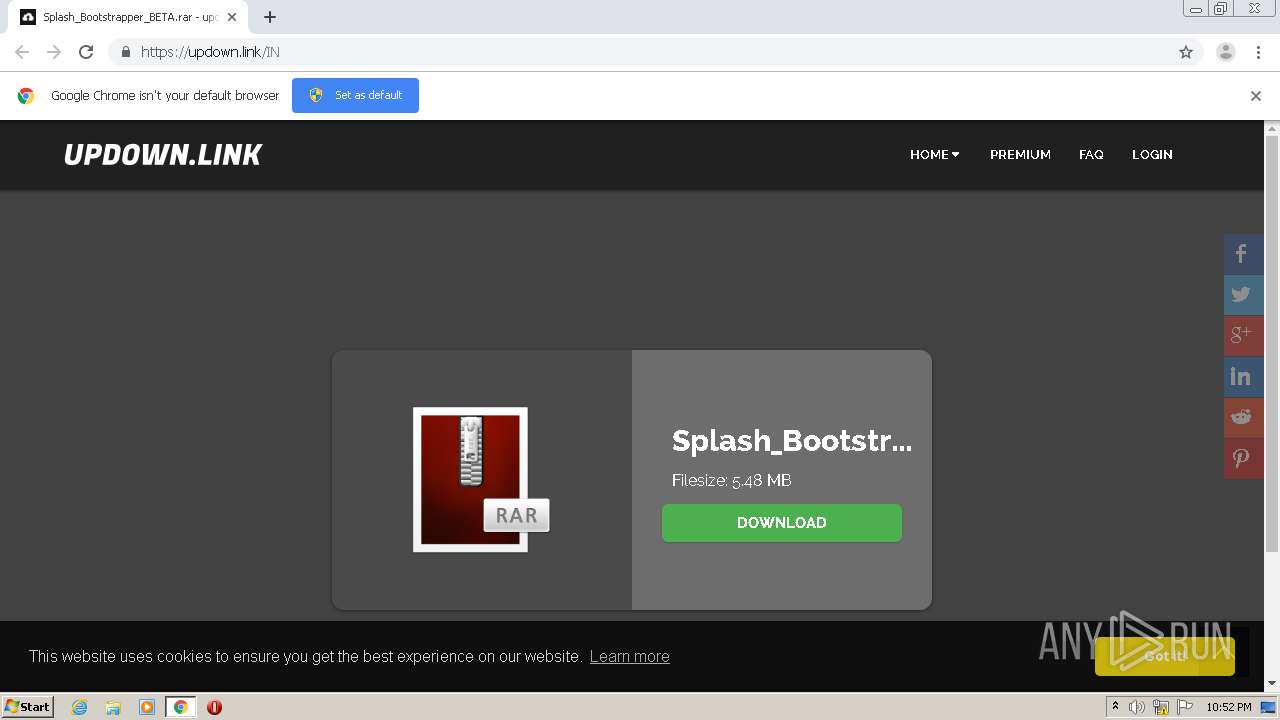
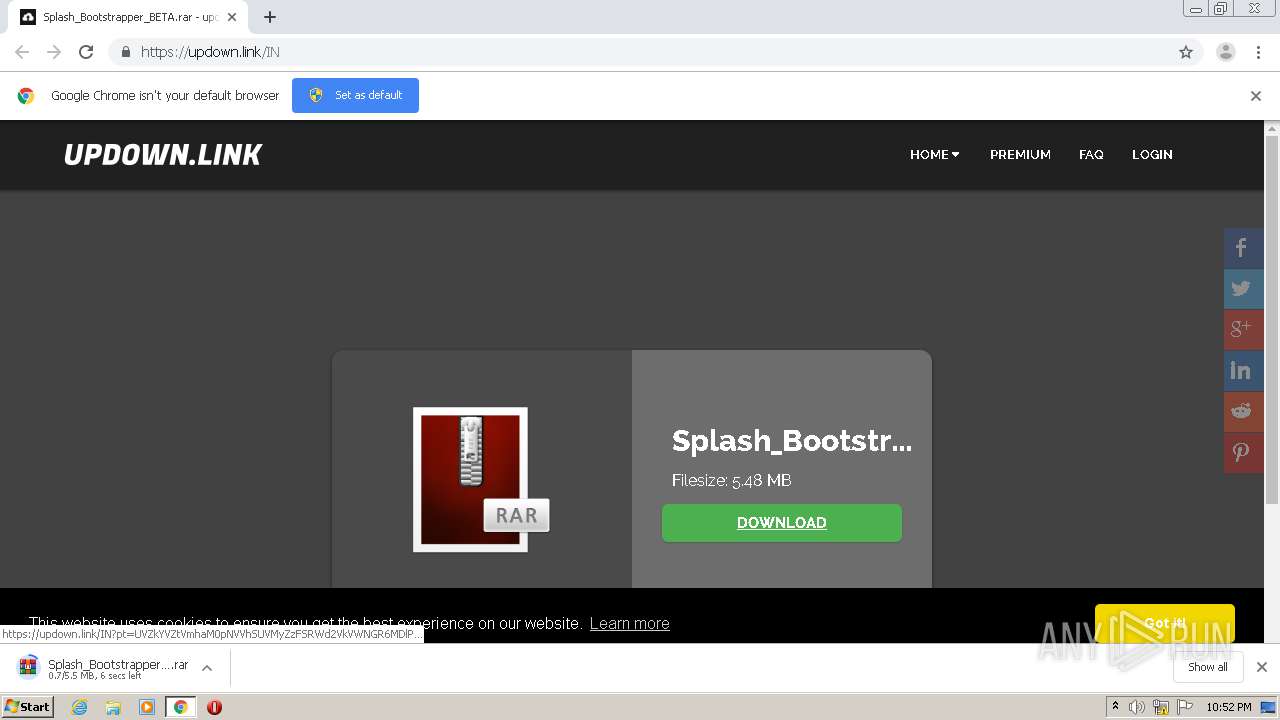
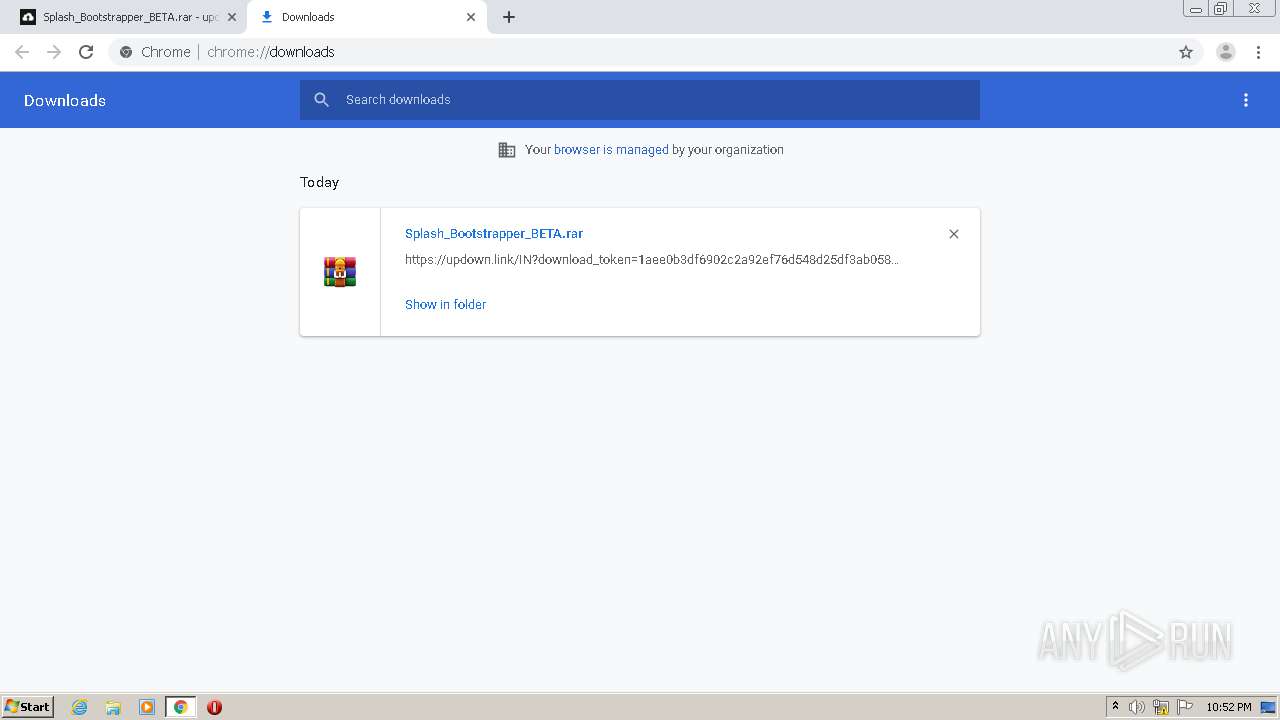
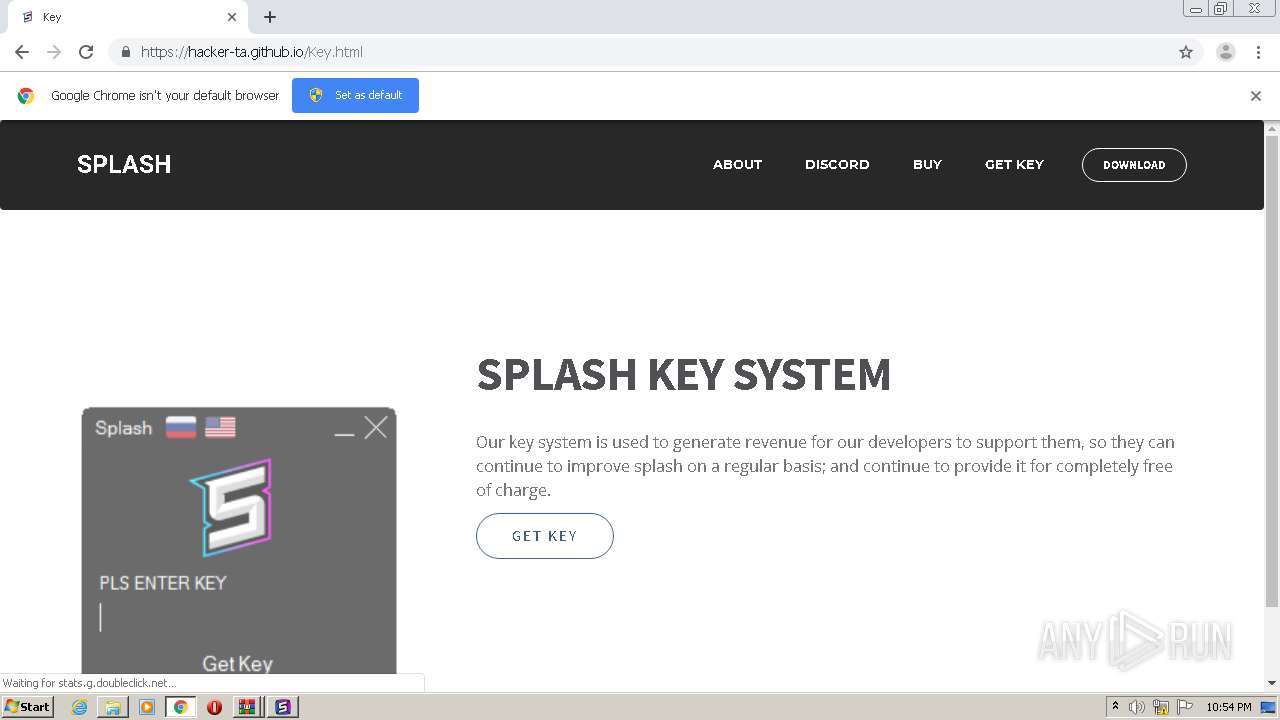
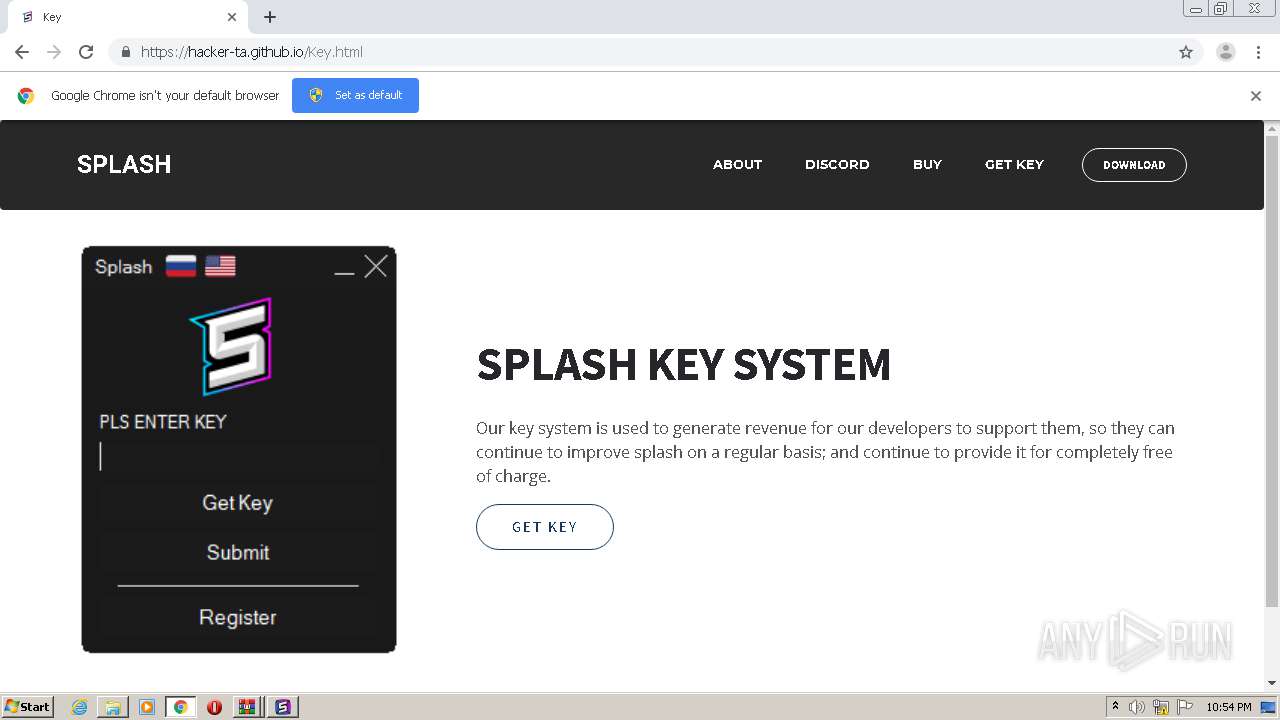
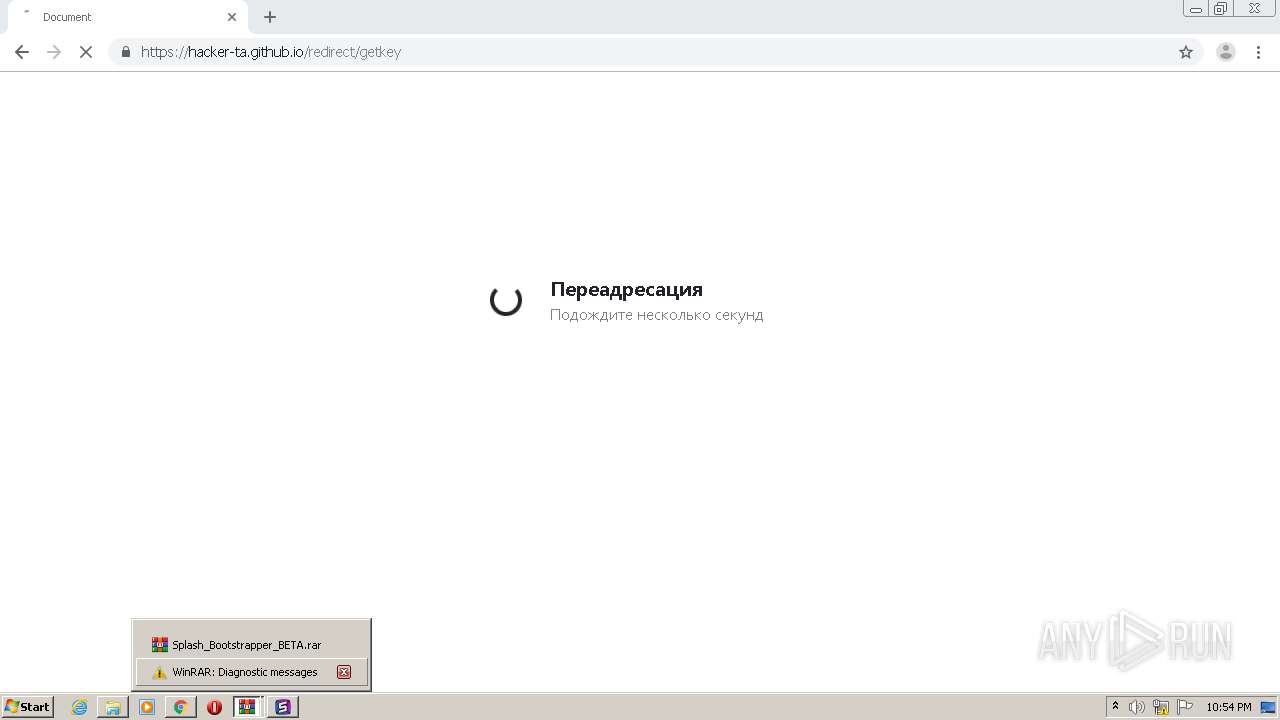
| URL: | https://updown.link/IN |
| Full analysis: | https://app.any.run/tasks/65a295af-9a17-49b4-9a5b-0bc70232cb0e |
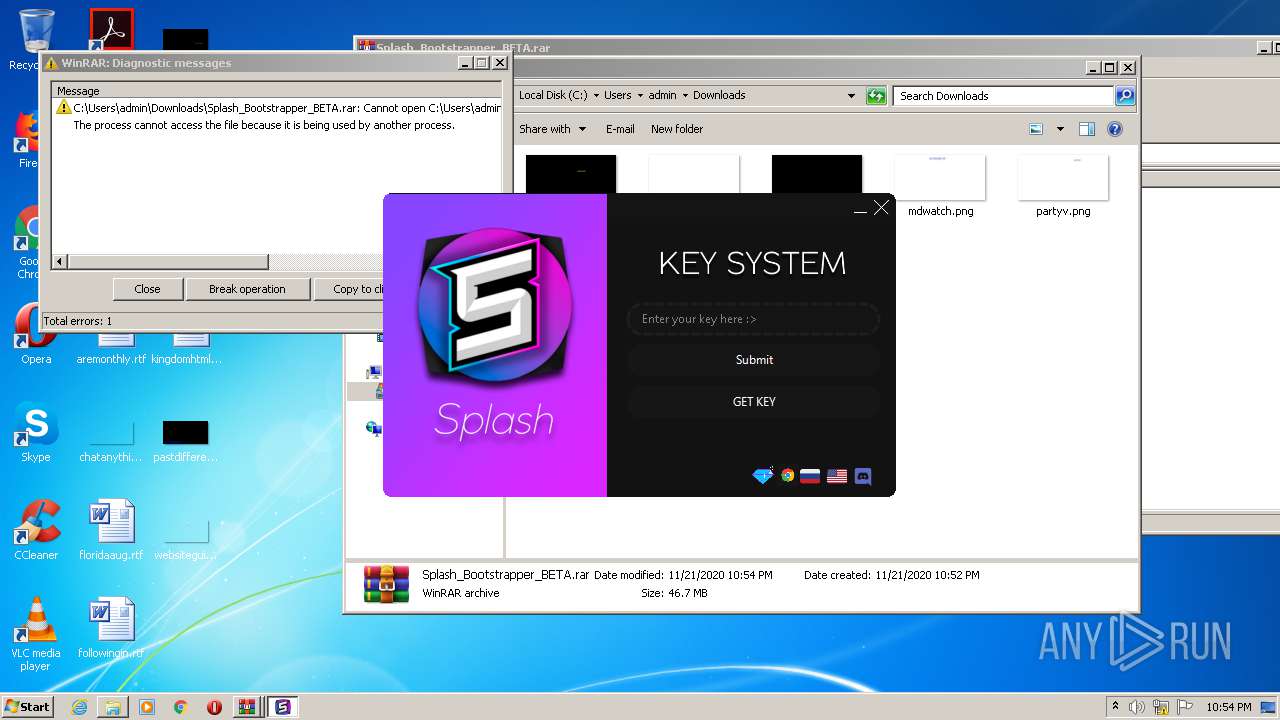
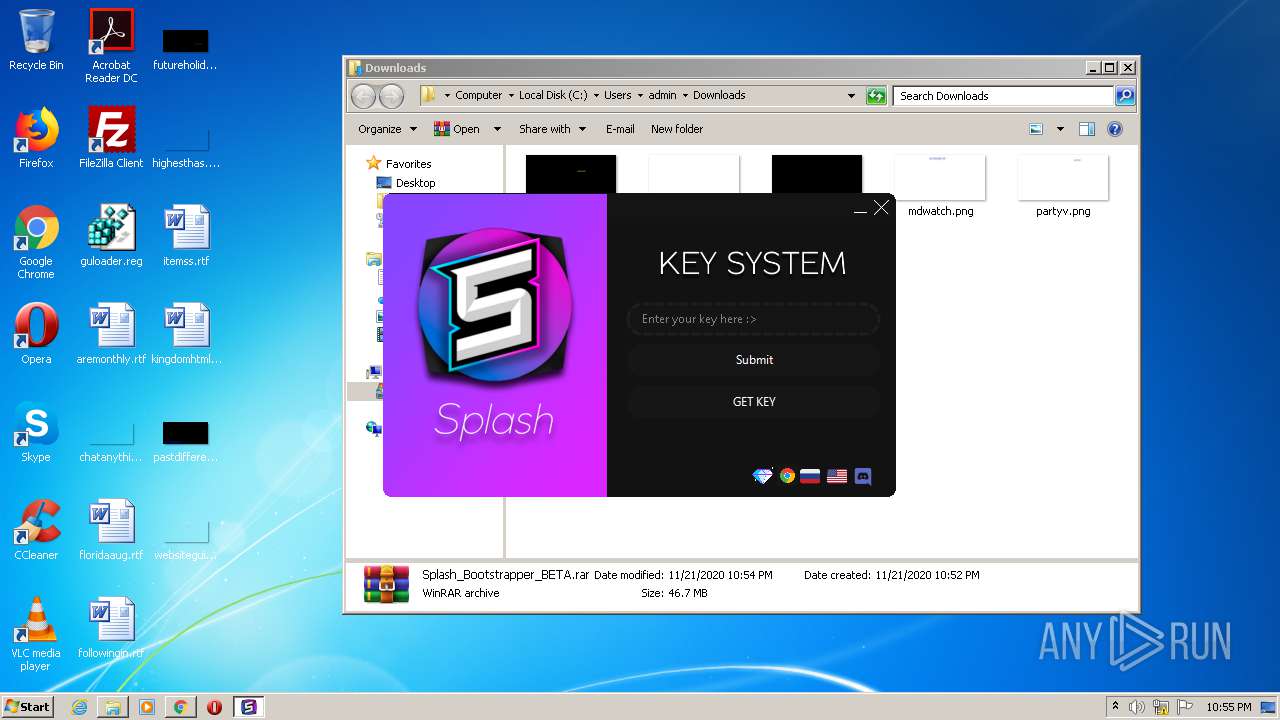
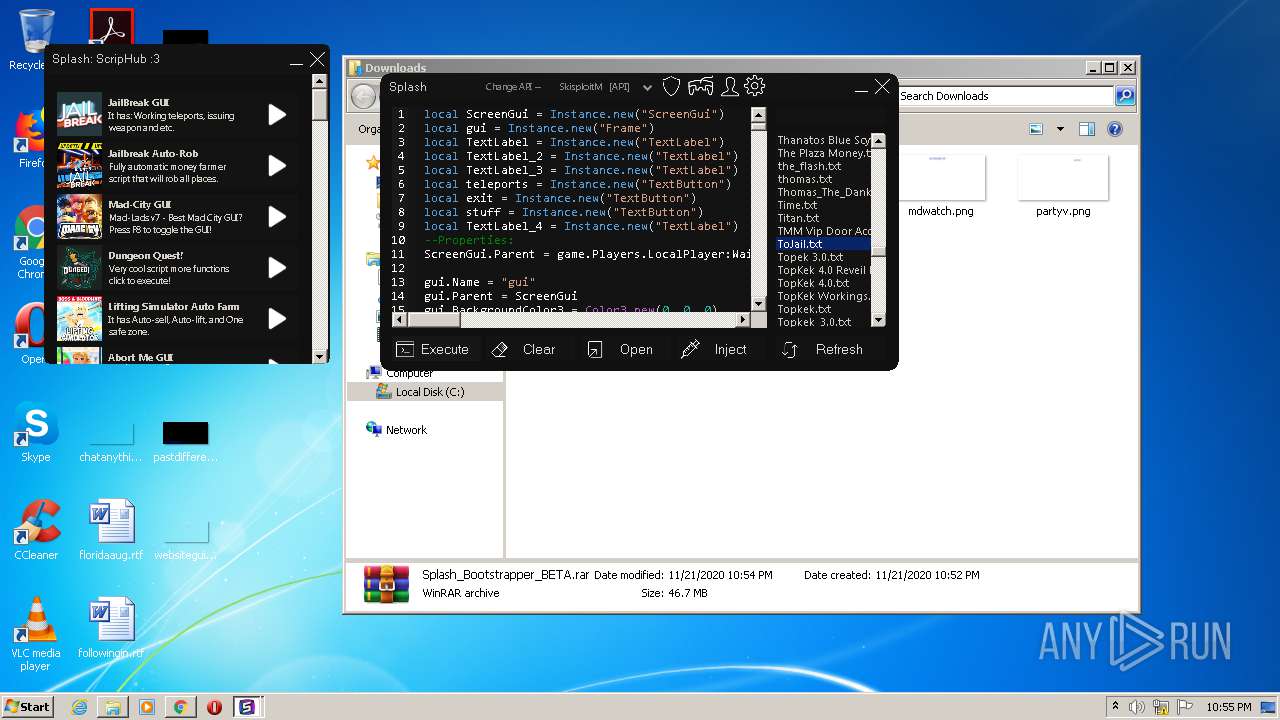
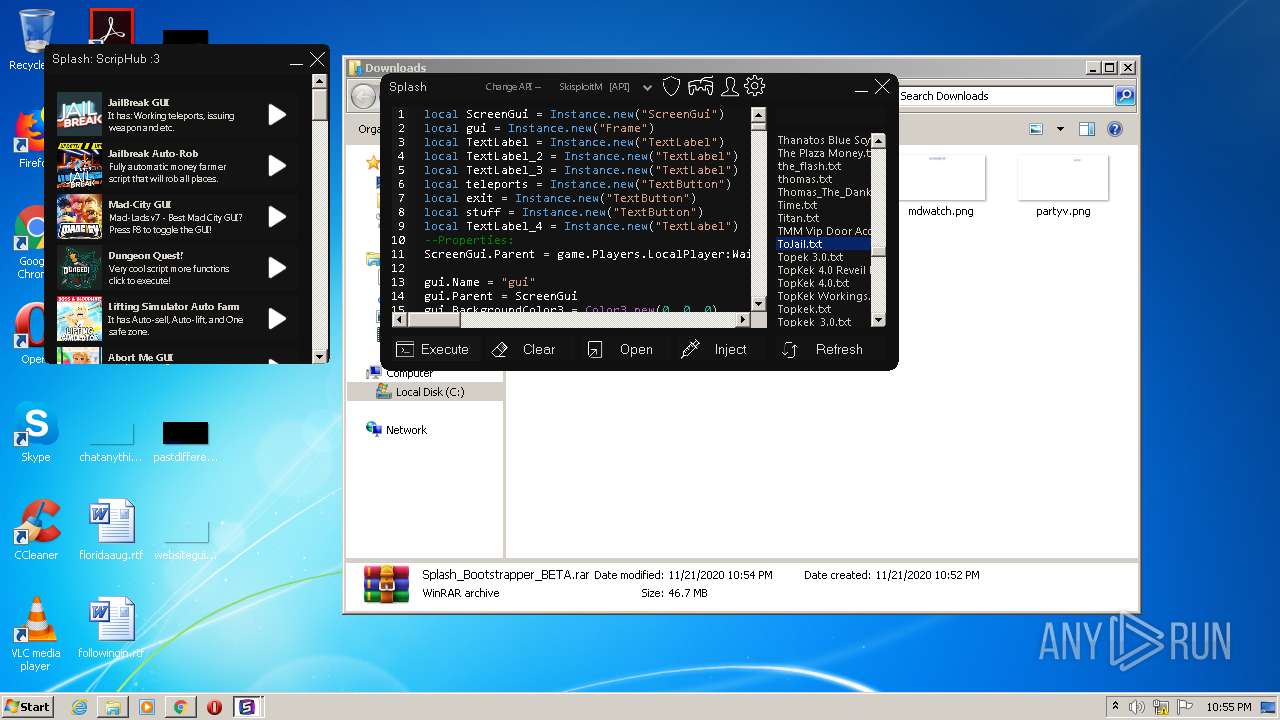
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2020, 22:52:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FE141922476925063DE5C90FD7607406 |
| SHA1: | 7836DAB48556BA1D87241B605B8DB6ECDBC0CD19 |
| SHA256: | 76AEAA895BCBD2E6ED89798BBB4B1169236751DA38EA9C1A55E821CB9331B98C |
| SSDEEP: | 3:N8hGC6Ksr:2hGzKK |
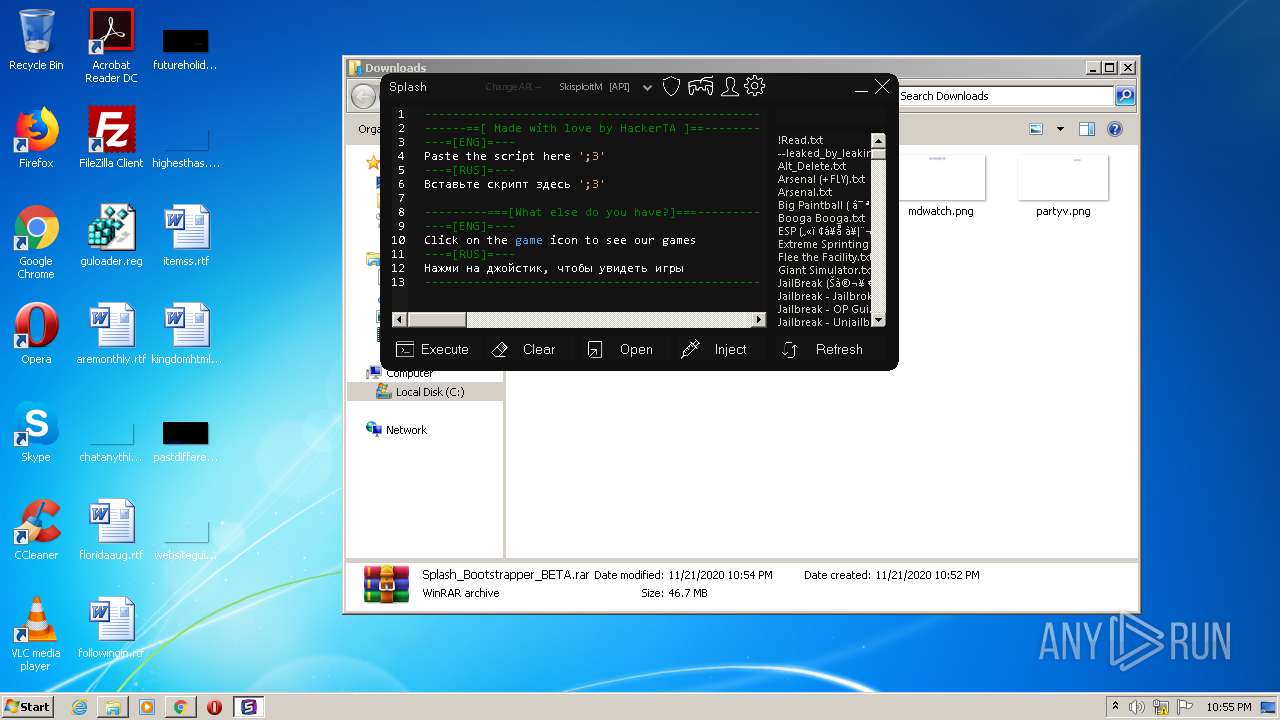
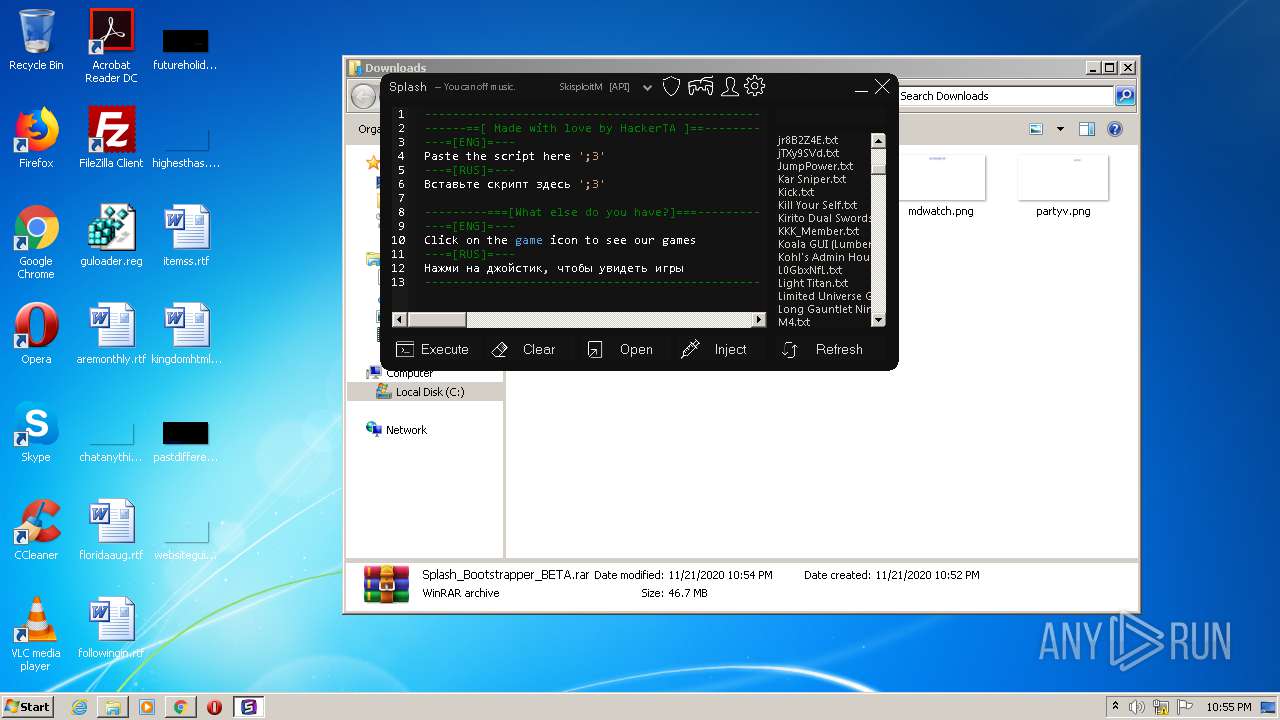
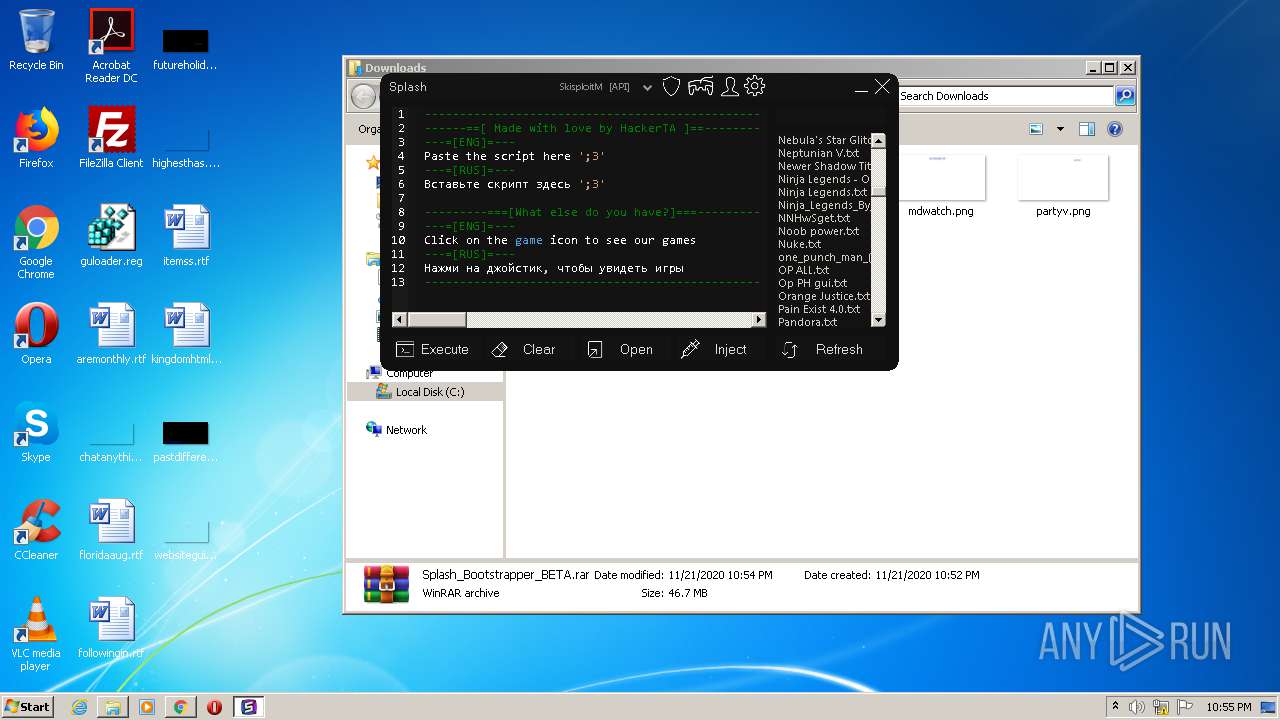
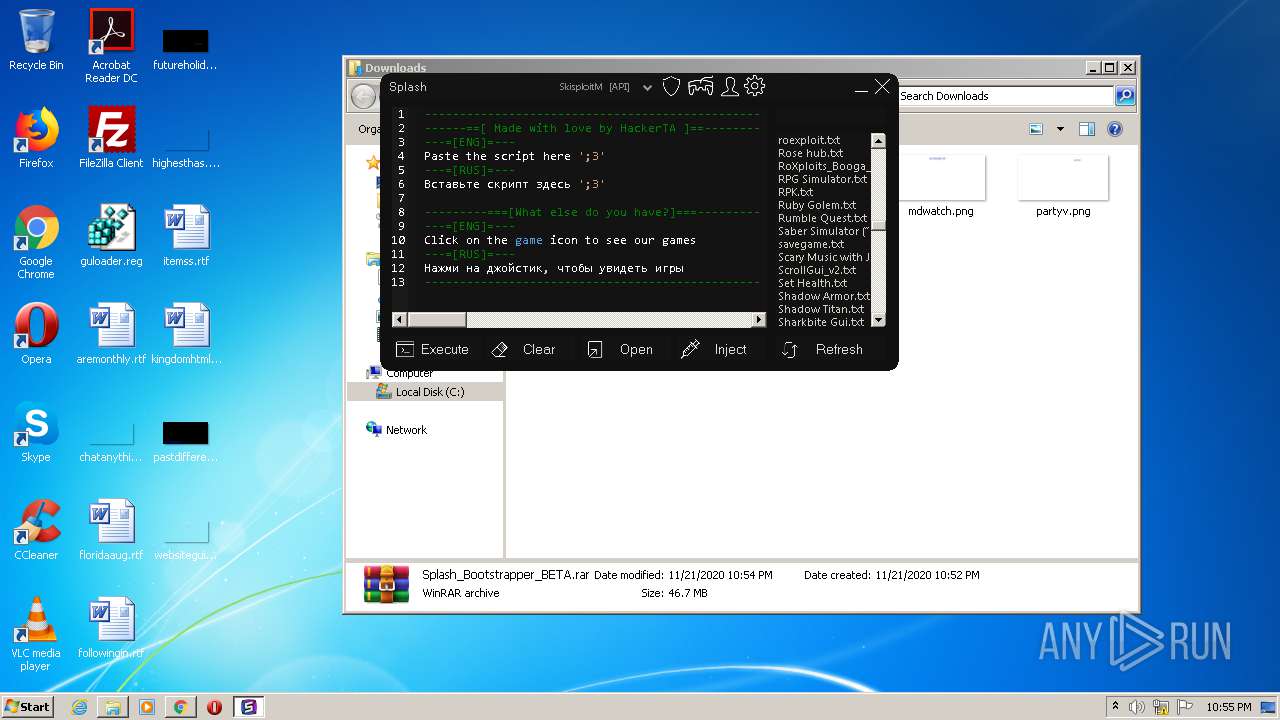
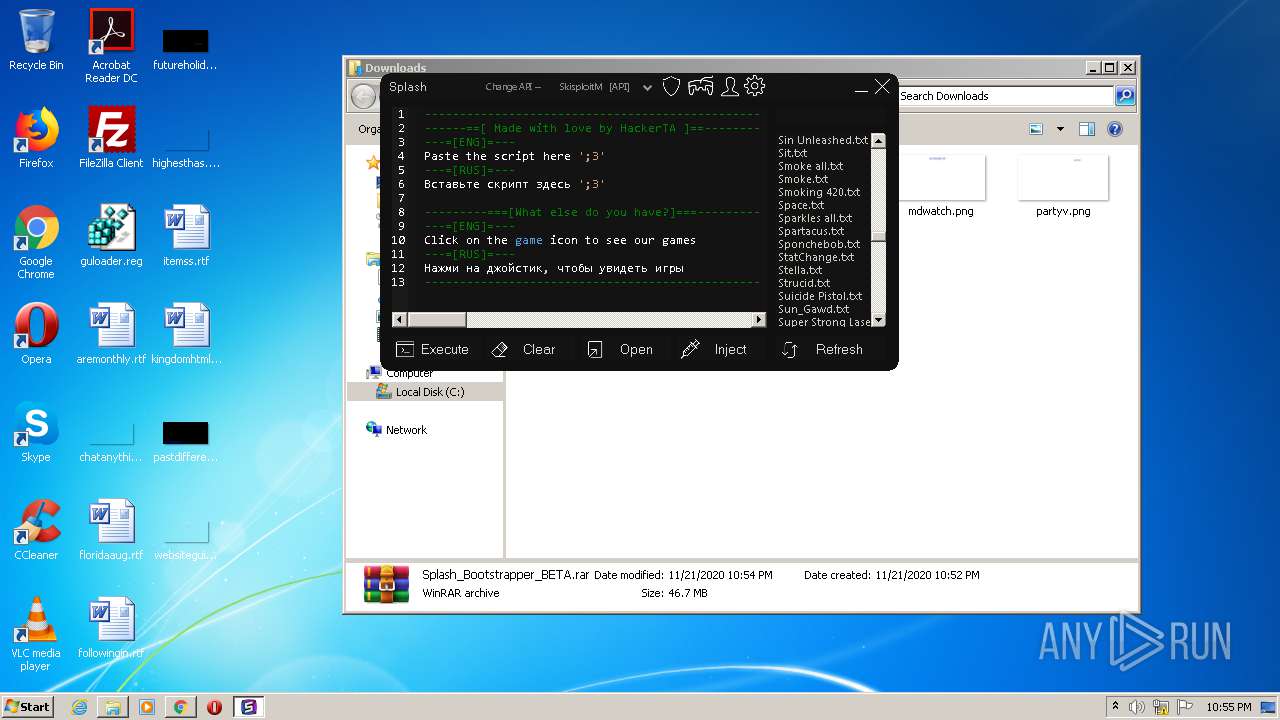
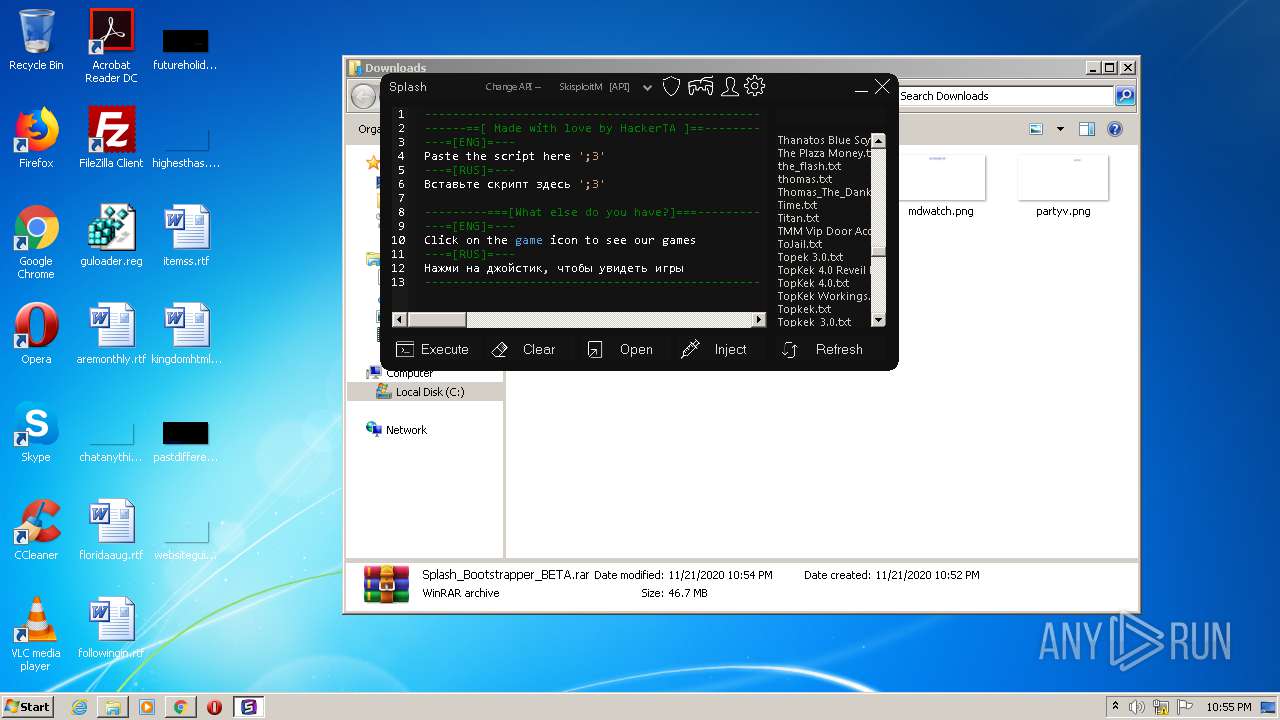
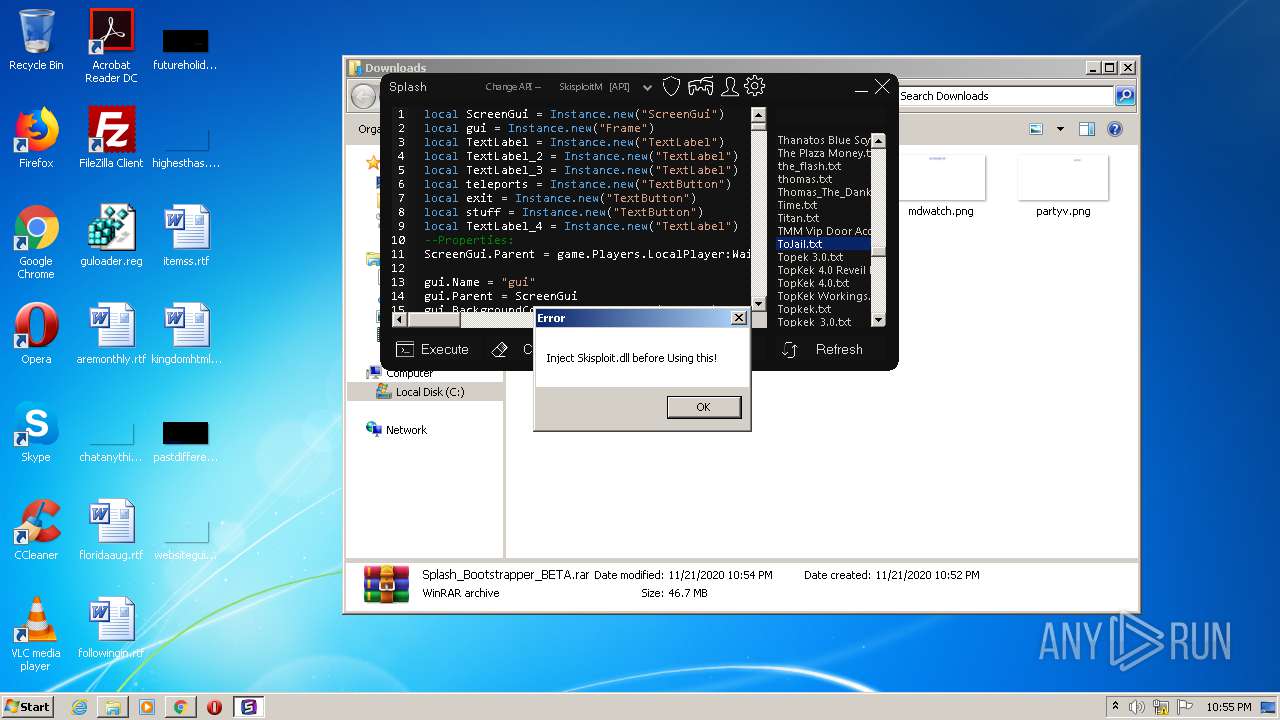
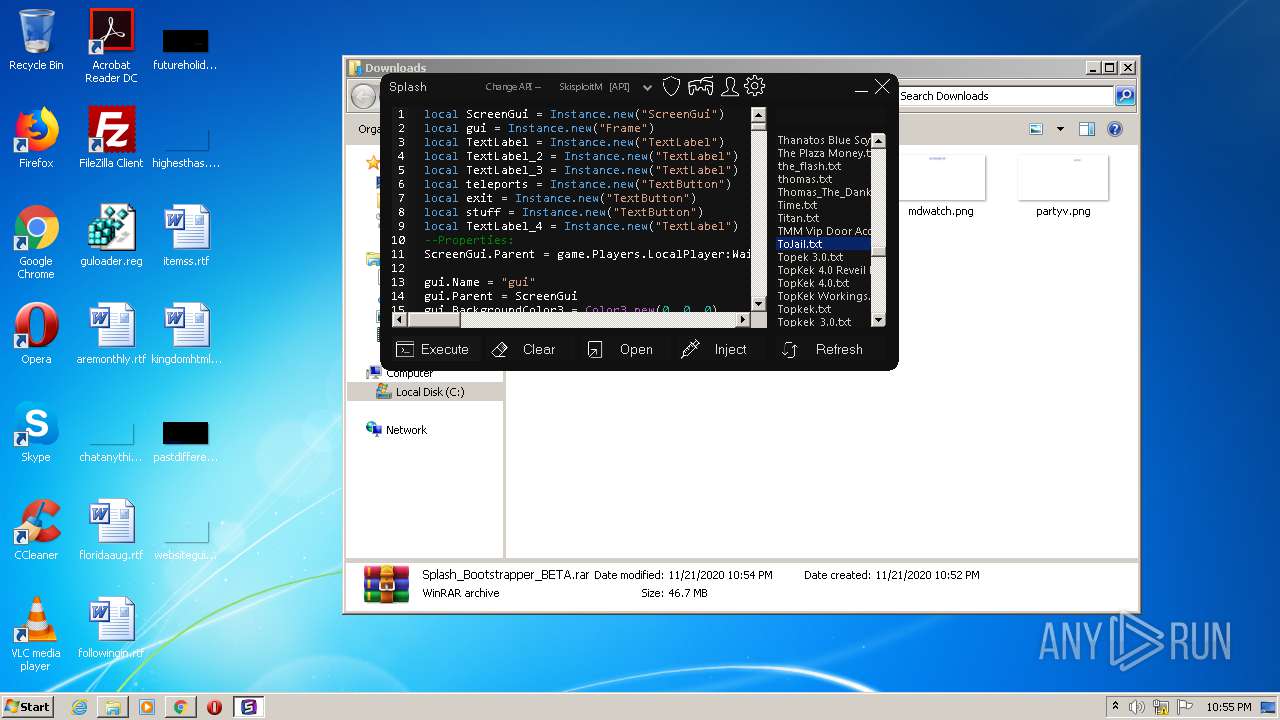
MALICIOUS
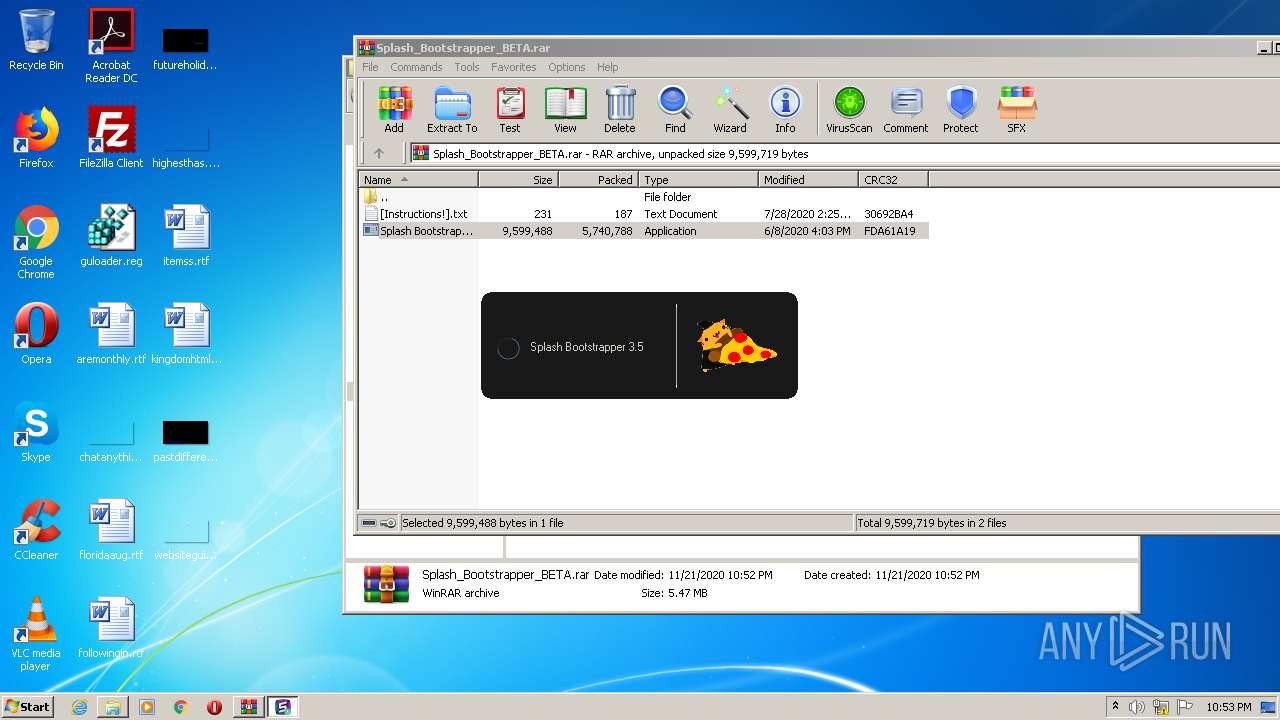
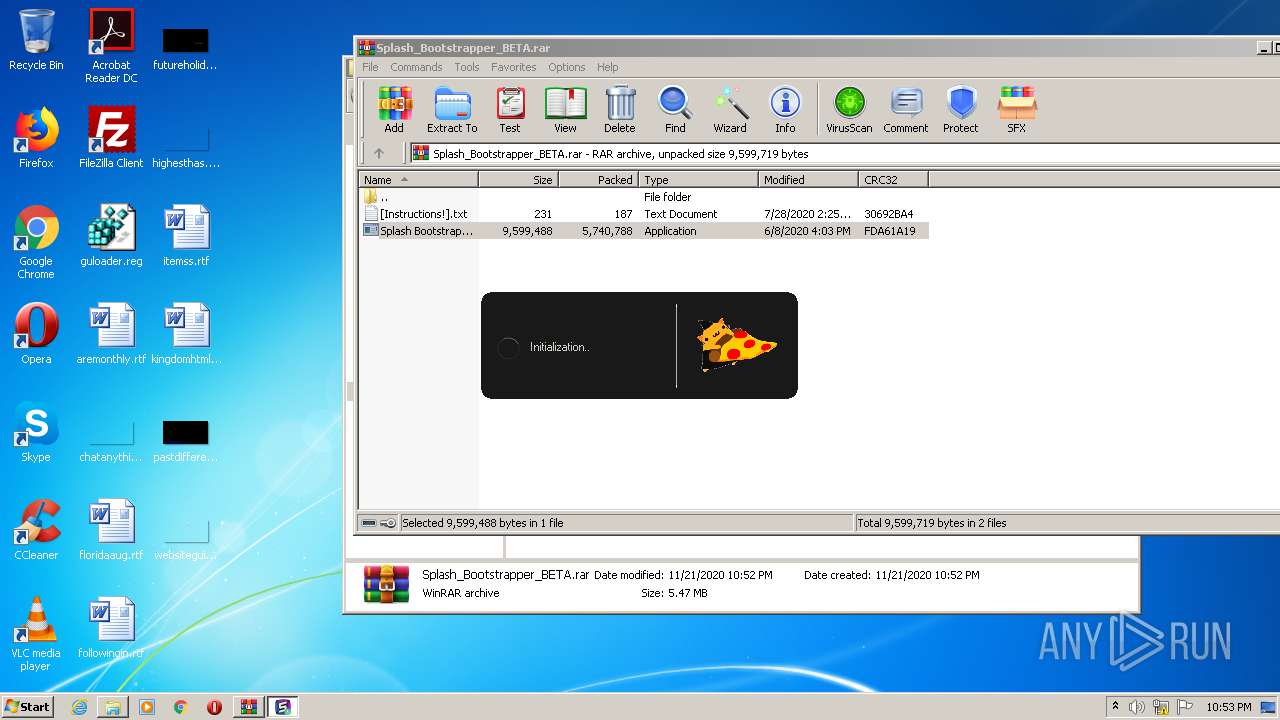
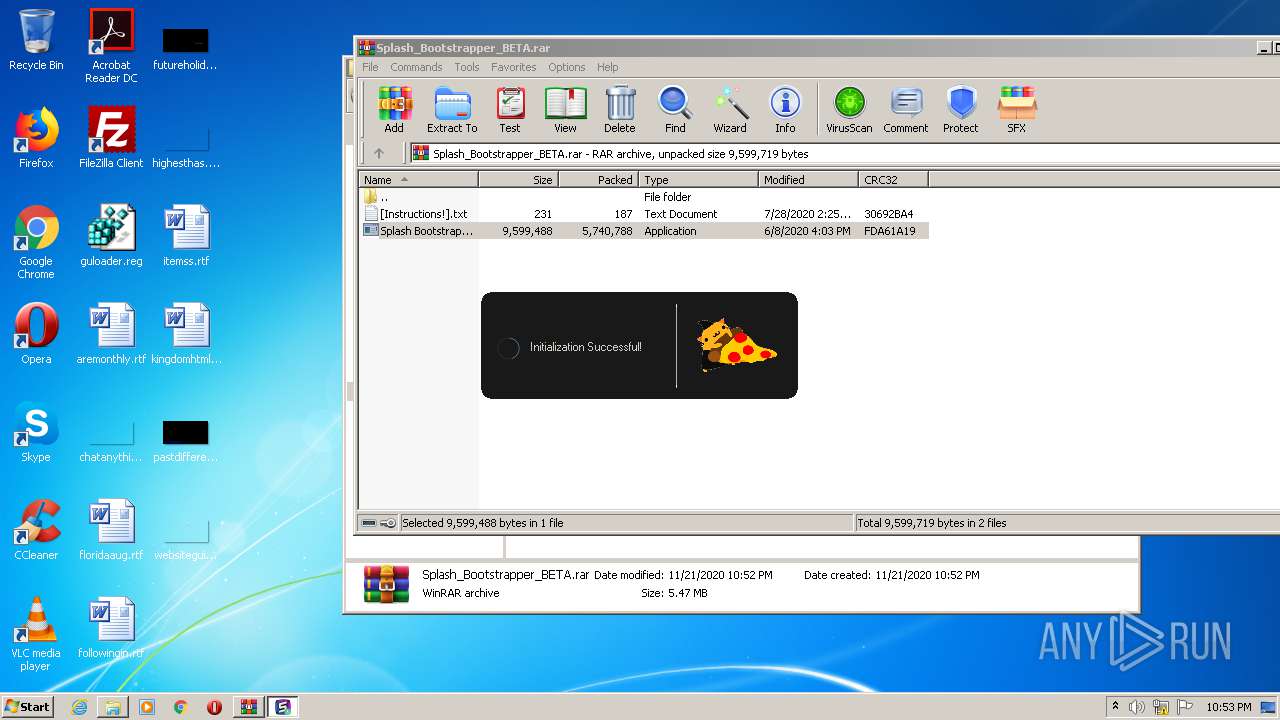
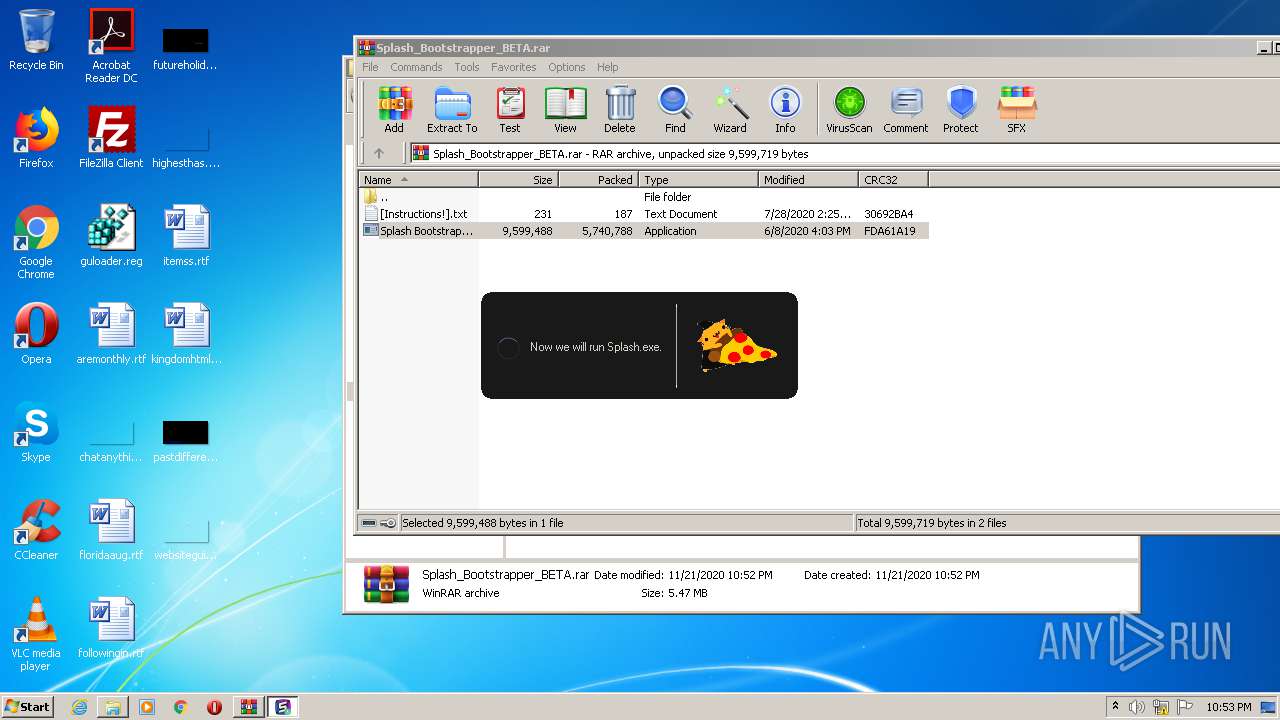
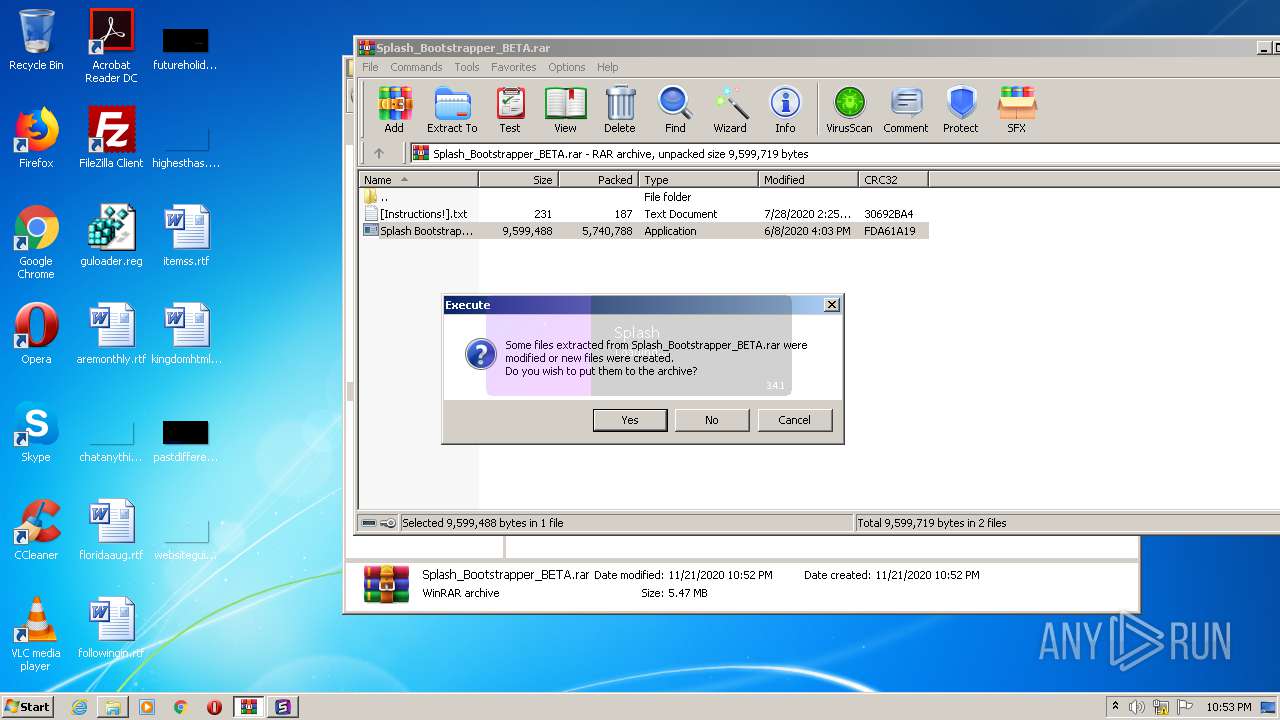
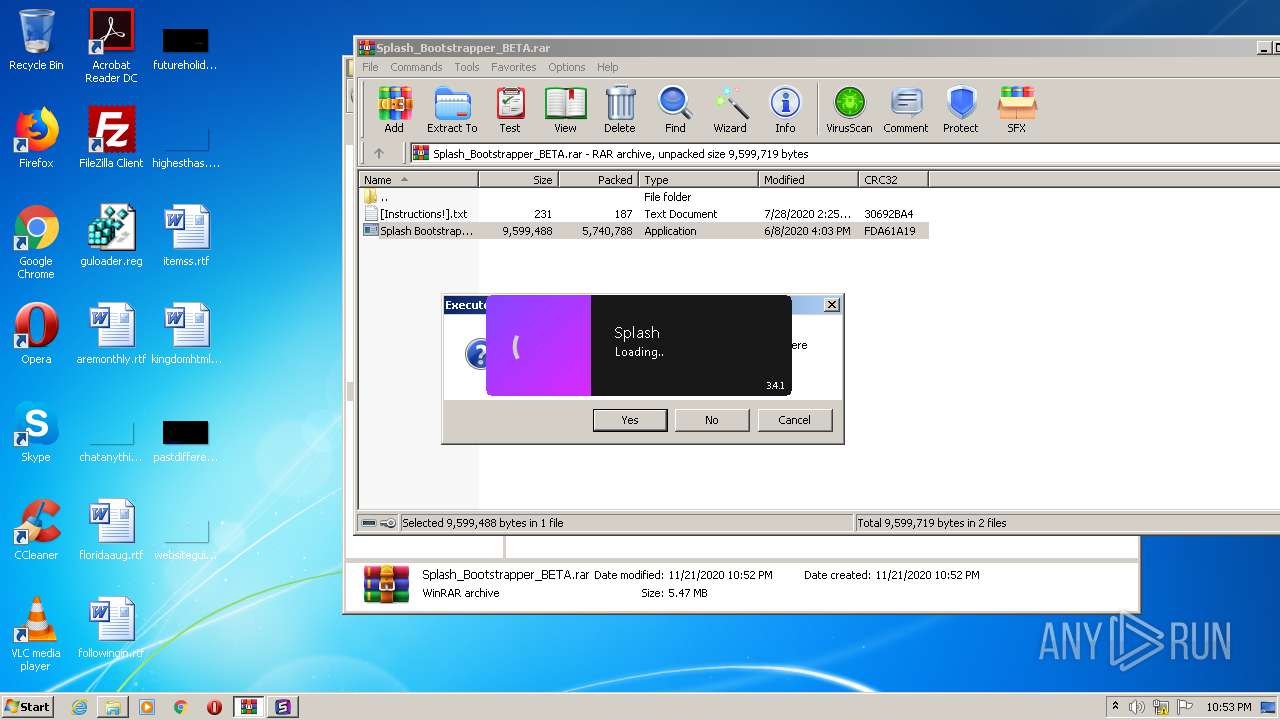
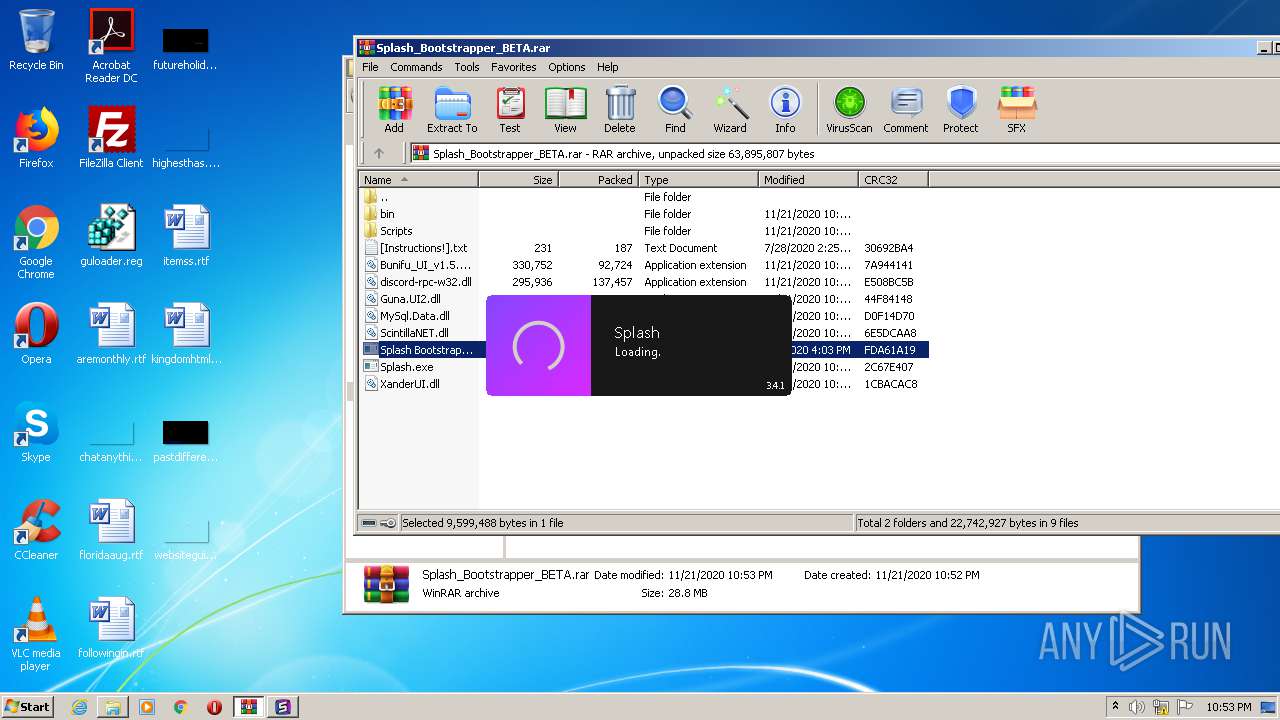
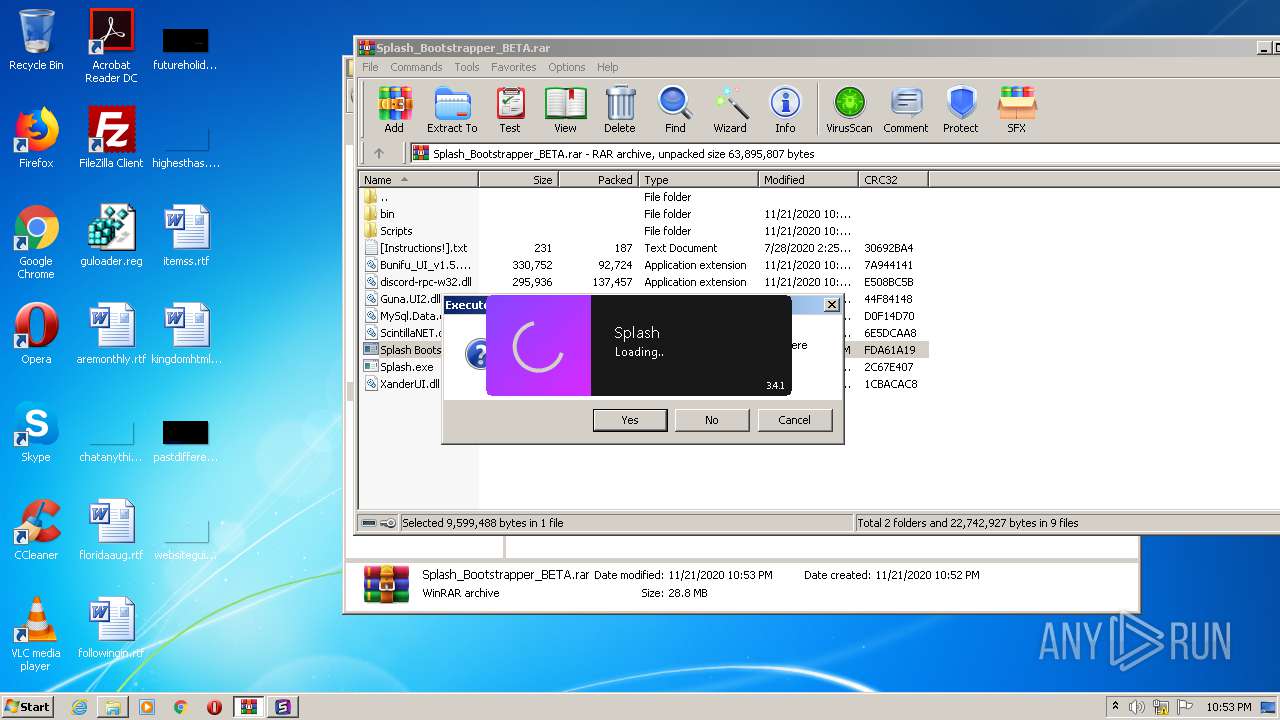
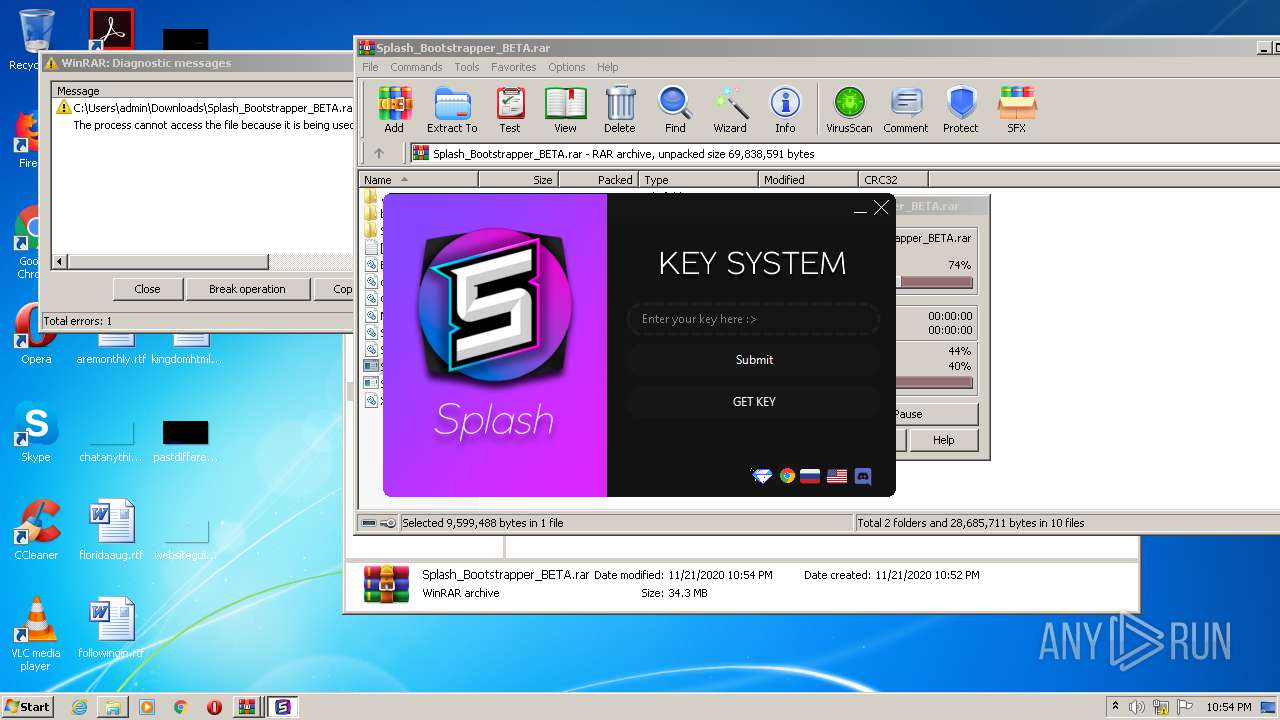
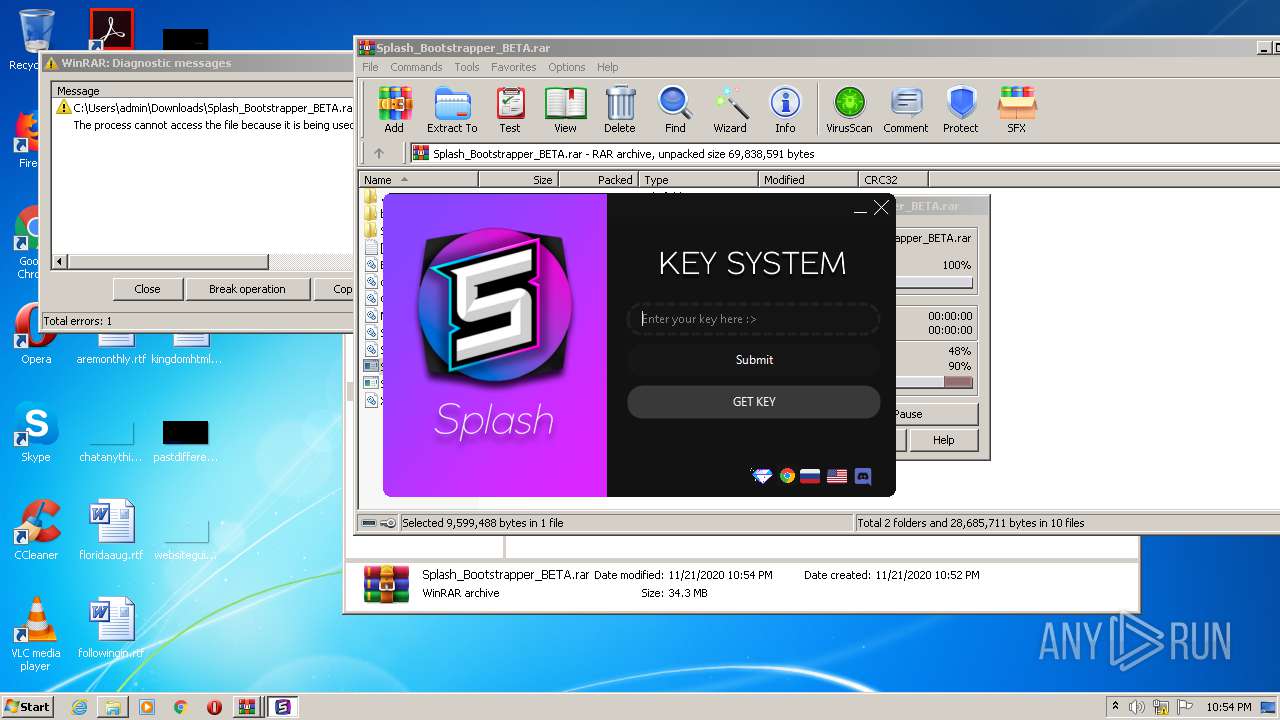
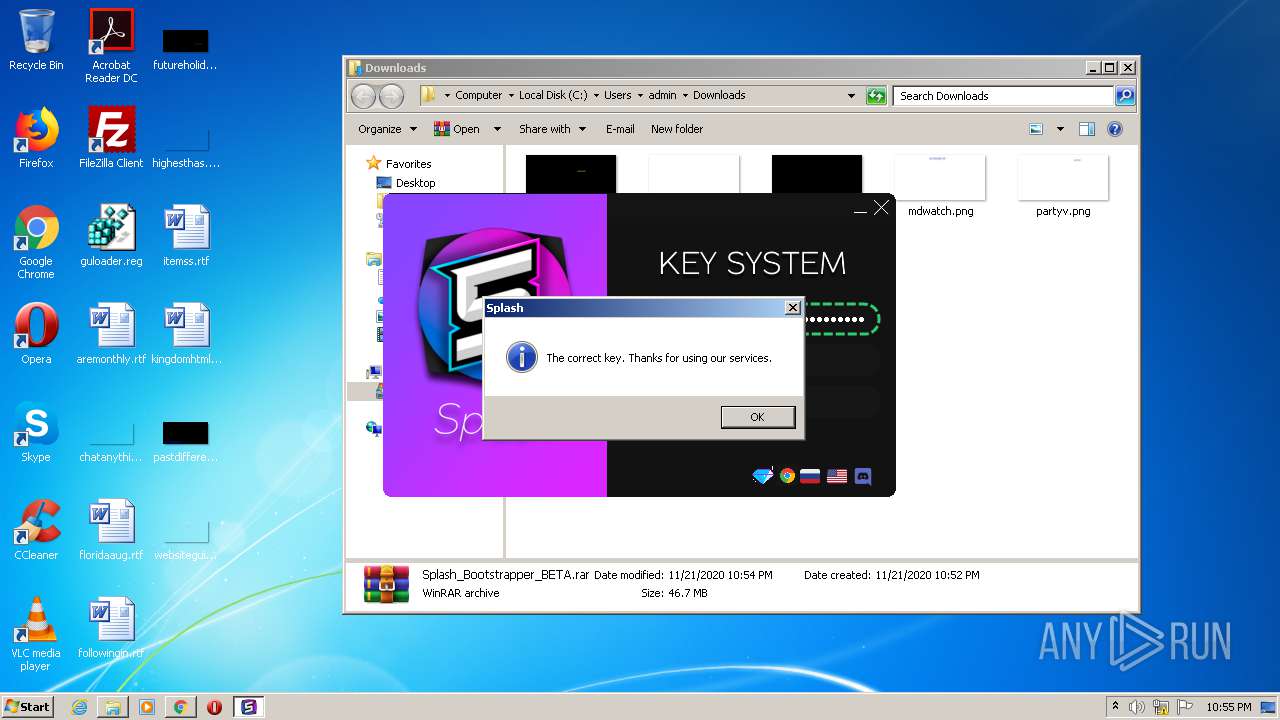
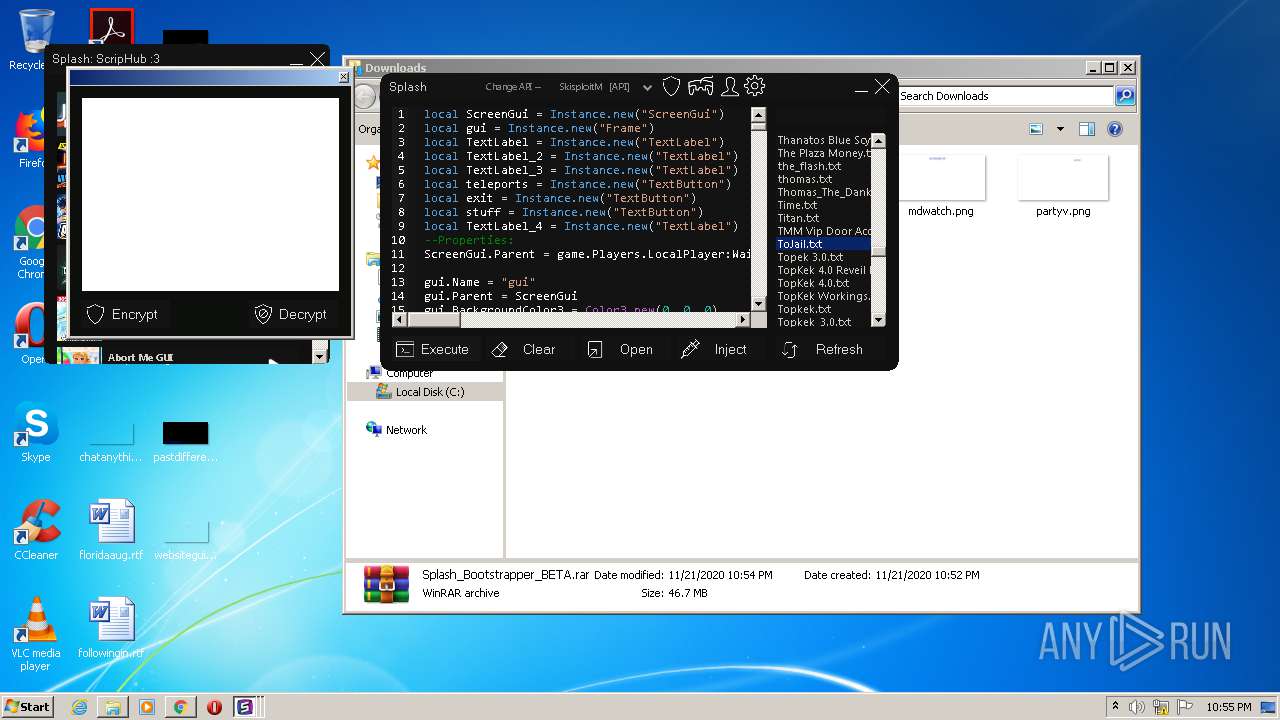
Application was dropped or rewritten from another process
- Splash.exe (PID: 972)
- Splash Bootstrapper.exe (PID: 2540)
Loads dropped or rewritten executable
- Splash.exe (PID: 972)
SUSPICIOUS
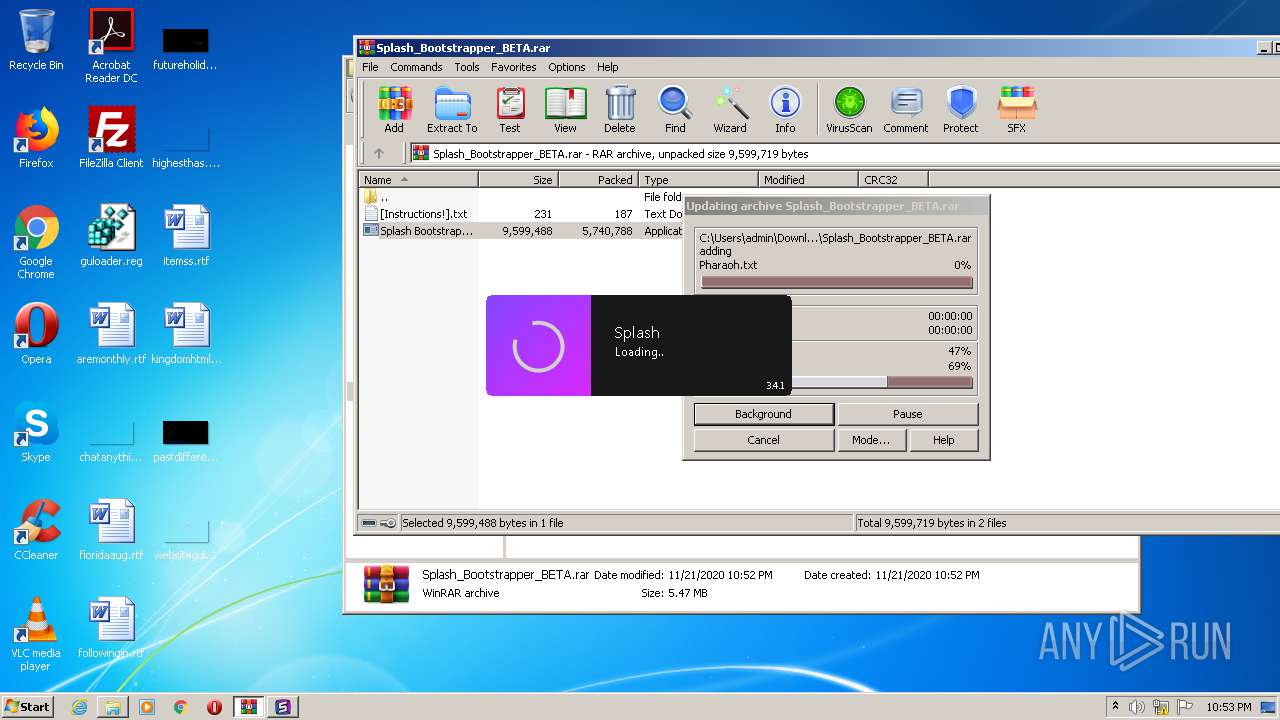
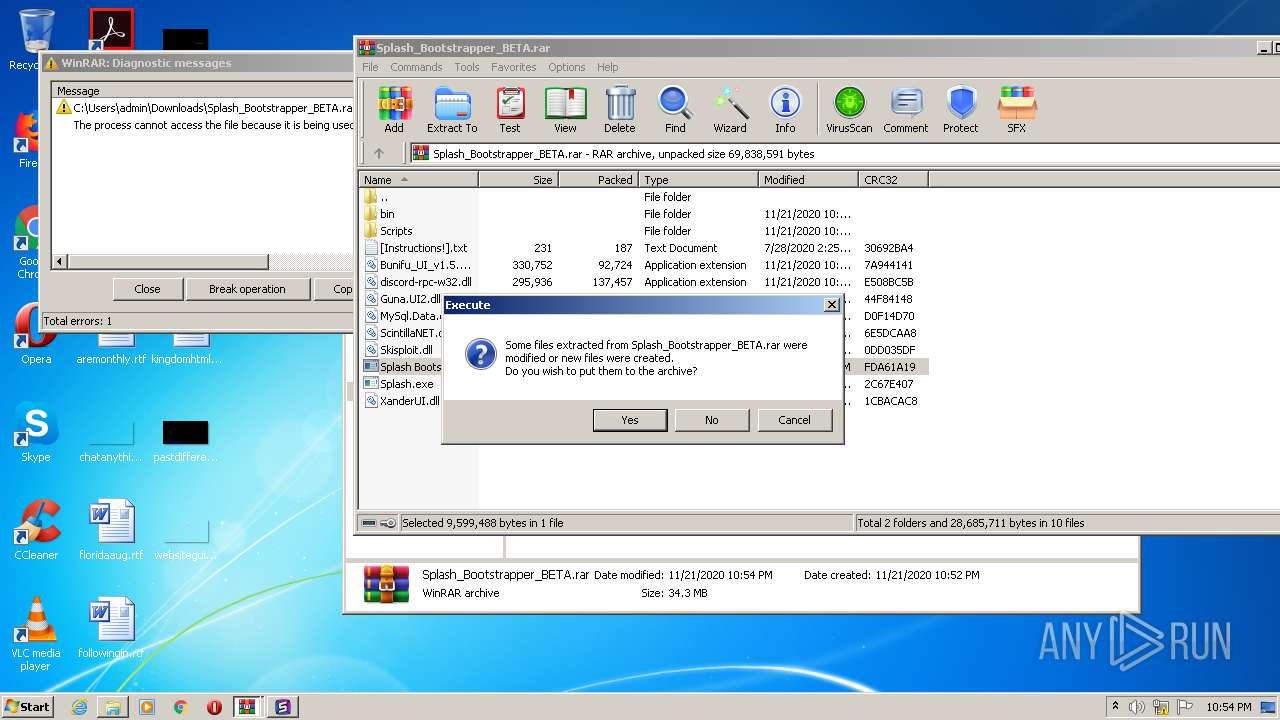
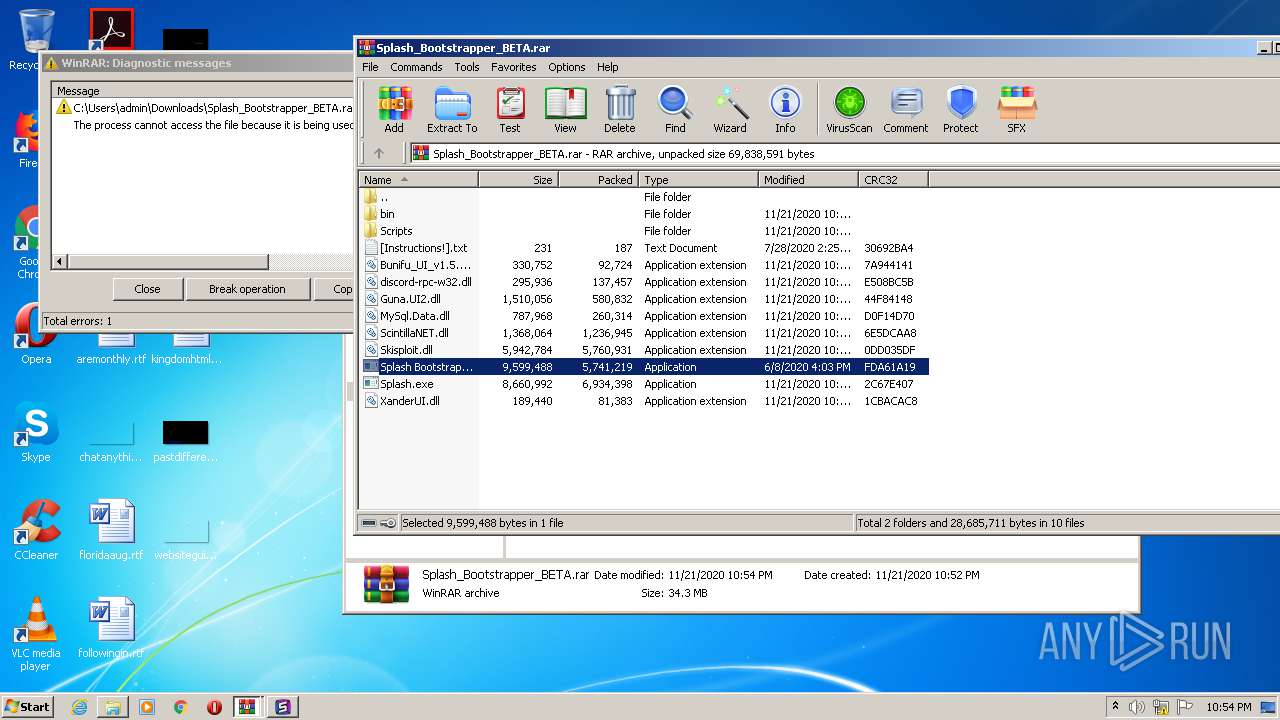
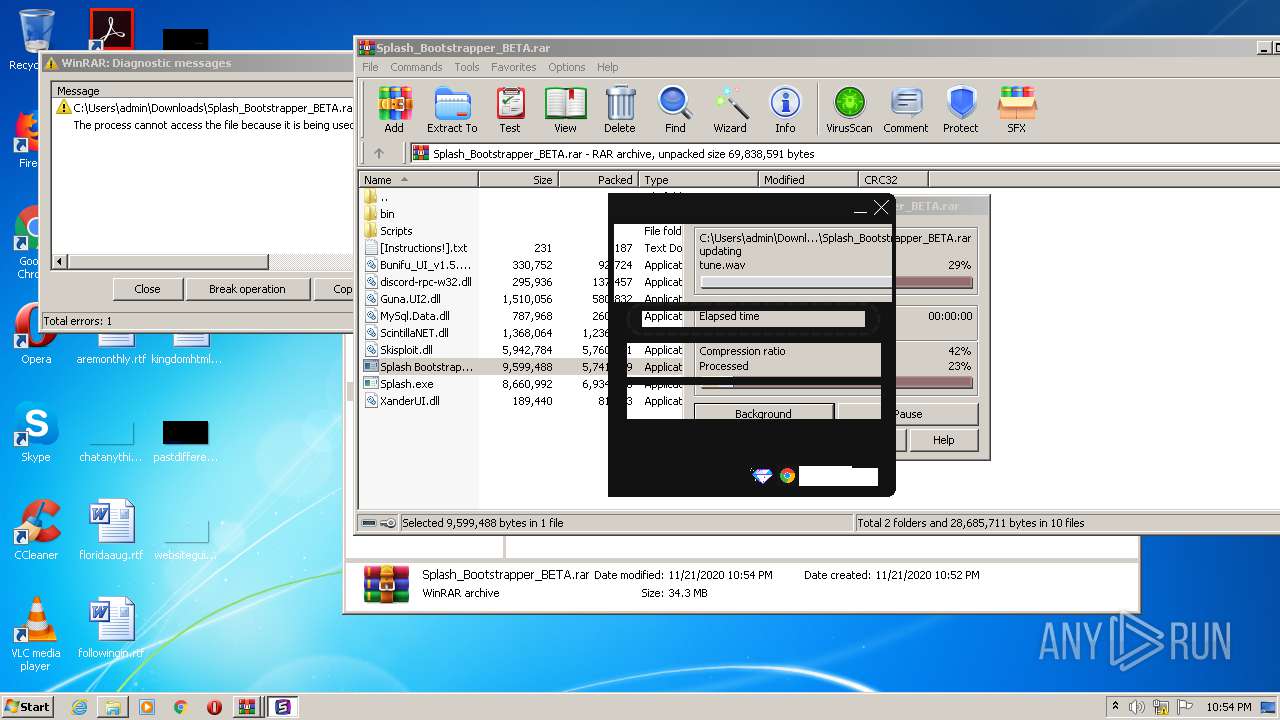
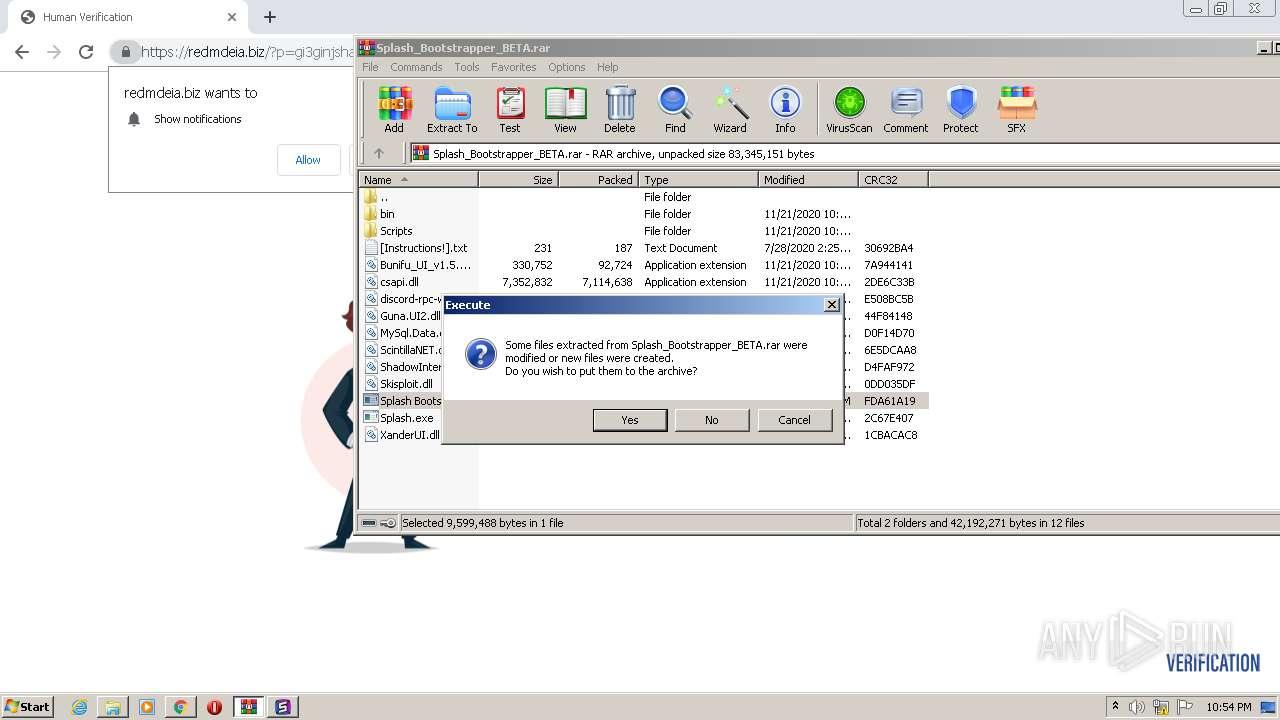
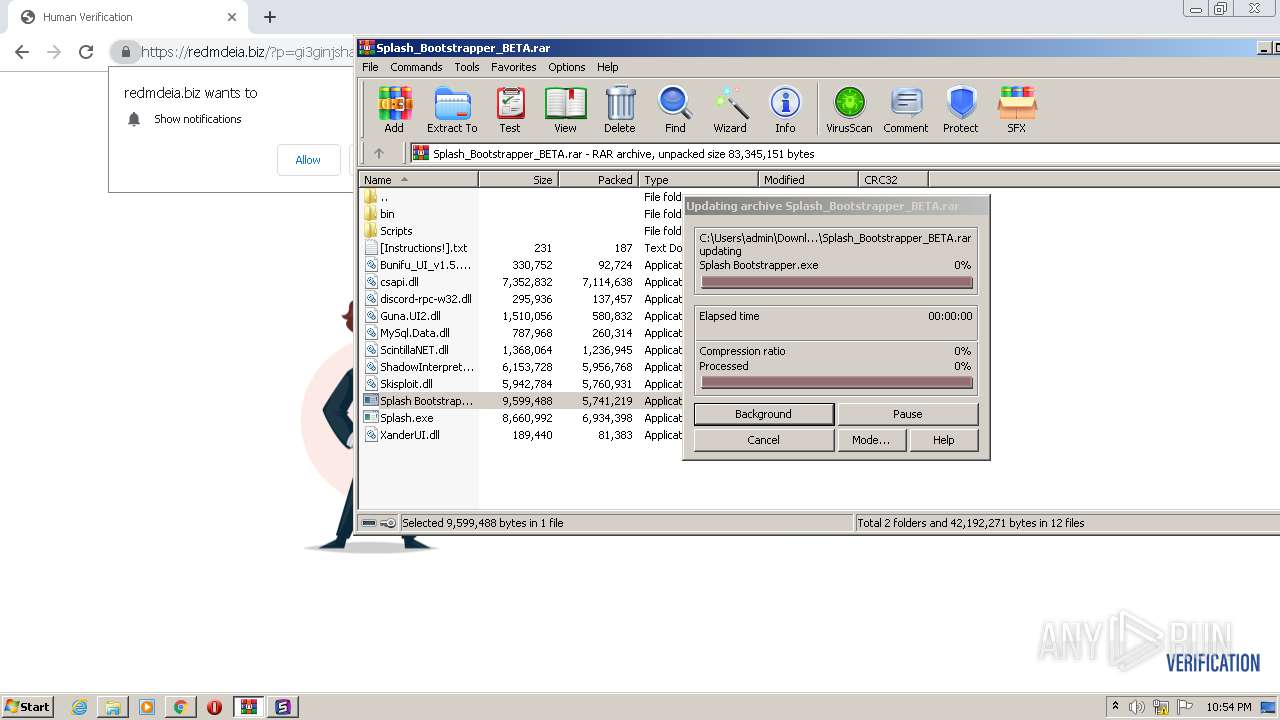
Executable content was dropped or overwritten
- WinRAR.exe (PID: 592)
- Splash.exe (PID: 972)
- Splash Bootstrapper.exe (PID: 2540)
Drops a file that was compiled in debug mode
- Splash Bootstrapper.exe (PID: 2540)
- Splash.exe (PID: 972)
Drops a file with too old compile date
- Splash Bootstrapper.exe (PID: 2540)
