| File name: | SKCertServiceSetup.exe |
| Full analysis: | https://app.any.run/tasks/6f33c28a-9ef0-435c-9940-80143a34f6ac |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2023, 04:30:09 |
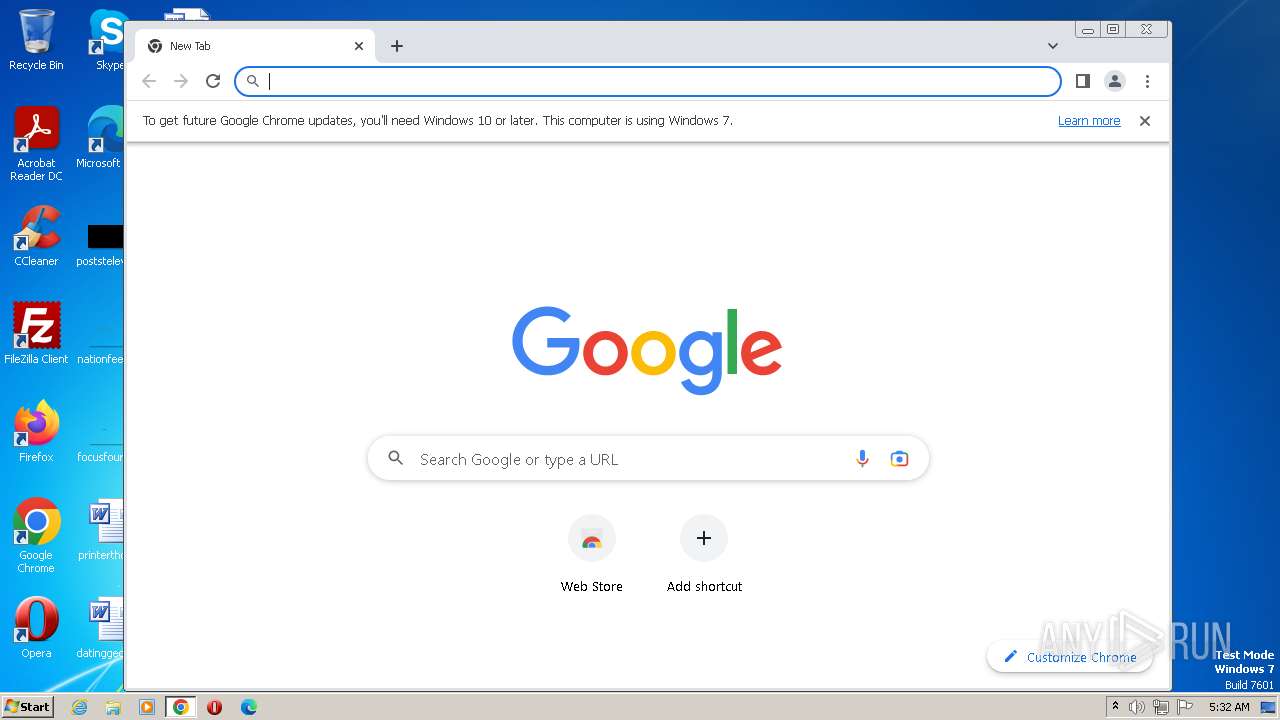
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B9A574BD78B869AEDCB69C5D08822387 |
| SHA1: | 5F6A71FBD2D8A10680A2D0620D4D524A4E4D6F30 |
| SHA256: | 77487E3F802AE80CB75C30860883C1A531B1A3EA736DA7366D3950CD6B627B54 |
| SSDEEP: | 196608:8ddrPkAWDboj2zDKZeuUQup8F9O3GVbZX1n7QOv0Kq0ziX4CdEX4TKH:Adr8AWDboanKxUQc8a6ZX97Xv20OhdET |
MALICIOUS
Application was dropped or rewritten from another process
- SignKoreaWD.exe (PID: 2808)
- SetupPKG.exe (PID: 2488)
- SignKoreaWD.exe (PID: 3048)
- SKCertService.exe (PID: 1548)
- SantiagoWireInitializer.exe (PID: 1576)
- SKCertService.exe (PID: 2720)
Loads dropped or rewritten executable
- SKCertService.exe (PID: 1548)
- SantiagoWireInitializer.exe (PID: 1576)
- SKCertService.exe (PID: 2720)
Actions looks like stealing of personal data
- SKCertService.exe (PID: 1548)
- SantiagoWireInitializer.exe (PID: 1576)
SUSPICIOUS
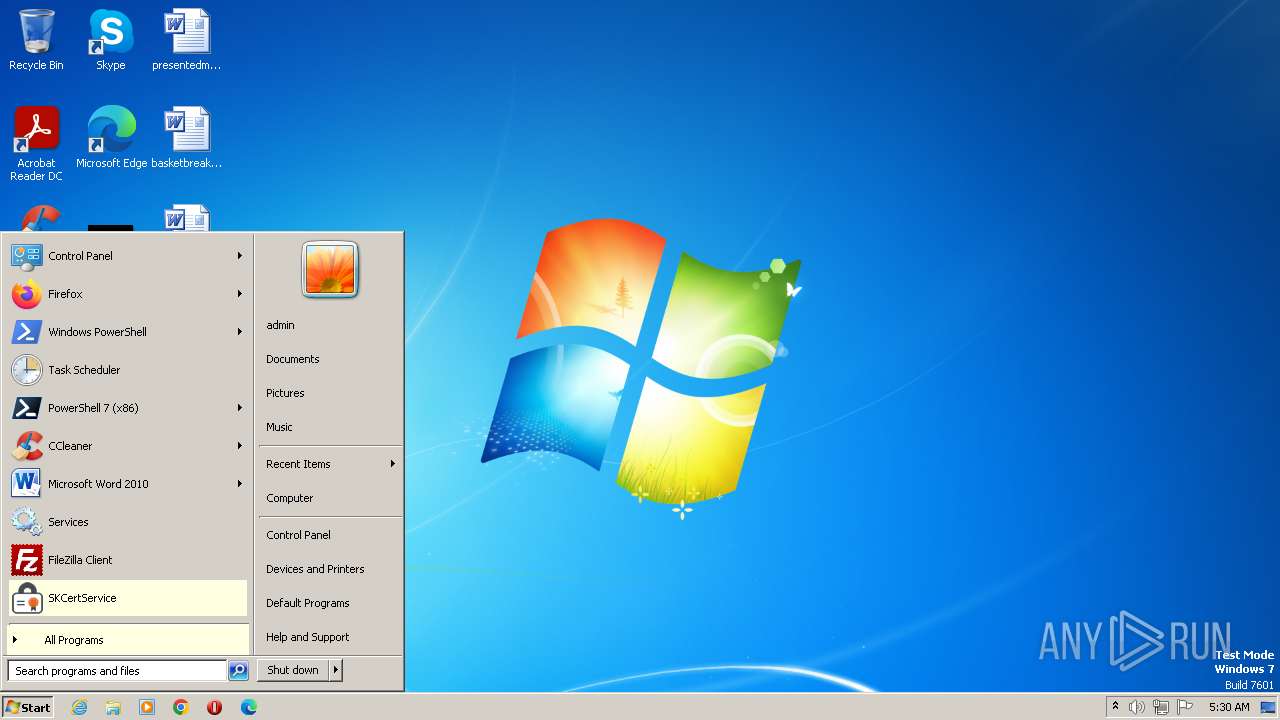
Executes as Windows Service
- SignKoreaWD.exe (PID: 2808)
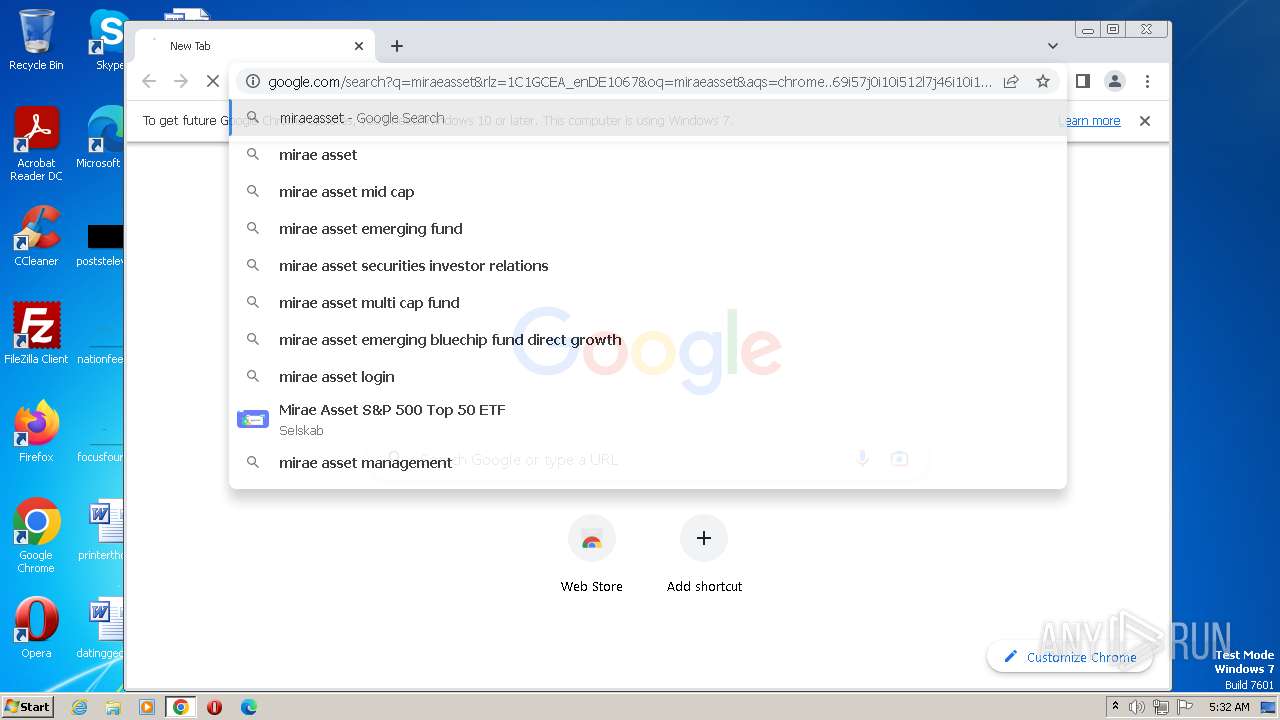
Searches for installed software
- SetupPKG.exe (PID: 2488)
