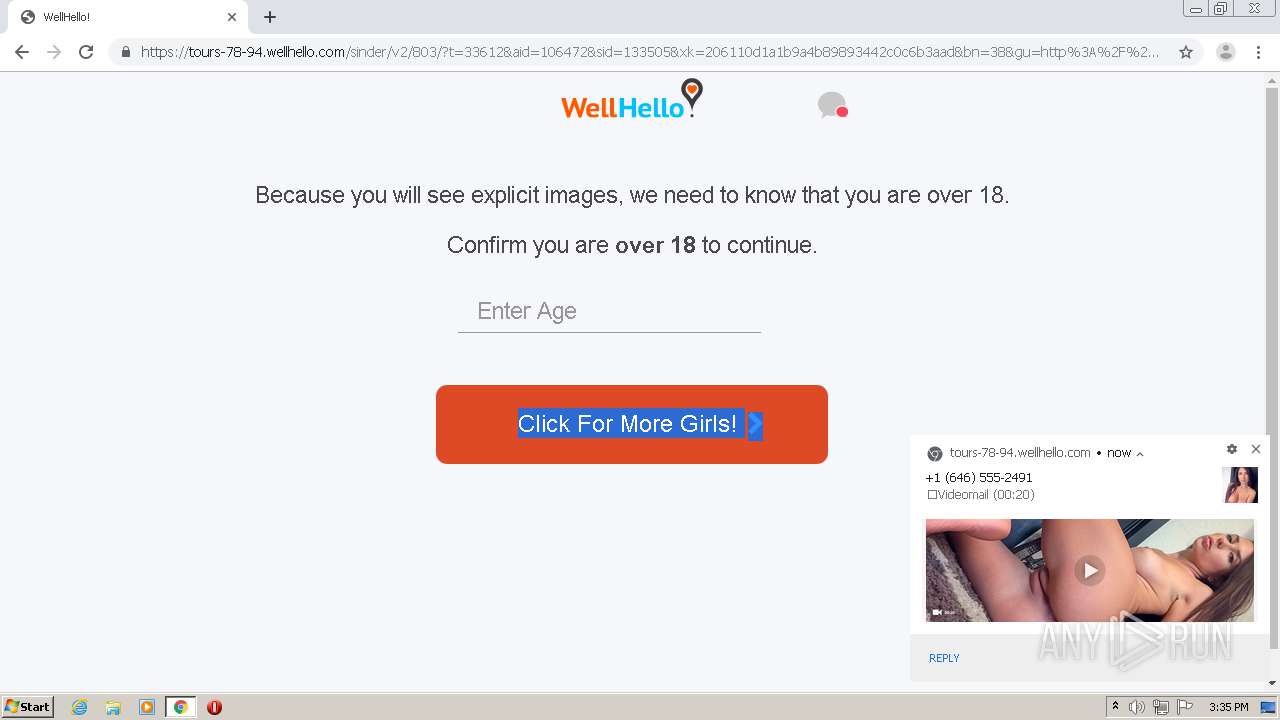
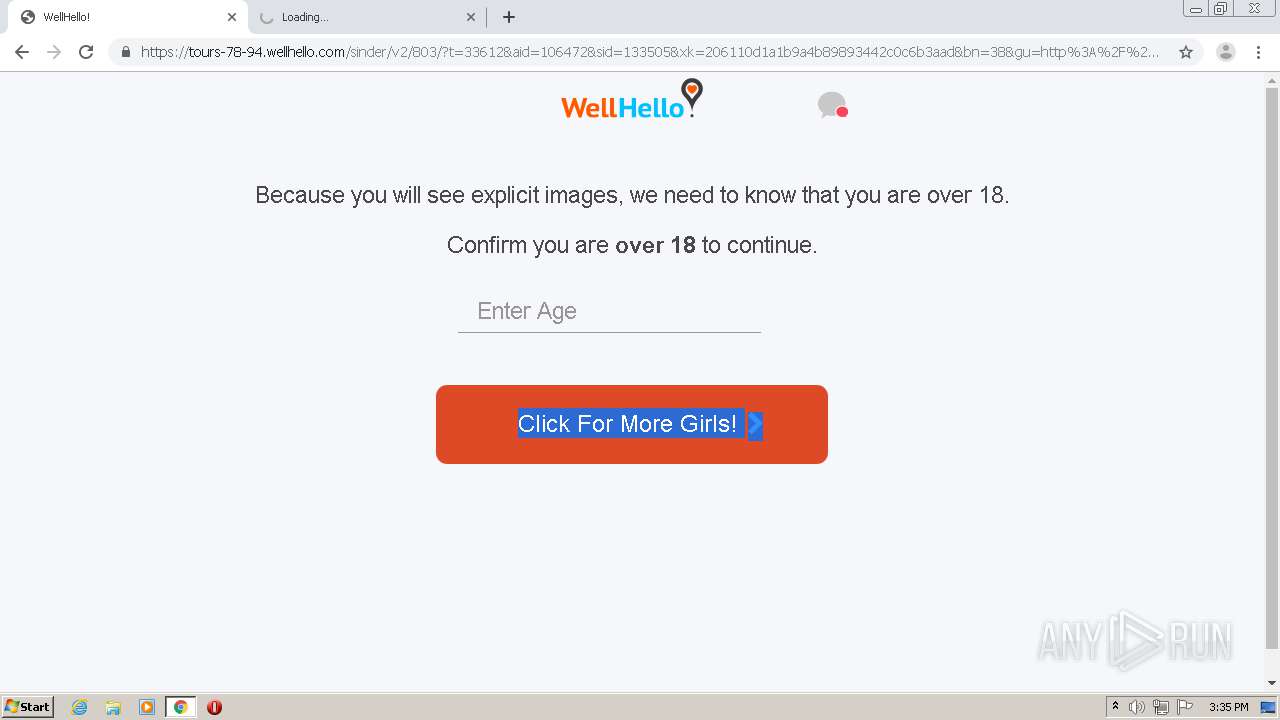
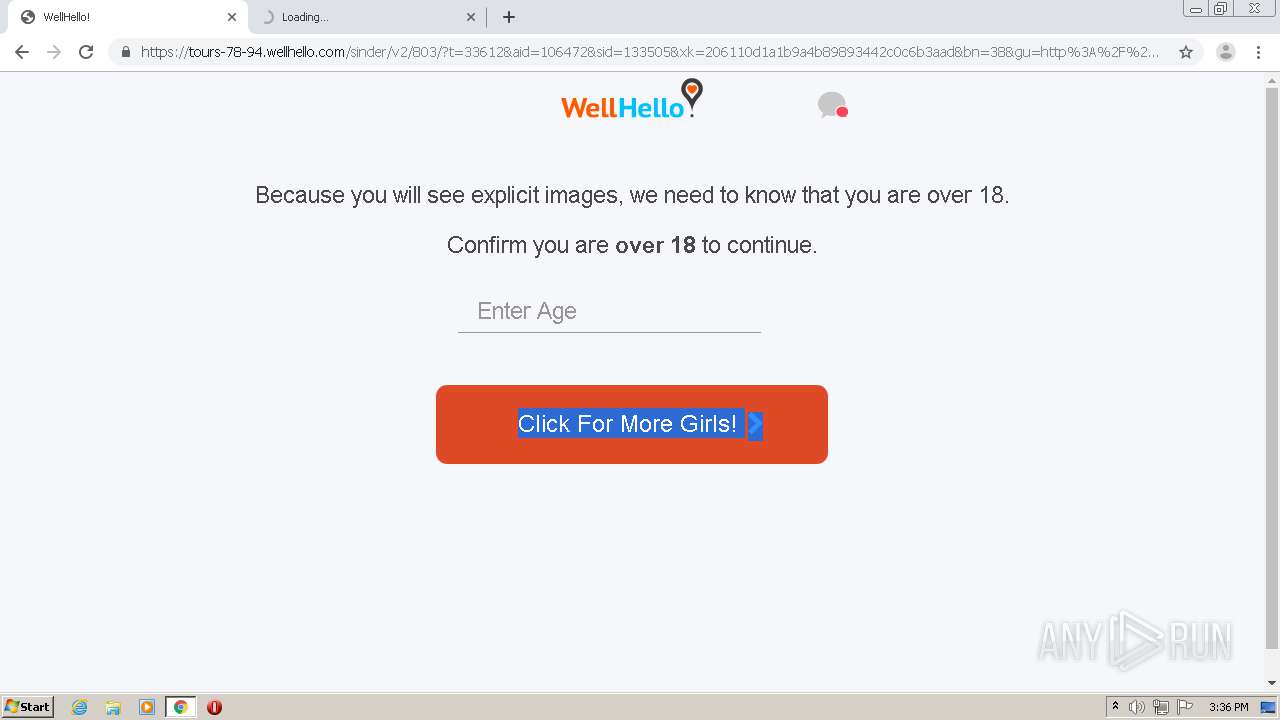
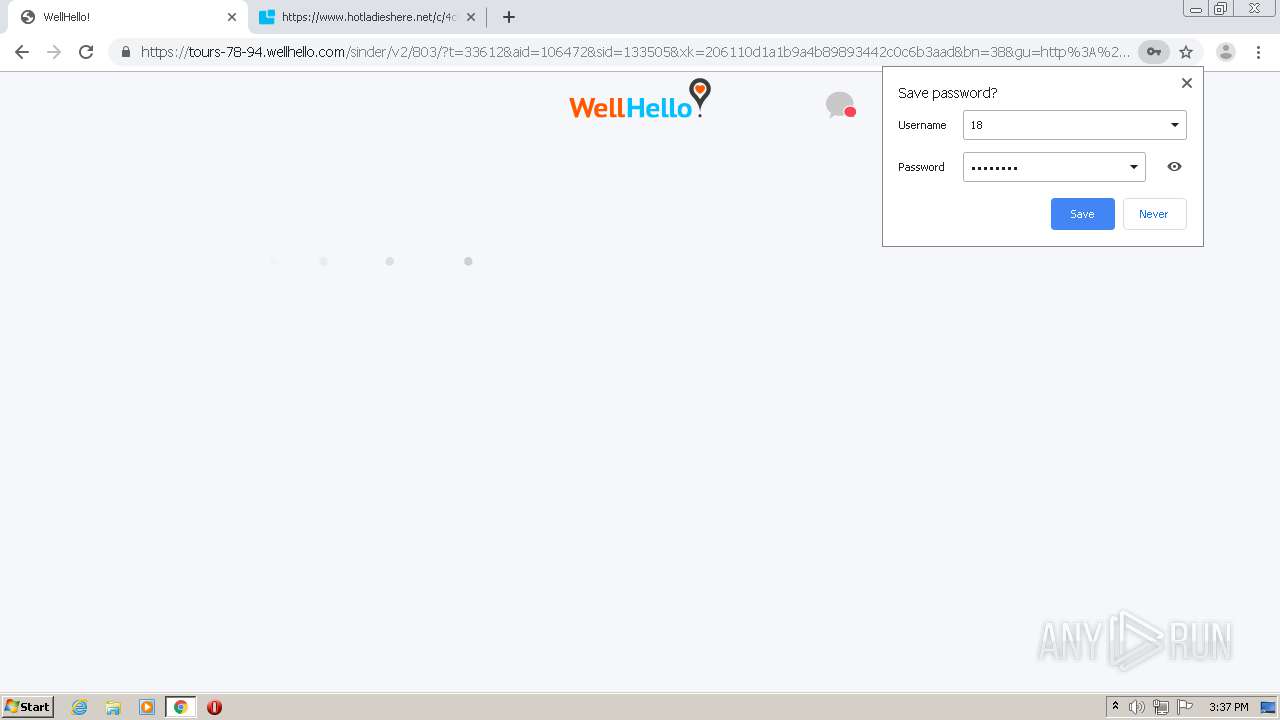
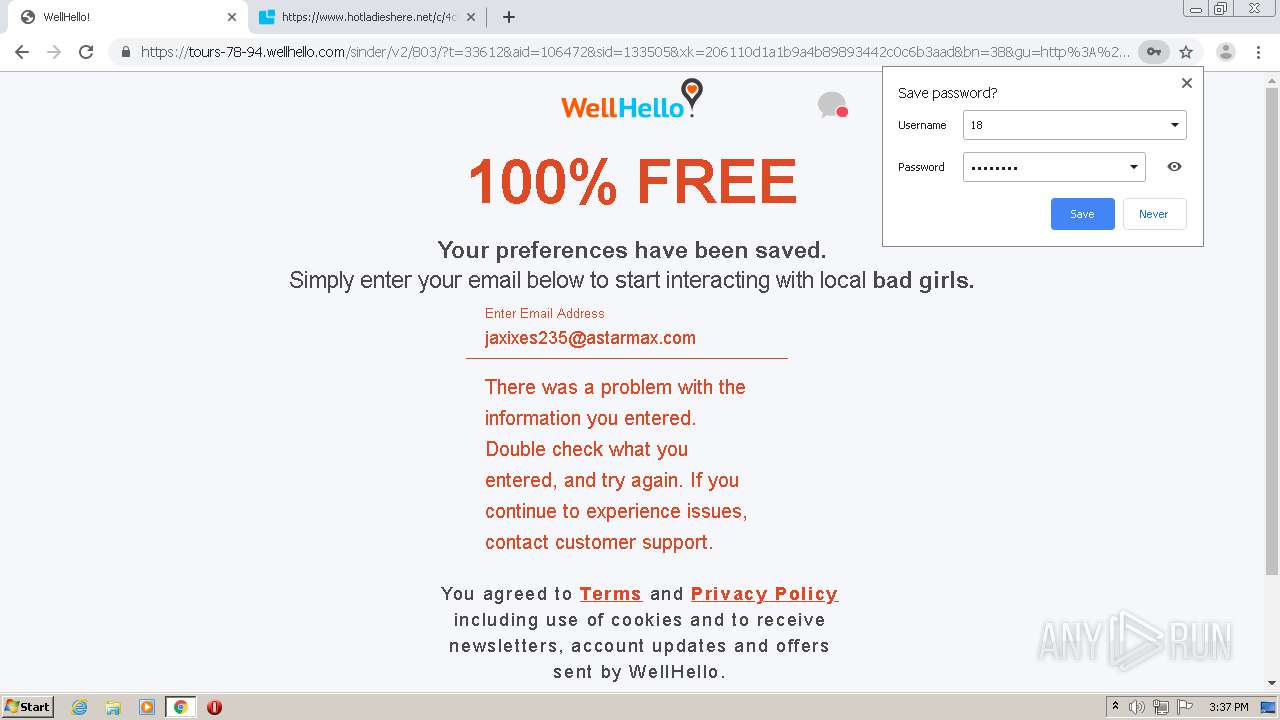
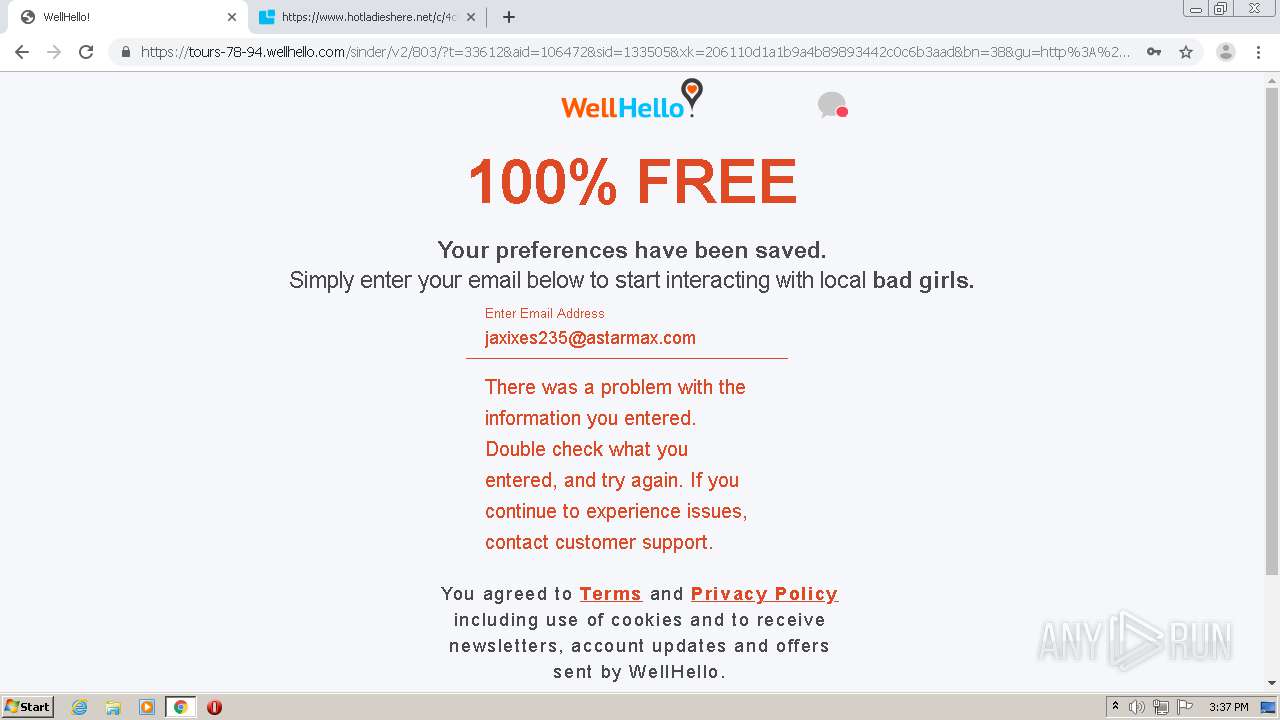
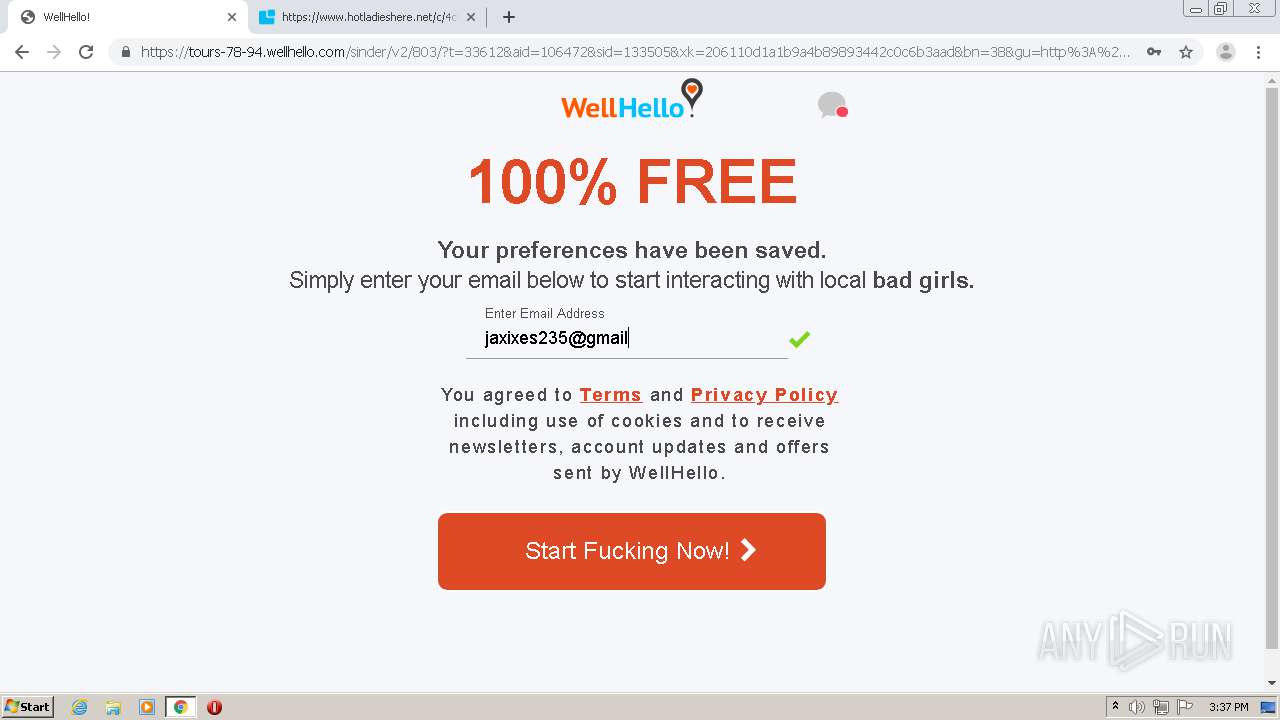
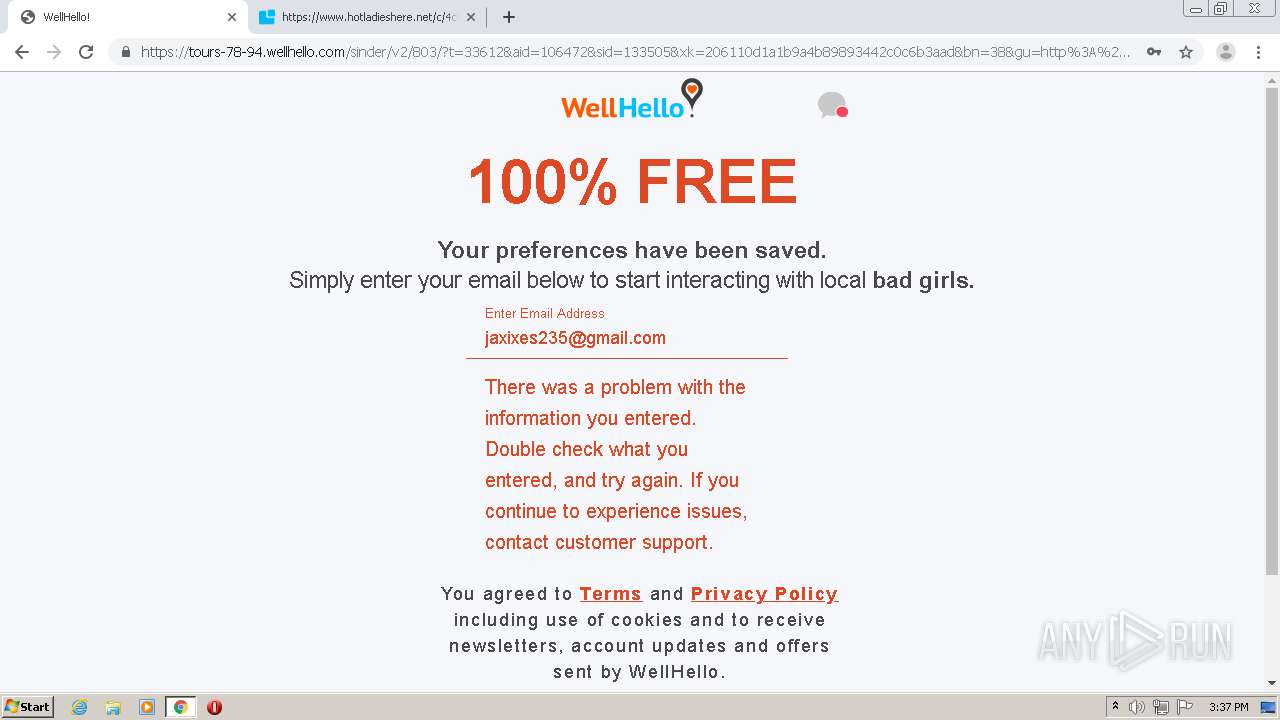
| URL: | https://gjddib.dateshookp.com/?utm_source=605792f18a441 |
| Full analysis: | https://app.any.run/tasks/04edae0c-28e7-4d57-a1d2-1382ceecc876 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2021, 15:33:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7224925D28F015421C16F3D2DA0D0857 |
