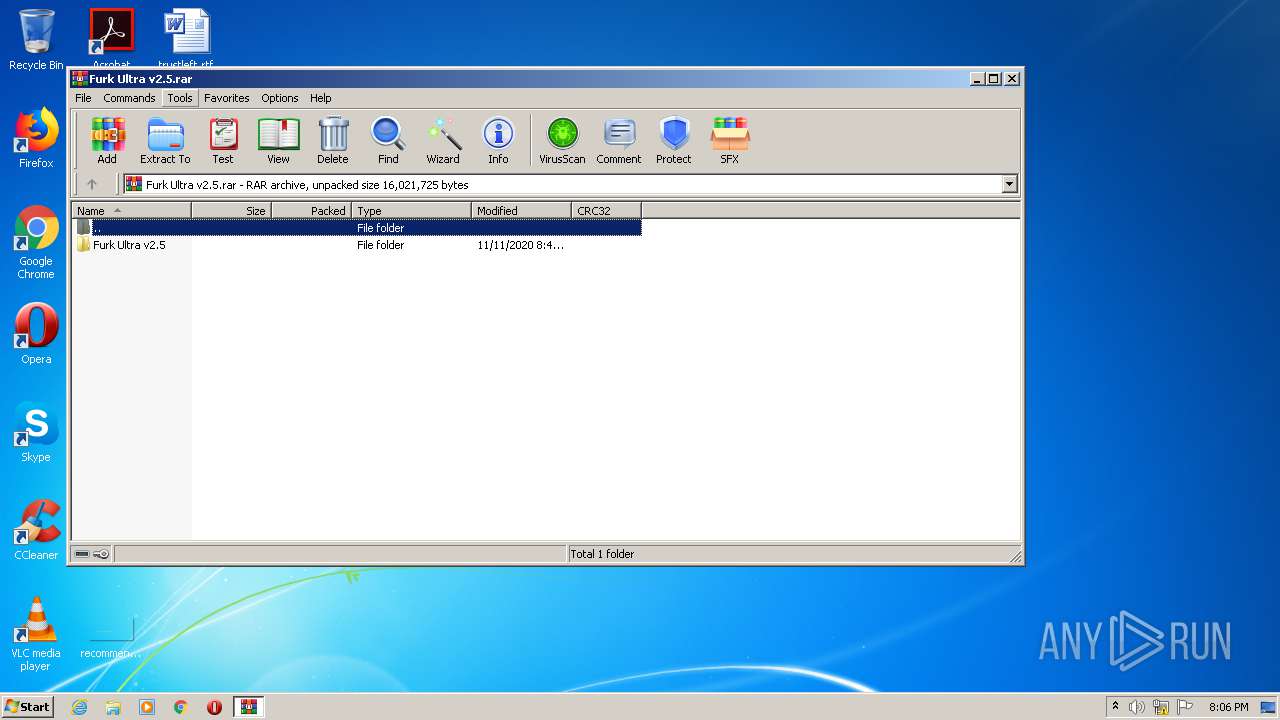
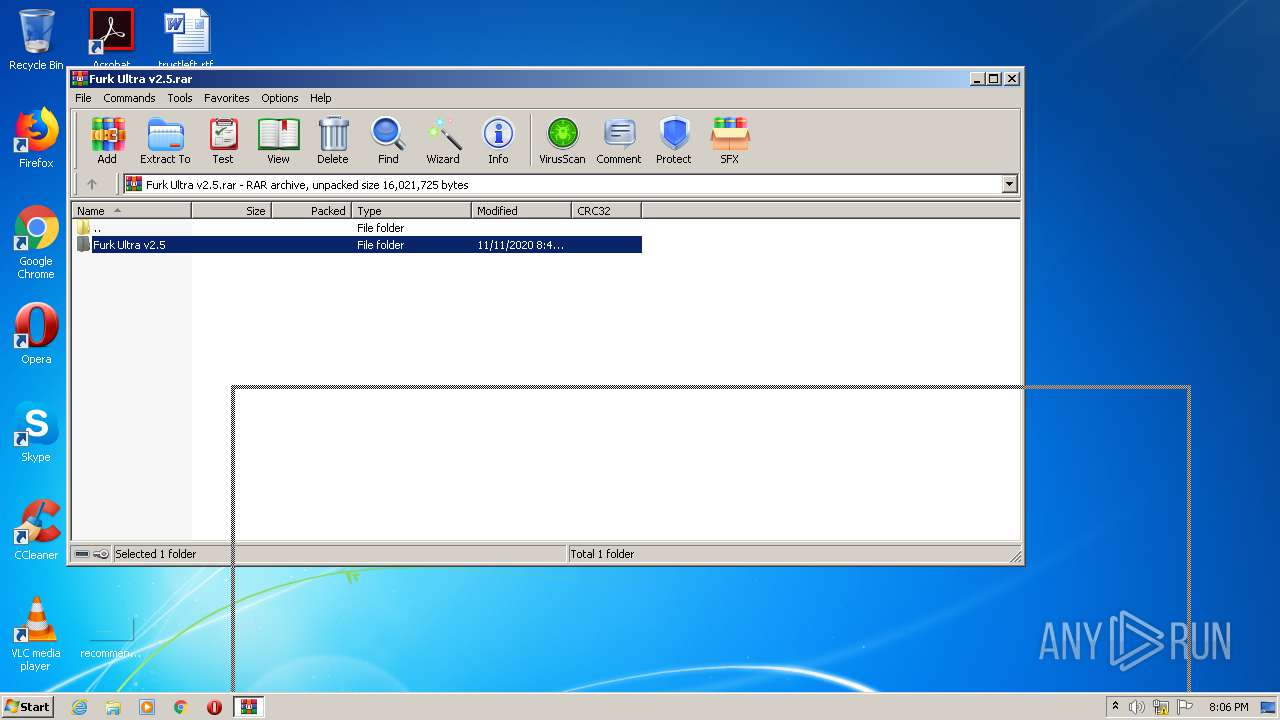
| File name: | Furk Ultra v2.5.rar |
| Full analysis: | https://app.any.run/tasks/299e2bb9-61f9-4f45-8ec6-e13ee7d3cfa9 |
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2020, 20:06:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2B8D583B912FE125C43DC90011F742BB |
| SHA1: | 9DE3C0E073FFF93D1A655D11A5FFAC1A9FC72232 |
| SHA256: | 768B2C490E8F8D515EC8BAA01AF9A39722711C6499A2C07A03D0EFD0704EFAB8 |
| SSDEEP: | 196608:mFQALMpYyIOyY5r0WfbPxkQu3Jd551SnvBhk5T87IGjd0ZH4+:mFtLqYmygrPpkQu31Ai5T87R0tl |
MALICIOUS
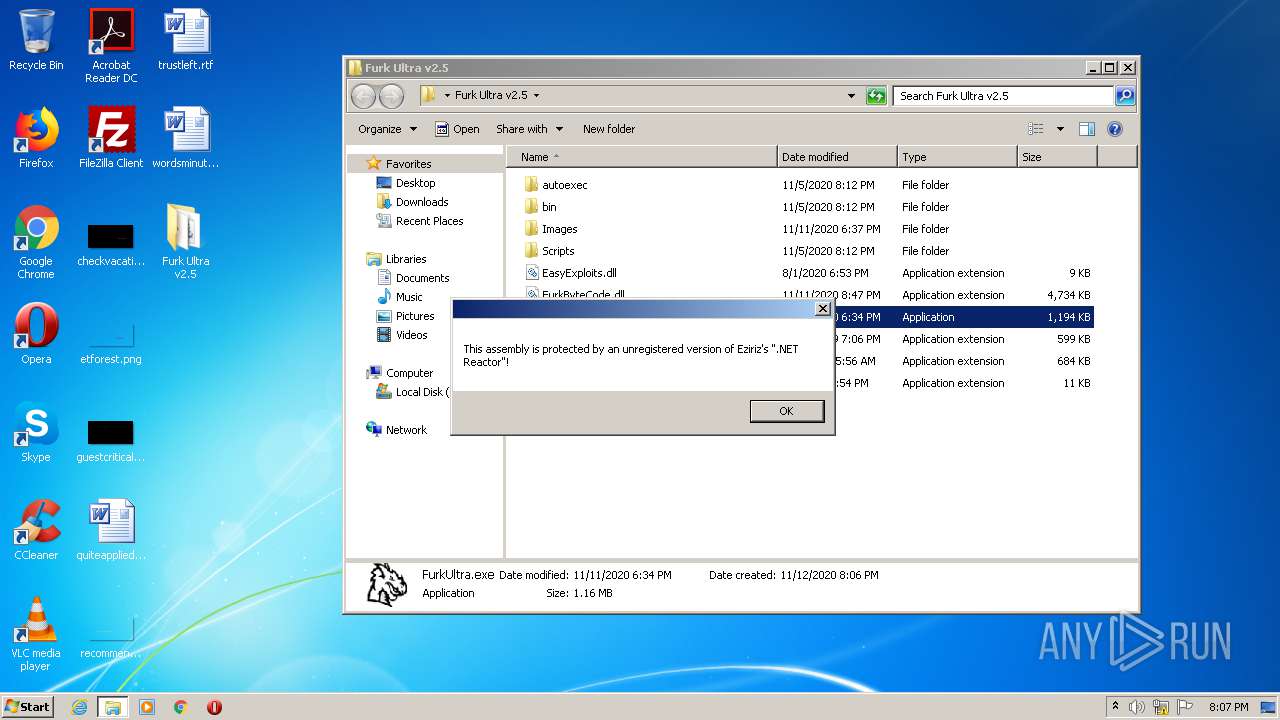
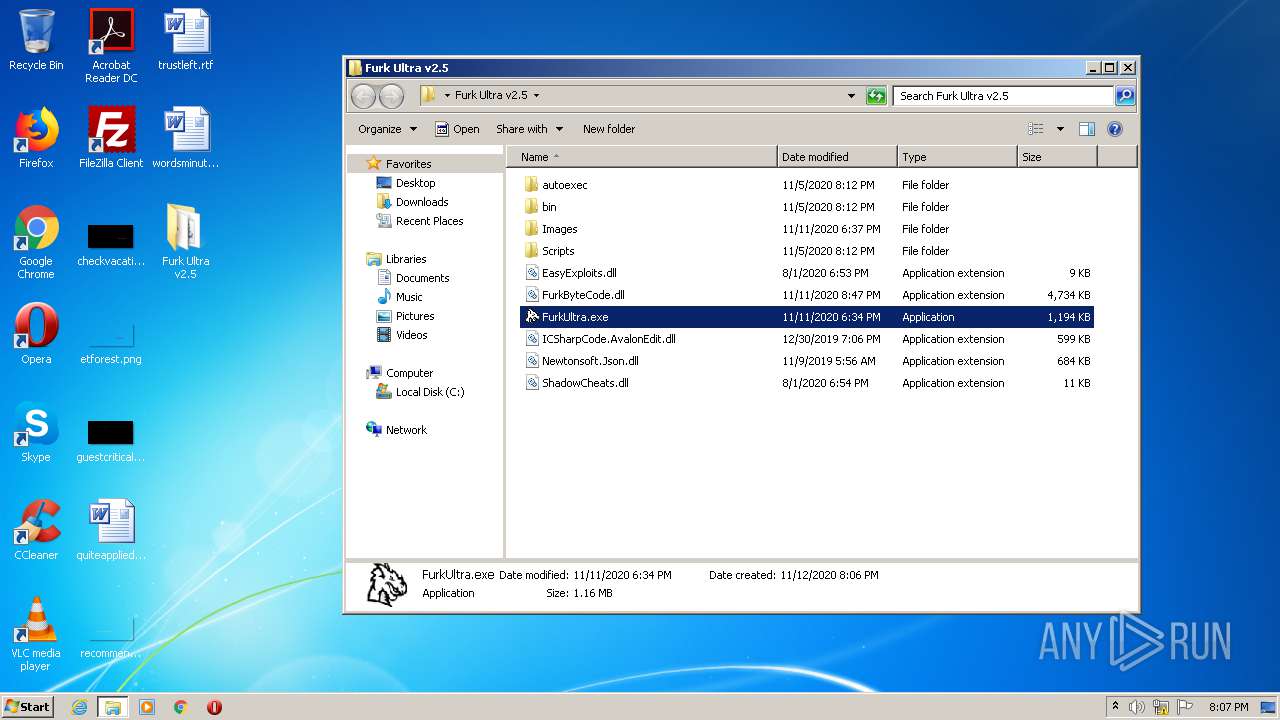
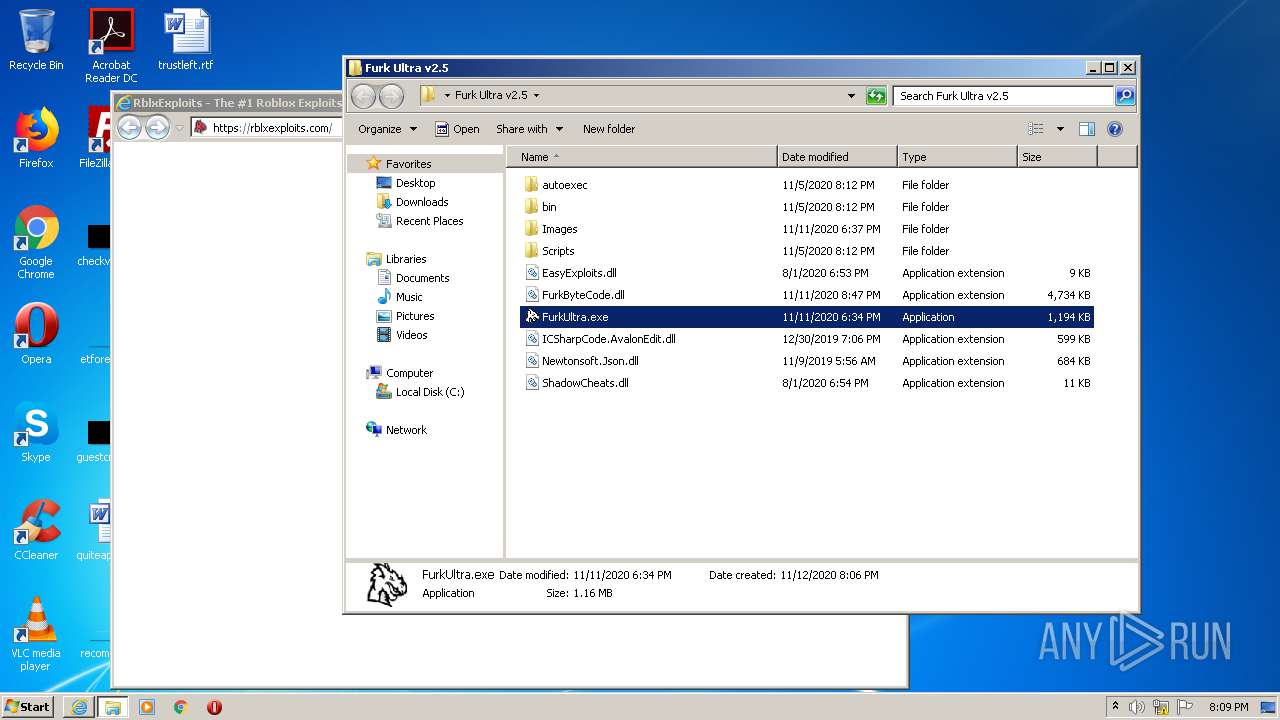
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3412)
- FurkUltra.exe (PID: 3272)
- FurkUltra.exe (PID: 3196)
Application was dropped or rewritten from another process
- FurkUltra.exe (PID: 3272)
- FurkUltra.exe (PID: 3196)
SUSPICIOUS
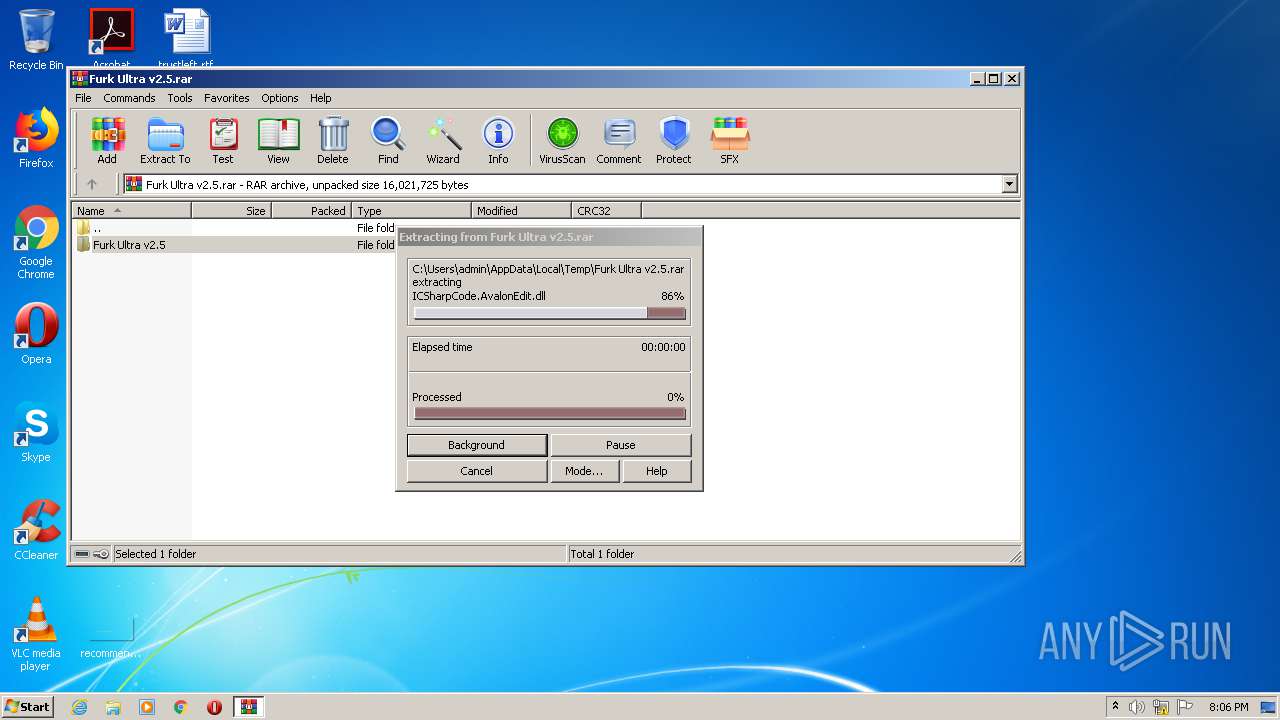
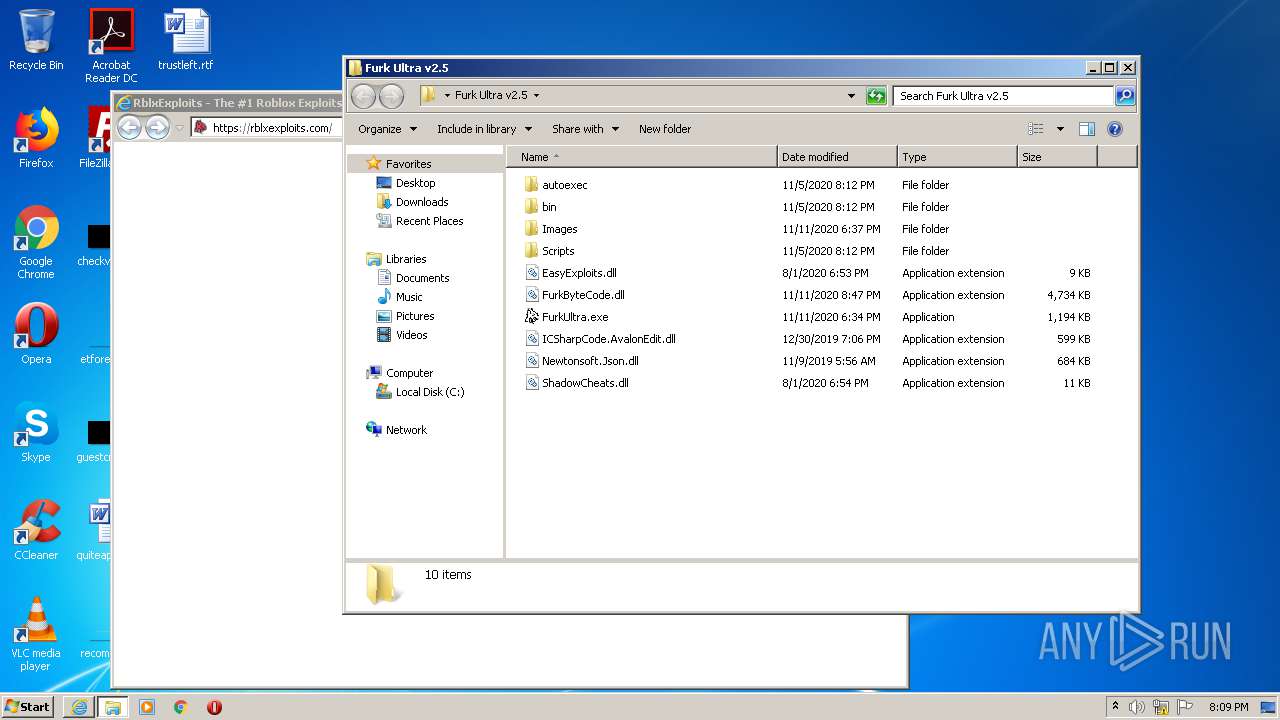
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2940)
Reads Environment values
- FurkUltra.exe (PID: 3272)
- FurkUltra.exe (PID: 3196)
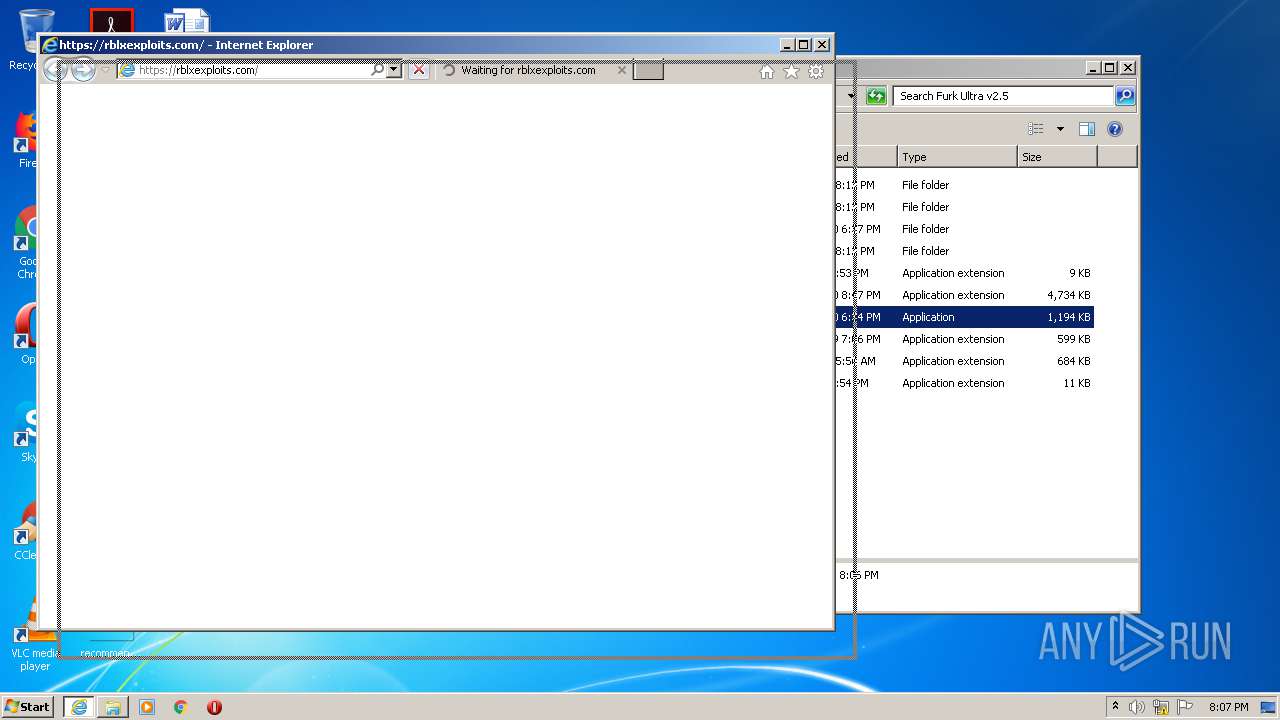
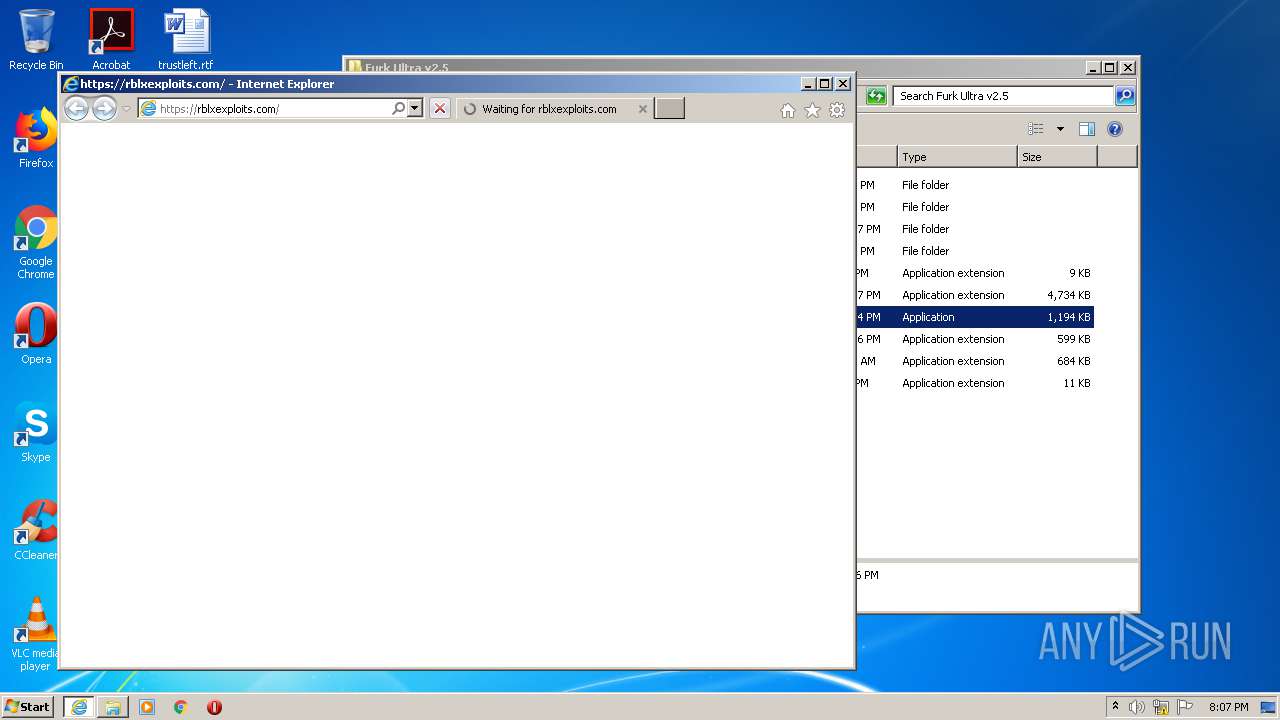
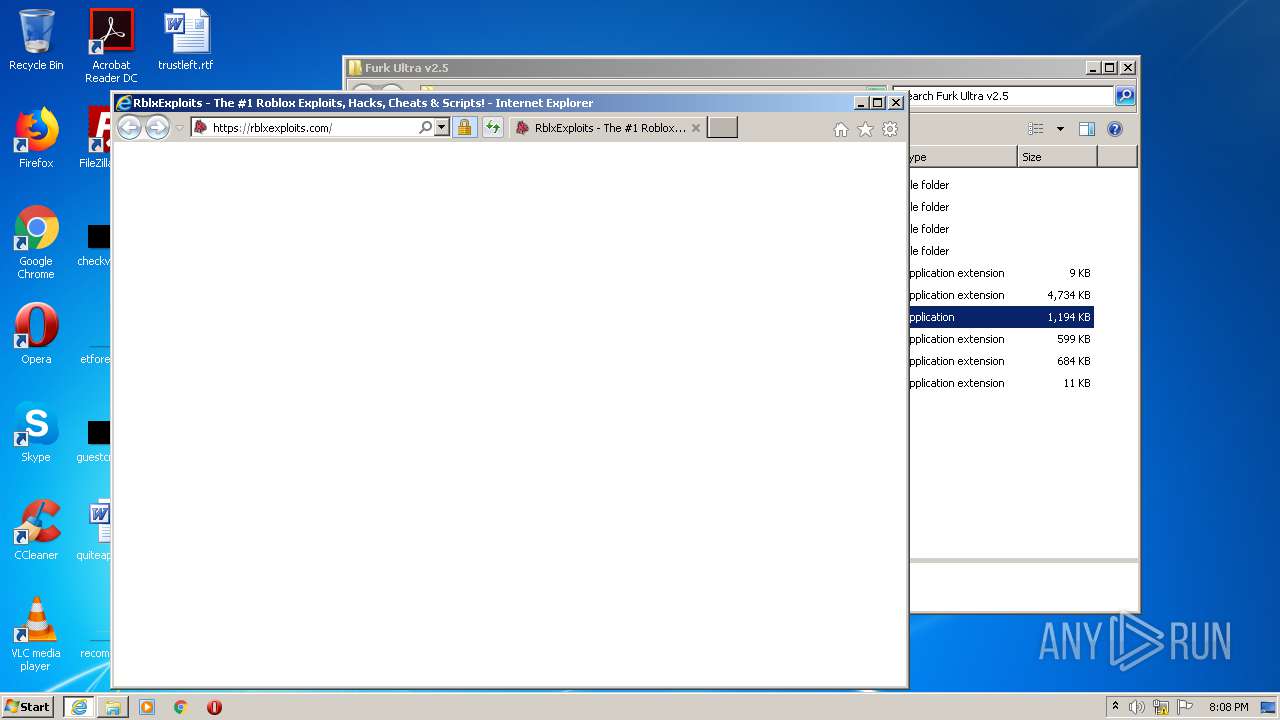
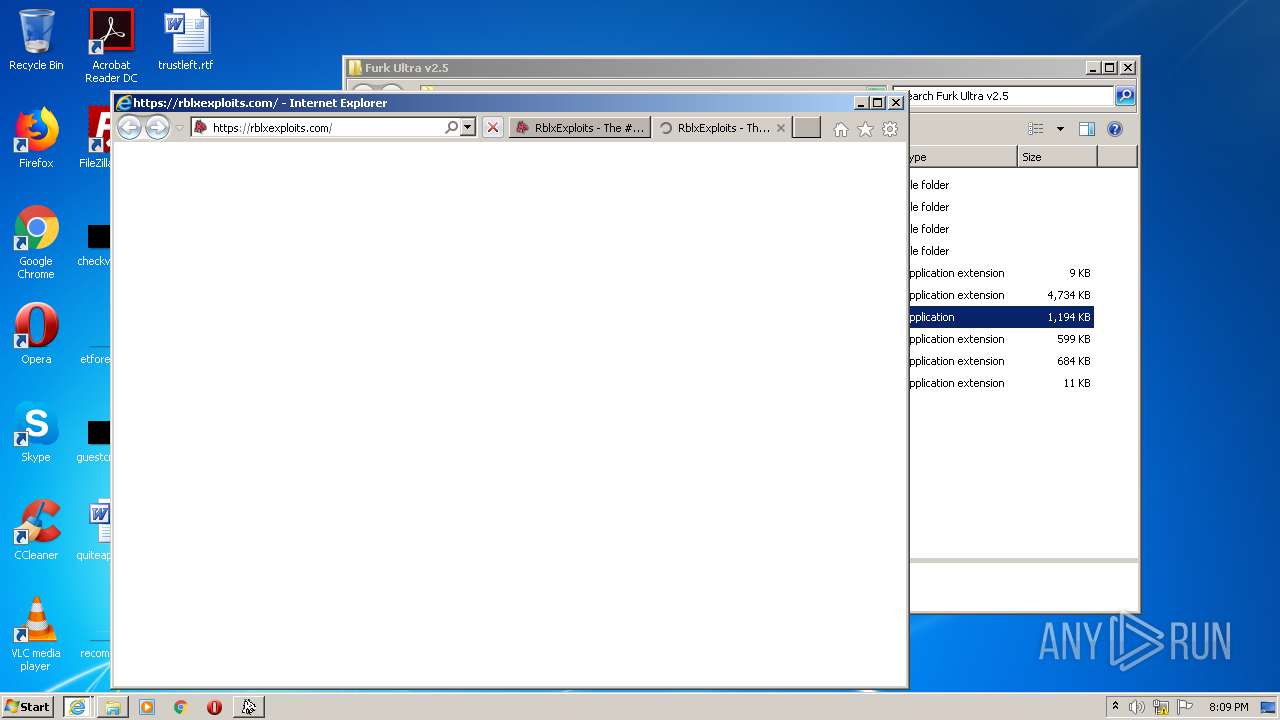
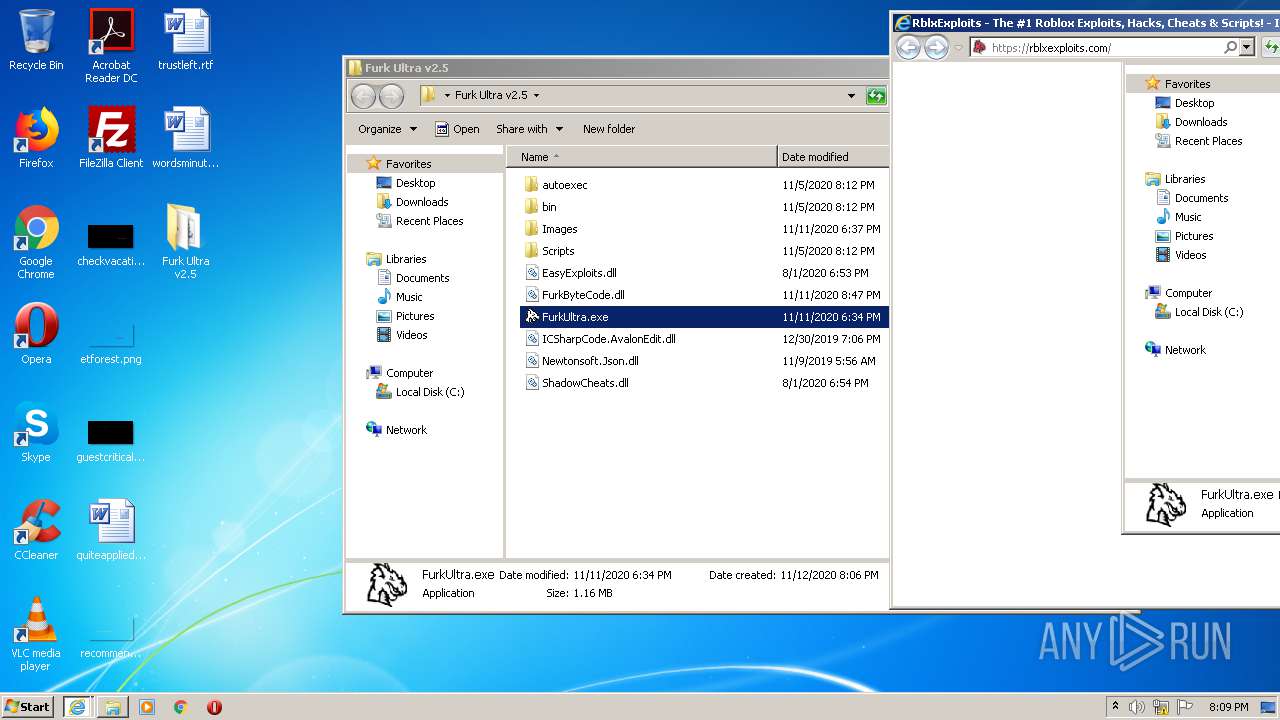
Starts Internet Explorer
- FurkUltra.exe (PID: 3272)
INFO
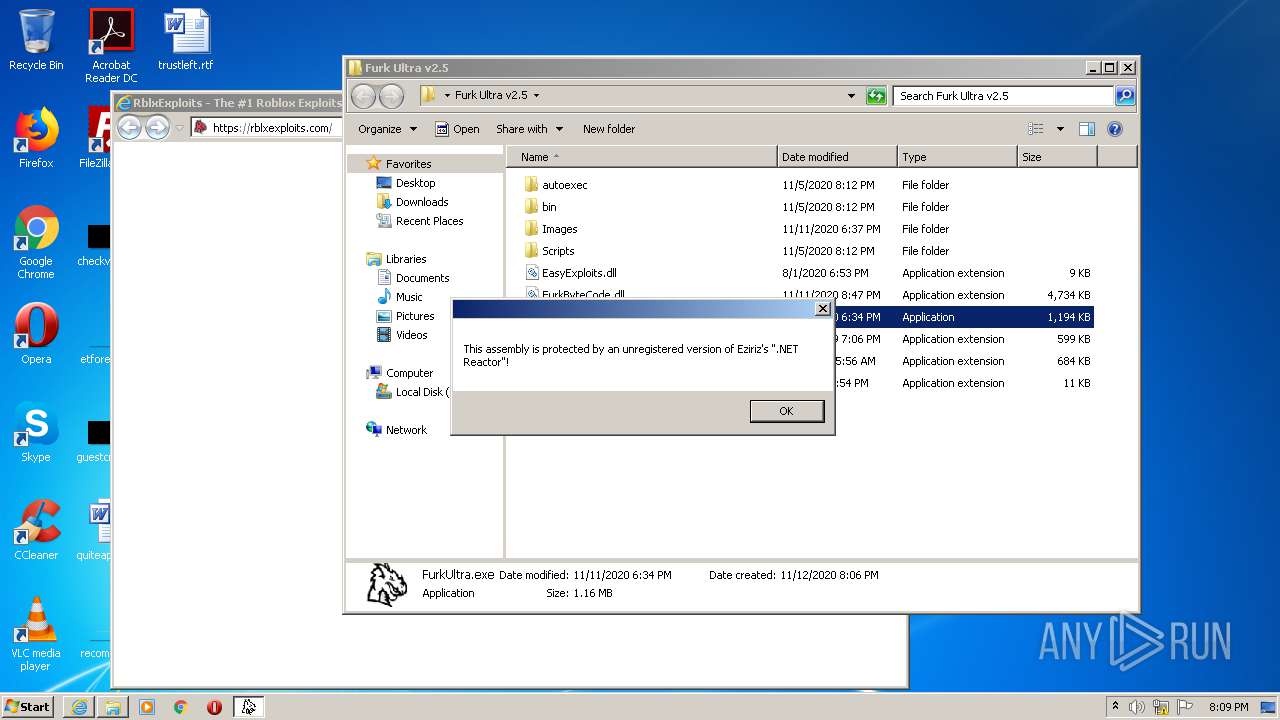
Manual execution by user
- FurkUltra.exe (PID: 3272)
- FurkUltra.exe (PID: 3196)
Reads Internet Cache Settings
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 4024)
Reads settings of System Certificates
- FurkUltra.exe (PID: 3272)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 4024)
Changes internet zones settings
- iexplore.exe (PID: 2972)
Reads internet explorer settings
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 4024)
Application launched itself
- iexplore.exe (PID: 2972)
Creates files in the user directory
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2972)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2972)
Changes settings of System certificates
- iexplore.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
43
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
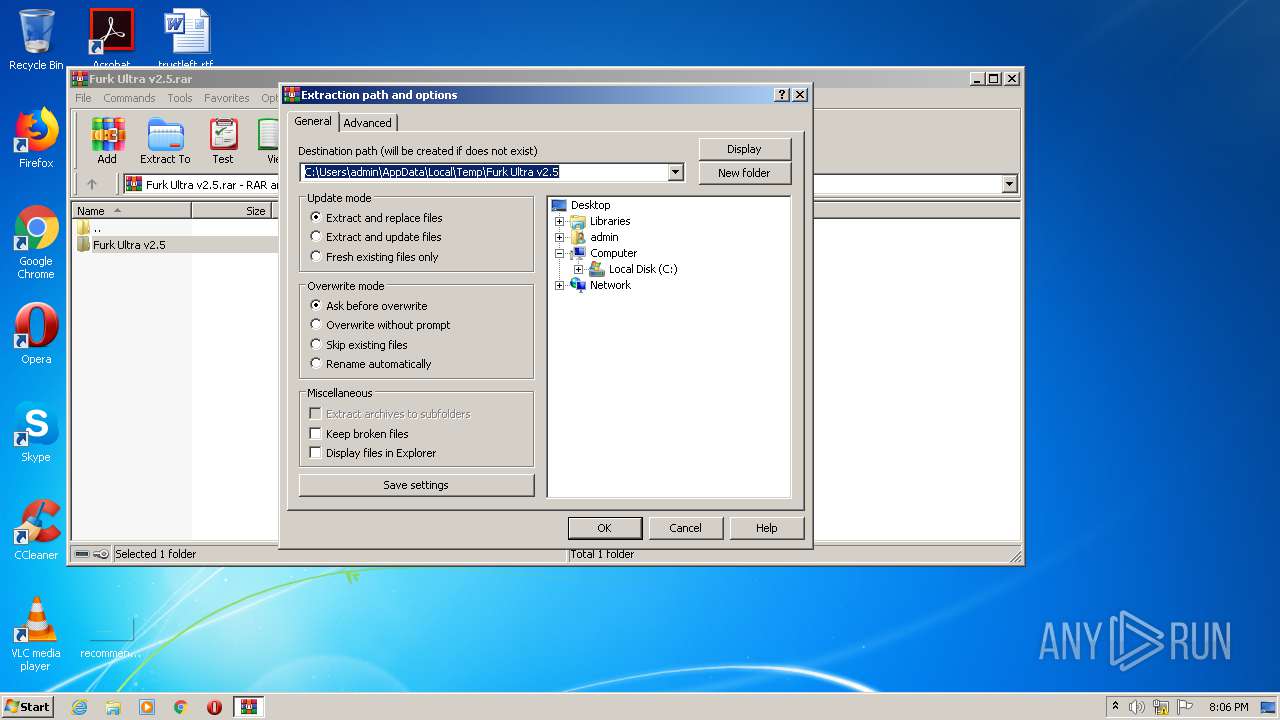
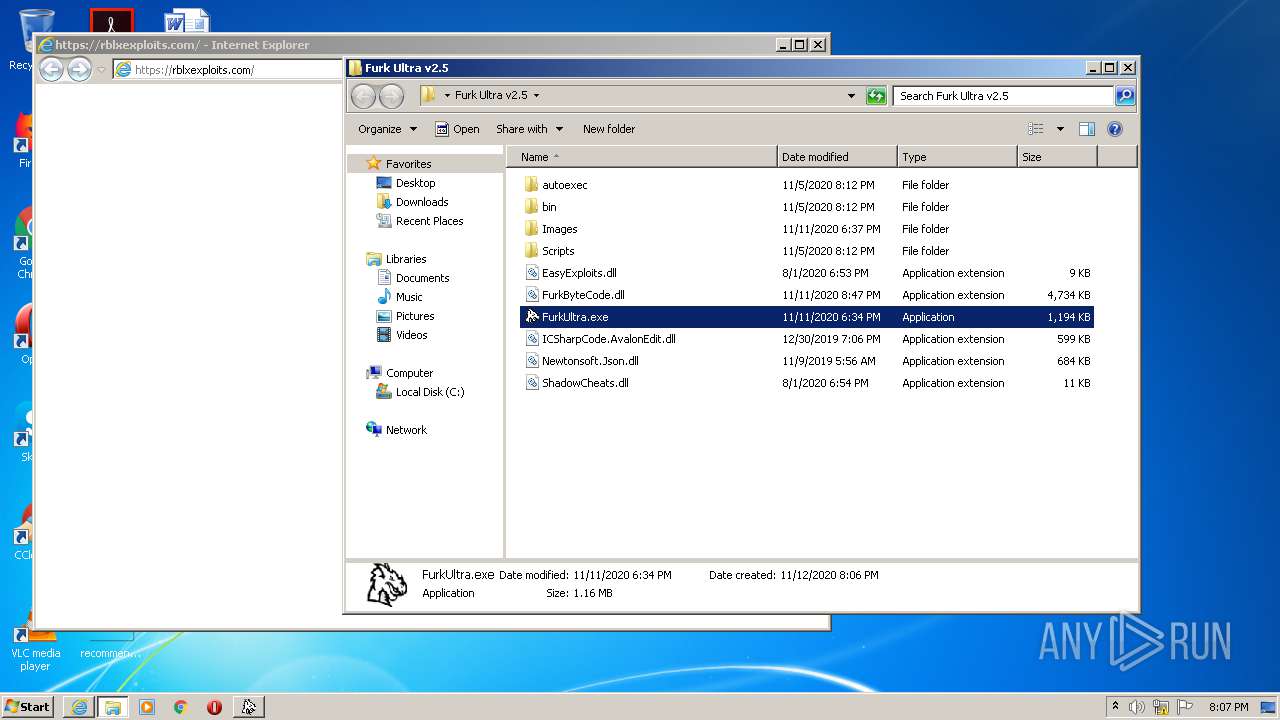
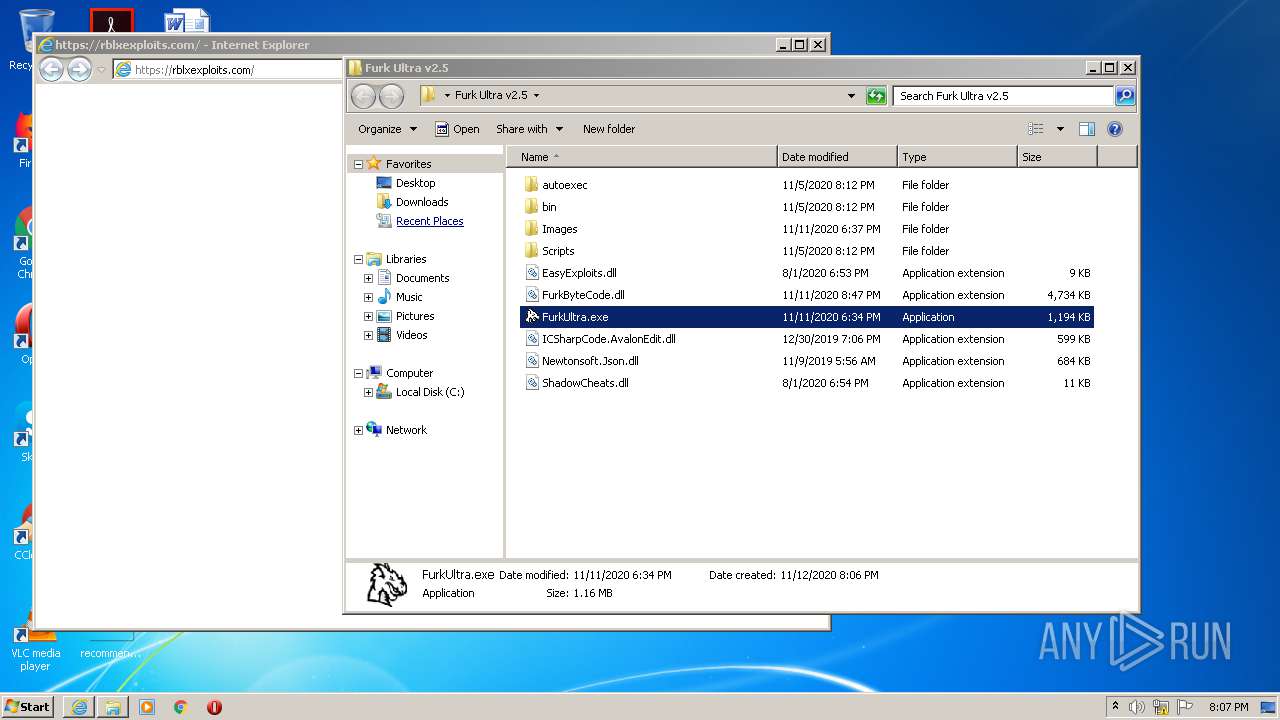
| 2940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Furk Ultra v2.5.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" https://rblxexploits.com/ | C:\Program Files\Internet Explorer\iexplore.exe | FurkUltra.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2972 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
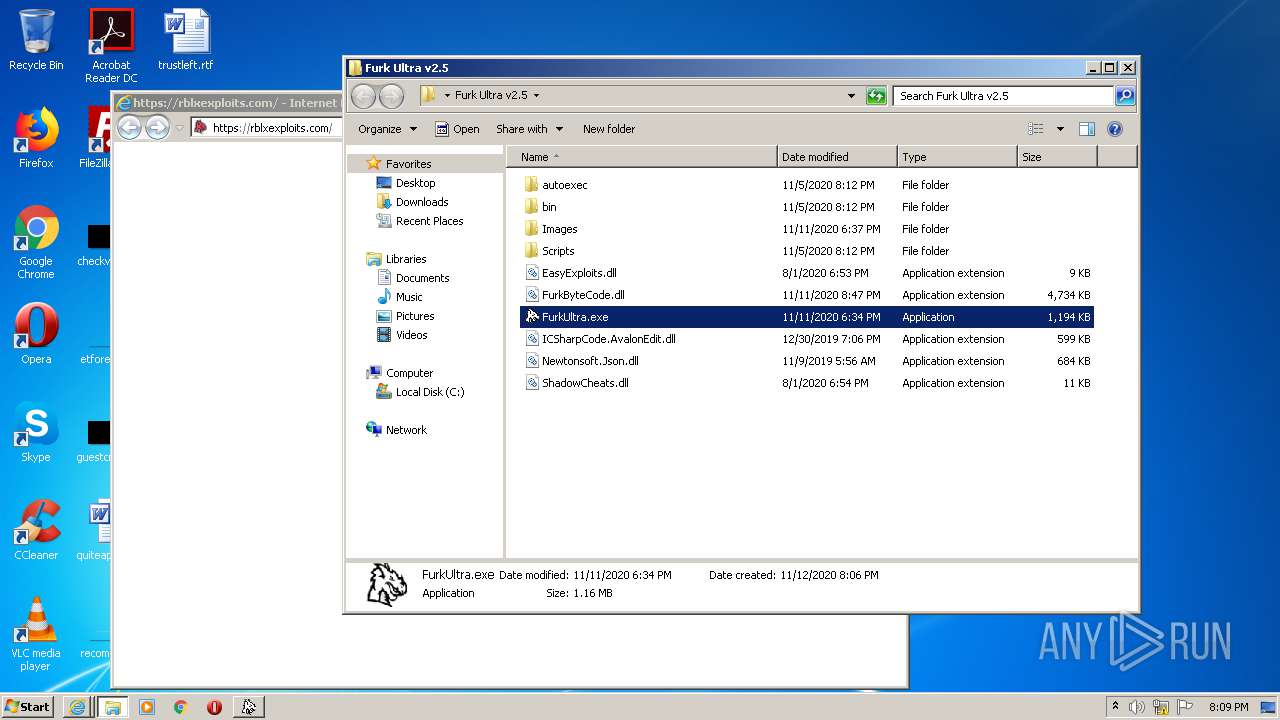
| 3196 | "C:\Users\admin\Desktop\Furk Ultra v2.5\FurkUltra.exe" | C:\Users\admin\Desktop\Furk Ultra v2.5\FurkUltra.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: FurkUltra Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3272 | "C:\Users\admin\Desktop\Furk Ultra v2.5\FurkUltra.exe" | C:\Users\admin\Desktop\Furk Ultra v2.5\FurkUltra.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: FurkUltra Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3412 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4024 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2972 CREDAT:2823437 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 078
Read events
7 889
Write events
187
Delete events
2
Modification events
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Furk Ultra v2.5.rar | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3412) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
6
Suspicious files
71
Text files
247
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\A Bizarre Day.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\autoexec\test.txt | text | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\A Universal Time.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\BloxBurg.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\Build A Boat For Treasure.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\Bad Business.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\Anime Fighting Simulator.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\Big Paintball.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\Counter Blox.jpg | image | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\Desktop\Furk Ultra v2.5\Images\Clicker Madness.jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
94
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAMTUCQLlvkozfNDacit2ng%3D | US | der | 279 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3148 | iexplore.exe | GET | 200 | 172.217.168.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAjD0BtlK1KzAgAAAAB%2FFDs%3D | US | der | 471 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCGfvk%2F7YkJPsm35ifeRXbY | US | der | 472 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAMTUCQLlvkozfNDacit2ng%3D | US | der | 279 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 172.217.168.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDQ45PuSdkrhAgAAAAAYdbq | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3272 | FurkUltra.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
2972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3148 | iexplore.exe | 104.28.16.152:443 | rblxexploits.com | Cloudflare Inc | US | shared |
3148 | iexplore.exe | 172.67.187.147:443 | rblxexploits.com | — | US | suspicious |
3148 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3148 | iexplore.exe | 173.192.101.24:443 | p353175.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
3148 | iexplore.exe | 172.217.23.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3148 | iexplore.exe | 216.58.208.34:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3148 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3148 | iexplore.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
rblxexploits.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
p353175.clksite.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |