| File name: | install_backblaze_512ffe191c8ceb07c.exe |
| Full analysis: | https://app.any.run/tasks/9db6406c-66e8-4d7e-84c3-38b381d2fe31 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2024, 19:19:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AE54E052659116F06DA71C2B326B1BE3 |
| SHA1: | 07EB40D4B2BDD054FA04B61919B51A93C7214907 |
| SHA256: | 7744A41DBB9D90DDA5347D2B426F6B05DC86B8DF2ABA148F85F18AC46D0418FD |
| SSDEEP: | 393216:cWiYrugV4SGtkjSshhOFLGjMRdPNZgQhkMo:XruE4YjSwIFEI+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
Executable content was dropped or overwritten
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
The process drops C-runtime libraries
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
INFO
Create files in a temporary directory
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
Creates files in the program directory
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
Reads product name
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
Checks supported languages
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
Reads Environment values
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
Reads the computer name
- install_backblaze_512ffe191c8ceb07c.exe (PID: 6612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:04:12 18:53:32+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 273408 |
| InitializedDataSize: | 173056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1405d |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.1.777 |
| ProductVersionNumber: | 9.0.1.777 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Backblaze |
| FileDescription: | - |
| FileVersion: | 9.0.1.777 |
| LegalCopyright: | Copyright © 2007-2024. Backblaze |
| ProductName: | Backblaze Backup |
| ProductVersion: | 9.0.1.777 |
Total processes
124
Monitored processes
9
Malicious processes
1
Suspicious processes
0
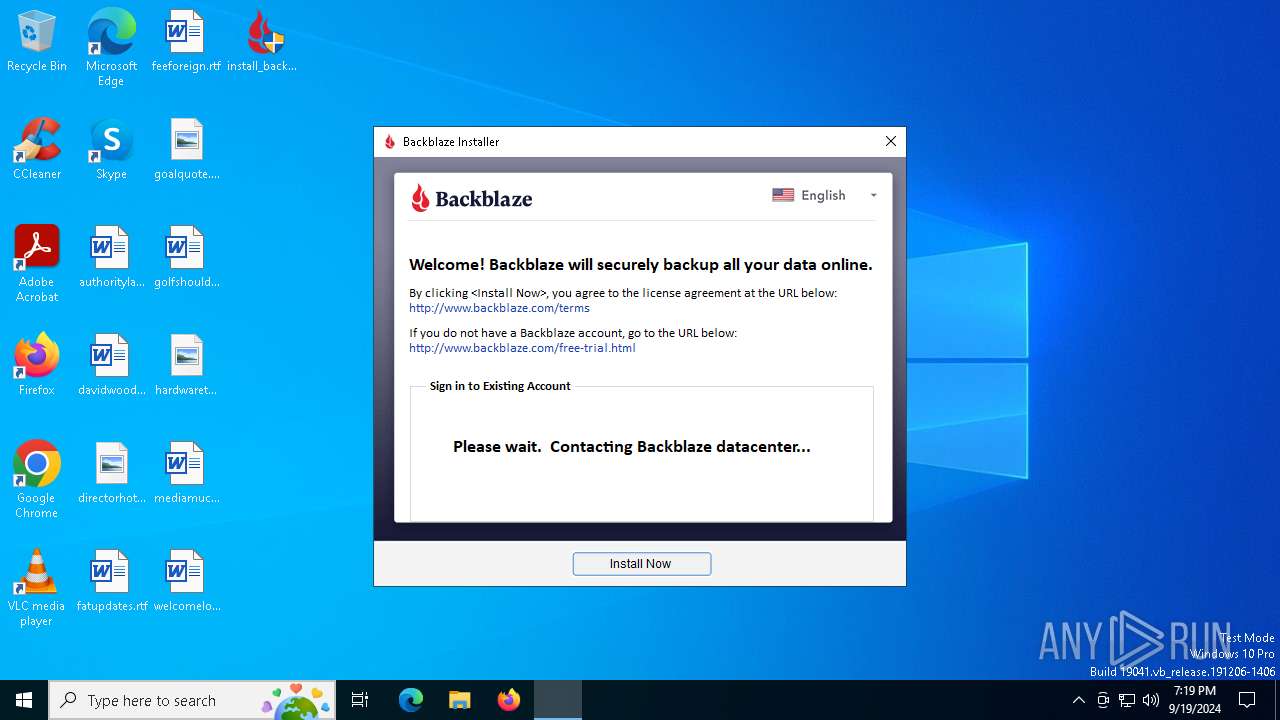
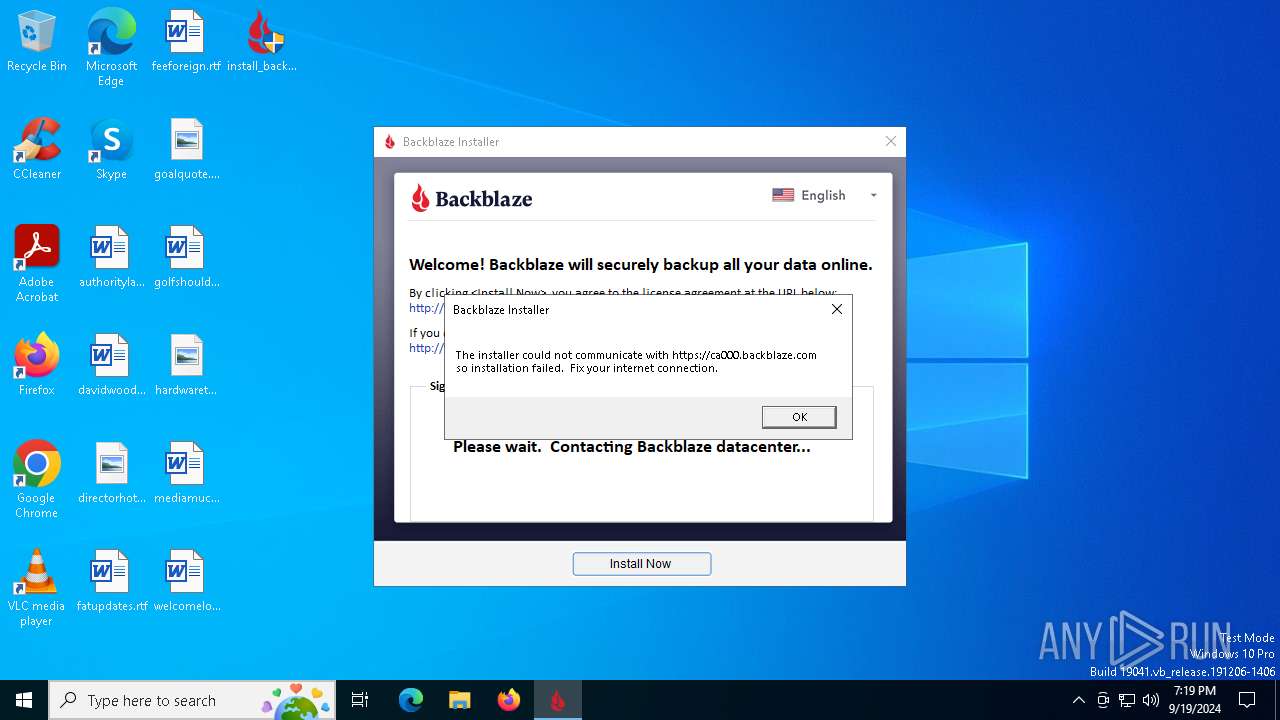
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | "C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit.exe" -fetchurltofile https://ca000.backblaze.com/api/clientversion.xml "C:\Users\admin\AppData\Local\Temp\bzt0919191948_0000001_5497_0007140.txt" | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit.exe | bzdoinstall.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit.exe" -fetchurltofile https://ca001.backblaze.com/api/clientversion.xml "C:\Users\admin\AppData\Local\Temp\bzt0919191948_0000002_5651_0007140.txt" | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit.exe | bzdoinstall.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit.exe" -at_install_time_checkuser https://ca000.backblaze.com 353132666665313931633863 | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit.exe | bzdoinstall.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | bztransmit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5996 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | bztransmit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6436 | "C:\Users\admin\Desktop\install_backblaze_512ffe191c8ceb07c.exe" | C:\Users\admin\Desktop\install_backblaze_512ffe191c8ceb07c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6612 | "C:\Users\admin\Desktop\install_backblaze_512ffe191c8ceb07c.exe" | C:\Users\admin\Desktop\install_backblaze_512ffe191c8ceb07c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6704 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | bztransmit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7140 | "C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzdoinstall.exe" -doinstall "C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir" | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzdoinstall.exe | — | install_backblaze_512ffe191c8ceb07c.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
1 521
Read events
1 510
Write events
10
Delete events
1
Modification events
| (PID) Process: | (7140) bzdoinstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\Compatibility Assistant |
| Operation: | write | Name: | ExecutablesToExclude |
Value: bzinstall-win32-9.0.1.777.exe | |||
| (PID) Process: | (7140) bzdoinstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\Compatibility Assistant |
| Operation: | delete value | Name: | ExecutablesToExclude |
Value: bzinstall-win32-9.0.1.777.exe | |||
Executable files
15
Suspicious files
2
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit64.exe | executable | |
MD5:F3A2BFEF82D4782A26EE486CB1CCF298 | SHA256:ABEC9B3FF93A5042E9F092B34DD26C5A6EEDD26852E83FAA021E82CE0B2FF072 | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzfilelist.exe | executable | |
MD5:76A99363C25A8DB4392990626E084246 | SHA256:0CD0ED9B210E69D7EDAA3FD7B4A2379D99BC72C37D343F7FDE55AA8809DCC5BF | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\files.zip | compressed | |
MD5:13E110DD11BF992FD919E17B4A22DB0F | SHA256:CFF2B6FDA40D6149F1204BE590661FF23F8627A9126570B1B2C6CED800FD9FB3 | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bztransmit.exe | executable | |
MD5:833E26CE17C55C3A6B2E4871D4CB036D | SHA256:F19A6CACD3BC6B2233155DDBBCFD8AACDDD3F443BE2A6D050BD467DC3E0B4DD2 | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzrestore.exe | executable | |
MD5:846A8DDDFCD90BD93F0ACCFA3025EBB0 | SHA256:8502B3DAD81646ECEBEEFFFC3C94CAD6B33FF8D374E5FA4AC8289BBB112C6768 | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzserv.exe | executable | |
MD5:7AB5C77B8BEF46B817FED64028370157 | SHA256:1406902AE86B64134CDCAD15E58E3FB72D6D83C854001BEC1AC15C598EAC418A | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzwinrt.dll | executable | |
MD5:C751CFDB887A88C8E50974FD8A8DAA14 | SHA256:245655311B352358901AF072B7789BC076005189905E0BD0A5C322CD1DD3874F | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzdownloader_ui_strings.xml | xml | |
MD5:450C0393B3292EF91A11F0F5C8DFA755 | SHA256:835A7893A0A1CF1414F7AAF9EA6FA6DCFB4310B23D8BCBF661ABF4A99A68FC5B | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\bzfclean.exe | executable | |
MD5:5DA3374069372609B45EE2920A14BE7B | SHA256:A612EFFFE5214CCBAB3C5B26B0A751FE8C1CC6103FBC3182C641112C838BB5E8 | |||
| 6612 | install_backblaze_512ffe191c8ceb07c.exe | C:\Users\admin\AppData\Local\Temp\bzi0919191946_0000001_9097dir\msvcr100.dll | executable | |
MD5:2B92A88E329F4845D31941967A3BAA90 | SHA256:649A7AB8E3B5C0940812E40EAFC8F004979BB48BFC8F4BC7DB9F2CBCDD715344 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
24
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 92.123.104.6:443 | — | Akamai International B.V. | DE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 52.168.117.168:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ca000.backblaze.com |
| whitelisted |
ca001.backblaze.com |
| whitelisted |