| File name: | IPTV-UrlChecker V3.5.bin |
| Full analysis: | https://app.any.run/tasks/fdae6b15-e519-444c-908b-654bbbf8f696 |
| Verdict: | No threats detected |
| Analysis date: | March 25, 2020, 16:16:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 6FFDA7C77F6625D6BD9D70D9BED5E9E7 |
| SHA1: | A67E1395570D6E037AE4CC3C7B9C41E3241C9E0E |
| SHA256: | 77225E1E9B0F5C5EBBDA09C4F0DEB492653078462256F4B1DCB2AA0FC3940080 |
| SSDEEP: | 12288:v2S/ifyCmMf/JATS4SJJrRjm5SUVTnWAs5GF6Mw43ugXHLuH:vLhhM3JAubJJrRjmXVTnWAs5A84G |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes JAVA applets
- IPTV-UrlChecker V3.5.bin.exe (PID: 3976)
Creates files in the user directory
- vlc.exe (PID: 2424)
INFO
Manual execution by user
- WINWORD.EXE (PID: 3888)
- WINWORD.EXE (PID: 2928)
- vlc.exe (PID: 2424)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2928)
- WINWORD.EXE (PID: 3888)
Creates files in the user directory
- WINWORD.EXE (PID: 3888)
- WINWORD.EXE (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:05:20 23:09:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 411172 |
| InitializedDataSize: | 449024 |
| UninitializedDataSize: | 18944 |
| EntryPoint: | 0x1240 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-May-2007 21:09:01 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 20-May-2007 21:09:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00064624 | 0x00064800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32879 |
.data | 0x00066000 | 0x00001274 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.69523 |
.bss | 0x00068000 | 0x000049F0 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.edata | 0x0006D000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.10882 |
.idata | 0x0006E000 | 0x00000FD0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.07547 |
.rsrc | 0x0006F000 | 0x0006F000 | 0x0006E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.64593 |
.reloc | 0x000DE000 | 0x00002F9C | 0x00003000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.7099 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.12382 | 744 | UNKNOWN | English - United States | RT_ICON |
2 | 1.87204 | 2216 | UNKNOWN | English - United States | RT_ICON |
102 | 6.65168 | 444613 | UNKNOWN | English - United States | JAVA |
103 | 4.90397 | 366 | UNKNOWN | English - United States | JAVA |
104 | 7.65625 | 2885 | UNKNOWN | English - United States | JAVA |
A | 1.87486 | 22 | UNKNOWN | English - United States | RT_GROUP_ICON |
A2 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_Z10testStringP7JNIEnv_P8_jobjectP8_jstring@12 | 1 | 0x0001E430 |
_Z15jnm_exitWindowsP7JNIEnv_P8_jobjectl@12 | 2 | 0x0001EB72 |
_Z16jnm_getdriveinfoP7JNIEnv_P8_jobjectS2_@12 | 3 | 0x0001EF02 |
_Z16jnm_shellexecuteP7JNIEnv_P8_jobjectP8_jstringS4_S4_S4_l@28 | 4 | 0x0001EC12 |
_Z21jnm_getExecutableNameP7JNIEnv_P8_jobject@8 | 5 | 0x0001E6B2 |
_Z21jnm_getExecutablePathP7JNIEnv_P8_jobject@8 | 6 | 0x0001E5E2 |
_Z22jnm_deleteFileOnRebootP7JNIEnv_P8_jobjectP8_jstring@12 | 7 | 0x0001E786 |
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1380 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -classpath "C:\Users\admin\AppData\Local\Temp\temp0.jar;C:\Users\admin\AppData\Local\Temp\temp1.jar;" propro.PROpro | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | IPTV-UrlChecker V3.5.bin.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
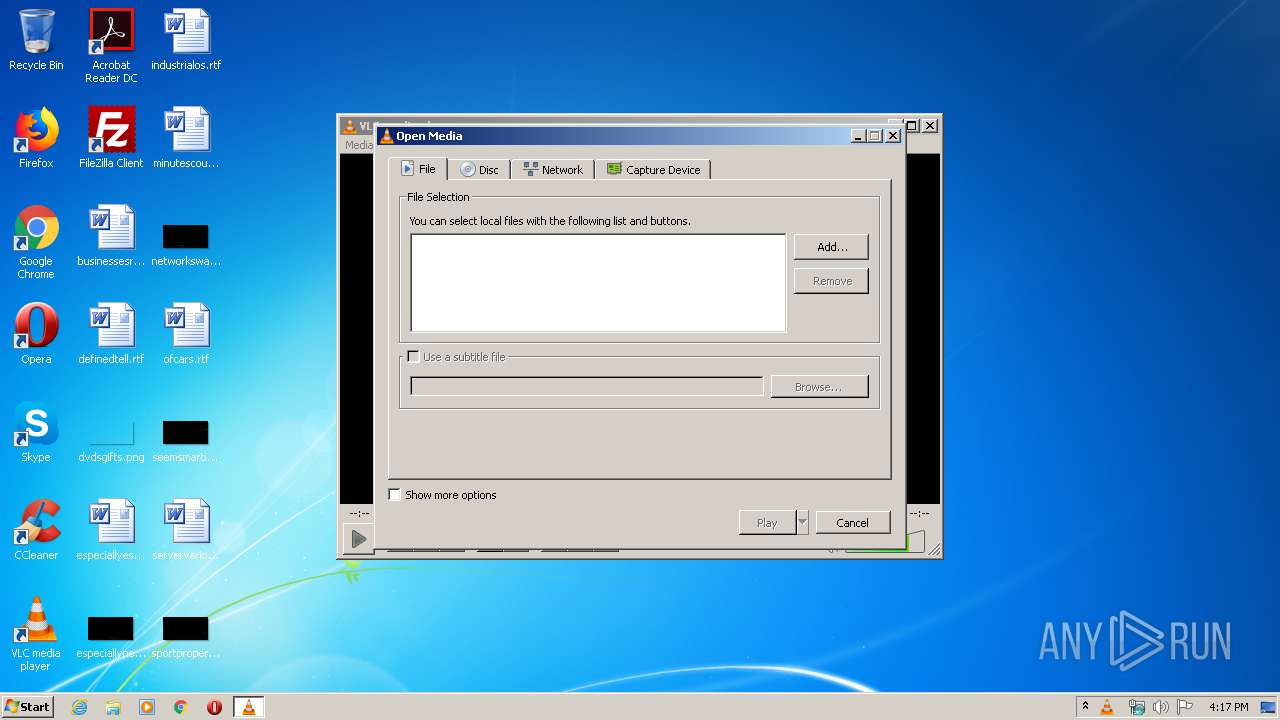
| 2424 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\industrialos.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\businessesroom.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\IPTV-UrlChecker V3.5.bin.exe" | C:\Users\admin\AppData\Local\Temp\IPTV-UrlChecker V3.5.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 281
Read events
1 636
Write events
346
Delete events
299
Modification events
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | p"6 |
Value: 70223600300F0000010000000000000000000000 | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
0
Text files
6
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2424 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlcrc.2424 | — | |
MD5:— | SHA256:— | |||
| 3888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE670.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B3BBEC67-E71C-44B1-AF94-664FFF9B1548}.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{8B81124B-8D34-4774-8EA7-850CAD29FD6B}.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{021B1DA8-96DE-4DD5-8250-973DFC2BB95C}.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3135.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{25C3B7EF-2EBD-4983-B646-AC09644DFD20}.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{1BAC07E4-6C9E-4518-AB3C-8783E3A64901}.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{17C8524F-D473-4F0B-ABE1-E674243E1535}.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | IPTV-UrlChecker V3.5.bin.exe | C:\Users\admin\AppData\Local\Temp\temp0.jar | java | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1380 | javaw.exe | GET | 301 | 67.199.248.10:80 | http://bit.ly/2zTez35 | US | html | 162 b | shared |
1380 | javaw.exe | GET | 404 | 173.212.219.42:80 | http://star7-dz.info/user.asp?id=107524&f=CharFcontroler351.txt | DE | html | 1.22 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1380 | javaw.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
1380 | javaw.exe | 173.212.219.42:80 | star7-dz.info | Contabo GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
star7-dz.info |
| unknown |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|