| File name: | 475cdd21589ec3f5791d2368c48a6eca.exe |
| Full analysis: | https://app.any.run/tasks/ed198472-c81a-4603-9636-37acc4a8e00b |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | May 16, 2025, 01:46:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 475CDD21589EC3F5791D2368C48A6ECA |
| SHA1: | 3CBBBF16F27015004671A0335B2F7D64BC30729B |
| SHA256: | 769F06587A7BA1FD224022495F4C9743A8070A54A1781CC551AB0068943CE17B |
| SSDEEP: | 98304:Oyi35NN4SlKuN7F7xmJ52hZLnfNNMk9aVPen20kkoyukPqjph8pYVDlNUch9s+hv:gyNkU |
MALICIOUS
DCRAT mutex has been found
- blockfontRuntimedll.exe (PID: 4988)
- explorer.exe (PID: 6744)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 1196)
DARKCRYSTAL has been detected (SURICATA)
- explorer.exe (PID: 6744)
DCRAT has been detected (YARA)
- explorer.exe (PID: 6744)
Connects to the CnC server
- explorer.exe (PID: 6744)
SUSPICIOUS
Runs shell command (SCRIPT)
- wscript.exe (PID: 1196)
Executable content was dropped or overwritten
- 475cdd21589ec3f5791d2368c48a6eca.exe (PID: 5124)
- blockfontRuntimedll.exe (PID: 4988)
- explorer.exe (PID: 6744)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1196)
- blockfontRuntimedll.exe (PID: 4988)
Reads security settings of Internet Explorer
- 475cdd21589ec3f5791d2368c48a6eca.exe (PID: 5124)
- blockfontRuntimedll.exe (PID: 4988)
Executing commands from a ".bat" file
- blockfontRuntimedll.exe (PID: 4988)
- wscript.exe (PID: 1196)
Starts application with an unusual extension
- cmd.exe (PID: 6388)
Reads the date of Windows installation
- blockfontRuntimedll.exe (PID: 4988)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 6388)
The process creates files with name similar to system file names
- blockfontRuntimedll.exe (PID: 4988)
There is functionality for taking screenshot (YARA)
- explorer.exe (PID: 6744)
Connects to the server without a host name
- explorer.exe (PID: 6744)
INFO
Process checks computer location settings
- 475cdd21589ec3f5791d2368c48a6eca.exe (PID: 5124)
- blockfontRuntimedll.exe (PID: 4988)
Checks supported languages
- 475cdd21589ec3f5791d2368c48a6eca.exe (PID: 5124)
- blockfontRuntimedll.exe (PID: 4988)
- chcp.com (PID: 6264)
- explorer.exe (PID: 6744)
Drops encrypted VBS script (Microsoft Script Encoder)
- 475cdd21589ec3f5791d2368c48a6eca.exe (PID: 5124)
Reads the computer name
- 475cdd21589ec3f5791d2368c48a6eca.exe (PID: 5124)
- blockfontRuntimedll.exe (PID: 4988)
- explorer.exe (PID: 6744)
Create files in a temporary directory
- blockfontRuntimedll.exe (PID: 4988)
Changes the display of characters in the console
- cmd.exe (PID: 6388)
Reads the machine GUID from the registry
- explorer.exe (PID: 6744)
- blockfontRuntimedll.exe (PID: 4988)
Reads Environment values
- explorer.exe (PID: 6744)
- blockfontRuntimedll.exe (PID: 4988)
Failed to create an executable file in Windows directory
- blockfontRuntimedll.exe (PID: 4988)
Checks proxy server information
- explorer.exe (PID: 6744)
Found Base64 encoded reference to AntiVirus WMI classes (YARA)
- explorer.exe (PID: 6744)
Disables trace logs
- explorer.exe (PID: 6744)
.NET Reactor protector has been detected
- explorer.exe (PID: 6744)
Found Base64 encoded reference to WMI classes (YARA)
- explorer.exe (PID: 6744)
Reads the software policy settings
- slui.exe (PID: 5408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(6744) explorer.exe
C2 (1)http://77.246.158.103/secureTrafficPublic
Options
Version5.0.1
Plugins (7)TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDANLV72QAAAAAAAAAAOAAAiELAQgAAJAAAAAGAAAAAAAAvq4AAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAA/8AAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAC82/2QAAAAAAAAAAOAAAiELAQgAAHgAAAAGAAAAAAAALpYAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAPMkAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMvY72QAAAAAAAAAAOAAAiELAQgAAIYAAAAGAAAAAAAAHqUAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAhvEAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAGve72QAAAAAAAAAAOAAAiELAQgAAHoAAAAGAAAAAAAAvpkAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAA3OEAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMIE8GQAAAAAAAAAAOAAAiELAQgAAHwAAAAGAAAAAAAArpoAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAqtoAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAOjQ72QAAAAAAAAAAOAAAiELAQgAAHYAAAAGAAAAAAAAbpQAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAACOMAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDACLT72QAAAAAAAAAAOAAAiELAQgAAJYAAAAGAAAAAAAAbrUAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAEvAAAAMAQIUA...
C2 (1)http://77.246.158.103/secureTrafficPublic
Options
Version5.0.1
Plugins (10)TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDANLV72QAAAAAAAAAAOAAAiELAQgAAJAAAAAGAAAAAAAAvq4AAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAA/8AAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAC82/2QAAAAAAAAAAOAAAiELAQgAAHgAAAAGAAAAAAAALpYAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAPMkAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMvY72QAAAAAAAAAAOAAAiELAQgAAIYAAAAGAAAAAAAAHqUAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAhvEAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMzf72QAAAAAAAAAAOAAIiALAQgAAAoBAAAGAAAAAAAALikBAAAgAAAAQAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAQAAAgAAOPMBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAAKX/2QAAAAAAAAAAOAAIiALAQgAAEYBAAAGAAAAAAAA7mUBAAAgAAAAgAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAQAAAgAAm0ACAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAGve72QAAAAAAAAAAOAAAiELAQgAAHoAAAAGAAAAAAAAvpkAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAA3OEAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMIE8GQAAAAAAAAAAOAAAiELAQgAAHwAAAAGAAAAAAAArpoAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAqtoAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAOjQ72QAAAAAAAAAAOAAAiELAQgAAHYAAAAGAAAAAAAAbpQAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAACOMAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDALI7+mQAAAAAAAAAAOAAIiALAQgAAAgBAAAGAAAAAAAAricBAAAgAAAAQAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAQAAAgAArNABAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDACLT72QAAAAAAAAAAOAAAiELAQgAAJYAAAAGAAAAAAAAbrUAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAEvAAAAMAQIUA...
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
143
Monitored processes
13
Malicious processes
6
Suspicious processes
0
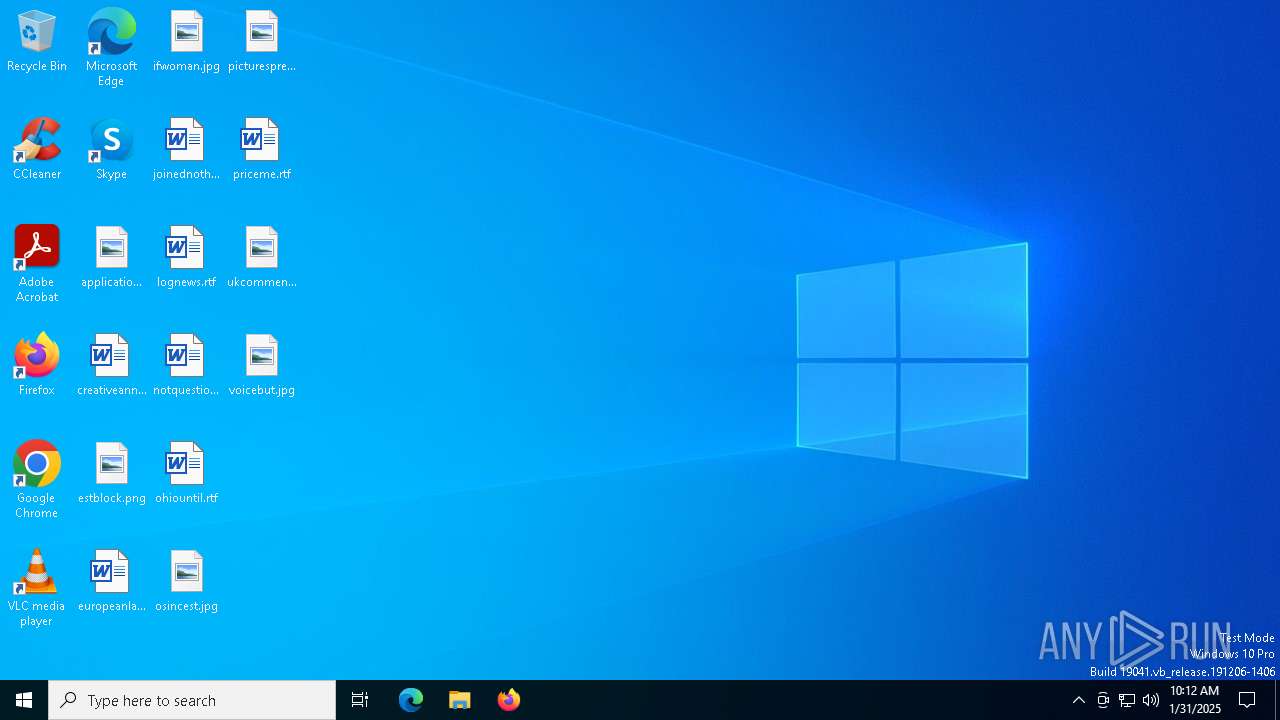
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\WINDOWS\System32\WScript.exe" "C:\msWeb\wpdCZCETh32gQqESyOXCWbX2UiHtTSMLrQcx4mRmEDMwD6qL8ItXJ.vbe" | C:\Windows\SysWOW64\wscript.exe | — | 475cdd21589ec3f5791d2368c48a6eca.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4976 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4988 | "C:\msWeb/blockfontRuntimedll.exe" | C:\msWeb\blockfontRuntimedll.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 5124 | "C:\Users\admin\AppData\Local\Temp\475cdd21589ec3f5791d2368c48a6eca.exe" | C:\Users\admin\AppData\Local\Temp\475cdd21589ec3f5791d2368c48a6eca.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5408 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5640 | C:\WINDOWS\system32\cmd.exe /c ""C:\msWeb\cSny31DvJcVjiLKtwoEJpFnfWAumM1nKzbjszpQ58fUy8Cx59UJrRmMcOJVX.bat" " | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6132 | w32tm /stripchart /computer:localhost /period:5 /dataonly /samples:2 | C:\Windows\System32\w32tm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Time Service Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 585
Read events
4 568
Write events
17
Delete events
0
Modification events
| (PID) Process: | (5124) 475cdd21589ec3f5791d2368c48a6eca.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (4988) blockfontRuntimedll.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\51f002018f5e57dc083d3558378de6011e8402a8 |
| Operation: | write | Name: | fb15565e9affefe97a5a3d78dba9a4f1d97c07c9 |
Value: H4sIAAAAAAAEAItWcraKicktDk9NiolJycnJyC8u0UutSFXSQZbwTMlJxRRNrSjIyS9KLcKU8U9Ly0xOdc7JTM4OyQ8qzcNUkZafV5JSVIbduqSc/ORskAqg1pLM3FSgu8CKYgHsX+YIrgAAAA== | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6744) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\explorer_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
30
Suspicious files
1
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4988 | blockfontRuntimedll.exe | C:\Users\admin\Desktop\cVSihfwQ.log | executable | |
MD5:51B1964F31C557AE8C2B01EA164ABD9F | SHA256:AF584F142A9A5A79355B212F8D7A2E3793E33FF23D50FDE591FB2F3E49BF308C | |||
| 4988 | blockfontRuntimedll.exe | C:\Users\admin\Desktop\uhunBBRf.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
| 5124 | 475cdd21589ec3f5791d2368c48a6eca.exe | C:\msWeb\blockfontRuntimedll.exe | executable | |
MD5:06AC26E7B684E8DFD7A4CFF368ACB9C4 | SHA256:24906B13DE83340376A8CB70AF59133A0172A582E864C38150ECFF5E59657B5F | |||
| 4988 | blockfontRuntimedll.exe | C:\Users\admin\Desktop\KIqdNJbB.log | executable | |
MD5:F4B38D0F95B7E844DD288B441EBC9AAF | SHA256:AAB95596475CA74CEDE5BA50F642D92FA029F6F74F6FAEAE82A9A07285A5FB97 | |||
| 4988 | blockfontRuntimedll.exe | C:\msWeb\fontdrvhost.exe | executable | |
MD5:06AC26E7B684E8DFD7A4CFF368ACB9C4 | SHA256:24906B13DE83340376A8CB70AF59133A0172A582E864C38150ECFF5E59657B5F | |||
| 4988 | blockfontRuntimedll.exe | C:\Users\admin\Desktop\ypswWTLa.log | executable | |
MD5:0D323E1CACEA89CAA5DDEAF2F37BCA69 | SHA256:873E7688D95DCAA5468BF94063A94C548EF0D8BE9D4111F1917DA482DBC2A64C | |||
| 4988 | blockfontRuntimedll.exe | C:\msWeb\OfficeClickToRun.exe | executable | |
MD5:06AC26E7B684E8DFD7A4CFF368ACB9C4 | SHA256:24906B13DE83340376A8CB70AF59133A0172A582E864C38150ECFF5E59657B5F | |||
| 4988 | blockfontRuntimedll.exe | C:\Users\admin\Desktop\jSGiKurE.log | executable | |
MD5:E84DCD8370FAC91DE71DEF8DCF09BFEC | SHA256:DD7AC164E789CAD96D30930EFE9BBA99698473EDEA38252C2C0EA44043FB1DB5 | |||
| 4988 | blockfontRuntimedll.exe | C:\Users\admin\Desktop\oGYgmqGt.log | executable | |
MD5:2D6975FD1CC3774916D8FF75C449EE7B | SHA256:75CE6EB6CDDD67D47FB7C5782F45FDC497232F87A883650BA98679F92708A986 | |||
| 4988 | blockfontRuntimedll.exe | C:\Users\admin\Desktop\nrqGCVxv.log | executable | |
MD5:16B480082780CC1D8C23FB05468F64E7 | SHA256:7A080D8BD178EC02C7F39F7F941479074C450C4FDD8E963C993D2FB5537C7708 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
97
TCP/UDP connections
24
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6744 | explorer.exe | POST | 200 | 77.246.158.103:80 | http://77.246.158.103/secureTrafficPublic.php | unknown | — | — | malicious |
6744 | explorer.exe | POST | 200 | 77.246.158.103:80 | http://77.246.158.103/secureTrafficPublic.php | unknown | — | — | malicious |
6744 | explorer.exe | POST | 200 | 77.246.158.103:80 | http://77.246.158.103/secureTrafficPublic.php | unknown | — | — | malicious |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6744 | explorer.exe | POST | 200 | 77.246.158.103:80 | http://77.246.158.103/secureTrafficPublic.php | unknown | — | — | malicious |
6744 | explorer.exe | POST | 200 | 77.246.158.103:80 | http://77.246.158.103/secureTrafficPublic.php | unknown | — | — | malicious |
6068 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6744 | explorer.exe | POST | 200 | 77.246.158.103:80 | http://77.246.158.103/secureTrafficPublic.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2432 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6744 | explorer.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
6744 | explorer.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |