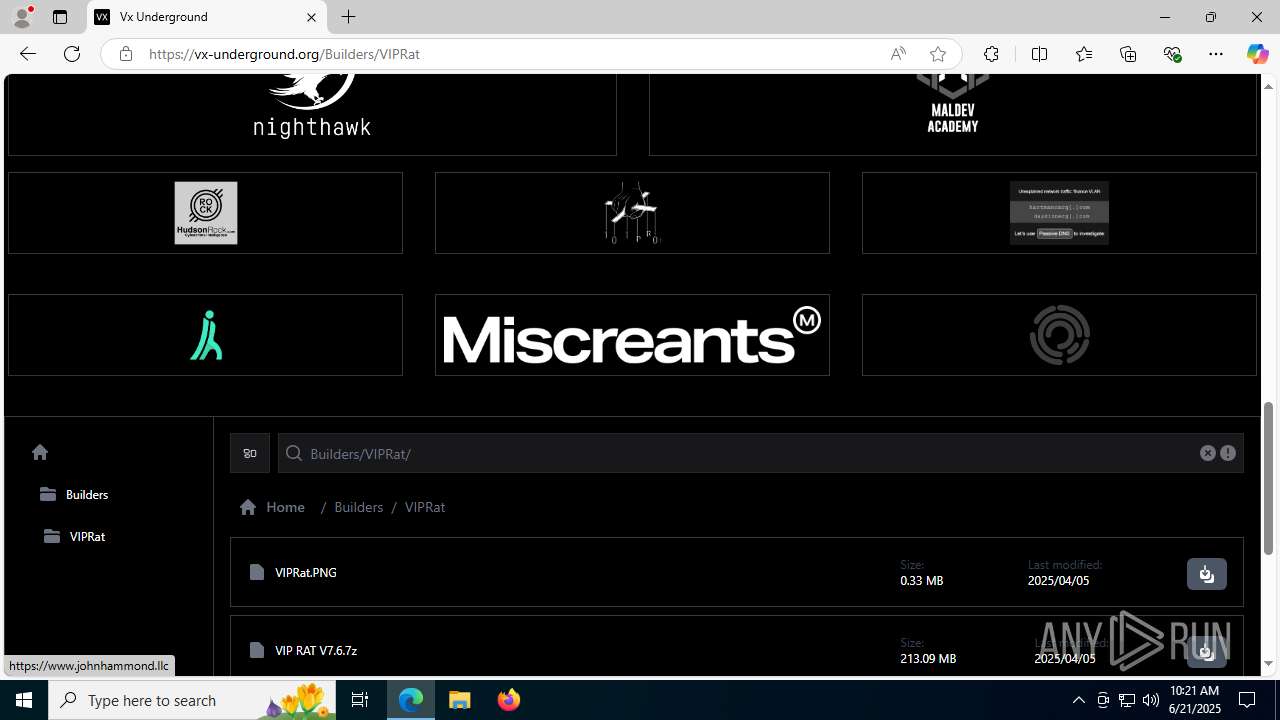
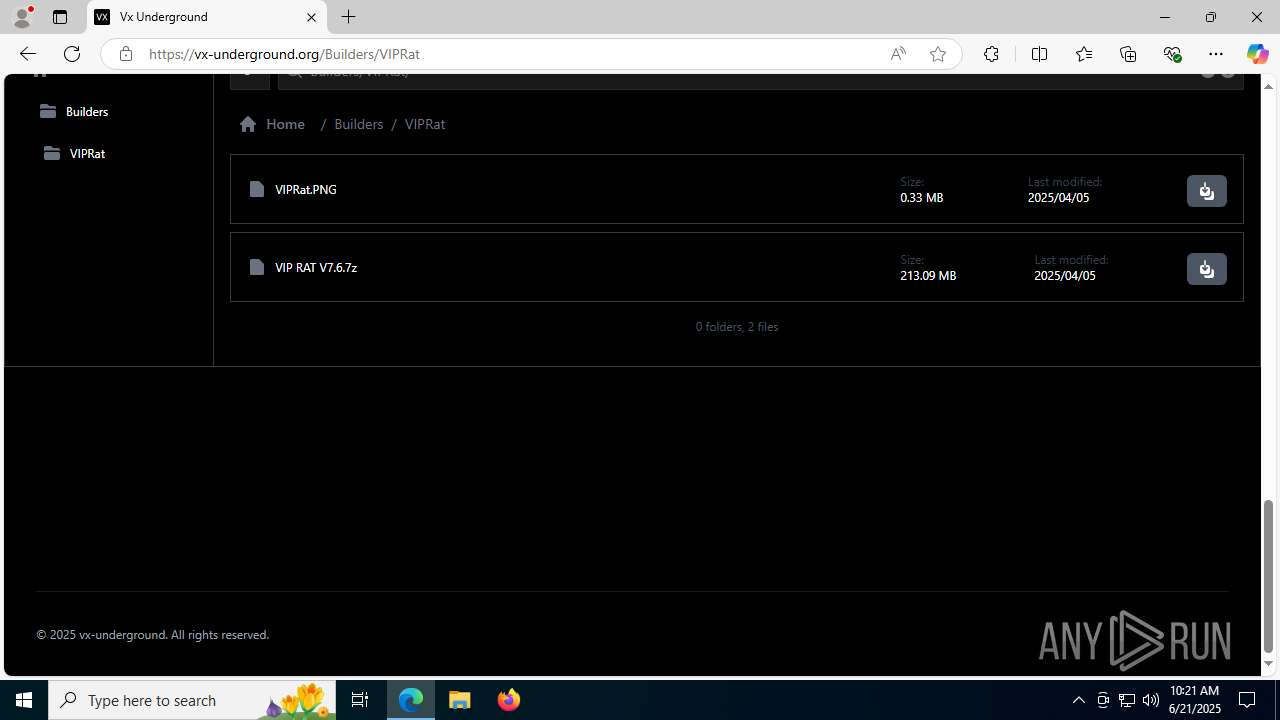
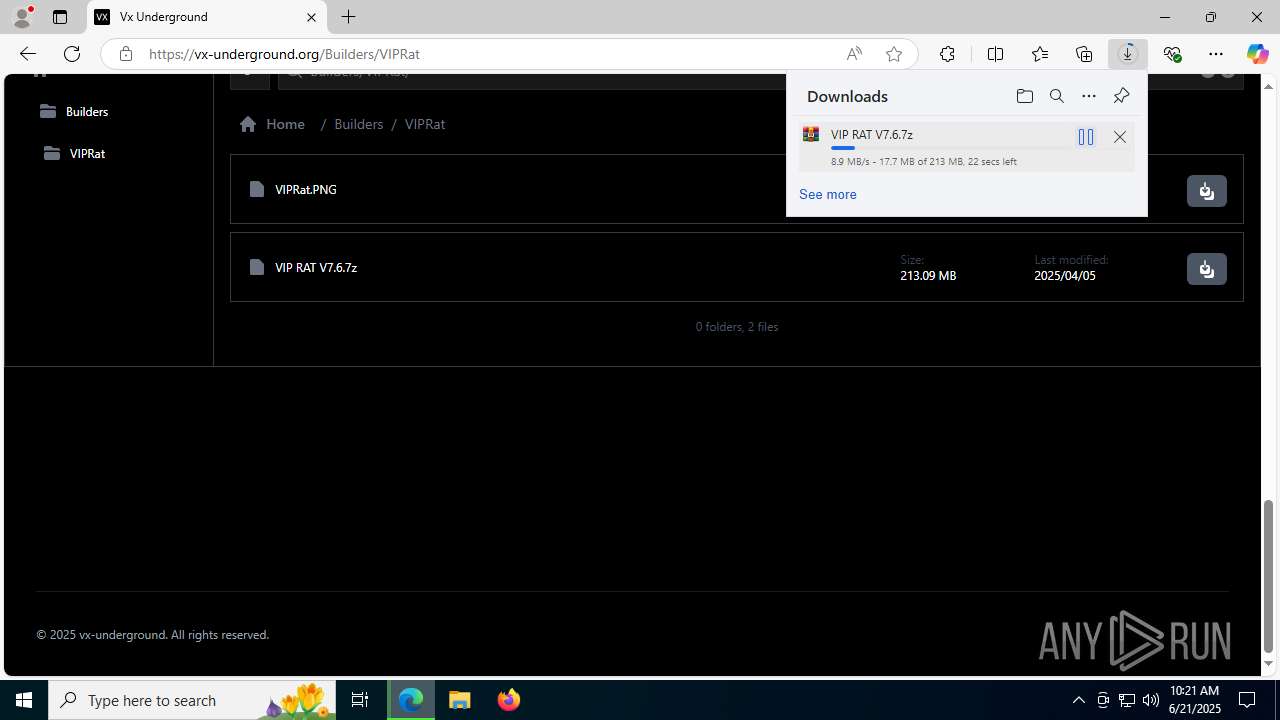
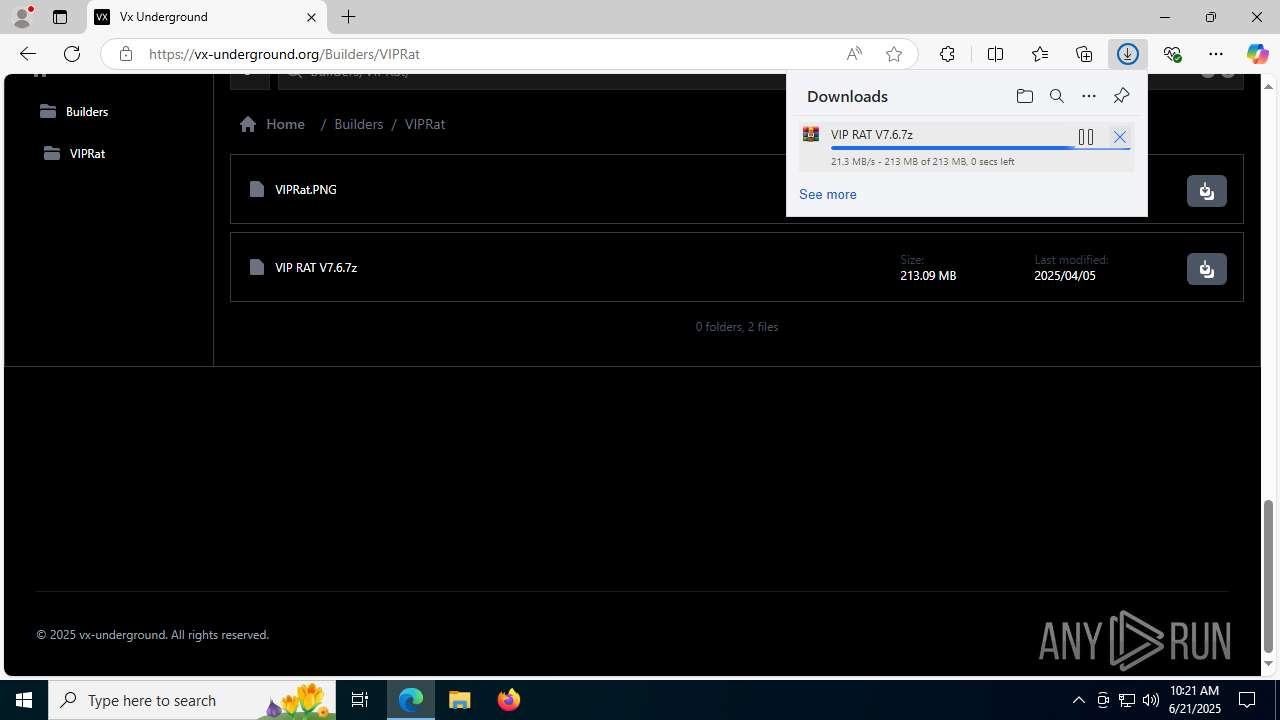
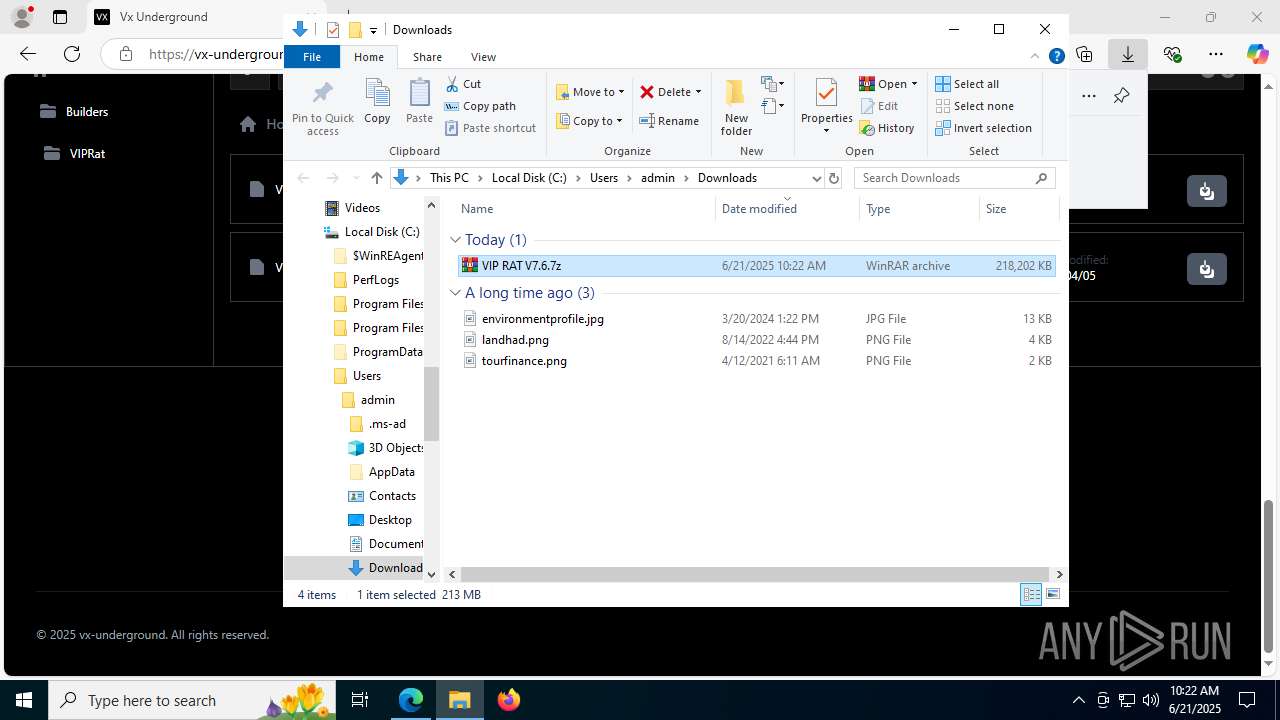
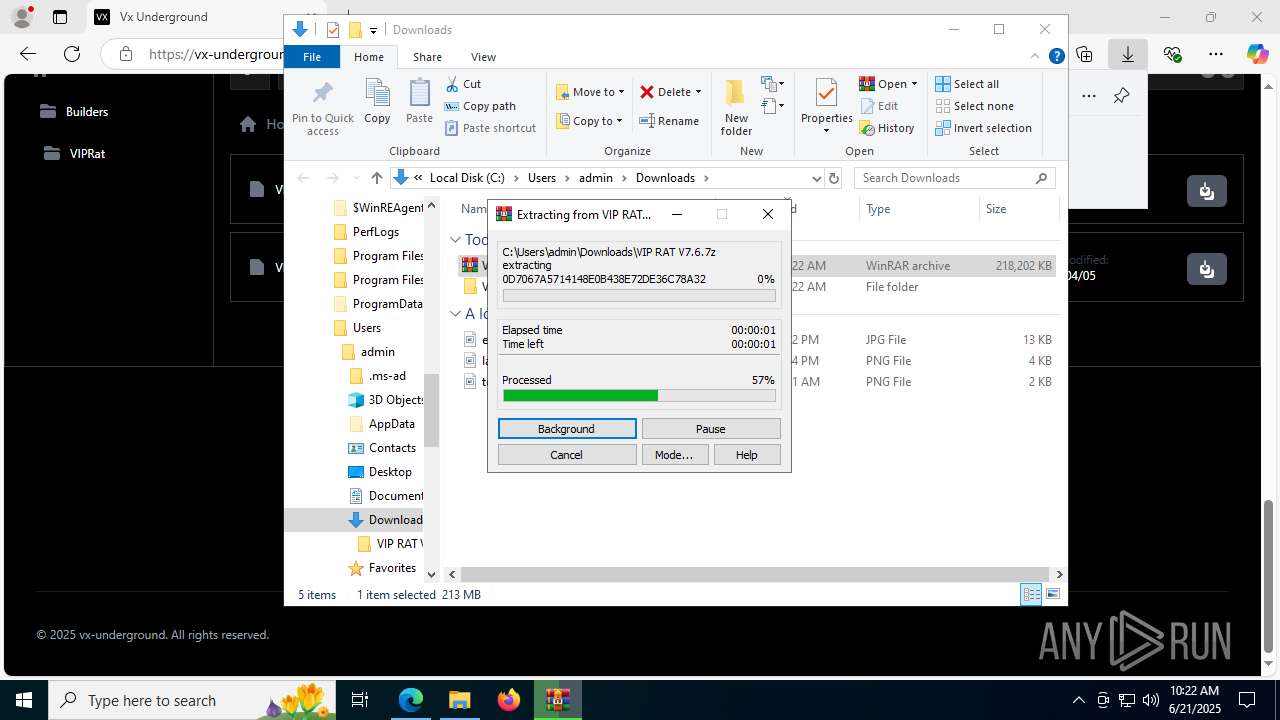
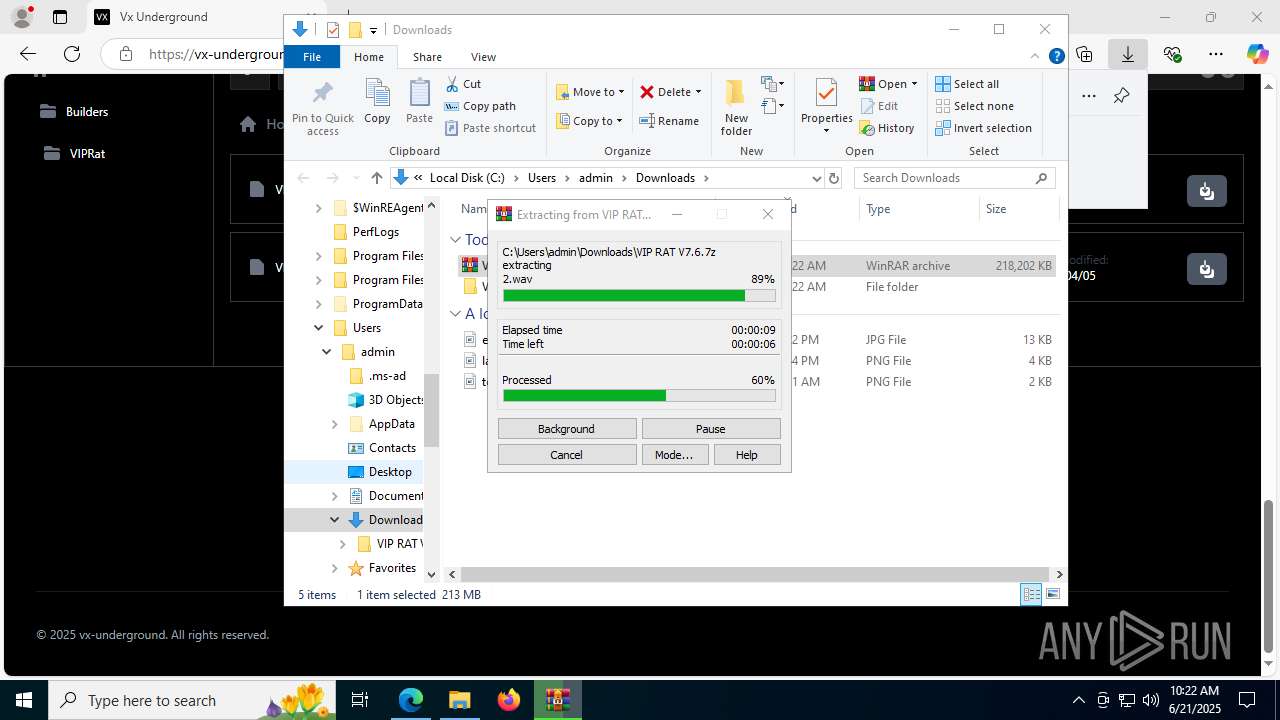
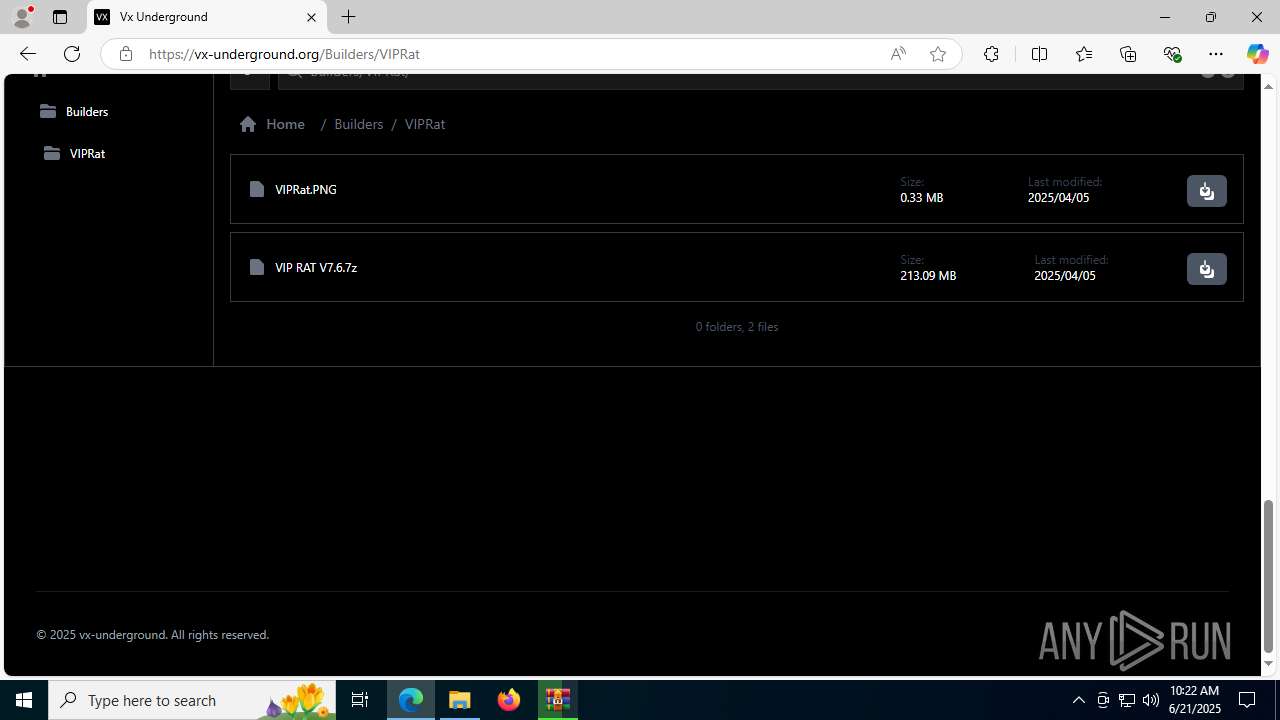
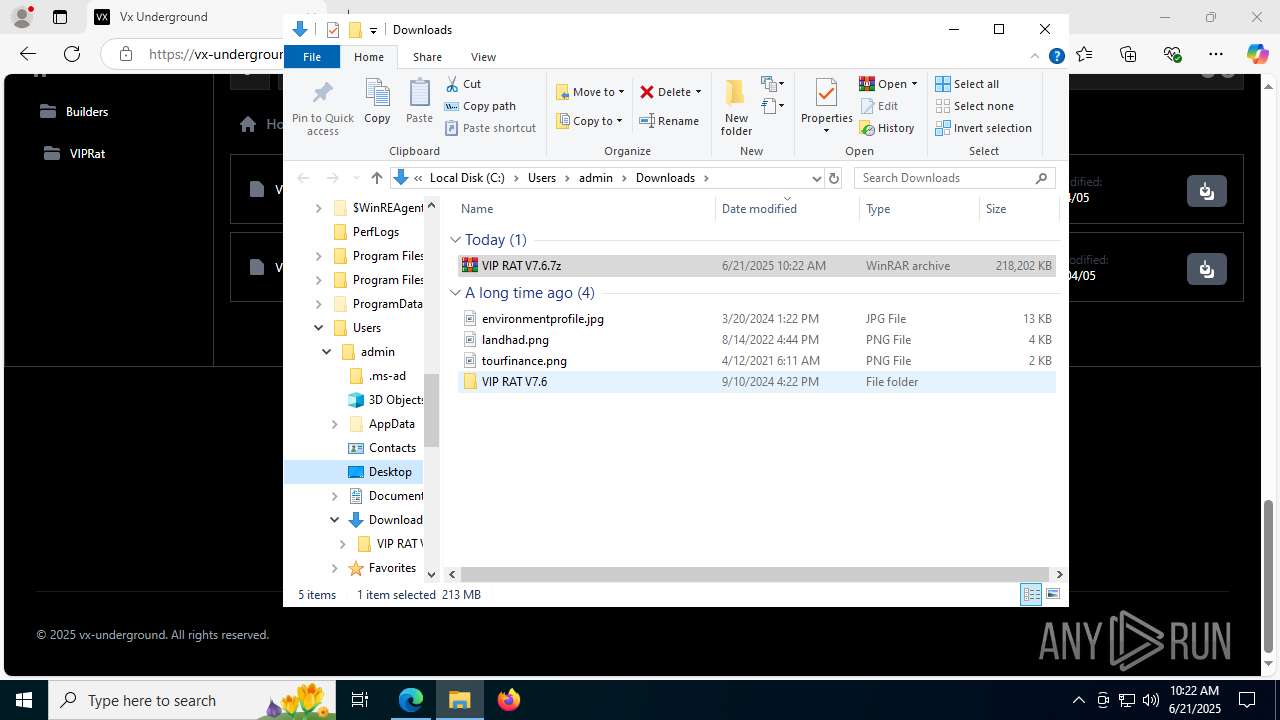
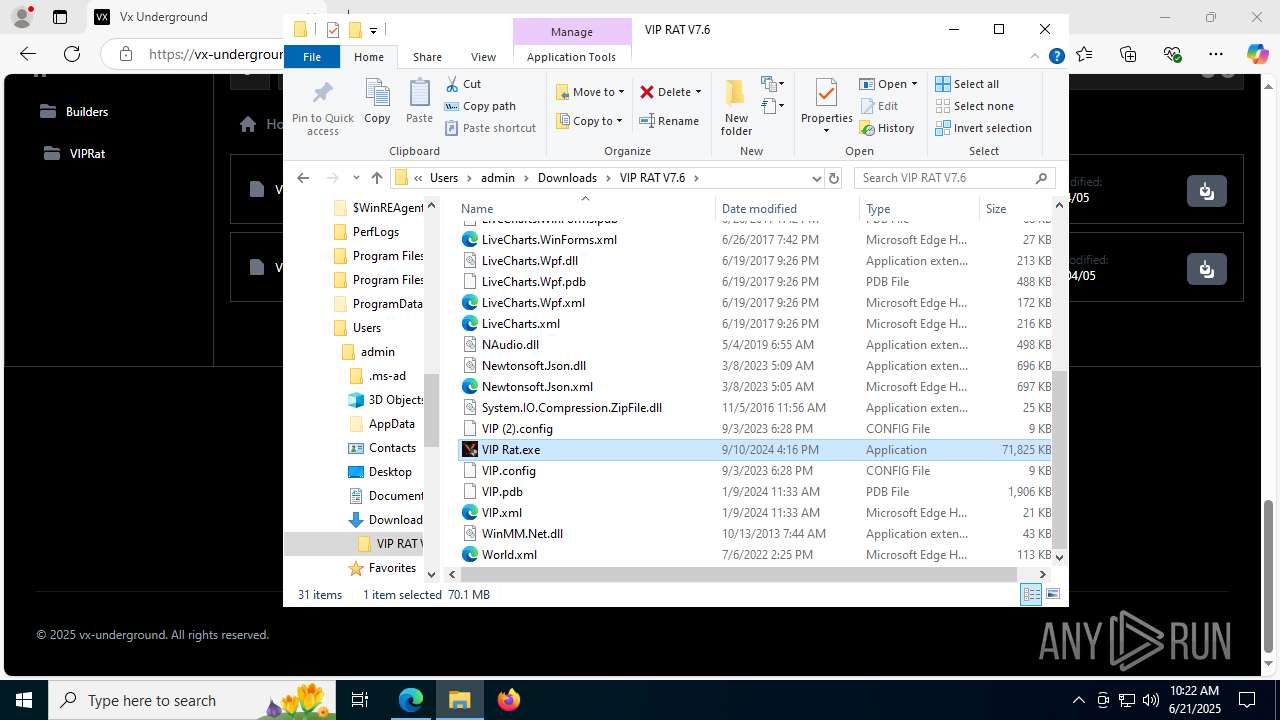
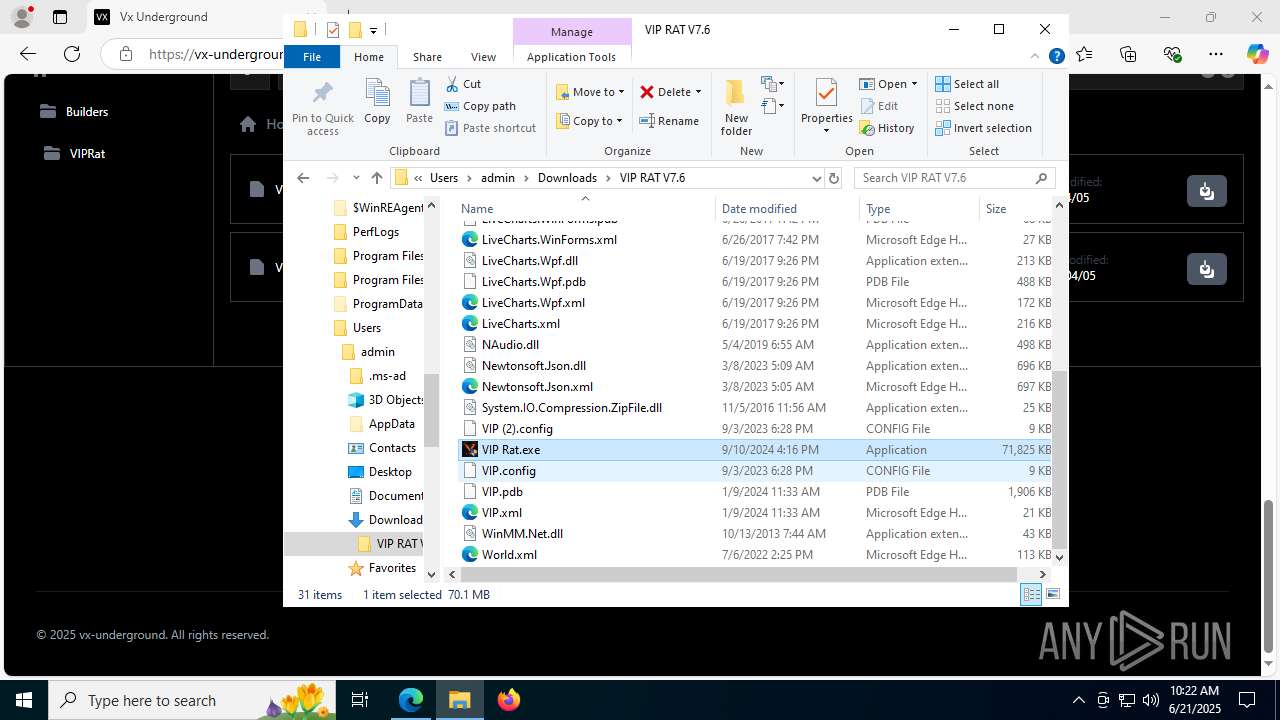
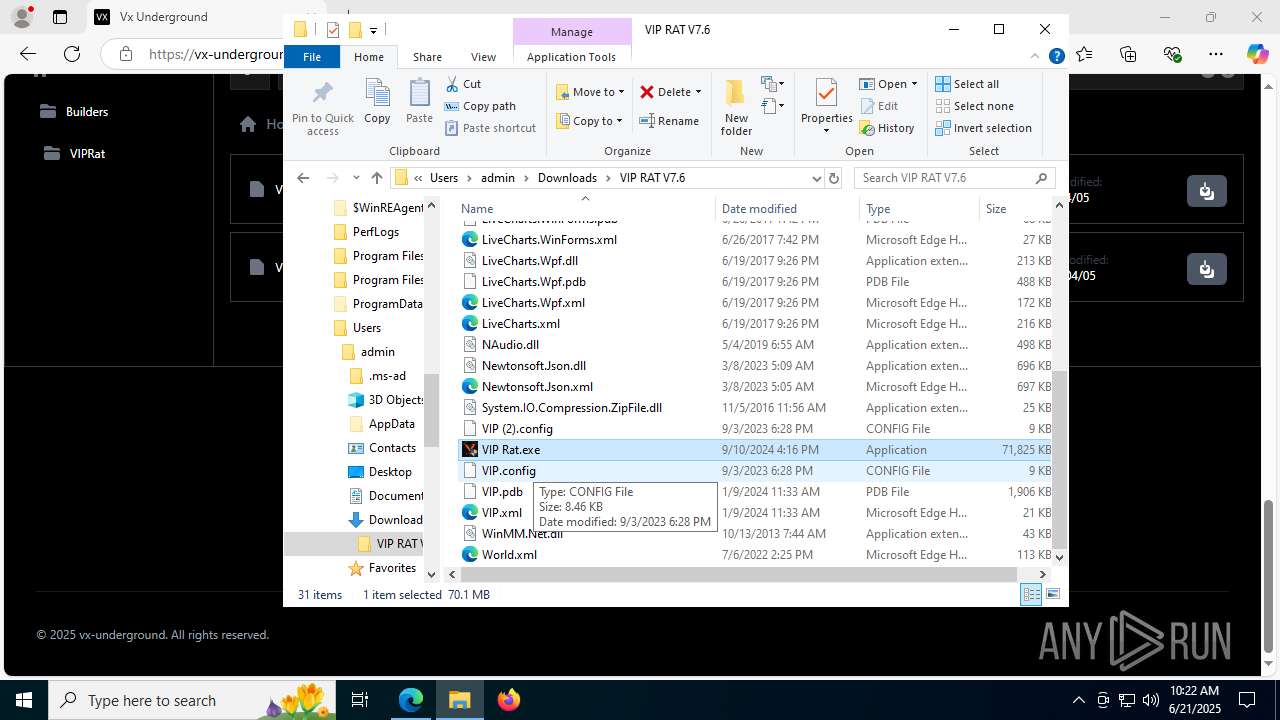
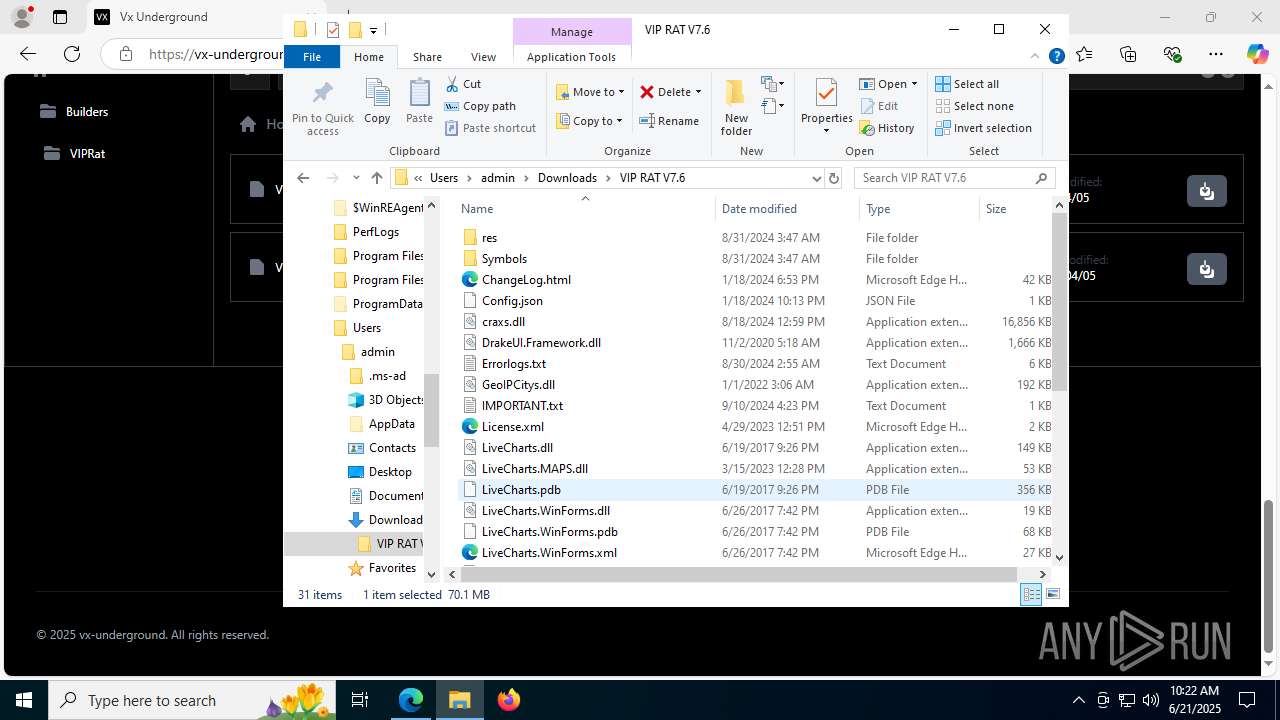
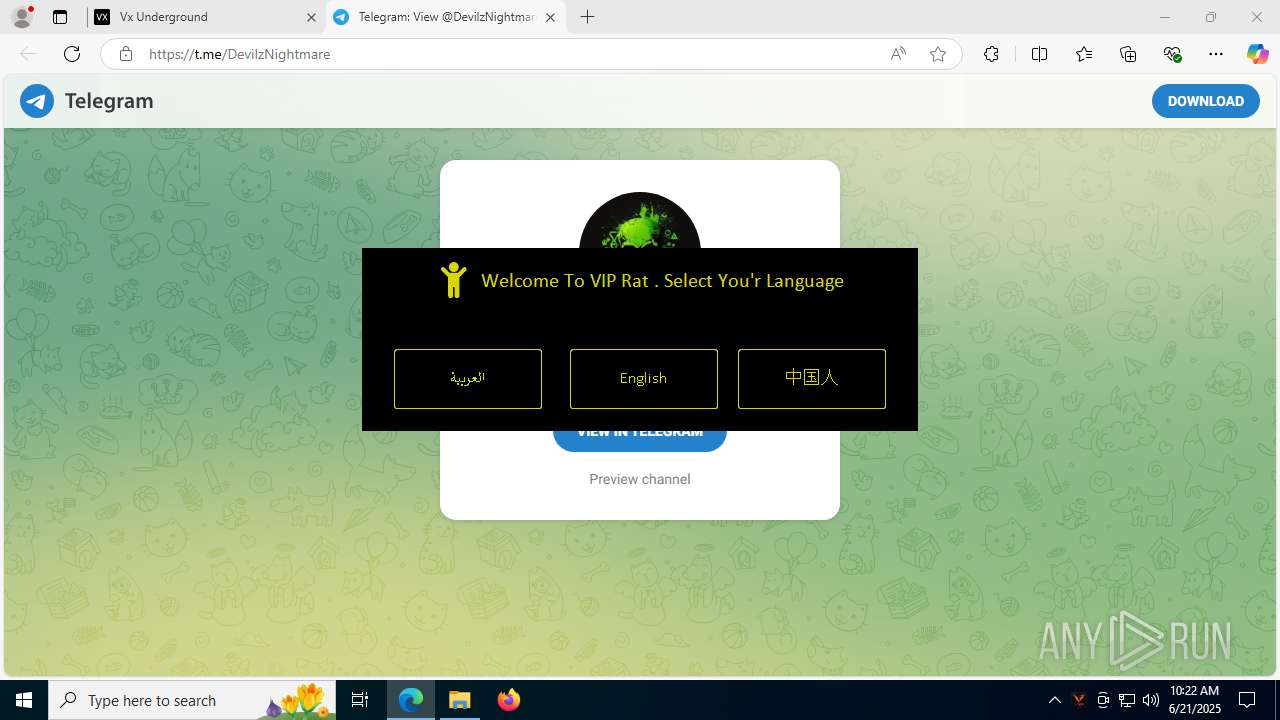
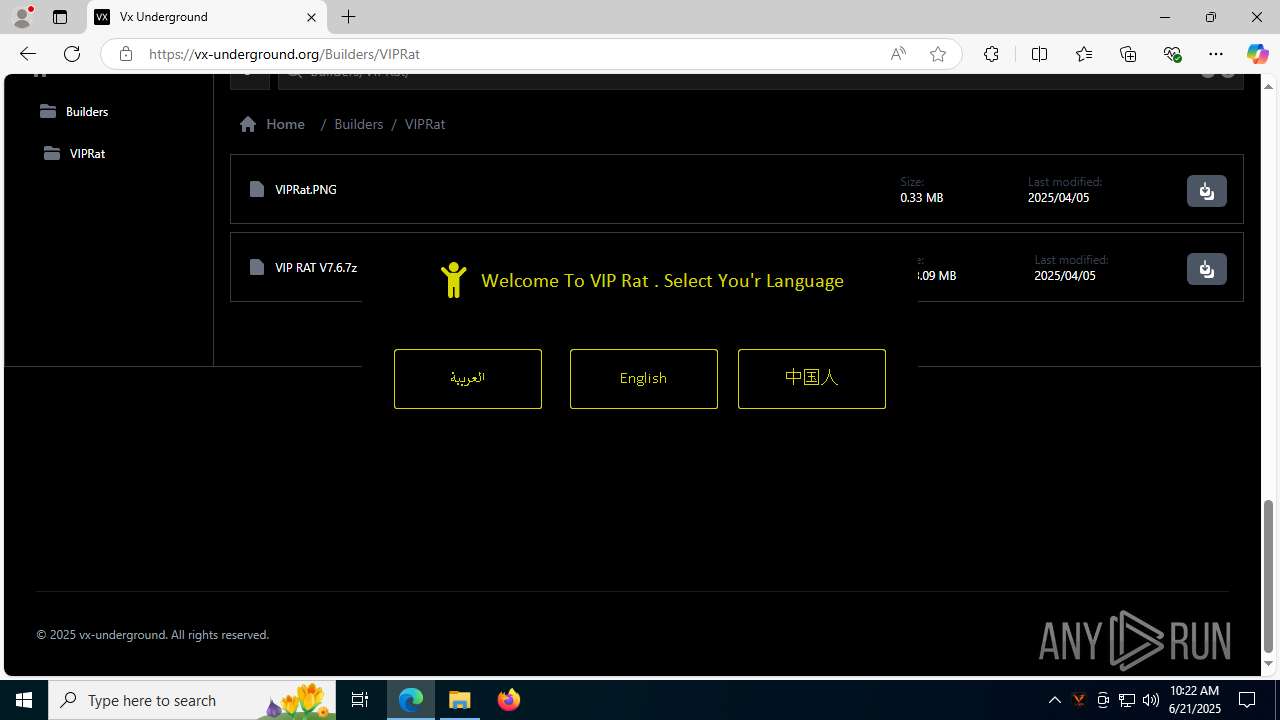
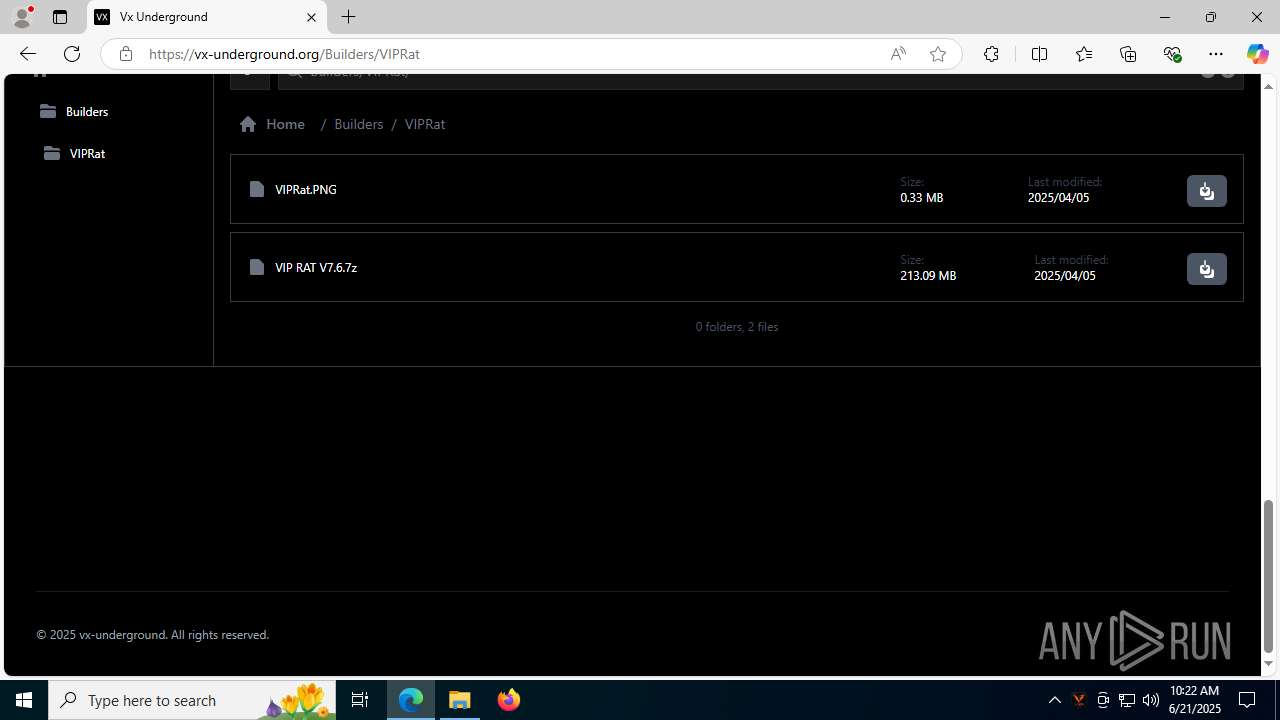
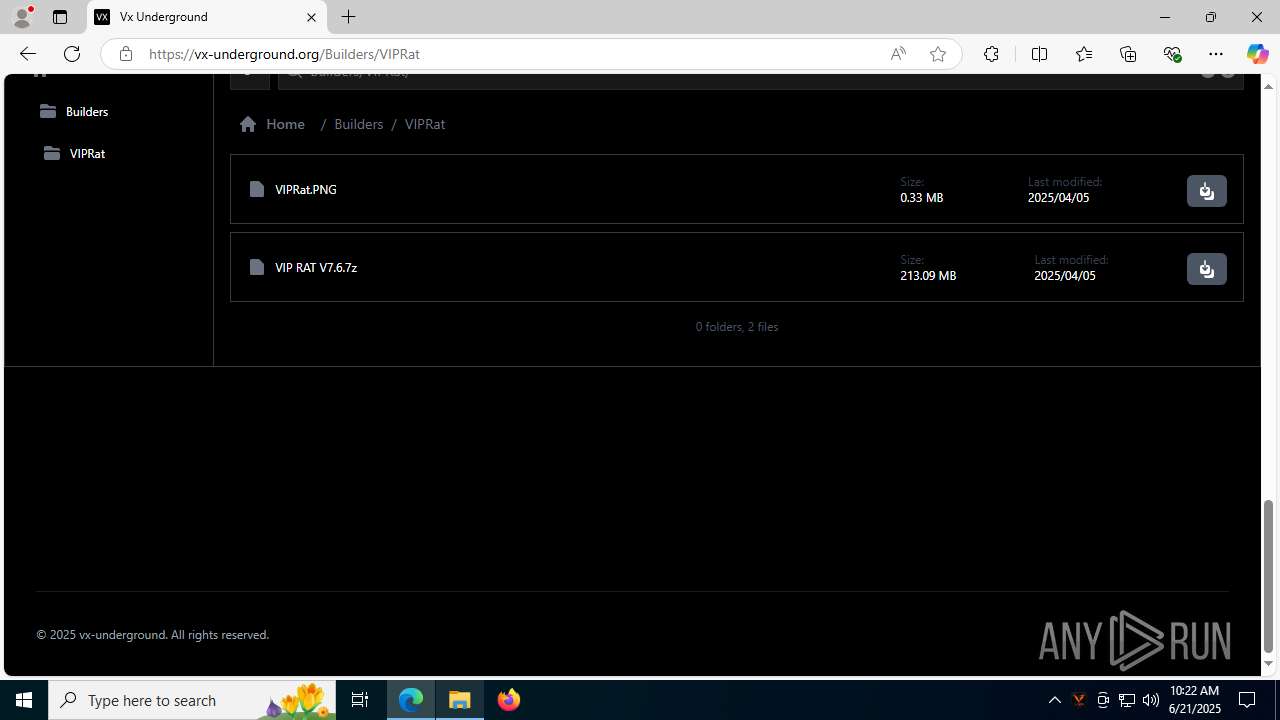
| URL: | https://vx-underground.org/Builders/VIPRat |
| Full analysis: | https://app.any.run/tasks/acec4ec1-0987-4911-8e11-3c615206a181 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 10:21:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A690B359148A8522BCF758A067E4D7B6 |
| SHA1: | 333C69CE443B6DE05B4A6932AF1749CCC790FC10 |
| SHA256: | 77074E3F642FB174765409522ABD39C294B917FE35B6163F79A78E2C8DF2941F |
| SSDEEP: | 3:N83mOUon:23mOln |
MALICIOUS
No malicious indicators.SUSPICIOUS
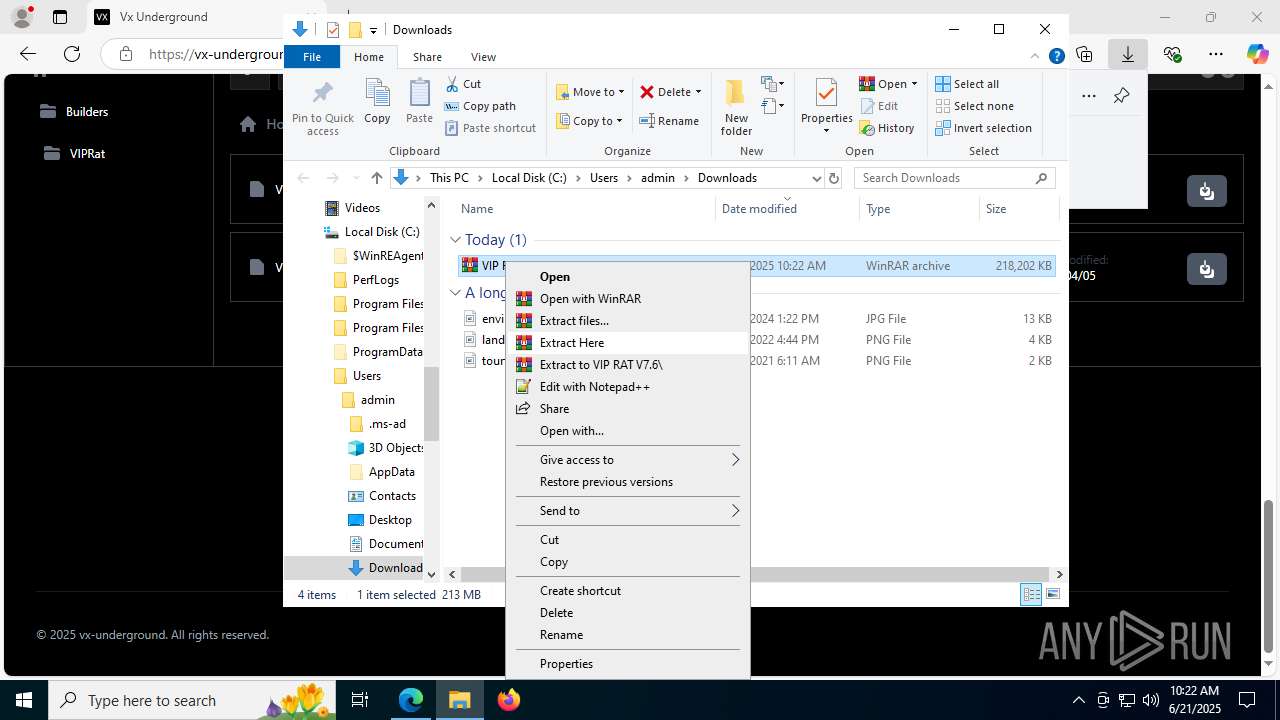
Process drops legitimate windows executable
- WinRAR.exe (PID: 7256)
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 7256)
Reads security settings of Internet Explorer
- VIP Rat.exe (PID: 5476)
INFO
Reads Environment values
- identity_helper.exe (PID: 7816)
- VIP Rat.exe (PID: 5476)
Reads the computer name
- identity_helper.exe (PID: 7816)
- VIP Rat.exe (PID: 5476)
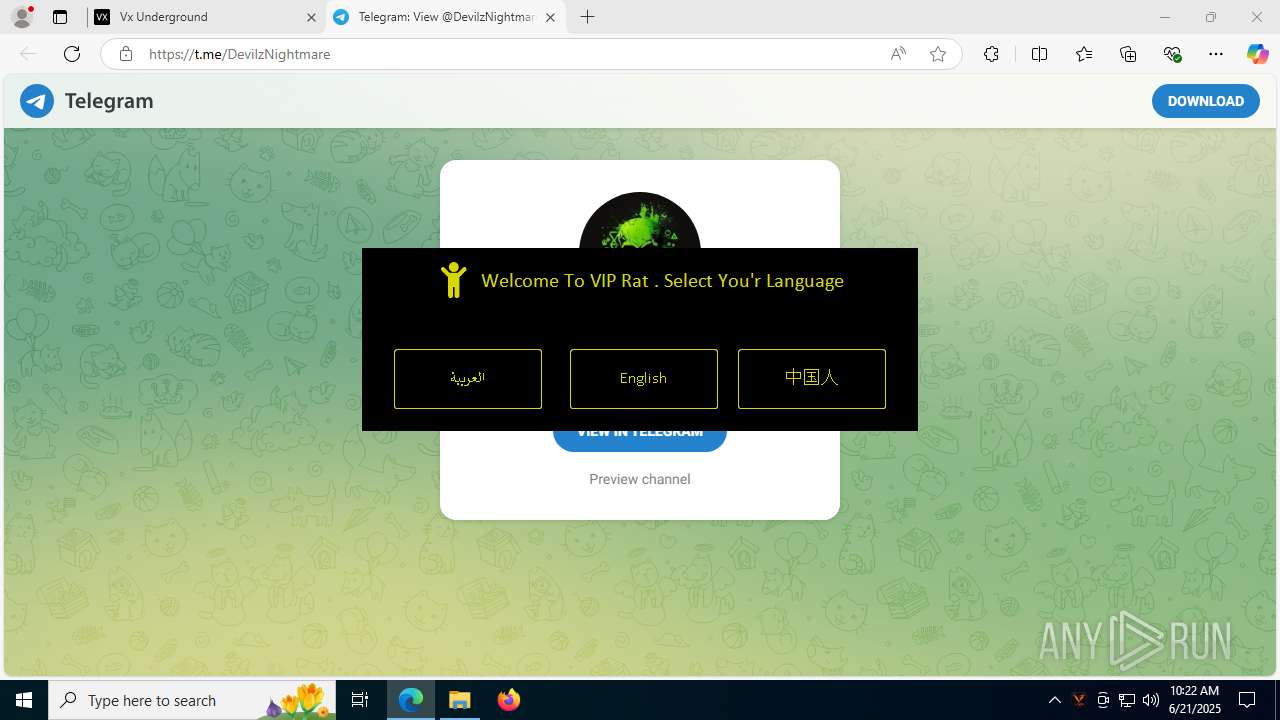
Checks supported languages
- identity_helper.exe (PID: 7816)
- VIP Rat.exe (PID: 5476)
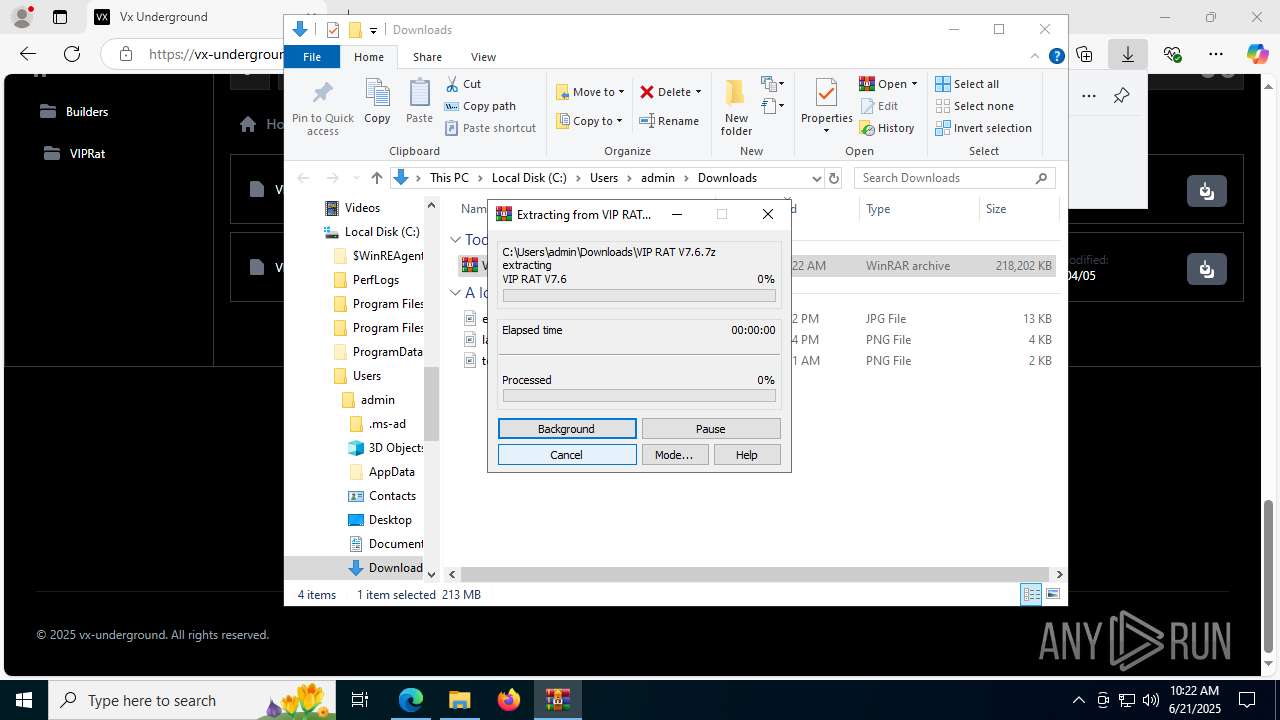
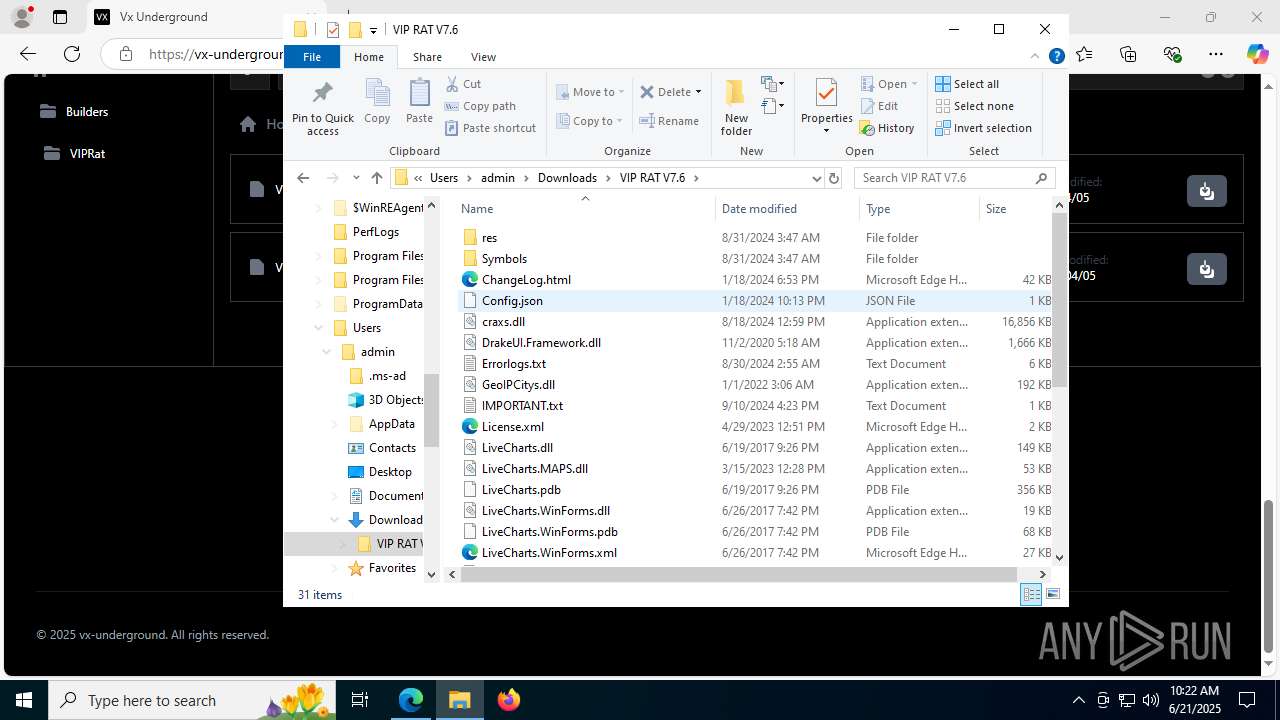
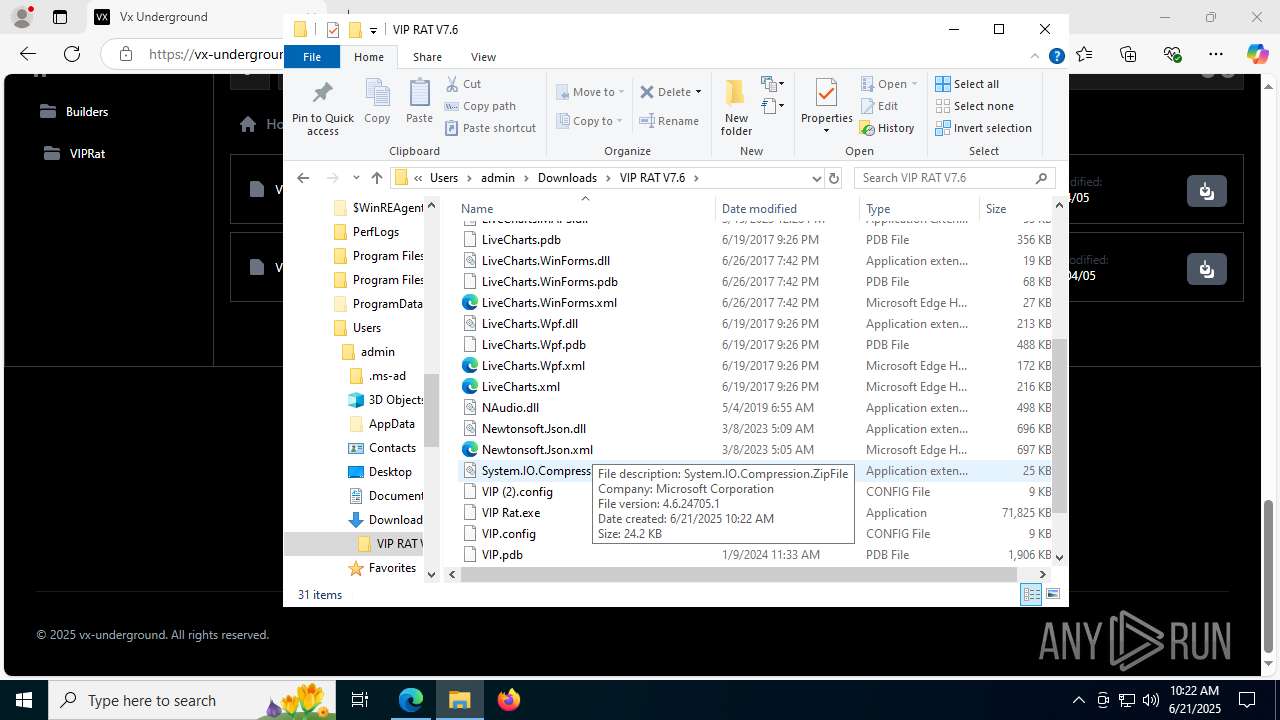
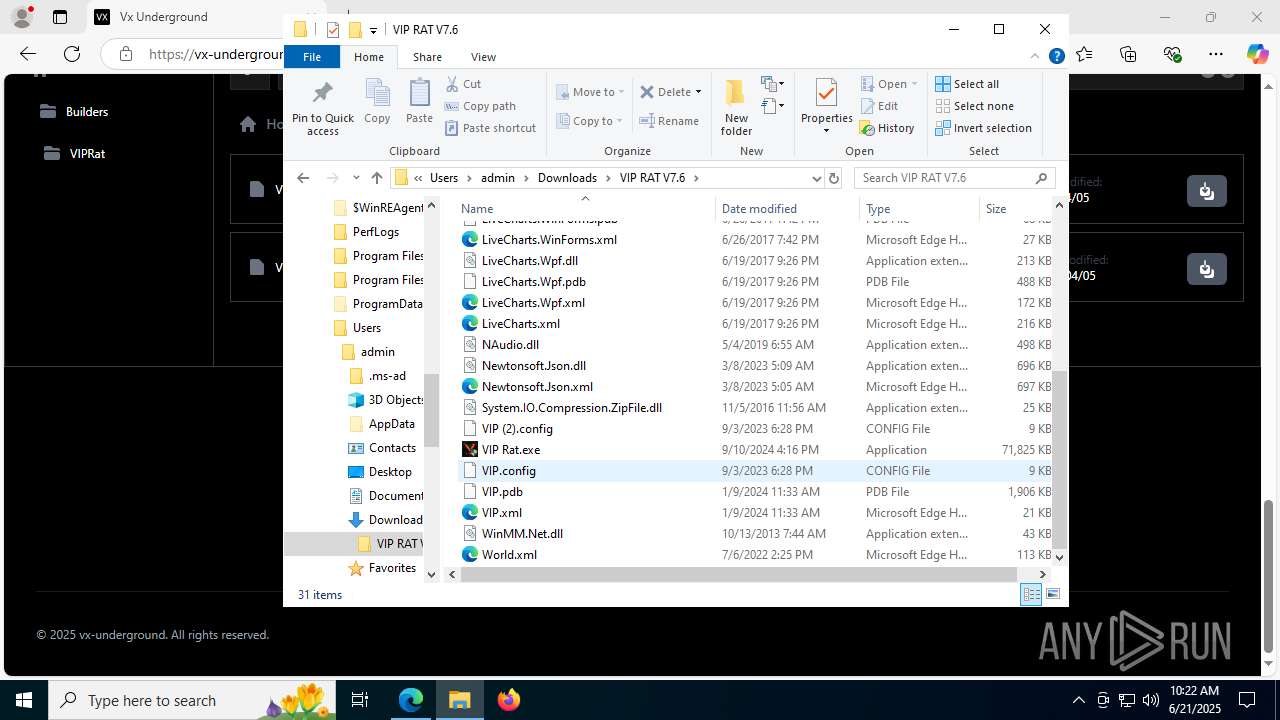
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7256)
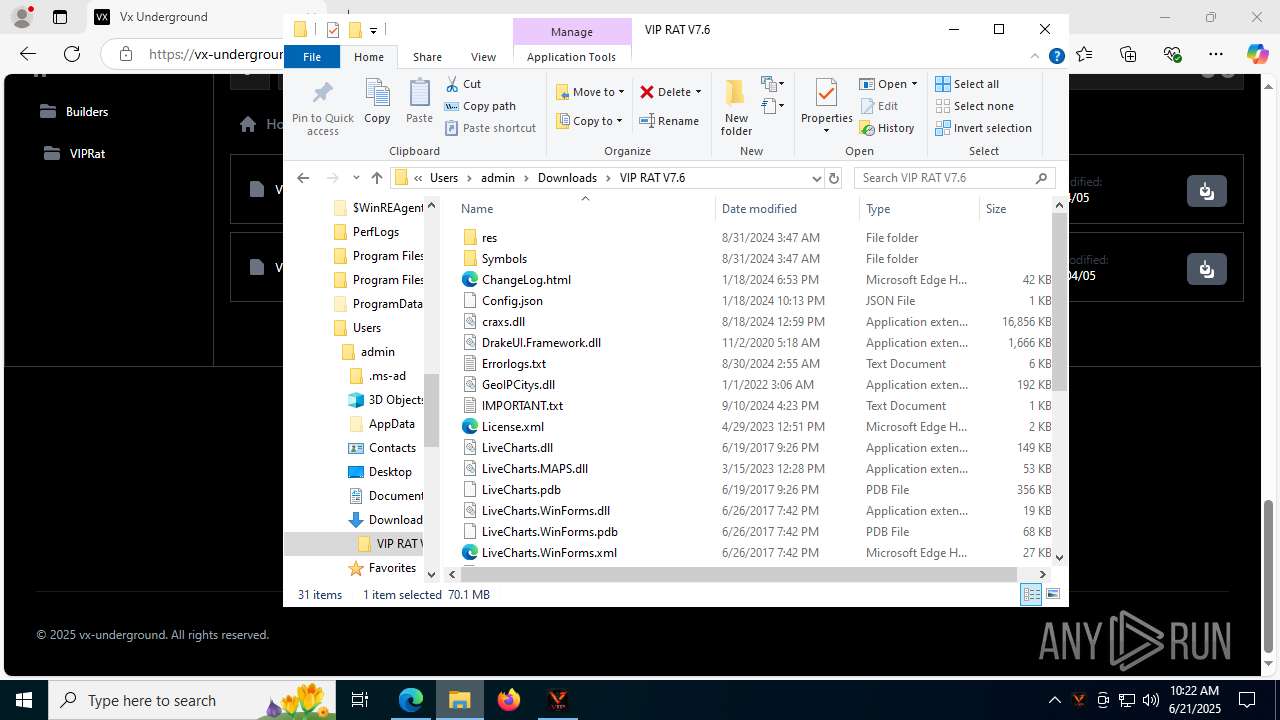
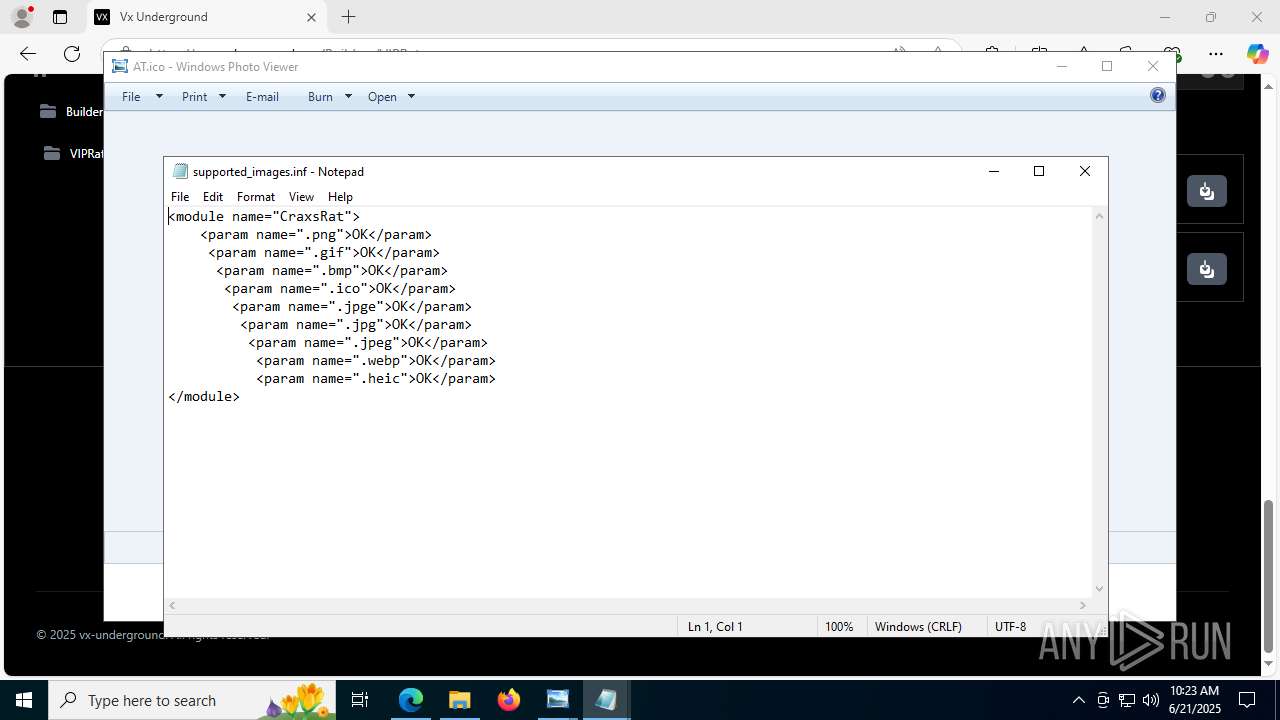
The sample compiled with chinese language support
- WinRAR.exe (PID: 7256)
The sample compiled with english language support
- WinRAR.exe (PID: 7256)
Application launched itself
- msedge.exe (PID: 2076)
- msedge.exe (PID: 6536)
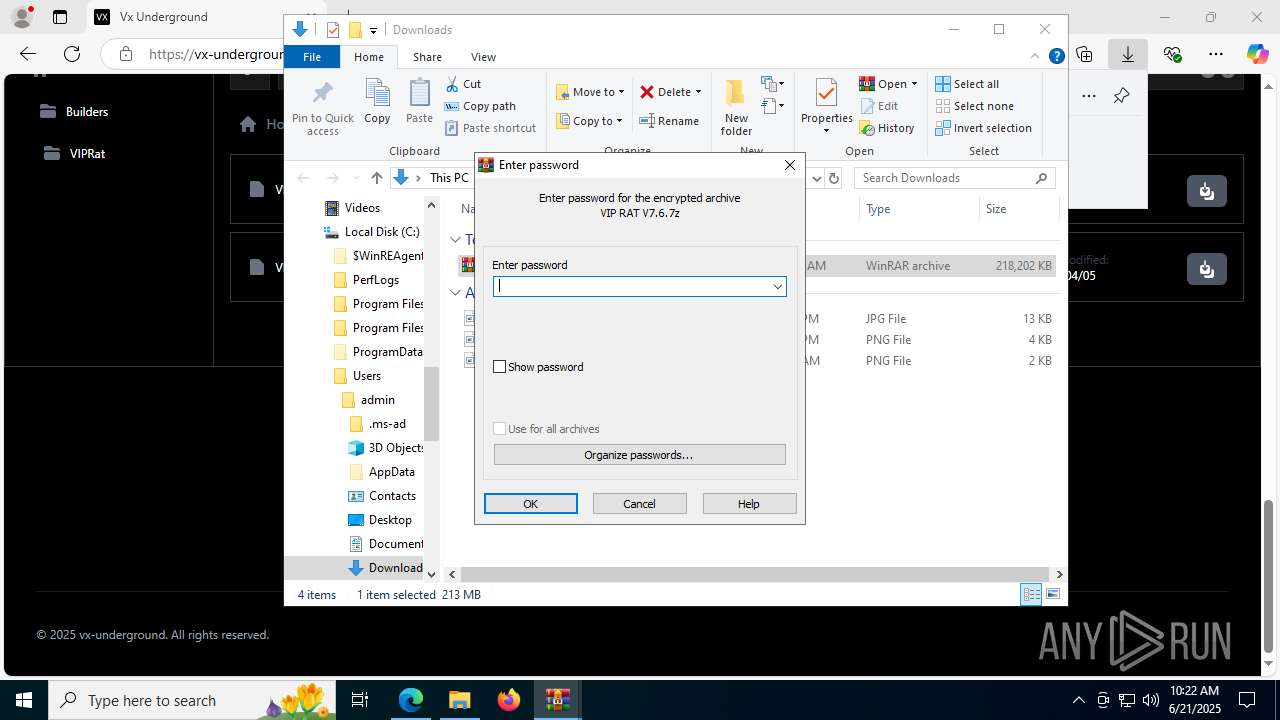
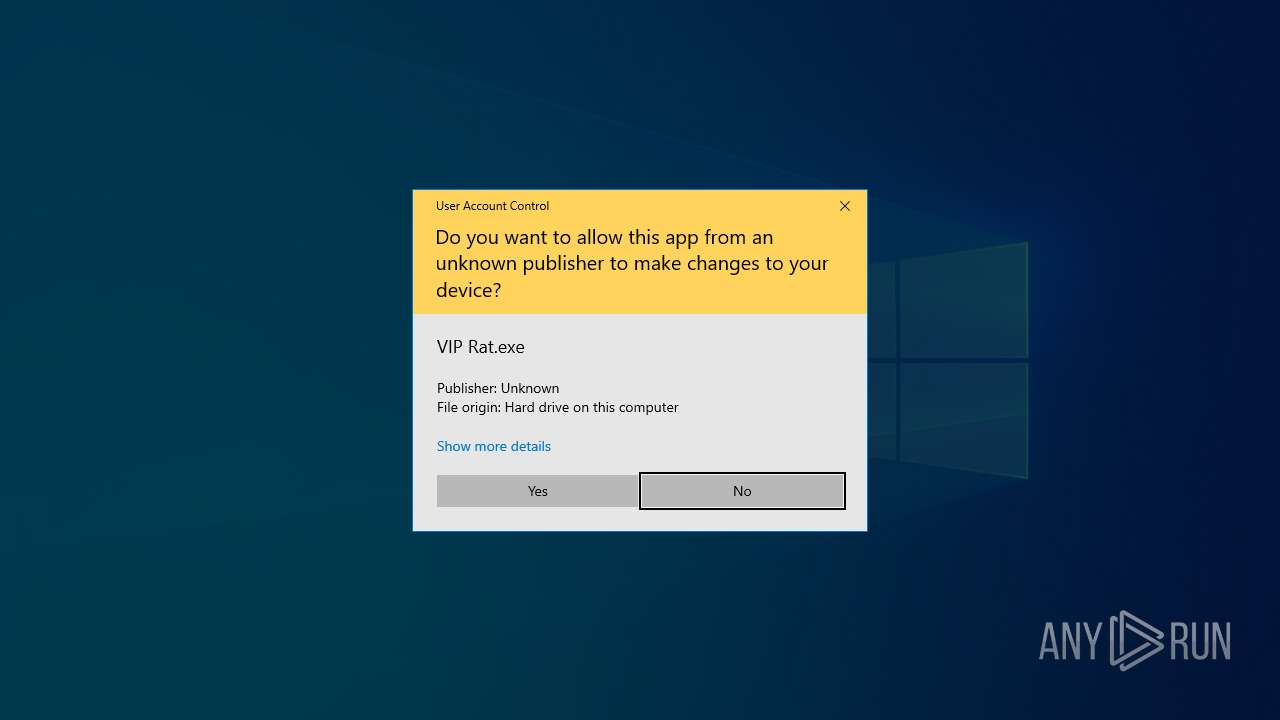
Manual execution by a user
- VIP Rat.exe (PID: 5476)
- WinRAR.exe (PID: 7256)
- VIP Rat.exe (PID: 7932)
- rundll32.exe (PID: 7380)
- notepad.exe (PID: 1028)
- rundll32.exe (PID: 1036)
- rundll32.exe (PID: 6876)
- rundll32.exe (PID: 5968)
- rundll32.exe (PID: 6404)
- notepad.exe (PID: 7084)
- iexplore.exe (PID: 1896)
- notepad.exe (PID: 5116)
- rundll32.exe (PID: 7980)
- rundll32.exe (PID: 7744)
- notepad.exe (PID: 2192)
- notepad.exe (PID: 4444)
- notepad.exe (PID: 4052)
- rundll32.exe (PID: 6492)
- iexplore.exe (PID: 3724)
- rundll32.exe (PID: 888)
- notepad.exe (PID: 7460)
- notepad.exe (PID: 7992)
- rundll32.exe (PID: 6164)
- rundll32.exe (PID: 8720)
- rundll32.exe (PID: 7120)
- rundll32.exe (PID: 8008)
- rundll32.exe (PID: 6012)
- rundll32.exe (PID: 6308)
- rundll32.exe (PID: 8288)
- iexplore.exe (PID: 8332)
- rundll32.exe (PID: 9188)
- rundll32.exe (PID: 8772)
- rundll32.exe (PID: 8844)
- notepad.exe (PID: 9128)
- rundll32.exe (PID: 9052)
- rundll32.exe (PID: 9000)
- iexplore.exe (PID: 8248)
- rundll32.exe (PID: 8364)
- rundll32.exe (PID: 4072)
- rundll32.exe (PID: 6652)
- rundll32.exe (PID: 6540)
- rundll32.exe (PID: 3748)
- rundll32.exe (PID: 8912)
- rundll32.exe (PID: 8352)
- iexplore.exe (PID: 8716)
- rundll32.exe (PID: 9648)
- rundll32.exe (PID: 8272)
- rundll32.exe (PID: 9116)
- rundll32.exe (PID: 8648)
- notepad.exe (PID: 9464)
- rundll32.exe (PID: 9212)
- rundll32.exe (PID: 9236)
- rundll32.exe (PID: 9564)
- rundll32.exe (PID: 9620)
- rundll32.exe (PID: 9804)
- rundll32.exe (PID: 9680)
- rundll32.exe (PID: 9732)
- rundll32.exe (PID: 9920)
- rundll32.exe (PID: 9844)
- rundll32.exe (PID: 10024)
- rundll32.exe (PID: 8964)
- rundll32.exe (PID: 10180)
- rundll32.exe (PID: 9256)
- rundll32.exe (PID: 8816)
- rundll32.exe (PID: 9992)
- rundll32.exe (PID: 8828)
- rundll32.exe (PID: 8336)
- rundll32.exe (PID: 9368)
- rundll32.exe (PID: 10084)
- rundll32.exe (PID: 10144)
- rundll32.exe (PID: 10172)
- rundll32.exe (PID: 9272)
- rundll32.exe (PID: 8260)
- rundll32.exe (PID: 8452)
- rundll32.exe (PID: 10212)
- rundll32.exe (PID: 10308)
- rundll32.exe (PID: 10360)
- rundll32.exe (PID: 10476)
- rundll32.exe (PID: 10524)
- rundll32.exe (PID: 10588)
- rundll32.exe (PID: 10640)
- rundll32.exe (PID: 10720)
- iexplore.exe (PID: 10844)
- rundll32.exe (PID: 10728)
- rundll32.exe (PID: 10920)
- rundll32.exe (PID: 11020)
- rundll32.exe (PID: 11088)
- rundll32.exe (PID: 11156)
- rundll32.exe (PID: 11224)
- rundll32.exe (PID: 10204)
- rundll32.exe (PID: 10448)
- rundll32.exe (PID: 10540)
- rundll32.exe (PID: 10972)
- rundll32.exe (PID: 11144)
- rundll32.exe (PID: 10912)
- rundll32.exe (PID: 11192)
- rundll32.exe (PID: 11152)
- rundll32.exe (PID: 11372)
- rundll32.exe (PID: 11300)
- rundll32.exe (PID: 11552)
- rundll32.exe (PID: 11544)
- rundll32.exe (PID: 12040)
- rundll32.exe (PID: 11712)
- rundll32.exe (PID: 12104)
- rundll32.exe (PID: 12260)
- rundll32.exe (PID: 12268)
- rundll32.exe (PID: 10936)
- rundll32.exe (PID: 12452)
- rundll32.exe (PID: 12504)
- rundll32.exe (PID: 12524)
- rundll32.exe (PID: 12804)
- rundll32.exe (PID: 12768)
- rundll32.exe (PID: 12848)
- rundll32.exe (PID: 12776)
- rundll32.exe (PID: 12796)
- rundll32.exe (PID: 12824)
- rundll32.exe (PID: 12812)
- rundll32.exe (PID: 12296)
- rundll32.exe (PID: 12872)
- rundll32.exe (PID: 12956)
- rundll32.exe (PID: 12972)
- rundll32.exe (PID: 12980)
- rundll32.exe (PID: 13036)
- rundll32.exe (PID: 10272)
- rundll32.exe (PID: 12372)
- rundll32.exe (PID: 10508)
- rundll32.exe (PID: 13512)
- rundll32.exe (PID: 13388)
- rundll32.exe (PID: 6320)
- rundll32.exe (PID: 14076)
- rundll32.exe (PID: 13556)
- rundll32.exe (PID: 14084)
- rundll32.exe (PID: 3392)
- rundll32.exe (PID: 14244)
- rundll32.exe (PID: 14300)
- rundll32.exe (PID: 14304)
- rundll32.exe (PID: 4192)
- rundll32.exe (PID: 12200)
- rundll32.exe (PID: 2708)
- rundll32.exe (PID: 6680)
- rundll32.exe (PID: 12280)
- rundll32.exe (PID: 14752)
- rundll32.exe (PID: 14916)
- rundll32.exe (PID: 14760)
- rundll32.exe (PID: 14888)
- rundll32.exe (PID: 14932)
- rundll32.exe (PID: 12660)
- rundll32.exe (PID: 12668)
- rundll32.exe (PID: 14376)
- rundll32.exe (PID: 12840)
- rundll32.exe (PID: 15276)
- rundll32.exe (PID: 15484)
- rundll32.exe (PID: 12520)
- rundll32.exe (PID: 15252)
- rundll32.exe (PID: 15376)
- rundll32.exe (PID: 15468)
- rundll32.exe (PID: 15476)
- rundll32.exe (PID: 15492)
- rundll32.exe (PID: 15632)
- rundll32.exe (PID: 15624)
- rundll32.exe (PID: 15640)
- rundll32.exe (PID: 16640)
- rundll32.exe (PID: 16648)
- rundll32.exe (PID: 16656)
- rundll32.exe (PID: 14924)
- rundll32.exe (PID: 16676)
- rundll32.exe (PID: 16736)
- rundll32.exe (PID: 16696)
- rundll32.exe (PID: 16712)
- rundll32.exe (PID: 16744)
- rundll32.exe (PID: 16764)
- rundll32.exe (PID: 16772)
- rundll32.exe (PID: 16916)
- rundll32.exe (PID: 16908)
- rundll32.exe (PID: 16952)
- rundll32.exe (PID: 16924)
- rundll32.exe (PID: 16936)
- rundll32.exe (PID: 16944)
- rundll32.exe (PID: 16960)
- rundll32.exe (PID: 16704)
- rundll32.exe (PID: 16756)
- rundll32.exe (PID: 16664)
- rundll32.exe (PID: 16900)
- rundll32.exe (PID: 16988)
- rundll32.exe (PID: 16996)
- rundll32.exe (PID: 17004)
- rundll32.exe (PID: 17012)
- rundll32.exe (PID: 18836)
- rundll32.exe (PID: 14280)
- rundll32.exe (PID: 13148)
- rundll32.exe (PID: 12176)
- rundll32.exe (PID: 13348)
- rundll32.exe (PID: 13488)
- rundll32.exe (PID: 18896)
- rundll32.exe (PID: 12608)
- rundll32.exe (PID: 18680)
- rundll32.exe (PID: 18880)
- rundll32.exe (PID: 18904)
- rundll32.exe (PID: 16972)
- rundll32.exe (PID: 16980)
- rundll32.exe (PID: 17020)
- rundll32.exe (PID: 6620)
- rundll32.exe (PID: 1560)
- rundll32.exe (PID: 19036)
- rundll32.exe (PID: 18996)
- rundll32.exe (PID: 19172)
- rundll32.exe (PID: 19064)
- rundll32.exe (PID: 19084)
- rundll32.exe (PID: 19092)
- rundll32.exe (PID: 19312)
- rundll32.exe (PID: 19272)
- rundll32.exe (PID: 19328)
- rundll32.exe (PID: 19304)
- rundll32.exe (PID: 19320)
- rundll32.exe (PID: 19332)
- rundll32.exe (PID: 19344)
- rundll32.exe (PID: 19360)
- rundll32.exe (PID: 19352)
- rundll32.exe (PID: 19380)
- rundll32.exe (PID: 18972)
- rundll32.exe (PID: 18980)
- rundll32.exe (PID: 18988)
- rundll32.exe (PID: 13636)
- rundll32.exe (PID: 19408)
- rundll32.exe (PID: 19424)
- rundll32.exe (PID: 19444)
- rundll32.exe (PID: 18456)
- rundll32.exe (PID: 19388)
Detects BoxedApp packer (YARA)
- VIP Rat.exe (PID: 5476)
Reads the machine GUID from the registry
- VIP Rat.exe (PID: 5476)
Boxedapp packer has been detected
- VIP Rat.exe (PID: 5476)
Disables trace logs
- VIP Rat.exe (PID: 5476)
Creates files or folders in the user directory
- VIP Rat.exe (PID: 5476)
Checks proxy server information
- VIP Rat.exe (PID: 5476)
- slui.exe (PID: 7832)
Reads the software policy settings
- VIP Rat.exe (PID: 5476)
- slui.exe (PID: 7832)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1028)
- notepad.exe (PID: 7084)
- notepad.exe (PID: 5116)
- notepad.exe (PID: 7992)
- notepad.exe (PID: 2192)
- notepad.exe (PID: 4444)
- notepad.exe (PID: 4052)
- notepad.exe (PID: 7460)
- notepad.exe (PID: 9128)
- notepad.exe (PID: 9464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
417
Monitored processes
276
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
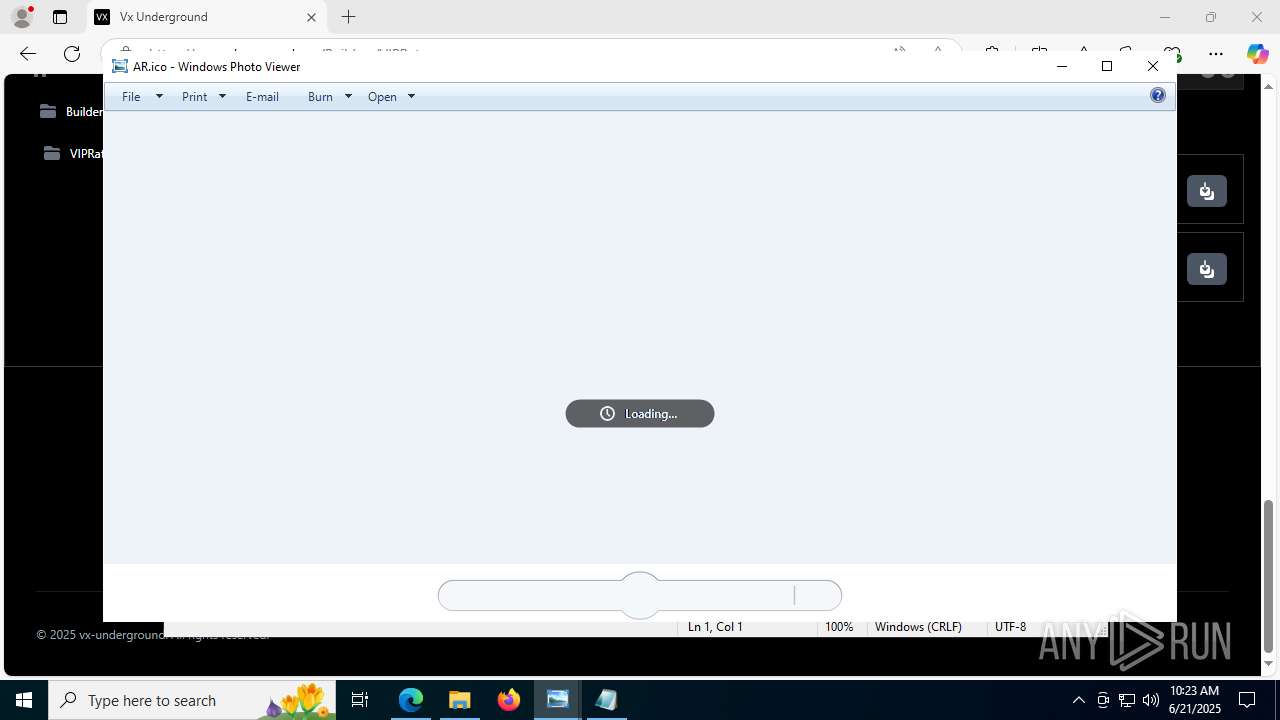
| 888 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Downloads\VIP RAT V7.6\res\GeoIP\Flags\AE.ico | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
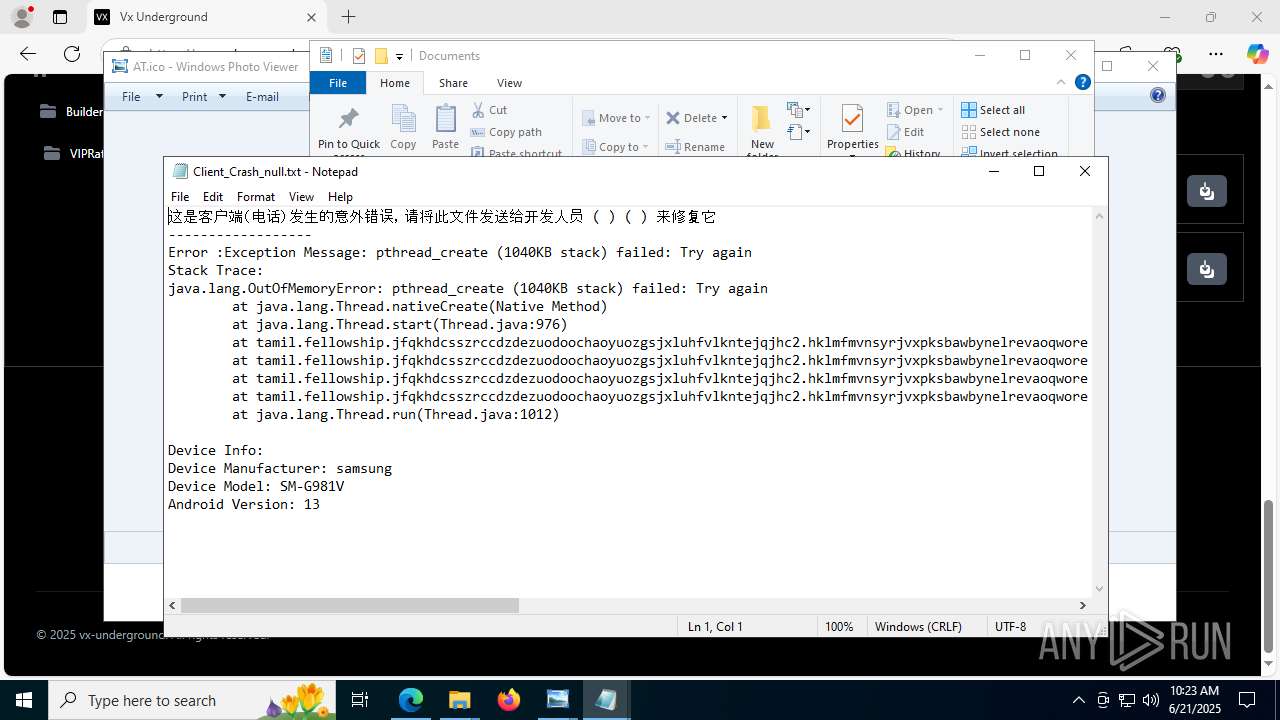
| 1028 | "C:\WINDOWS\system32\NOTEPAD.EXE" "C:\Users\admin\Downloads\VIP RAT V7.6\res\ClientCrashs\Client_Crash_0843aeb8ad9b24d2.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Downloads\VIP RAT V7.6\res\GeoIP\Flags\AD.ico | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1560 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Downloads\VIP RAT V7.6\res\GeoIP\Flags\UG.ico | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4323f208,0x7ffc4323f214,0x7ffc4323f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
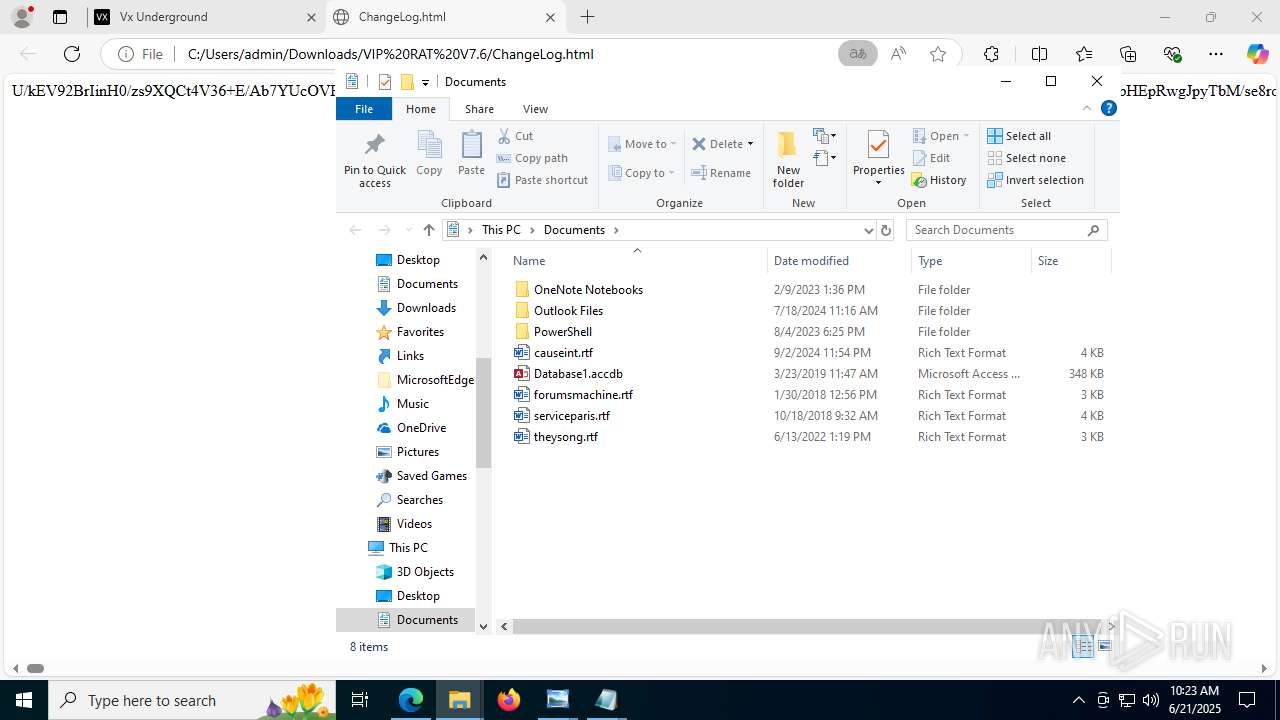
| 1896 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" "C:\Users\admin\Downloads\VIP RAT V7.6\ChangeLog.html" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://vx-underground.org/Builders/VIPRat" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
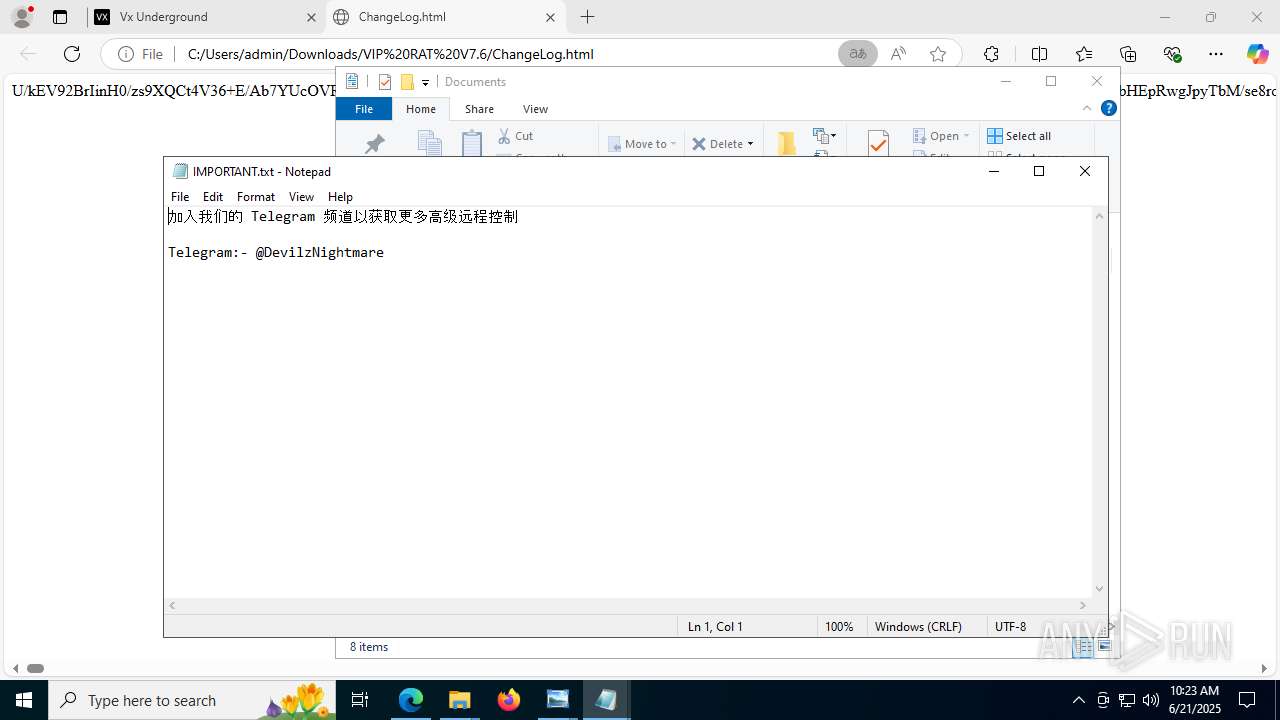
| 2192 | "C:\WINDOWS\system32\NOTEPAD.EXE" "C:\Users\admin\Downloads\VIP RAT V7.6\IMPORTANT.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --always-read-main-dll --field-trial-handle=3704,i,7648782756489755207,3787838392359223689,262144 --variations-seed-version --mojo-platform-channel-handle=6792 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2708 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Downloads\VIP RAT V7.6\res\GeoIP\Flags\HR.ico | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
82 207
Read events
82 098
Write events
109
Delete events
0
Modification events
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9A8EC6A0A8962F00 | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393940 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DB77284F-A1DF-4D96-94DB-10494BE19ADC} | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393940 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D93D1858-0C65-4751-8D49-8BCB0A7DDD35} | |||
| (PID) Process: | (2076) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393940 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9768CD23-201B-4949-9437-89E7479EDAD6} | |||
Executable files
28
Suspicious files
183
Text files
515
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176e89.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176e89.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176e98.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176ea8.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176eb7.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
88
DNS requests
79
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5612 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:29WKgESYBiCm0RAircH2JGrWQB276cmsALy2YSfatfM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2632 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.25.50.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7264 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7264 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3100 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751020856&P2=404&P3=2&P4=hee88j8jXj1xiTzpddqYgj5TzBB%2fcLTw1B6QmPrhhDkp5erWQdcEes5OVdkyfTR7Z3E2ACMN7ZKcyRnGqA1fwQ%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751020856&P2=404&P3=2&P4=hee88j8jXj1xiTzpddqYgj5TzBB%2fcLTw1B6QmPrhhDkp5erWQdcEes5OVdkyfTR7Z3E2ACMN7ZKcyRnGqA1fwQ%3d%3d | unknown | — | — | whitelisted |
3100 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751020856&P2=404&P3=2&P4=hee88j8jXj1xiTzpddqYgj5TzBB%2fcLTw1B6QmPrhhDkp5erWQdcEes5OVdkyfTR7Z3E2ACMN7ZKcyRnGqA1fwQ%3d%3d | unknown | — | — | whitelisted |
5476 | VIP Rat.exe | GET | 200 | 142.250.185.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4844 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5612 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5612 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5612 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5612 | msedge.exe | 104.18.6.192:443 | vx-underground.org | CLOUDFLARENET | — | shared |
5612 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
vx-underground.org |
| malicious |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
5612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
5612 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
5612 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |