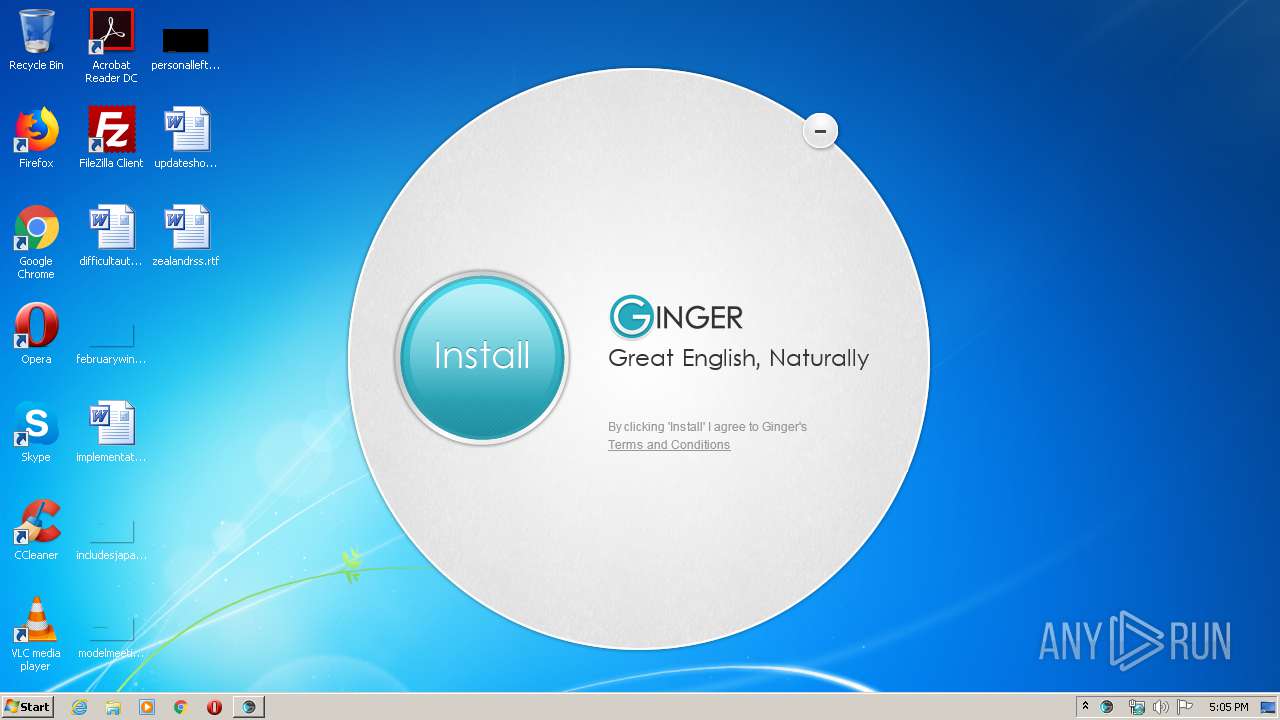
| File name: | Ginger.exe |
| Full analysis: | https://app.any.run/tasks/dfb19bcf-083a-413a-bc1c-82b76efd2123 |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2020, 16:04:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7E42CF45265F71819AE49D2CD89E5A1A |
| SHA1: | 039DE5A180286A6AE733B8A484623D385DF0BD13 |
| SHA256: | 771D01A746D13624D6C61300F10302E64517D534051F78E04836F43C28DF5652 |
| SSDEEP: | 24576:VBlUob0s2Bh3ovpvPHvJintk+X6cdd4Ojwsl:XgJh4vpvPPJkGvUd4OjwC |
MALICIOUS
Changes settings of System certificates
- Ginger.exe (PID: 3100)
SUSPICIOUS
Application launched itself
- Ginger.exe (PID: 1392)
Reads Internet Cache Settings
- Ginger.exe (PID: 3100)
- Ginger.exe (PID: 1392)
Reads internet explorer settings
- Ginger.exe (PID: 3100)
Adds / modifies Windows certificates
- Ginger.exe (PID: 3100)
INFO
Reads settings of System Certificates
- Ginger.exe (PID: 3100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:05 16:14:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 457216 |
| InitializedDataSize: | 442368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49b21 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.7.227.0 |
| ProductVersionNumber: | 3.7.227.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build, Special build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Ginger Software |
| FileDescription: | Ginger |
| FileVersion: | 3.7.227 |
| InternalName: | Ginger |
| PrivateBuild: | - |
| ProductName: | Ginger |
| ProductVersion: | 3.7.227 |
| SpecialBuild: | - |
| LegalCopyright: | Copyright (C) 2009 |
| OriginalFileName: | TinyInstaller.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Nov-2018 15:14:59 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Ginger Software |
| FileDescription: | Ginger |
| FileVersion: | 3.7.227 |
| InternalName: | Ginger |
| PrivateBuild: | 0 |
| ProductName: | Ginger |
| ProductVersion: | 3.7.227 |
| SpecialBuild: | 0 |
| LegalCopyright: | Copyright (C) 2009 |
| OriginalFilename: | TinyInstaller.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Nov-2018 15:14:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006F82B | 0x0006FA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61534 |
.rdata | 0x00071000 | 0x0002ADF0 | 0x0002AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41366 |
.data | 0x0009C000 | 0x000063A8 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.50821 |
.rsrc | 0x000A3000 | 0x000311C8 | 0x00031200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.87106 |
.reloc | 0x000D5000 | 0x00009B30 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61832 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23881 | 609 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.04884 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 6.21004 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 3.26299 | 762 | UNKNOWN | English - United States | RT_STRING |
8 | 3.24236 | 1748 | UNKNOWN | English - United States | RT_STRING |
106 | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
109 | 1.79879 | 16 | UNKNOWN | English - United States | RT_ACCELERATOR |
148 | 5.24384 | 165 | UNKNOWN | English - United States | PLIST |
149 | 7.8513 | 2682 | UNKNOWN | English - United States | PNG |
150 | 7.83904 | 2390 | UNKNOWN | English - United States | PNG |
Imports
ADVAPI32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
Total processes
42
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1392 | "C:\Users\admin\AppData\Local\Temp\Ginger.exe" | C:\Users\admin\AppData\Local\Temp\Ginger.exe | explorer.exe | ||||||||||||
User: admin Company: Ginger Software Integrity Level: MEDIUM Description: Ginger Exit code: 0 Version: 3.7.227 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\Ginger.exe" RunAsAdmin | C:\Users\admin\AppData\Local\Temp\Ginger.exe | Ginger.exe | ||||||||||||
User: admin Company: Ginger Software Integrity Level: HIGH Description: Ginger Exit code: 0 Version: 3.7.227 Modules
| |||||||||||||||
Total events
1 682
Read events
468
Write events
1 214
Delete events
0
Modification events
| (PID) Process: | (1392) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1392) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1392) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1392) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1392) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1392) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1392) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3100) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3100) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3100) Ginger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
8
Text files
18
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | Ginger.exe | C:\Users\admin\AppData\Local\Temp\CabAB23.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | Ginger.exe | C:\Users\admin\AppData\Local\Temp\TarAB24.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | Ginger.exe | C:\Users\admin\AppData\Local\Temp\CabC5FE.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | Ginger.exe | C:\Users\admin\AppData\Local\Temp\TarC5FF.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | Ginger.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\tinyStart[1].htm | html | |
MD5:6D08940DA0D4CCC414363CB3407914ED | SHA256:4552706AB04AF3C1D948E87BDD321951EC6D9276F49D3A64CBEB4E45344475FC | |||
| 3100 | Ginger.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\tinyStart[1].js | text | |
MD5:20B779903F0E389783C9087D02E34EC2 | SHA256:2CC3C43395C52B3DC7690528B4232F93572E1CD4A16D0EAF55FED76F722DF55D | |||
| 3100 | Ginger.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\btn[1].png | image | |
MD5:C36667398365A38424EF3142B0290EBC | SHA256:7CA246568FCBBB7EBBA26AF2F69803907A74863EAA16386D7F600D16BEF2676C | |||
| 3100 | Ginger.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\logo[1].png | image | |
MD5:7E8D1D9A1517546497871329C0BF6266 | SHA256:792EAE9AEAE2AA575457944C940C0C696E46BBFEA5AD45F03184D0888EBCFB28 | |||
| 1392 | Ginger.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E7EC0C85688F4738F3BE49B104BA67 | der | |
MD5:390EB6193DD17D193CF41A821314AE1B | SHA256:7C193BB66A9B9ED783FD9F6CED2E521EBCCAA00AFD0BC6730F3174BED02A5127 | |||
| 1392 | Ginger.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E7EC0C85688F4738F3BE49B104BA67 | binary | |
MD5:4833FA8704F81B527526941A63E77058 | SHA256:EB54F54E2BDBAFBEA41EB519421A870224CE4B4D7EEB733923E8268C895D0939 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
14
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1392 | Ginger.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsalphasha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSE1Wv4CYvTB7dm2OHrrWWWqmtnYQQU9c3VPAhQ%2BWpPOreX2laD5mnSaPcCDBdFbsuE7JHBiV4j6Q%3D%3D | US | der | 1.49 Kb | whitelisted |
3100 | Ginger.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEApFQkhjIuntAgAAAABiB5I%3D | US | der | 471 b | whitelisted |
3100 | Ginger.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1392 | Ginger.exe | 95.183.2.17:443 | splunkci.gingersoftware.com | Xglobe Online LTD | US | unknown |
1392 | Ginger.exe | 95.183.2.30:80 | tr.gingersoftware.com | Xglobe Online LTD | US | unknown |
1392 | Ginger.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3100 | Ginger.exe | 95.183.2.30:80 | tr.gingersoftware.com | Xglobe Online LTD | US | unknown |
3100 | Ginger.exe | 95.183.2.17:443 | splunkci.gingersoftware.com | Xglobe Online LTD | US | unknown |
3100 | Ginger.exe | 52.222.158.132:80 | downloads.gingersoftware.com | Amazon.com, Inc. | US | malicious |
3100 | Ginger.exe | 52.222.158.103:80 | cdn.gingersoftware.com | Amazon.com, Inc. | US | whitelisted |
3100 | Ginger.exe | 172.217.23.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
splunkci.gingersoftware.com |
| unknown |
tr.gingersoftware.com |
| unknown |
ocsp.globalsign.com |
| whitelisted |
downloads.gingersoftware.com |
| whitelisted |
cdn.gingersoftware.com |
| whitelisted |
crl.globalsign.net |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
Process | Message |
|---|---|
Ginger.exe | 20200504-170439.002 3.7.227 TID:02660 C E main.cpp,L#74 IsProcessHasAdminPreveliges(): Elevation Type: 3
|
Ginger.exe | 20200504-170439.002 3.7.227 TID:02660 C E main.cpp,L#214 InitTrace(): <**************************************** START ****************************************>
|
Ginger.exe | 20200504-170440.252 3.7.227 TID:03376 C E main.cpp,L#214 InitTrace(): <**************************************** START ****************************************>
|
Ginger.exe | 20200504-170440.252 3.7.227 TID:03376 C E main.cpp,L#74 IsProcessHasAdminPreveliges(): Elevation Type: 2
|
Ginger.exe | 20200504-170446.799 3.7.227 TID:01640 C E InstallApp.cpp,L#197 CInstalledApp::DetectBrowsers(): Chrome detection status [1]
|
Ginger.exe | 20200504-170446.814 3.7.227 TID:01640 C E InstallApp.cpp,L#237 CInstalledApp::DetectBrowsers(): Iexplore detection status [1]
|
Ginger.exe | 20200504-170446.814 3.7.227 TID:01640 C E InstallApp.cpp,L#277 CInstalledApp::DetectBrowsers(): Default browser detection status [1][IEXPLORE.EXE]
|
Ginger.exe | 20200504-170446.799 3.7.227 TID:01640 C E InstallApp.cpp,L#218 CInstalledApp::DetectBrowsers(): Firefox detection status [1]
|
Ginger.exe | 20200504-170446.814 3.7.227 TID:01640 C E InstallApp.cpp,L#337 CInstalledApp::DetectMSOffice(): Office x64 [0] Affiliate[A]
|
Ginger.exe | 20200504-170446.814 3.7.227 TID:01640 C E InstallApp.cpp,L#255 CInstalledApp::DetectBrowsers(): Safari detection status [0]
|