Executable content was dropped or overwritten
- SetupPKG.exe (PID: 2488)
- SKCertServiceSetup.exe (PID: 2828)
Reads the Internet Settings
- SetupPKG.exe (PID: 2488)
- SKCertService.exe (PID: 1548)
Reads the BIOS version
- SKCertService.exe (PID: 1548)
- SKCertService.exe (PID: 2720)
INFO
Checks supported languages
- SKCertServiceSetup.exe (PID: 2828)
- SetupPKG.exe (PID: 2488)
- SignKoreaWD.exe (PID: 2808)
- SignKoreaWD.exe (PID: 3048)
- SantiagoWireInitializer.exe (PID: 1576)
- SKCertService.exe (PID: 1548)
- SKCertService.exe (PID: 2720)
Create files in a temporary directory
- SKCertServiceSetup.exe (PID: 2828)
Creates files in the program directory
- SetupPKG.exe (PID: 2488)
- SignKoreaWD.exe (PID: 2808)
- SignKoreaWD.exe (PID: 3048)
- SKCertService.exe (PID: 1548)
Reads the computer name
- SignKoreaWD.exe (PID: 2808)
- SetupPKG.exe (PID: 2488)
- SignKoreaWD.exe (PID: 3048)
- SKCertService.exe (PID: 1548)
- SantiagoWireInitializer.exe (PID: 1576)
Creates files or folders in the user directory
- SetupPKG.exe (PID: 2488)
- SKCertService.exe (PID: 1548)
- SantiagoWireInitializer.exe (PID: 1576)
Reads the machine GUID from the registry
- SKCertService.exe (PID: 1548)
- SantiagoWireInitializer.exe (PID: 1576)
- SKCertService.exe (PID: 2720)
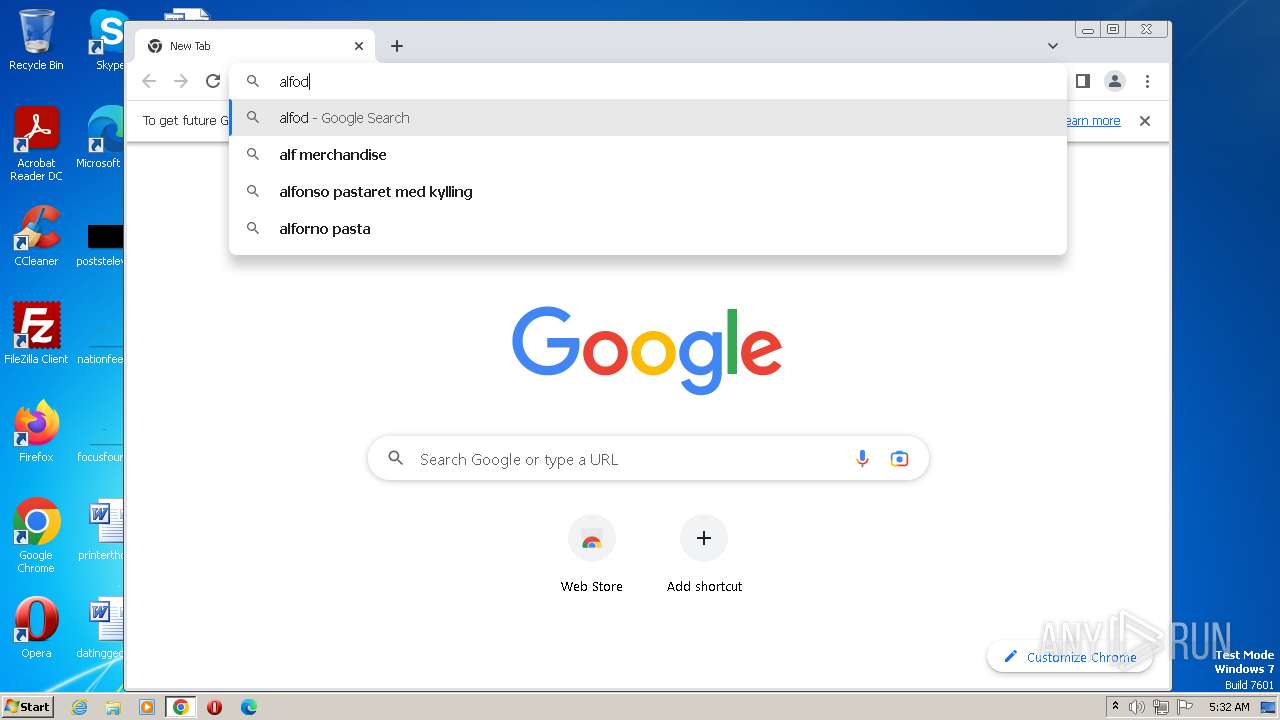
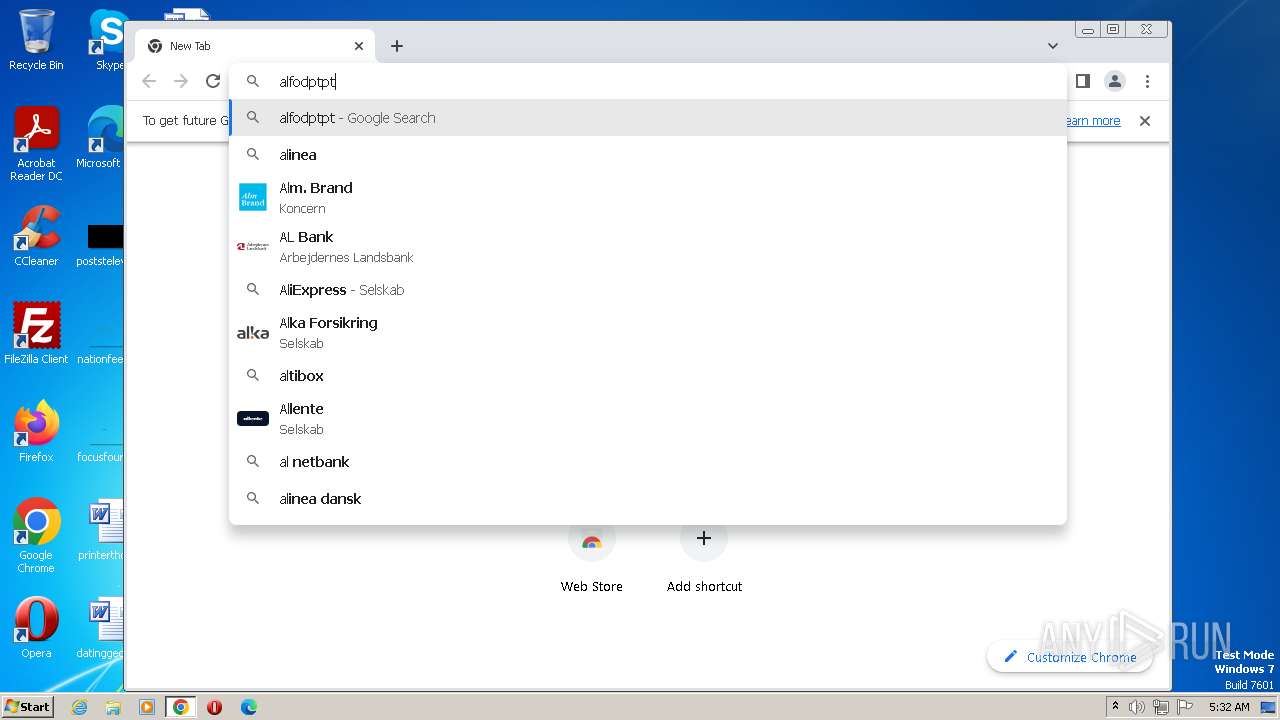
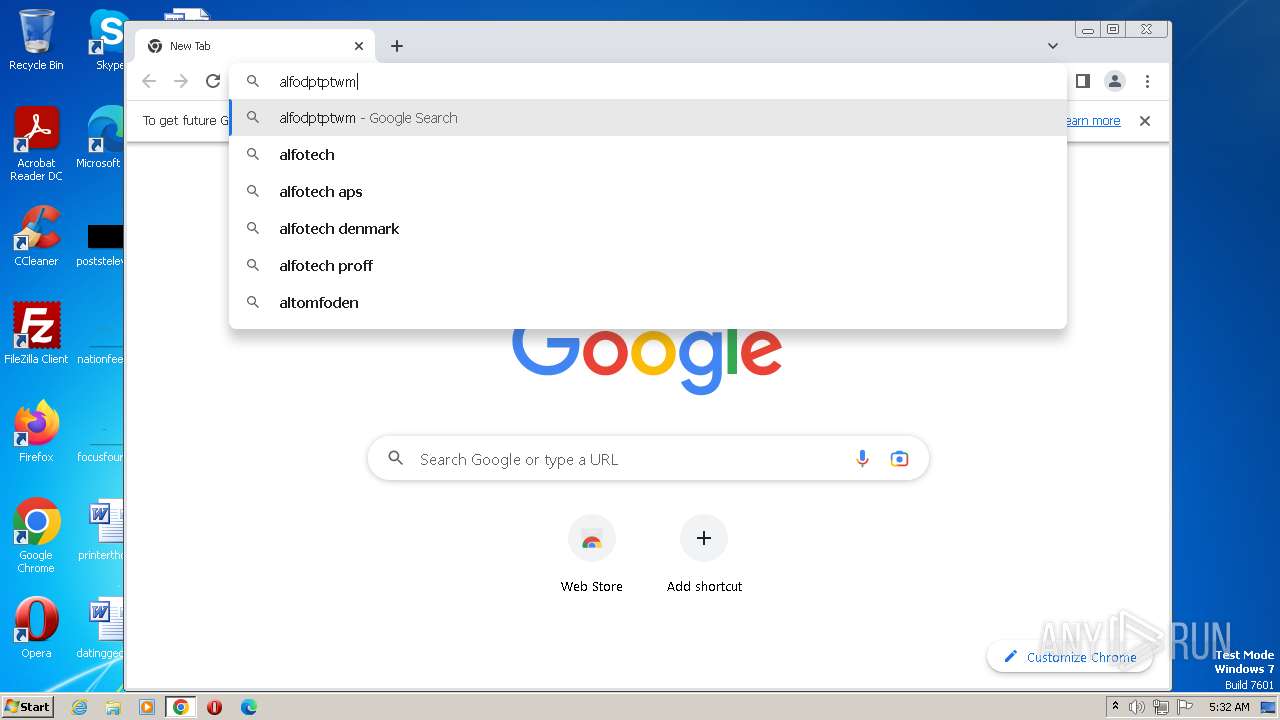
Manual execution by a user
- SKCertService.exe (PID: 2720)
- chrome.exe (PID: 3576)
The process uses the downloaded file
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2424)
Application launched itself
- chrome.exe (PID: 3576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 9.2 |
|---|---|
| ProductName: | 7-Zip |
| OriginalFileName: | 7zS.sfx.exe |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| InternalName: | 7zS.sfx |
| FileVersion: | 9.2 |
| FileDescription: | 7z Setup SFX |
| CompanyName: | Igor Pavlov |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 9.20.0.0 |
| FileVersionNumber: | 9.20.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1373c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 30208 |
| CodeSize: | 82944 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2010:11:18 16:27:32+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 16:27:32 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 9.20 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Nov-2010 16:27:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000143CA | 0x00014400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53688 |
.rdata | 0x00016000 | 0x00003CA6 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.04219 |
.data | 0x0001A000 | 0x0000292C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.44382 |
.sxdata | 0x0001D000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0001E000 | 0x00000A60 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.30387 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.44049 | 700 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.18403 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
500 | 3.09294 | 184 | UNKNOWN | English - United States | RT_DIALOG |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
65
Monitored processes
25
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1240 --field-trial-handle=1152,i,2506239805880447164,10102434516585616834,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=4108 --field-trial-handle=1152,i,2506239805880447164,10102434516585616834,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f1a8b38,0x6f1a8b48,0x6f1a8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1436 --field-trial-handle=1152,i,2506239805880447164,10102434516585616834,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\SignKorea\skcert\SKCertService.exe" | C:\Program Files\SignKorea\skcert\SKCertService.exe | SignKoreaWD.exe | ||||||||||||
User: admin Company: SignKorea Integrity Level: MEDIUM Description: SKCertService Exit code: 0 Version: 2.5.29.194 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\SignKorea\skcert\SantiagoWireInitializer.exe" S F C | C:\Program Files\SignKorea\skcert\SantiagoWireInitializer.exe | SKCertService.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\SKCertServiceSetup.exe" | C:\Users\admin\AppData\Local\Temp\SKCertServiceSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 3221226540 Version: 9.20 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3896 --field-trial-handle=1152,i,2506239805880447164,10102434516585616834,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4180 --field-trial-handle=1152,i,2506239805880447164,10102434516585616834,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1100 --field-trial-handle=1152,i,2506239805880447164,10102434516585616834,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
8 369
Read events
8 293
Write events
76
Delete events
0
Modification events
| (PID) Process: | (2488) SetupPKG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2488) SetupPKG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2488) SetupPKG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2488) SetupPKG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1548) SKCertService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1548) SKCertService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1548) SKCertService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1548) SKCertService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
44
Suspicious files
92
Text files
36
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\SignKorea\045445B0DE12C4279CA04F02698BD55B14146307_4128.der | der | |
MD5:5BFE0C9F3CB29500F663B4B7F836AA64 | SHA256:F3F56CD450922C6E770996AF7A7EF733D5A0ED2BCB451488B85025164C9A9492 | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\CrossCert\43D6F3657F659DCD6BC1CE730ABF3210A051E711_4126.der | der | |
MD5:78D9211607E40E4529A4EBD8950A5D65 | SHA256:1A37A4BB6A65E2E06466A250779D22DA2E90CD0C305FB057E78BD32A0111D237 | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\TradeSign\4D5D560A0703DF83CAF3D56D8F19FC12AC90A28A_4105.der | der | |
MD5:913113A4E0AE839CCA81C060475CD91F | SHA256:16AFC10A401DB5C68A50EAEDC76198757FD677CA20AA3F2FE6791C89F2C9B07F | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\CrossCert\0FD92CAF8B33B1B2B4F1151C9D786162E19B1427_10078.der | binary | |
MD5:61747C43532E687FACF06DE42565CB87 | SHA256:880FEBB841584F86C4BCC6C9FB54E6B4476605AD13A55F4532857621835B283D | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\KICA\AE52FD0E0E01F83086377EF618C649254A600970_4106.der | der | |
MD5:1D7A6ECDEAB591AE7628F7BEB53F3DD4 | SHA256:87E8D328C77923A2479932278725933D4674E2755B15A9AE8A014979B677BF34 | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\NCASign\766D8BCDAD940DF5A5B63F2202B6F59F4349398A_10045.der | der | |
MD5:C22F2264DE5188D95A27A1C36DDC6D0F | SHA256:D1717B6BF25F0063ECA79FDF523B8A3D07F7FEA4791E17ADC277C7485112DA54 | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\CrossCert\B674A99B923CC751B122A44FBCB73CFE2233D776_4100.der | der | |
MD5:EC746254751B75CC482DA57C8A3EAD02 | SHA256:E54153845DE915701251E84AF58A6F2B88FD3456A0A4655861F33C334B936DA5 | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\SignKorea\b063e7eba3dbd862c64427ff65e9316273a7c6cc_10043.der | der | |
MD5:872EC695399A2B23AC9B6FE2FC39E1ED | SHA256:275D74F432B613269738744D51DA94166C7E62F176D860050F84360DFB305448 | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\SignKorea\279696BEF384DC5901622423E2187BD3418D2D42_4098.der | der | |
MD5:0D3DD8492DA7764424902C30346A4EEF | SHA256:EFB2BAC7FDB49528B0ED679DBEF8C323FD42B472095192EBD94A9C3CA3AD54B6 | |||
| 2828 | SKCertServiceSetup.exe | C:\Users\admin\AppData\Local\Temp\7zS8B3F.tmp\NPKI\yessign\4AFBBD332D8BB1D18C946BFFE042365F1C91CB08_10080.der | der | |
MD5:3C358D13A20A45F6E879030550E35844 | SHA256:7C48FD35F6ABA2B1980E0DC0C041BEFA56A01D805A45A27DF44EECF182F4D881 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
20
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1052 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1052 | chrome.exe | 142.250.186.45:443 | accounts.google.com | GOOGLE | US | suspicious |
3576 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1052 | chrome.exe | 216.58.206.36:443 | www.google.com | GOOGLE | US | whitelisted |
1052 | chrome.exe | 142.250.185.99:443 | update.googleapis.com | GOOGLE | US | whitelisted |
1052 | chrome.exe | 142.250.185.206:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
3576 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1052 | chrome.exe | 216.58.206.35:443 | www.gstatic.com | GOOGLE | US | whitelisted |
1052 | chrome.exe | 142.250.185.106:443 | optimizationguide-pa.googleapis.com | GOOGLE | US | whitelisted |
1052 | chrome.exe | 216.58.212.129:443 | lh5.googleusercontent.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
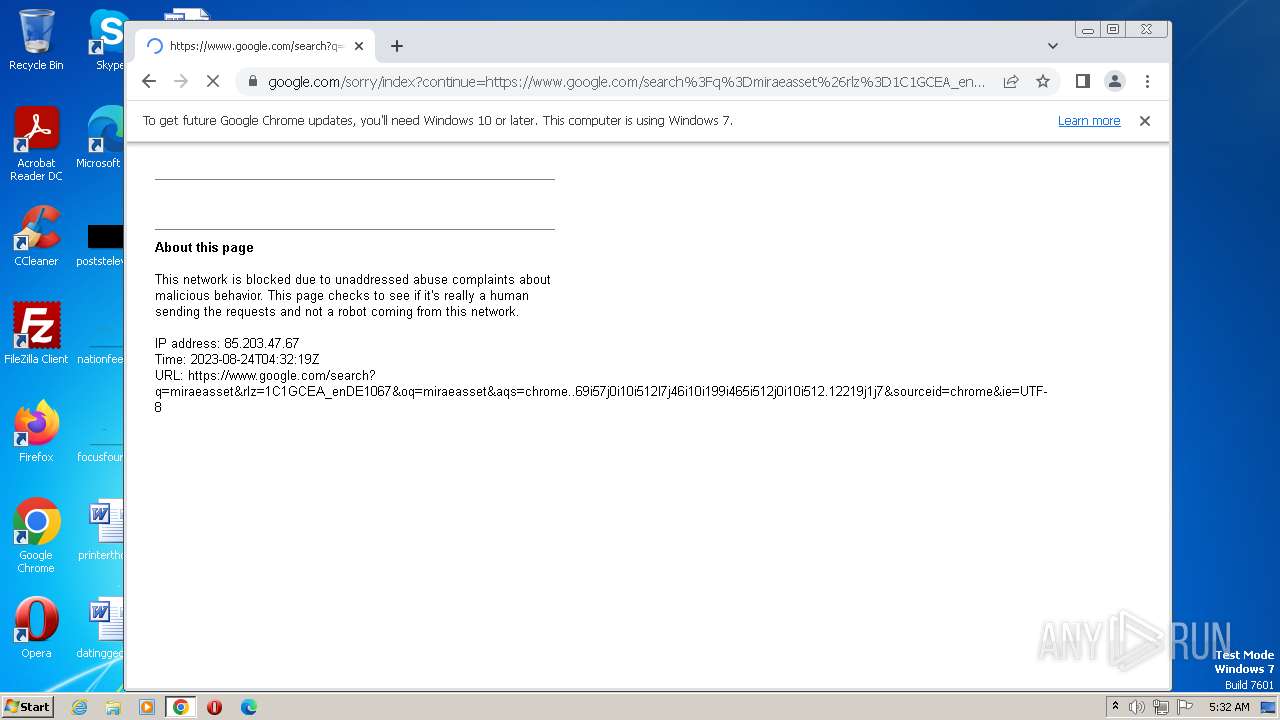
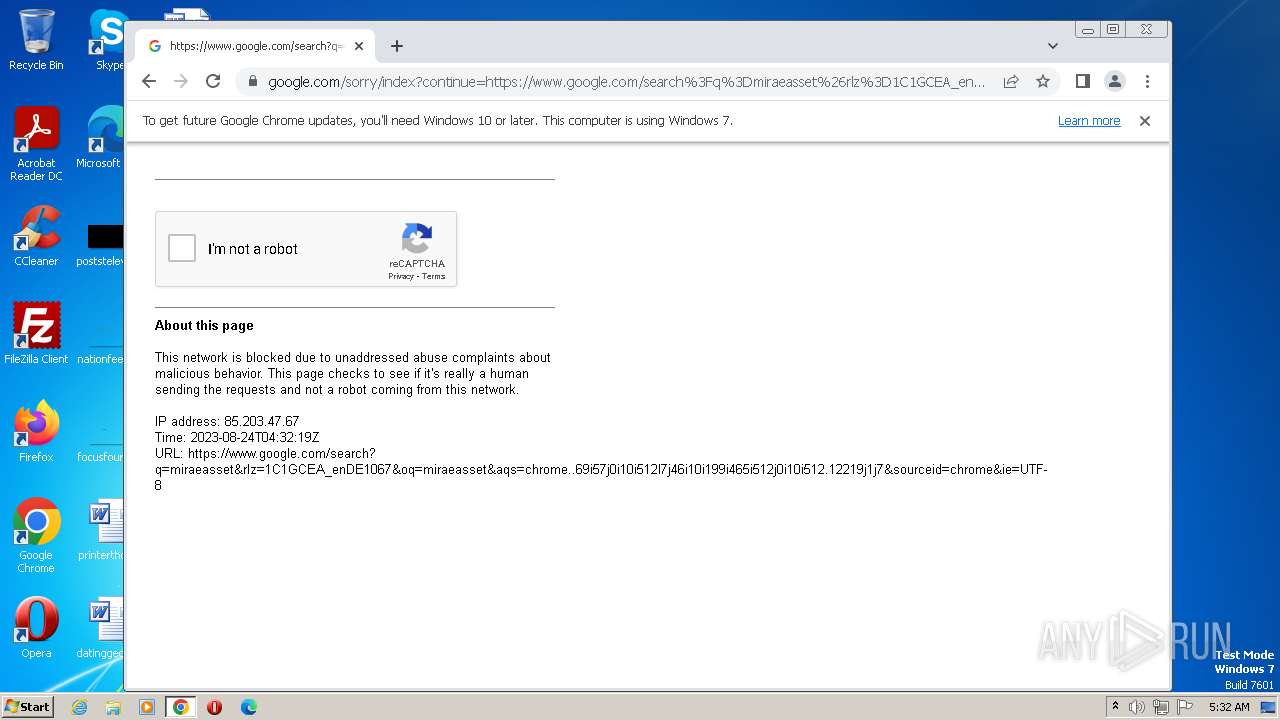
www.google.com |
| malicious |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
SignKoreaWD.exe | TID:001444( INFO) PipeMonitor run.. |
SignKoreaWD.exe | TID:001496( INFO) SKCertService is not alive |