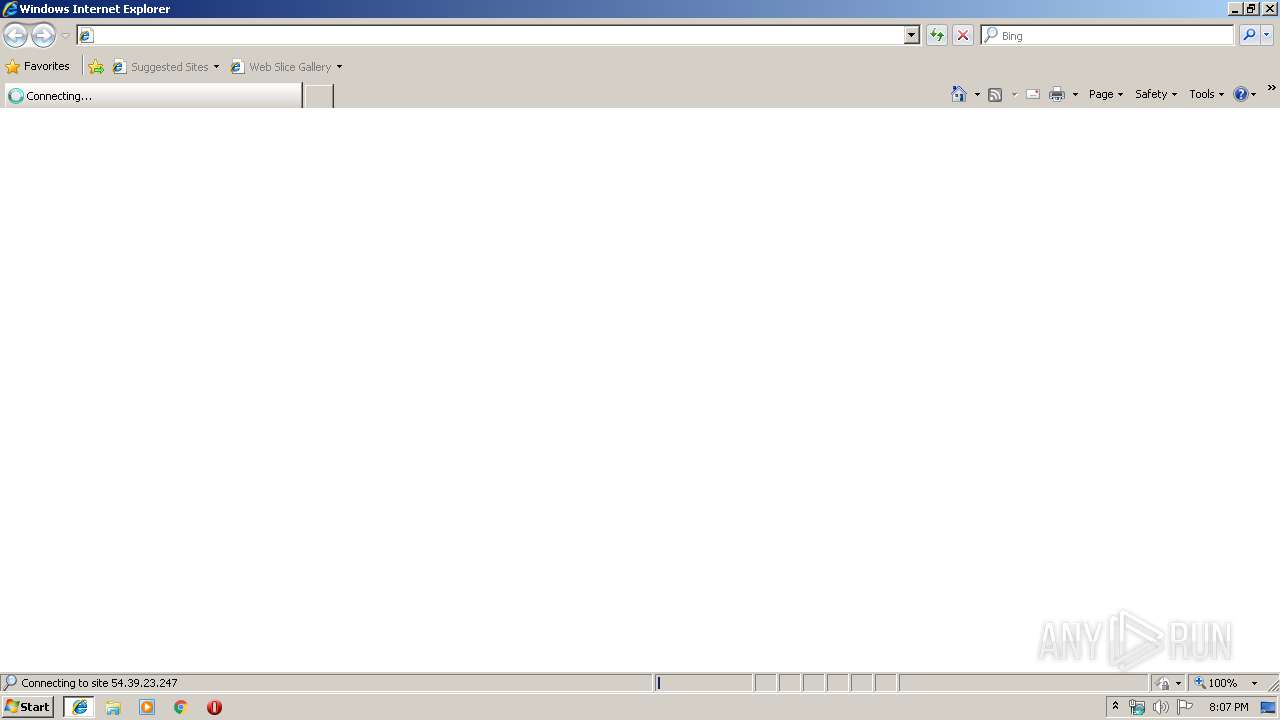
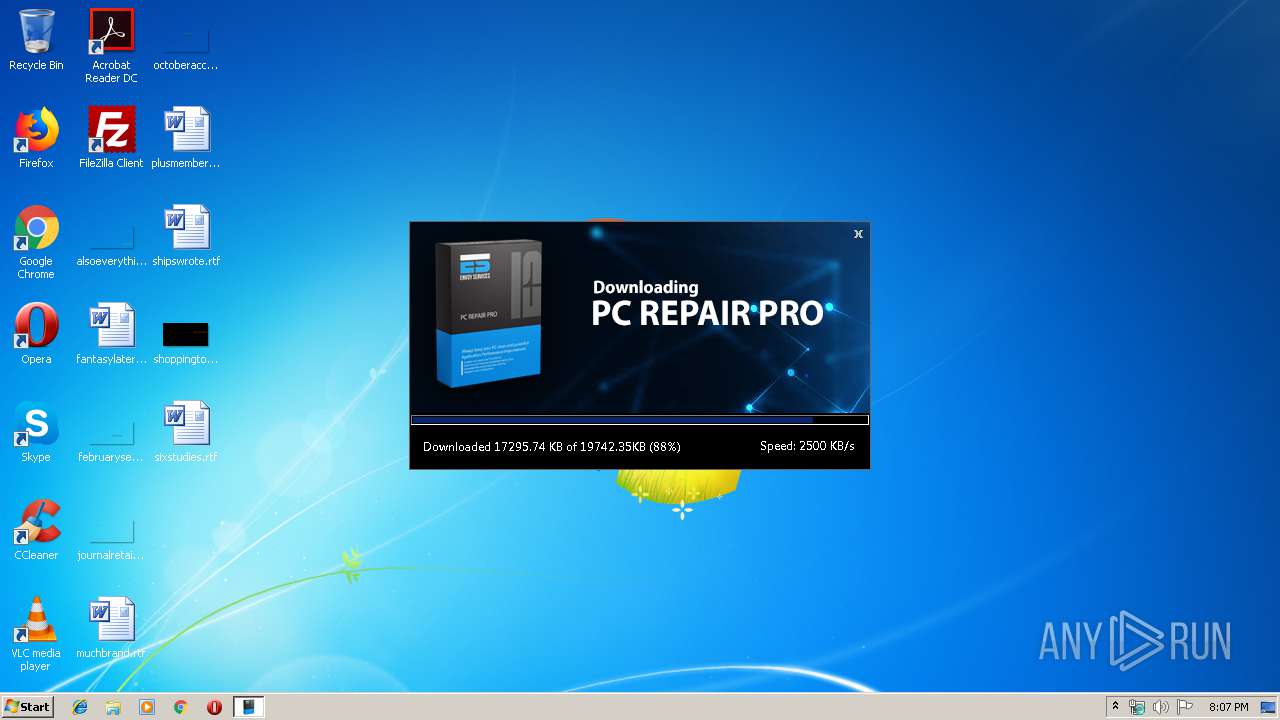
| URL: | https://ca.dl-myes.com/dl.php?src=flv |
| Full analysis: | https://app.any.run/tasks/42fc4a19-76df-40f7-82e7-e9df4eb2260e |
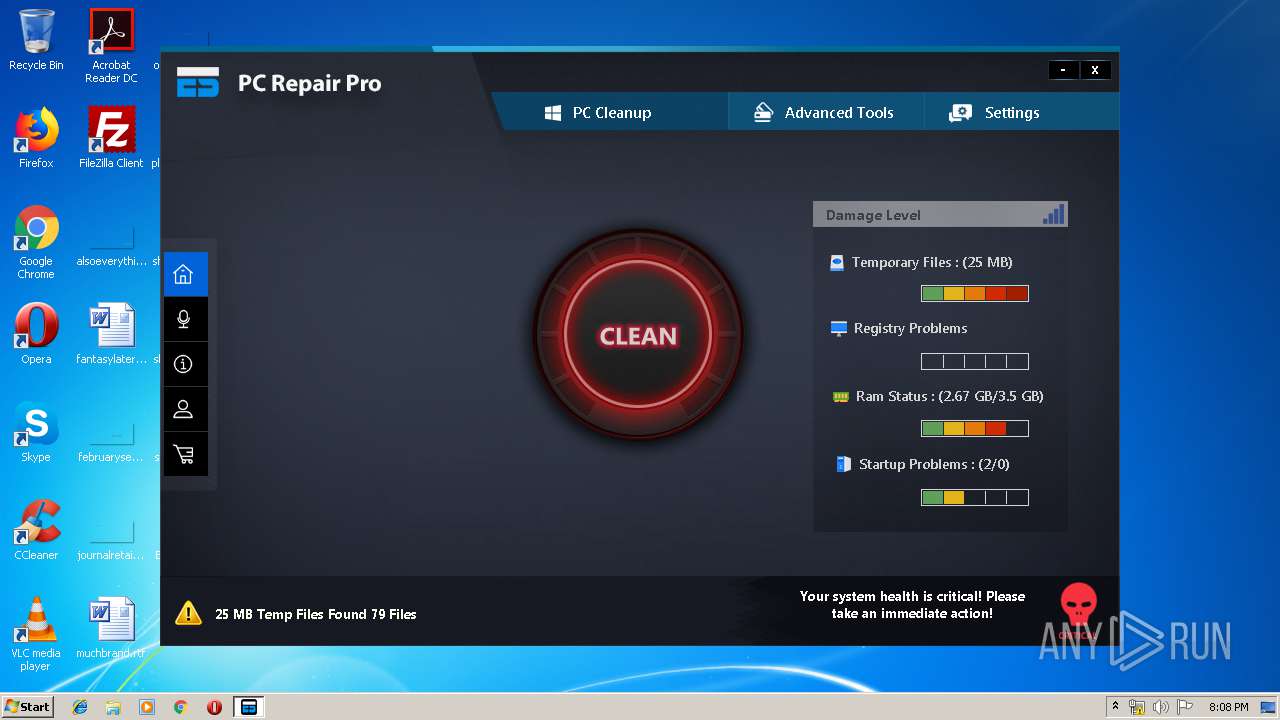
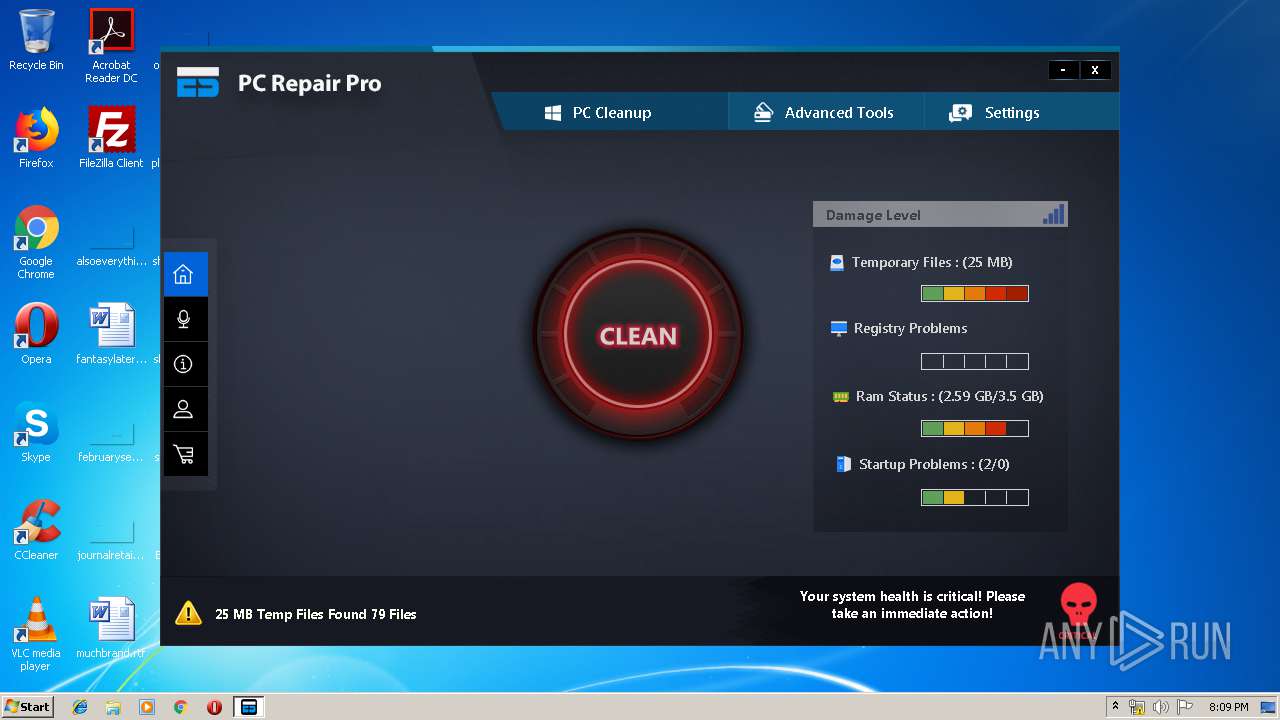
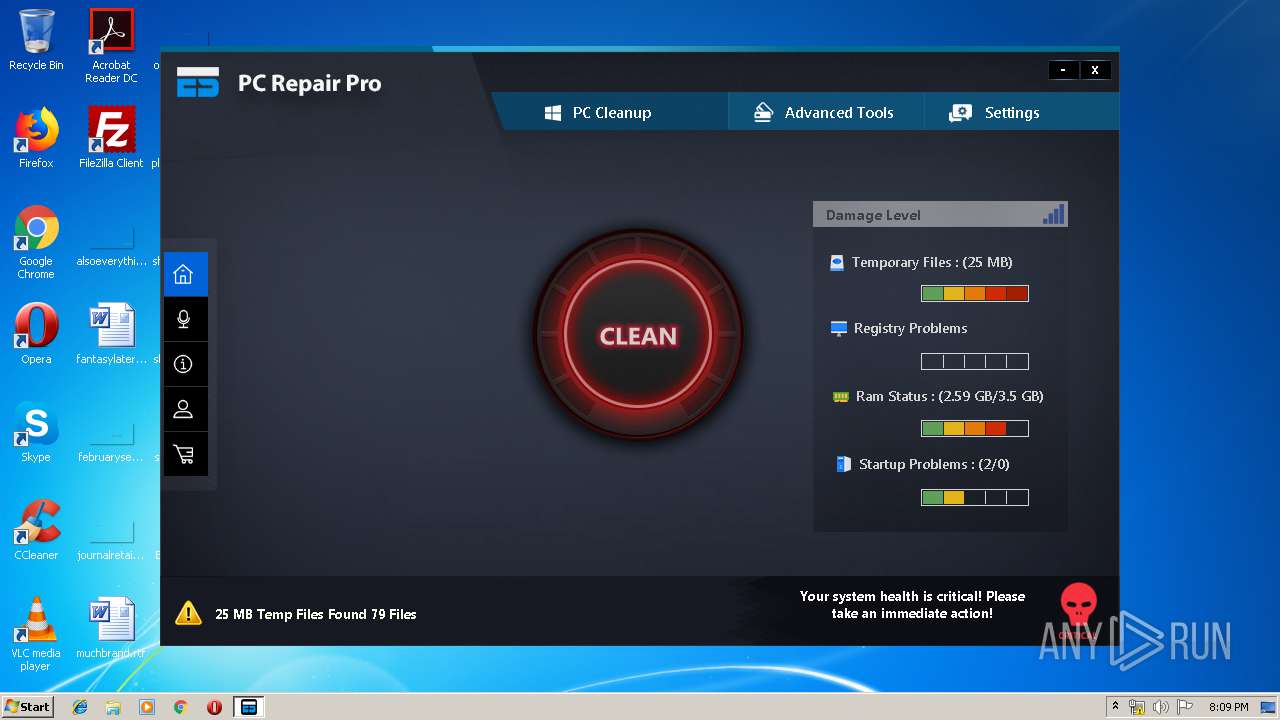
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 19:06:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7445146FB0611FBF9DE44287C4A7C0E0 |
| SHA1: | 5670AC87AFEAFD0C624DA641BB30E99E64718F7C |
| SHA256: | 770A99966FCD98F6B5BD542FC3F55158F92CCB0D22C3279D7C1204AEF2417A82 |
| SSDEEP: | 3:N8ZLBfx2JnfDd:2zxo5 |
MALICIOUS
Application was dropped or rewritten from another process
- espcp_1.0.exe (PID: 2844)
- dl[1].exe (PID: 2880)
- dl[1].exe (PID: 3936)
- ESC.exe (PID: 3676)
- espcp_1.0.exe (PID: 3784)
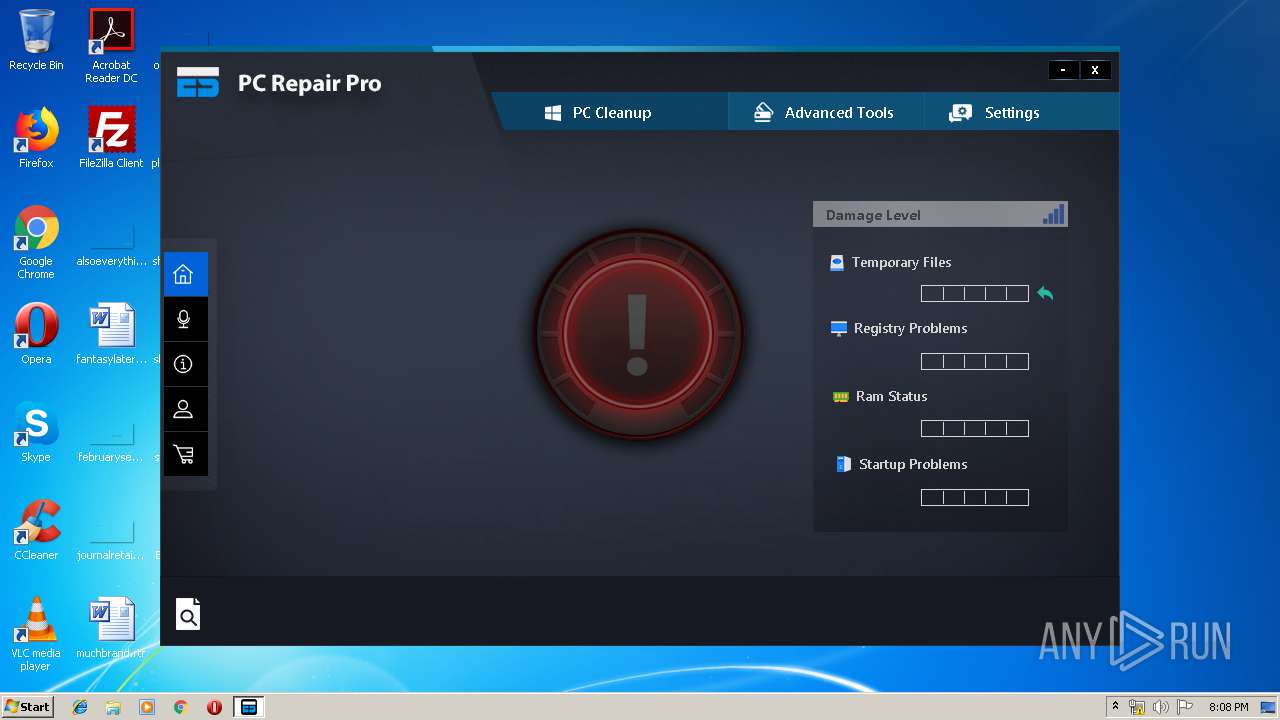
Changes settings of System certificates
- dl[1].exe (PID: 3936)
- ESC.exe (PID: 3676)
Loads the Task Scheduler DLL interface
- espcp_1.0.exe (PID: 3784)
Loads dropped or rewritten executable
- ESC.exe (PID: 3676)
SUSPICIOUS
Application launched itself
- espcp_1.0.exe (PID: 3784)
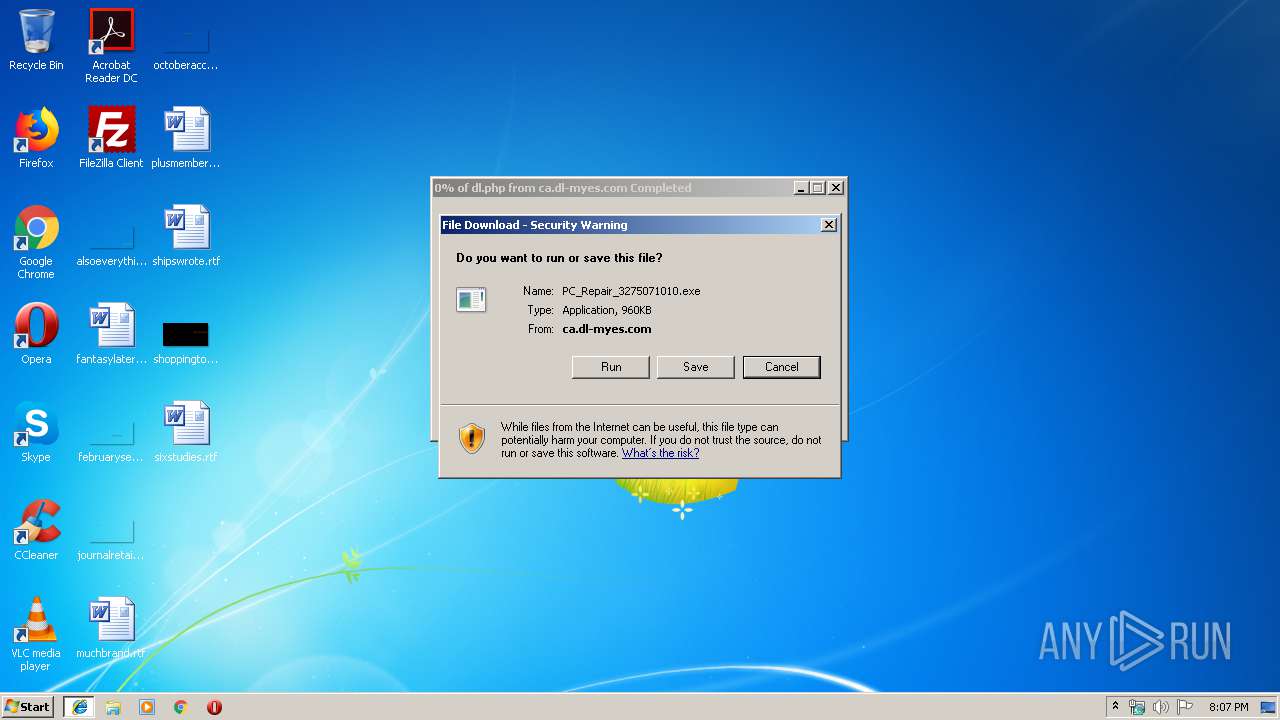
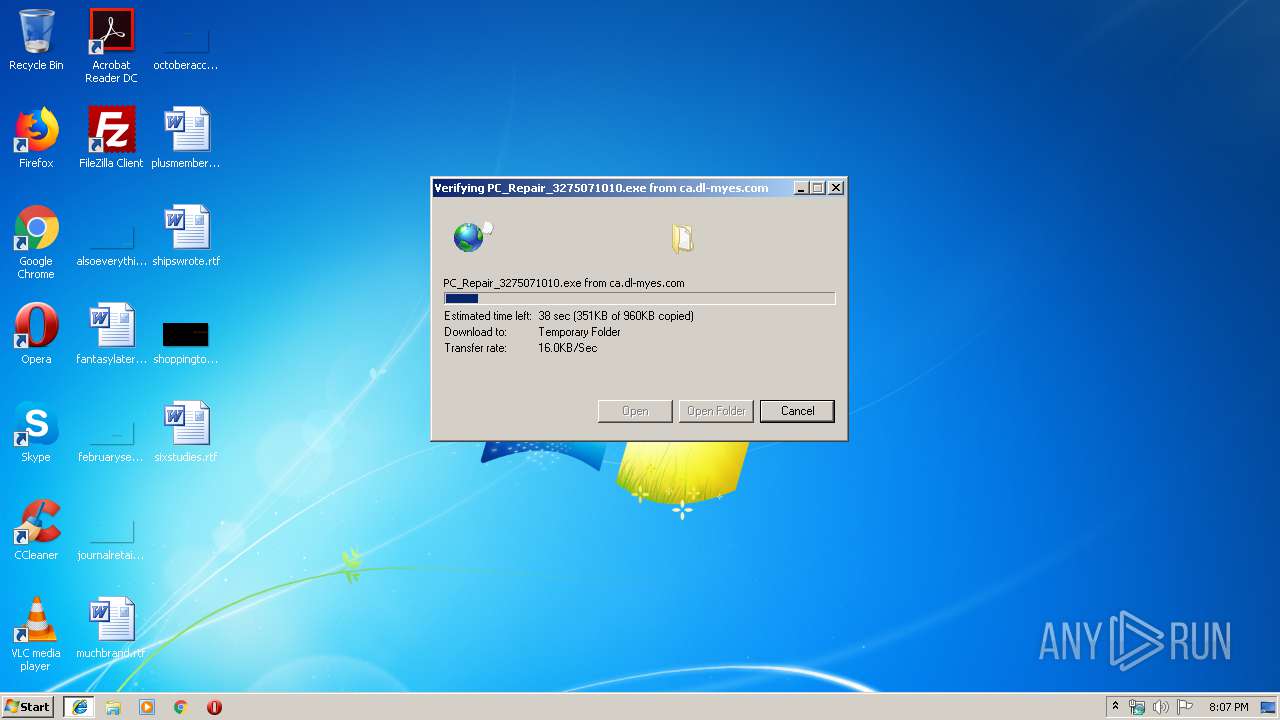
Executable content was dropped or overwritten
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 2940)
- msiexec.exe (PID: 3728)
- espcp_1.0.exe (PID: 2844)
- espcp_1.0.exe (PID: 3784)
- dl[1].exe (PID: 3936)
Adds / modifies Windows certificates
- dl[1].exe (PID: 3936)
- ESC.exe (PID: 3676)
Creates files in the user directory
- espcp_1.0.exe (PID: 3784)
- MsiExec.exe (PID: 3428)
Changes the autorun value in the registry
- msiexec.exe (PID: 3728)
Creates files in the Windows directory
- msiexec.exe (PID: 3728)
Creates files in the program directory
- espcp_1.0.exe (PID: 2844)
- ESC.exe (PID: 3676)
Reads Environment values
- ESC.exe (PID: 3676)
Reads CPU info
- ESC.exe (PID: 3676)
INFO
Application launched itself
- iexplore.exe (PID: 2940)
- msiexec.exe (PID: 3728)
Changes internet zones settings
- iexplore.exe (PID: 2940)
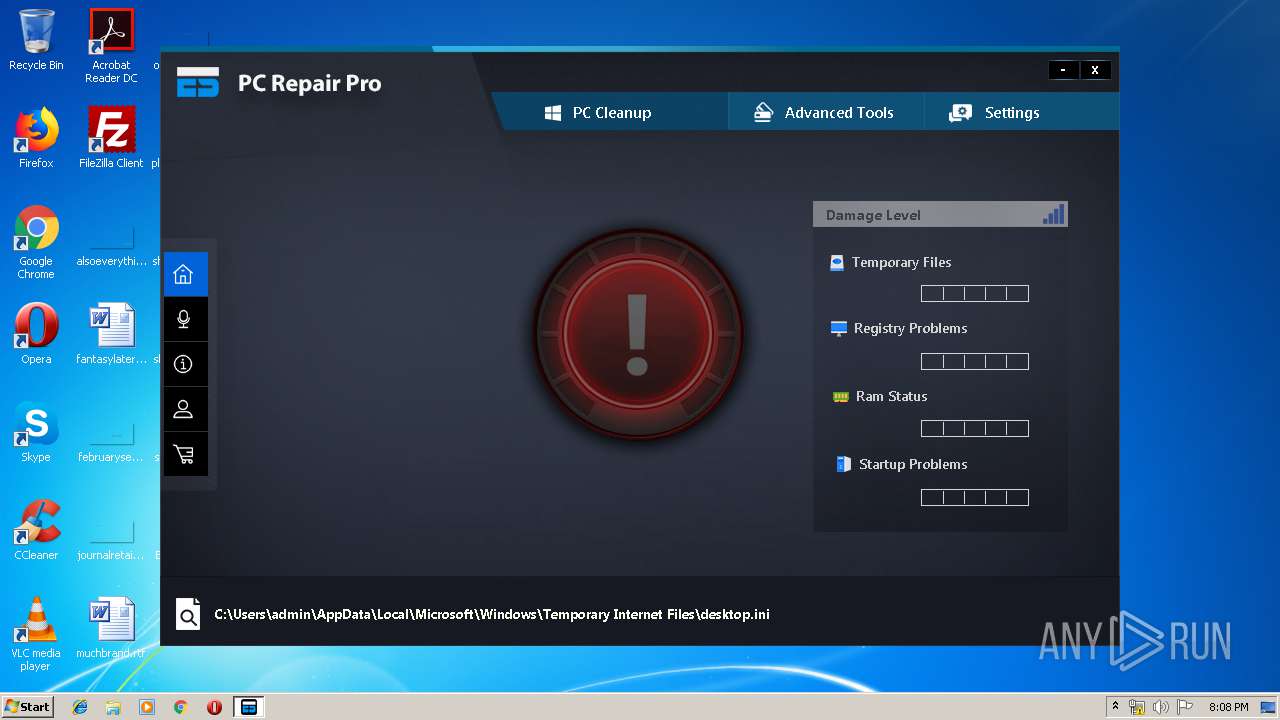
Reads Internet Cache Settings
- iexplore.exe (PID: 3176)
Creates files in the user directory
- iexplore.exe (PID: 3176)
Searches for installed software
- msiexec.exe (PID: 3728)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3448)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4028)
- MsiExec.exe (PID: 3428)
Creates files in the program directory
- msiexec.exe (PID: 3728)
Creates a software uninstall entry
- msiexec.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
12
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
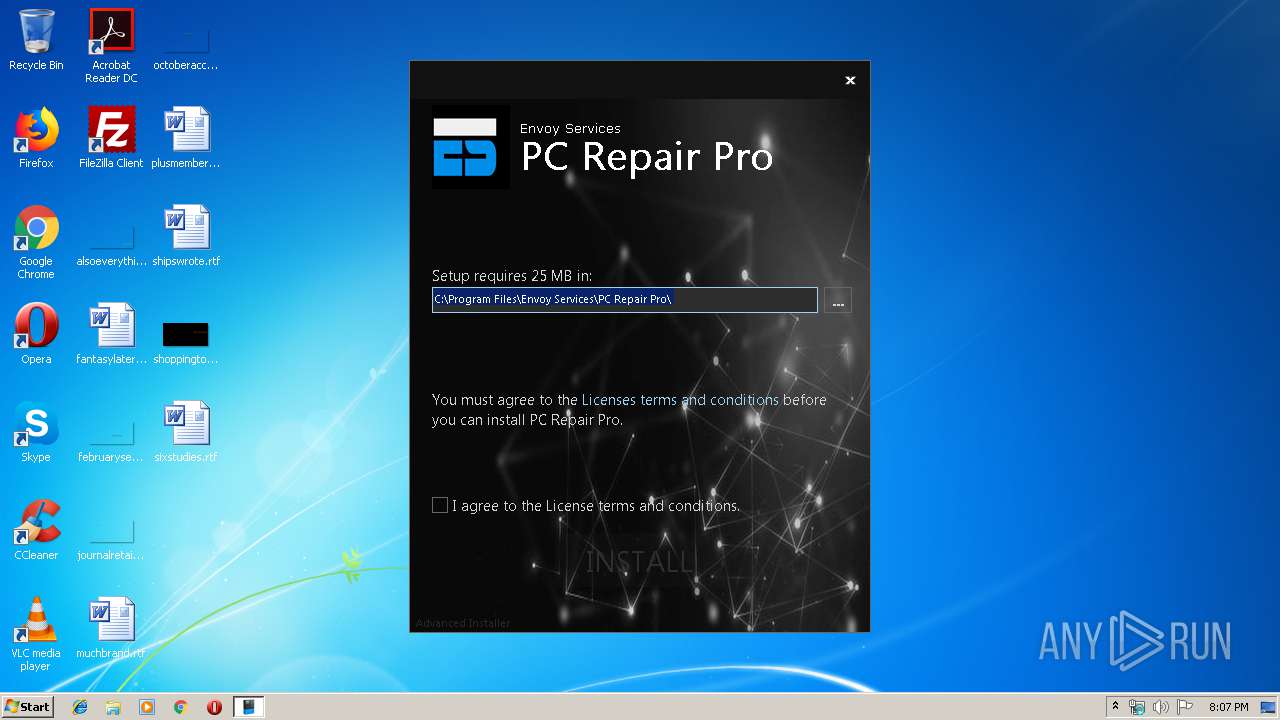
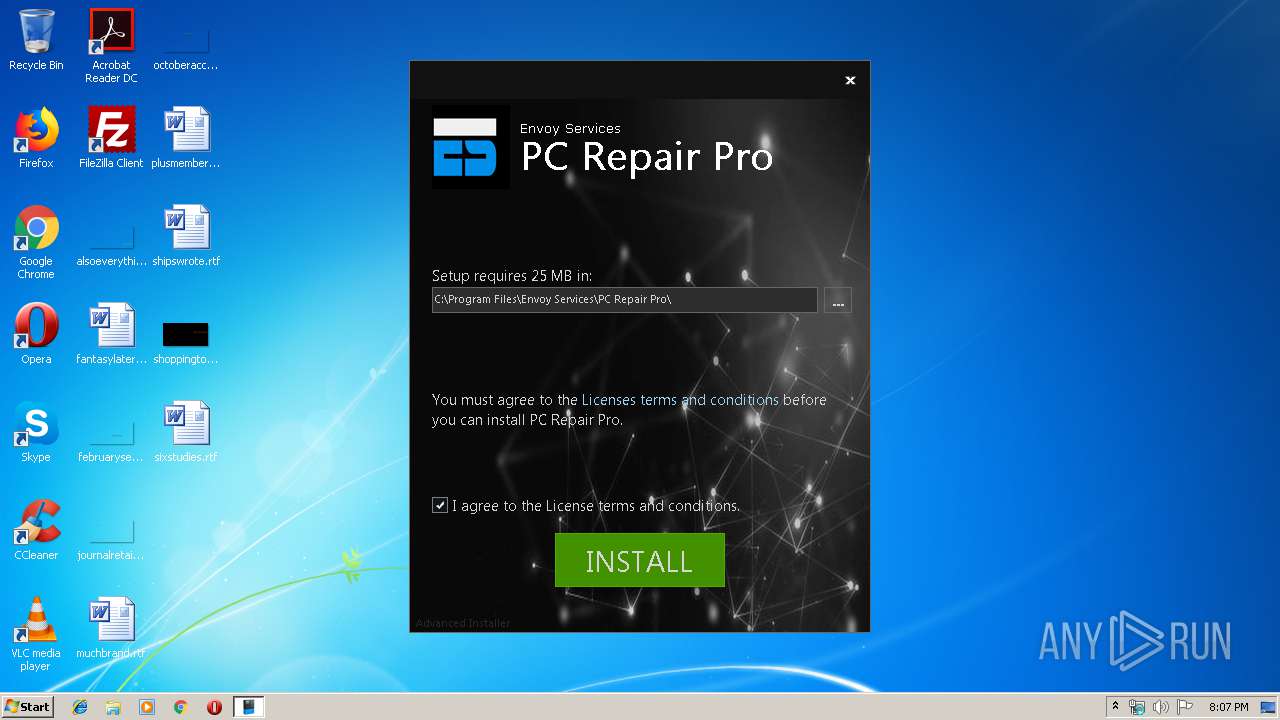
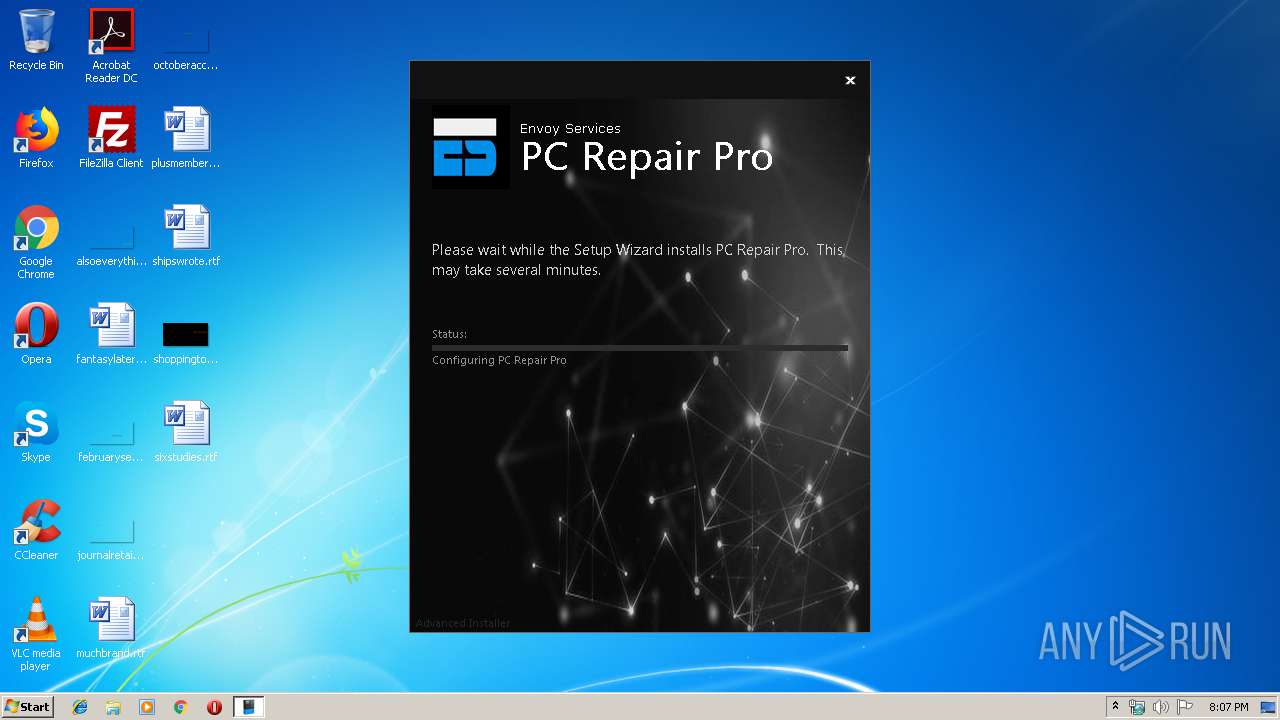
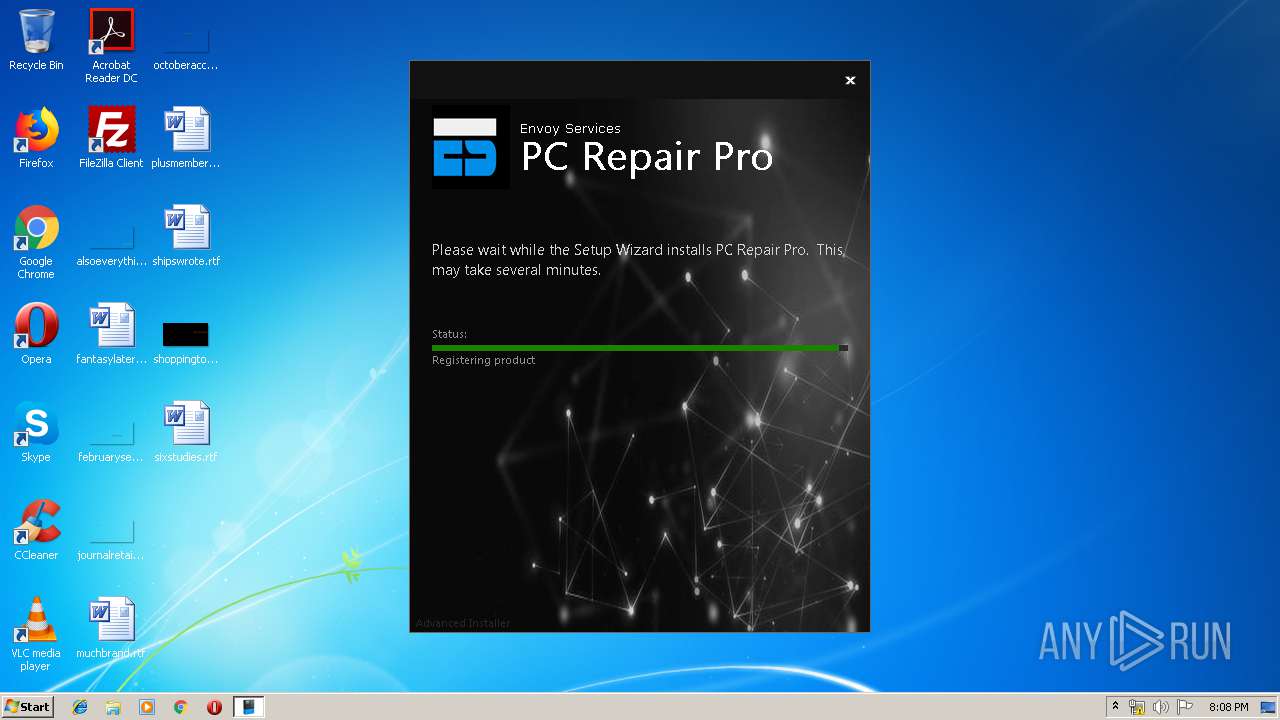
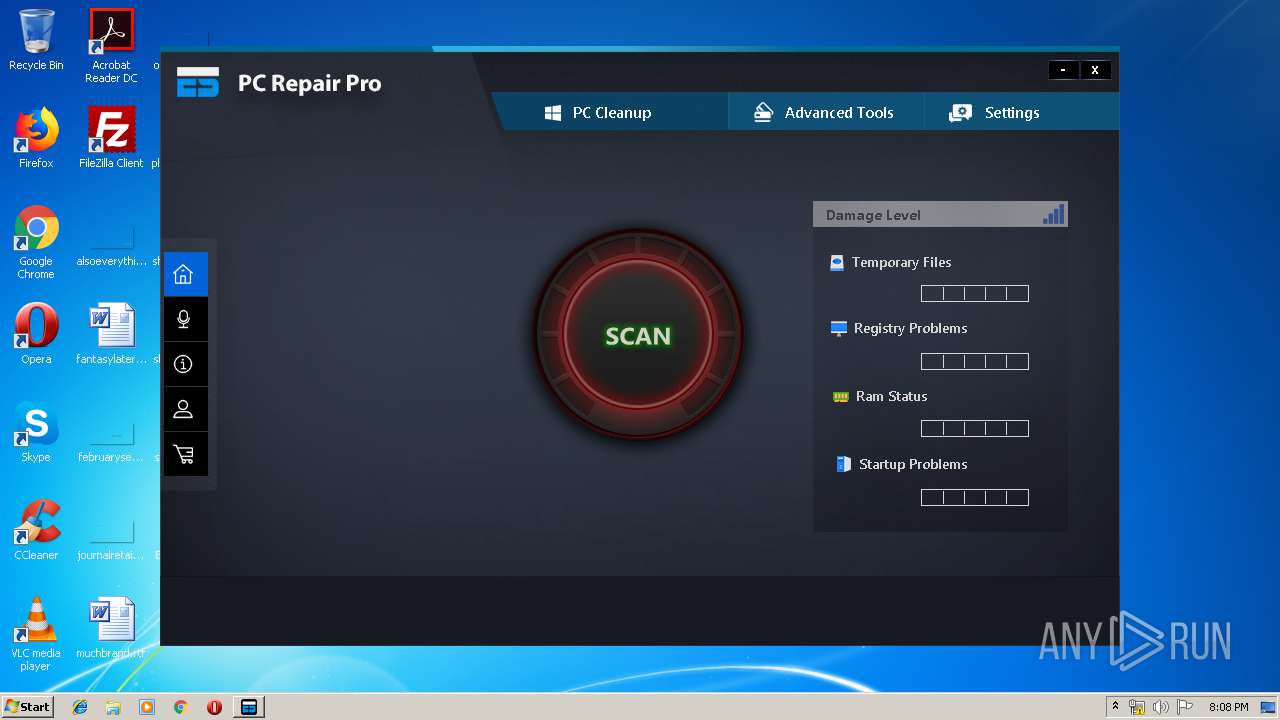
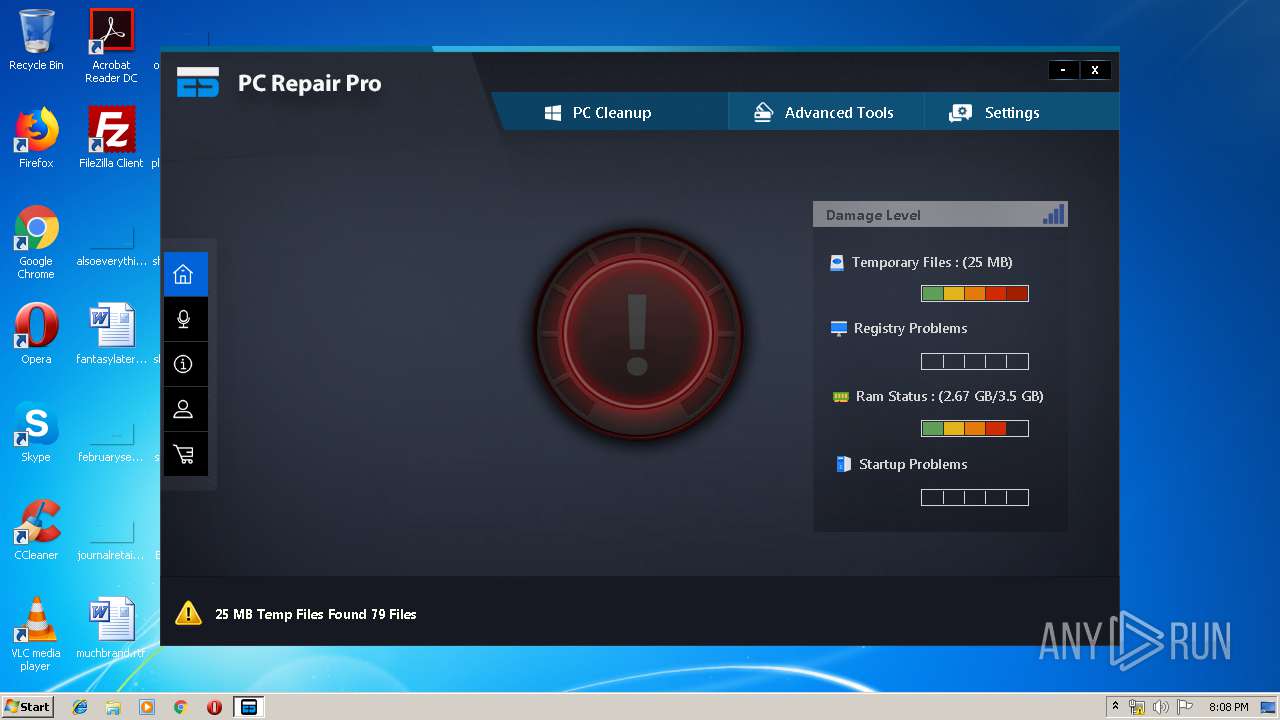
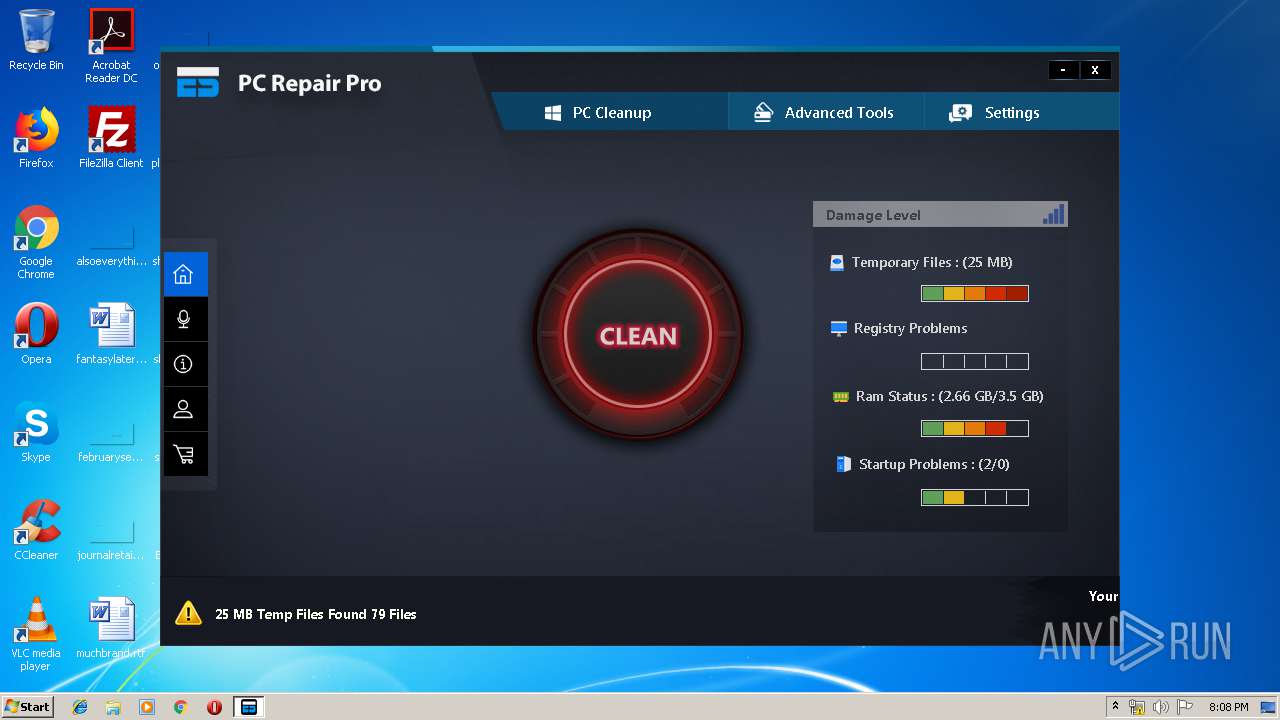
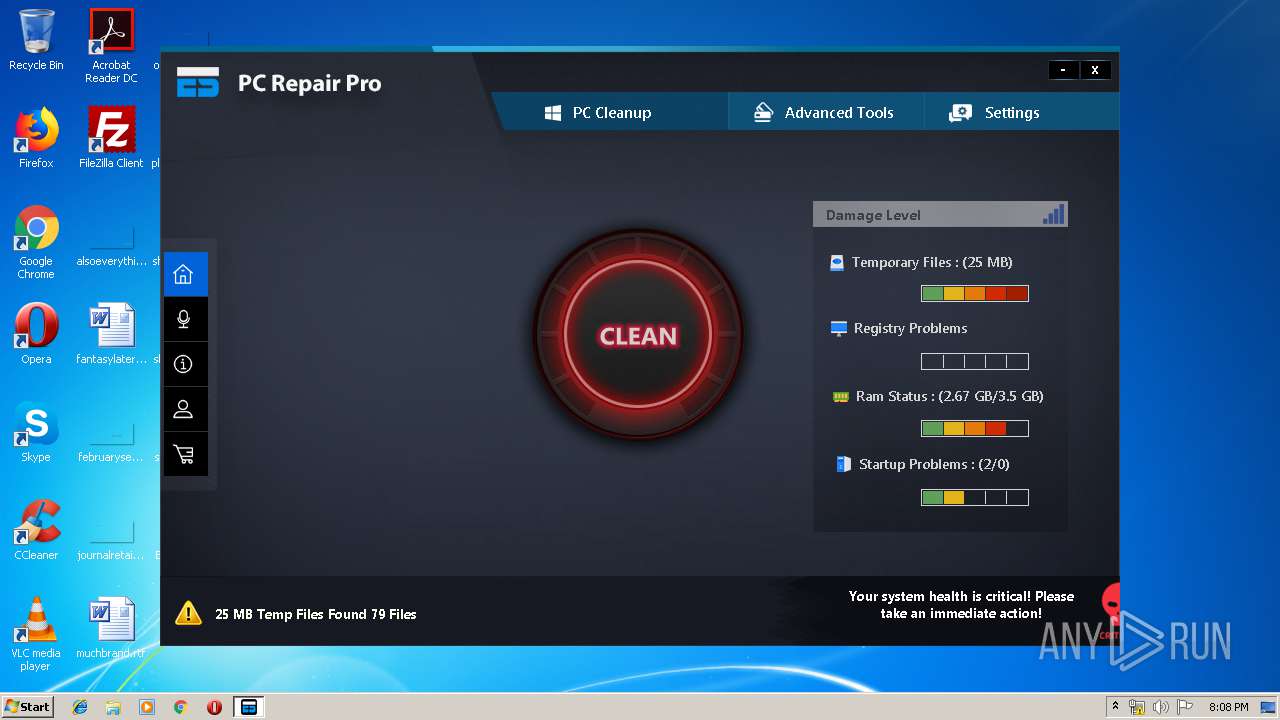
| 2844 | "C:\Users\admin\AppData\Local\Temp\espcp_1.0.exe" /i "C:\Users\admin\AppData\Roaming\Envoy Services\PC Repair Pro 1.0.0\install\UCleaner.msi" AI_EUIMSI=1 APPDIR="C:\Program Files\Envoy Services\PC Repair Pro" CLIENTPROCESSID="3784" SECONDSEQUENCE="1" CHAINERUIPROCESSID="3784Chainer" ACTION="INSTALL" EXECUTEACTION="INSTALL" CLIENTUILEVEL="0" ADDLOCAL="MainFeature" AGREE_CHECKBOX="Yes" PRIMARYFOLDER="APPDIR" ROOTDRIVE="C:\" AI_FOUND_PREREQS=".NET Framework 4.0 (web installer)" AI_DETECTED_INTERNET_CONNECTION="1" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\espcp_1.0.exe" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\" EXE_CMD_LINE="/exenoupdates " TARGETDIR="C:\" AI_SETUPEXEPATH_ORIGINAL="C:\Users\admin\AppData\Local\Temp\espcp_1.0.exe" AI_INSTALL="1" | C:\Users\admin\AppData\Local\Temp\espcp_1.0.exe | espcp_1.0.exe | ||||||||||||
User: admin Company: Envoy Services Integrity Level: HIGH Description: PC Repair Pro Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2880 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\dl[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\dl[1].exe | — | iexplore.exe | |||||||||||
User: admin Company: Envoy Services Integrity Level: MEDIUM Description: ES Setup Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2940 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3428 | C:\Windows\system32\MsiExec.exe -Embedding CFB220B1A4A0D059990E03945E4D5342 C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3672 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "00000390" "000005C4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
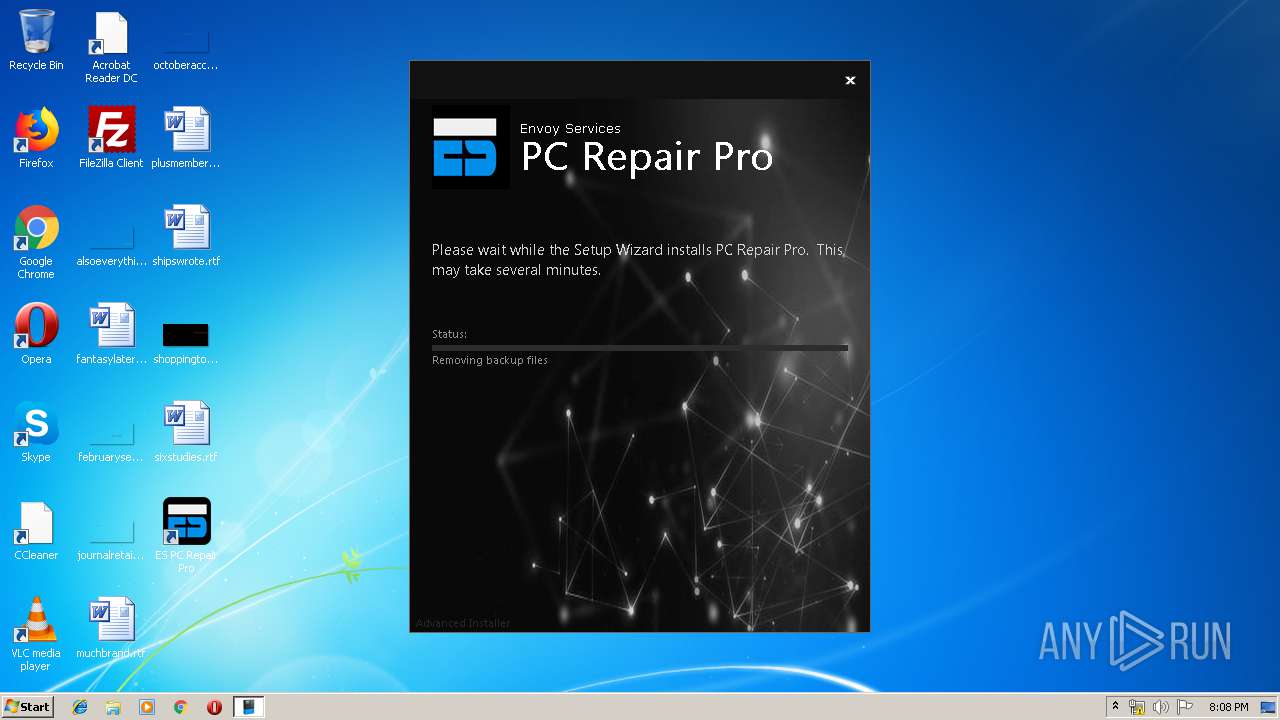
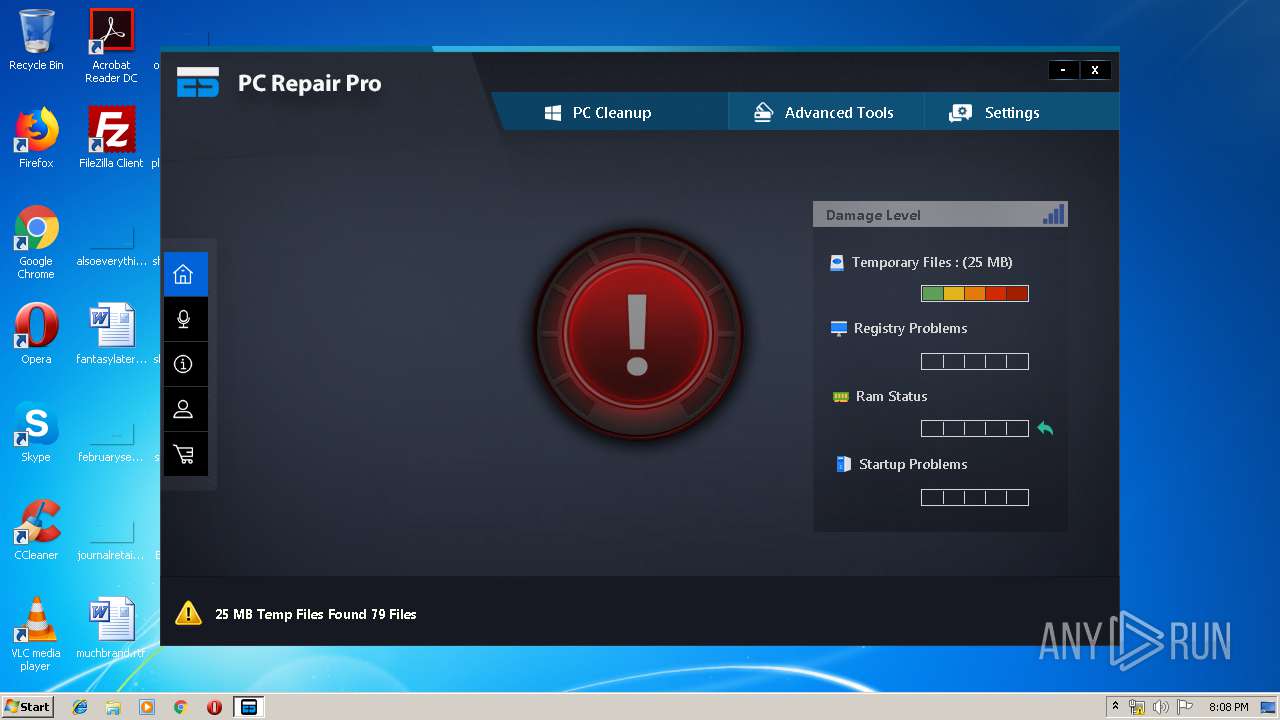
| 3676 | "C:\Program Files\Envoy Services\PC Repair Pro\ESC.exe" -rescan | C:\Program Files\Envoy Services\PC Repair Pro\ESC.exe | MsiExec.exe | ||||||||||||
User: admin Company: Enoy Services Integrity Level: HIGH Description: ES PC Repair Pro Exit code: 0 Version: 1.0.0.2 Modules
| |||||||||||||||
| 3728 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3784 | "C:\Users\admin\AppData\Local\Temp\espcp_1.0.exe" | C:\Users\admin\AppData\Local\Temp\espcp_1.0.exe | dl[1].exe | ||||||||||||
User: admin Company: Envoy Services Integrity Level: HIGH Description: PC Repair Pro Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
Total events
3 529
Read events
3 103
Write events
412
Delete events
14
Modification events
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {546777EF-678D-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307040004001900130007000D004E00 | |||
Executable files
28
Suspicious files
9
Text files
213
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF702D9F9C13EE0F72.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCA16278111BE75E2.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{546777EF-678D-11E9-B3B3-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\6BUBOLAE\PC_Repair_3275071010[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3784 | espcp_1.0.exe | C:\Users\admin\AppData\Roaming\Envoy Services\PC Repair Pro 1.0.0\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{546777F0-678D-11E9-B3B3-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3784 | espcp_1.0.exe | C:\Users\admin\AppData\Local\Temp\MSI5CE8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
10
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.186.8:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | unknown | der | 727 b | whitelisted |
— | — | GET | 200 | 2.16.186.32:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | unknown | der | 471 b | whitelisted |
3428 | MsiExec.exe | GET | 200 | 172.217.16.132:80 | http://www.google.com/ | US | html | 13.9 Kb | malicious |
3428 | MsiExec.exe | GET | 200 | 172.217.16.132:80 | http://www.google.com/ | US | html | 13.9 Kb | malicious |
2940 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2940 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3176 | iexplore.exe | 54.39.23.247:443 | ca.dl-myes.com | OVH SAS | FR | unknown |
3936 | dl[1].exe | 46.4.74.228:443 | dl-myes.com | Hetzner Online GmbH | DE | unknown |
3936 | dl[1].exe | 54.37.155.185:443 | fr.dl-myes.com | OVH SAS | FR | unknown |
3428 | MsiExec.exe | 172.217.16.132:80 | www.google.com | Google Inc. | US | whitelisted |
— | — | 2.16.186.32:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
3676 | ESC.exe | 104.20.62.85:443 | wyday.com | Cloudflare Inc | US | shared |
3676 | ESC.exe | 46.4.74.228:443 | dl-myes.com | Hetzner Online GmbH | DE | unknown |
— | — | 2.16.186.8:80 | ocsp.comodoca.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ca.dl-myes.com |
| unknown |
dl-myes.com |
| unknown |
fr.dl-myes.com |
| unknown |
www.google.com |
| malicious |
wyday.com |
| unknown |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report