Drops a file with a compile date too recent
- Splash.exe (PID: 972)
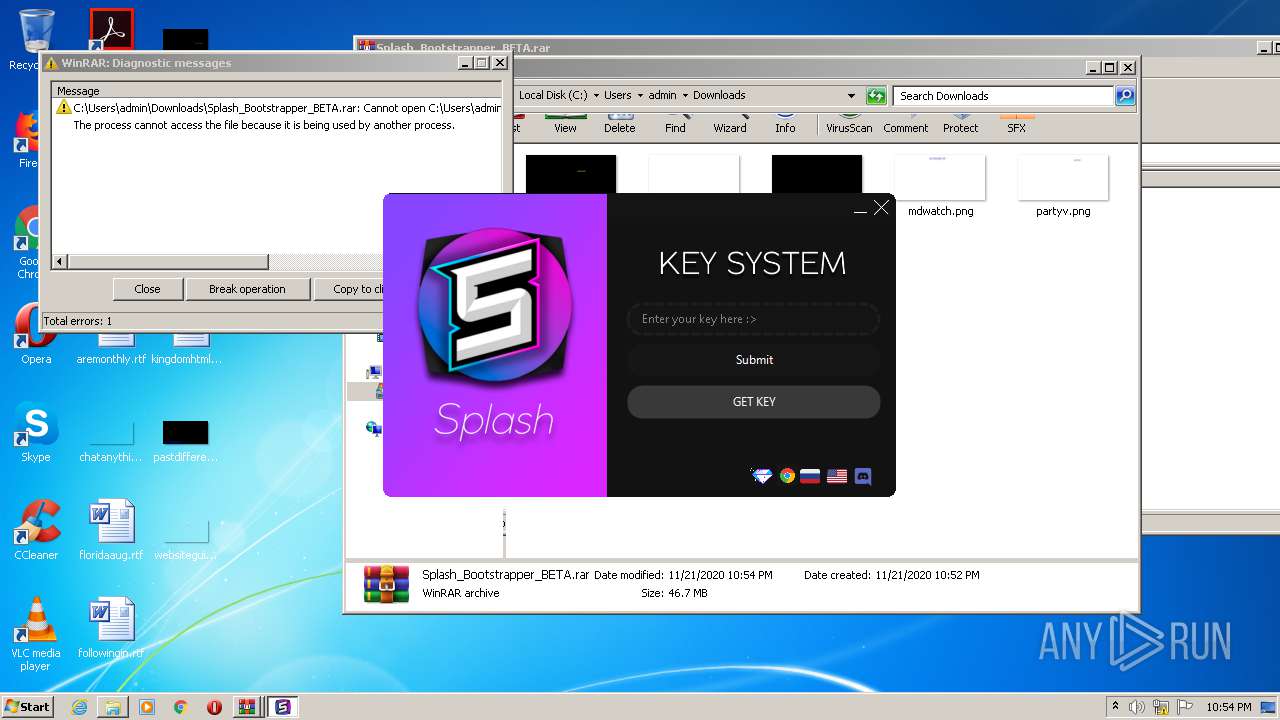
Reads internet explorer settings
- Splash.exe (PID: 972)
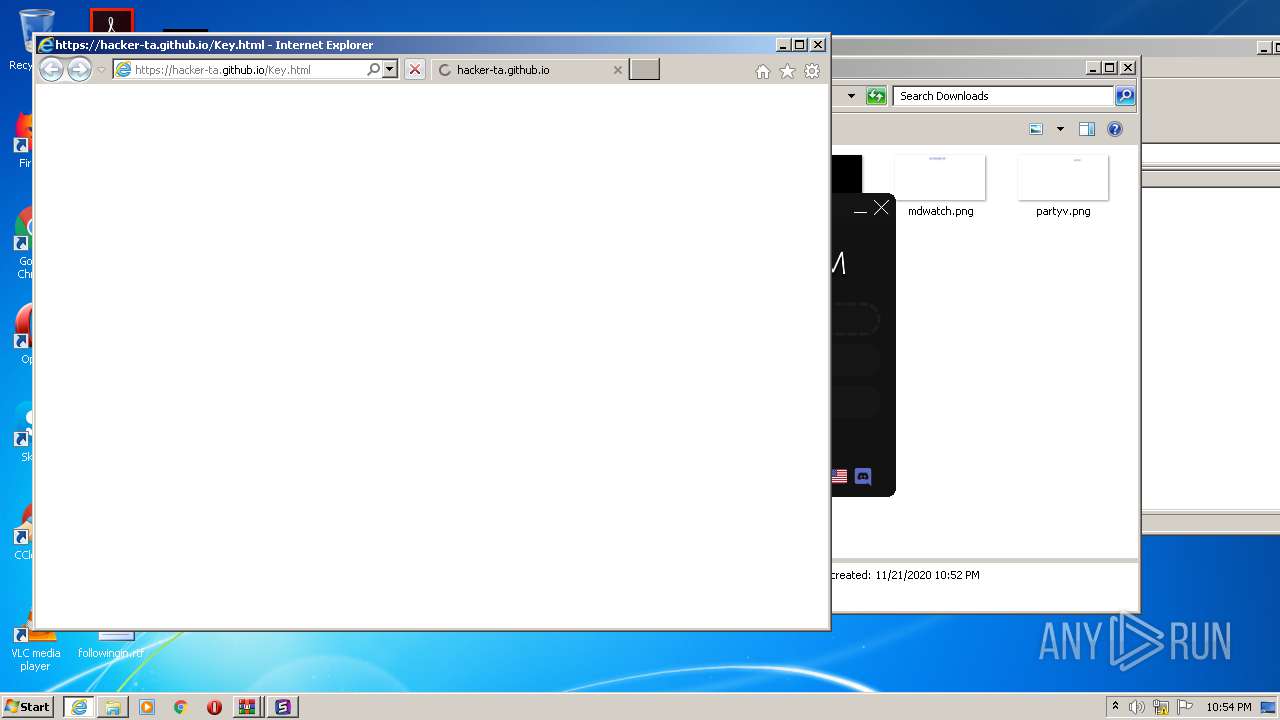
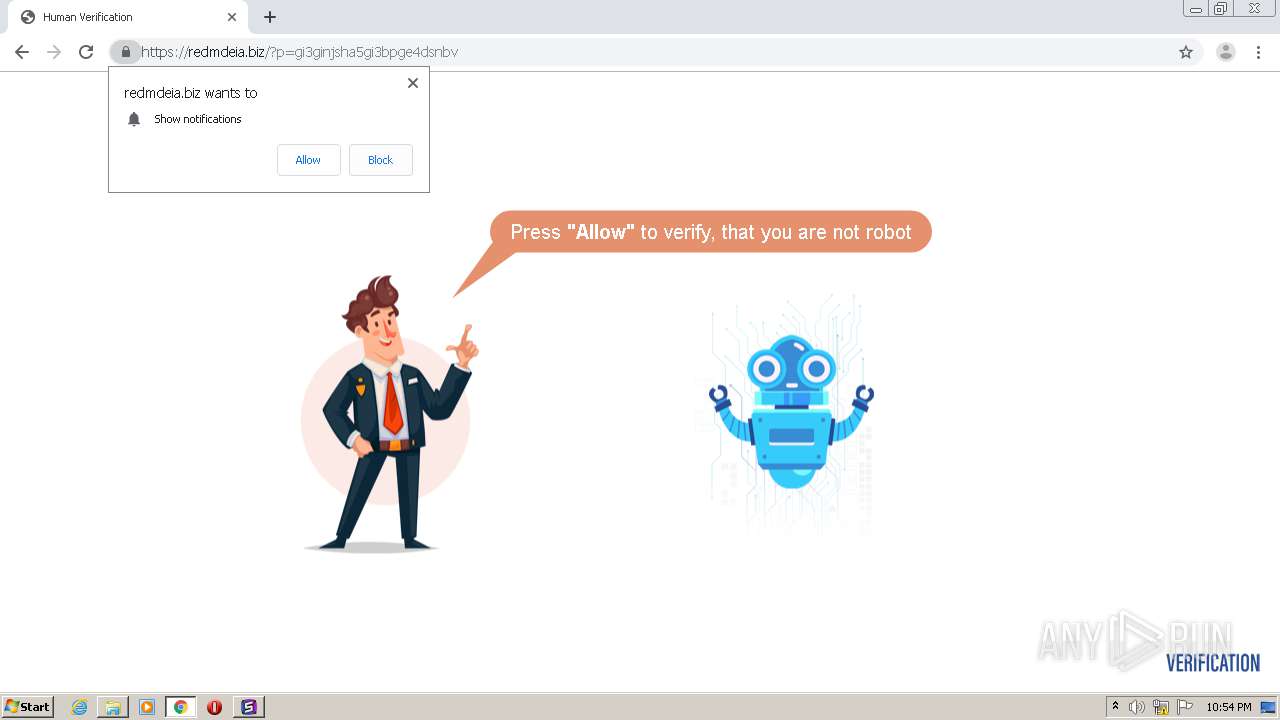
Starts Internet Explorer
- Splash.exe (PID: 972)
Creates files in the user directory
- Splash.exe (PID: 972)
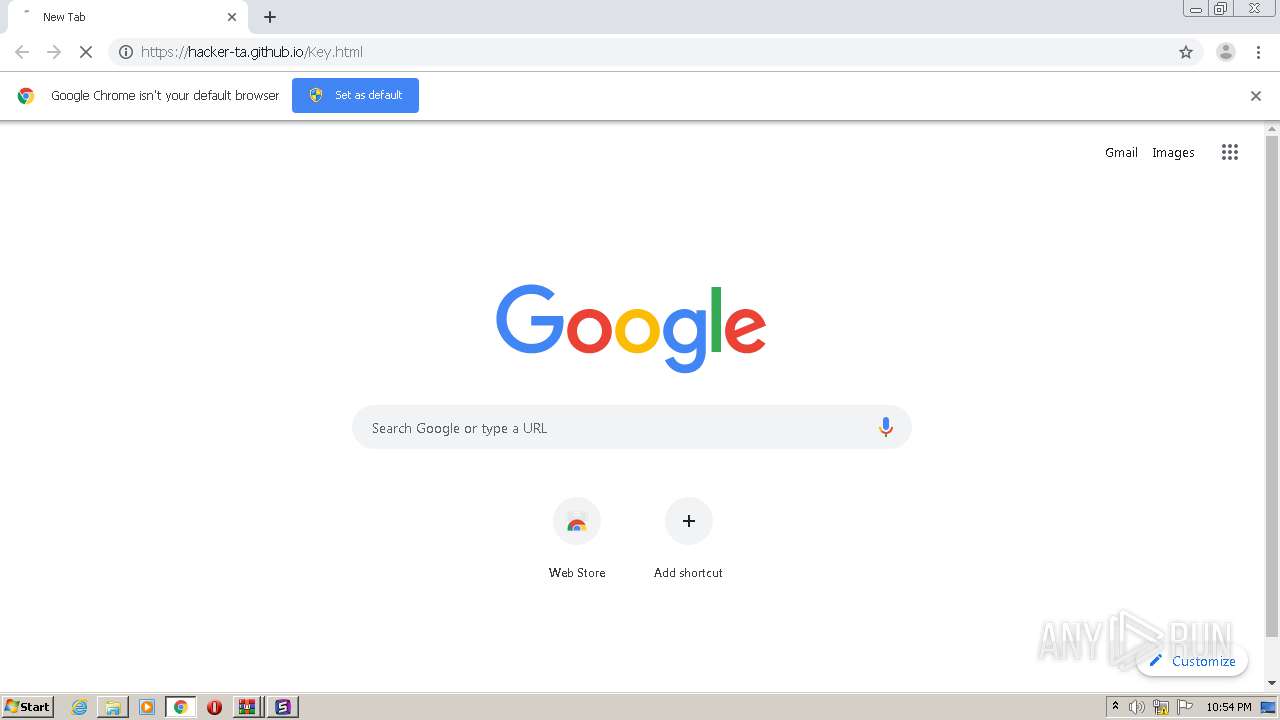
Modifies files in Chrome extension folder
- chrome.exe (PID: 3176)
Modifies the open verb of a shell class
- Splash.exe (PID: 972)
INFO
Application launched itself
- chrome.exe (PID: 1336)
- iexplore.exe (PID: 3372)
- chrome.exe (PID: 3176)
Reads the hosts file
- chrome.exe (PID: 1708)
- chrome.exe (PID: 1336)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 3284)
Dropped object may contain Bitcoin addresses
- Splash Bootstrapper.exe (PID: 2540)
- Splash.exe (PID: 972)
Changes internet zones settings
- iexplore.exe (PID: 3372)
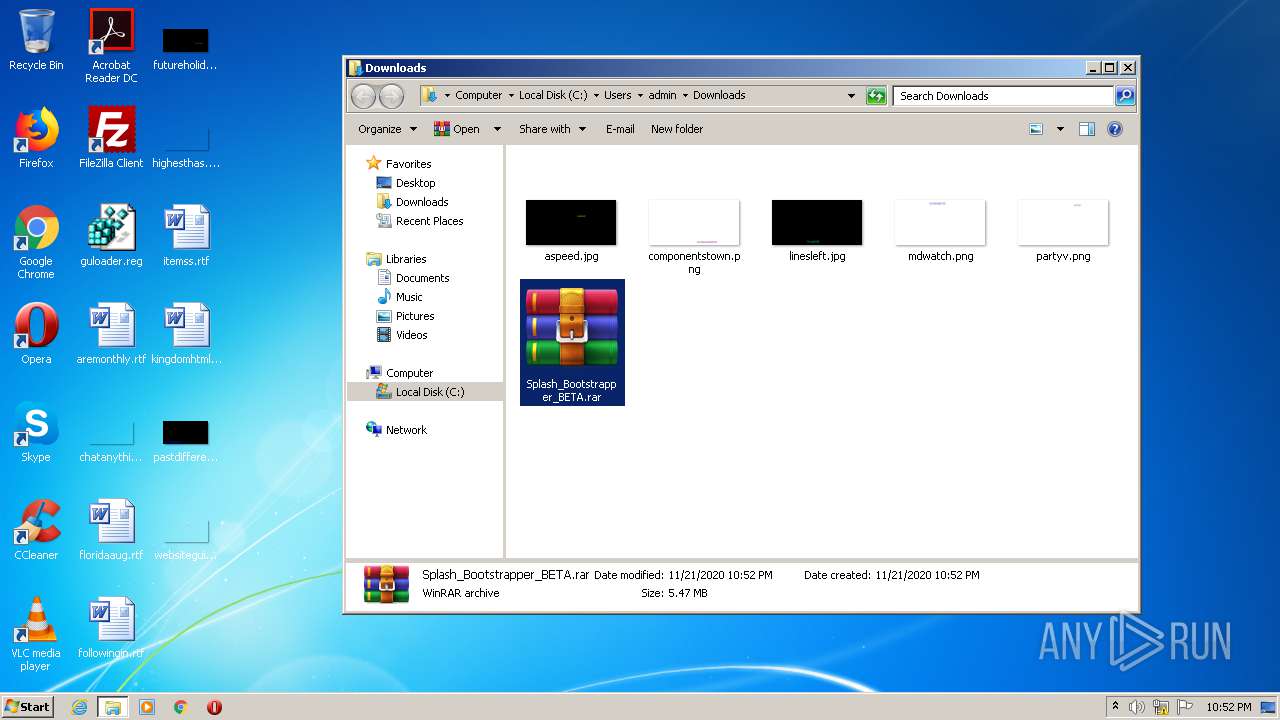
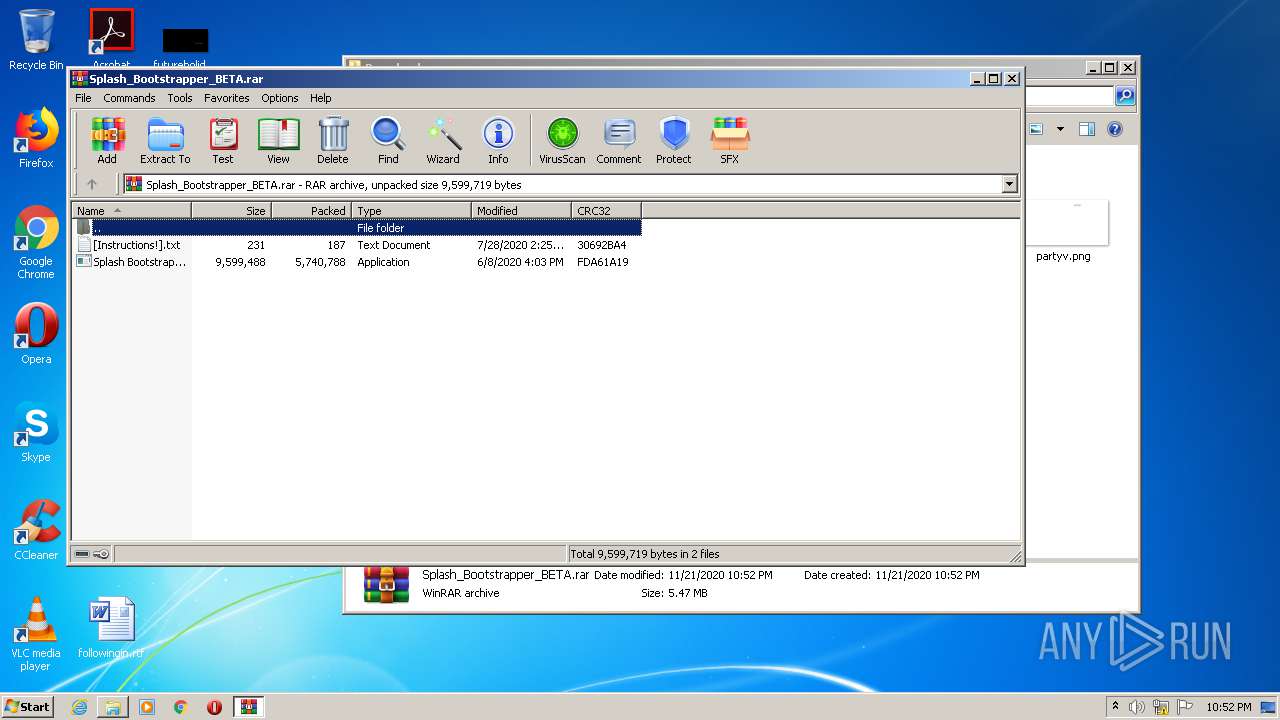
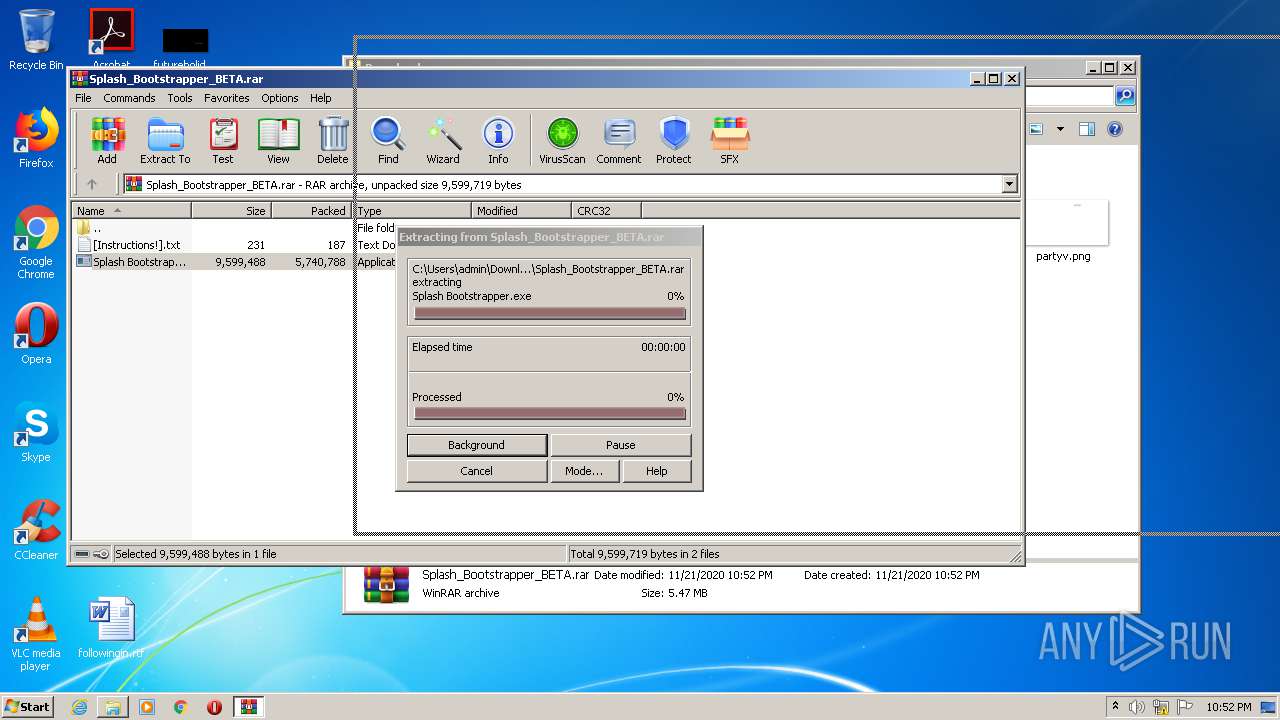
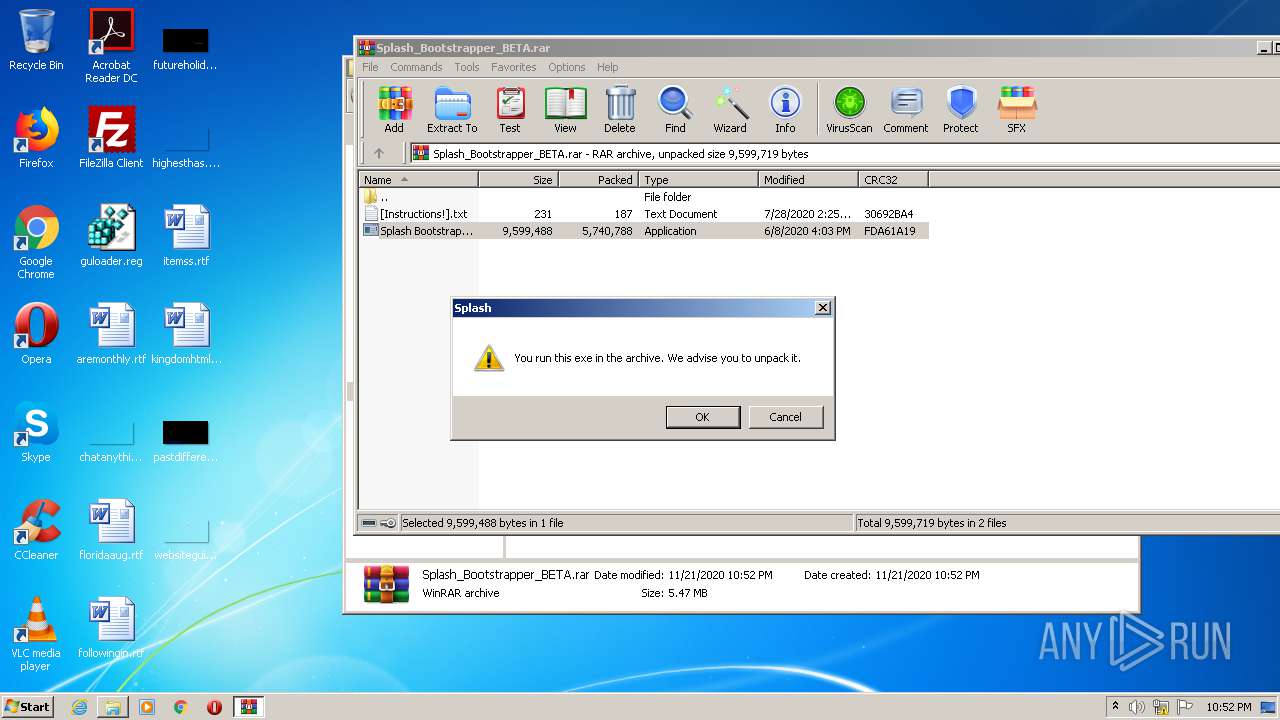
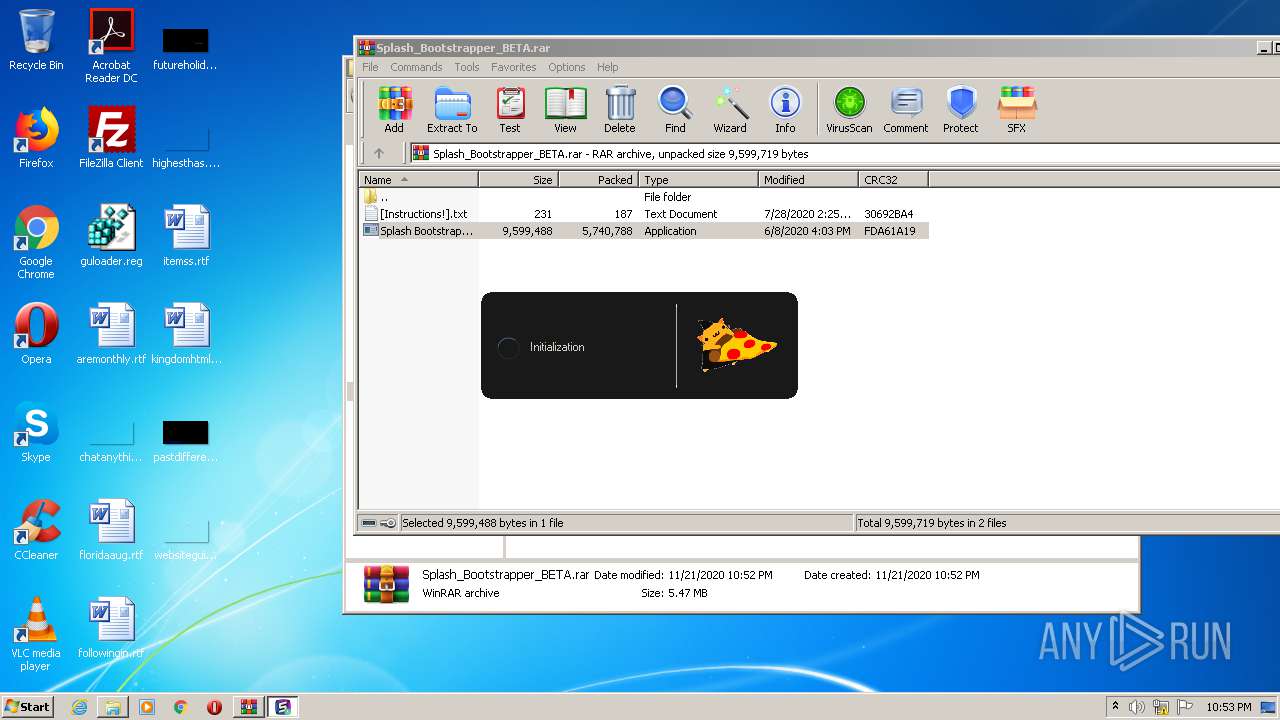
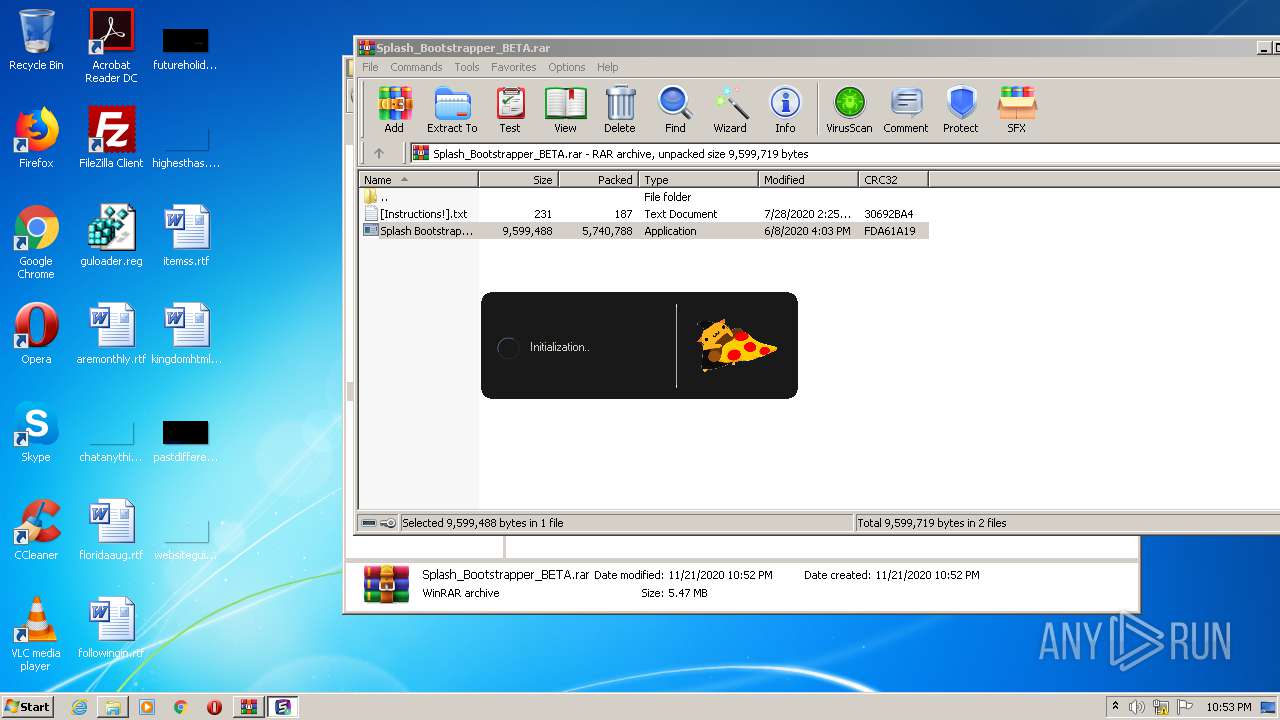
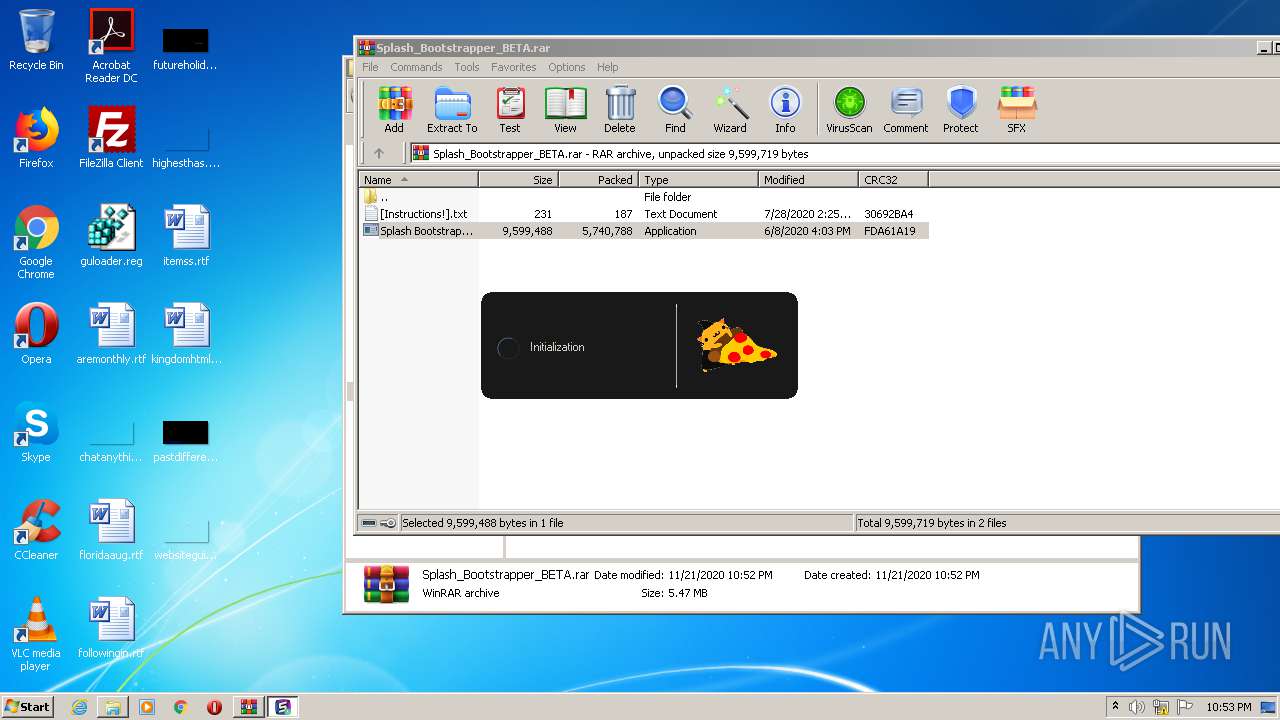
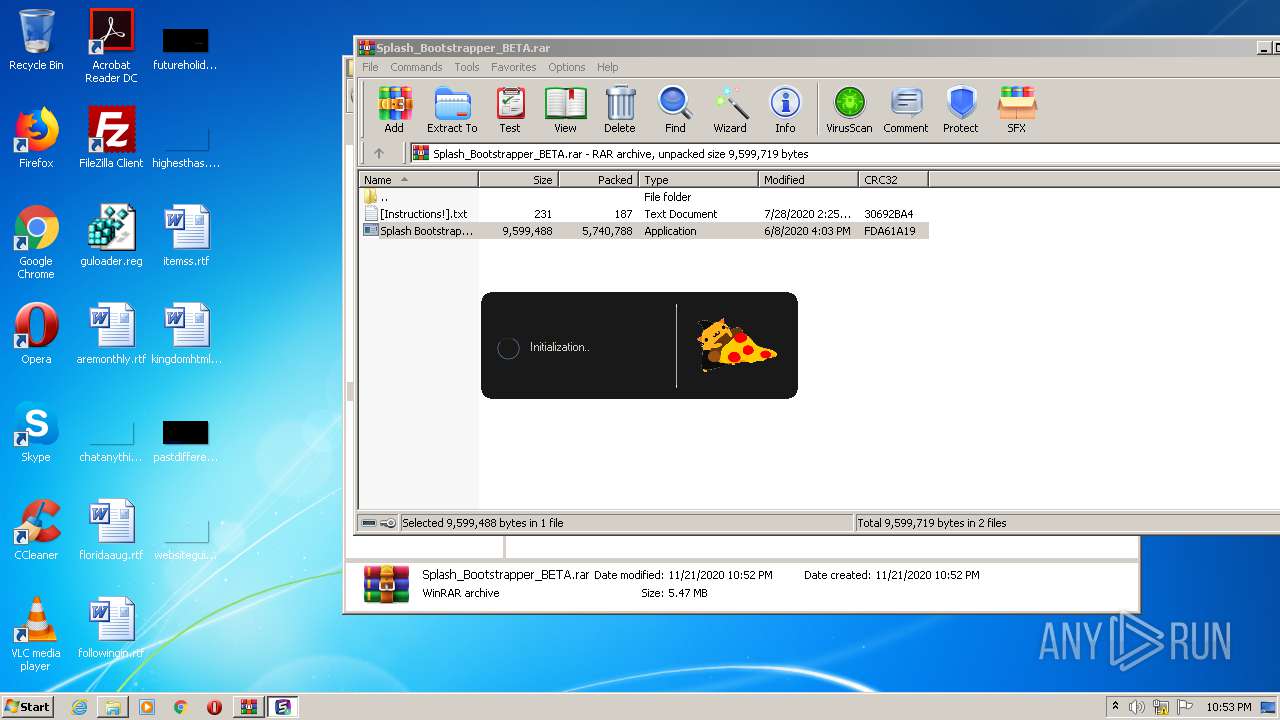
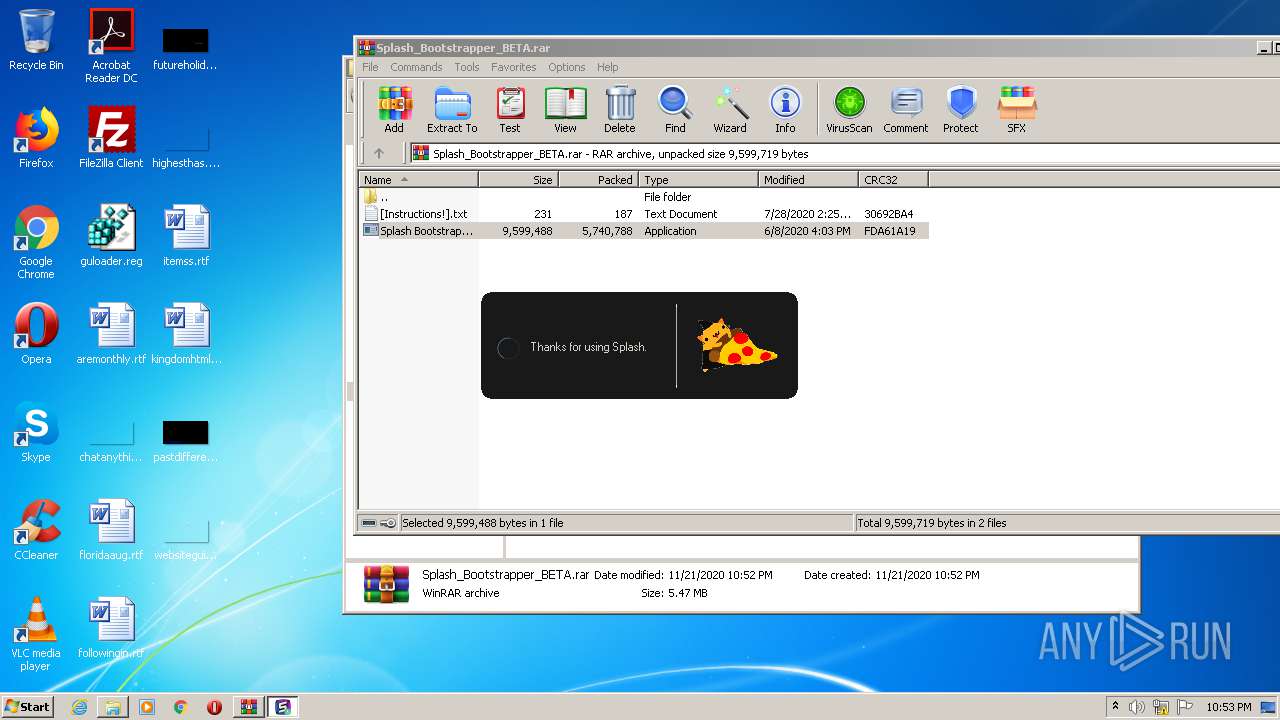
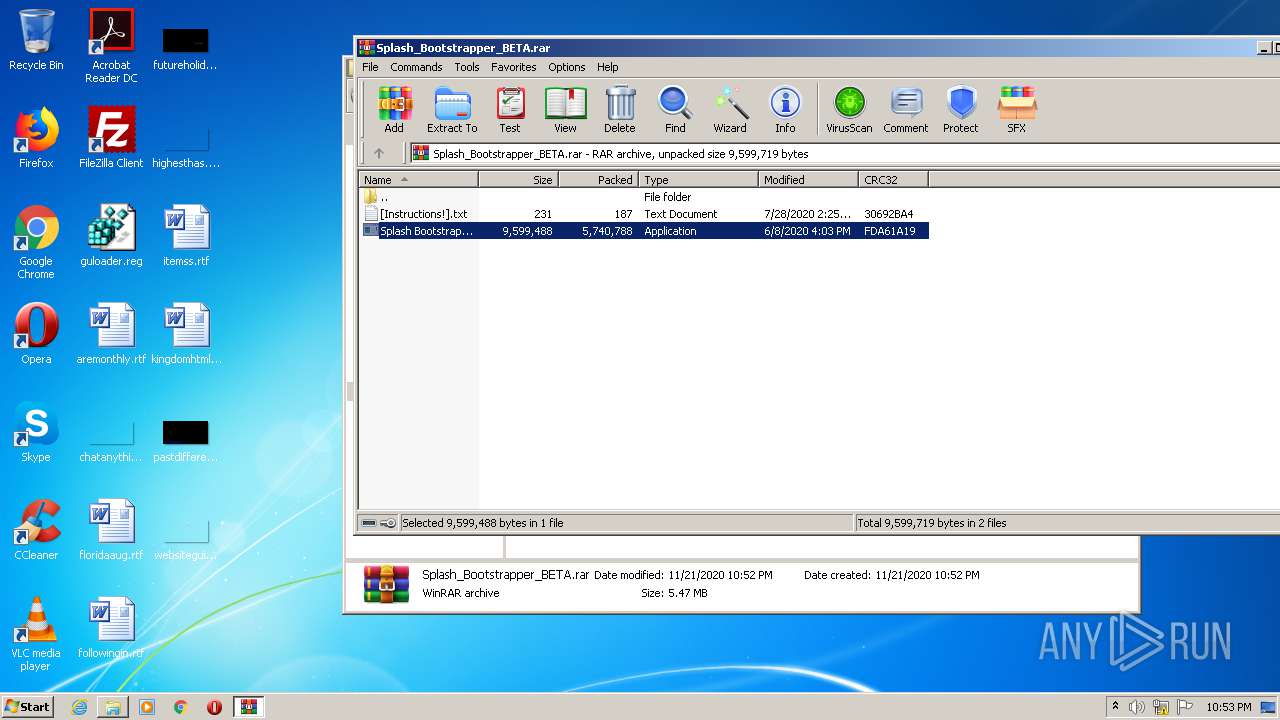
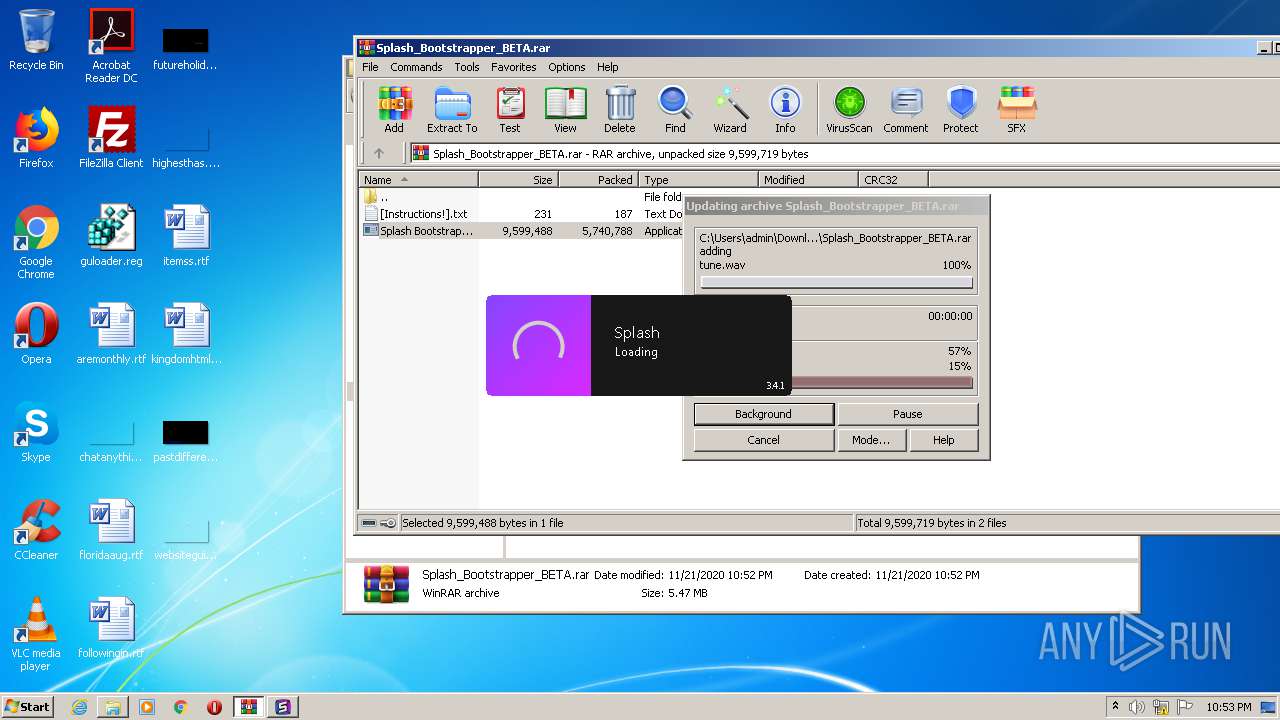
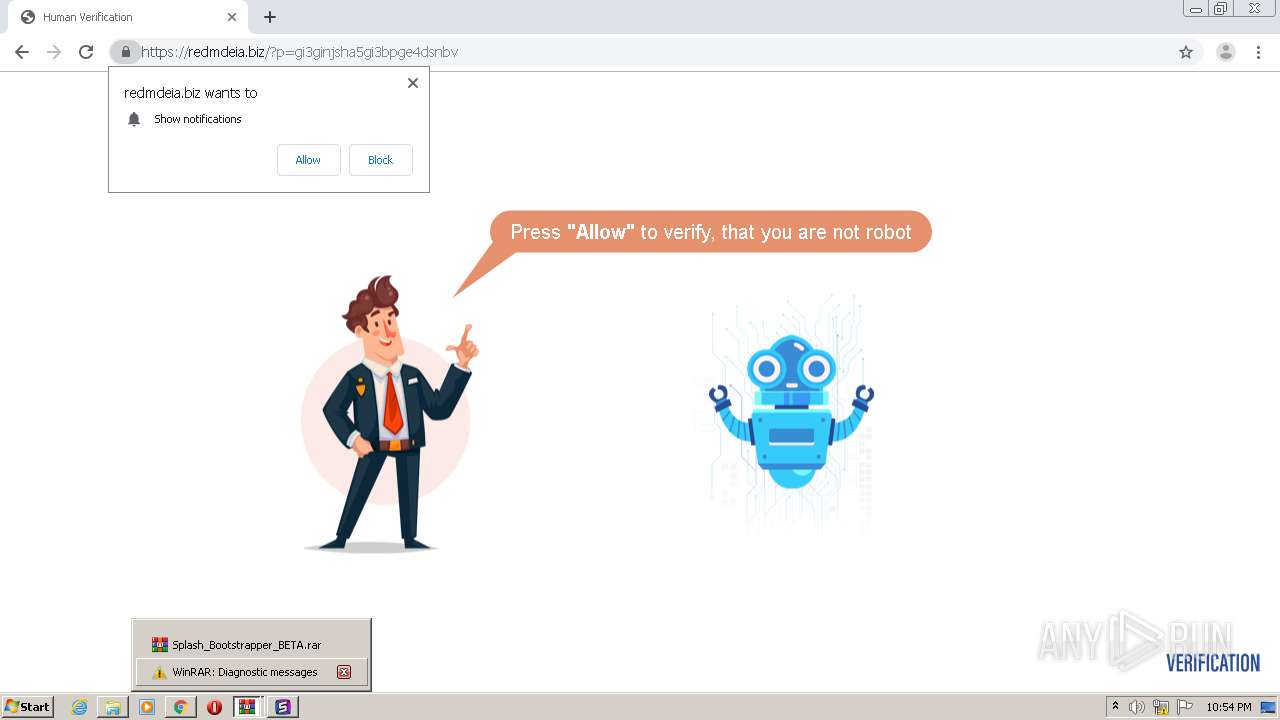
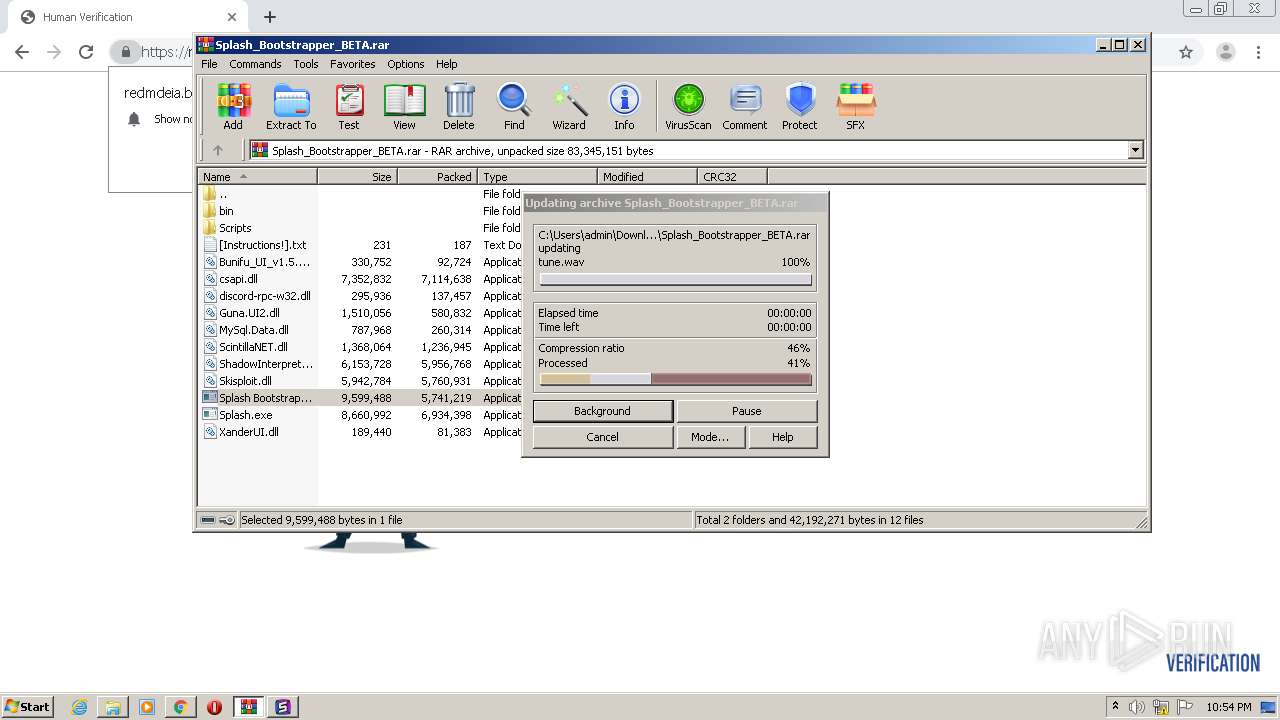
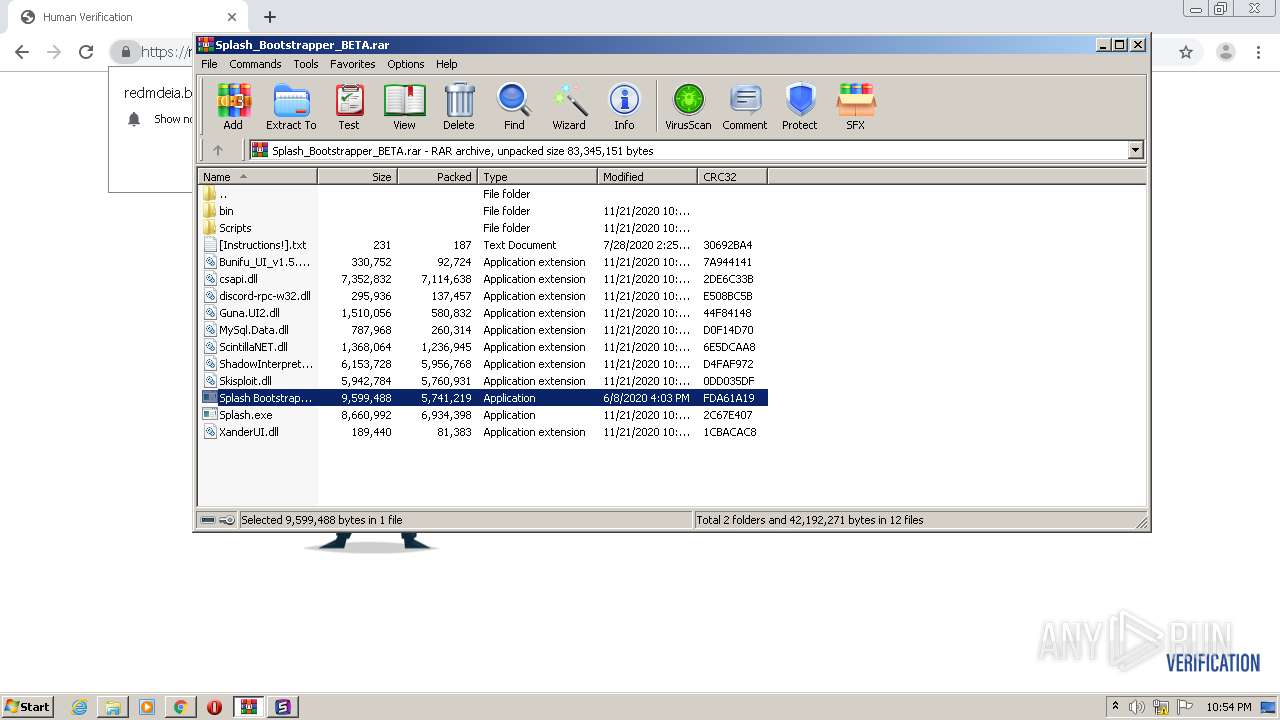
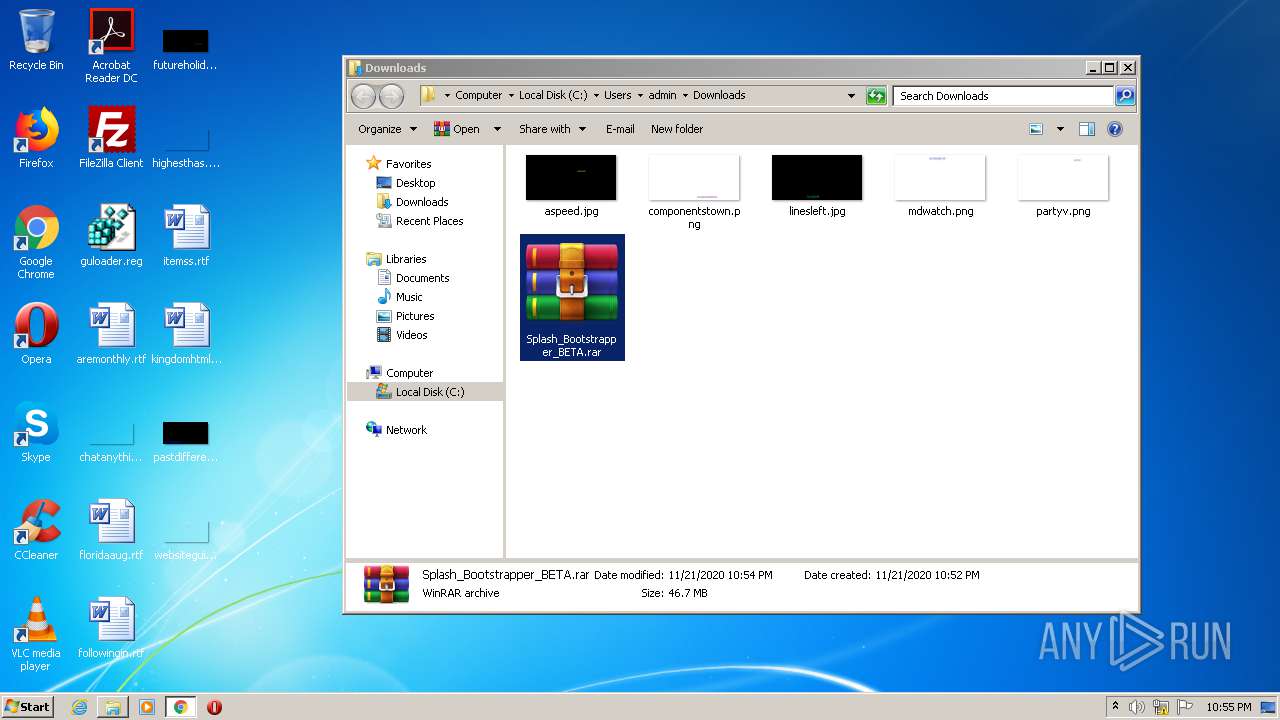
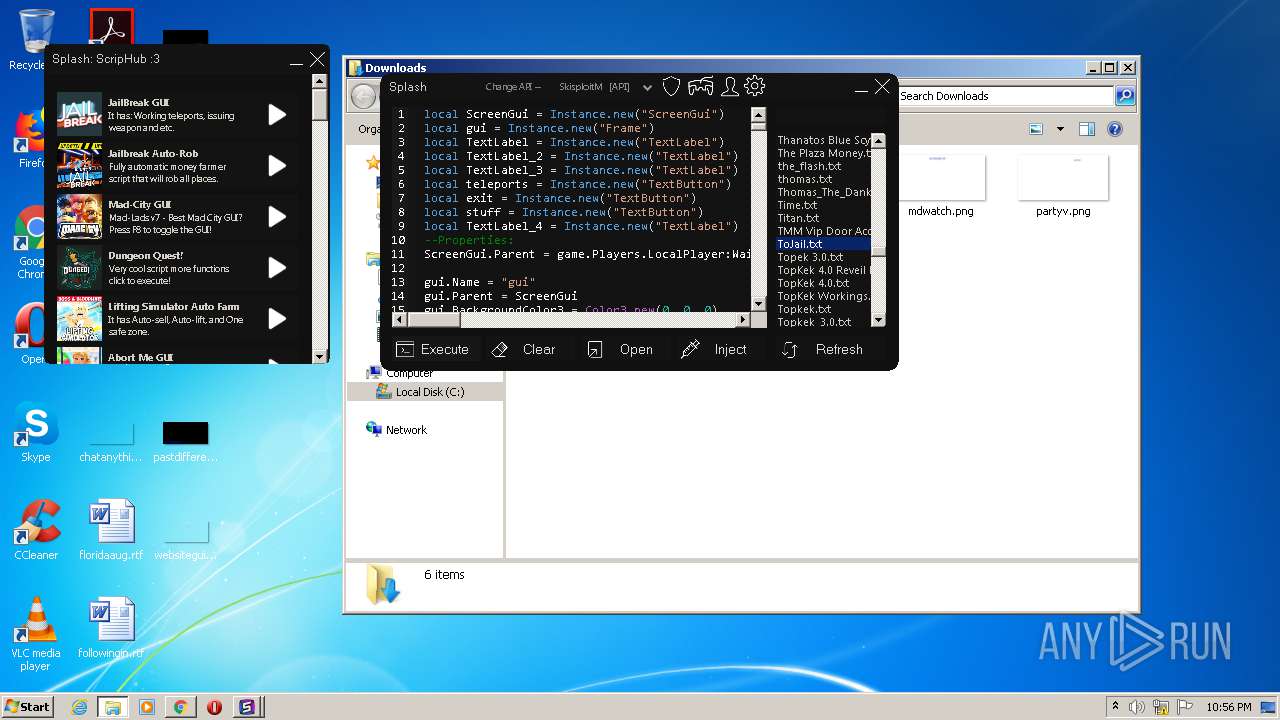
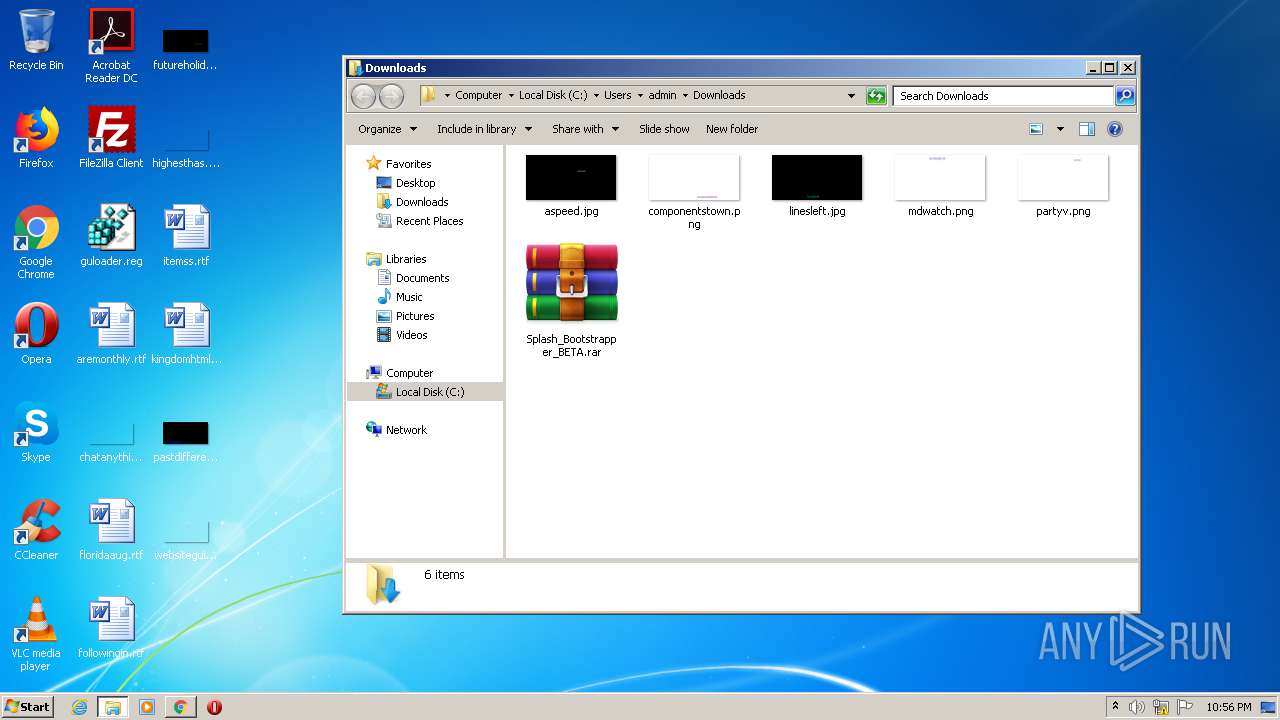
Manual execution by user
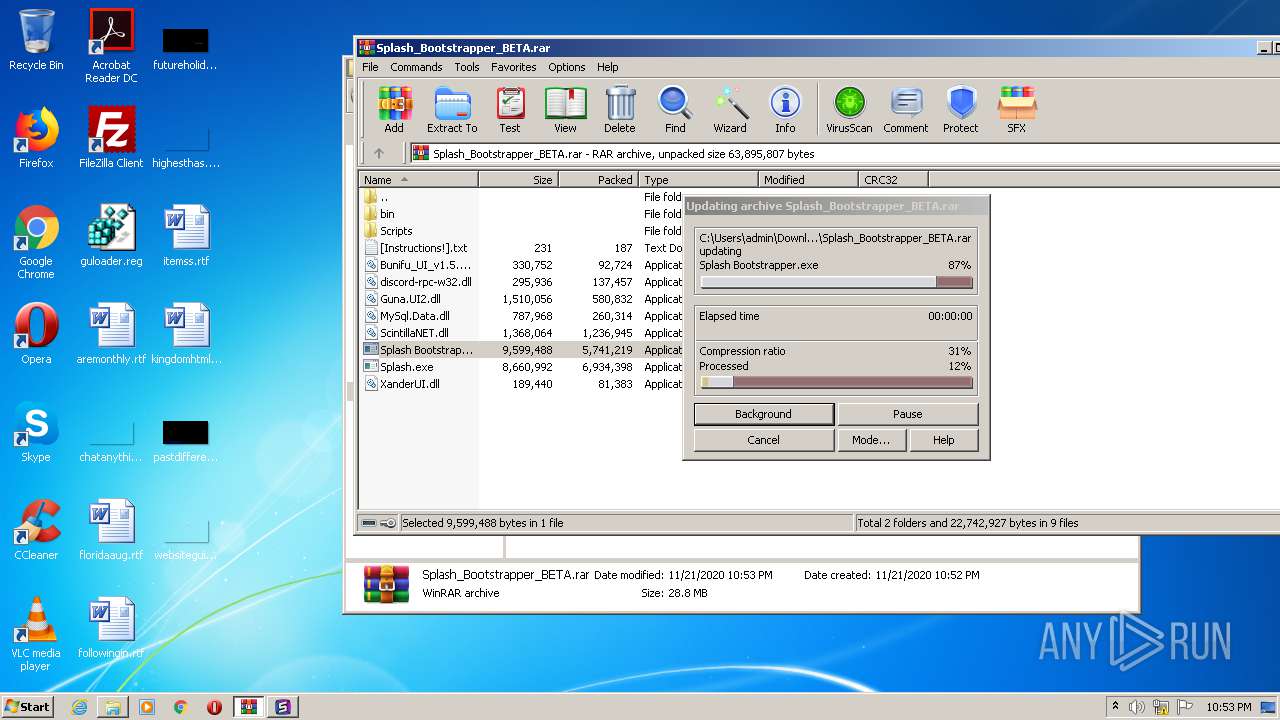
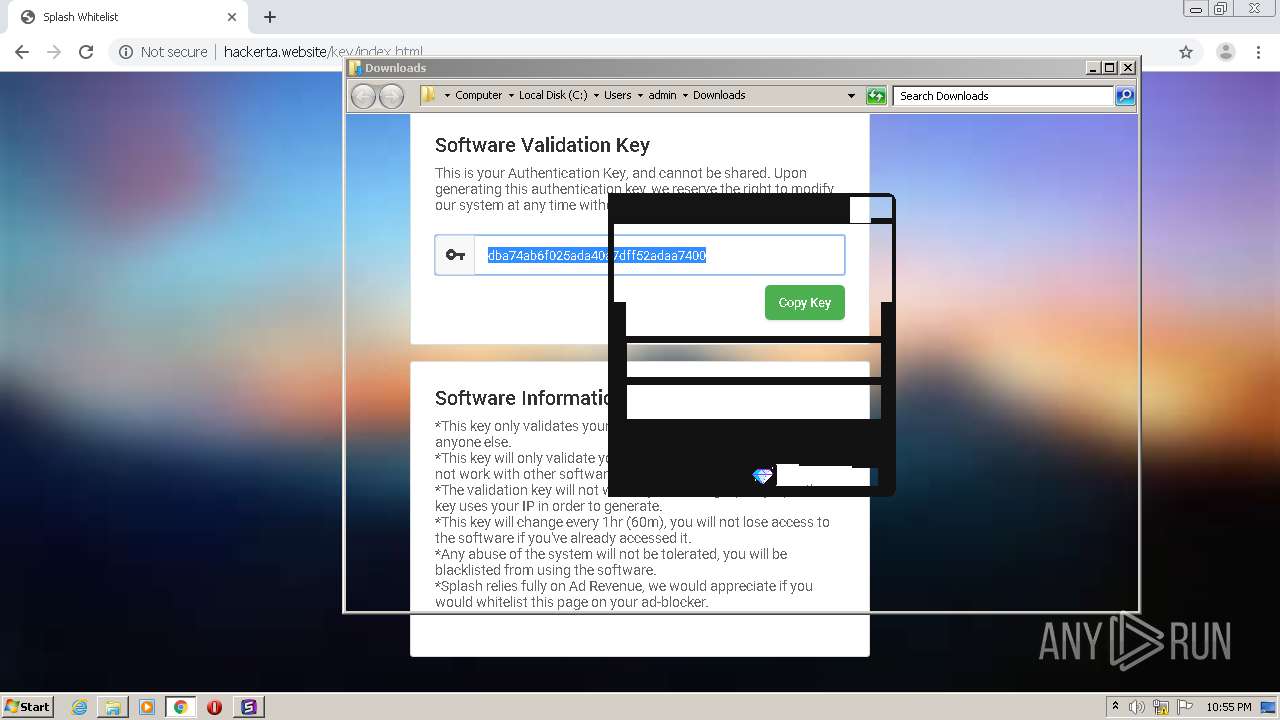
- WinRAR.exe (PID: 592)
- chrome.exe (PID: 3176)
Reads settings of System Certificates
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3372)
- chrome.exe (PID: 3284)
Reads internet explorer settings
- iexplore.exe (PID: 1132)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3372)
Changes settings of System certificates
- iexplore.exe (PID: 3372)
Modifies the open verb of a shell class
- chrome.exe (PID: 3176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
57
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8938709900150434833,1579103474528524987,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16688204071849671777 