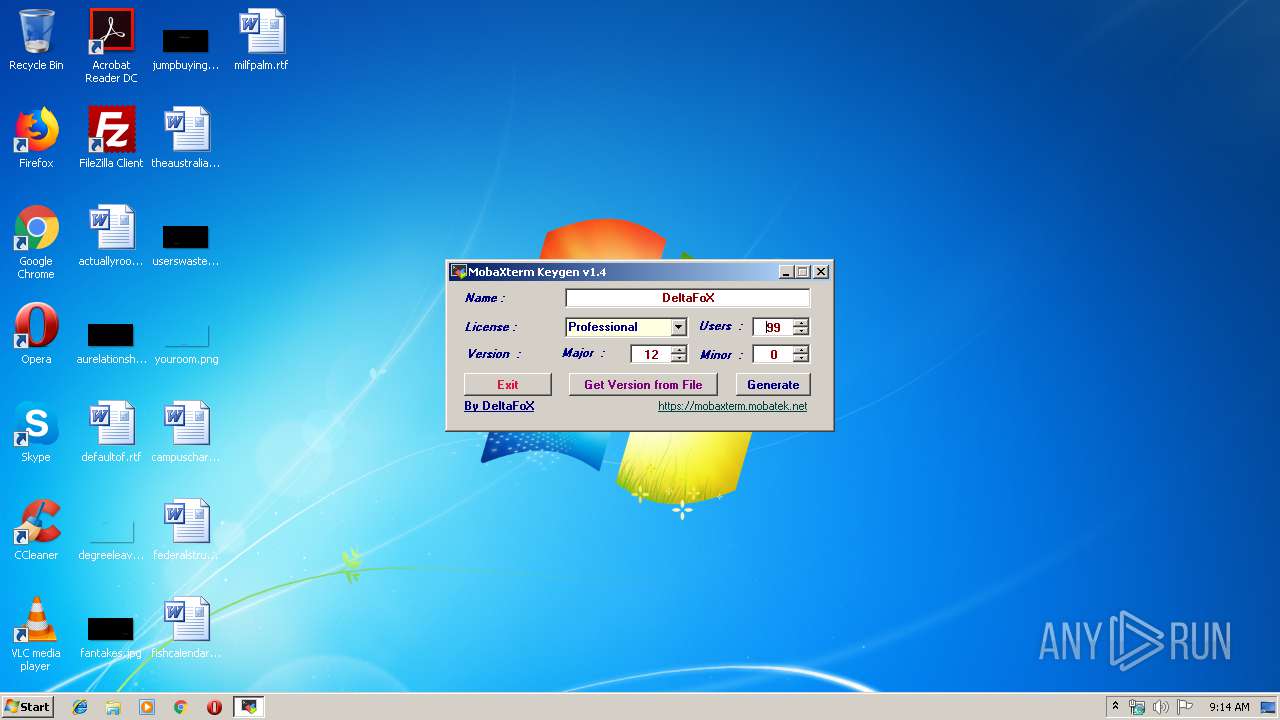
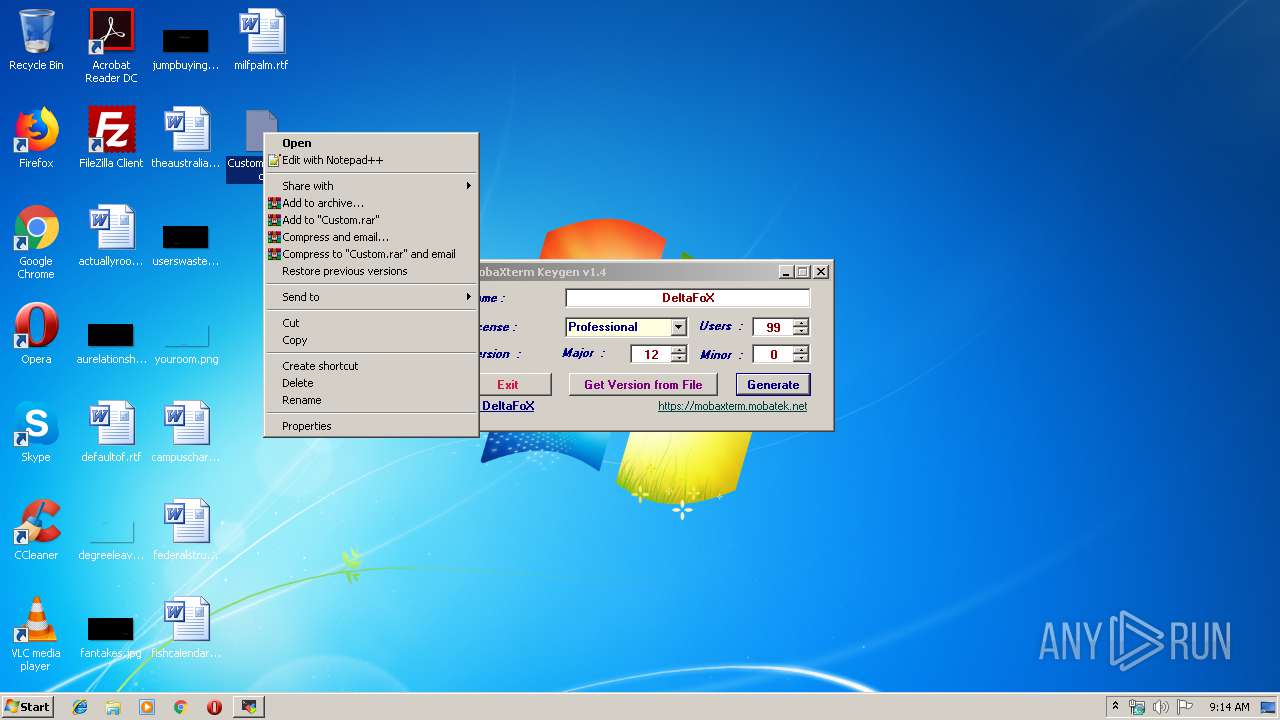
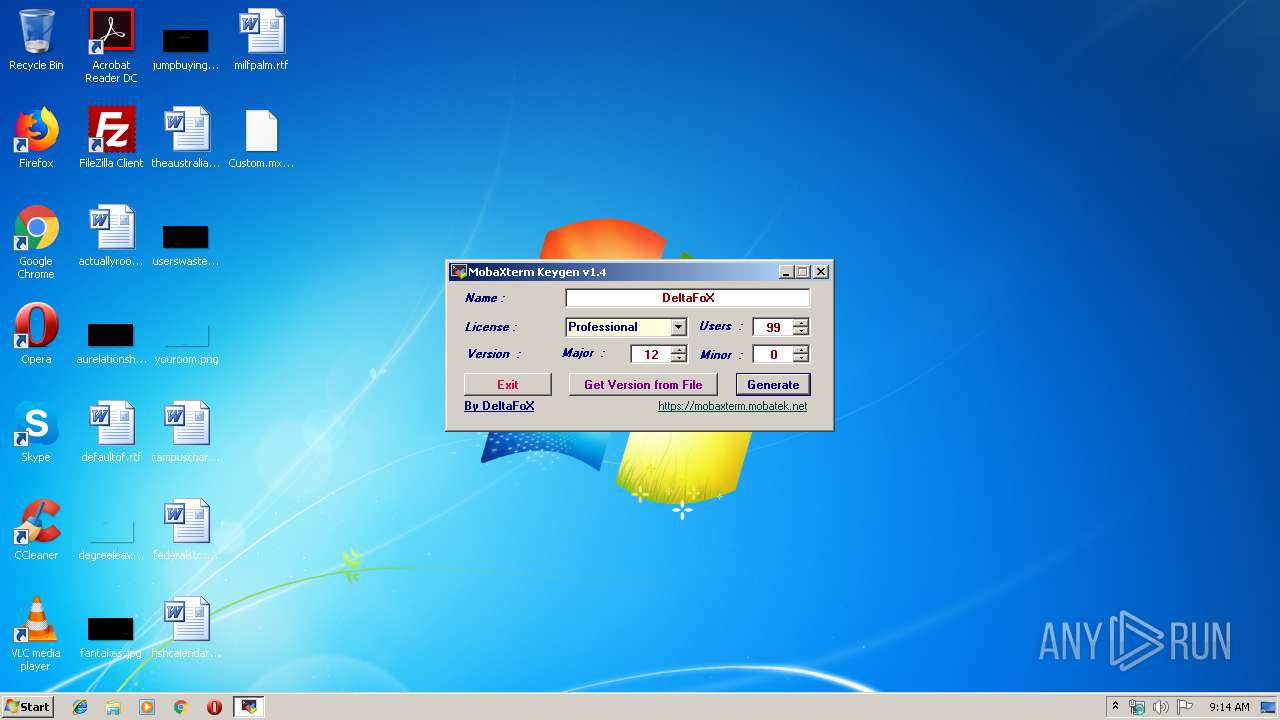
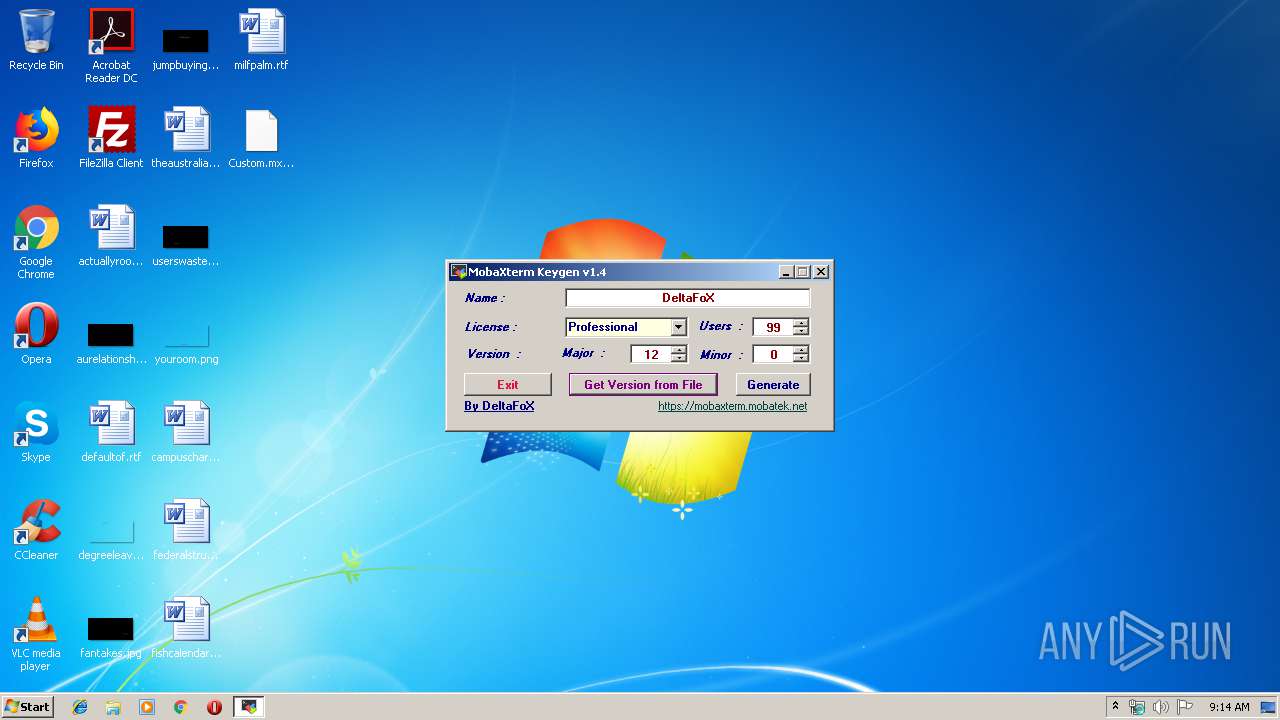
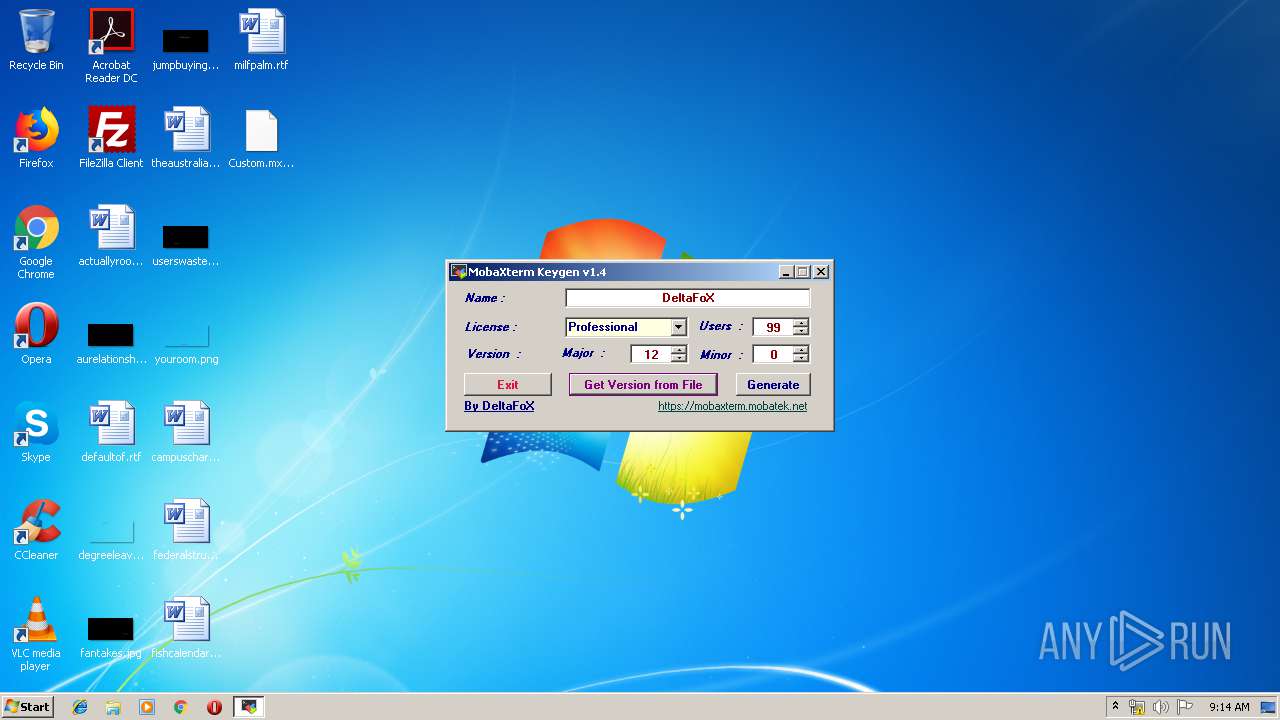
| File name: | MobaXterm_Keygen_v1.4_By_DeltaFoX.exe |
| Full analysis: | https://app.any.run/tasks/979c18e8-0276-48d1-9902-96322581a44a |
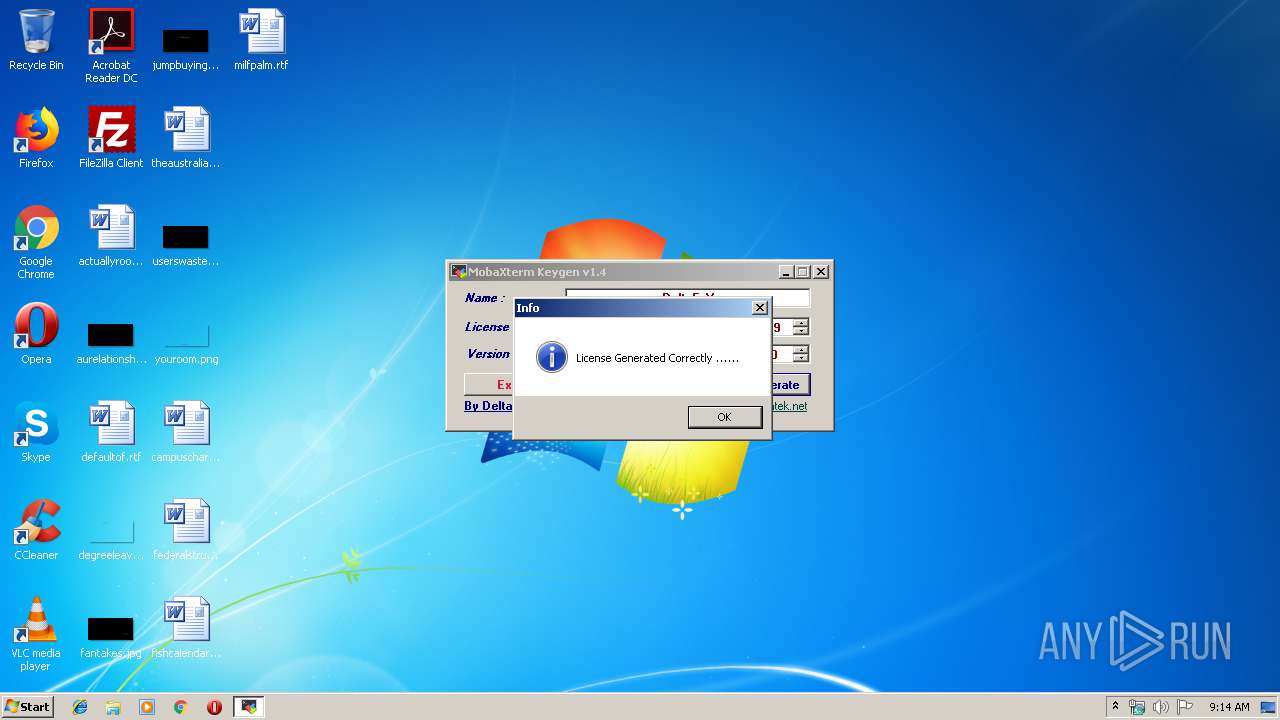
| Verdict: | No threats detected |
| Analysis date: | November 22, 2019, 09:13:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5FAEF6B582F5152A117A84CBF39BB114 |
| SHA1: | C22156833848D500D84F6EE8C9E7CFBDA7CBD6FA |
| SHA256: | 772E26F74B6A2FD3BD306598F22BE914B8EFAF31A9D5C7DBED8A4C8D0E765C10 |
| SSDEEP: | 3072:7snSOuzJahuKZqZVoSQ0k/ze1lSu0sru0viL:IVuzIbZqZVheq1lSu0gu0a |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- MobaXterm_Keygen_v1.4_By_DeltaFoX.exe (PID: 2720)
Creates files in the user directory
- notepad++.exe (PID: 4088)
INFO
Manual execution by user
- notepad++.exe (PID: 4088)
- rundll32.exe (PID: 2168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (45.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.2) |
| .exe | | | Win64 Executable (generic) (17) |
| .scr | | | Windows screen saver (8) |
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2093:12:24 04:42:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 134656 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x22dae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.0.0 |
| ProductVersionNumber: | 1.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Keygen for MobaXterm Software |
| CompanyName: | DeFconX |
| FileDescription: | MobaXterm_Keygen |
| FileVersion: | 1.4.0.0 |
| InternalName: | MobaXterm_Keygen.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | DeltaFoX |
| OriginalFileName: | MobaXterm_Keygen.exe |
| ProductName: | MobaXterm_Keygen |
| ProductVersion: | 1.4.0.0 |
| AssemblyVersion: | 1.4.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Nov-1957 21:13:46 |
| Debug artifacts: |
|
| Comments: | Keygen for MobaXterm Software |
| CompanyName: | DeFconX |
| FileDescription: | MobaXterm_Keygen |
| FileVersion: | 1.4.0.0 |
| InternalName: | MobaXterm_Keygen.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | DeltaFoX |
| OriginalFilename: | MobaXterm_Keygen.exe |
| ProductName: | MobaXterm_Keygen |
| ProductVersion: | 1.4.0.0 |
| Assembly Version: | 1.4.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 17-Nov-1957 21:13:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00020DB4 | 0x00020E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.36631 |
.sdata | 0x00024000 | 0x00000162 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.99059 |
.rsrc | 0x00026000 | 0x000099F0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.93265 |
.reloc | 0x00030000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.988 | 3481 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.27987 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.60944 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.77446 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.01242 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79808 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
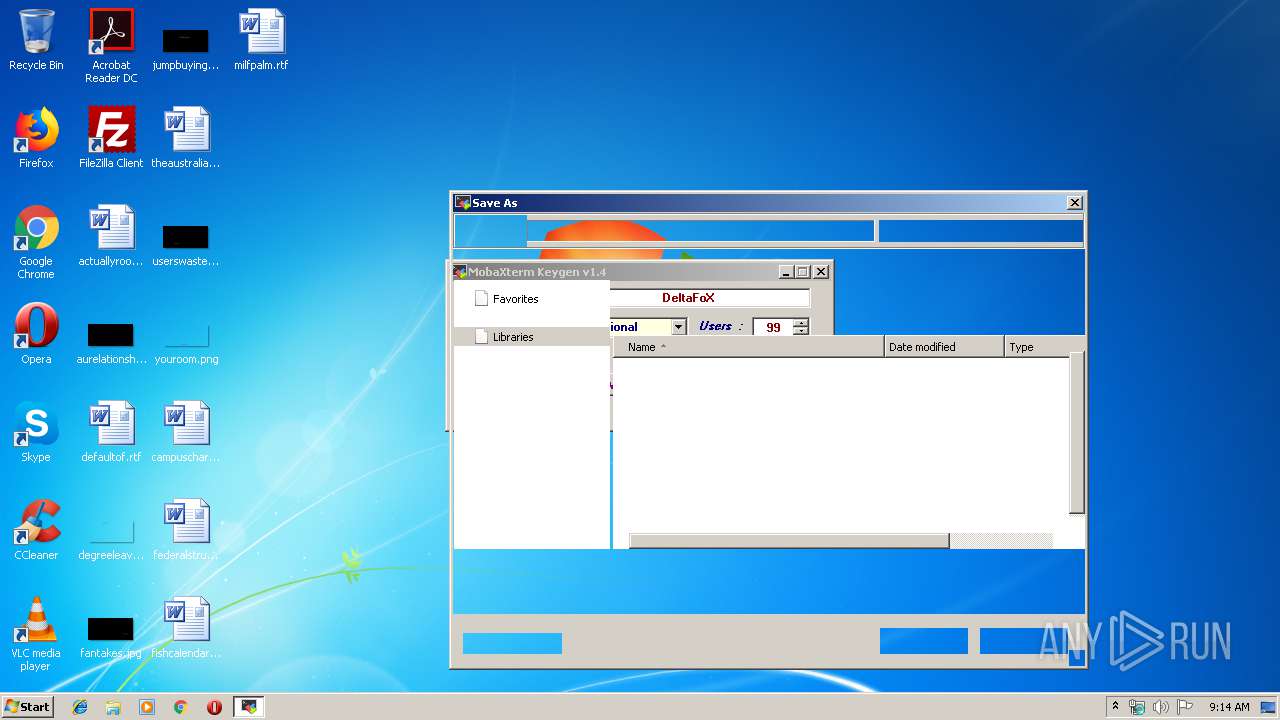
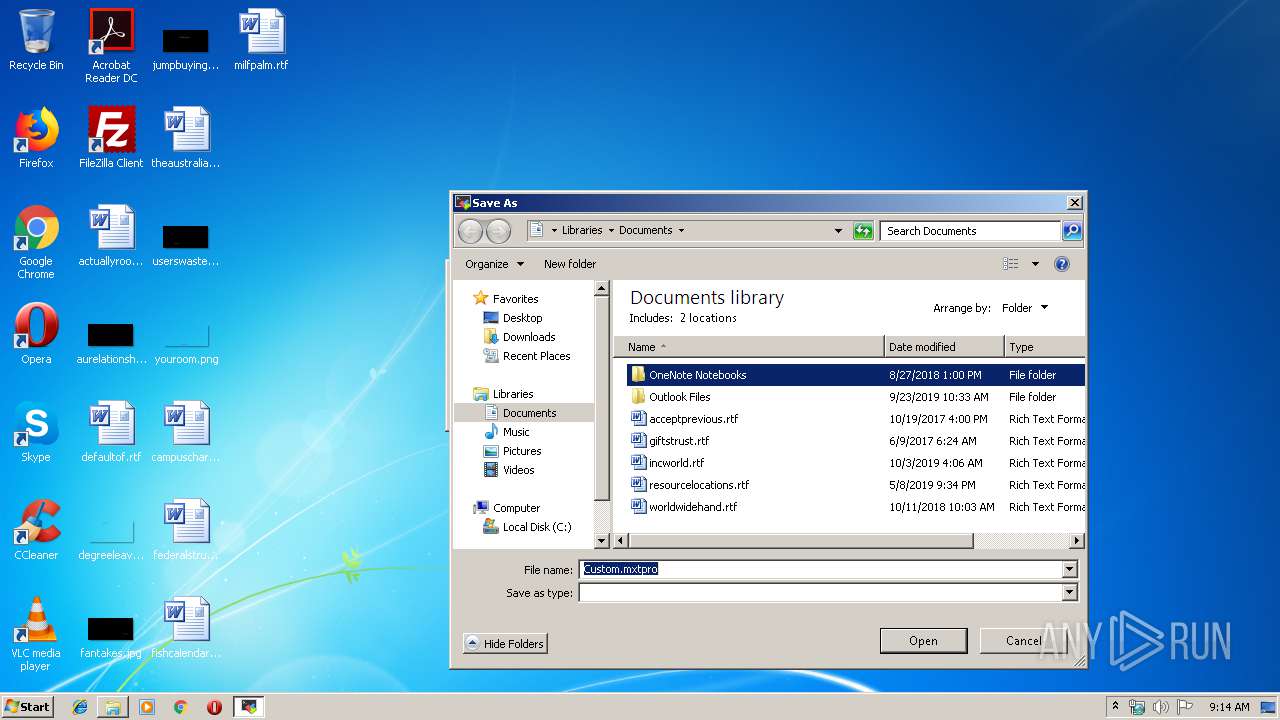
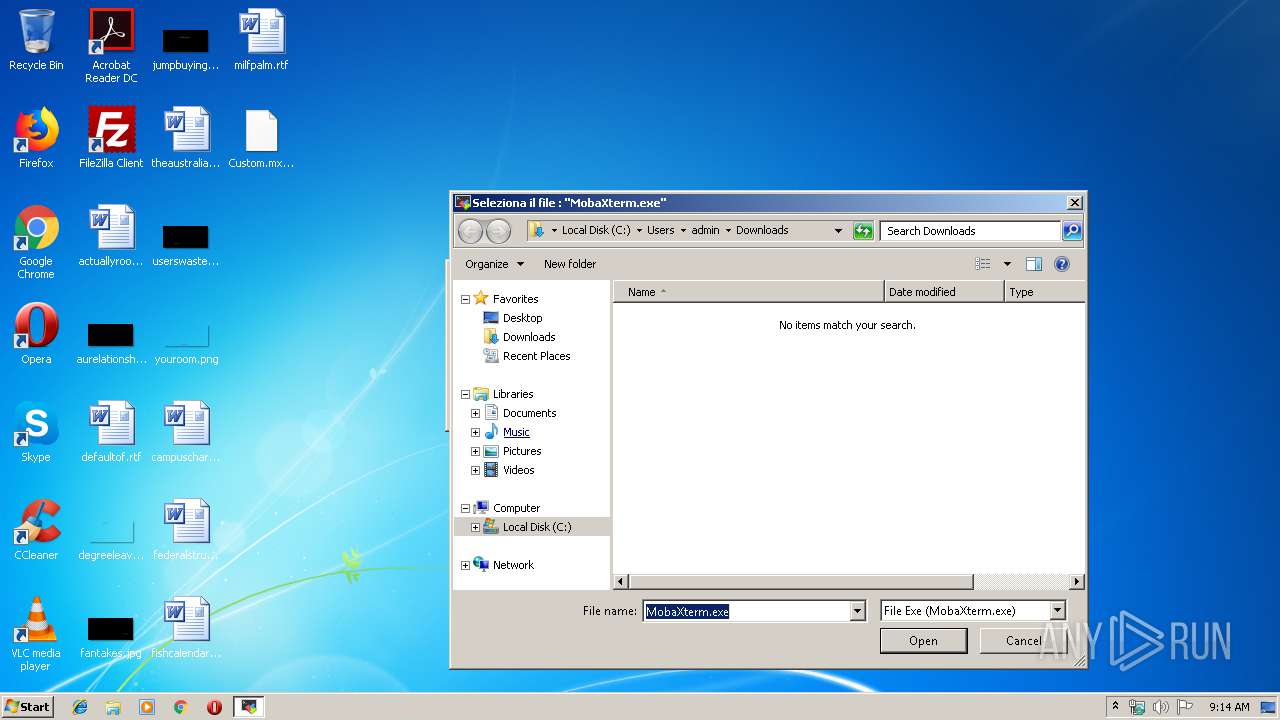
| 1728 | "C:\Users\admin\Downloads\MobaXterm_Keygen_v1.4_By_DeltaFoX.exe" | C:\Users\admin\Downloads\MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | — | explorer.exe | |||||||||||
User: admin Company: DeFconX Integrity Level: MEDIUM Description: MobaXterm_Keygen Exit code: 3221226540 Version: 1.4.0.0 Modules
| |||||||||||||||
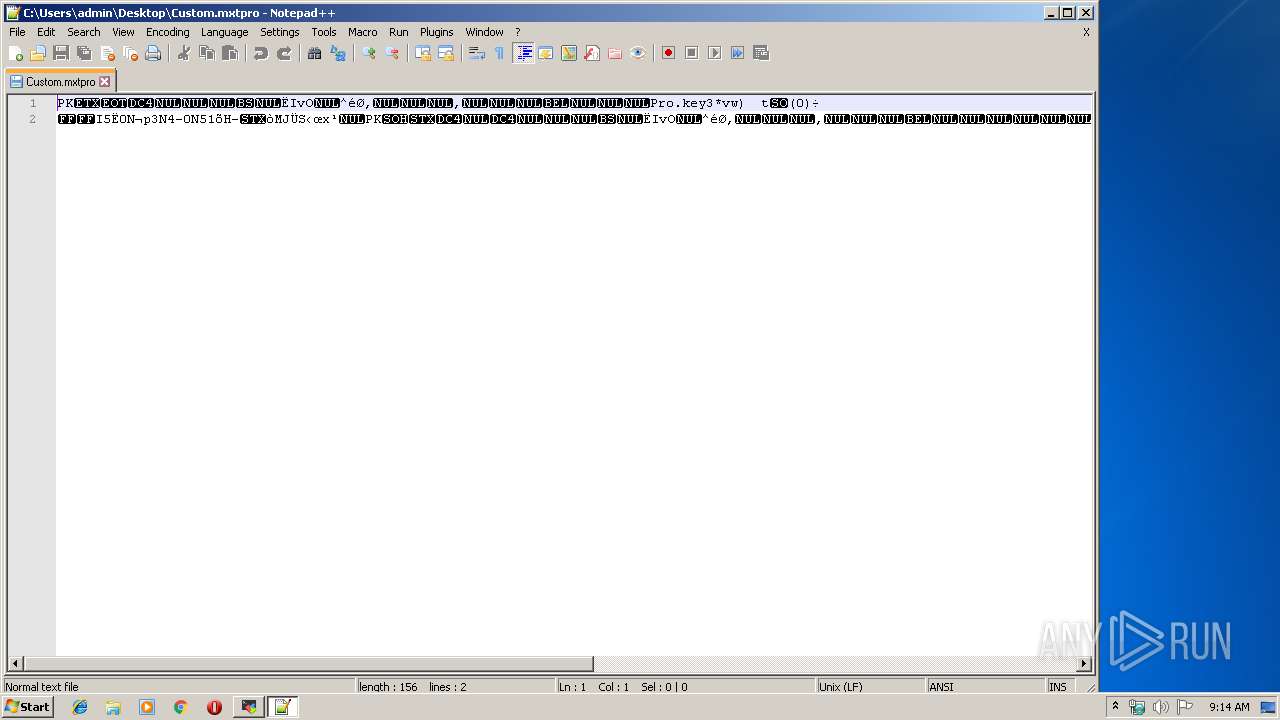
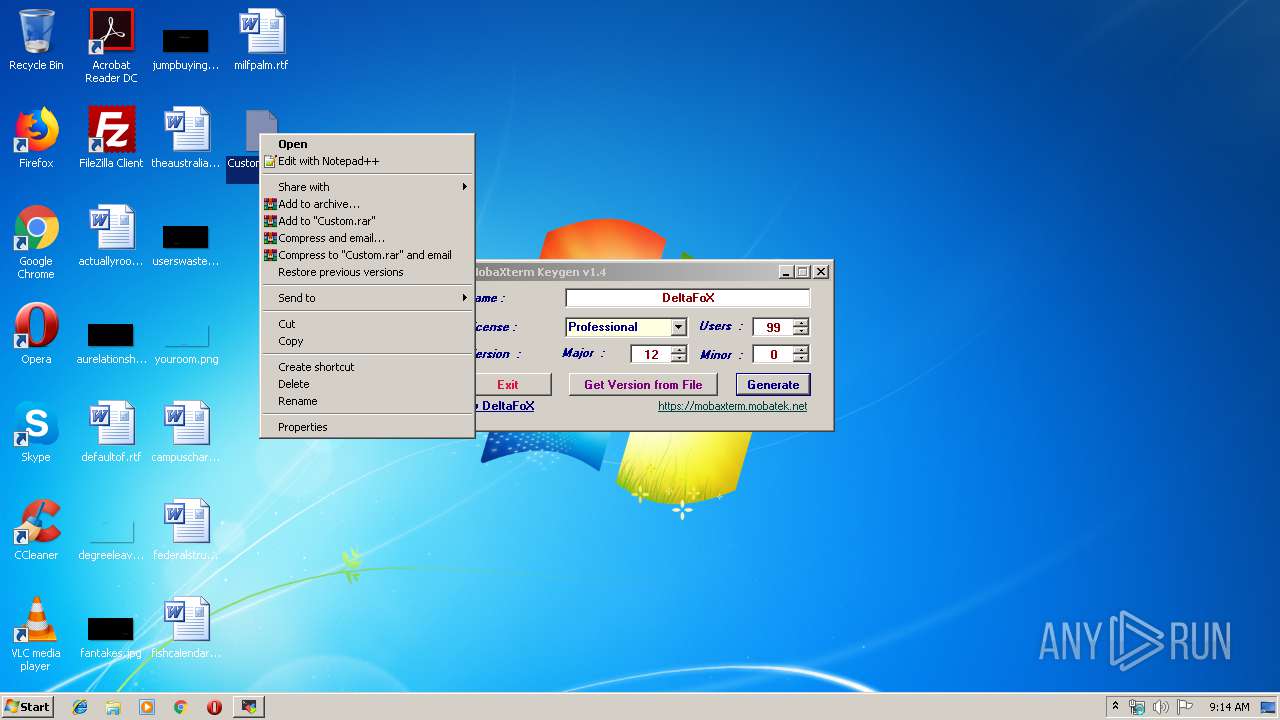
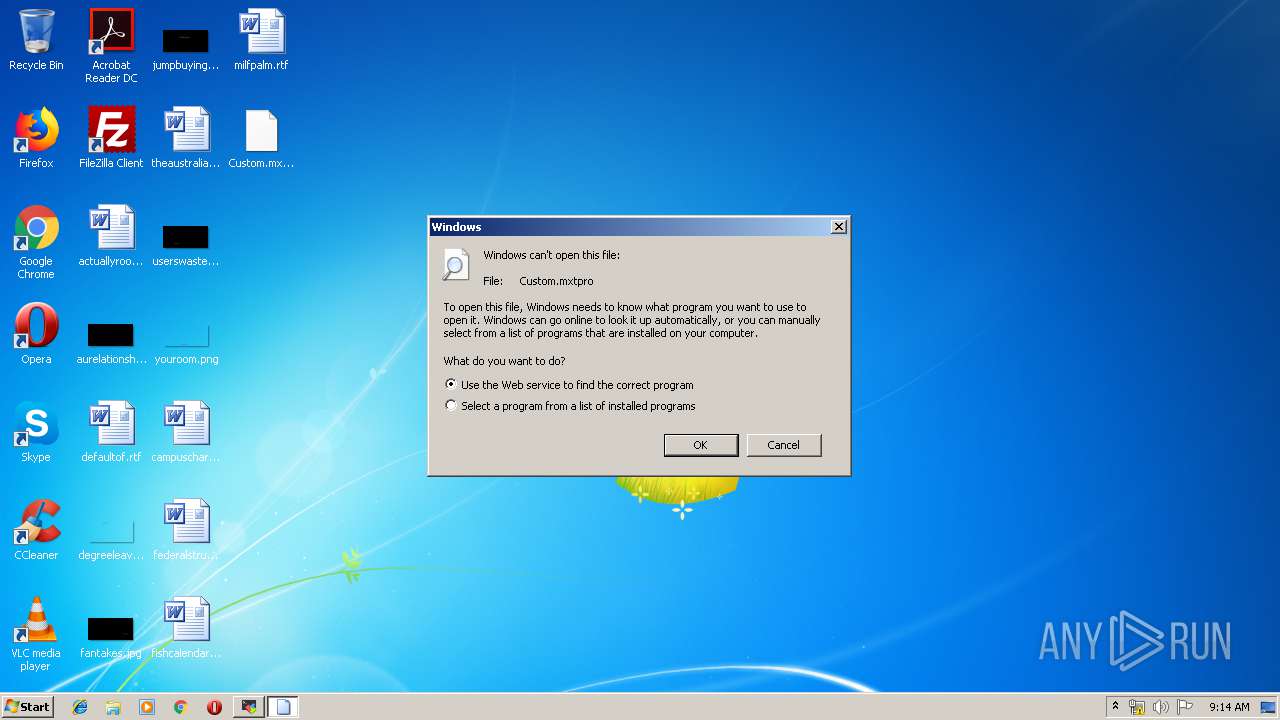
| 2168 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\Custom.mxtpro | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\Downloads\MobaXterm_Keygen_v1.4_By_DeltaFoX.exe" | C:\Users\admin\Downloads\MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | explorer.exe | ||||||||||||
User: admin Company: DeFconX Integrity Level: HIGH Description: MobaXterm_Keygen Exit code: 0 Version: 1.4.0.0 Modules
| |||||||||||||||
| 4088 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\Custom.mxtpro" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
739
Read events
625
Write events
109
Delete events
5
Modification events
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 4D006F006200610058007400650072006D005F004B0065007900670065006E005F00760031002E0034005F00420079005F00440065006C007400610046006F0058002E006500780065000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000100000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (2720) MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: 1092616257 | |||
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 2720 | MobaXterm_Keygen_v1.4_By_DeltaFoX.exe | C:\Users\admin\Desktop\Custom.mxtpro | compressed | |
MD5:— | SHA256:— | |||
| 4088 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:44982E1D48434C0AB3E8277E322DD1E4 | SHA256:3E661D3F1FF3977B022A0ACC26B840B5E57D600BC03DCFC6BEFDB408C665904C | |||
| 4088 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 4088 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 4088 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:AD21A64014891793DD9B21D835278F36 | SHA256:C24699C9D00ABDD510140FE1B2ACE97BFC70D8B21BF3462DED85AFC4F73FE52F | |||
| 4088 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:EA9FE896B4305C2A9629FEB279084544 | SHA256:EF99FB4EFE424FABB1F3CD0076CC532EF5767D6CD1D09611C4F69F1BE03702B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2712 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|