| File name: | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe |
| Full analysis: | https://app.any.run/tasks/fd6faebe-dca2-47f3-bf9a-5f4026db8521 |
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2019, 14:33:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 41F04143113A759524BD13993AFA4B8E |
| SHA1: | 213FB7A5317293B22AE9CF076997A94CC7FA49B7 |
| SHA256: | 76A40DC24A8AD150407F98ED0E69E68CC6481543DB7DA7C6615140805A07721F |
| SSDEEP: | 49152:dErSOG06fu8EirLITO8KlcsDsRe0TaIlAiJWtptzfwhK:VOG0wFEirLb8KlnIBlAiYPzos |
MALICIOUS
Changes settings of System certificates
- stats_uploader.exe (PID: 3728)
- stats_uploader.exe (PID: 1732)
Application was dropped or rewritten from another process
- stats_uploader.exe (PID: 1732)
- stats_uploader.exe (PID: 3728)
- stats_uploader.exe (PID: 1096)
SUSPICIOUS
Adds / modifies Windows certificates
- stats_uploader.exe (PID: 3728)
- stats_uploader.exe (PID: 1732)
Executable content was dropped or overwritten
- UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe (PID: 3280)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (78.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (11.3) |
| .exe | | | Generic Win/DOS Executable (5) |
| .exe | | | DOS Executable Generic (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:20 06:42:56+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 757760 |
| InitializedDataSize: | 929792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x92dd7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.185.1002 |
| ProductVersionNumber: | 7.0.185.1002 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build, Special build |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | UCWeb Inc. |
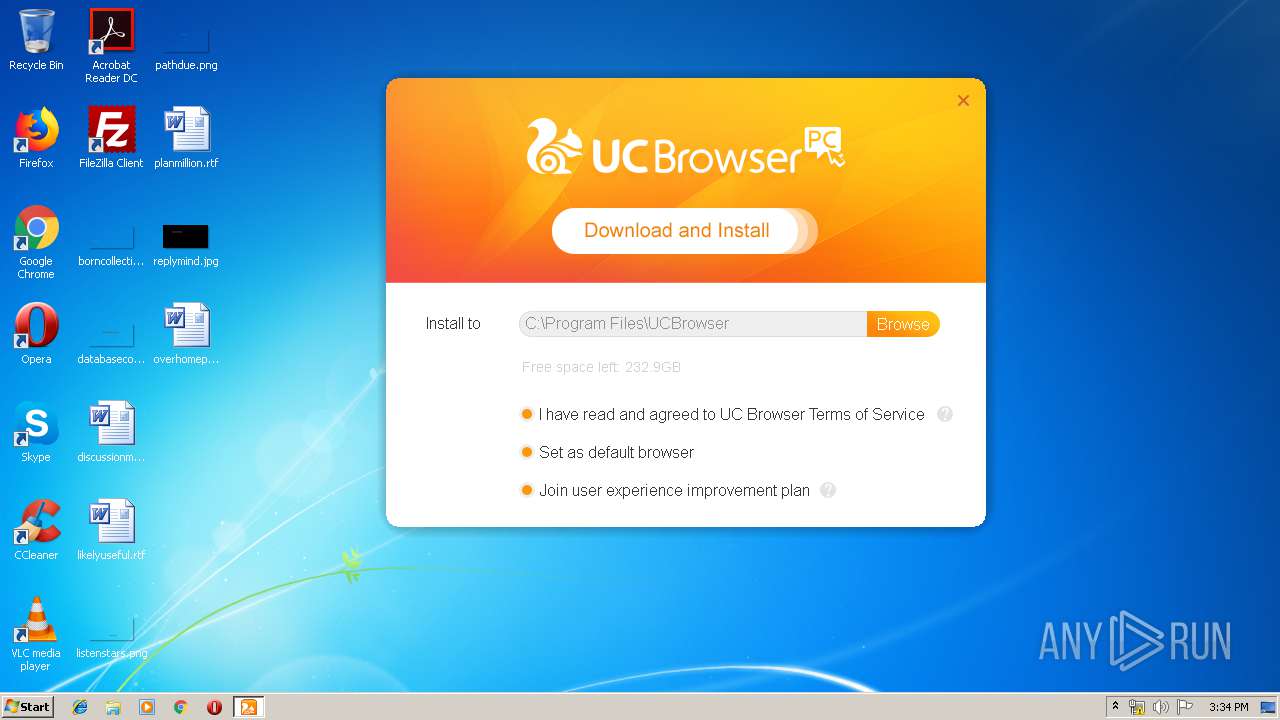
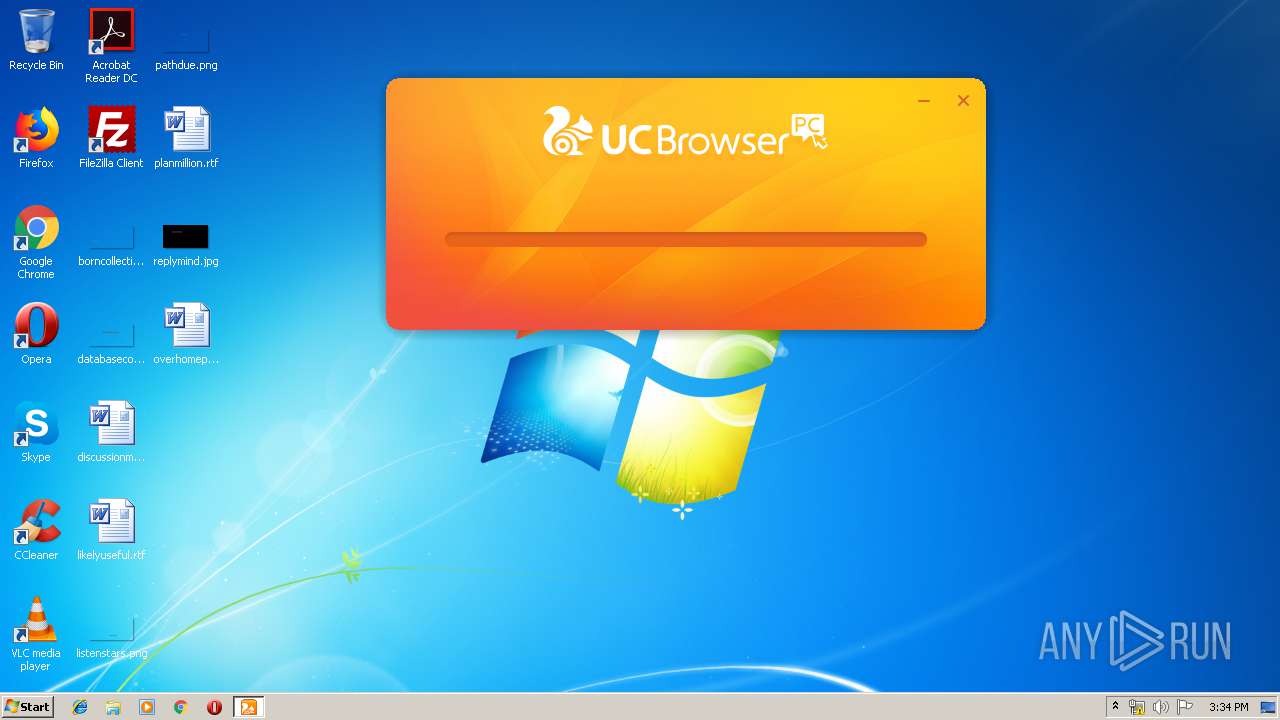
| FileDescription: | UCBrowser Online Installer |
| FileVersion: | 7.0.185.1002 |
| InternalName: | online_installer_exe |
| LegalCopyright: | Copyright 2008-2017 UCWeb Inc. All rights reserved. |
| ProductName: | UC Browser |
| ProductVersion: | 7.0.185.1002 |
| CompanyShortName: | UCWeb Inc. |
| ProductShortName: | UC Browser |
| LastChange: | 80c44ef8676ce2ef96c98d57958e86cc328431ef-bus-1218-185 |
| OfficialBuild: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Dec-2017 05:42:56 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | UCWeb Inc. |
| FileDescription: | UCBrowser Online Installer |
| FileVersion: | 7.0.185.1002 |
| InternalName: | online_installer_exe |
| LegalCopyright: | Copyright 2008-2017 UCWeb Inc. All rights reserved. |
| ProductName: | UC Browser |
| ProductVersion: | 7.0.185.1002 |
| CompanyShortName: | UCWeb Inc. |
| ProductShortName: | UC Browser |
| LastChange: | 80c44ef8676ce2ef96c98d57958e86cc328431ef-bus-1218-185 |
| Official Build: | 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000140 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 20-Dec-2017 05:42:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B8E2B | 0x000B9000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62223 |
.rdata | 0x000BA000 | 0x00022F48 | 0x00023000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.00964 |
.data | 0x000DD000 | 0x00008A44 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.87706 |
.gfids | 0x000E6000 | 0x00000330 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.28892 |
.tls | 0x000E7000 | 0x00000002 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000E8000 | 0x000B7494 | 0x000B7600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.59515 |
.reloc | 0x001A0000 | 0x00006C9C | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.70248 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.55414 | 1072 | Latin 1 / Western European | Chinese - PRC | RT_VERSION |
2 | 5.84529 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.55272 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
8 | 1.57841 | 58 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
127 | 2.44441 | 48 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
129 | 2.3448 | 284 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
376 | 2.85186 | 236 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
377 | 3.10207 | 656 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
378 | 3.08434 | 510 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
379 | 2.97937 | 402 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
GetHandleVerifier | 1 | 0x000263F0 |
curl_easy_cleanup | 2 | 0x00066EF8 |
curl_easy_duphandle | 3 | 0x00066F09 |
curl_easy_escape | 4 | 0x00085A4C |
curl_easy_getinfo | 5 | 0x000670D7 |
curl_easy_init | 6 | 0x000670ED |
curl_easy_pause | 7 | 0x00067124 |
curl_easy_perform | 8 | 0x00067221 |
curl_easy_recv | 9 | 0x000672B8 |
curl_easy_reset | 10 | 0x00067302 |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Users\admin\AppData\Local\Temp\UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe" | C:\Users\admin\AppData\Local\Temp\UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | — | explorer.exe | |||||||||||
User: admin Company: UCWeb Inc. Integrity Level: MEDIUM Description: UCBrowser Online Installer Exit code: 3221226540 Version: 7.0.185.1002 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\stats_uploader.exe" --normal-stats1=https://i18nmmstat.ucweb.com/lv=1.0&encrypt_data=bTkwAjLHpsSuQGAFbC3O3wcNw3U/dQmvkiWuN5oY3CwzJJhp17QKkUQu7i3uvNBT485ZcqWXWvMtkA8kzPDcY4Ddegn+71rYKIHDAb/W3kbl/bpQSTp2McLmmBdUffegO/zrHXpIcBmhpAMQWXGnhBuCcHsdIXRxqJ4tKicOo+Uwl80lZ6cgCB7voWCG8vrF46qELb7CLLxzv7wz+OamYvX3DHOL42SQOk9zzJK1mGFPSVeS4sJ779hIzMpIOvxhYm//hARaOoDQOMWBMwP7RxZ6t48lPTc89SxAi2KjcQ== | C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\stats_uploader.exe | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1732 | "C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\stats_uploader.exe" --normal-stats1=https://i18nmmstat.ucweb.com/lv=1.0&encrypt_data=bTkwAm7A/hpqSRjTKFR2aZ87kym3Y9kDZTq2Oc4zpC7DwTuR7lCqyZDDVpvCURi9e+RJfk29KveJo5f6MKdEmaCFutkel5qoDMA7B5uXtkC9syrs8YSGbbaxQNnArr9yS0DLBSq8UBG1Abu2JdRfOkNgILdFgyTFLHV1FKthi+/wB01FpzegqBpW2baCe6KTOyzUMXZEHLCHMCRdDB0+AAWDLMtbfwRoLtJLOr4IUG+X88c+yljrC3zr1JTUXYQ7woc/lGTy+pD0yT0nV7JT4Q6kp/M98yeAgeuYpdbXtg== | C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\stats_uploader.exe | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3280 | "C:\Users\admin\AppData\Local\Temp\UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe" | C:\Users\admin\AppData\Local\Temp\UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | explorer.exe | ||||||||||||
User: admin Company: UCWeb Inc. Integrity Level: HIGH Description: UCBrowser Online Installer Exit code: 0 Version: 7.0.185.1002 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\stats_uploader.exe" --normal-stats1=https://i18nmmstat.ucweb.com/lv=1.0&encrypt_data=bTkwAgPBAPn/ShrwgytoCOk5l+udYd3FIj3klg09r9VzwCUXE1+TRbnaYT6JQVtRpuZMvZPuYJnNqdWHAvsHpQiP2YYWzTjtTJp6I9mA0S+H/HMu/fr9Jduiv0Bl4/ruF+D0xy7RH69ZF5Oz7JZmBqlWGDTyNkYX52RTBWQgaYomd6tRIkTA1yREvOGgWaVLvBI88Khd9V/+Kw7EeX9Rb41WB0B4YGTrCNSQY/hdctkk2vvz4wk1eIHsPYR8v80l2v17w2Tr0bQYj1l0ttjr8QTa1jENilIP+s6MSFmoYn2F/7g= | C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\stats_uploader.exe | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
193
Read events
125
Write events
68
Delete events
0
Modification events
| (PID) Process: | (3280) UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\UCBrowserPID |
| Operation: | write | Name: | MachineID |
Value: 185e8f2ef2fa4a220c4d6d94e6988a7c | |||
| (PID) Process: | (3280) UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | Key: | HKEY_CURRENT_USER\Software\UCBrowserPID |
| Operation: | write | Name: | MachineID |
Value: 185e8f2ef2fa4a220c4d6d94e6988a7c | |||
| (PID) Process: | (3280) UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\UCBrowserPID |
| Operation: | write | Name: | MachineIDEx |
Value: 96024595e61a5b44e28edf4b3d5551d5v0000002bf42240e | |||
| (PID) Process: | (3280) UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | Key: | HKEY_CURRENT_USER\Software\UCBrowserPID |
| Operation: | write | Name: | MachineIDEx |
Value: 96024595e61a5b44e28edf4b3d5551d5v0000002bf42240e | |||
| (PID) Process: | (1732) stats_uploader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\stats_uploader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1732) stats_uploader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\stats_uploader_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1732) stats_uploader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\stats_uploader_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1732) stats_uploader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\stats_uploader_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1732) stats_uploader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\stats_uploader_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1732) stats_uploader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\stats_uploader_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | stats_uploader.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | — | |
MD5:— | SHA256:— | |||
| 3728 | stats_uploader.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | — | |
MD5:— | SHA256:— | |||
| 3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\installer_url_config.tmp | — | |
MD5:— | SHA256:— | |||
| 3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | C:\Users\admin\AppData\Local\UCBrowser\Online_Downloader\installer_channel.md5.tmp | — | |
MD5:— | SHA256:— | |||
| 1096 | stats_uploader.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | hiv | |
MD5:— | SHA256:— | |||
| 1732 | stats_uploader.exe | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 1732 | stats_uploader.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 1096 | stats_uploader.exe | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 1096 | stats_uploader.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
| 1732 | stats_uploader.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | GET | 302 | 195.27.31.250:80 | http://umpackpc.ucweb.com/pcbrowser_i18n/down.php?id=101&type=zip&pid=4601 | DE | — | — | malicious |
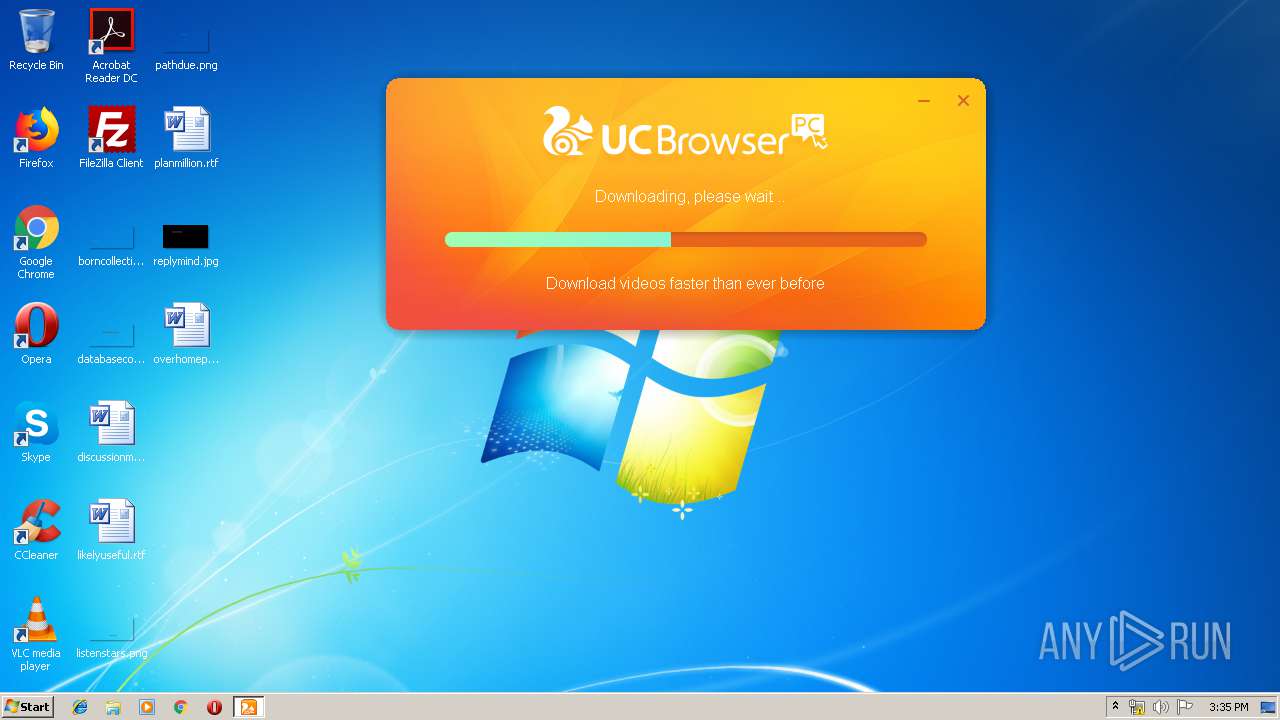
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | GET | — | 2.16.186.106:80 | http://umcdnpc.ucweb.com/down/i18n/35151/4601/UCBrowser_V7.0.185.1002_4601_(Build1801021540)_(en-us).exe.zip | unknown | — | — | whitelisted |
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | GET | 200 | 168.235.203.204:80 | http://ucip.uc.cn/get_ip_attr?type=1&format=0&caller=gj_pcbrowser&key=097a6150b0c772f7952807c0cb48fb86 | US | text | 105 b | unknown |
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | GET | 302 | 195.27.31.250:80 | http://umpackpc.ucweb.com/pcbrowser_i18n/down.php?id=101&type=md5&pid=4601 | DE | — | — | malicious |
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | GET | 200 | 80.231.126.181:80 | http://www.uc123.com/pcbrowser_i18n/downloader.php?pid=4601&version=7.0.185.1002&os=win&arch=x86 | ES | text | 656 b | malicious |
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | GET | 200 | 2.16.186.106:80 | http://umcdnpc.ucweb.com/down/i18n/35151/4601/UCBrowser_V7.0.185.1002_4601_(Build1801021540)_(en-us).exe.md5 | unknown | text | 68 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | 168.235.203.204:80 | ucip.uc.cn | QUANTIL, INC | US | unknown |
3728 | stats_uploader.exe | 168.235.203.193:443 | i18nmmstat.ucweb.com | QUANTIL, INC | US | unknown |
1732 | stats_uploader.exe | 168.235.203.193:443 | i18nmmstat.ucweb.com | QUANTIL, INC | US | unknown |
1096 | stats_uploader.exe | 168.235.203.193:443 | i18nmmstat.ucweb.com | QUANTIL, INC | US | unknown |
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | 80.231.126.181:80 | www.uc123.com | TATA COMMUNICATIONS (AMERICA) INC | ES | malicious |
3280 | UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | 195.27.31.250:80 | umpackpc.ucweb.com | CW Vodafone Group PLC | DE | unknown |
— | — | 2.16.186.106:80 | umcdnpc.ucweb.com | Akamai International B.V. | — | whitelisted |
— | — | 195.27.31.250:80 | umpackpc.ucweb.com | CW Vodafone Group PLC | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ucip.uc.cn |
| unknown |
i18nmmstat.ucweb.com |
| unknown |
www.uc123.com |
| malicious |
umpackpc.ucweb.com |
| unknown |
umcdnpc.ucweb.com |
| whitelisted |
Threats
Process | Message |
|---|---|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:2336:0430/153415:INFO:wow_locale_util.cc(118)] Country Code: US
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3148:0430/153415:WARNING:wow_install_downloader_proxy.cc(190)] clear temp download data
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3456:0430/153415:ERROR:wow_wmi_utils.cc(149)] Failed to initialize security. result = -2147417831
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3148:0430/153415:INFO:wow_stats_helper.cc(325)] bluesky.1.2.3.1.1?cache=942889000&ka=&kb=185e8f2ef2fa4a220c4d6d94e6988a7c&kc=96024595e61a5b44e28edf4b3d5551d5v0000002bf42240e&firstpid=4595&bid=35151&os_ver=6.1.7601_SP1&ver=7.0.185.1002&installpid=4601&lang=en-US
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3148:0430/153415:INFO:wow_stats_helper.cc(329)] https://i18nmmstat.ucweb.com/lv=1.0&encrypt_data=bTkwAm7A/hpqSRjTKFR2aZ87kym3Y9kDZTq2Oc4zpC7DwTuR7lCqyZDDVpvCURi9e+RJfk29KveJo5f6MKdEmaCFutkel5qoDMA7B5uXtkC9syrs8YSGbbaxQNnArr9yS0DLBSq8UBG1Abu2JdRfOkNgILdFgyTFLHV1FKthi+/wB01FpzegqBpW2baCe6KTOyzUMXZEHLCHMCRdDB0+AAWDLMtbfwRoLtJLOr4IUG+X88c+yljrC3zr1JTUXYQ7woc/lGTy+pD0yT0nV7JT4Q6kp/M98yeAgeuYpdbXtg==
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3148:0430/153415:INFO:wow_stats_helper.cc(325)] bluesky.1.2.3.1.15?cache=942921000&ka=&kb=185e8f2ef2fa4a220c4d6d94e6988a7c&kc=96024595e61a5b44e28edf4b3d5551d5v0000002bf42240e&firstpid=4595&bid=35151&os_ver=6.1.7601_SP1&ver=7.0.185.1002&from=1&avproducts=&lang=en-US
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3148:0430/153415:INFO:wow_stats_helper.cc(329)] https://i18nmmstat.ucweb.com/lv=1.0&encrypt_data=bTkwAgPBAPn/ShrwgytoCOk5l+udYd3FIj3klg09r9VzwCUXE1+TRbnaYT6JQVtRpuZMvZPuYJnNqdWHAvsHpQiP2YYWzTjtTJp6I9mA0S+H/HMu/fr9Jduiv0Bl4/ruF+D0xy7RH69ZF5Oz7JZmBqlWGDTyNkYX52RTBWQgaYomd6tRIkTA1yREvOGgWaVLvBI88Khd9V/+Kw7EeX9Rb41WB0B4YGTrCNSQY/hdctkk2vvz4wk1eIHsPYR8v80l2v17w2Tr0bQYj1l0ttjr8QTa1jENilIP+s6MSFmoYn2F/7g=
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3148:0430/153424:INFO:wow_stats_helper.cc(325)] bluesky.1.2.3.1.2?cache=951811000&ka=&kb=185e8f2ef2fa4a220c4d6d94e6988a7c&kc=96024595e61a5b44e28edf4b3d5551d5v0000002bf42240e&firstpid=4595&bid=35151&os_ver=6.1.7601_SP1&ver=7.0.185.1002&installpid=4601&lang=en-US
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:3148:0430/153424:INFO:wow_stats_helper.cc(329)] https://i18nmmstat.ucweb.com/lv=1.0&encrypt_data=bTkwAjLHpsSuQGAFbC3O3wcNw3U/dQmvkiWuN5oY3CwzJJhp17QKkUQu7i3uvNBT485ZcqWXWvMtkA8kzPDcY4Ddegn+71rYKIHDAb/W3kbl/bpQSTp2McLmmBdUffegO/zrHXpIcBmhpAMQWXGnhBuCcHsdIXRxqJ4tKicOo+Uwl80lZ6cgCB7voWCG8vrF46qELb7CLLxzv7wz+OamYvX3DHOL42SQOk9zzJK1mGFPSVeS4sJ779hIzMpIOvxhYm//hARaOoDQOMWBMwP7RxZ6t48lPTc89SxAi2KjcQ==
|
UCBrowser_V7.0.185.1002_windows_pf101_(Build18010215).exe | [3280:4020:0430/153424:INFO:wow_install_downloader_proxy.cc(425)] Config url: http://www.uc123.com/pcbrowser_i18n/downloader.php?pid=4601&version=7.0.185.1002&os=win&arch=x86
|