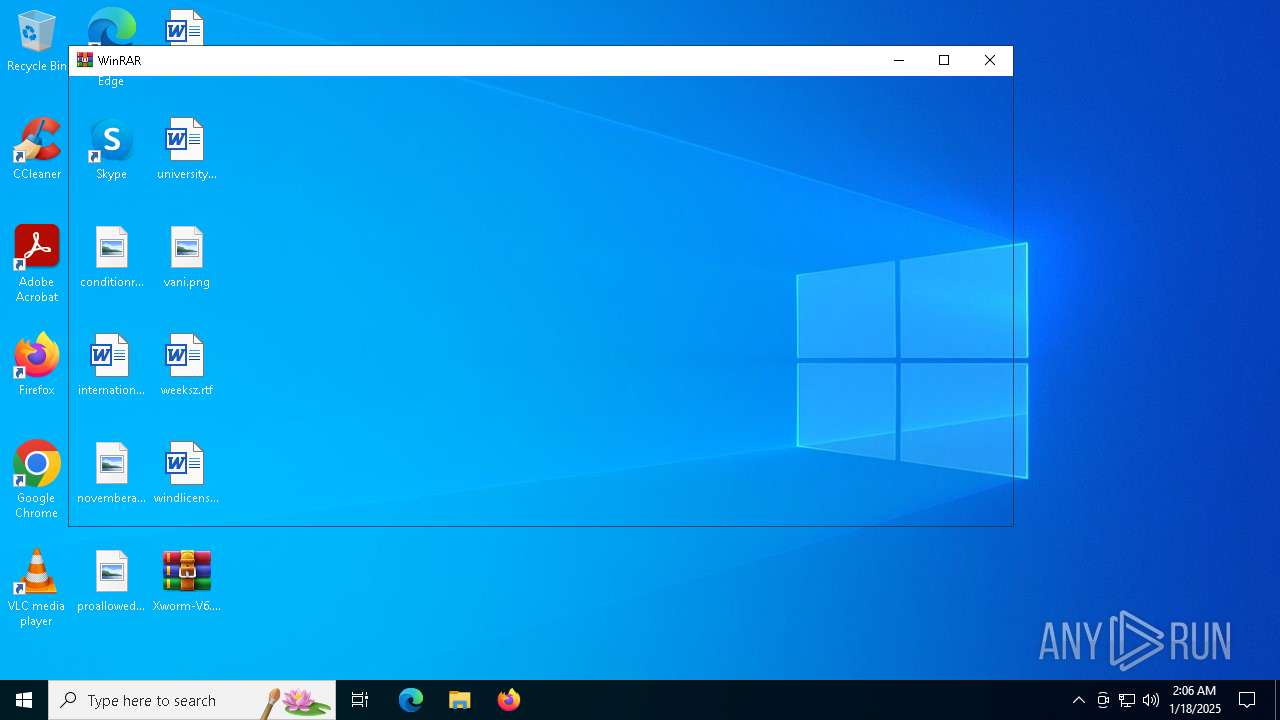
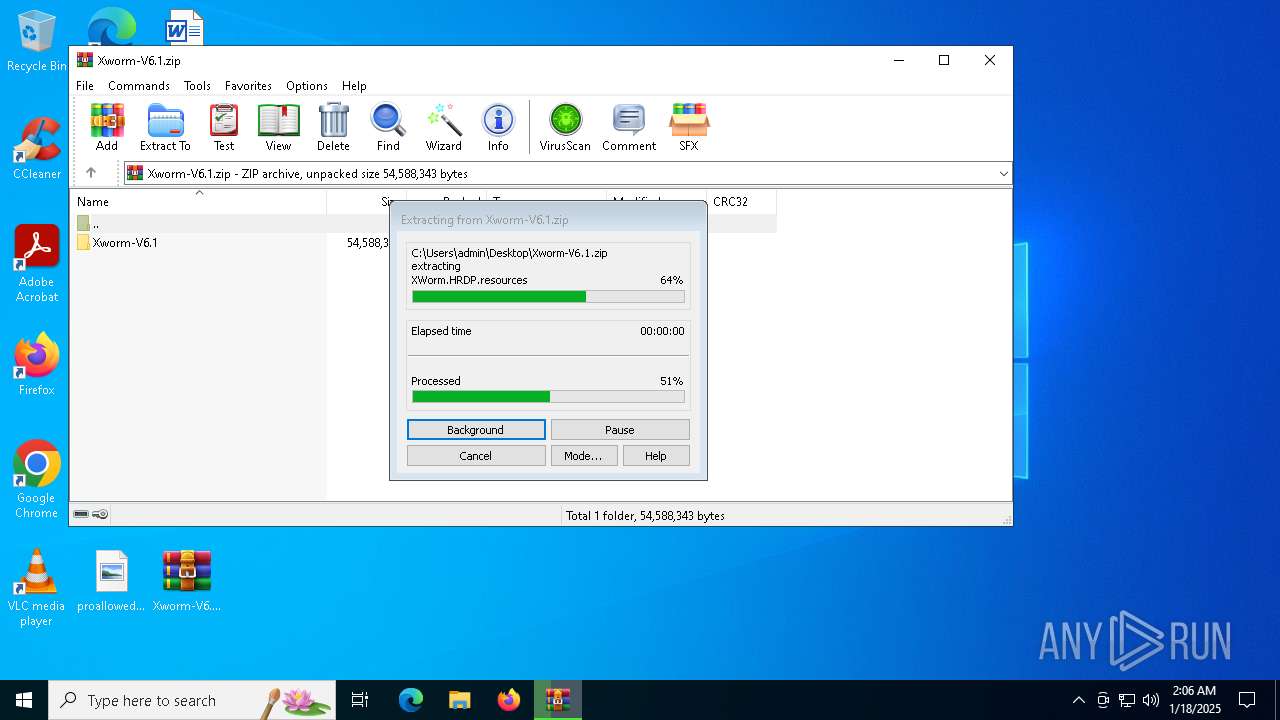
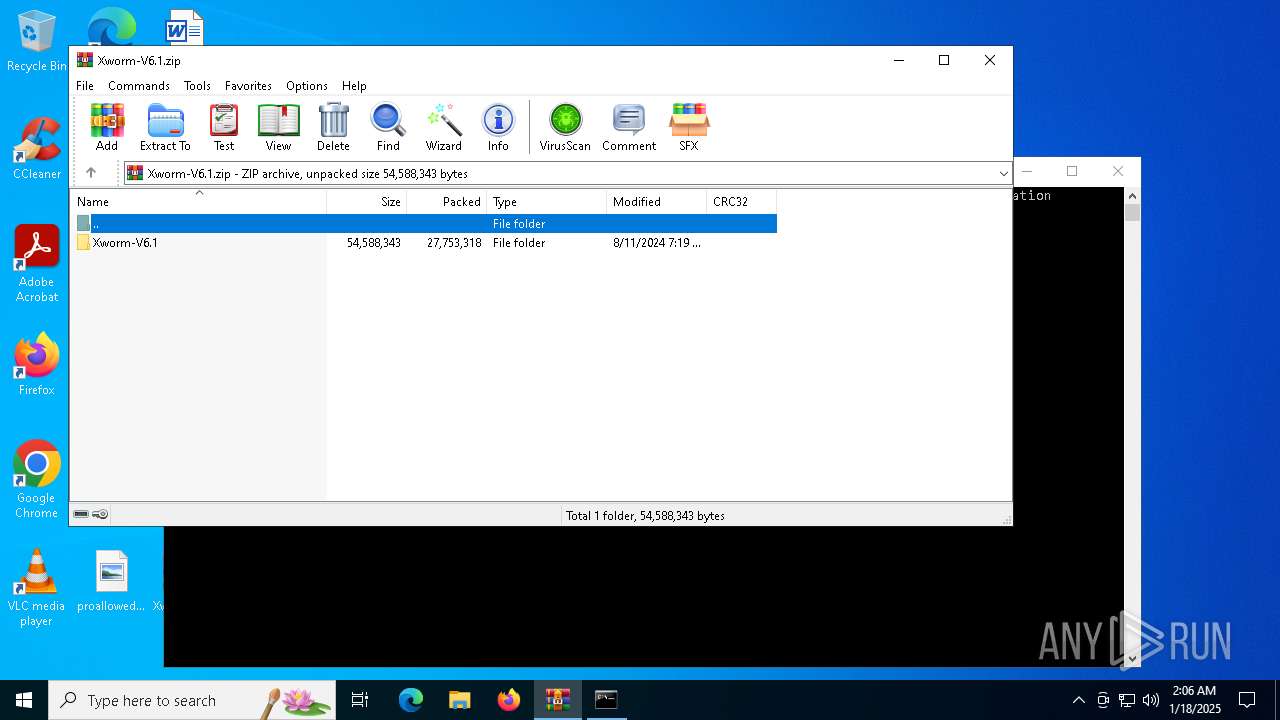
| File name: | Xworm-V6.1.zip |
| Full analysis: | https://app.any.run/tasks/21c0e40b-d8d5-4cdc-bcb1-2977f2502faa |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2025, 02:06:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 75B715E998C88F168728E27DC6887819 |
| SHA1: | 2D4D3F9702C0CD8B89B1B1D61CE05AA5C4B430D1 |
| SHA256: | 76F7A5D79B8DF10DEC30DC9FAF6CBB6039FDE1B93BD74210A61BF0943931F09D |
| SSDEEP: | 196608:S8kZyVuCHkRCUahNUQM9Hkav2D/e2sL8LwRxy1Iirs4e4dTRIj6:S8k4Hyah+Q4HkaK08Lw4Id4ekTRIm |
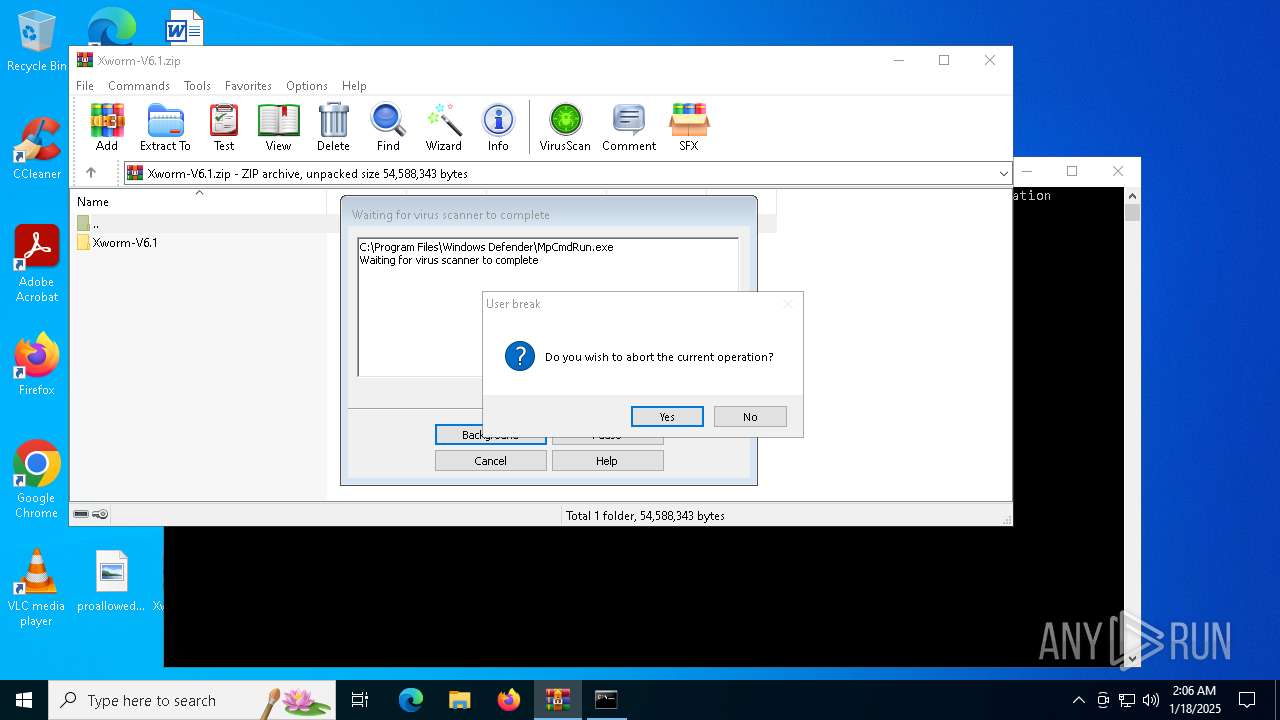
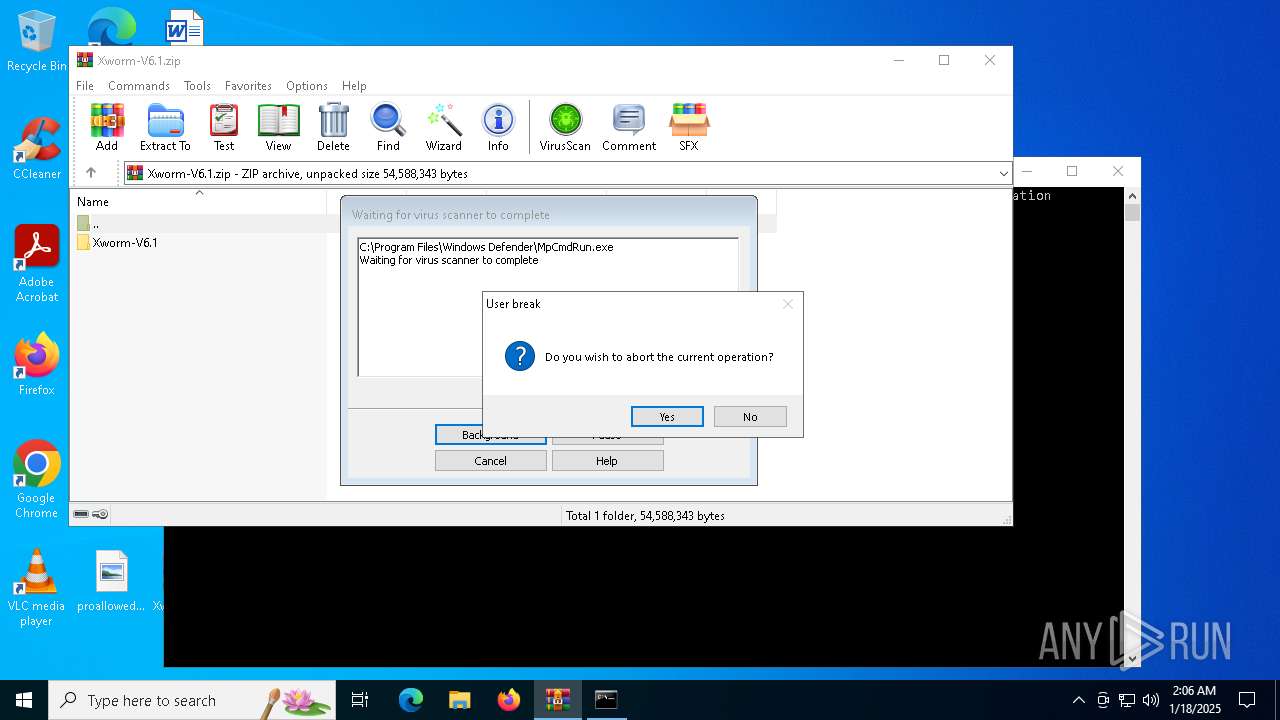
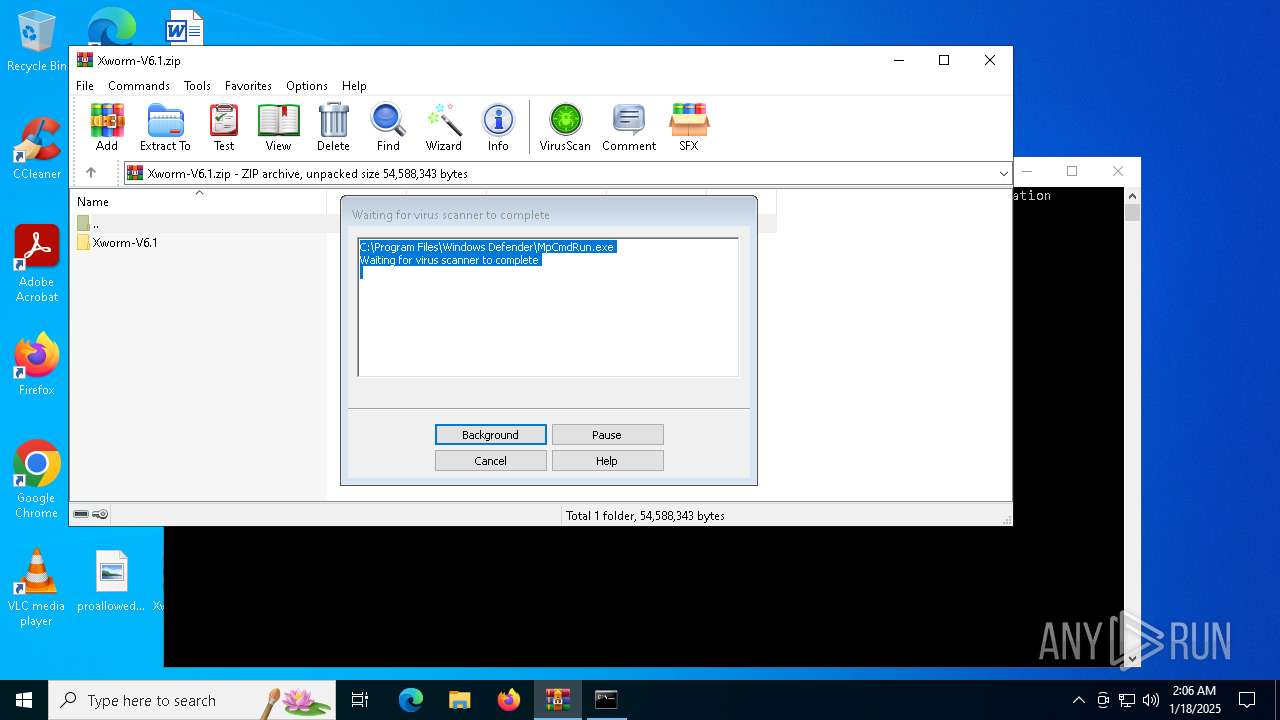
MALICIOUS
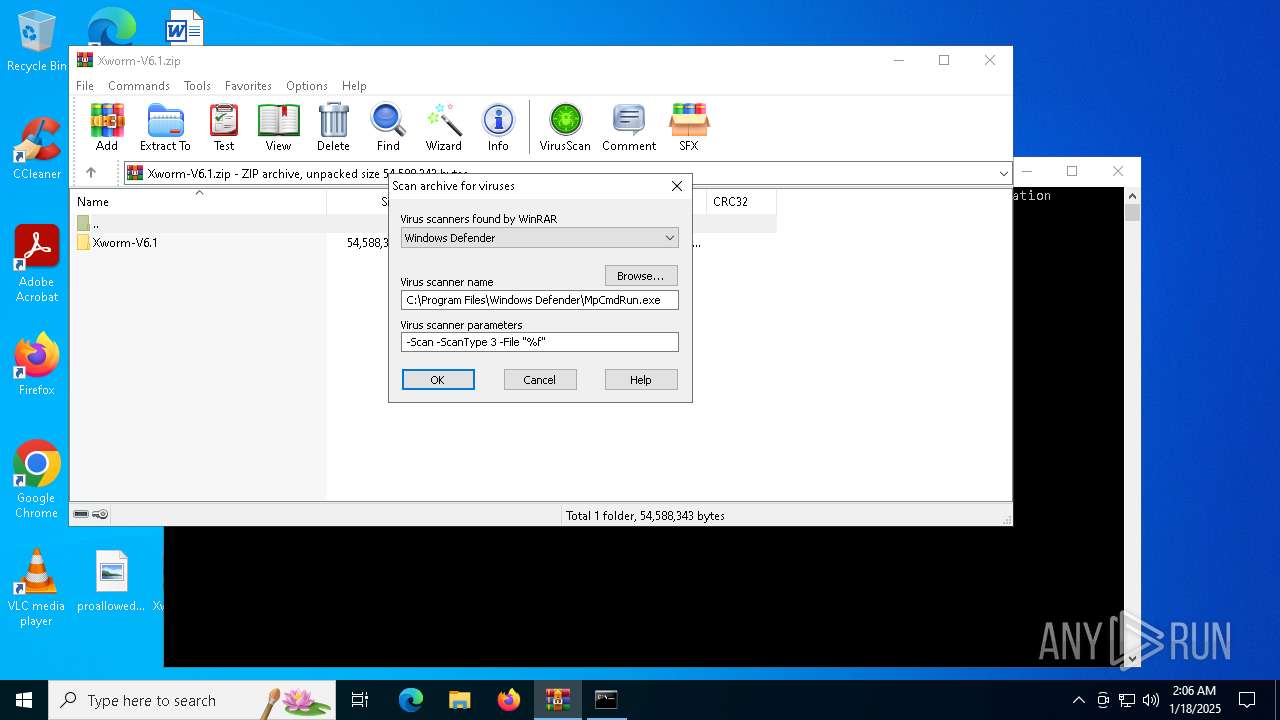
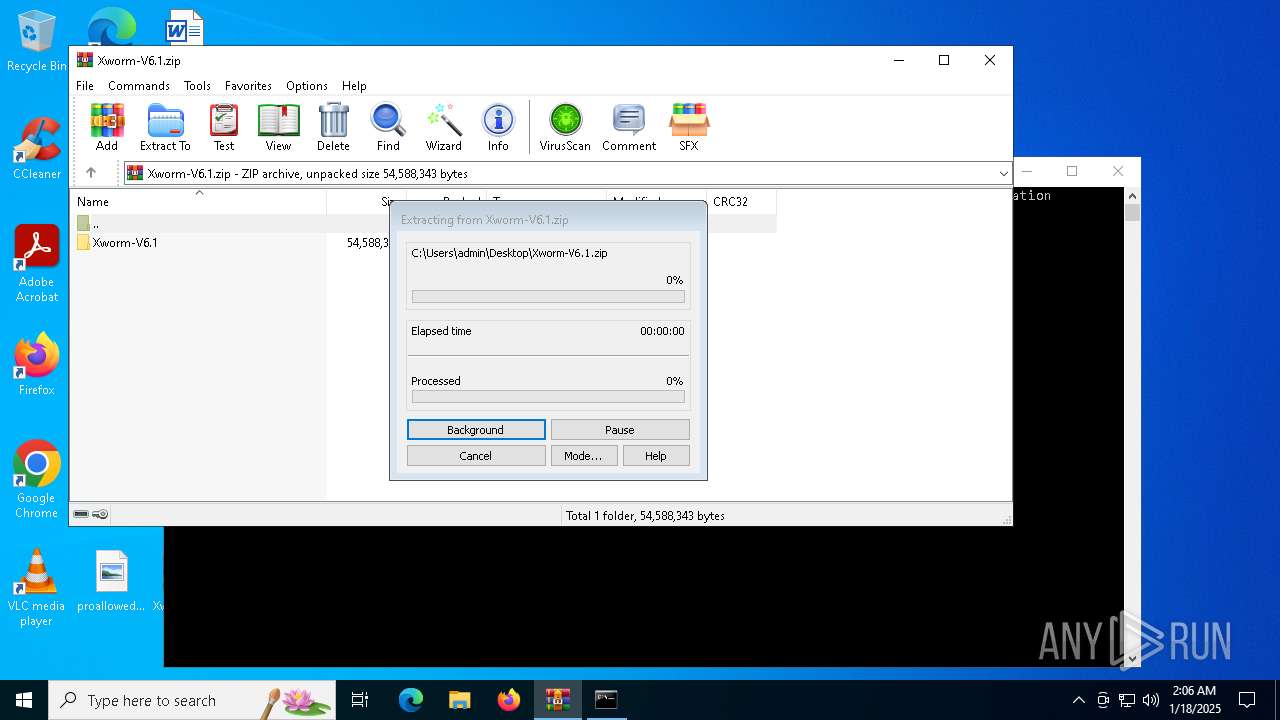
Generic archive extractor
- WinRAR.exe (PID: 3840)
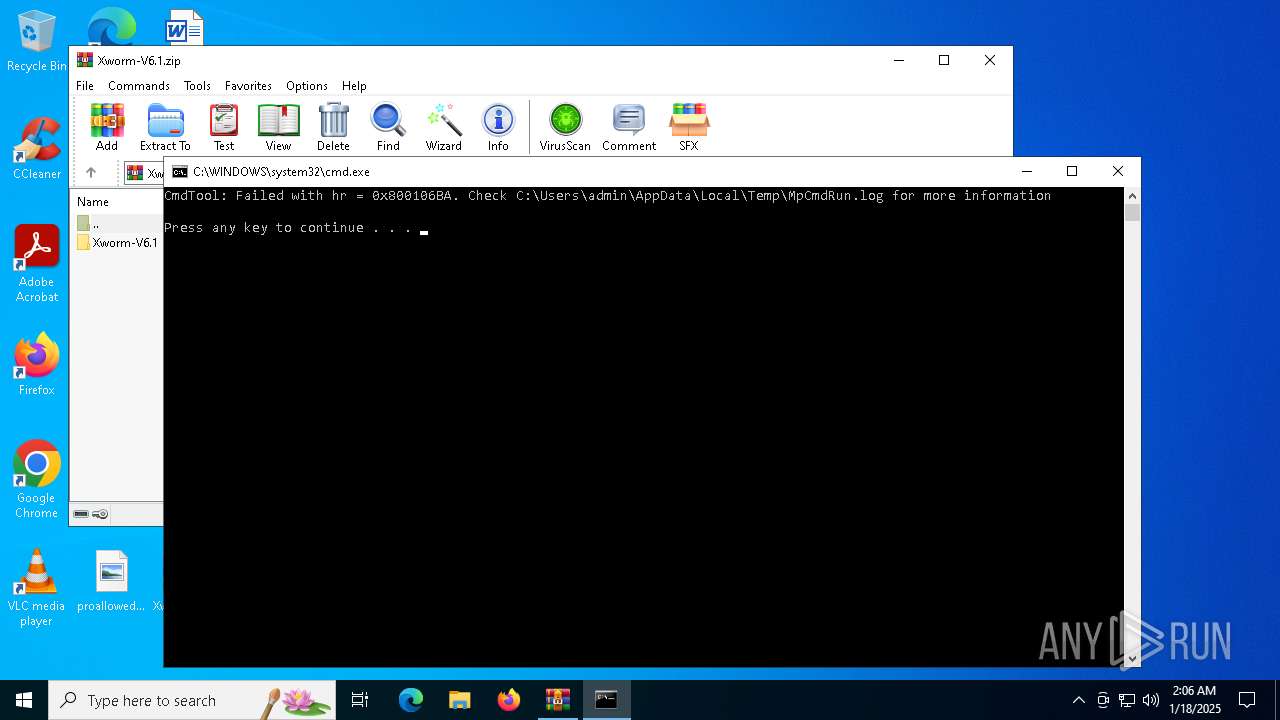
SUSPICIOUS
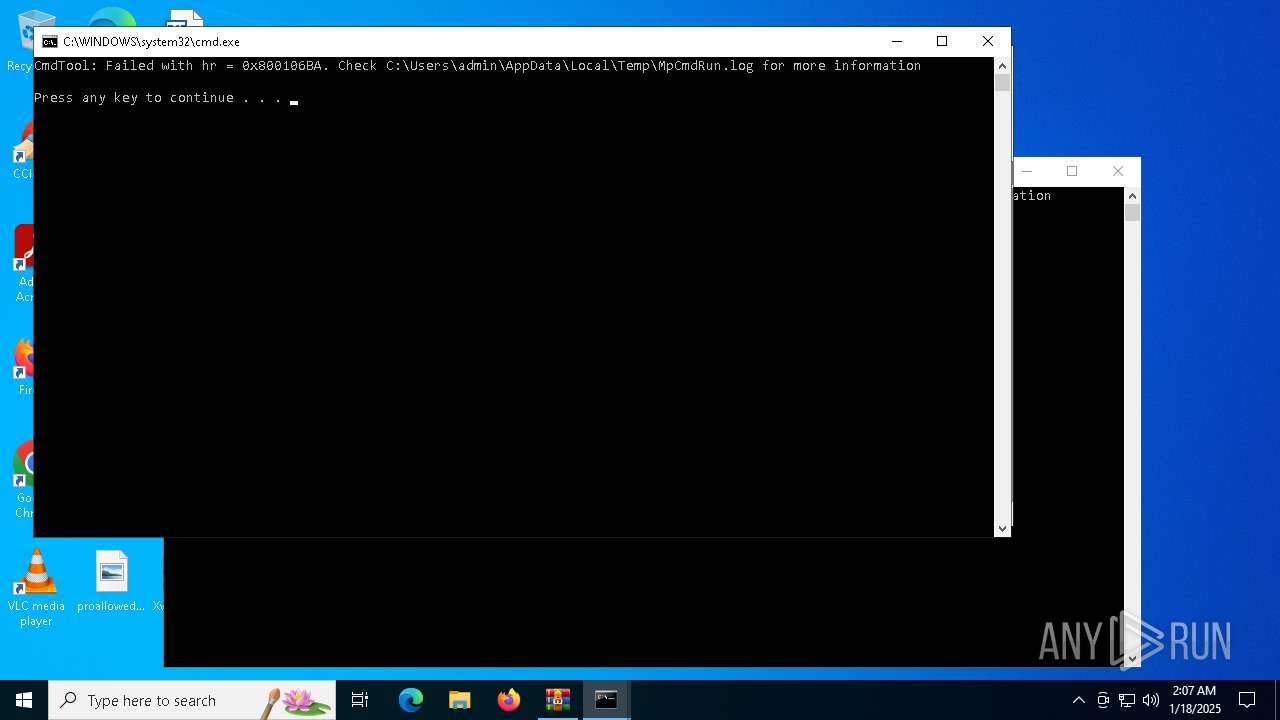
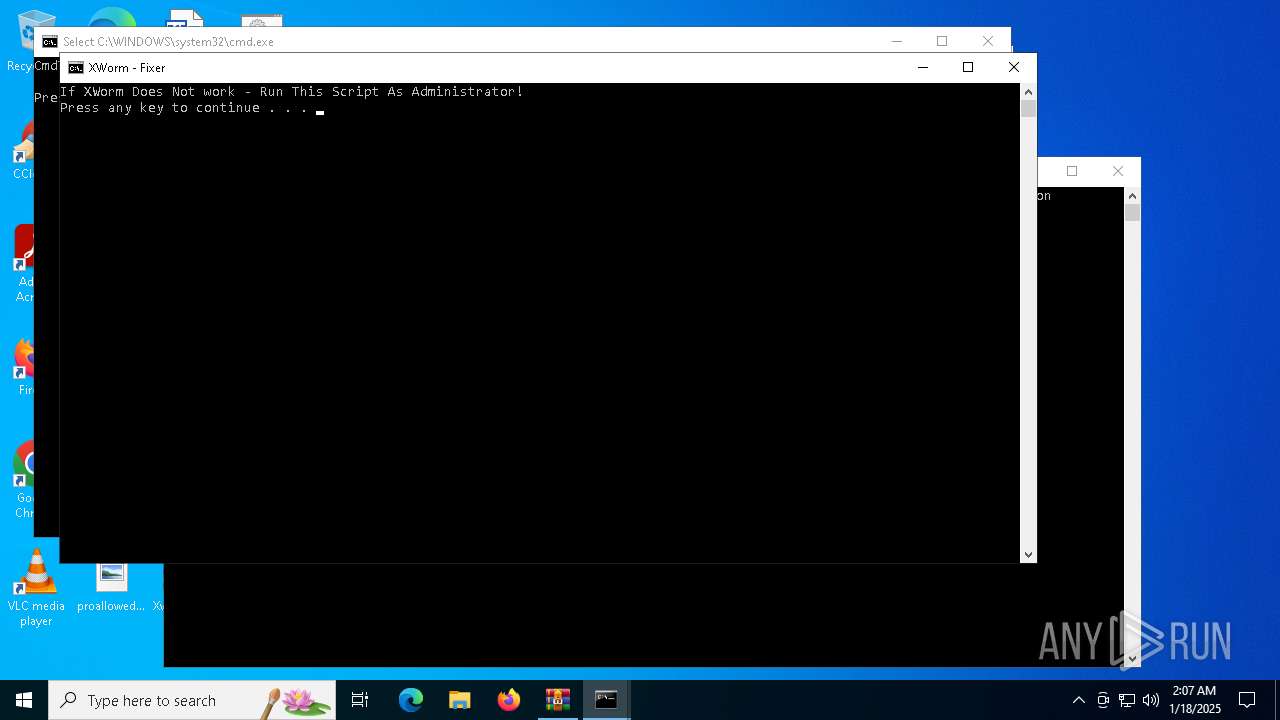
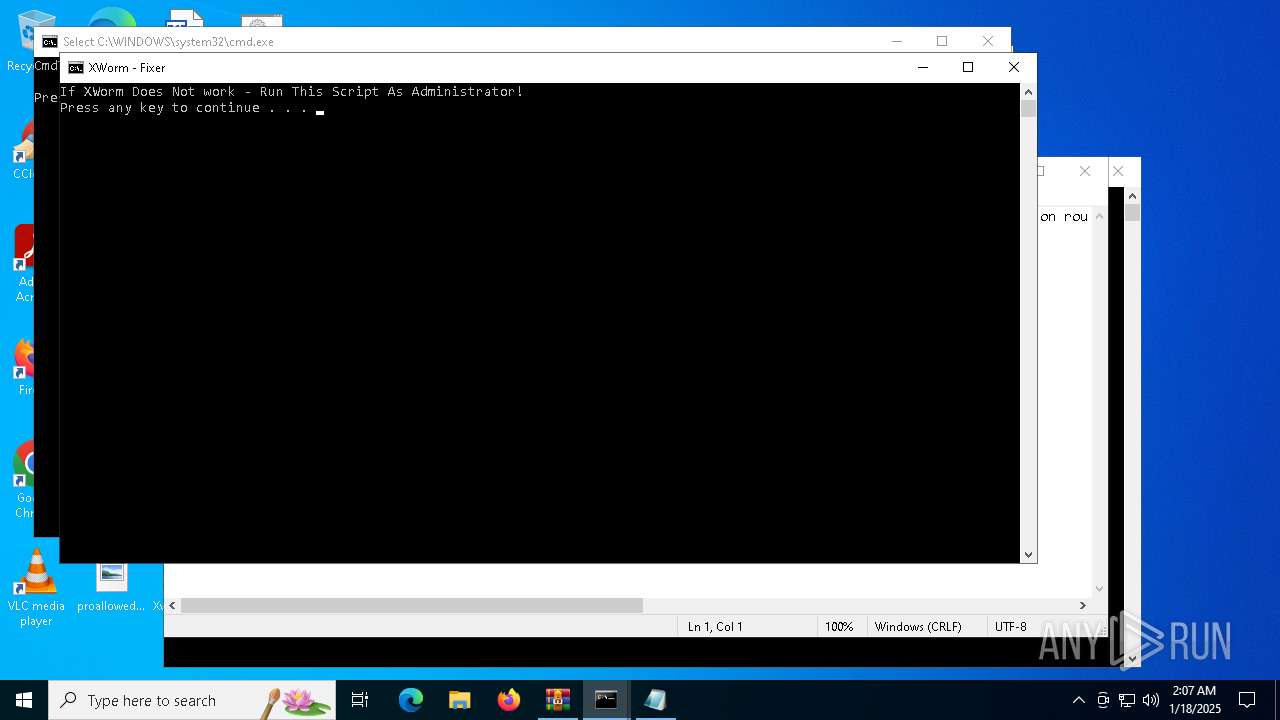
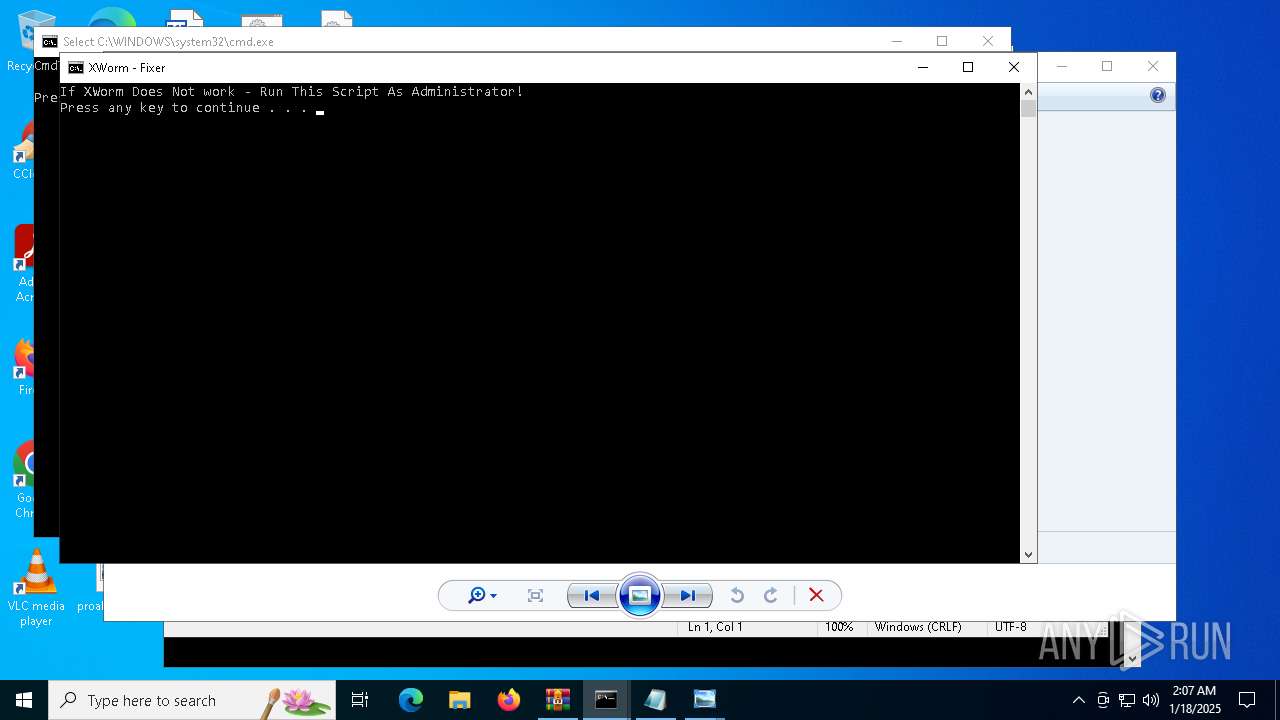
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3840)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 3840)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3840)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3840)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3840)
Reads the computer name
- MpCmdRun.exe (PID: 4996)
- MpCmdRun.exe (PID: 4120)
The process uses the downloaded file
- WinRAR.exe (PID: 3840)
Create files in a temporary directory
- MpCmdRun.exe (PID: 4996)
Checks supported languages
- MpCmdRun.exe (PID: 4996)
- MpCmdRun.exe (PID: 4120)
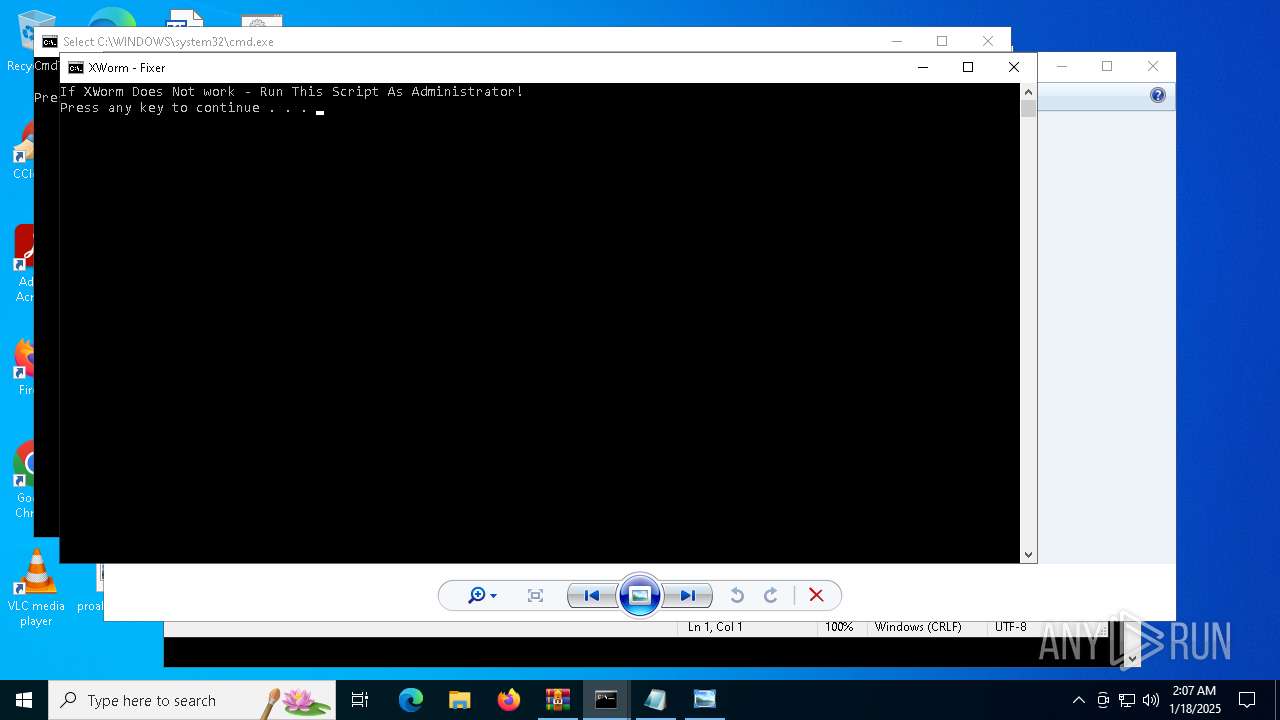
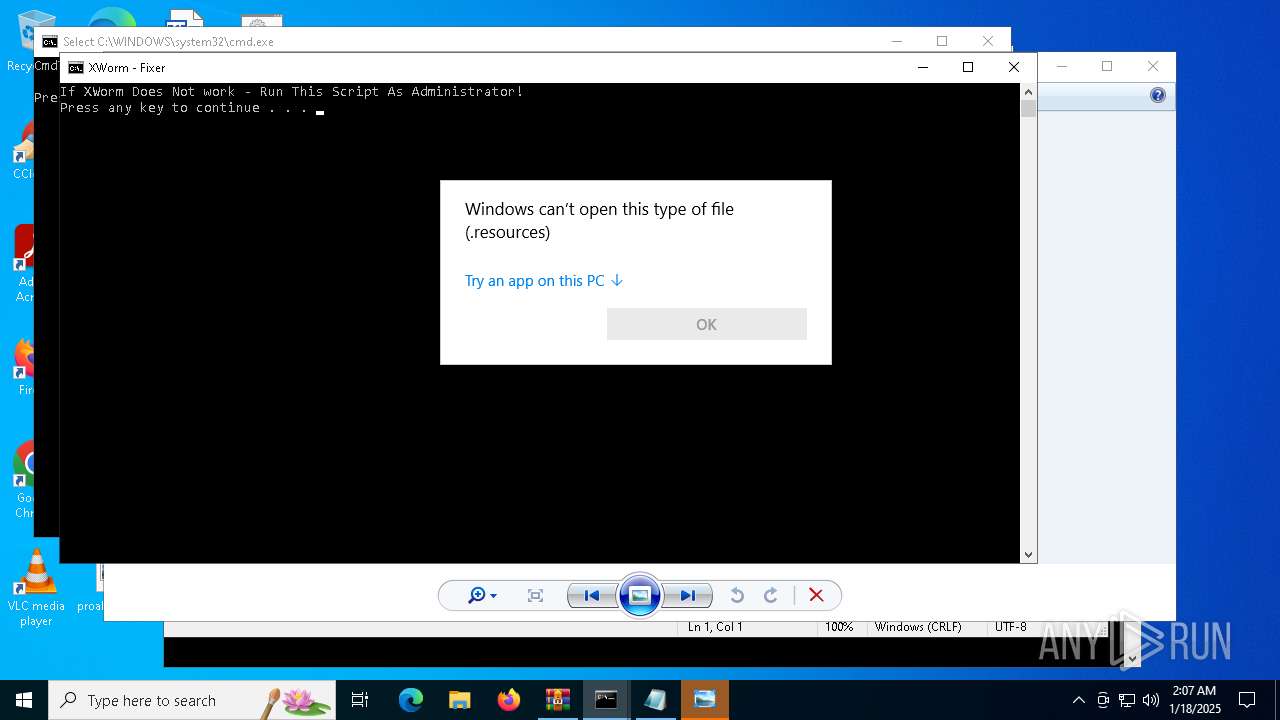
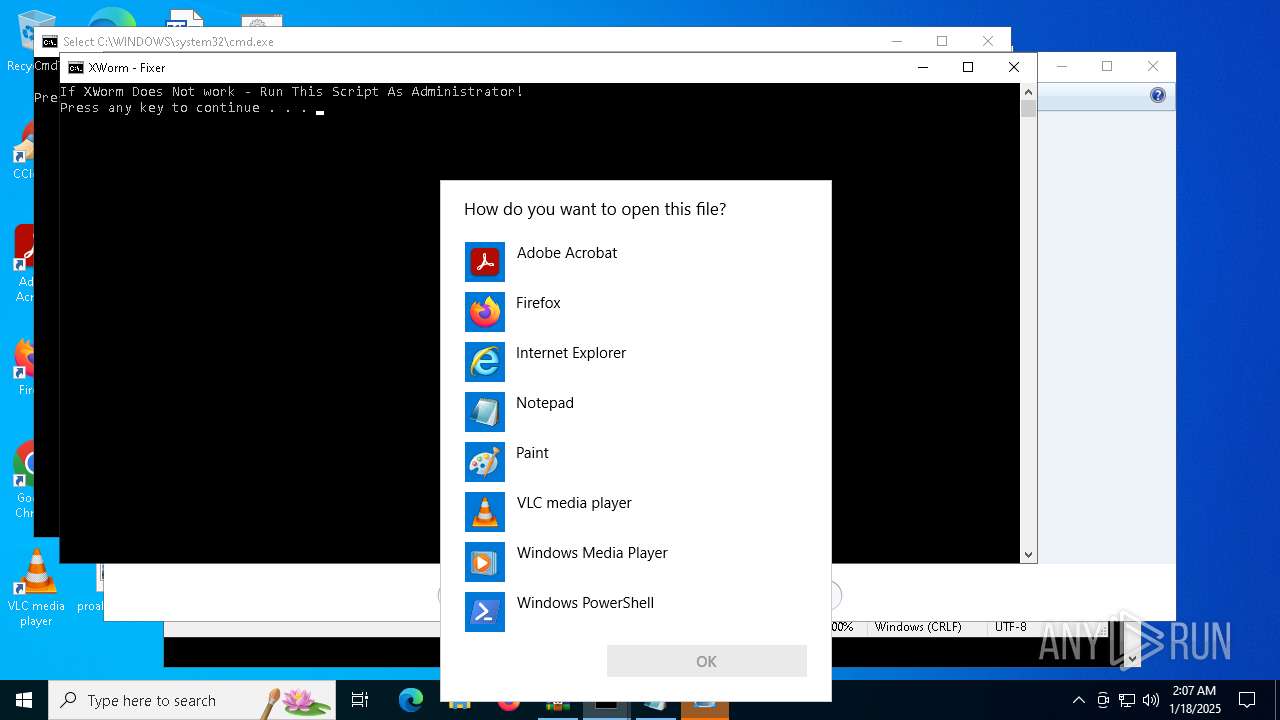
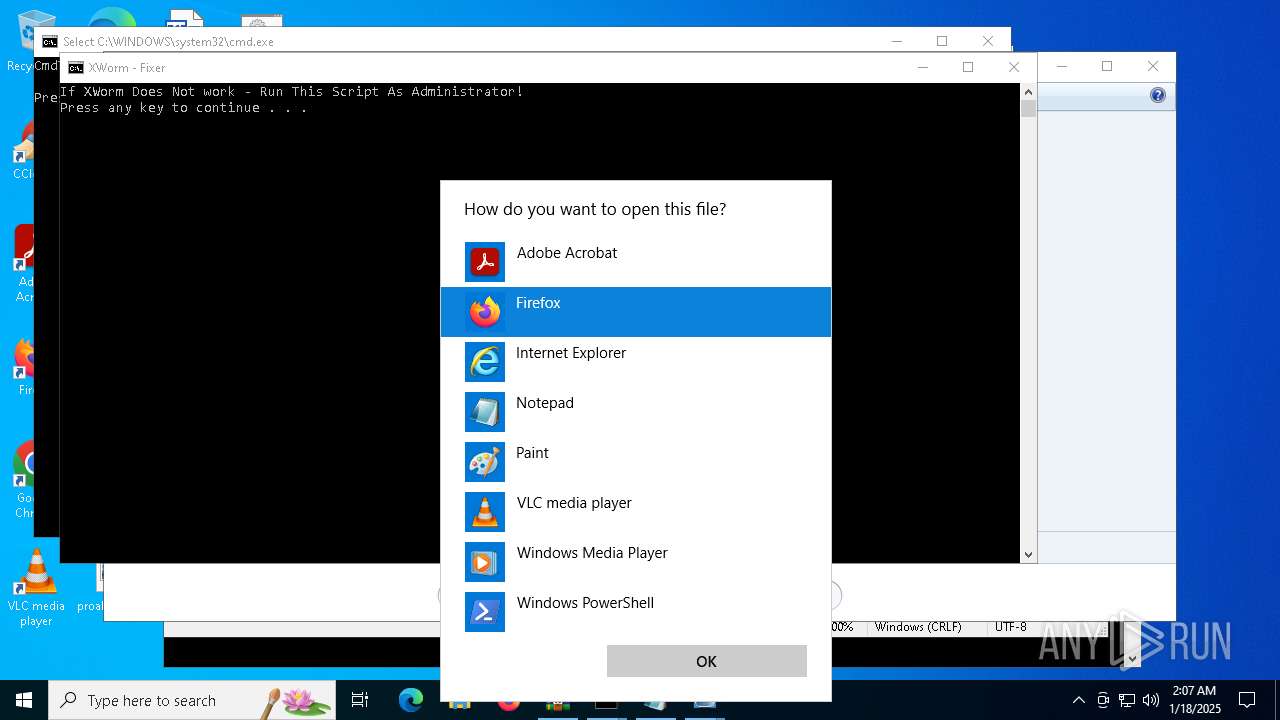
Manual execution by a user
- cmd.exe (PID: 5092)
- notepad.exe (PID: 448)
- rundll32.exe (PID: 5728)
- OpenWith.exe (PID: 5964)
- OpenWith.exe (PID: 5560)
- rundll32.exe (PID: 932)
- OpenWith.exe (PID: 5528)
- OpenWith.exe (PID: 1572)
Reads security settings of Internet Explorer
- notepad.exe (PID: 448)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5560)
- OpenWith.exe (PID: 5964)
- OpenWith.exe (PID: 5528)
- OpenWith.exe (PID: 1572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
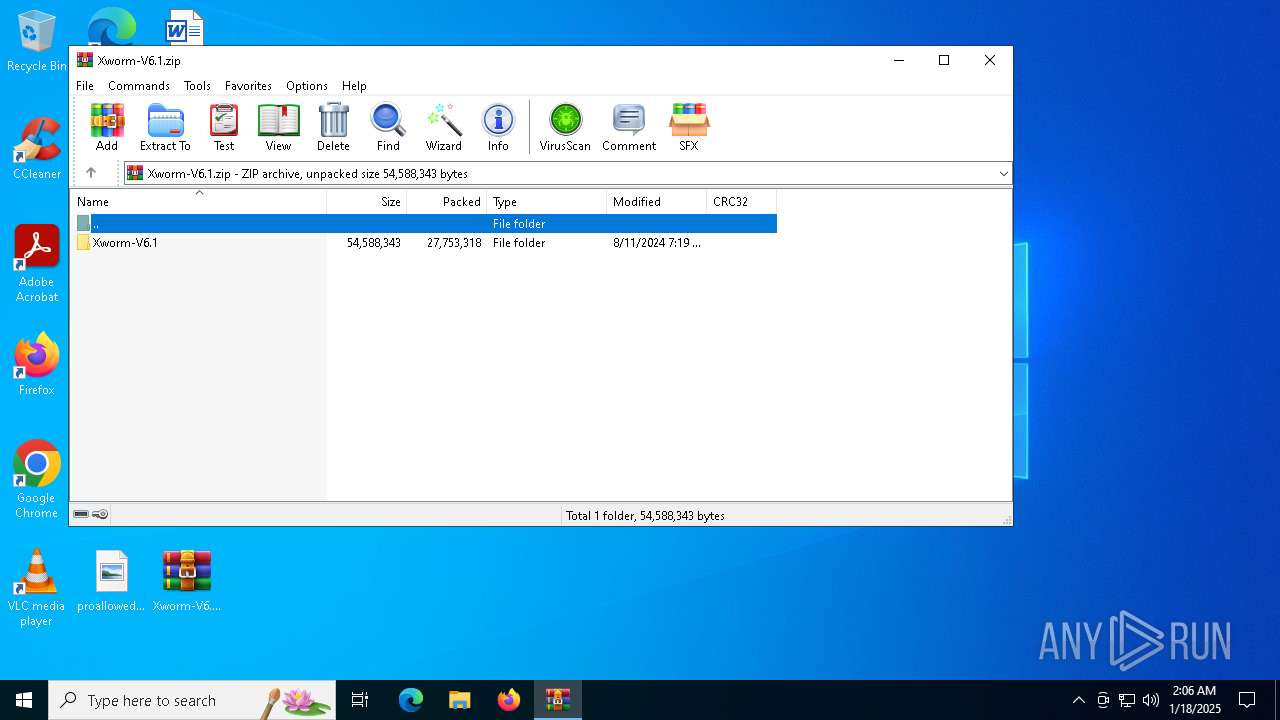
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:08:11 17:19:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Xworm-V6.1/ |
Total processes
135
Monitored processes
16
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\ErrorLogs.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 932 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\icon (5).ico | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1572 | "C:\WINDOWS\System32\OpenWith.exe" "C:\Users\admin\Desktop\XWorm V5.6.exe.config" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1920 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Rar$Scan8170.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Xworm-V6.1.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
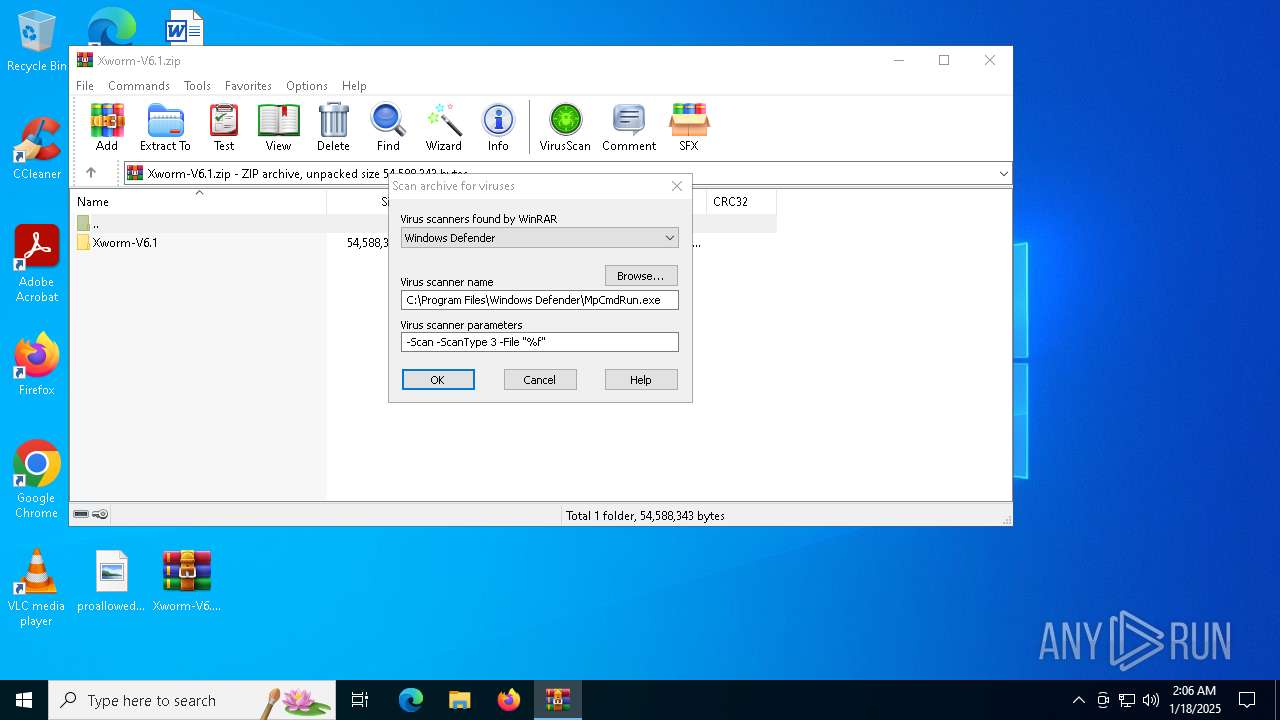
| 4120 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR3840.32804" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4548 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR3840.32804\Rar$Scan24362.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4996 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 007
Read events
4 997
Write events
10
Delete events
0
Modification events
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Xworm-V6.1.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
96
Suspicious files
102
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\Guna.UI2.dll | executable | |
MD5:BCC0FE2B28EDD2DA651388F84599059B | SHA256:C6264665A882E73EB2262A74FEA2C29B1921A9AF33180126325FB67A851310EF | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\FastColoredTextBox.dll | executable | |
MD5:B746707265772B362C0BA18D8D630061 | SHA256:3701B19CCDAC79B880B197756A972027E2AC609EBED36753BD989367EA4EF519 | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\IconExtractor.dll | executable | |
MD5:640D8FFA779C6DD5252A262E440C66C0 | SHA256:440912D85D2F98BB4F508AB82847067C18E1E15BE0D8ECDCFF0CC19327527FC2 | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\Icons\icon (11).ico | image | |
MD5:1C2CEA154DEEDC5A39DAEC2F1DADF991 | SHA256:3B64B79E4092251EBF090164CD2C4815390F34849BBD76FB51085B6A13301B6D | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\Icons\icon (13).ico | image | |
MD5:E6FEC4185B607E01A938FA405E0A6C6C | SHA256:2E2F17B7DD15007192E7CBBD0019355F8BE58068DC5042323123724B99AE4B44 | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\Icons\icon (4).ico | image | |
MD5:9C053BEF57C4A7B575A0726AF0E26DAE | SHA256:5BB21D6C04ED64A1368DACE8F44AFF855860E69F235492A5DC8B642A9EA88E41 | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\Icons\icon (1).ico | image | |
MD5:4F409511E9F93F175CD18187379E94CB | SHA256:115F0DB669B624D0A7782A7CFAF6E7C17282D88DE3A287855DBD6FE0F8551A8F | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\GMap.NET.Core.dll | executable | |
MD5:819352EA9E832D24FC4CEBB2757A462B | SHA256:58C755FCFC65CDDEA561023D736E8991F0AD69DA5E1378DEA59E98C5DB901B86 | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\Icons\icon (10).ico | image | |
MD5:AD1740CB3317527AA1ACAE6E7440311E | SHA256:7A97547954AAAD629B0563CC78BCA75E3339E8408B70DA2ED67FA73B4935D878 | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3840.31218\Xworm-V6.1.zip\Xworm-V6.1\Xworm-V6.1\GeoIP.dat | binary | |
MD5:8EF41798DF108CE9BD41382C9721B1C9 | SHA256:BC07FF22D4EE0B6FAFCC12482ECF2981C172A672194C647CEDF9B4D215AD9740 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
19
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5448 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | — | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | — | 1.01 Kb | whitelisted |
2220 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | — | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | — | 973 b | whitelisted |
5448 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | — | 1.01 Kb | whitelisted |
2220 | RUXIMICS.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | — | 1.01 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5448 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2220 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
5448 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2220 | RUXIMICS.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5448 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2220 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
crl.microsoft.com |
| unknown |
www.microsoft.com |
| unknown |
self.events.data.microsoft.com |
| unknown |