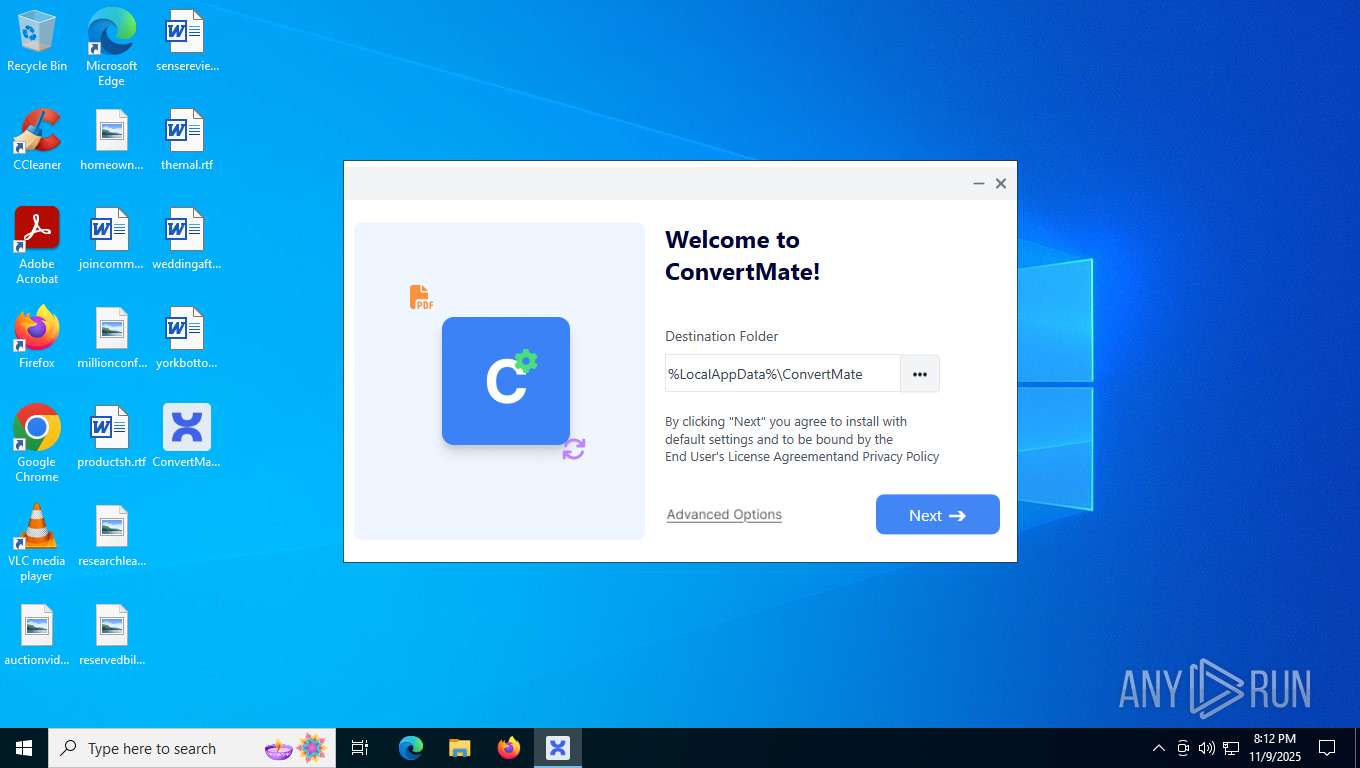
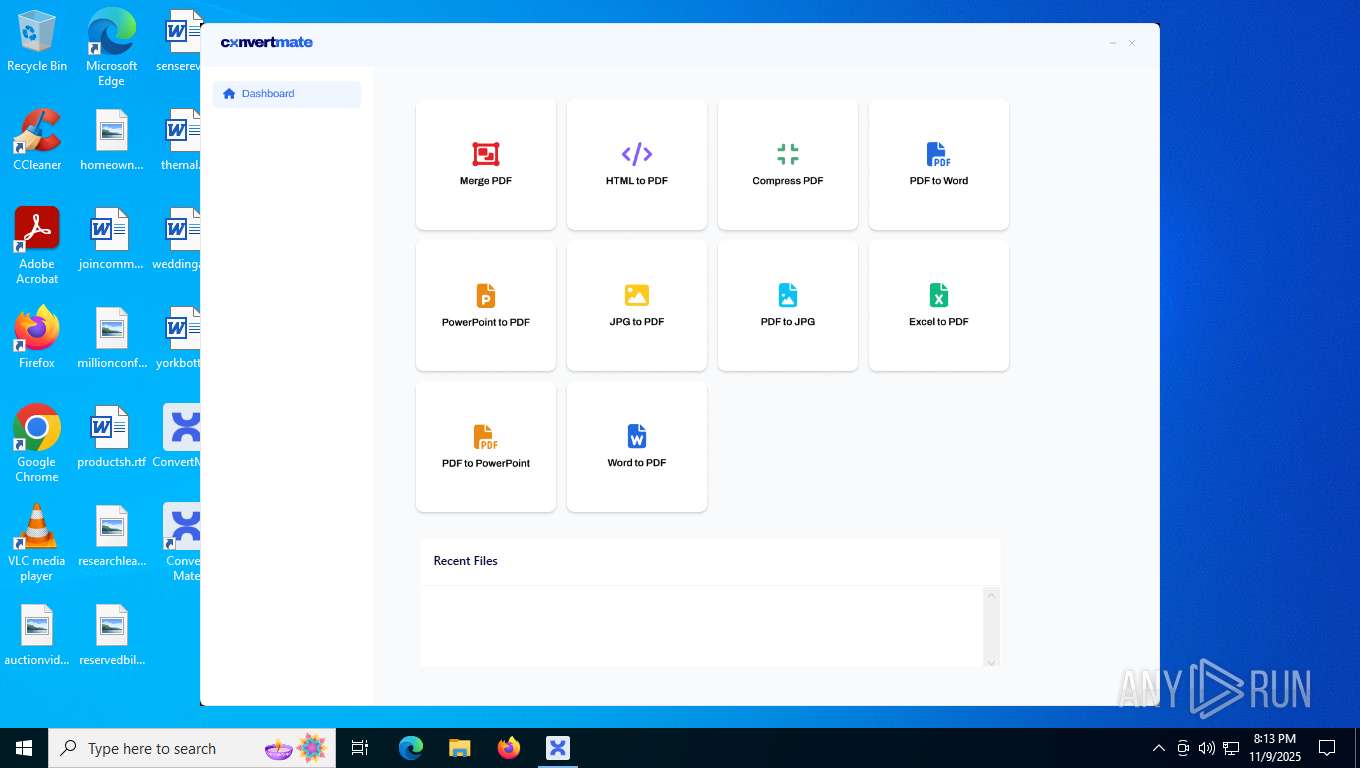
| File name: | ConvertMate.exe |
| Full analysis: | https://app.any.run/tasks/0be43654-1a19-4836-a47a-9b6076047500 |
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2025, 20:12:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | FCEE986BDE6FBDAC75CA8DCC7E07B7DA |
| SHA1: | 1B8668ED667AC01CC11A61210A991FA974D2B0A0 |
| SHA256: | 7744B67501A840BA687C641B01E9924D40A034B02582E0F233174E11A85480D3 |
| SSDEEP: | 98304:HqJam/AdVa2OH7/qC3DkDr9ac1rALT/VHrr4+uh4Nn9bprVBa091RFS6Nb6F5o8o:Hyi5ZrpavIw |
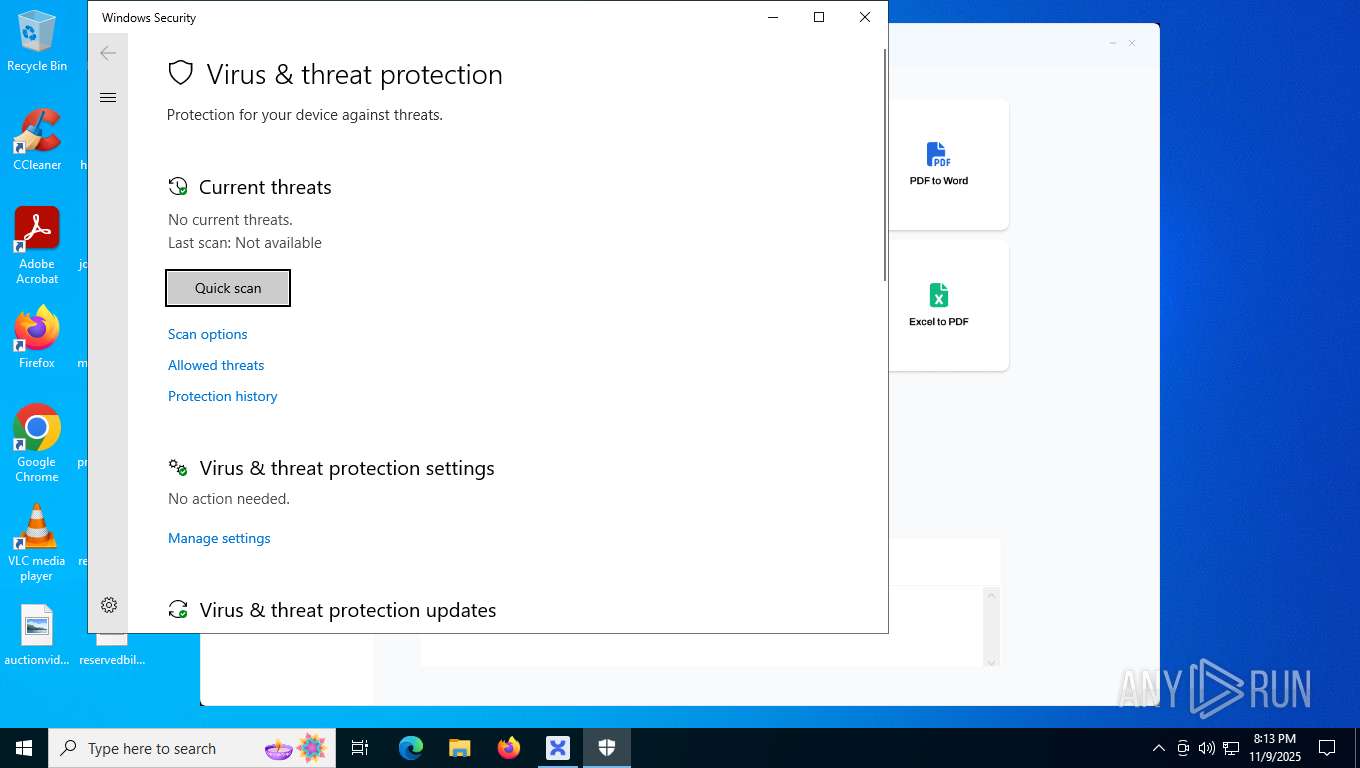
MALICIOUS
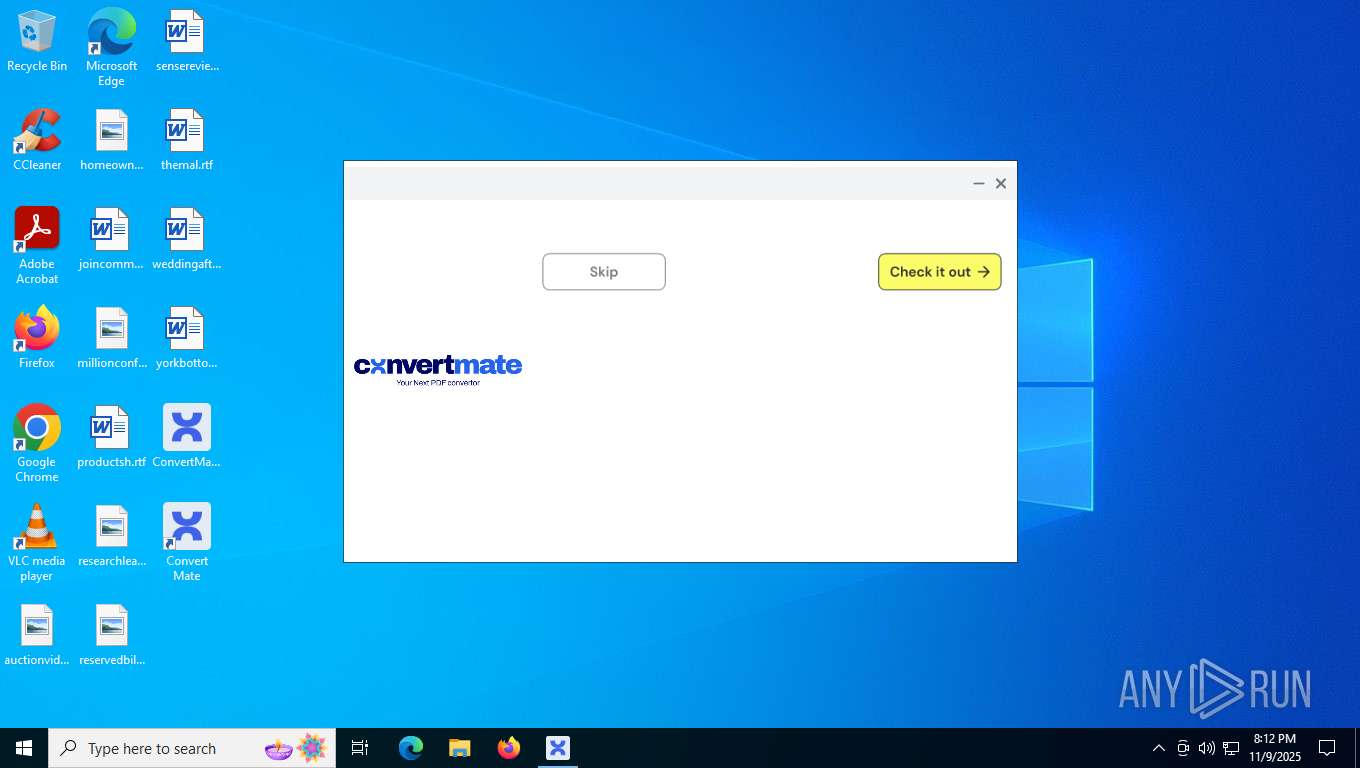
Changes powershell execution policy (RemoteSigned)
- ConvertMate.exe (PID: 7284)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- ConvertMate.exe (PID: 7284)
Process drops legitimate windows executable
- ConvertMate.exe (PID: 7284)
SQL CE related mutex has been found
- ConvertMate.exe (PID: 7284)
Reads the date of Windows installation
- ConvertMate.exe (PID: 7284)
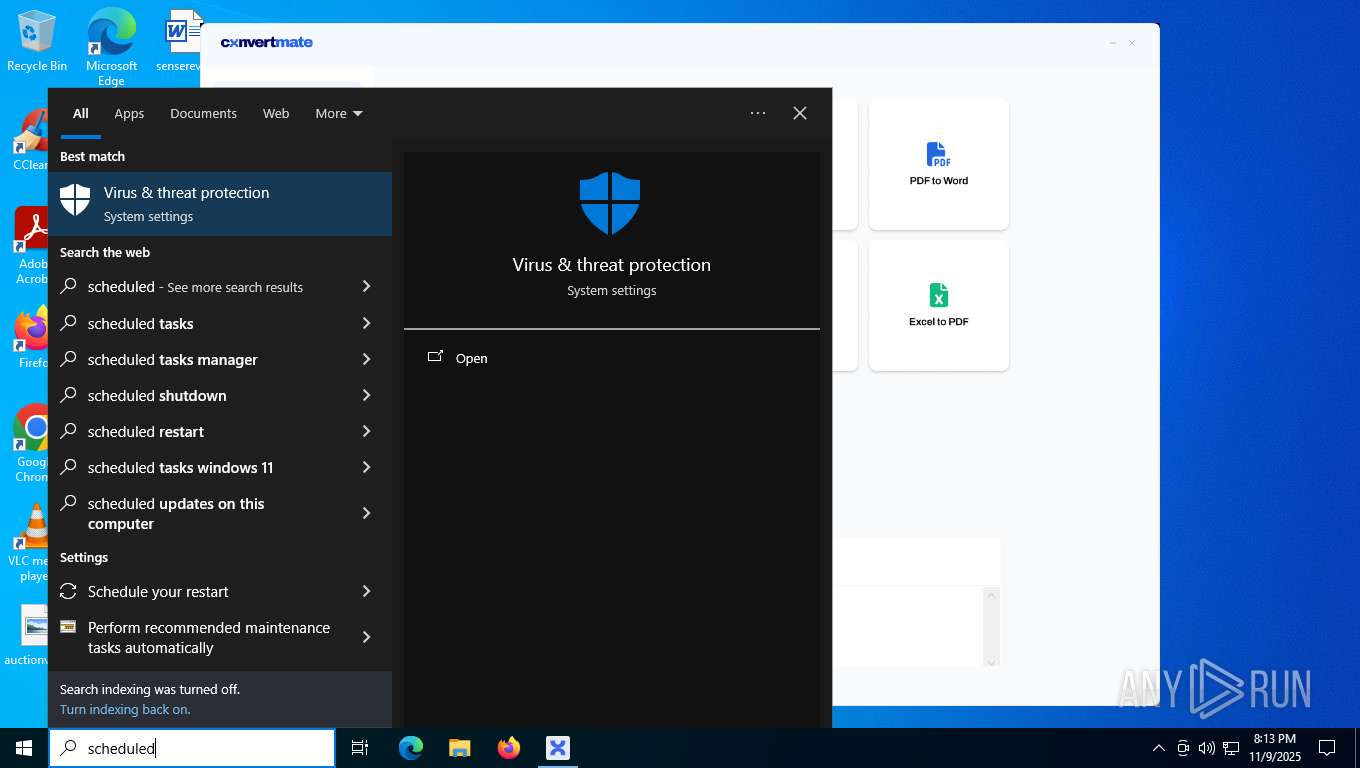
Reads security settings of Internet Explorer
- SecHealthUI.exe (PID: 5304)
- Convert Mate.exe (PID: 8072)
- ConvertMate.exe (PID: 7284)
Executable content was dropped or overwritten
- ConvertMate.exe (PID: 7284)
The process executes Powershell scripts
- ConvertMate.exe (PID: 7284)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7564)
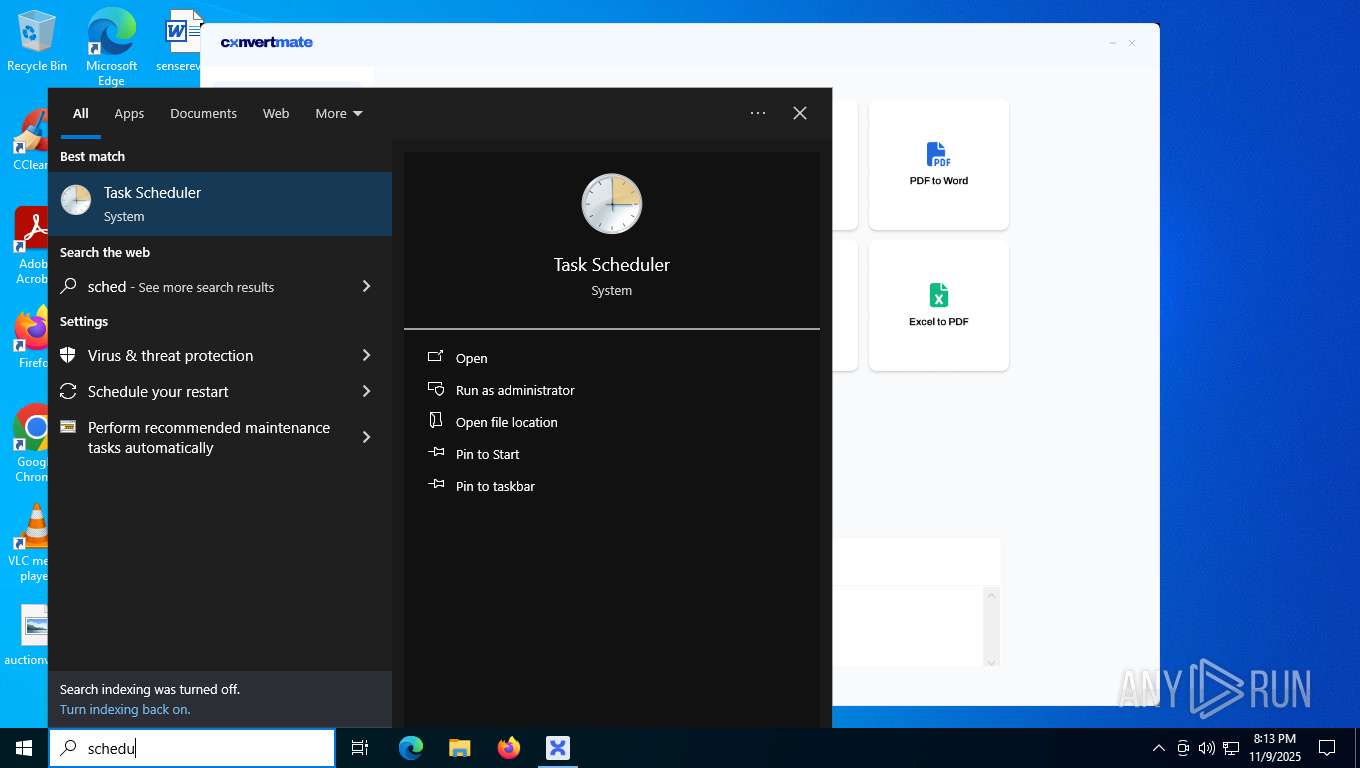
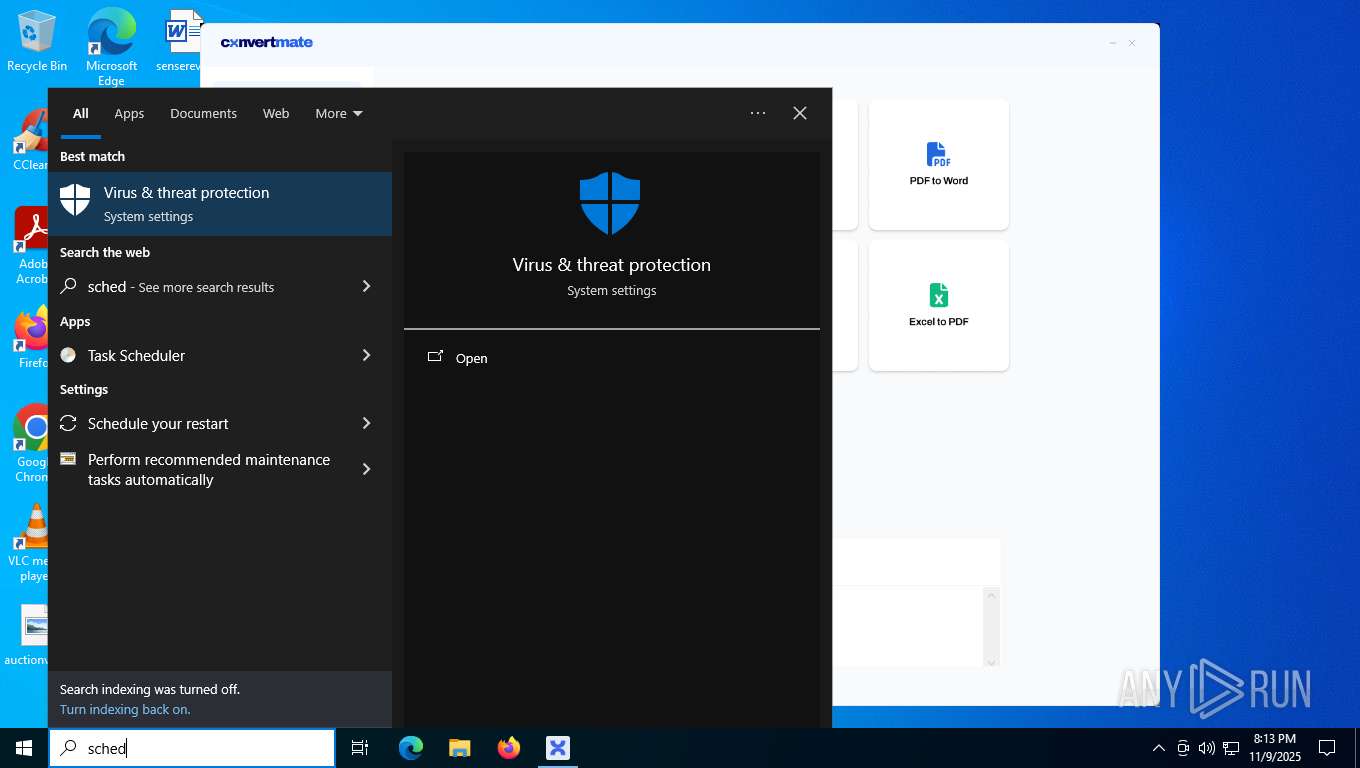
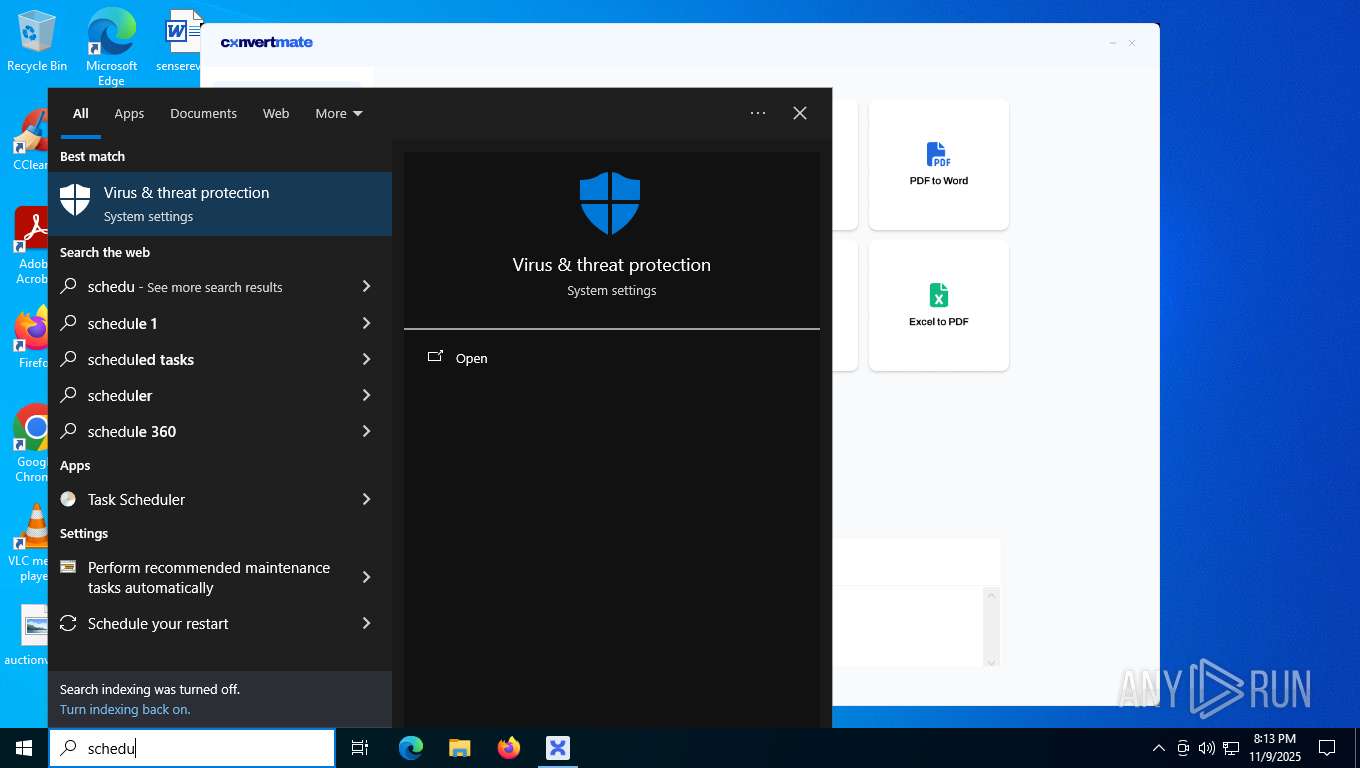
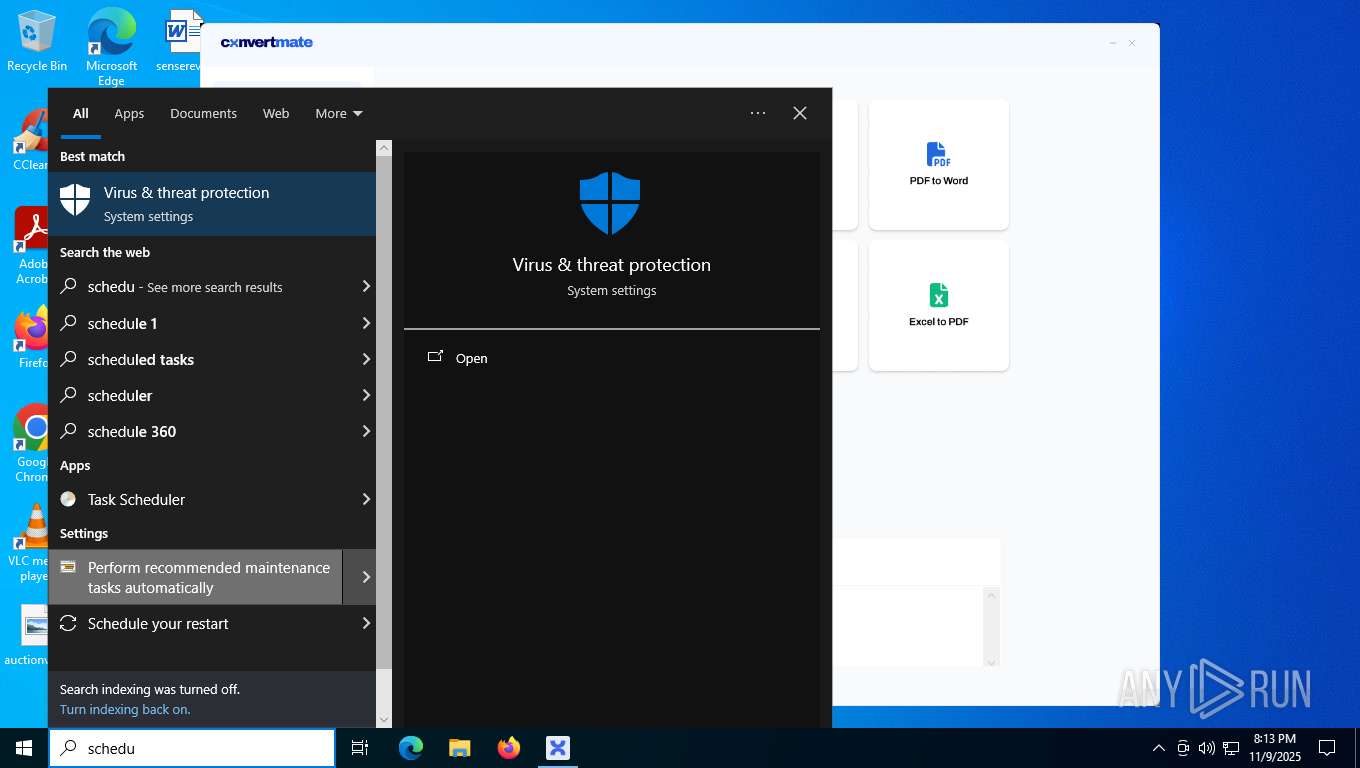
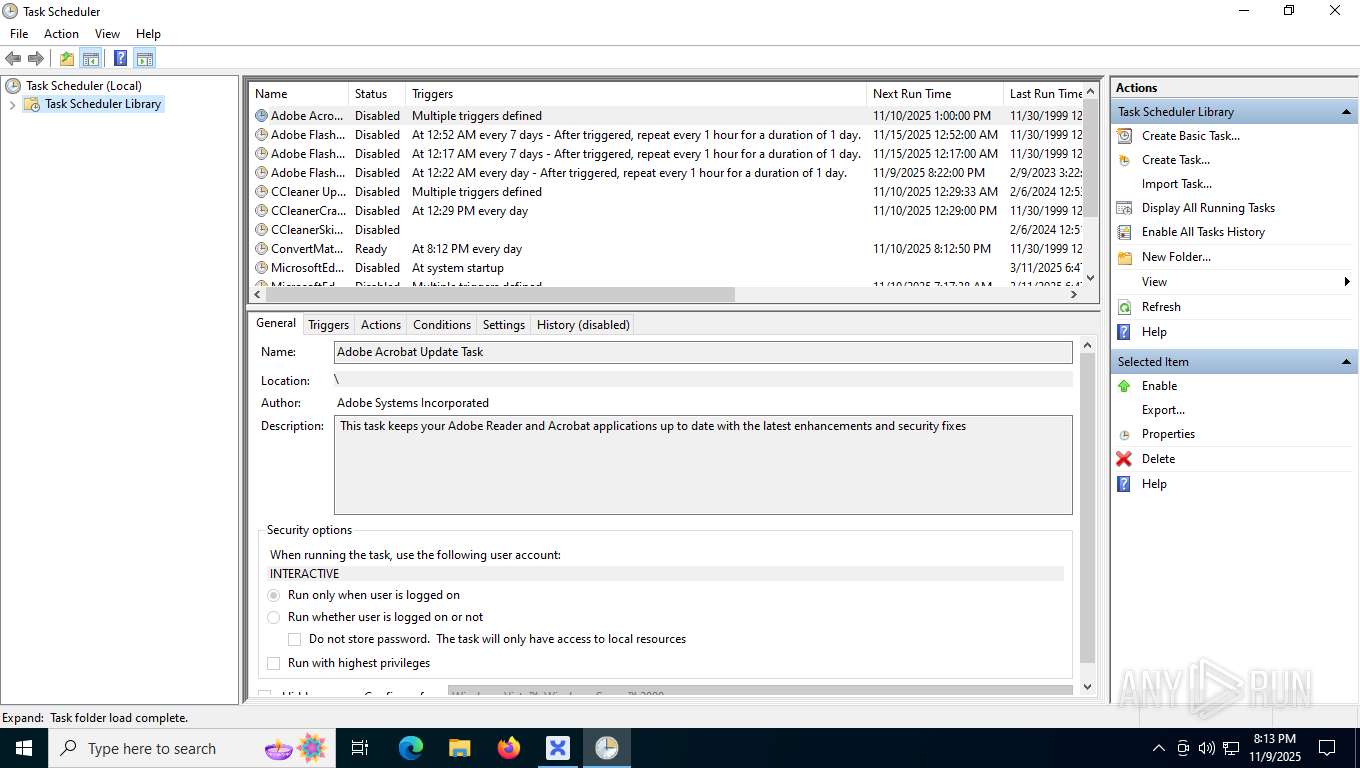
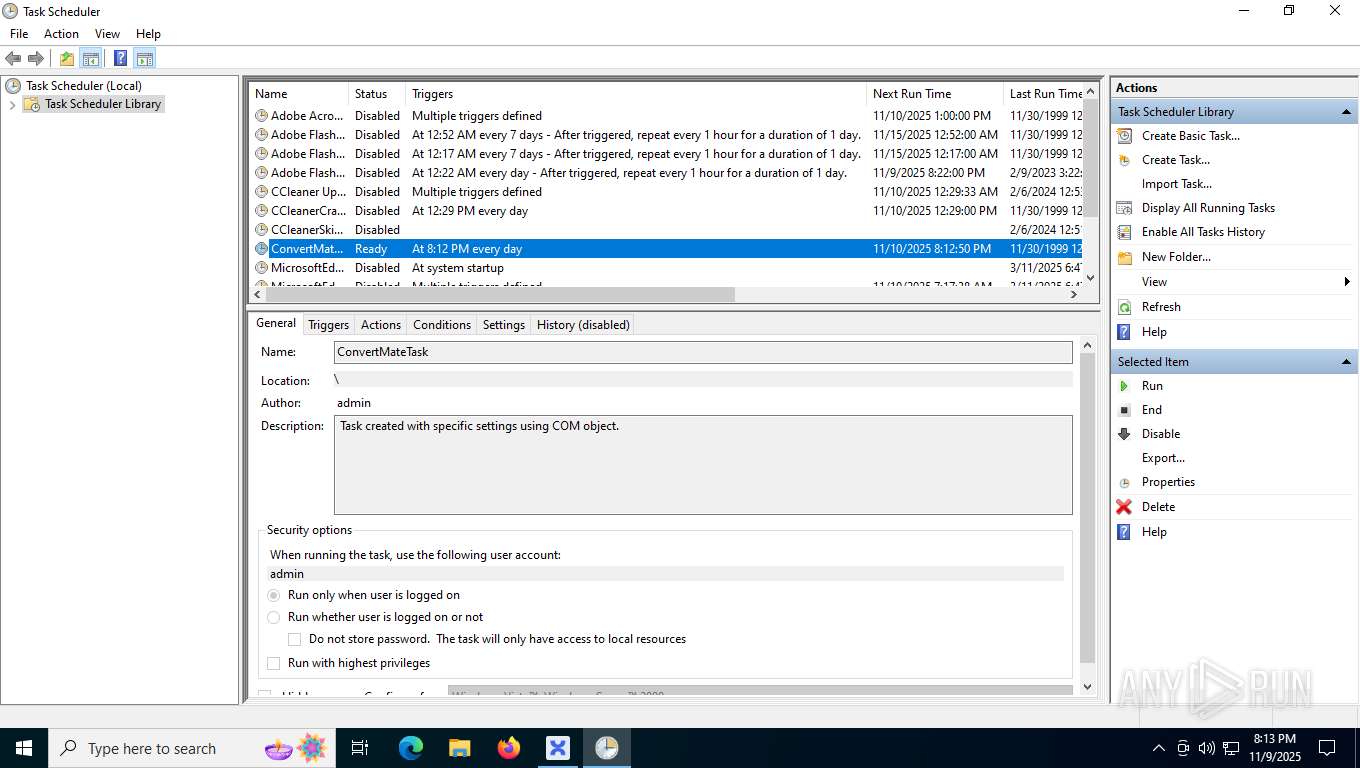
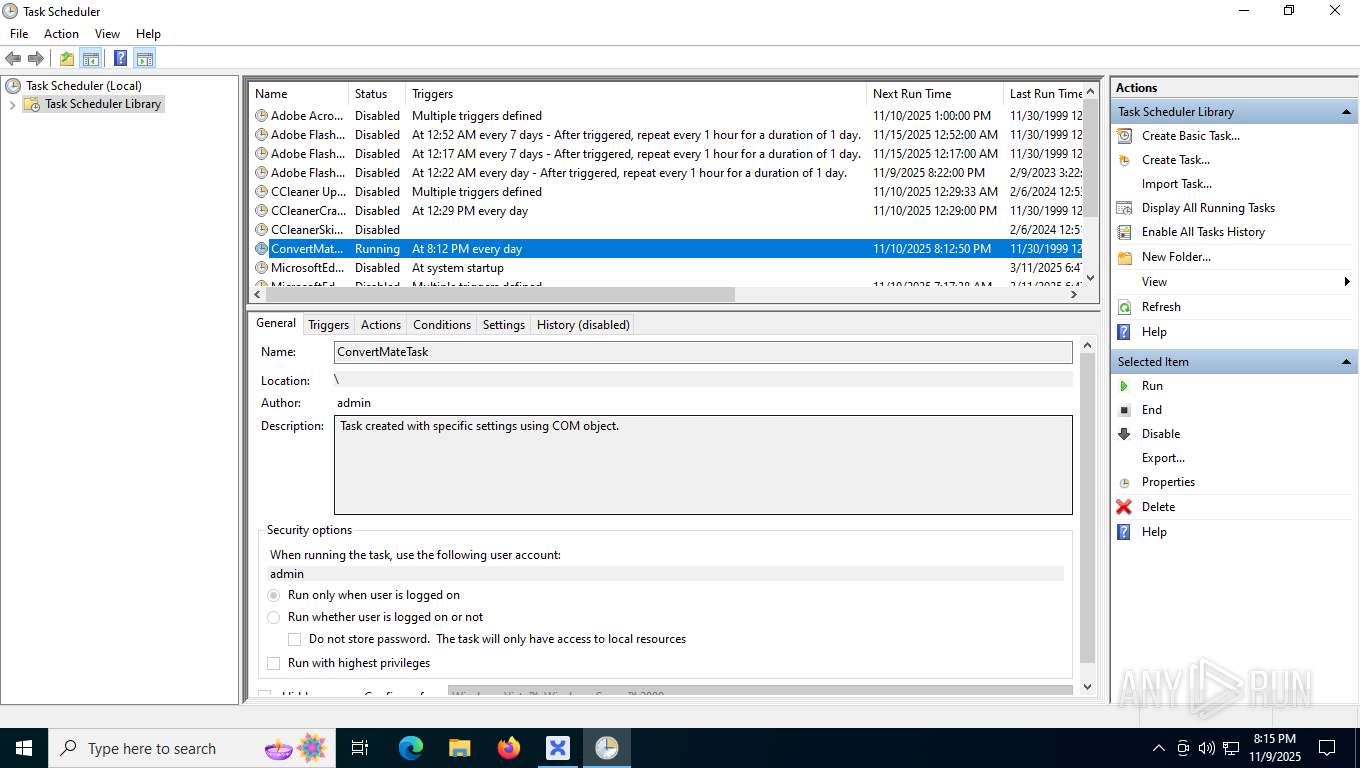
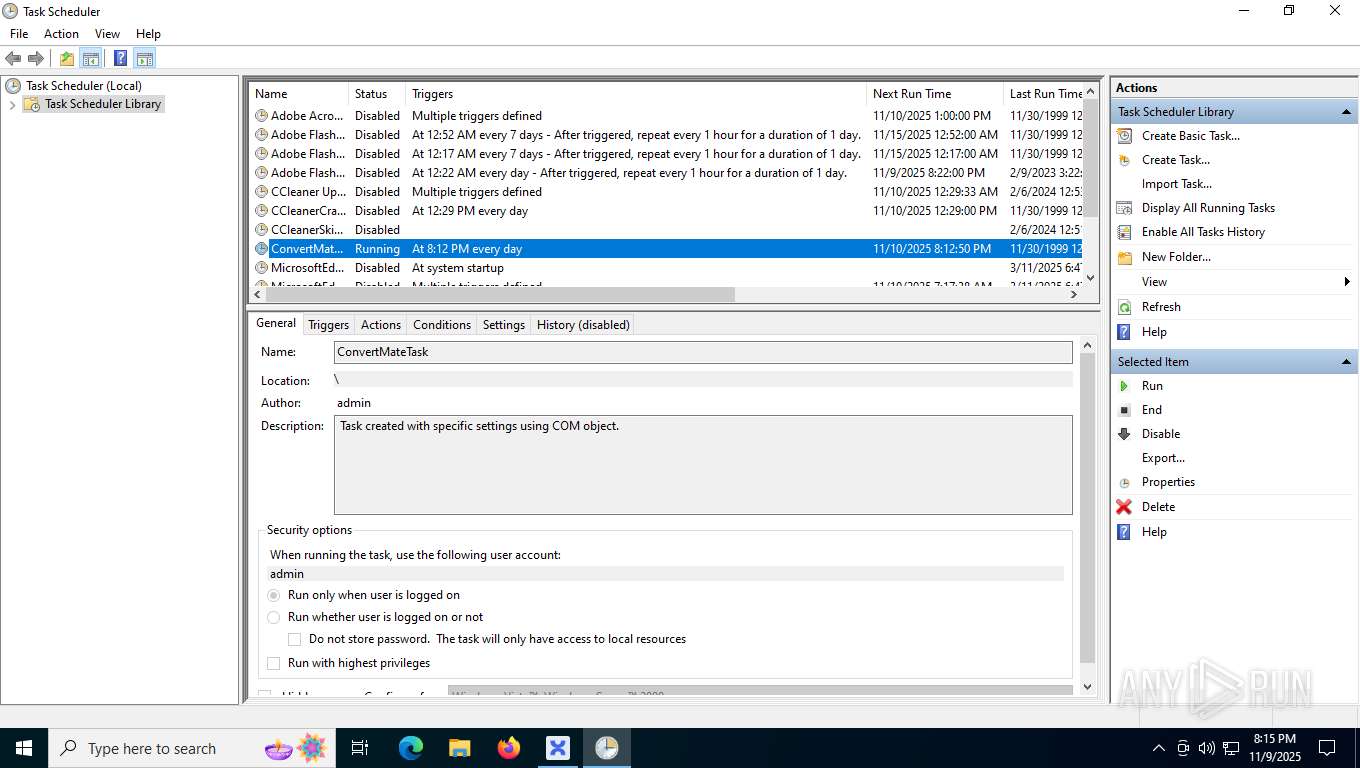
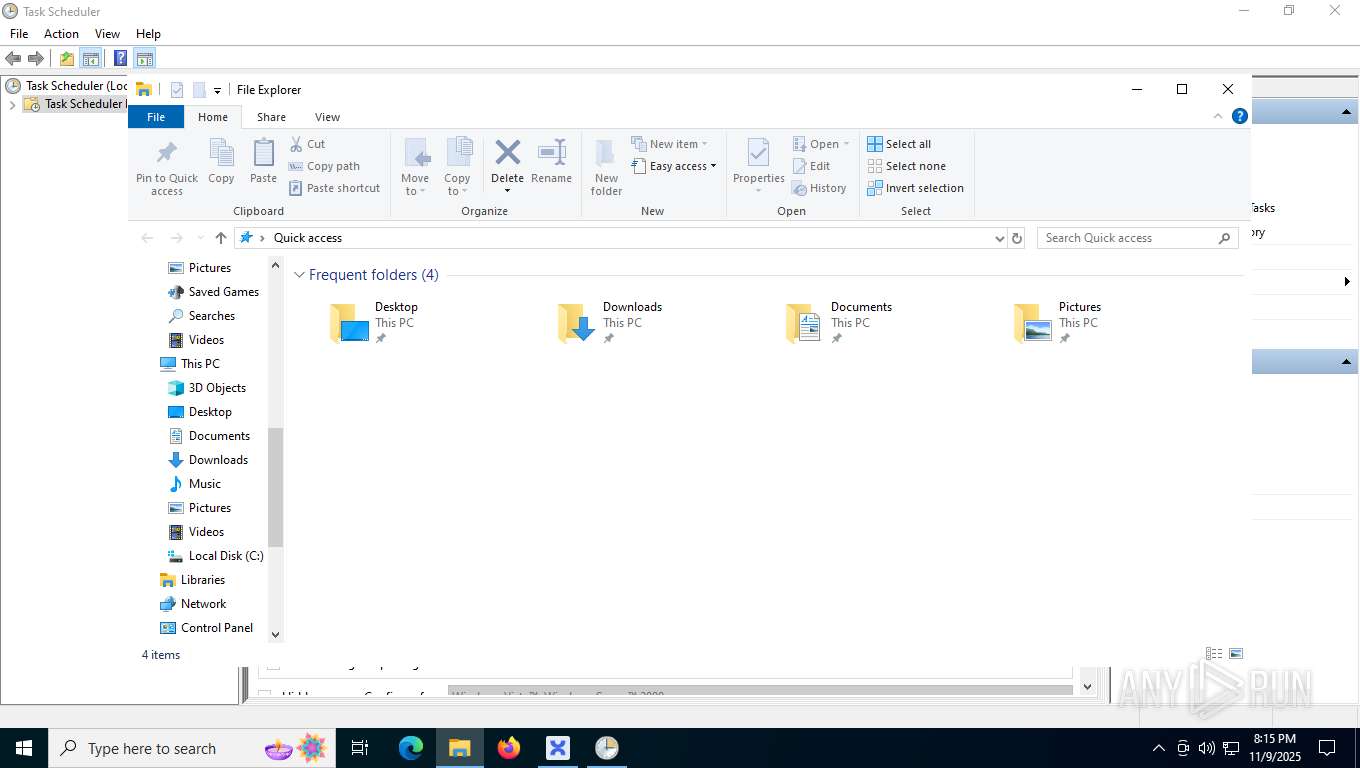
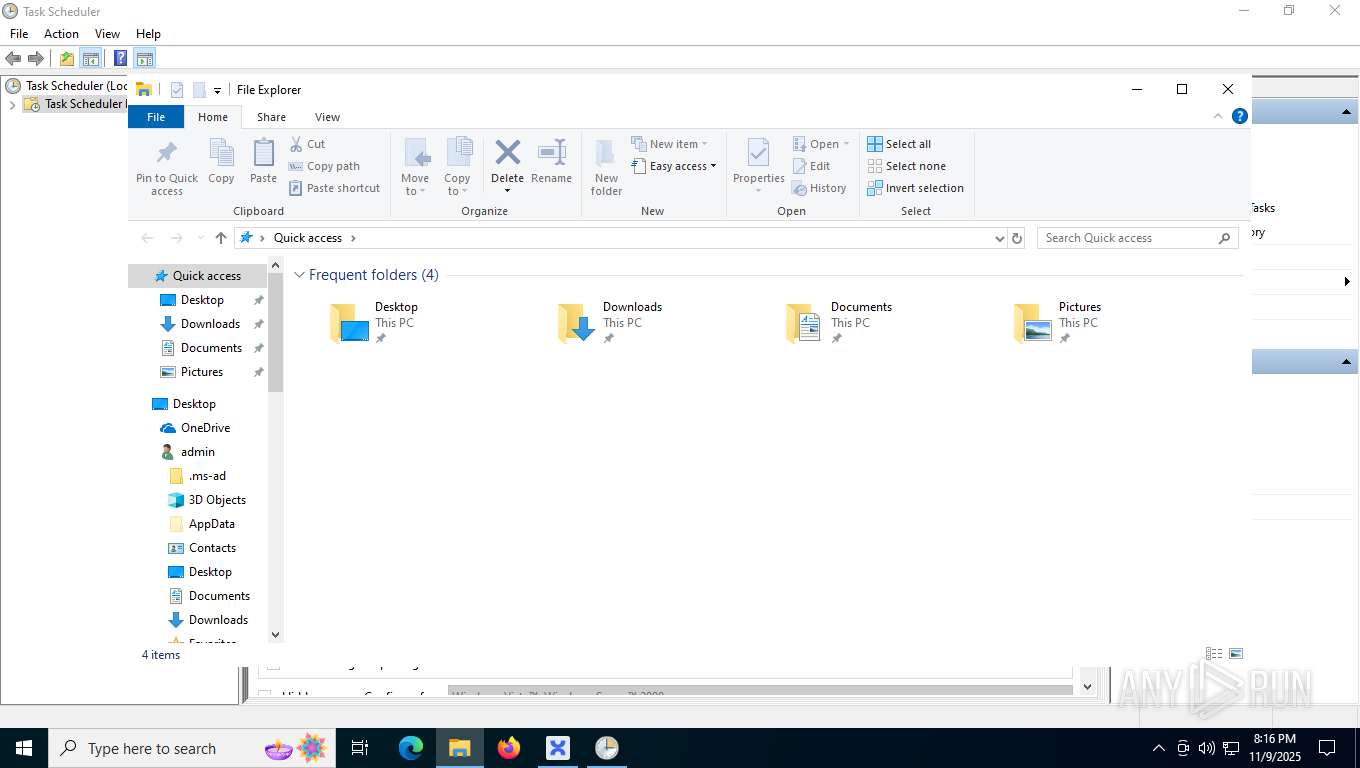
The process executes via Task Scheduler
- UpdateRetreiver.exe (PID: 5656)
INFO
Checks supported languages
- ConvertMate.exe (PID: 7284)
- Convert Mate.exe (PID: 8072)
- SecHealthUI.exe (PID: 5304)
- UpdateRetreiver.exe (PID: 5656)
Reads the software policy settings
- ConvertMate.exe (PID: 7284)
- UpdateRetreiver.exe (PID: 5656)
- slui.exe (PID: 6044)
Reads the machine GUID from the registry
- ConvertMate.exe (PID: 7284)
- Convert Mate.exe (PID: 8072)
- UpdateRetreiver.exe (PID: 5656)
Reads the computer name
- ConvertMate.exe (PID: 7284)
- Convert Mate.exe (PID: 8072)
- SecHealthUI.exe (PID: 5304)
- UpdateRetreiver.exe (PID: 5656)
Checks proxy server information
- ConvertMate.exe (PID: 7284)
- UpdateRetreiver.exe (PID: 5656)
- slui.exe (PID: 6044)
Reads Environment values
- ConvertMate.exe (PID: 7284)
- UpdateRetreiver.exe (PID: 5656)
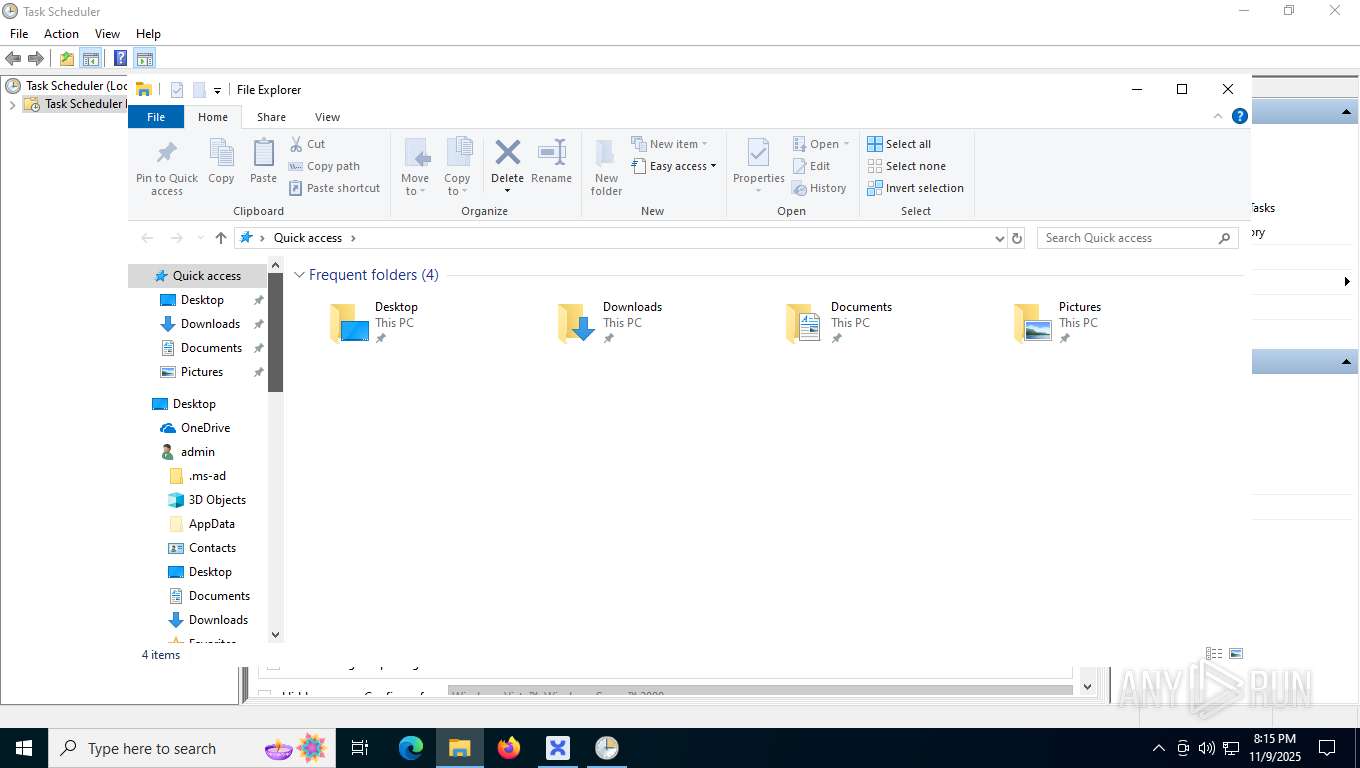
Creates files or folders in the user directory
- ConvertMate.exe (PID: 7284)
Disables trace logs
- ConvertMate.exe (PID: 7284)
- UpdateRetreiver.exe (PID: 5656)
Create files in a temporary directory
- ConvertMate.exe (PID: 7284)
Process checks computer location settings
- ConvertMate.exe (PID: 7284)
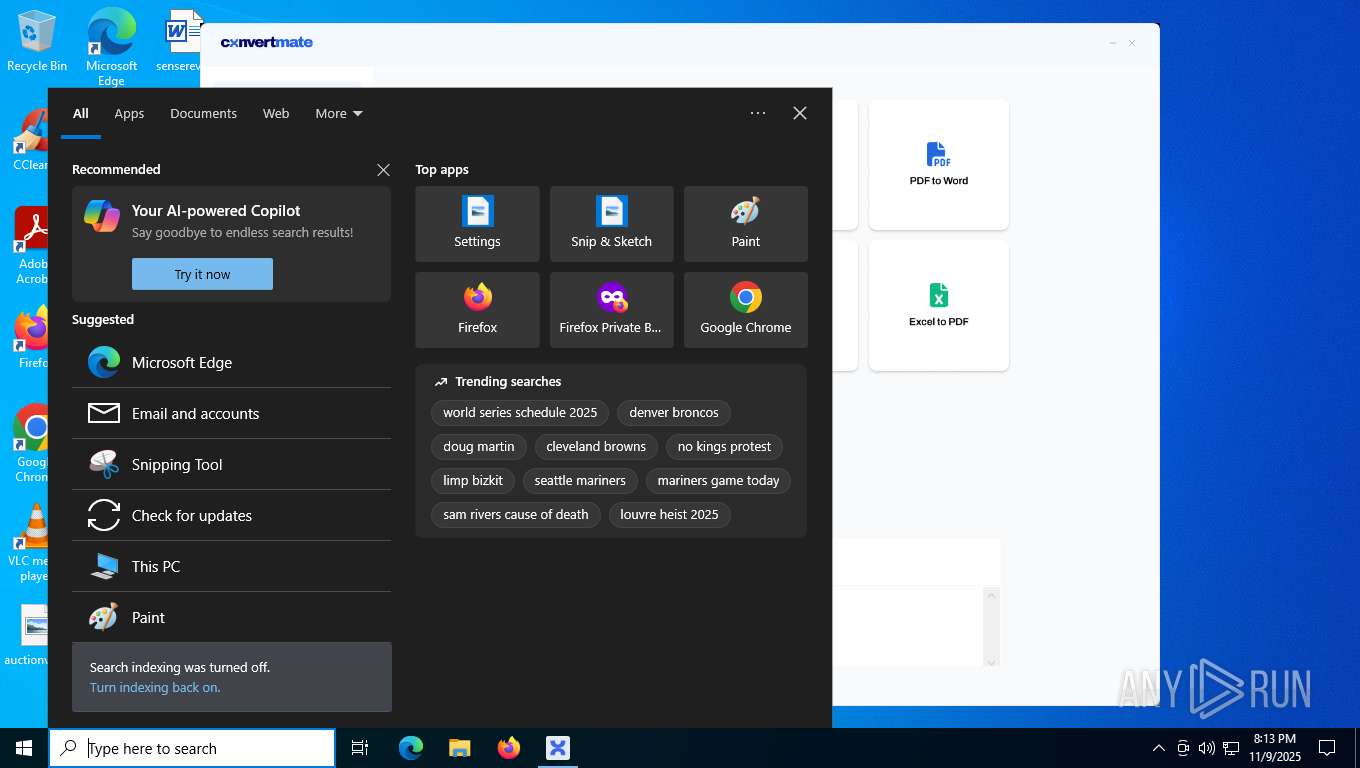
Manual execution by a user
- mmc.exe (PID: 7536)
- mmc.exe (PID: 1384)
Reads security settings of Internet Explorer
- mmc.exe (PID: 1384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2082:10:31 11:46:13+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 7757312 |
| InitializedDataSize: | 17408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.1.2.1002 |
| ProductVersionNumber: | 12.1.2.1002 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
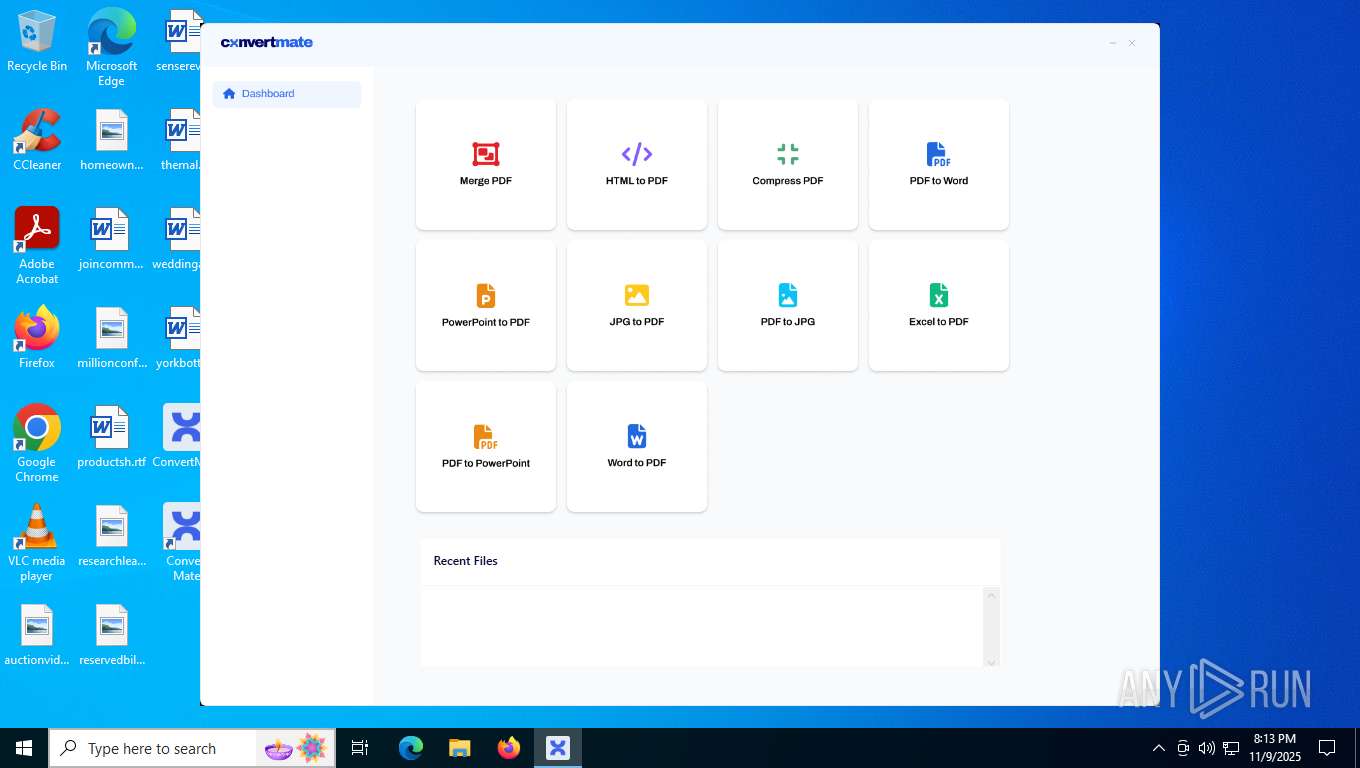
| FileDescription: | ConvertMate |
| FileVersion: | 12.1.2.1002 |
| InternalName: | ConvertMate.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | ConvertMate.exe |
| ProductName: | ConvertMate |
| ProductVersion: | 12.1.2.1002 |
| AssemblyVersion: | 12.1.2.1002 |
Total processes
165
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1384 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
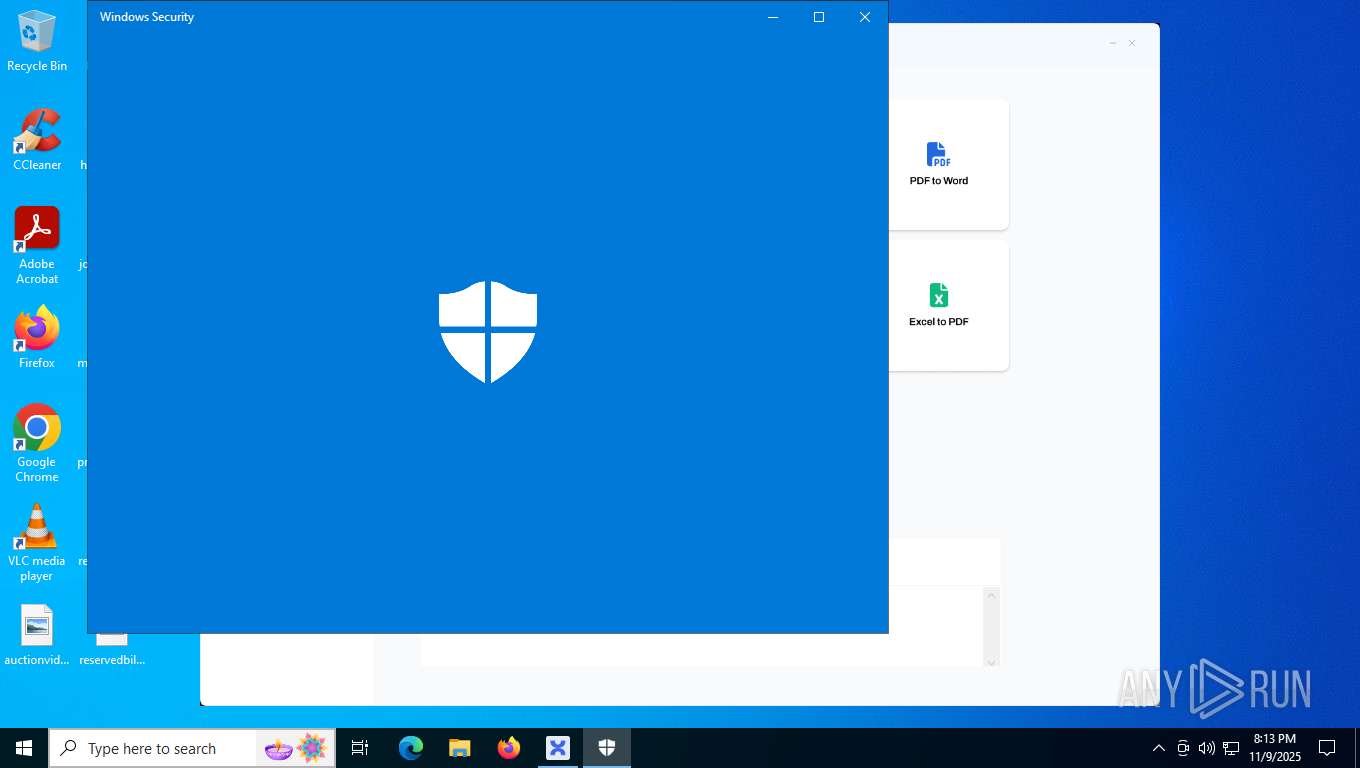
| 5304 | "C:\WINDOWS\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe" -ServerName:SecHealthUI.AppXep4x2tbtjws1v9qqs0rmb3hxykvkpqtn.mca | C:\Windows\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender application Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5656 | "C:\Users\admin\AppData\Local\ConvertMate\UpdateRetreiver.exe" | C:\Users\admin\AppData\Local\ConvertMate\UpdateRetreiver.exe | svchost.exe | ||||||||||||
User: admin Company: UpdateRetreiver Integrity Level: MEDIUM Description: UpdateRetreiver Exit code: 0 Version: 12.0.0.1002 Modules
| |||||||||||||||
| 6044 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7284 | "C:\Users\admin\Desktop\ConvertMate.exe" | C:\Users\admin\Desktop\ConvertMate.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ConvertMate Exit code: 0 Version: 12.1.2.1002 Modules
| |||||||||||||||
| 7536 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7564 | "powershell.exe" -ep RemoteSigned -File "C:\Users\admin\AppData\Local\ConvertMate\conmate_update.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ConvertMate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7752 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 659
Read events
14 562
Write events
95
Delete events
2
Modification events
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7284) ConvertMate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ConvertMate_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
5
Suspicious files
7
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | xml | |
MD5:90BE2701C8112BEBC6BD58A7DE19846E | SHA256:644FBCDC20086E16D57F31C5BAD98BE68D02B1C061938D2F5F91CBE88C871FBF | |||
| 7564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fiyxeds5.olj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\Microsoft\Media Player\LocalMLS_3.wmdb | binary | |
MD5:73C1475B93D217F339D144F6FA24DADD | SHA256:8AAC2360BBA2E14B2D302DD3B0365F6E82E9626525DEF6828B3745F11F68352A | |||
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\id.txt | text | |
MD5:E5EB761BDA19D8C2E915DF7E2E5871E7 | SHA256:BE51B5428C90ECC8770988F2AF975F8152526ADE96290997E9BEDBB14F47EA4E | |||
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\conmate_update.ps1 | text | |
MD5:F882CF611AB98EB285086706E4A4A567 | SHA256:A5DA5AD1532885EDBCAFA60838C8457BA83C3A5738837A3D091BEBEBDC151557 | |||
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\UpdateRetreiver.exe | executable | |
MD5:8AF38C01F2AD49F7927F80940755BB4C | SHA256:7DD4A34DB2C1EFB425254E7D311F008275489B2A7A1DDD679850D7A11223CBE2 | |||
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\Temp\video.mp4 | binary | |
MD5:F23E33FA595FFE6651EEDC80F89B2415 | SHA256:0B2F6EACA78D898D26E183EFE4E514CD81526A13DF1AF38F712DBE0CB22B742B | |||
| 7284 | ConvertMate.exe | C:\Users\admin\AppData\Local\ConvertMate\StructureV10Logic.Assets.favicon.ico | image | |
MD5:F75D7A5431CFE6F4E2E0DDF692629F72 | SHA256:29BFA4D992ECE56289664FE492A9ACDF7B07092A0A0DA0B5D049C070893463FC | |||
| 7284 | ConvertMate.exe | C:\Users\admin\Desktop\Convert Mate.lnk | binary | |
MD5:880993616B1917EA39B7732A40A5D33B | SHA256:F9F200D797D1FC19836F696D9574E7DE56157FFDB69C6E85BD6A277CBA334F47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
58
DNS requests
30
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4916 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | whitelisted |
6752 | svchost.exe | GET | 200 | 2.16.168.200:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
8004 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
8004 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
8004 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 402 b | whitelisted |
8004 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
7088 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7088 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRQYDQ9OzS3QItbZP0dCcU0b%2Fgz8gQUw16sQHbABk3jK5SZMGBzNJgpxlECEzMAAzbSUUMXa%2BvUXxwAAAADNtI%3D | US | binary | 5 b | whitelisted |
7088 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEA8fFXWCzc0zc0vcX82UGjM%3D | DE | binary | 314 b | whitelisted |
7088 | SearchApp.exe | POST | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp | US | binary | 1.02 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6752 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2116 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7088 | SearchApp.exe | 2.16.204.141:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7284 | ConvertMate.exe | 104.18.25.125:443 | climatcon.com | CLOUDFLARENET | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4916 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4916 | svchost.exe | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | — | whitelisted |
6752 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
climatcon.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | A Network Trojan was detected | ET MALWARE Trojan-Dropper.MSIL CnC Traffic - POST |
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|