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8938709900150434833,1579103474528524987,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=316431553902661628 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8938709900150434833,1579103474528524987,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3915949087585258363 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Splash_Bootstrapper_BETA.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,8938709900150434833,1579103474528524987,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10290574541310488685 --mojo-platform-channel-handle=4052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8938709900150434833,1579103474528524987,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14163385363119397007 --mojo-platform-channel-handle=4872 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa592.441\Splash.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa592.441\Splash.exe | Splash Bootstrapper.exe | ||||||||||||
User: admin Company: Made by HackerTA Integrity Level: MEDIUM Description: Splash Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,8879744808475694257,574792280283358513,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14064323486836092996 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,8879744808475694257,574792280283358513,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2340546999590747238 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3372 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 502
Read events
3 104
Write events
381
Delete events
17
Modification events
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1336-13250472749736625 |
Value: 259 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
14
Suspicious files
189
Text files
579
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FB99A2E-538.pma | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13eea9.TMP | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1c52ebd9-4e2e-4fef-ad37-23fe33f5bc02.tmp | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13eec8.TMP | text | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13f06e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
127
DNS requests
75
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
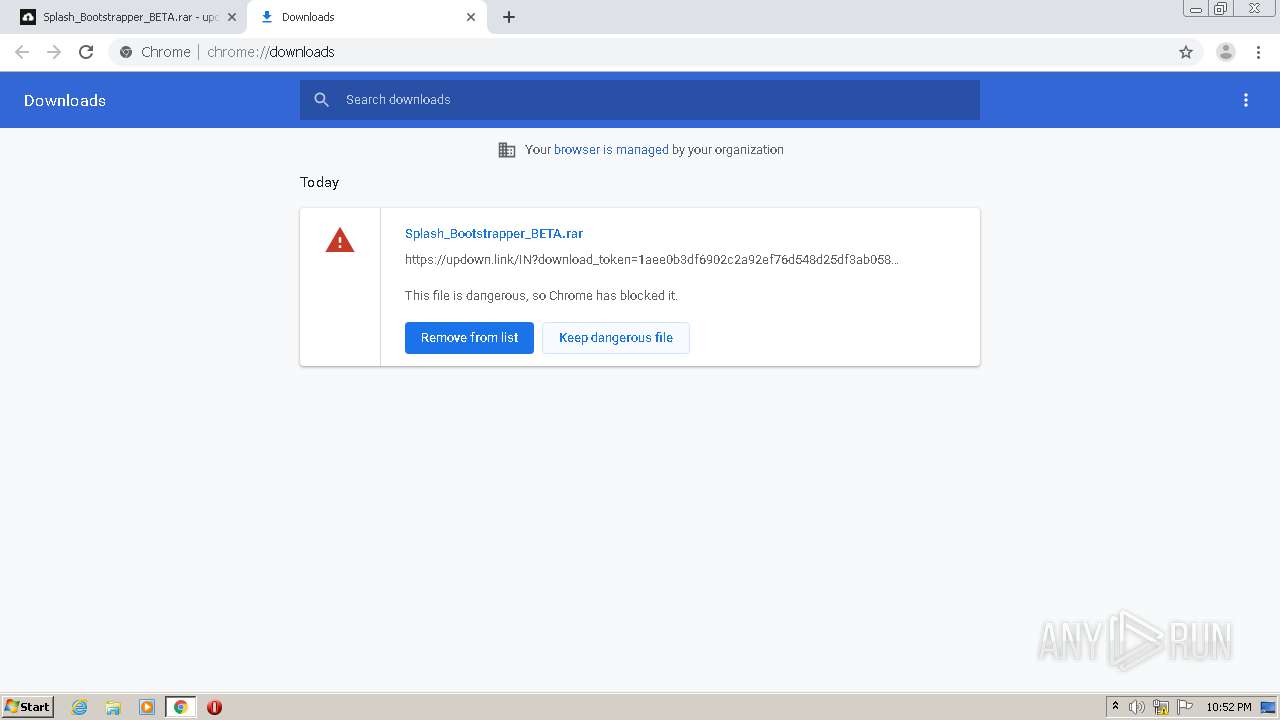
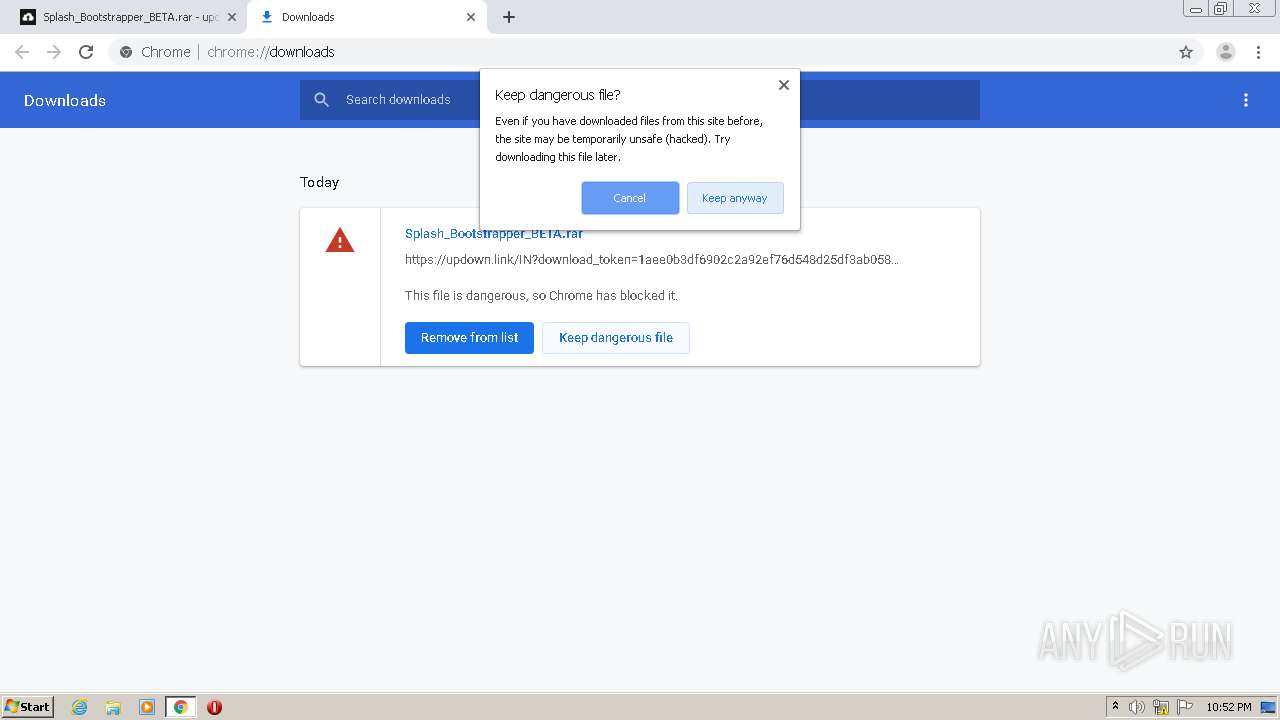
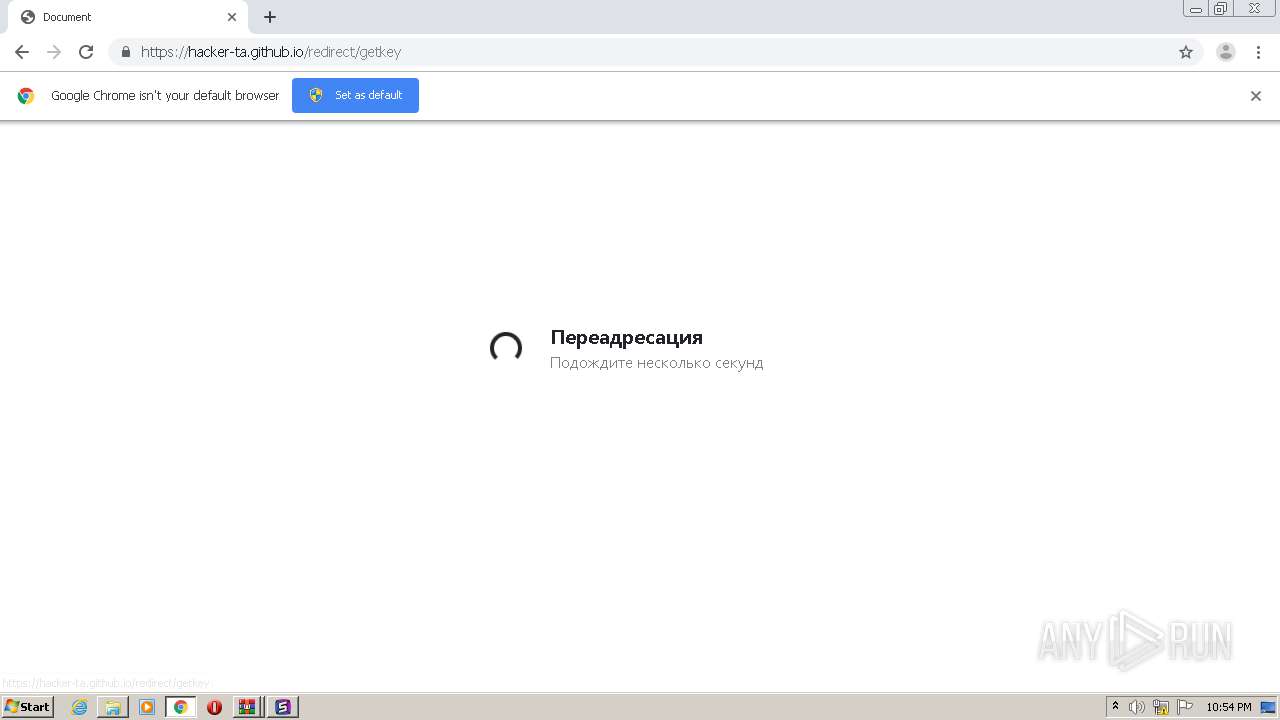
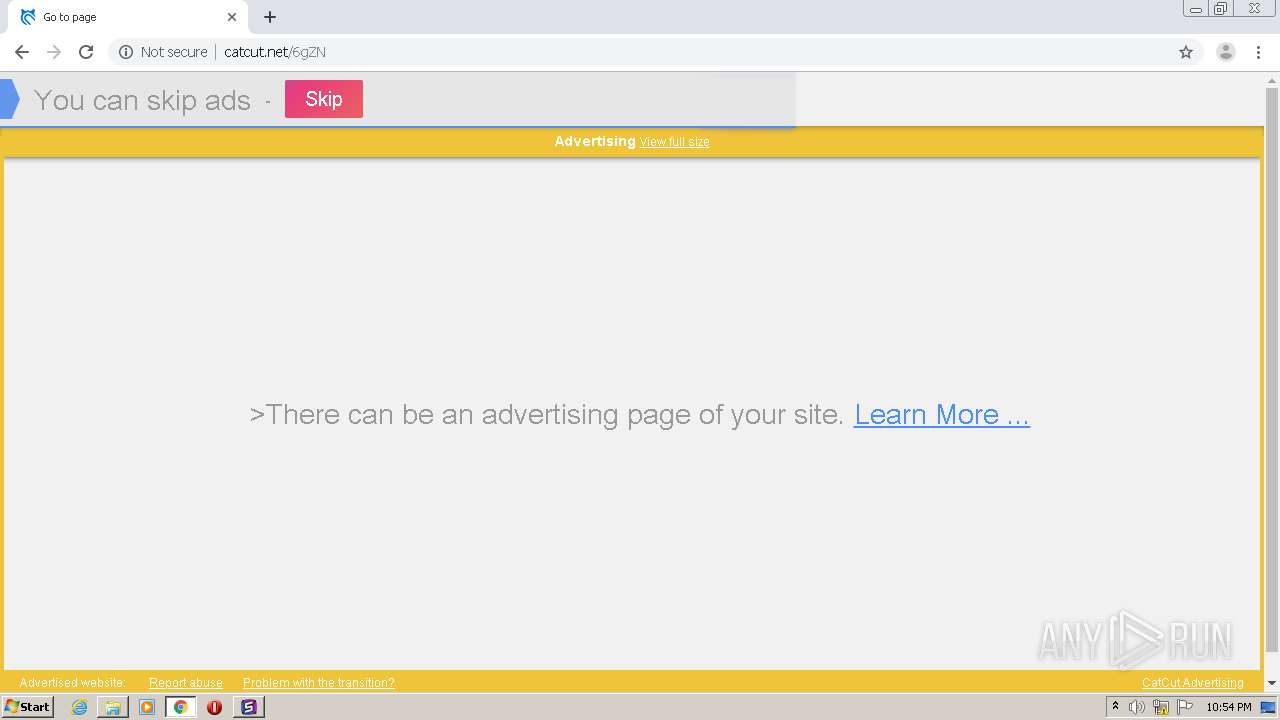
1708 | chrome.exe | GET | 301 | 172.67.143.17:80 | http://updown.link/IN?download_token=1aee0b3df6902c2a92ef76d548d25df3ab058adc98f787da16abb10b7ff6068c | US | — | — | malicious |
972 | Splash.exe | GET | 200 | 104.24.106.9:80 | http://api.thundermods.com/dlldownload.txt | US | text | 90 b | malicious |
972 | Splash.exe | GET | 200 | 188.225.32.199:5555 | http://188.225.32.199:5555/ | RU | text | 2.98 Kb | unknown |
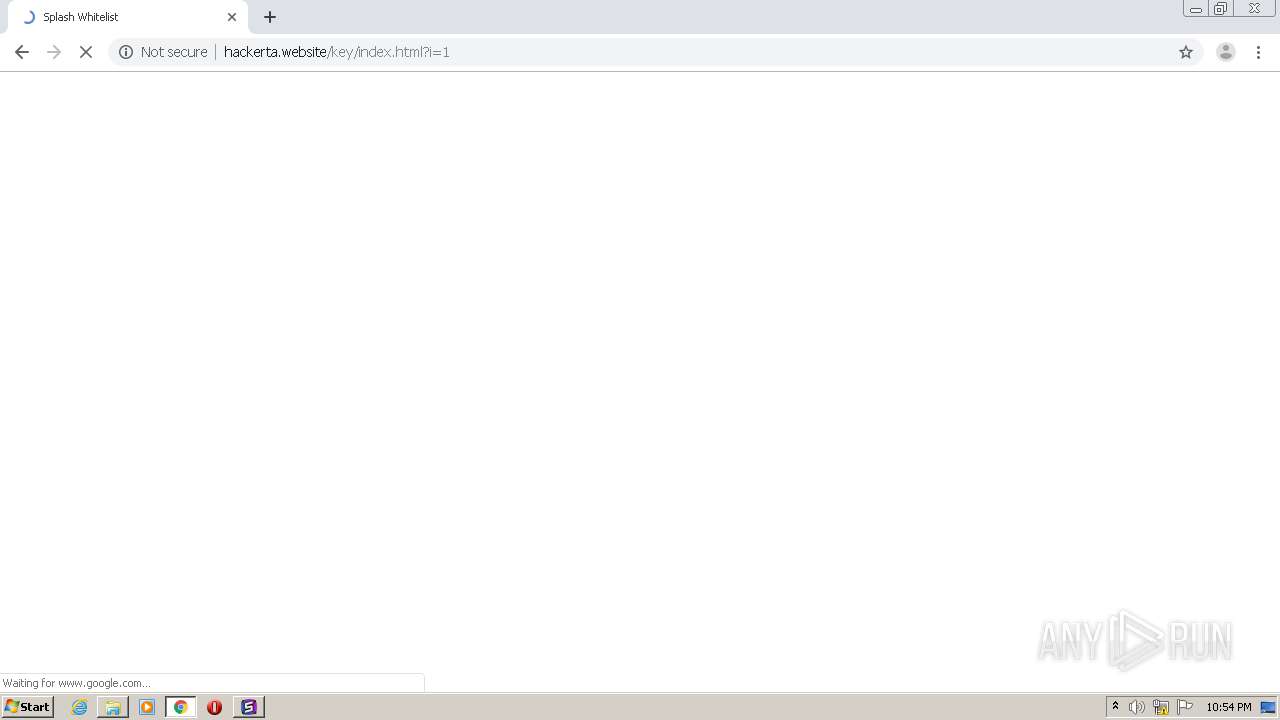
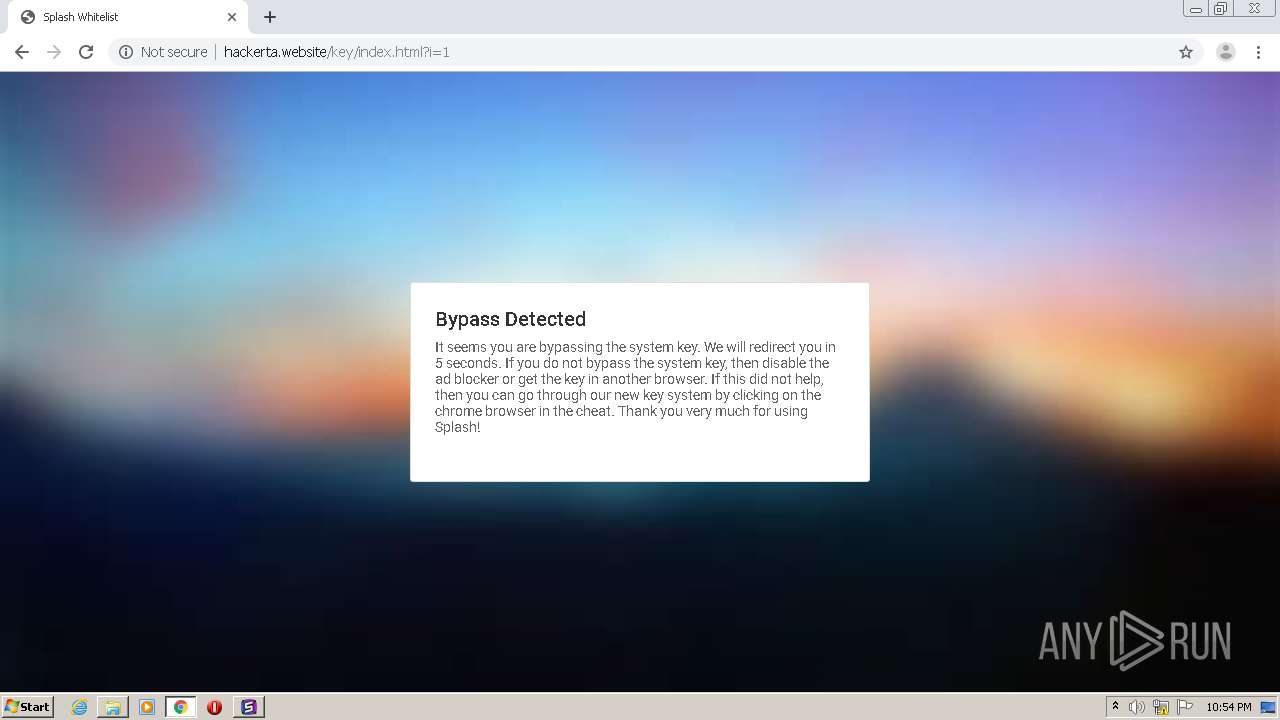
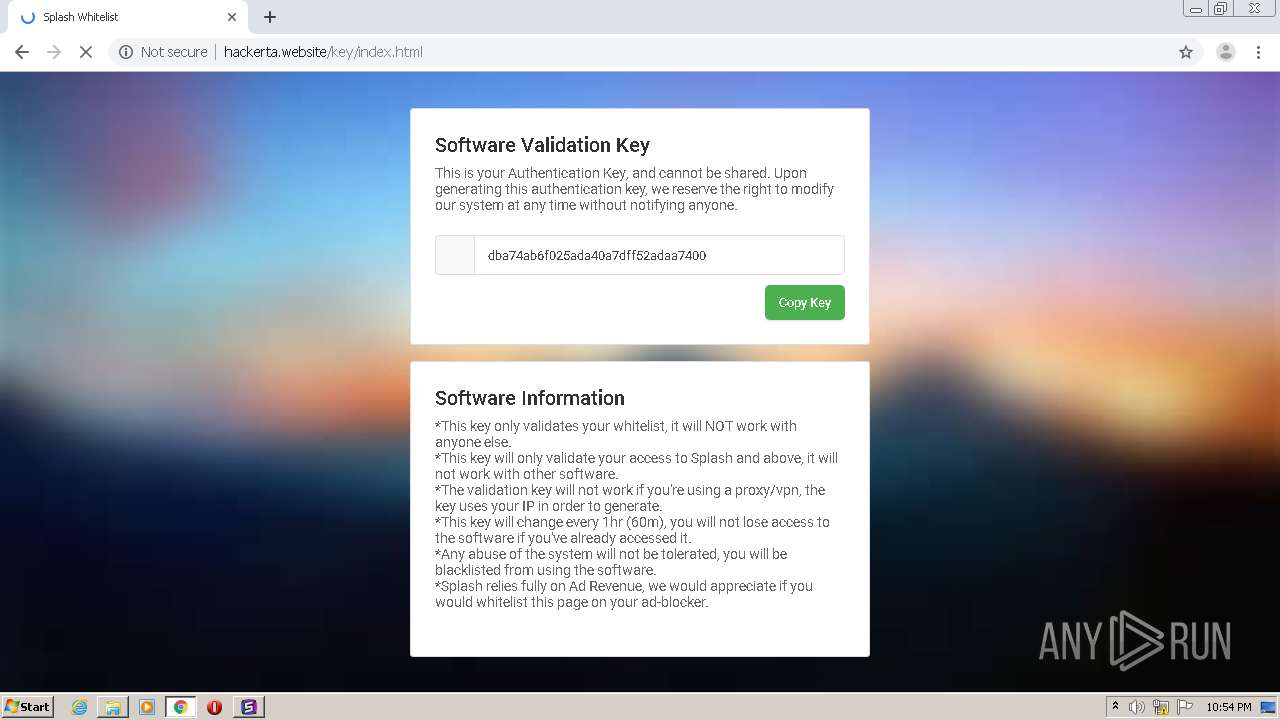
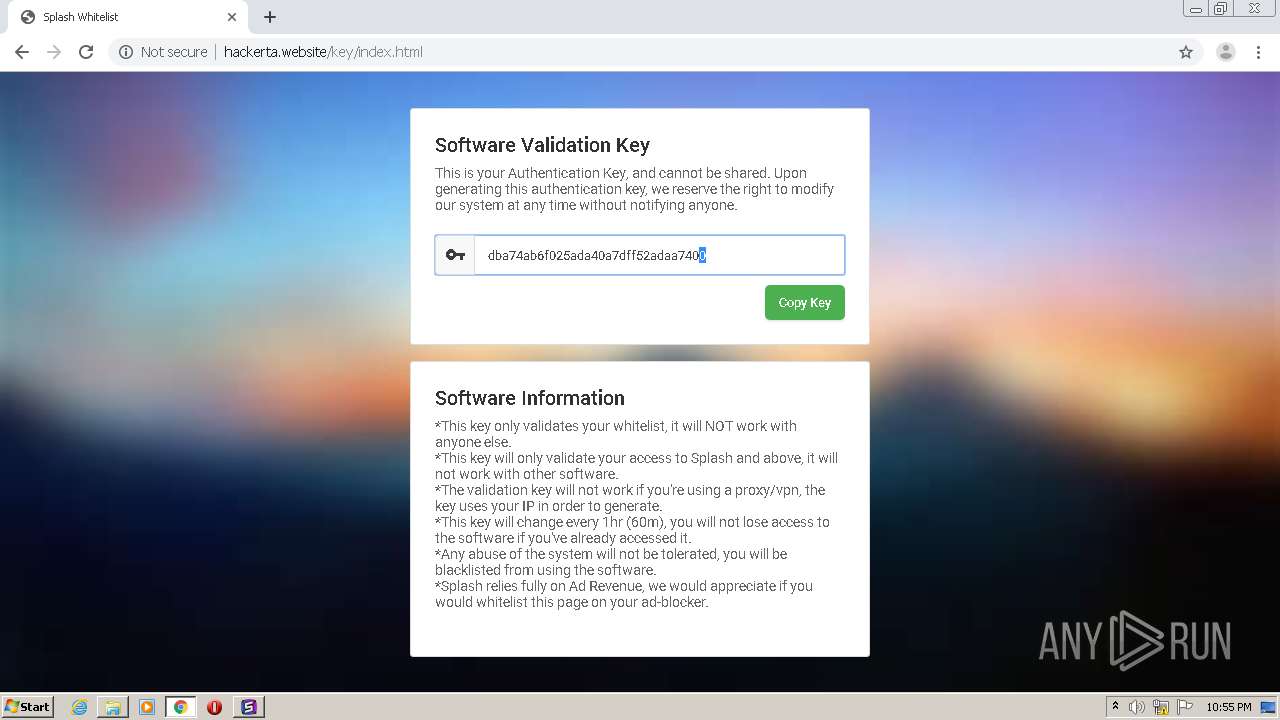
972 | Splash.exe | GET | 200 | 185.27.134.221:80 | http://hackerta.website/key/goawayandfuckoff.php | GB | html | 570 b | malicious |
1132 | iexplore.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
972 | Splash.exe | GET | 200 | 185.27.134.221:80 | http://hackerta.website/key/goawayandfuckoff.php?i=1 | GB | text | 52 b | malicious |
1132 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1132 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1132 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPtFDol%2Bljtio1d57BIDoJblg%3D%3D | unknown | der | 527 b | whitelisted |
1132 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPtFDol%2Bljtio1d57BIDoJblg%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1708 | chrome.exe | 108.177.104.84:443 | accounts.google.com | Google Inc. | US | unknown |
1708 | chrome.exe | 172.67.143.17:443 | updown.link | — | US | suspicious |
1708 | chrome.exe | 172.217.195.139:443 | clients4.google.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.67.143.17:80 | updown.link | — | US | suspicious |
1708 | chrome.exe | 64.233.180.190:443 | sb-ssl.google.com | Google Inc. | US | unknown |
1708 | chrome.exe | 108.177.104.93:443 | safebrowsing.google.com | Google Inc. | US | unknown |
2540 | Splash Bootstrapper.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
2540 | Splash Bootstrapper.exe | 162.159.133.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
updown.link |
| malicious |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
clients4.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
cdn.discordapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
972 | Splash.exe | Misc activity | SUSPICIOUS [PTsecurity] Encryptor aes.js script (PedCont ransomware) |
972 | Splash.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3284 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Encryptor aes.js script (PedCont ransomware) |
1 ETPRO signatures available at the full report