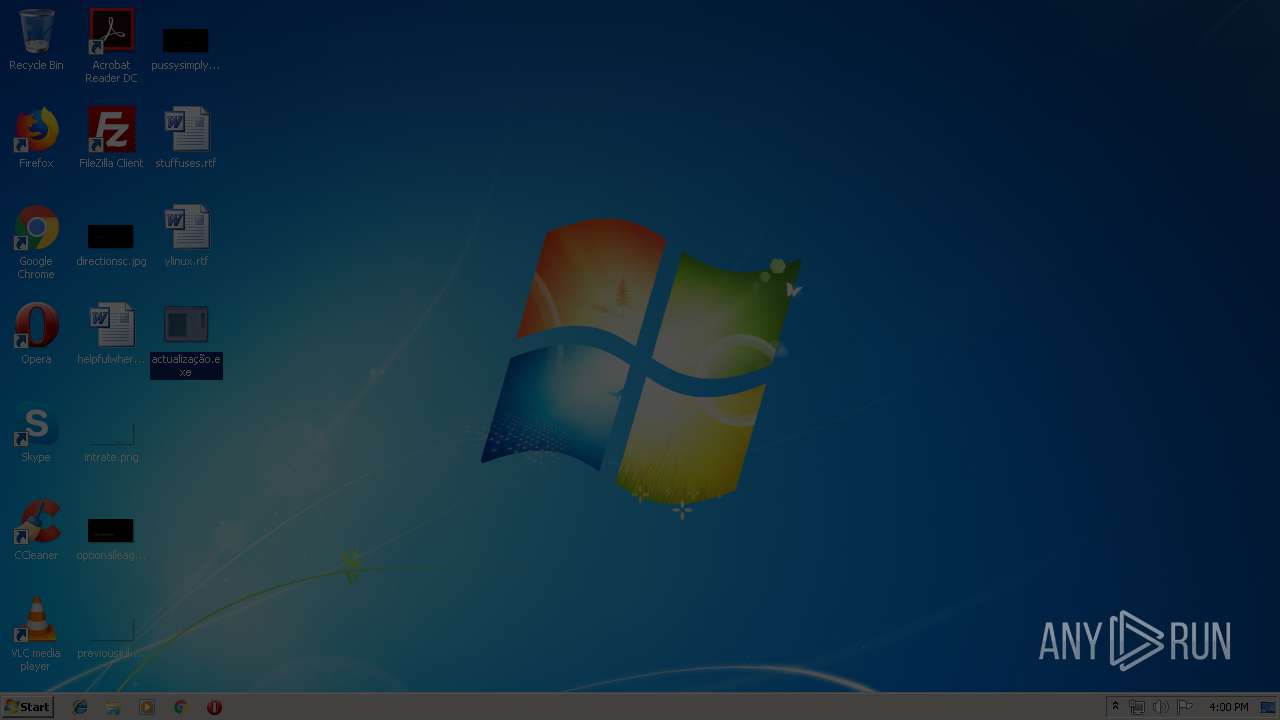
| File name: | actualização.exe |
| Full analysis: | https://app.any.run/tasks/04e39207-e4c4-473a-851f-d2e31fca7a48 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | April 25, 2019, 14:59:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2BB1EACAA0AA4865A3D538D8876312EA |
| SHA1: | FCE185DD2AFAD573E62974D33207CBBD60FD7A32 |
| SHA256: | 76BFEA449A7F6E9E19CE36D147F287A7CAC650639DFC3CE9DA6304CF0369168A |
| SSDEEP: | 384:gl+ieB2NzuHs9/l/I4UlGuUjLrazDY59UTW/fiWutqD8CzYcHeUZv:g6INiU/l//qGuUXqTKHutqDJzYcHeUZ |
MALICIOUS
Downloads executable files from IP
- actualização.exe (PID: 2156)
- actualização.exe (PID: 1740)
- actualização.exe (PID: 3900)
Downloads executable files from the Internet
- actualização.exe (PID: 3900)
- actualização.exe (PID: 1740)
- actualização.exe (PID: 2156)
SUSPICIOUS
Executable content was dropped or overwritten
- actualização.exe (PID: 3900)
- actualização.exe (PID: 1740)
- actualização.exe (PID: 2156)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:28 04:32:24+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 15872 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5de2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | down |
| FileVersion: | 1.0.0.0 |
| InternalName: | down.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | down.exe |
| ProductName: | down |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Feb-2019 03:32:24 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | down |
| FileVersion: | 1.0.0.0 |
| InternalName: | down.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | down.exe |
| ProductName: | down |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 28-Feb-2019 03:32:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00003DE8 | 0x00003E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.5872 |
.rsrc | 0x00006000 | 0x00000EC4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.85342 |
.reloc | 0x00008000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04224 | 2850 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
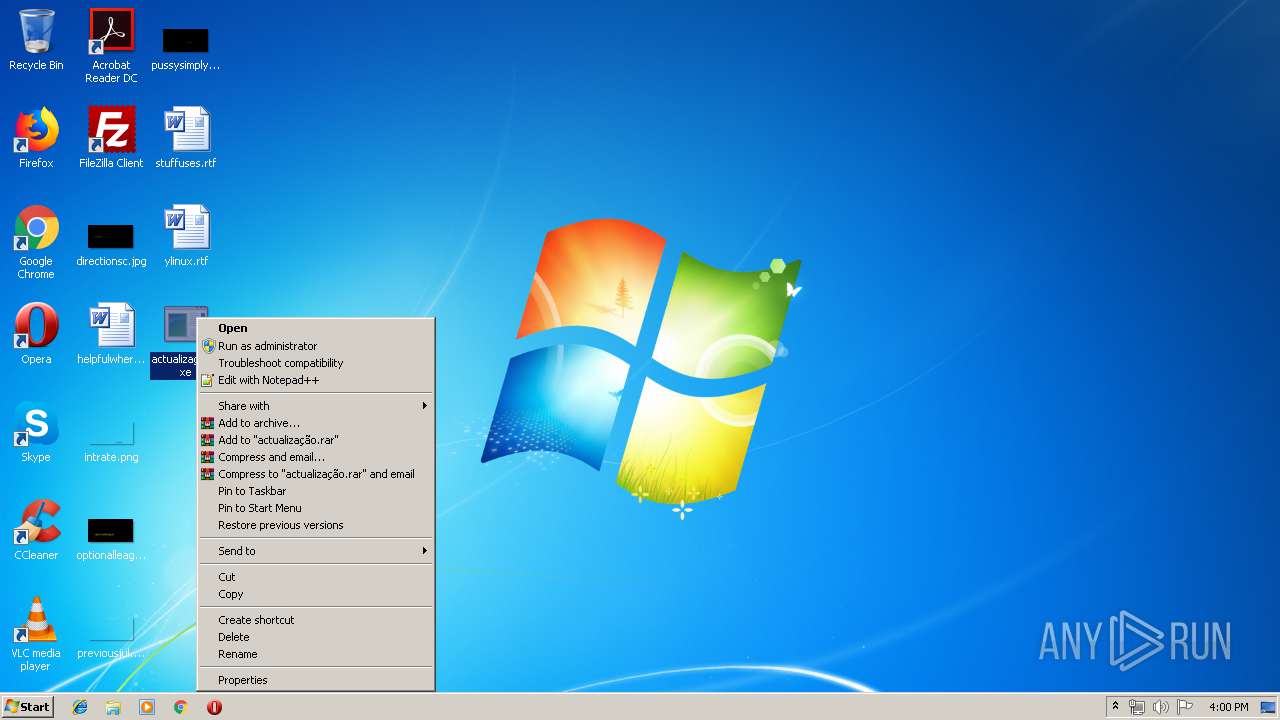
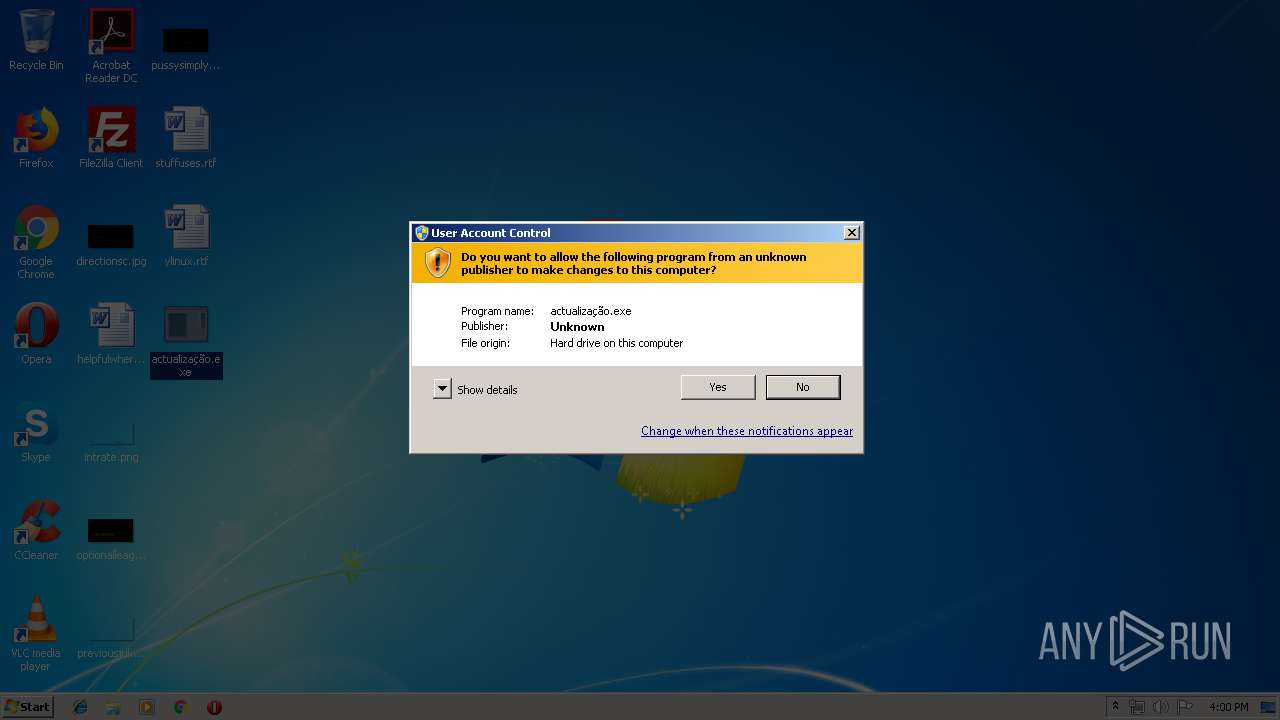
| 1740 | "C:\Users\admin\Desktop\actualização.exe" | C:\Users\admin\Desktop\actualização.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: down Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\Desktop\actualização.exe" | C:\Users\admin\Desktop\actualização.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: down Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3900 | "C:\Users\admin\Desktop\actualização.exe" | C:\Users\admin\Desktop\actualização.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: down Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
84
Read events
72
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2156) actualização.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\actualização_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
10
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1740 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\vshost.exe | executable | |
MD5:— | SHA256:— | |||
| 2156 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\vshost.exe | executable | |
MD5:— | SHA256:— | |||
| 2156 | actualização.exe | C:\Users\admin\AppData\Local\Temp\explorer32.exe | executable | |
MD5:— | SHA256:— | |||
| 3900 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\vshost.exe | executable | |
MD5:— | SHA256:— | |||
| 3900 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\install.bat | text | |
MD5:— | SHA256:— | |||
| 1740 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\explorer32.exe | executable | |
MD5:— | SHA256:— | |||
| 1740 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\install.bat | text | |
MD5:— | SHA256:— | |||
| 3900 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\explorer32.exe | executable | |
MD5:— | SHA256:— | |||
| 2156 | actualização.exe | C:\Users\admin\AppData\Local\Temp\update2804\install.bat | text | |
MD5:— | SHA256:— | |||
| 2156 | actualização.exe | C:\Users\admin\AppData\Local\Temp\vshost.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
3
DNS requests
0
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2156 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/explorer32.exe | CA | executable | 35.5 Kb | suspicious |
2156 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/vshost.exe | CA | executable | 53.0 Kb | suspicious |
3900 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/vshost.exe | CA | executable | 53.0 Kb | suspicious |
3900 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/install.bat | CA | text | 425 b | suspicious |
2156 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/install.bat | CA | text | 425 b | suspicious |
3900 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/explorer32.exe | CA | executable | 35.5 Kb | suspicious |
1740 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/vshost.exe | CA | executable | 53.0 Kb | suspicious |
1740 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/explorer32.exe | CA | executable | 35.5 Kb | suspicious |
1740 | actualização.exe | GET | 200 | 192.99.215.95:80 | http://192.99.215.95/uploads/Ciclope/install.bat | CA | text | 425 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2156 | actualização.exe | 192.99.215.95:80 | — | OVH SAS | CA | suspicious |
3900 | actualização.exe | 192.99.215.95:80 | — | OVH SAS | CA | suspicious |
1740 | actualização.exe | 192.99.215.95:80 | — | OVH SAS | CA | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2156 | actualização.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2156 | actualização.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2156 | actualização.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2156 | actualização.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2156 | actualização.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2156 | actualização.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2156 | actualização.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3900 | actualização.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3900 | actualização.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3900 | actualização.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |