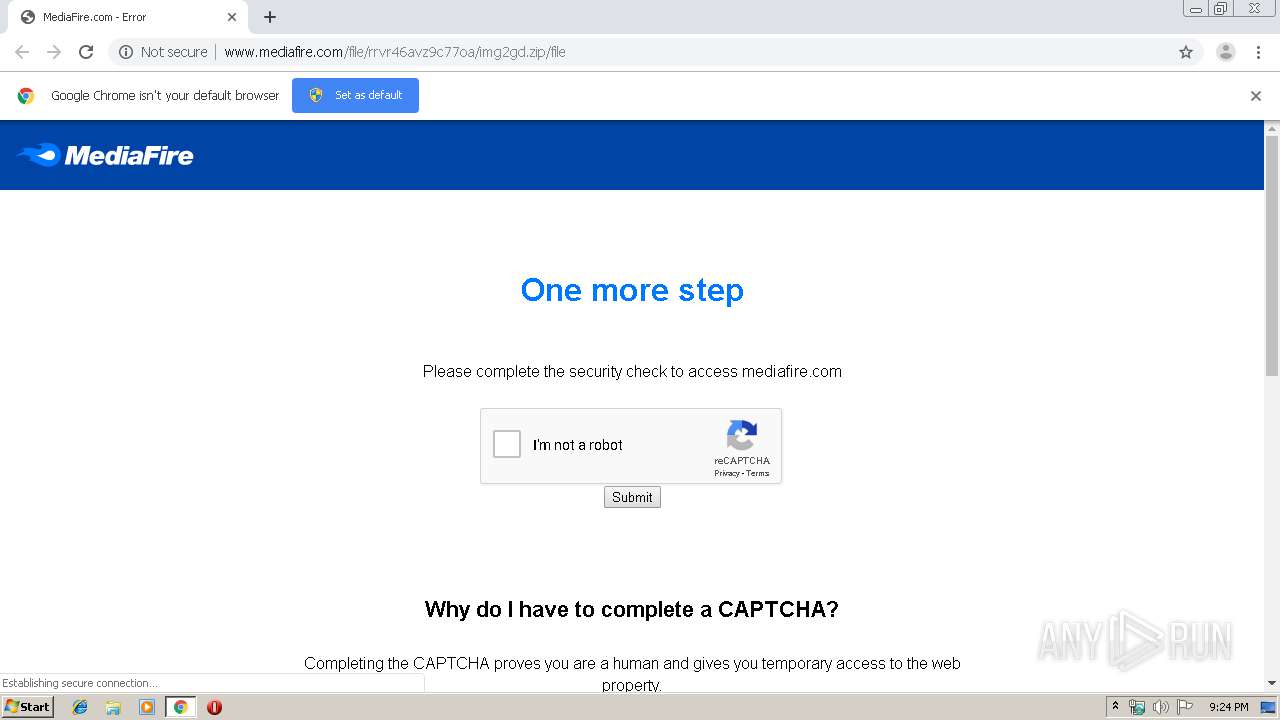
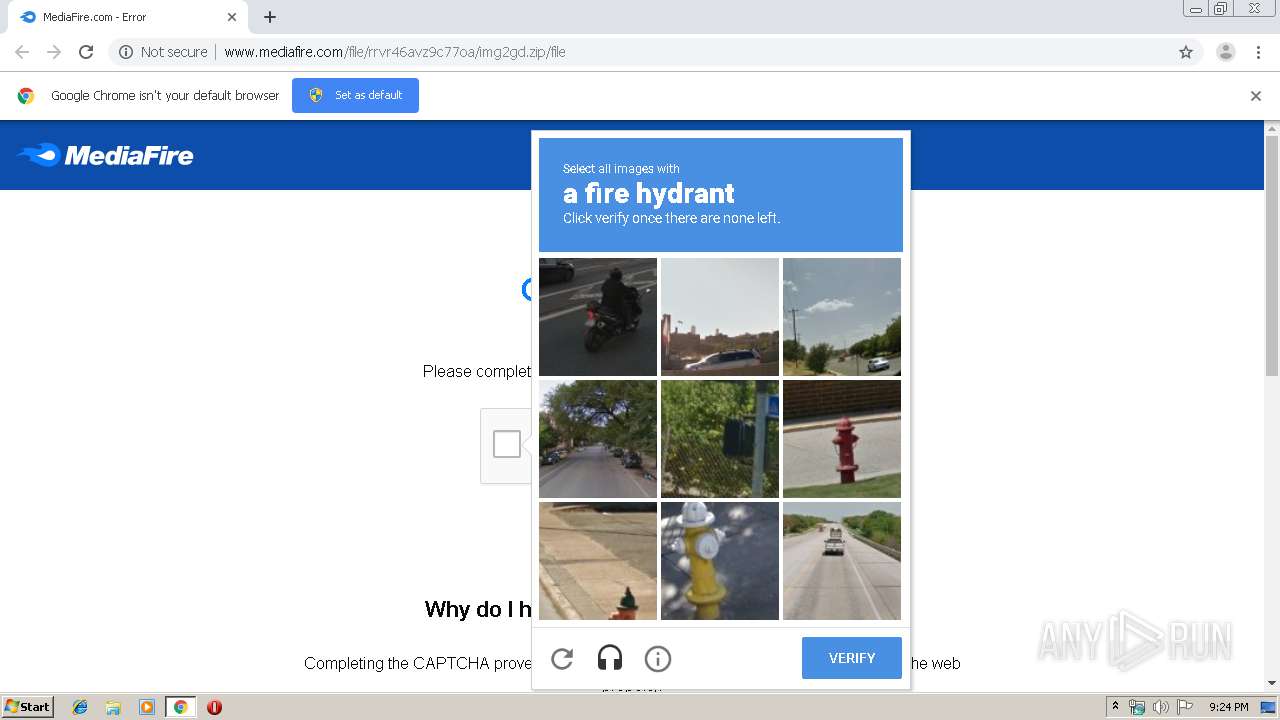
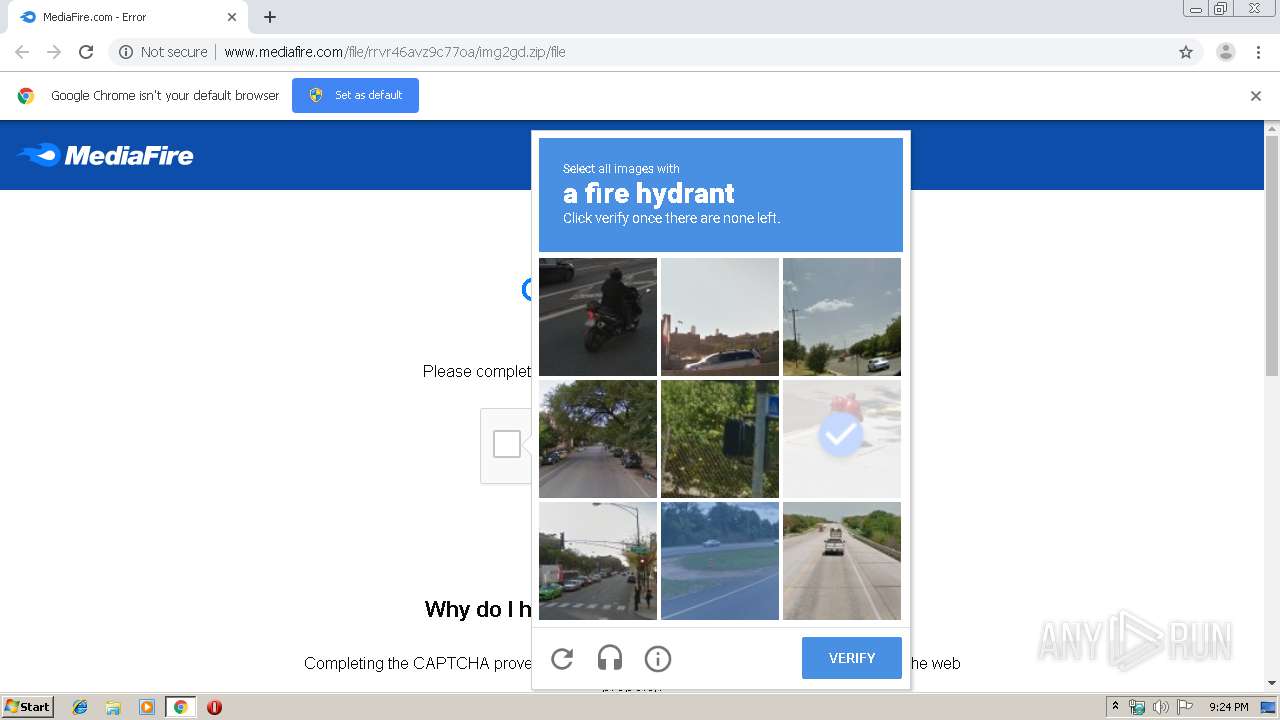
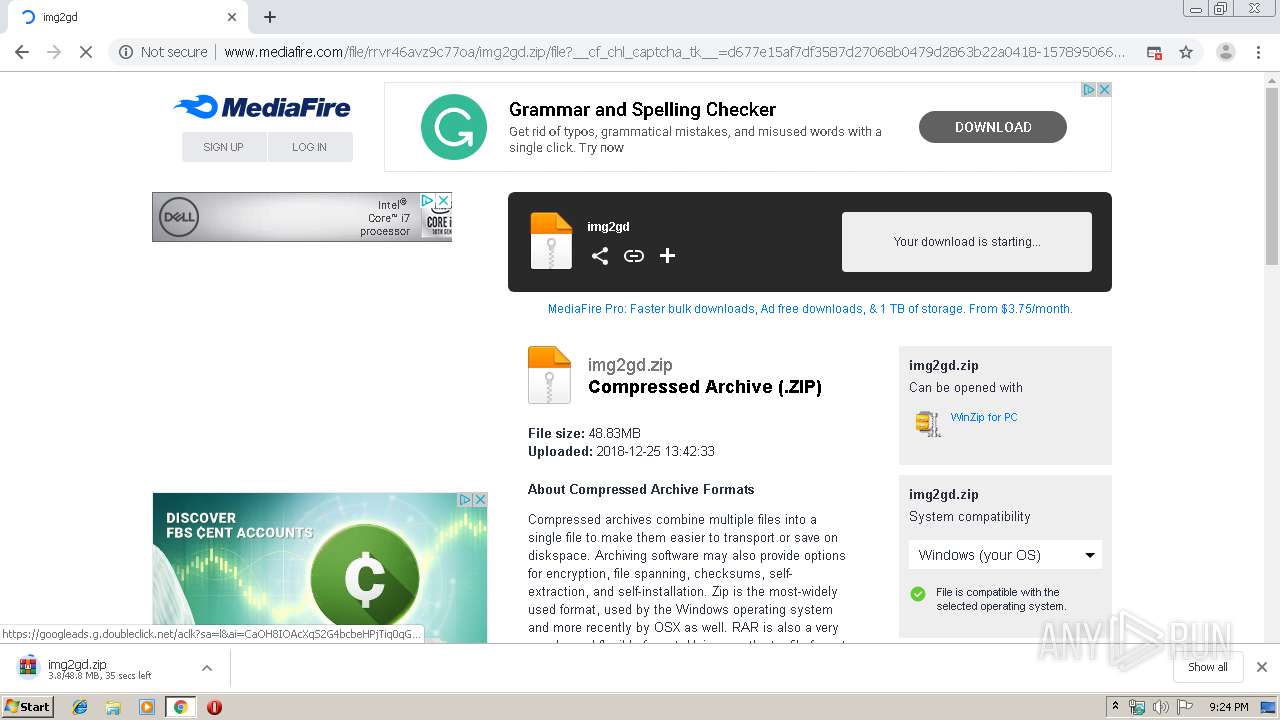
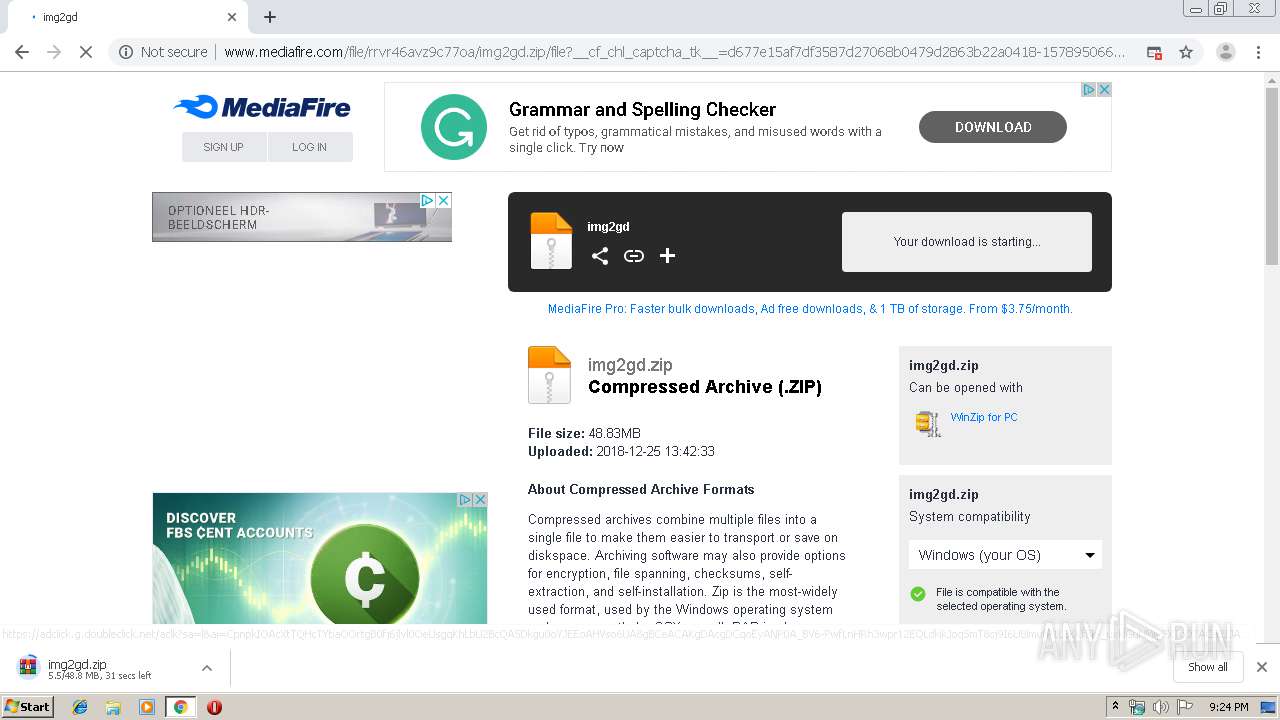
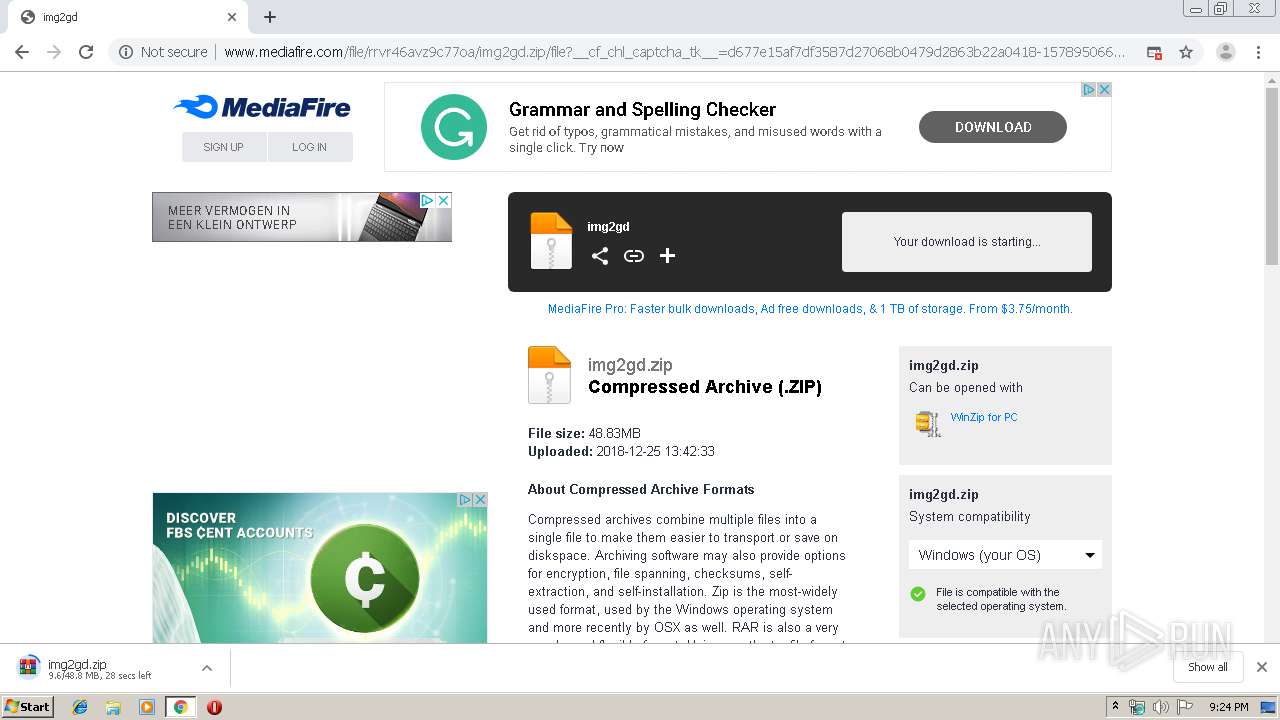
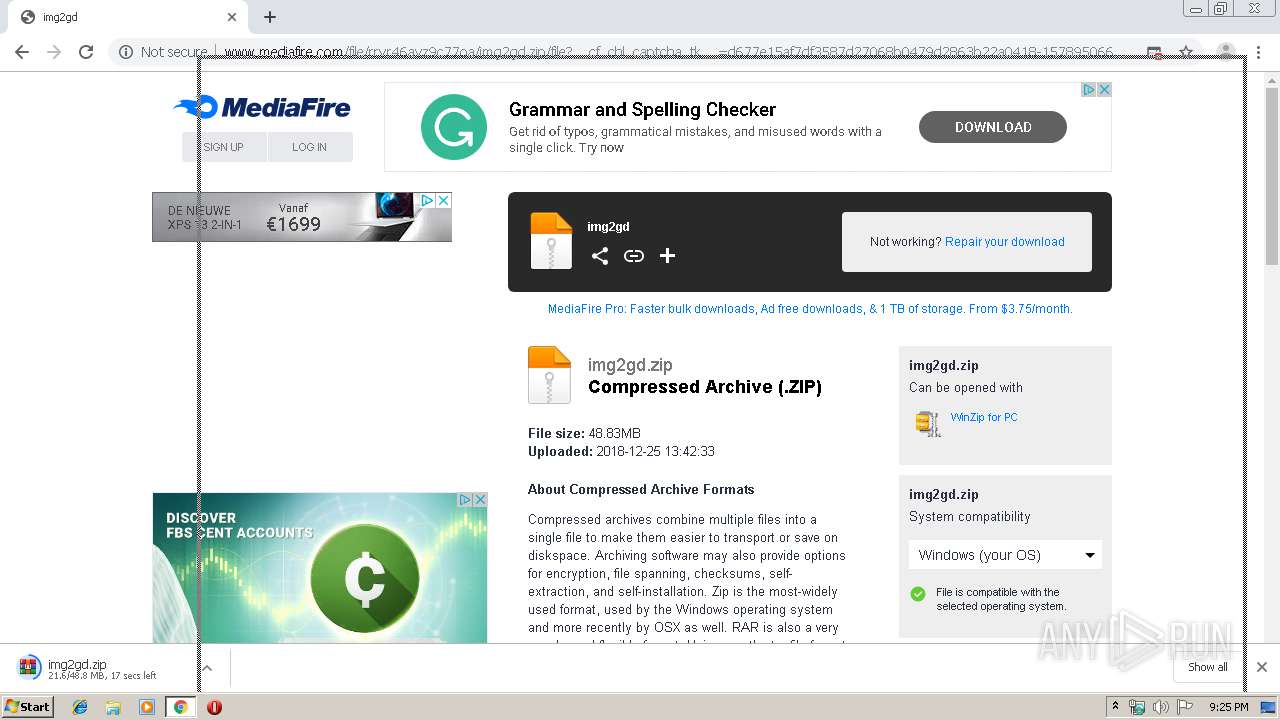
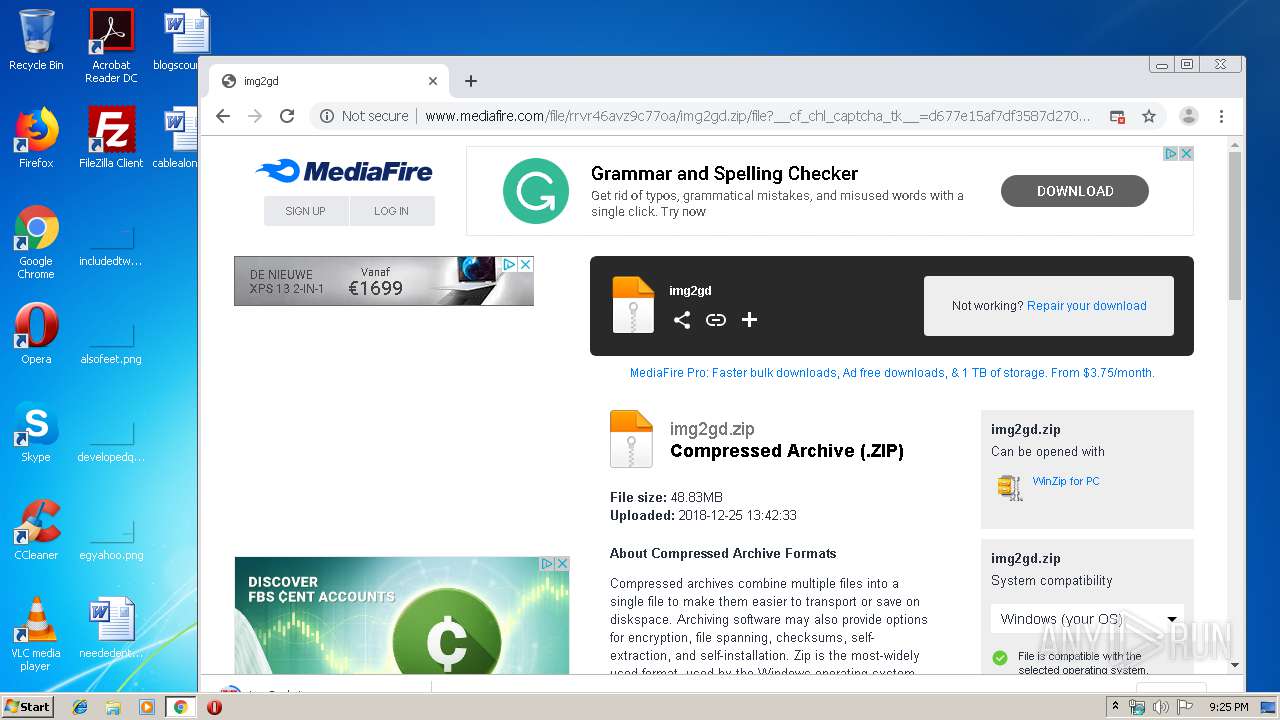
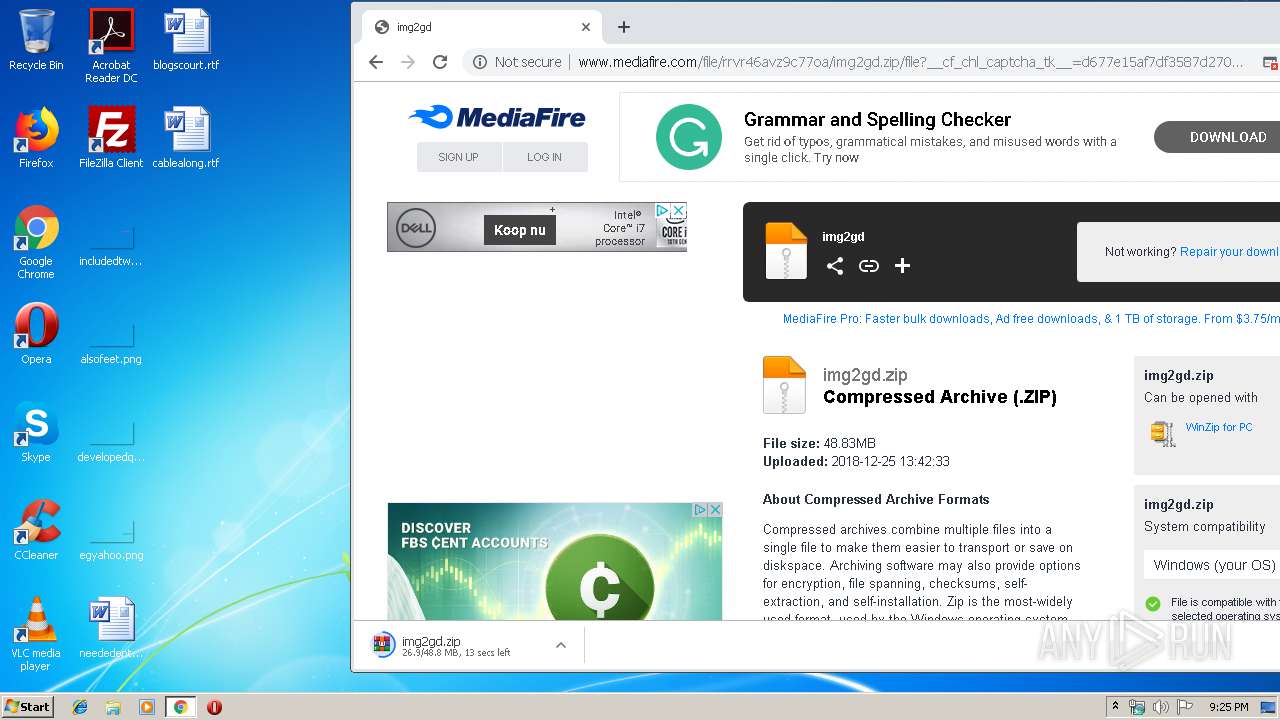
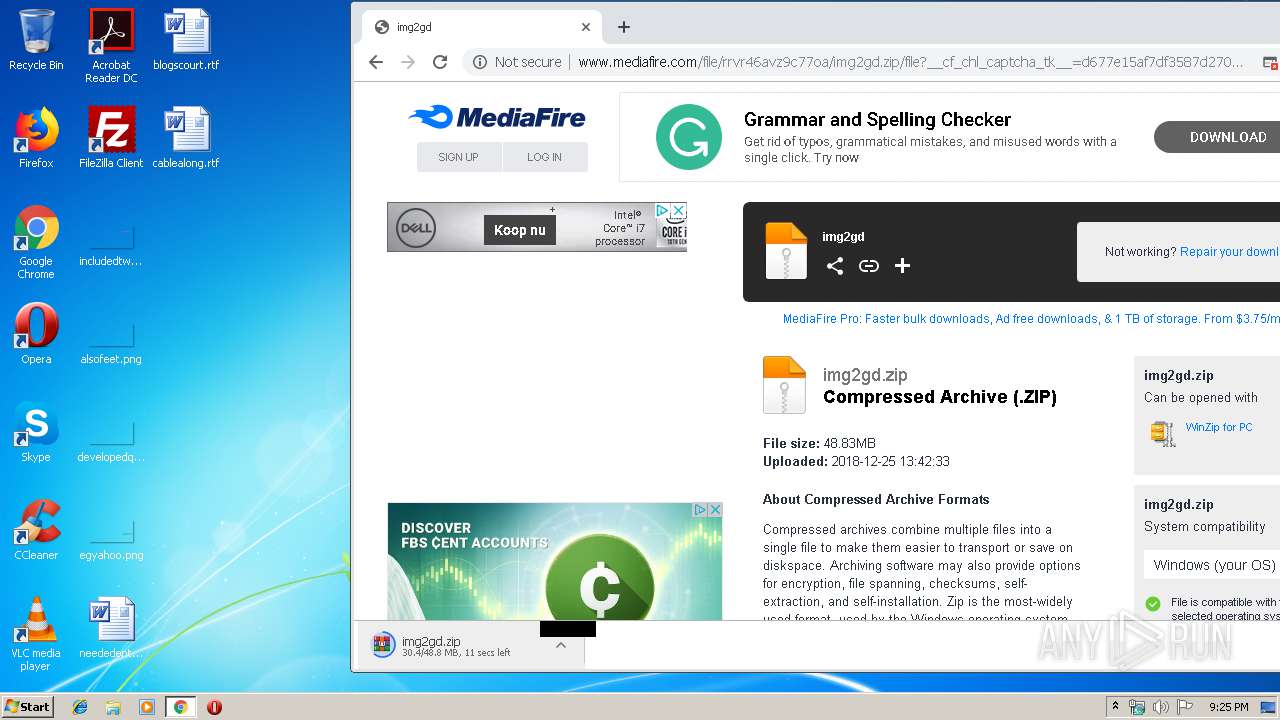
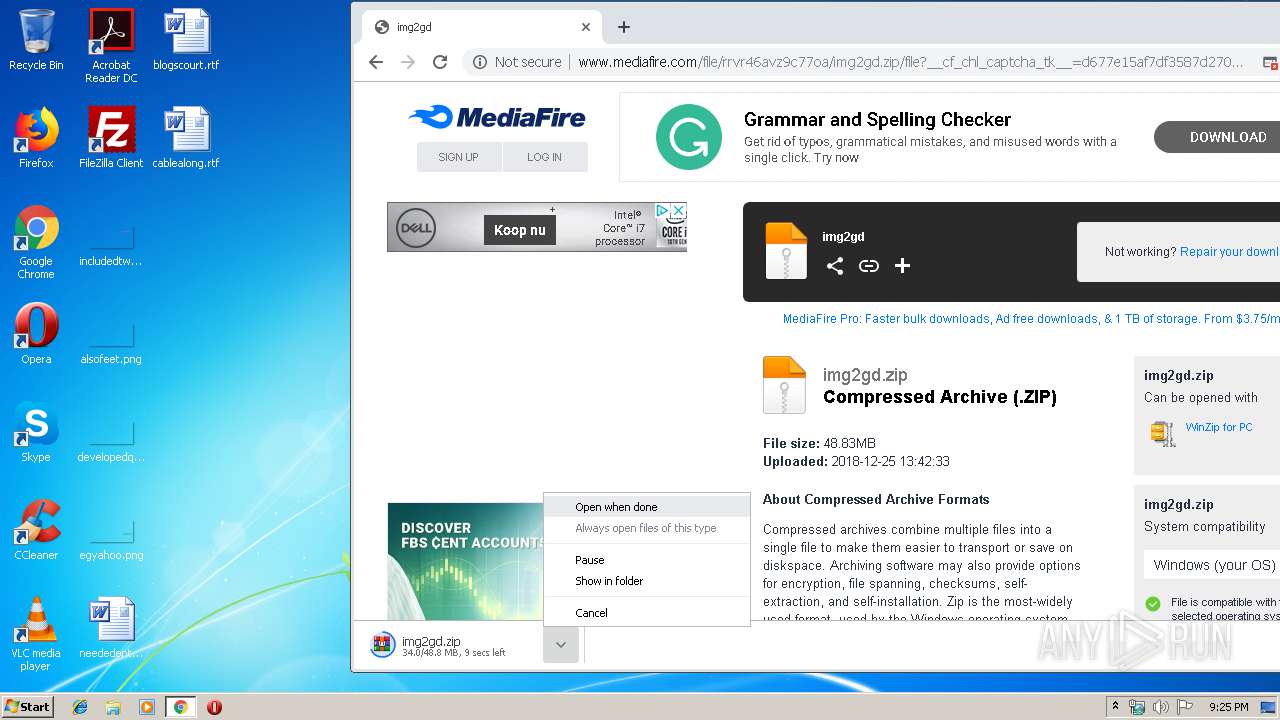
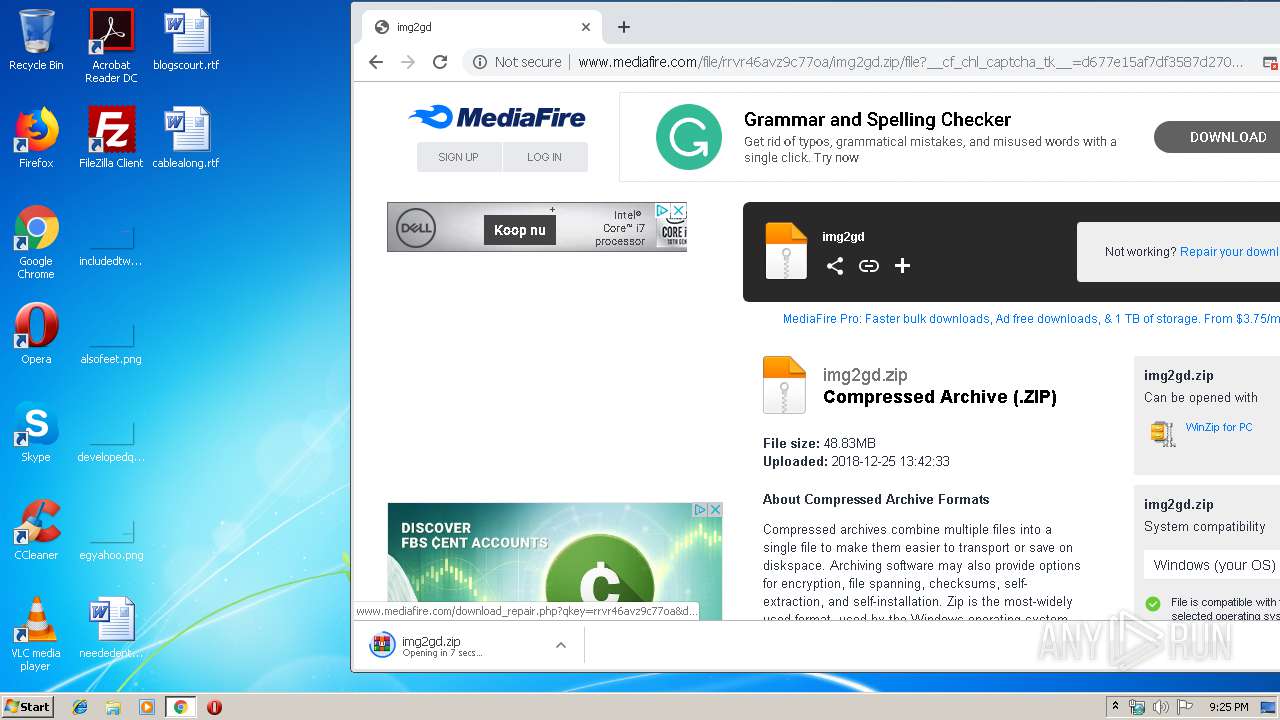
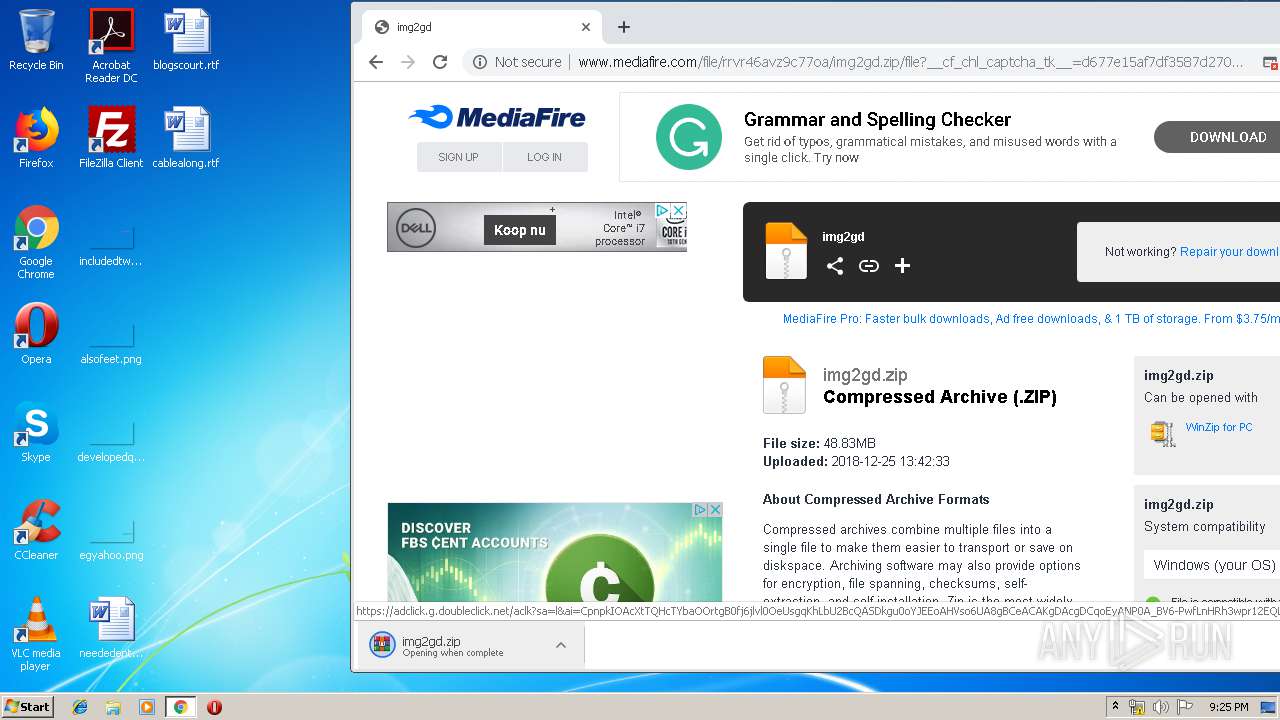
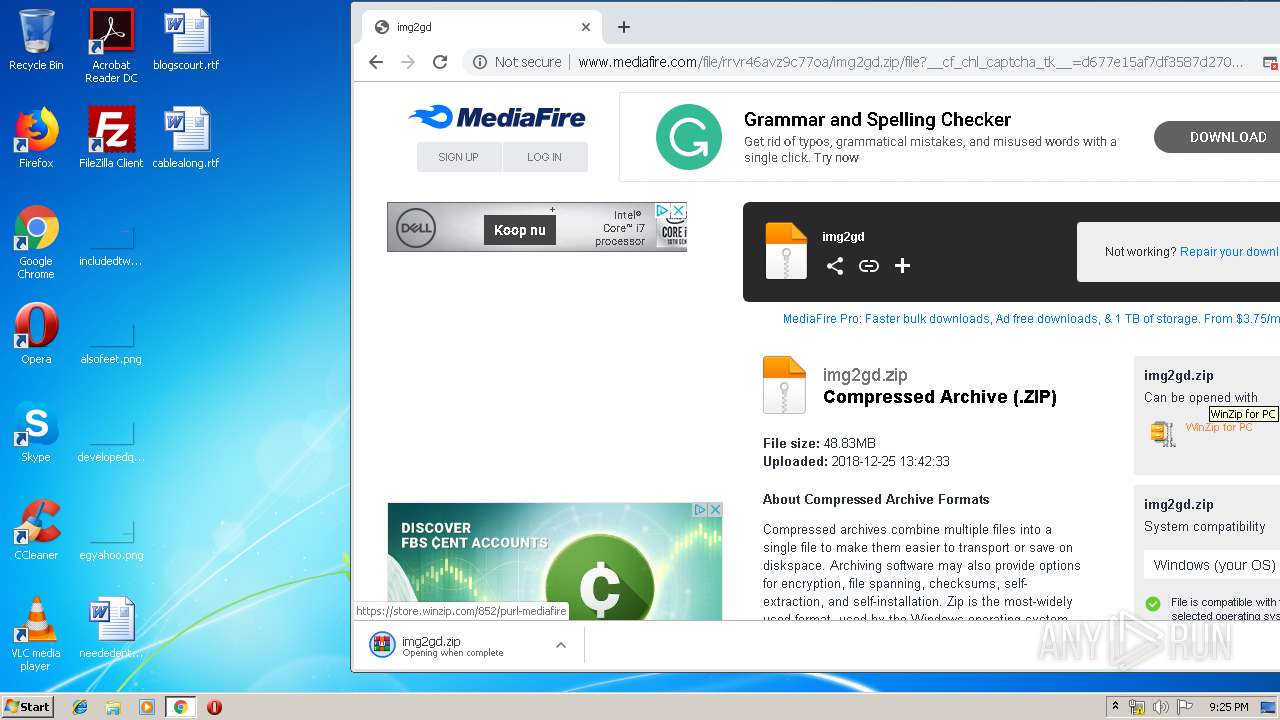
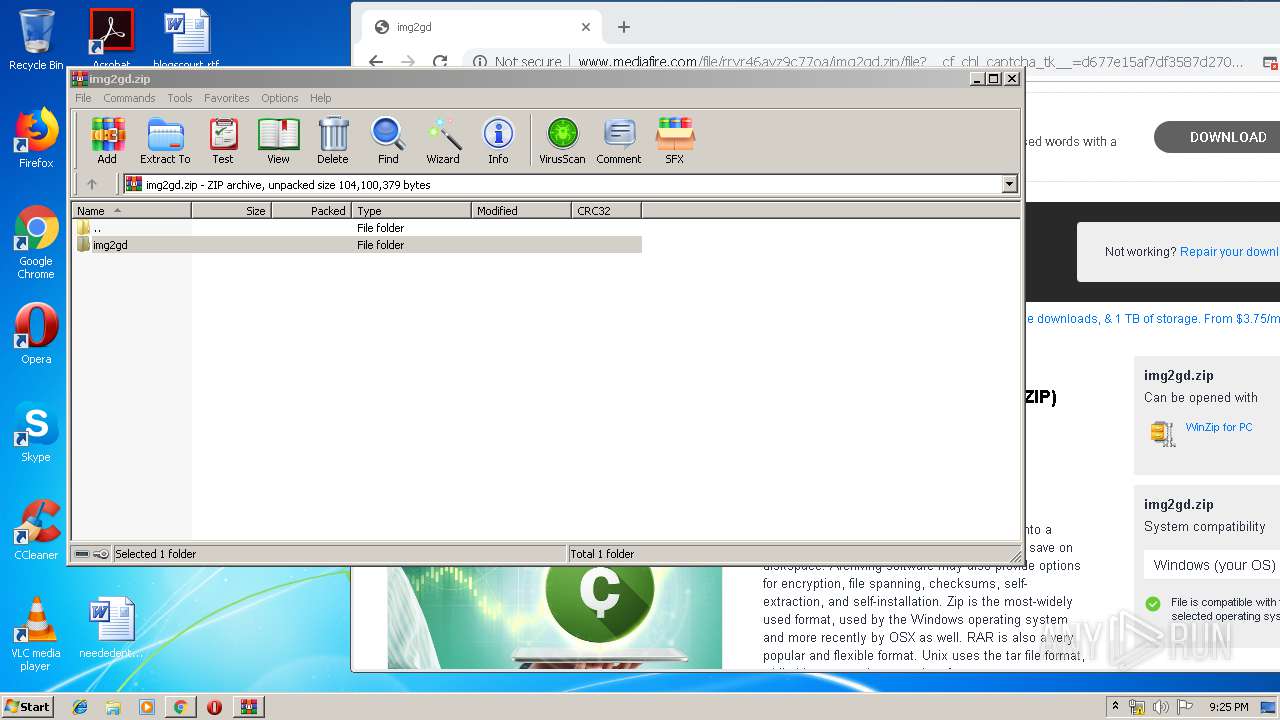
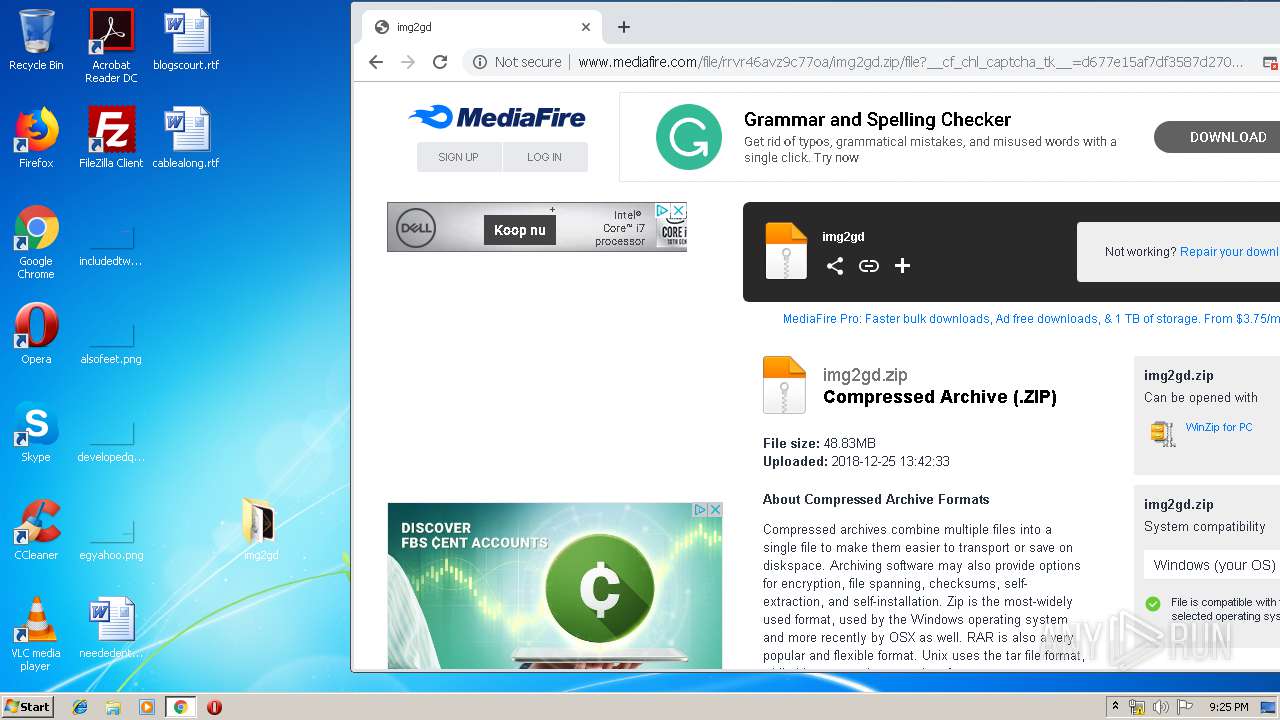
| URL: | http://www.mediafire.com/file/rrvr46avz9c77oa/img2gd.zip/file |
| Full analysis: | https://app.any.run/tasks/316a9de9-d929-4078-b504-40c1a8c0d99d |
| Verdict: | Malicious activity |
| Analysis date: | January 13, 2020, 21:24:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5C4C0DF640BFDB5C68A9D6A39D42FF7E |
| SHA1: | 287E6171CF997194CAE1D6C2133544E33EA31D01 |
| SHA256: | 76D00A9A04C69F3D3E67BAE9CBE4975EECC1F167B33B85F3FC8722280165F98E |
| SSDEEP: | 3:N1KJS4w3eGUo7OeoiUY9:Cc4w3eGHOeoq |
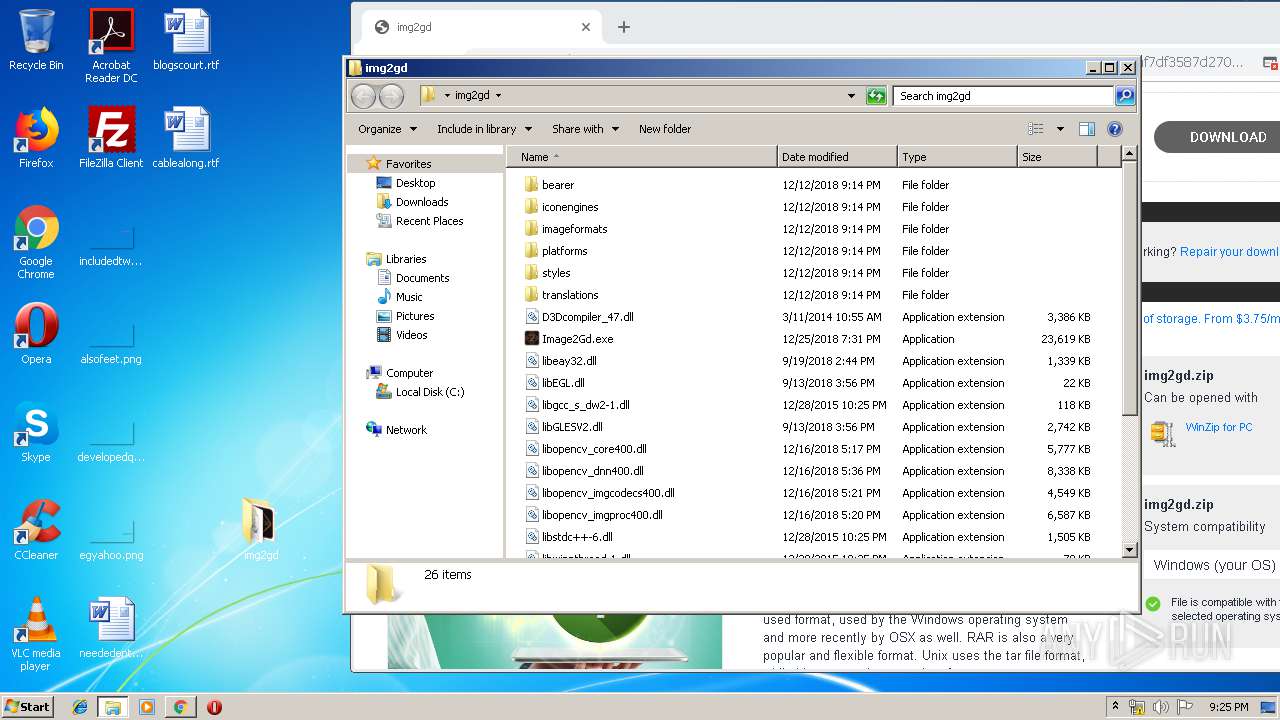
MALICIOUS
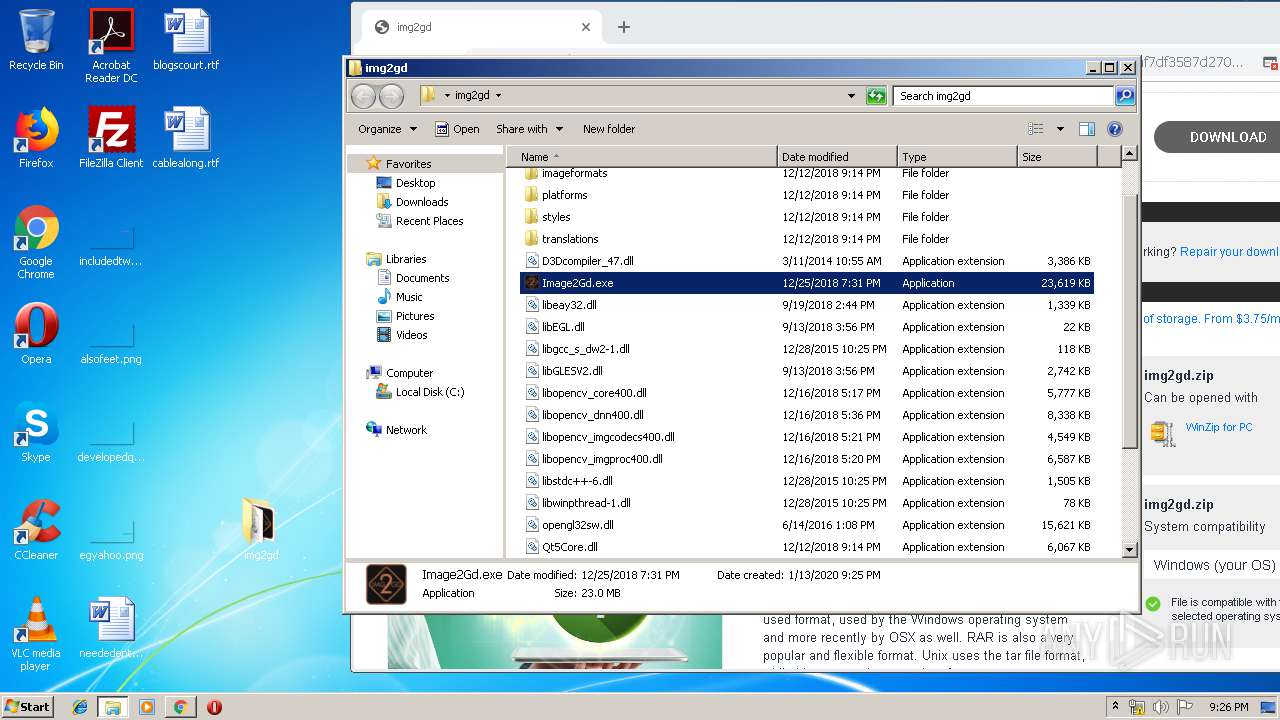
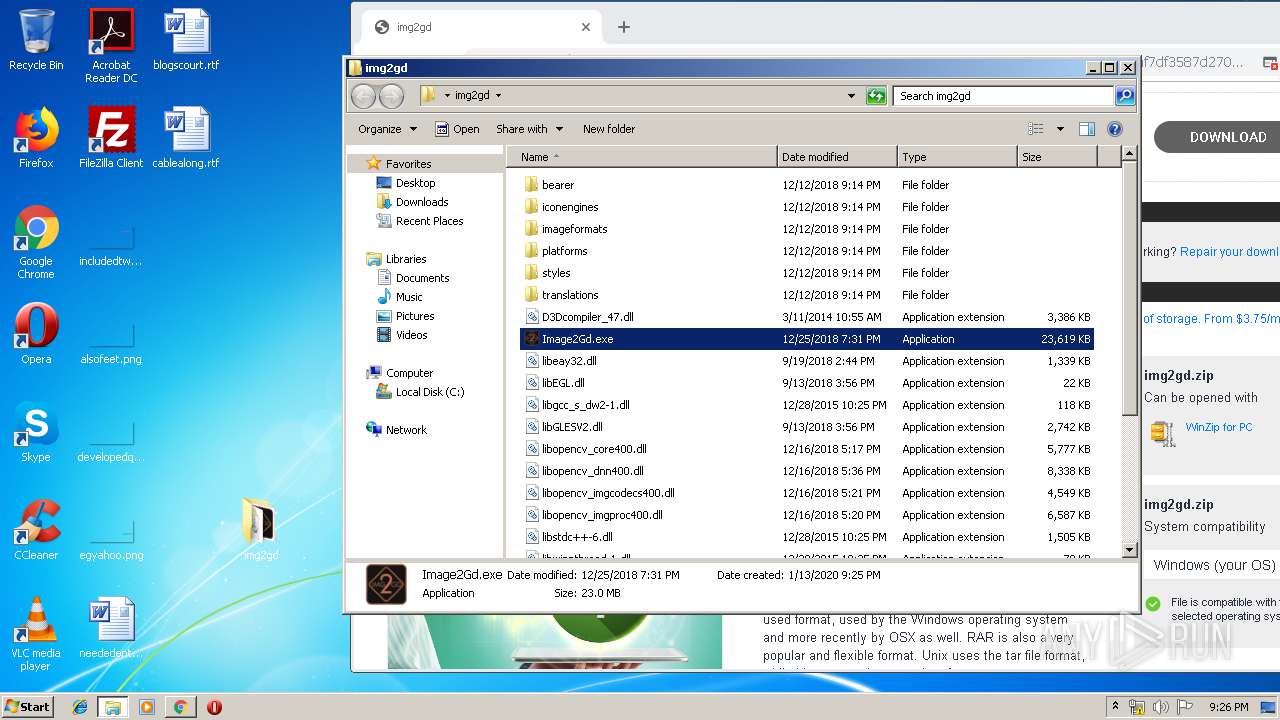
Application was dropped or rewritten from another process
- Image2Gd.exe (PID: 2112)
- Image2Gd.exe (PID: 2456)
Loads dropped or rewritten executable
- Image2Gd.exe (PID: 2112)
- SearchProtocolHost.exe (PID: 3476)
- explorer.exe (PID: 352)
- Image2Gd.exe (PID: 2456)
SUSPICIOUS
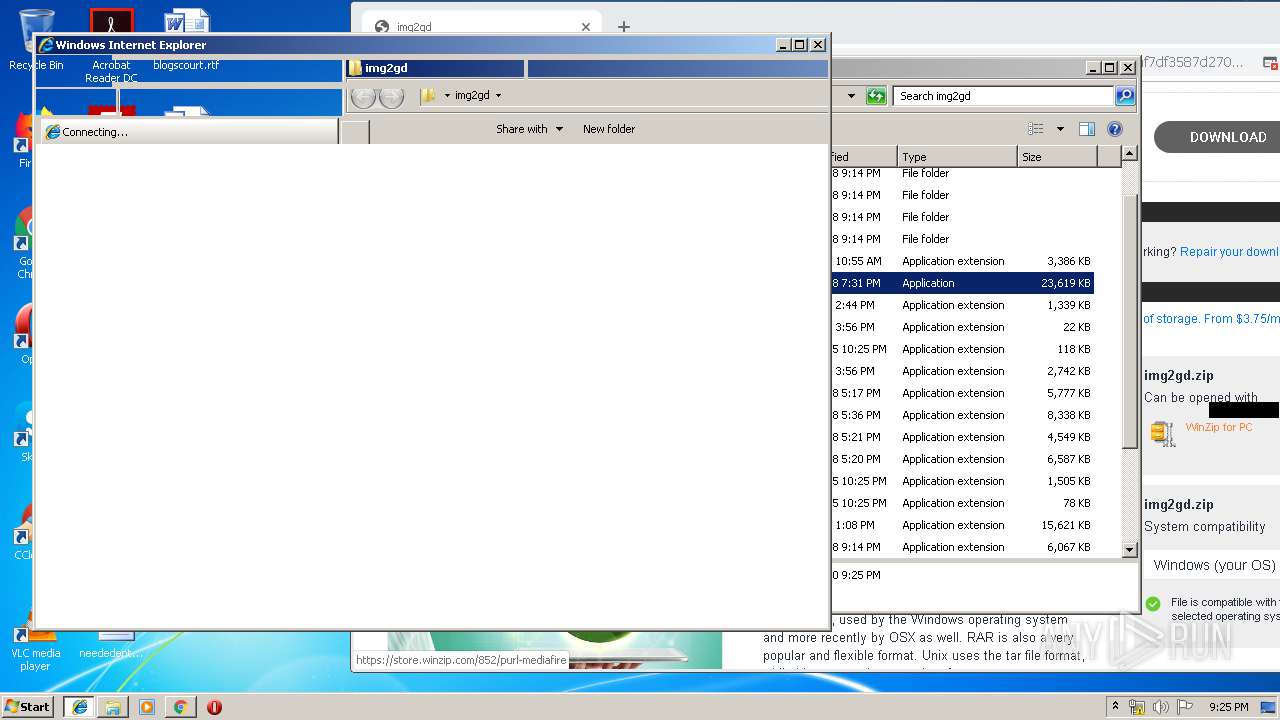
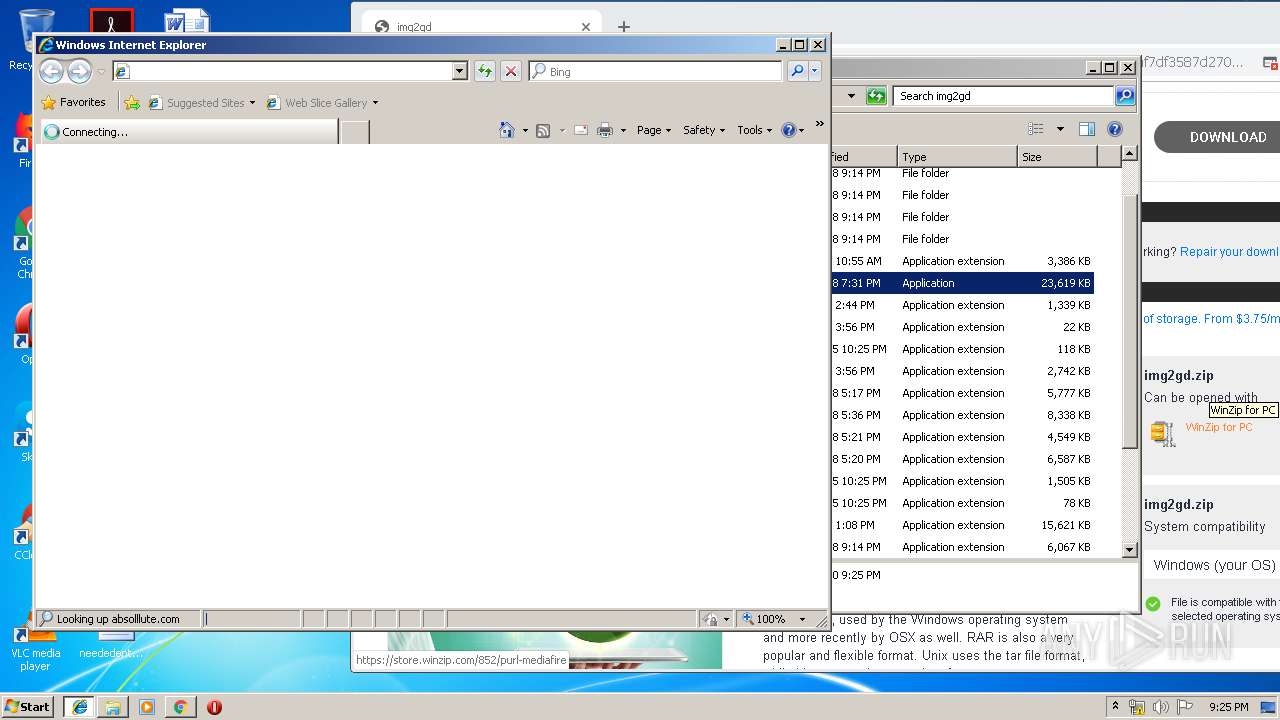
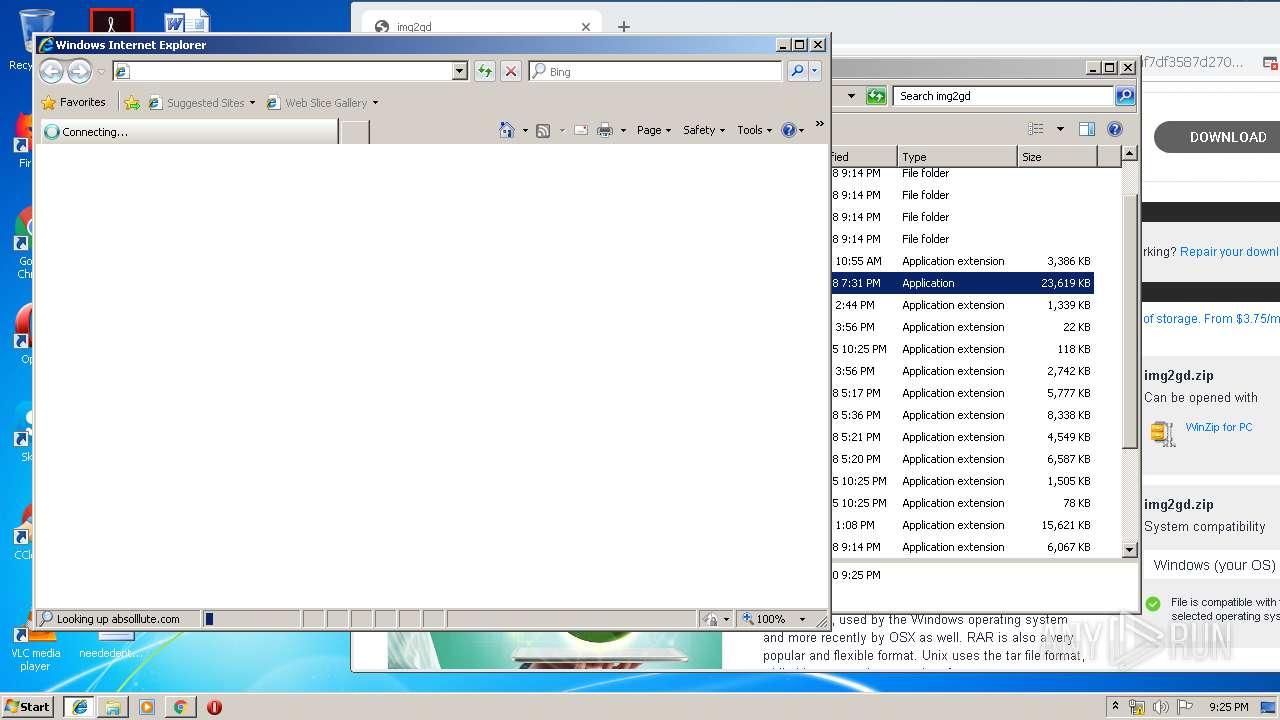
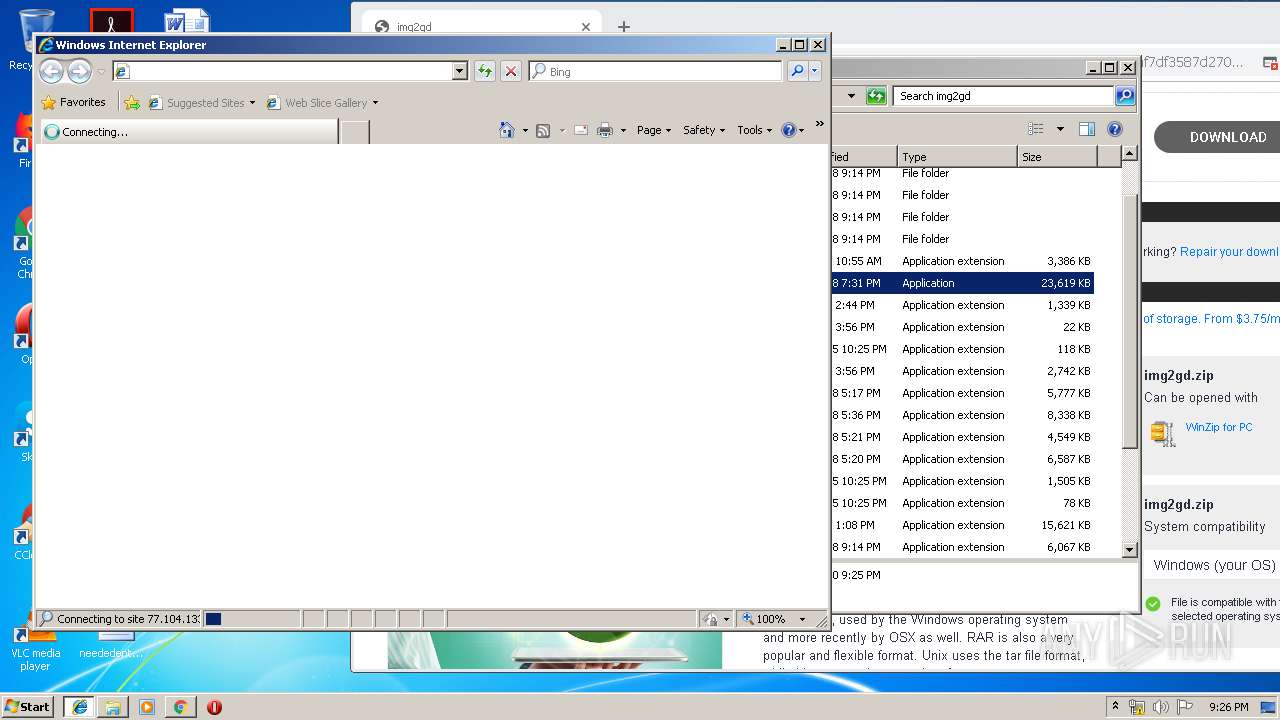
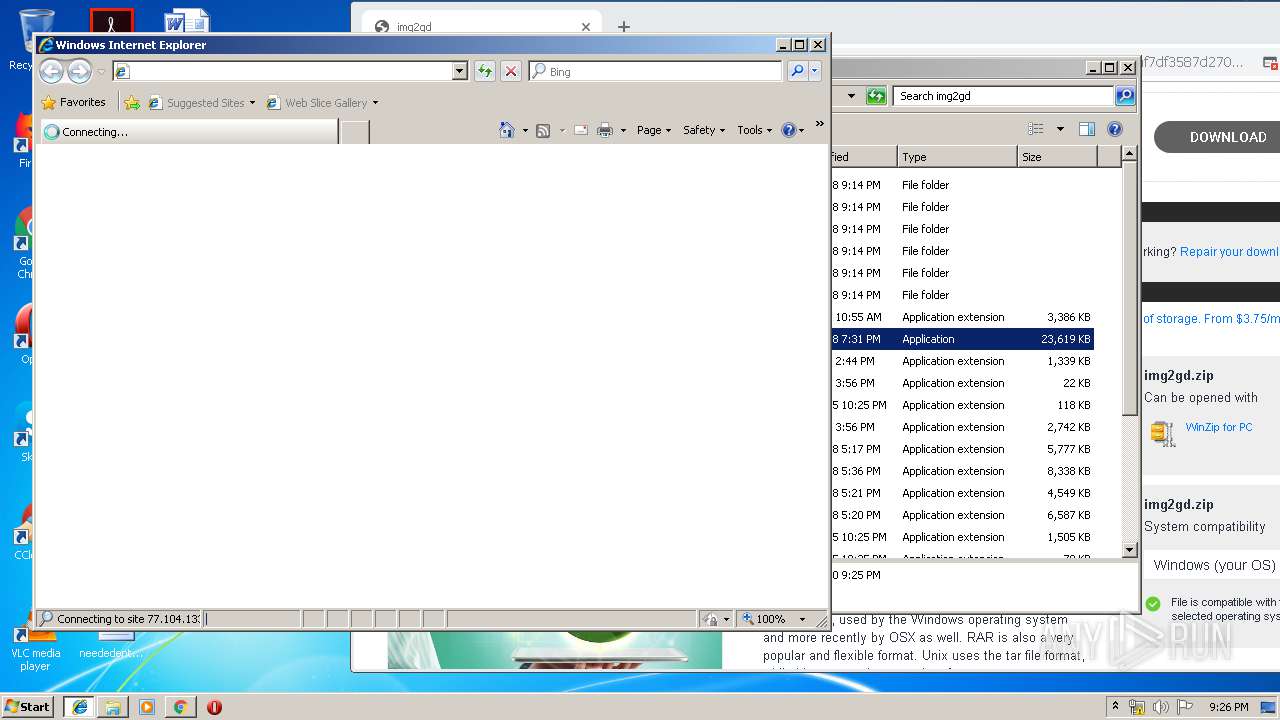
Starts Internet Explorer
- Image2Gd.exe (PID: 2112)
- Image2Gd.exe (PID: 2456)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1248)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
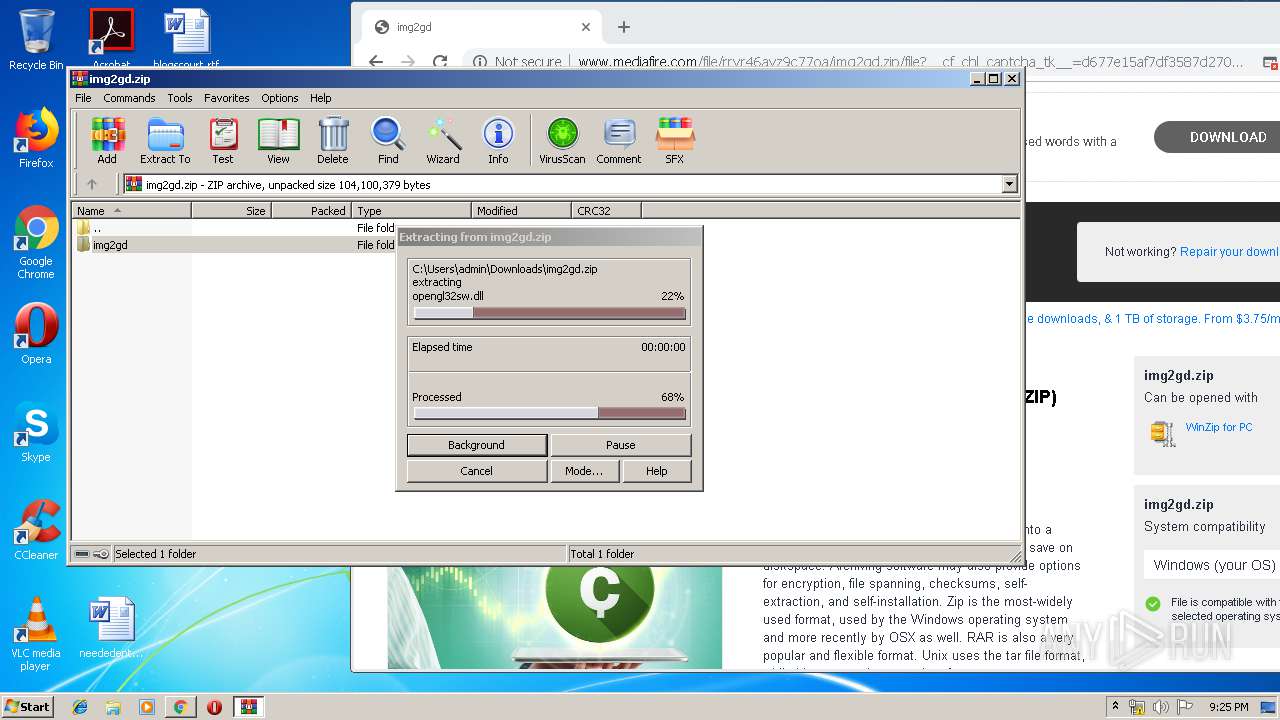
Executable content was dropped or overwritten
- WinRAR.exe (PID: 516)
Creates files in the user directory
- explorer.exe (PID: 352)
INFO
Reads the hosts file
- chrome.exe (PID: 1248)
- chrome.exe (PID: 3948)
Application launched itself
- iexplore.exe (PID: 3100)
- chrome.exe (PID: 1248)
- iexplore.exe (PID: 1888)
Reads Internet Cache Settings
- iexplore.exe (PID: 3124)
- chrome.exe (PID: 1248)
- iexplore.exe (PID: 3464)
Changes internet zones settings
- iexplore.exe (PID: 1888)
- iexplore.exe (PID: 3100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
45
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
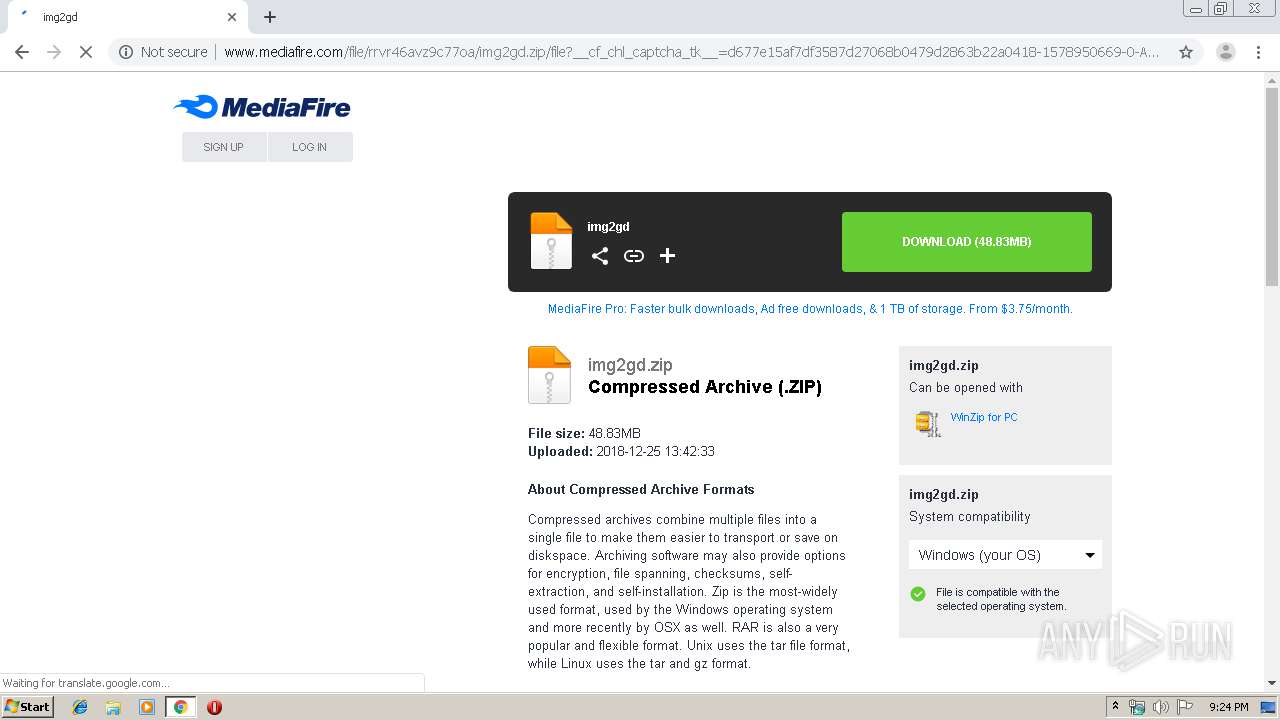
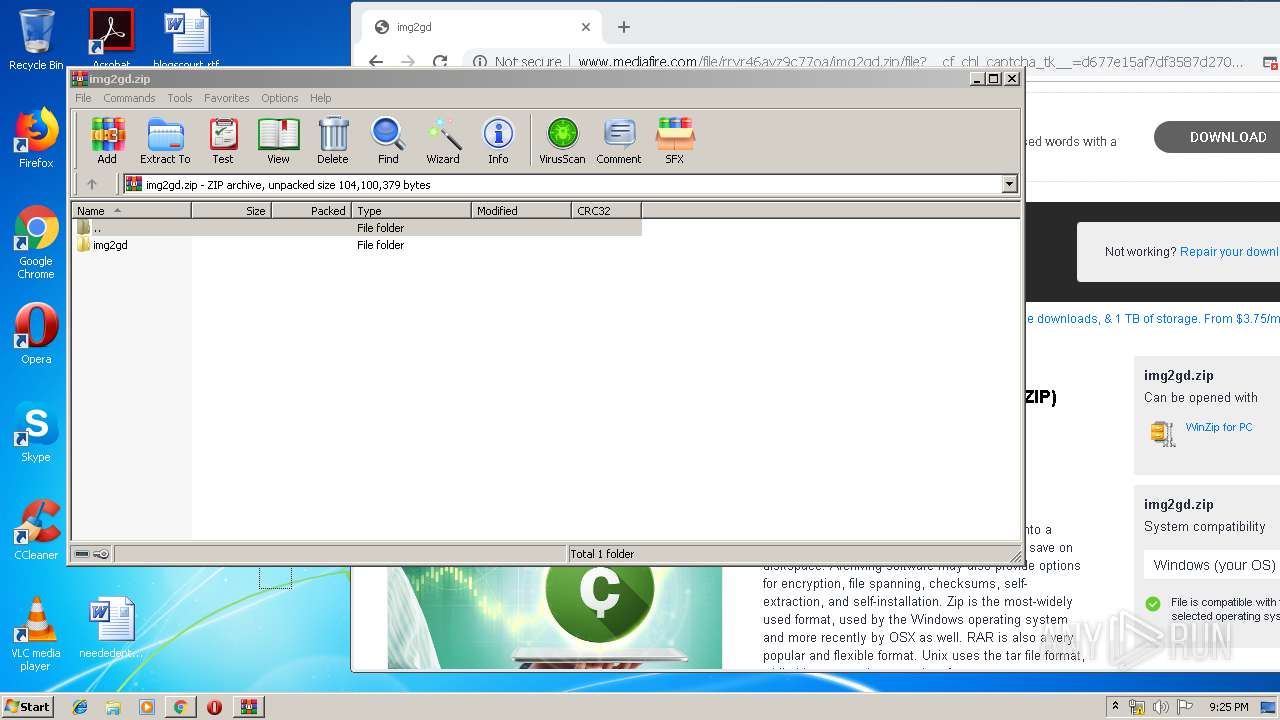
| 516 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\img2gd.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11381905114397681843,17283107736662440792,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14464158960146121439 --mojo-platform-channel-handle=4560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11381905114397681843,17283107736662440792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15964175743702167230 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11381905114397681843,17283107736662440792,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2146984398045338124 --mojo-platform-channel-handle=4732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11381905114397681843,17283107736662440792,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18326006351509724531 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11381905114397681843,17283107736662440792,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5315569400317403989 --mojo-platform-channel-handle=4552 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11381905114397681843,17283107736662440792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13305515260426478565 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11381905114397681843,17283107736662440792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2199344055327874077 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.mediafire.com/file/rrvr46avz9c77oa/img2gd.zip/file" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 510
Read events
3 214
Write events
287
Delete events
9
Modification events
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1248-13223424266296500 |
Value: 259 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
29
Suspicious files
82
Text files
269
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1e71ddfe-8df0-43b9-a836-6cf07d236d56.tmp | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39b977.TMP | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39b967.TMP | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39b996.TMP | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
80
DNS requests
77
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3948 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/cdn-cgi/scripts/cf.challenge.js | US | text | 3.20 Kb | shared |
3948 | chrome.exe | GET | 403 | 104.16.202.237:80 | http://www.mediafire.com/file/rrvr46avz9c77oa/img2gd.zip/file | US | html | 5.61 Kb | shared |
3948 | chrome.exe | GET | 302 | 216.58.206.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
3948 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.20 Kb | shared |
3948 | chrome.exe | GET | 302 | 216.58.206.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3948 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
3948 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/js/prebid2.44.1.js | US | text | 52.9 Kb | shared |
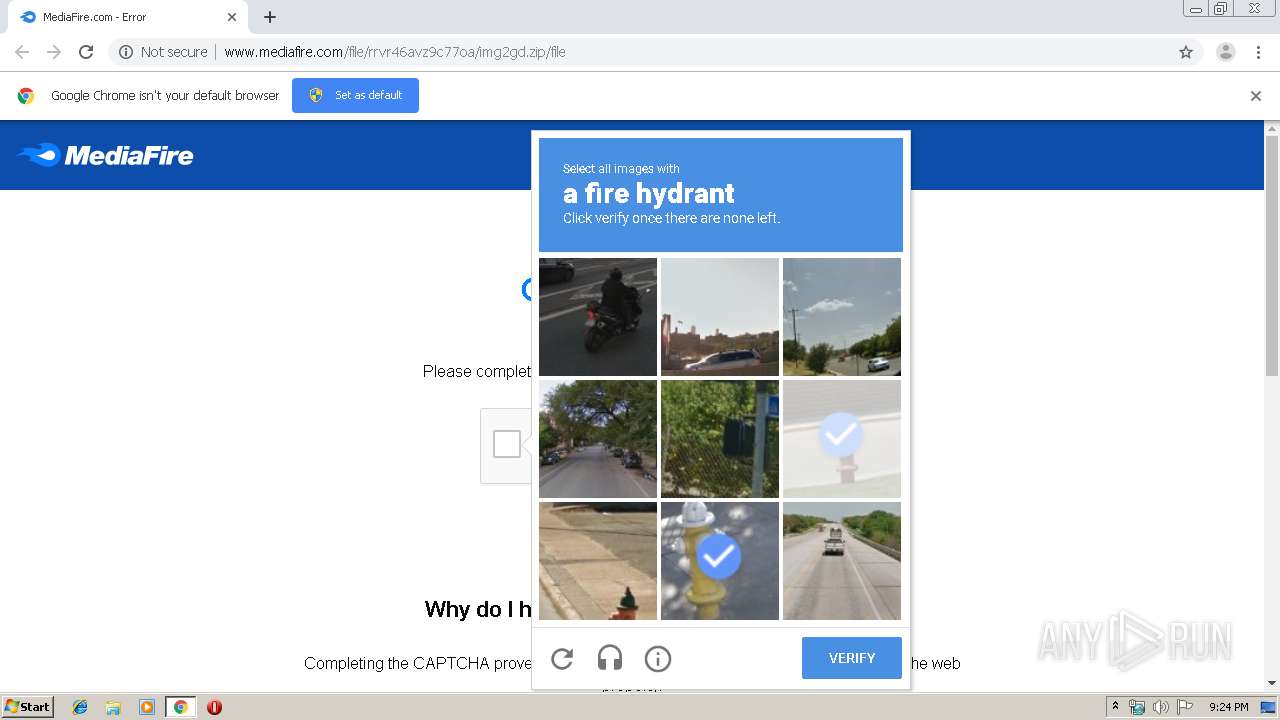
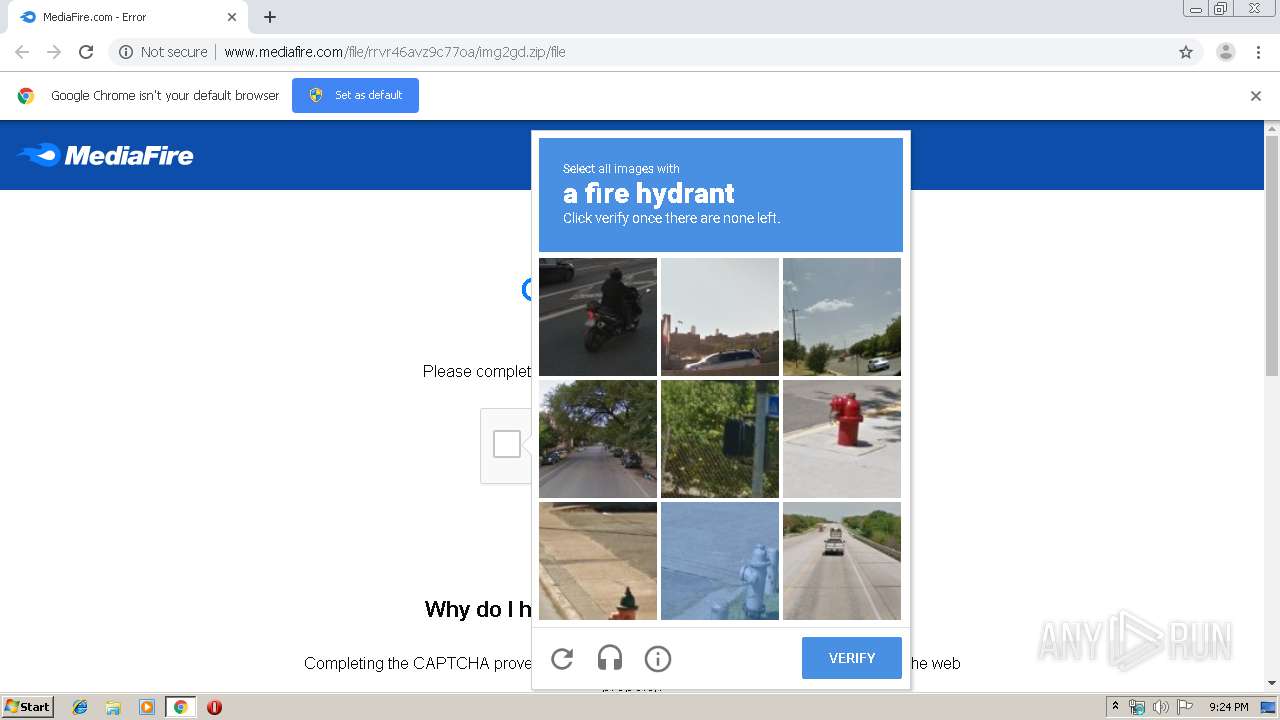
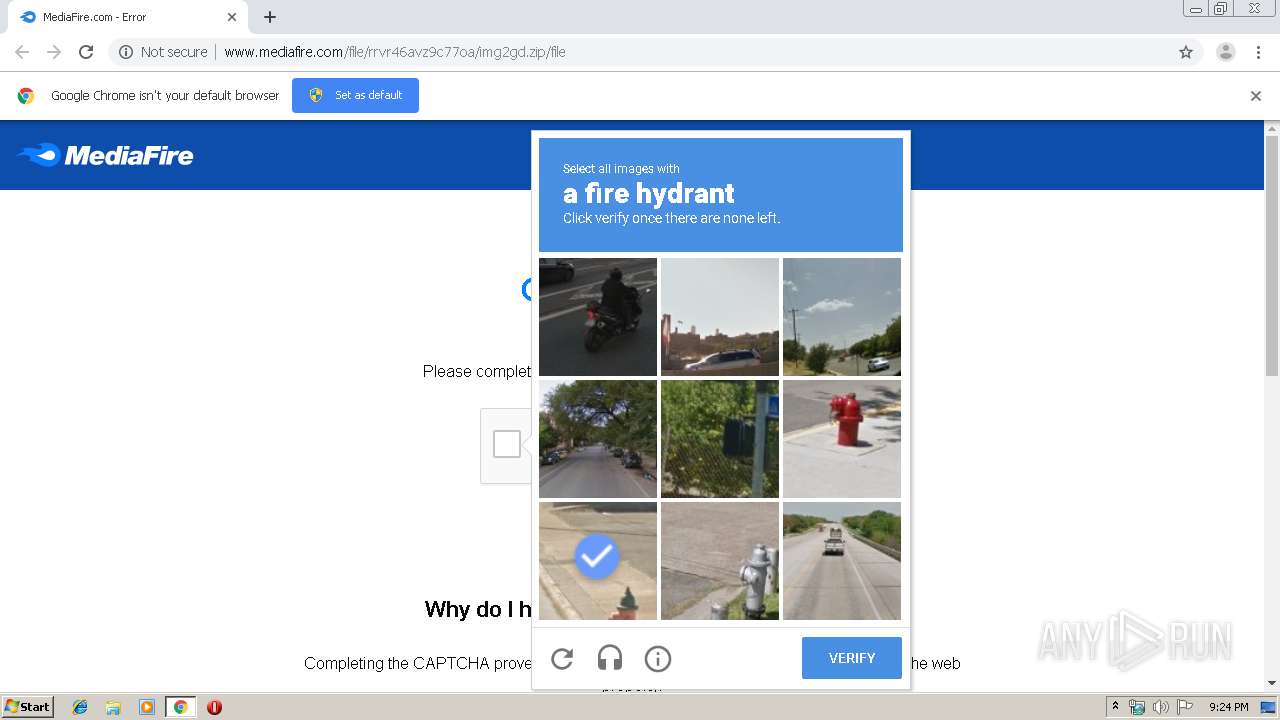
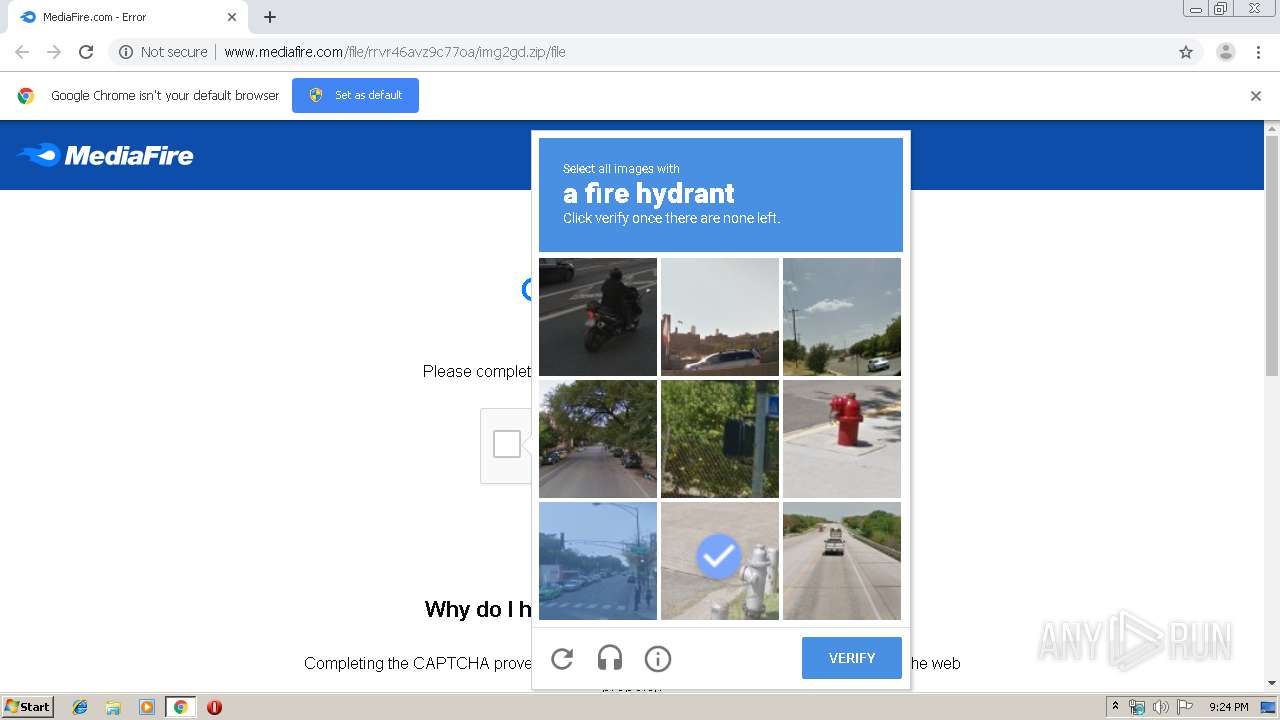
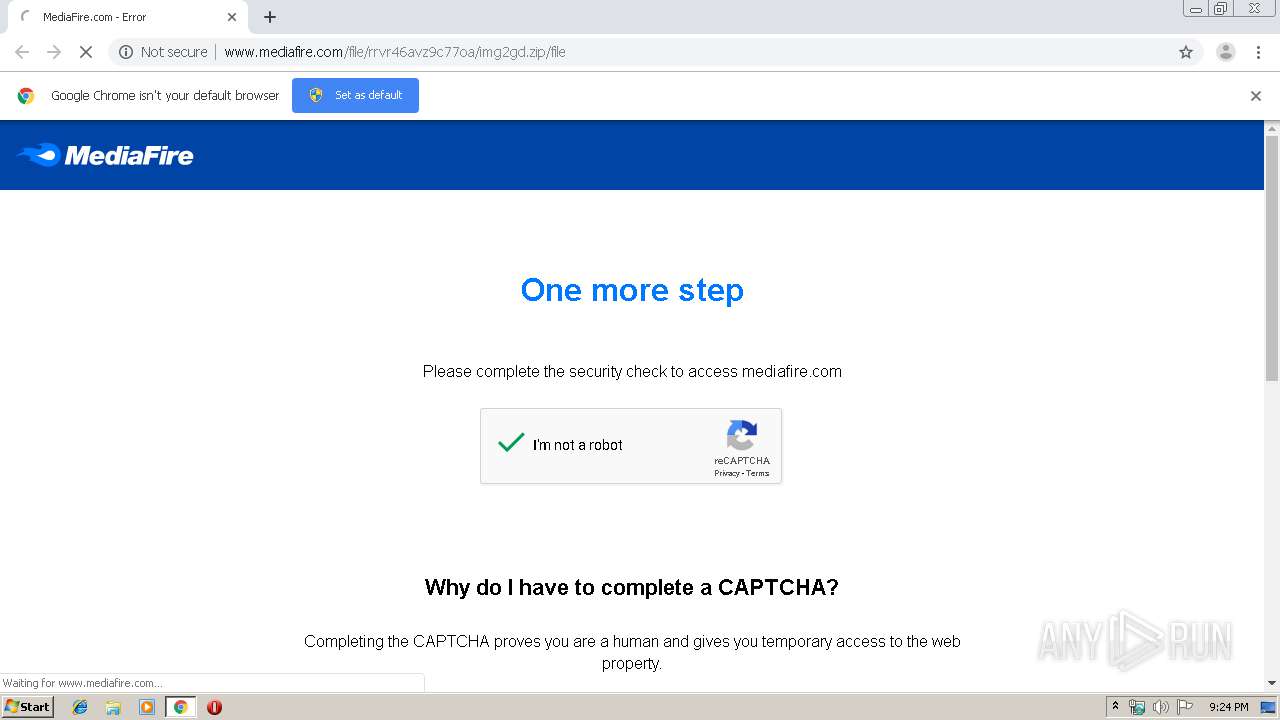
3948 | chrome.exe | POST | 200 | 104.16.202.237:80 | http://www.mediafire.com/file/rrvr46avz9c77oa/img2gd.zip/file?__cf_chl_captcha_tk__=d677e15af7df3587d27068b0479d2863b22a0418-1578950669-0-AbM4Xpl2cD0RkYP88kw-w_HZYH0rBEoK24XV4T6Up_ApsfrlXhrBx3ke5CrIeWpmmxFA5Dt9lPoGVa-uvkR_efmM5vFleydsoRPI8Bgr58YKqPecmavV6z1WfplL-au06JJfR8aZkW6eVyM7imBTMxBWWV8sDvs0IiI0vxoUS9eee1LHp1LblRR8Ub0n57cnSRIFkj_ESQVx_q33DM9P7S_E9qmcuf8ItXyS8IBDFPszy2rJrEFpZ8cqRP6rv89qopvYY1BWiZjPQGtLTGpubs9lXSwnQ2Zsy_Dz05kD3MxOgiZBhWsHjetZH7aqqND4S495r7pnu0qwQW6JK1e6_rJGodnPl6oWM7nrLJ43O2STlkKyUyDf8AgcsFoGtOVFPw | US | html | 73.4 Kb | shared |
3948 | chrome.exe | GET | 200 | 2.20.10.114:80 | http://c.aaxads.com/aax.js?pub=AAX3221EY&hst=www.mediafire.com&ver=1.2 | unknown | text | 103 Kb | whitelisted |
3948 | chrome.exe | GET | 200 | 216.58.201.238:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 798 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3948 | chrome.exe | 216.58.198.196:443 | www.google.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 216.58.204.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 216.58.206.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.19.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 216.58.204.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.132.40:80 | r3---sn-5hne6nsk.gvt1.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 216.58.204.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.22.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 216.58.204.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.18.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
mediafire.zendesk.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3948 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
Image2Gd.exe | QMetaObject::connectSlotsByName: No matching signal for on_fpsSpinBox_valueChanged(int)
|
Image2Gd.exe | QMetaObject::connectSlotsByName: No matching signal for on_fpsSpinBox_valueChanged(int)
|