| SHA1: | E44D00C5F8562161DE4AB4DBC5D7B68BFAB7F4B6 |
| SHA256: | 774C2FB8B7D879D990870B69F529B55536776F64E5D6712970AA3522D1470F21 |
| SSDEEP: | 3:N8uB6HXhGKIyCWjgyn:2uBMhGKIlWjNn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
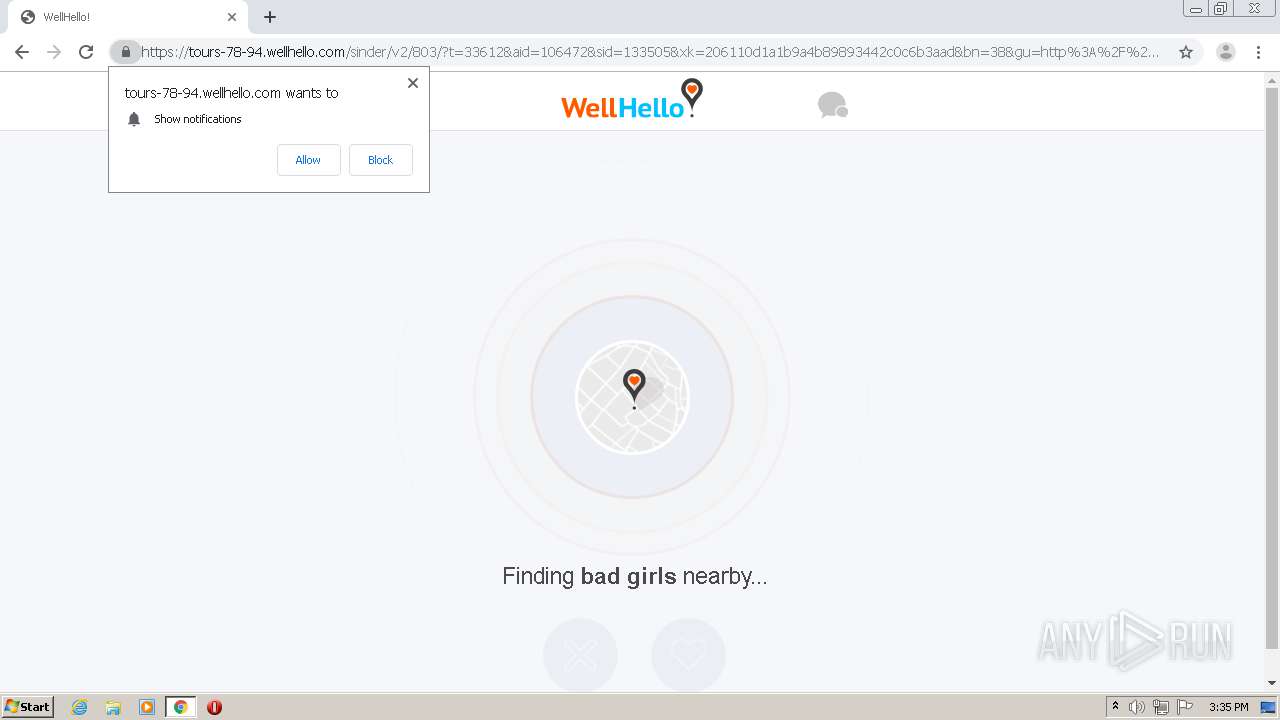
Reads settings of System Certificates
- chrome.exe (PID: 2148)
Reads the hosts file
- chrome.exe (PID: 2156)
- chrome.exe (PID: 2148)
Application launched itself
- chrome.exe (PID: 2156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1274058427848717328 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3735636184624859328 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2544 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15032473501864875978 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9506733423027199981 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12645710080528542624 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3065513503725436234 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14268879641672717658 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4773990980446029294 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16655163678524070103,11183873782113670033,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12828868306075915129 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c1ea9d0,0x6c1ea9e0,0x6c1ea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
629
Read events
533
Write events
93
Delete events
3
Modification events
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2156-13261160040667375 |
Value: 259 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2156) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
98
Text files
116
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-605CAD69-86C.pma | — | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f7fa3826-f6e2-47cc-8642-feca8588fcd1.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe6c33.TMP | text | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe6c33.TMP | text | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe6e65.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
106
DNS requests
49
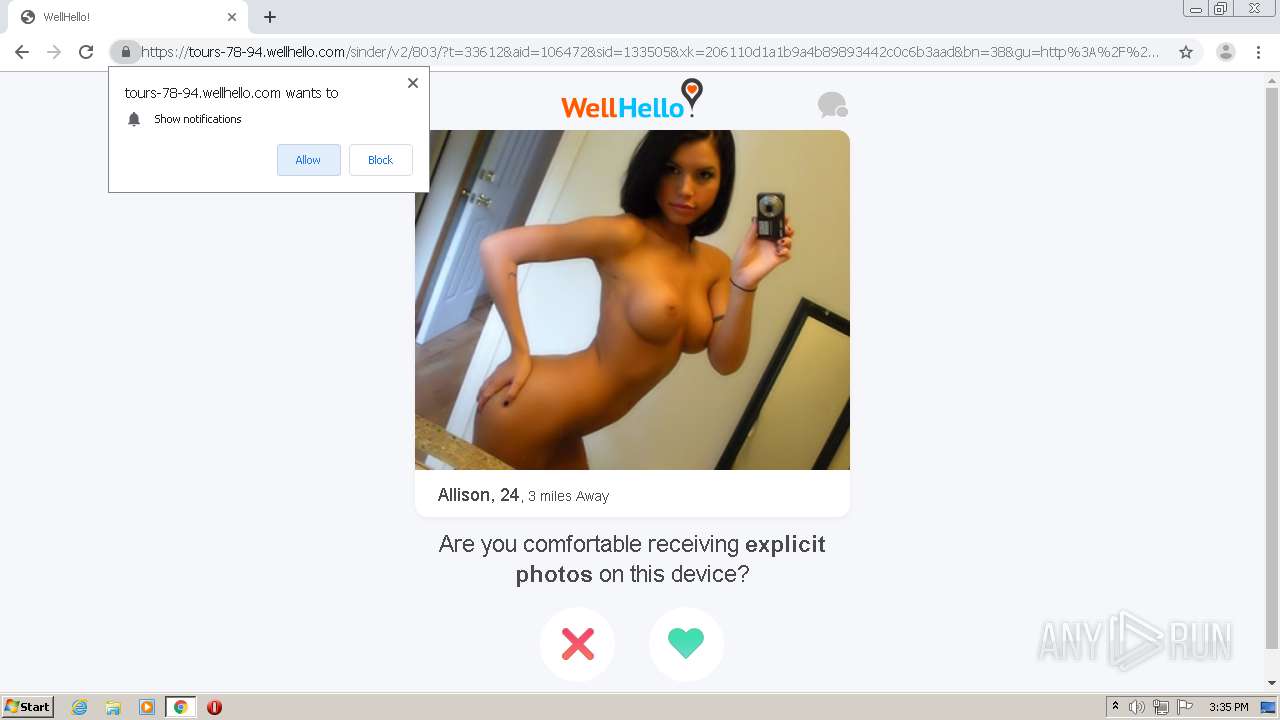
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
2148 | chrome.exe | GET | — | 64.188.52.46:80 | http://go.moartraffic.com/go.php?t=40231&aid=106472&sid=133505&clickid=10222d9d55f0e4774cd04dc4548225&bt=0 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
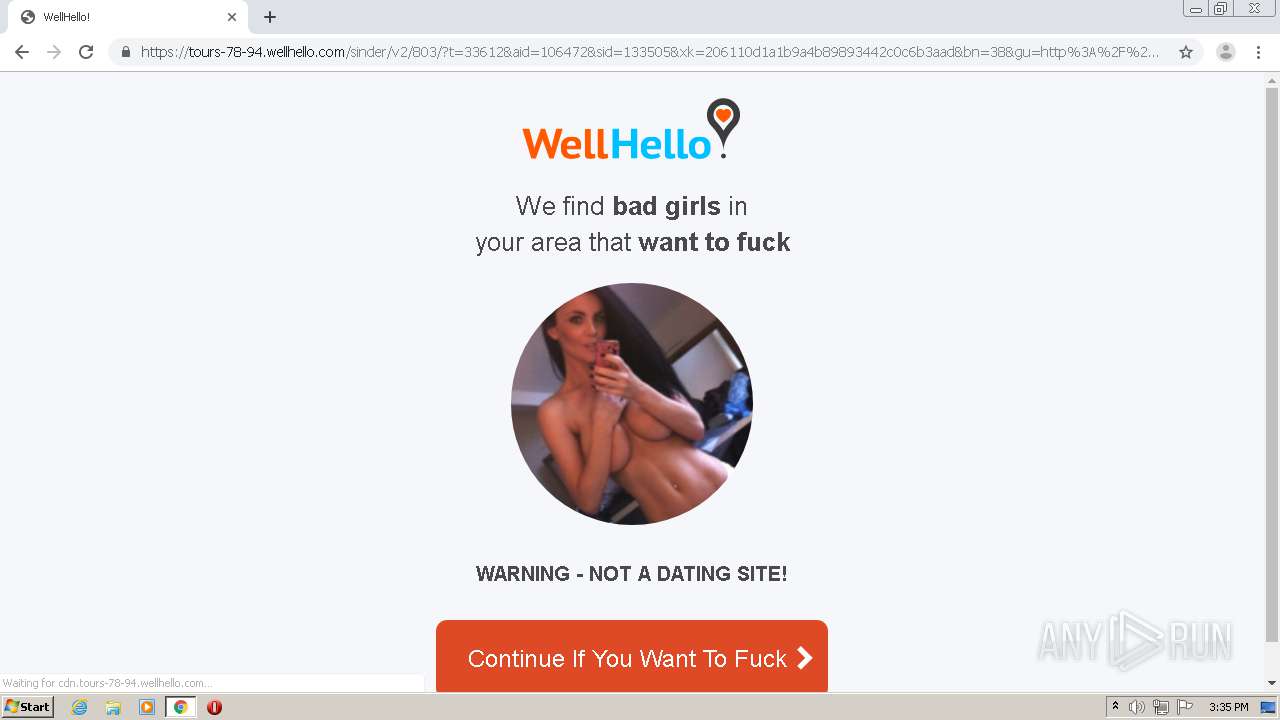
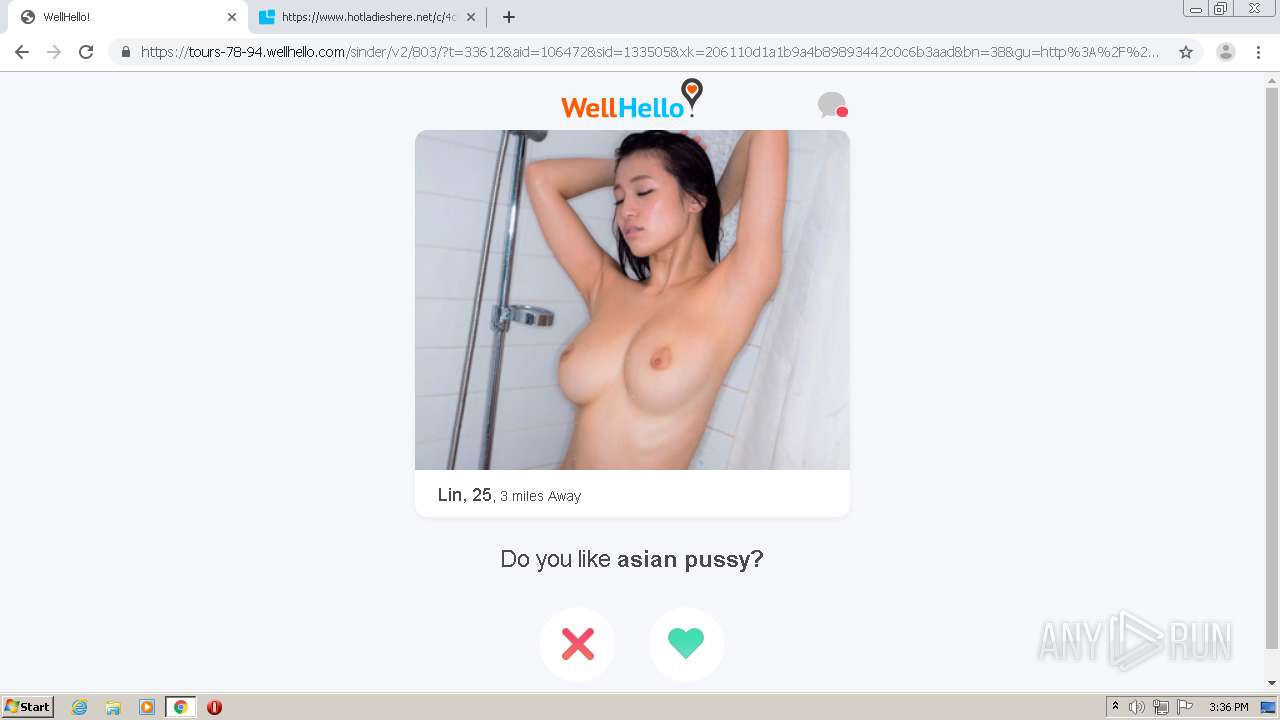
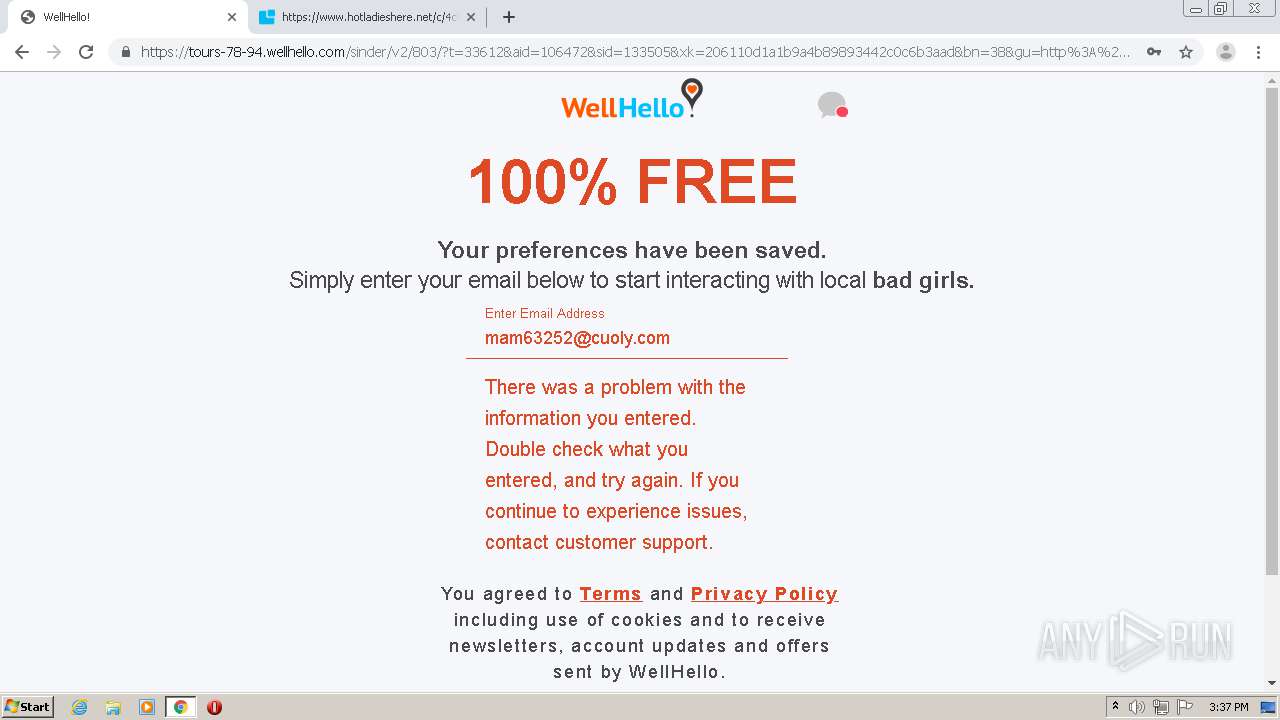
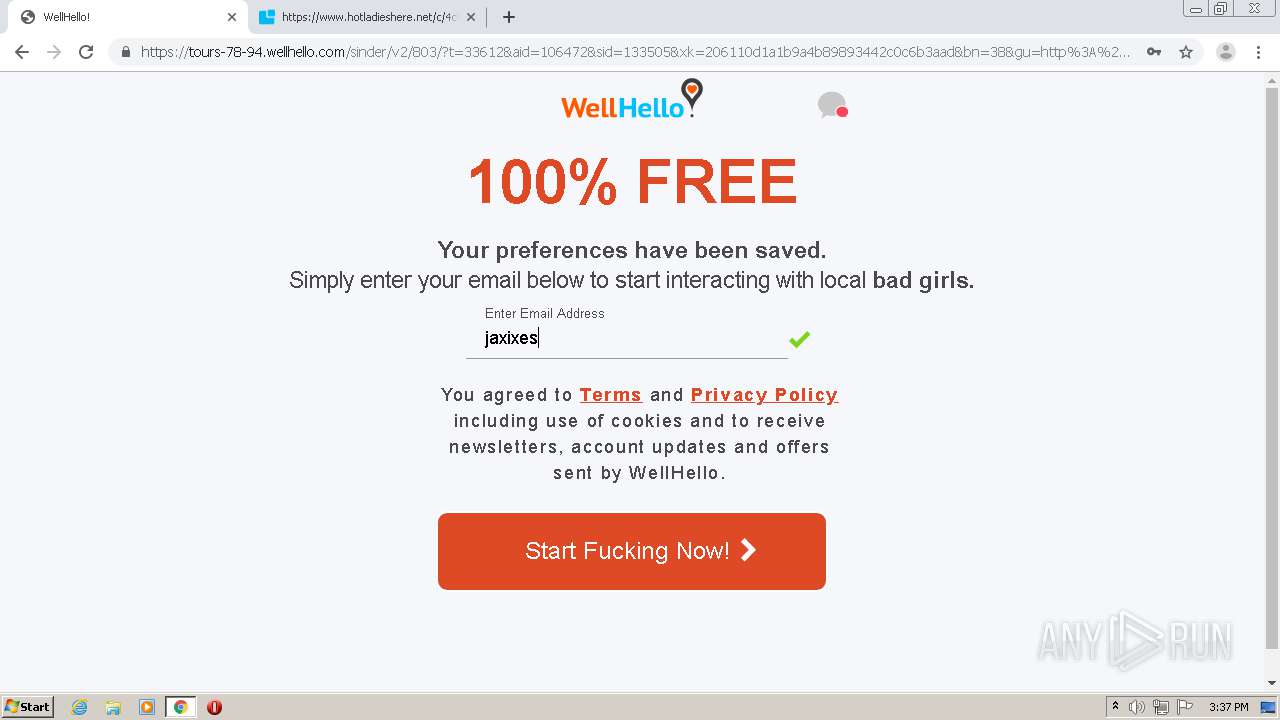
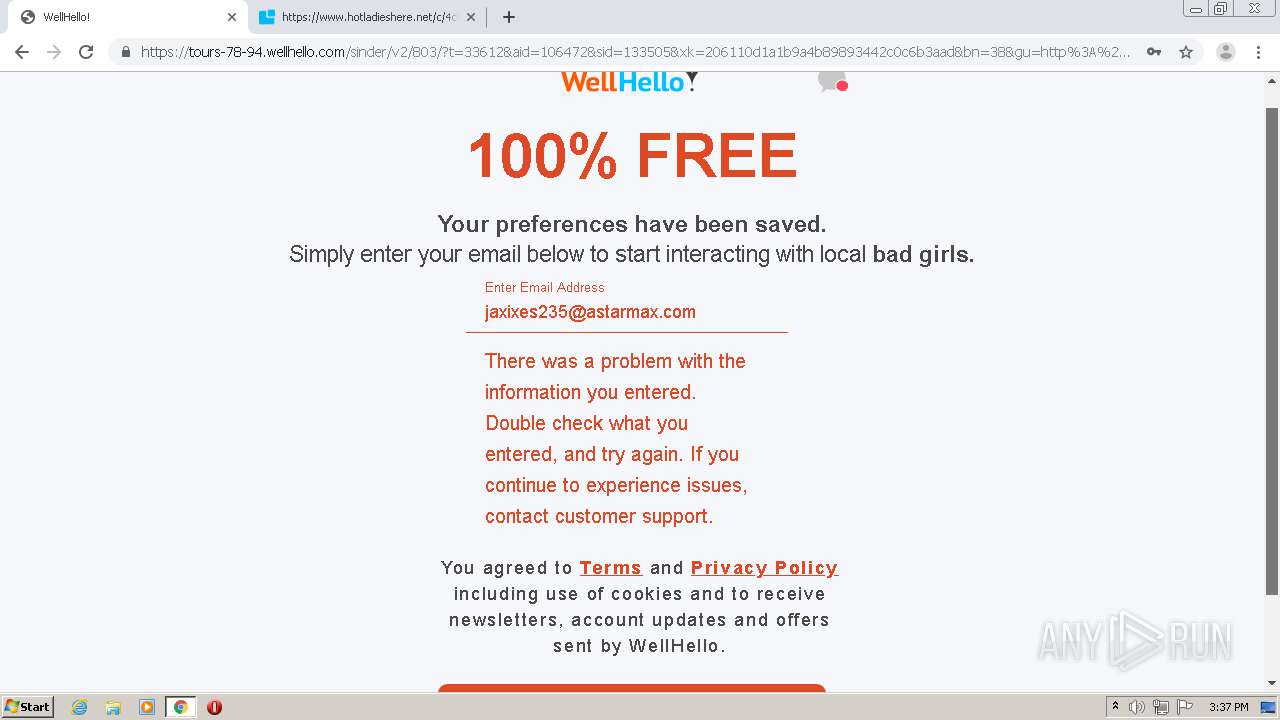
2148 | chrome.exe | 144.76.30.237:443 | gjddib.dateshookp.com | Hetzner Online GmbH | DE | suspicious |
2148 | chrome.exe | 172.217.18.77:443 | accounts.google.com | Google Inc. | US | unknown |
2148 | chrome.exe | 216.58.214.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
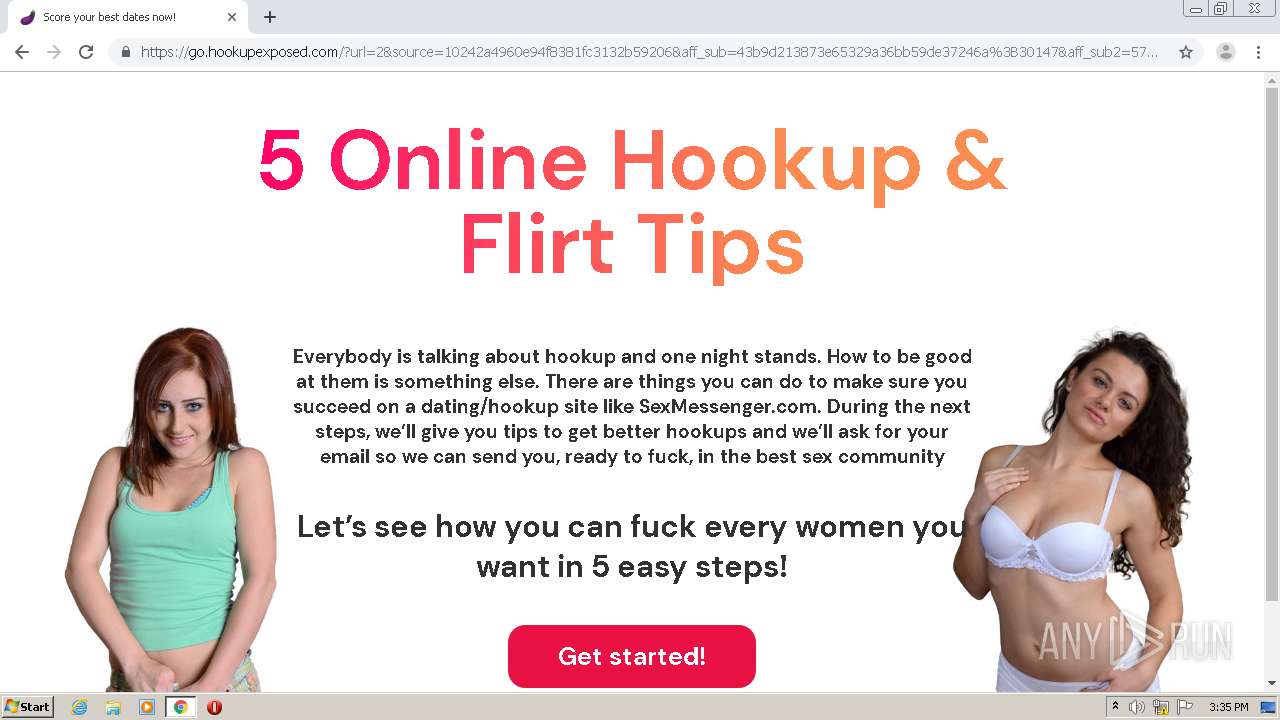
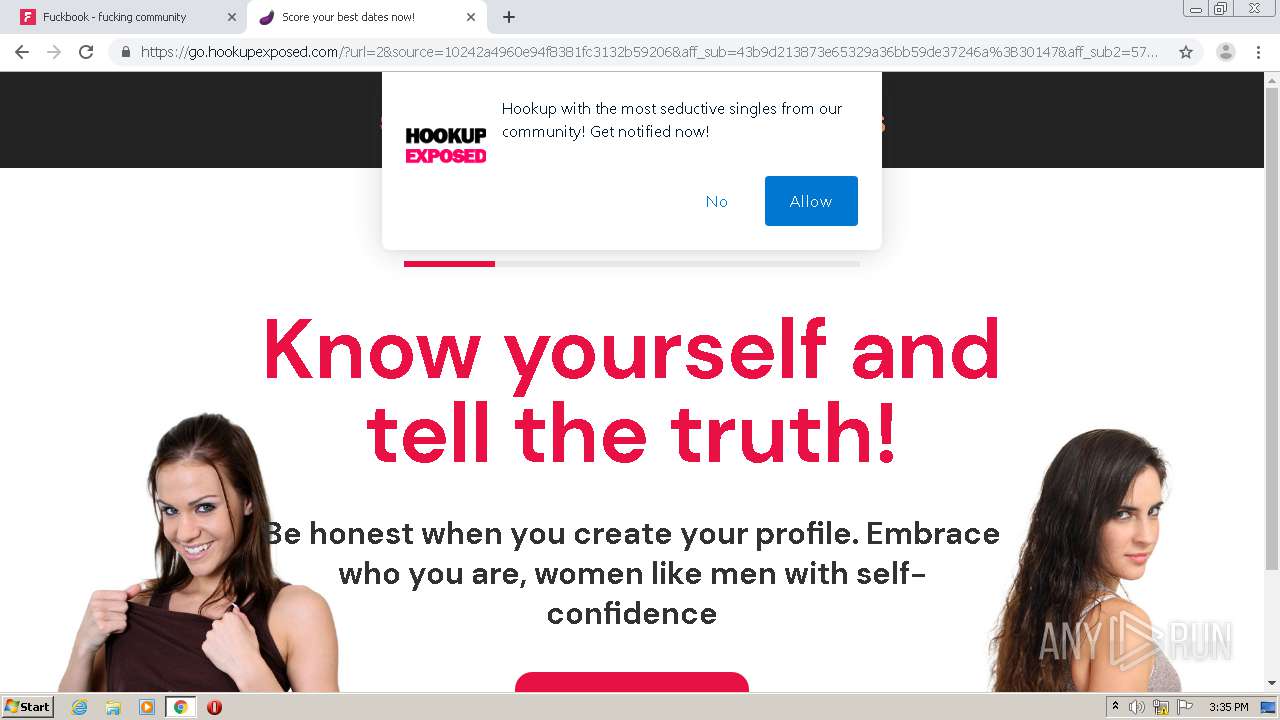
2148 | chrome.exe | 54.237.191.95:443 | go.hookupexposed.com | Amazon.com, Inc. | US | suspicious |
2148 | chrome.exe | 172.217.18.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 185.59.220.199:443 | gateway.hookupexposed.com | Datacamp Limited | DE | suspicious |
2148 | chrome.exe | 172.217.20.8:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2148 | chrome.exe | 151.139.128.11:443 | static.selfpuc.com | Highwinds Network Group, Inc. | US | malicious |
2148 | chrome.exe | 64.233.167.188:5228 | mtalk.google.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 142.250.74.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gjddib.dateshookp.com |
| unknown |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
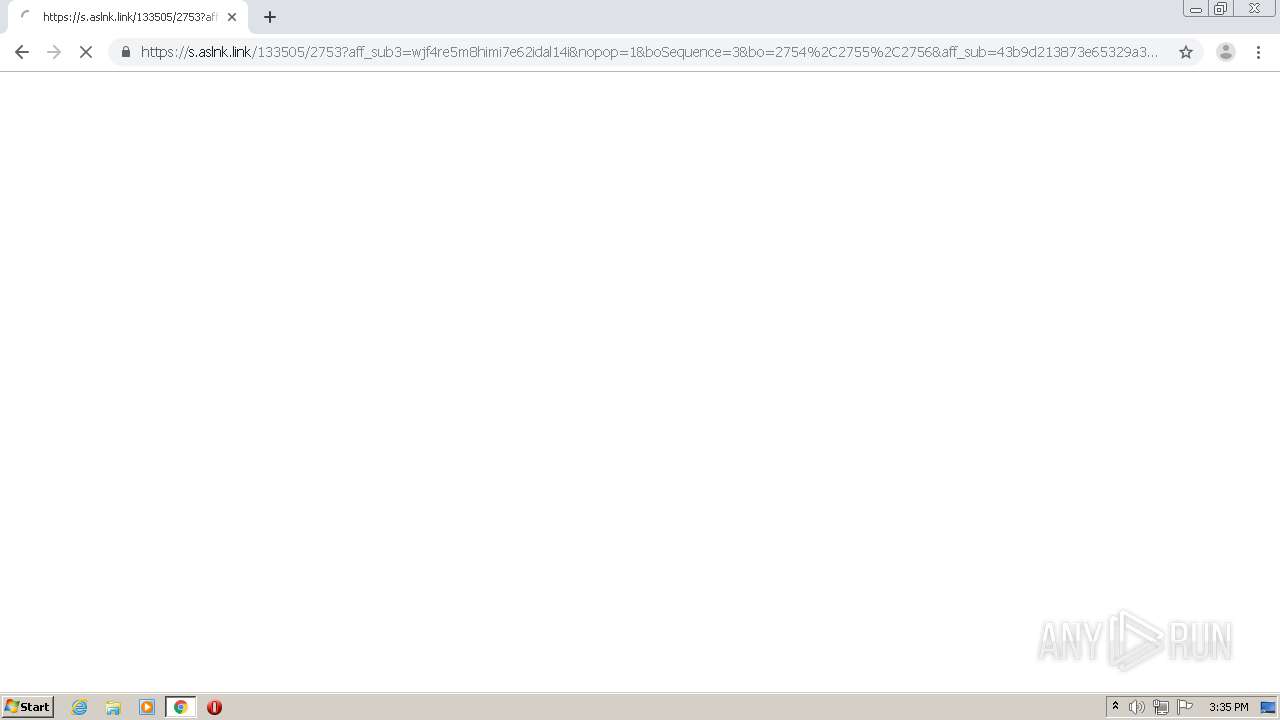
t.aslnk.link |
| malicious |
ckstatic.com |
| suspicious |
a.vfgtg.com |
| suspicious |
go.hookupexposed.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
gateway.hookupexposed.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |