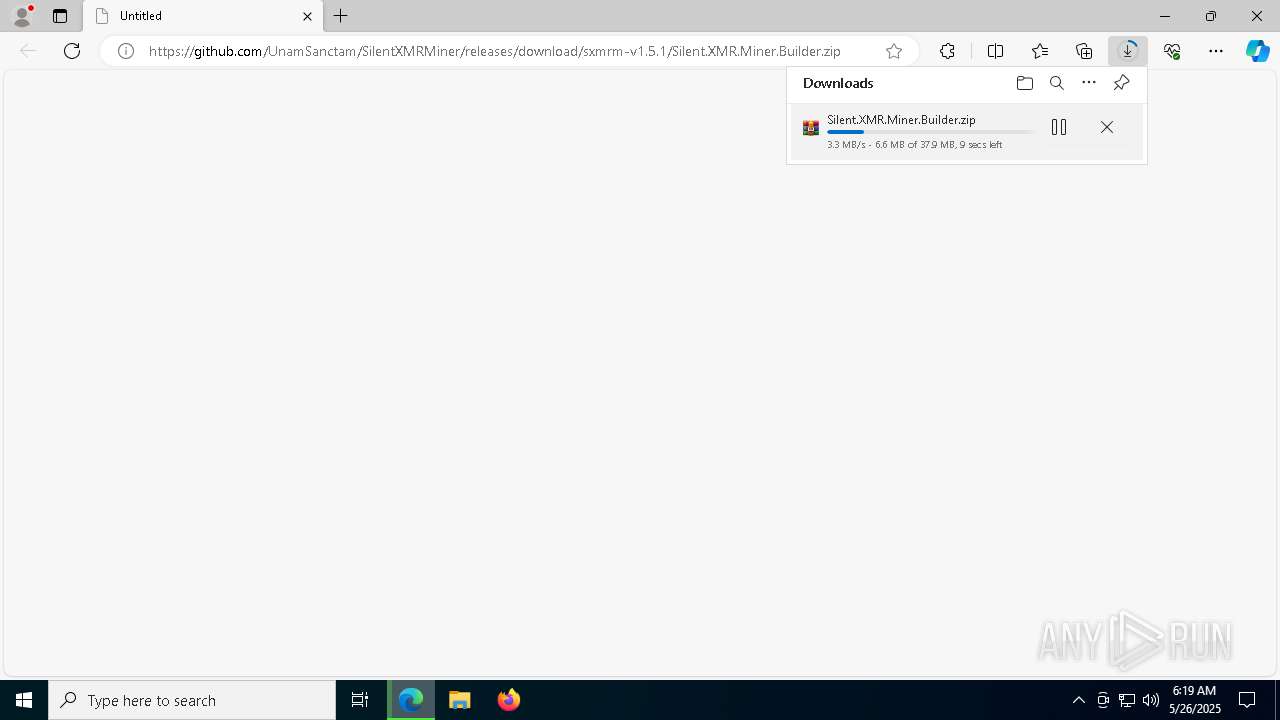
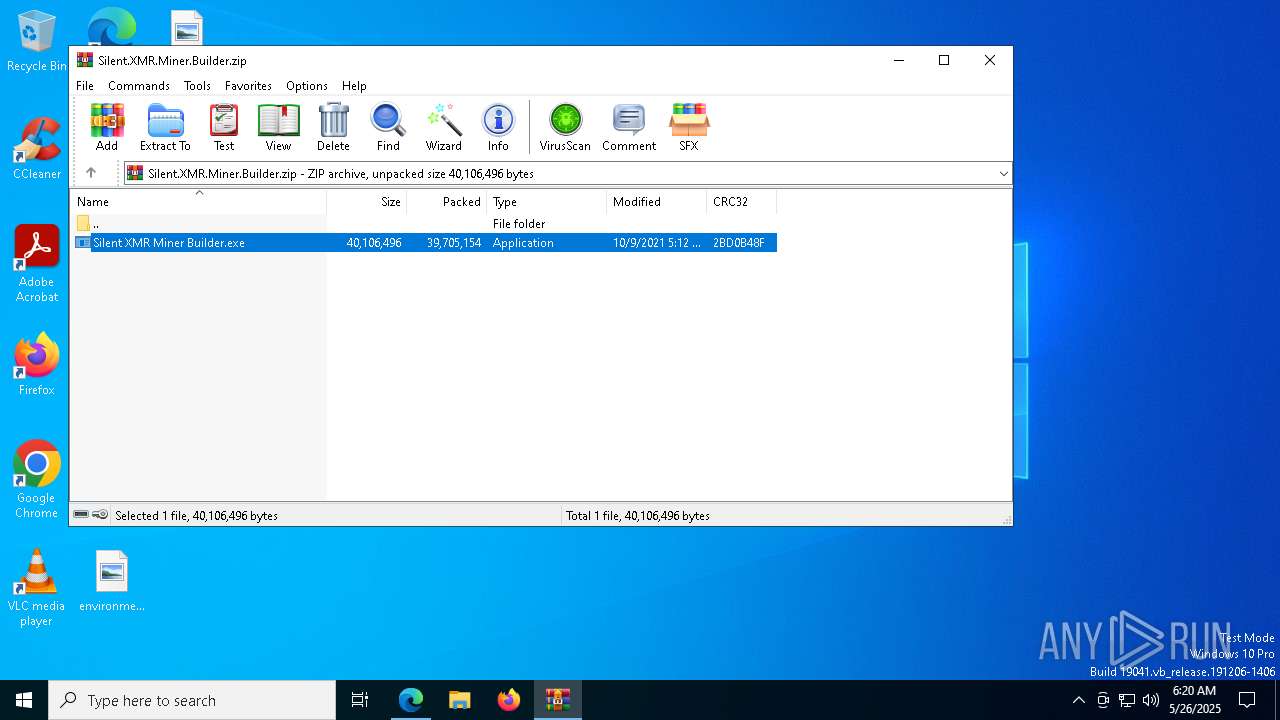
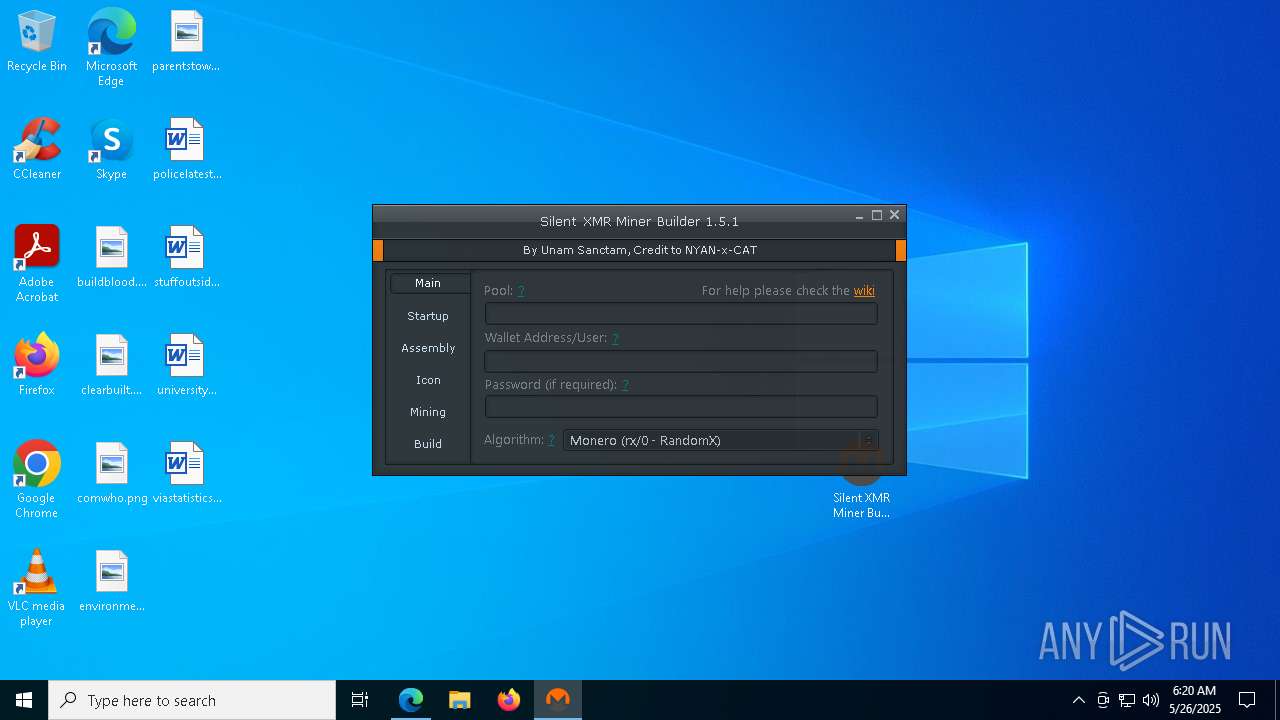
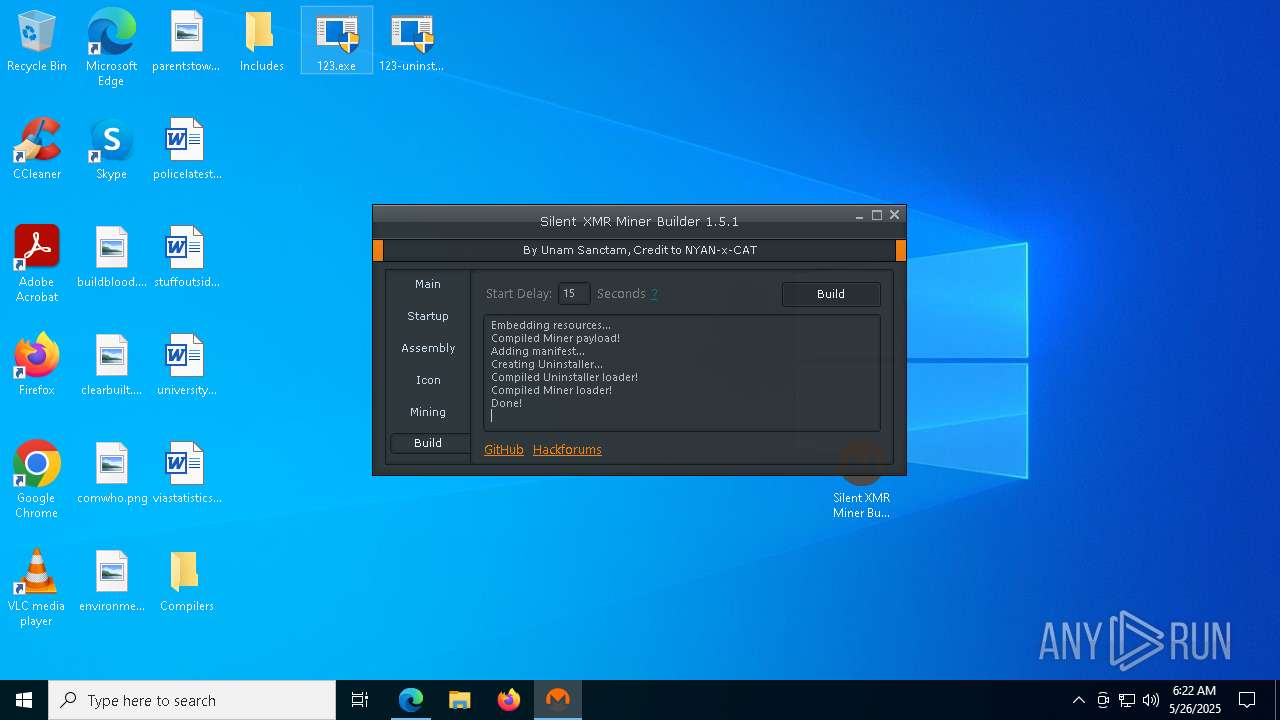
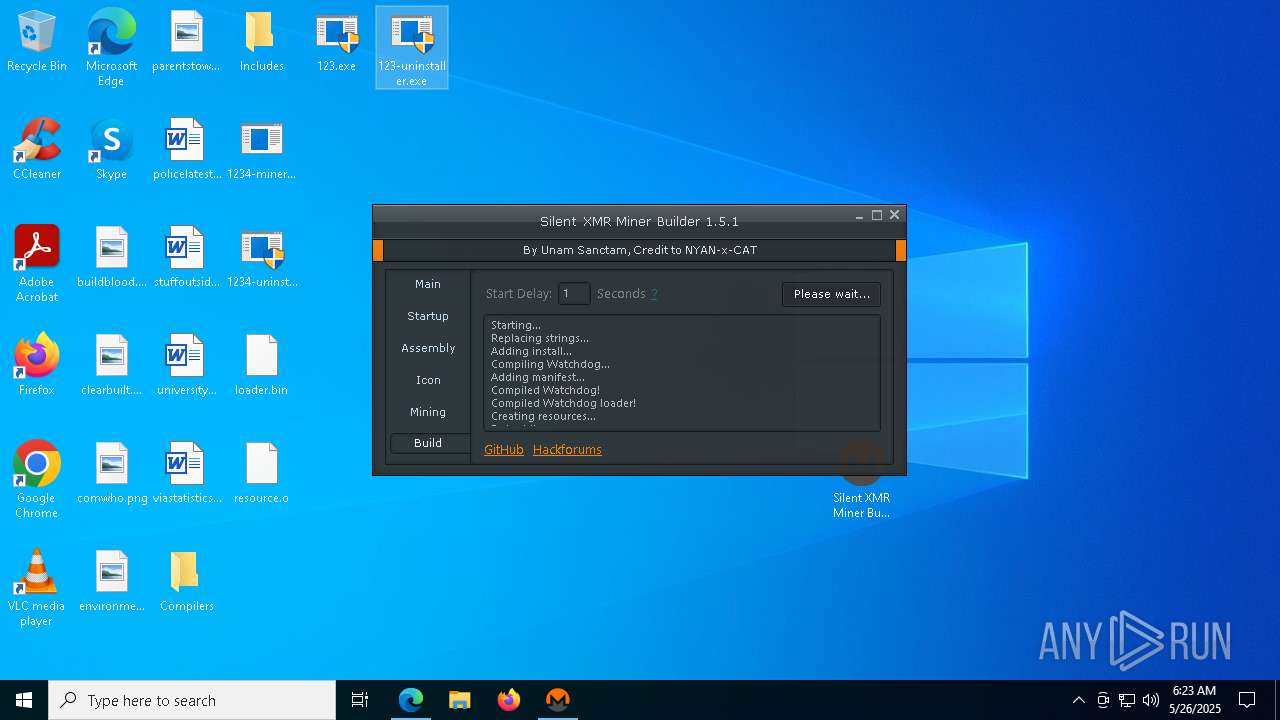
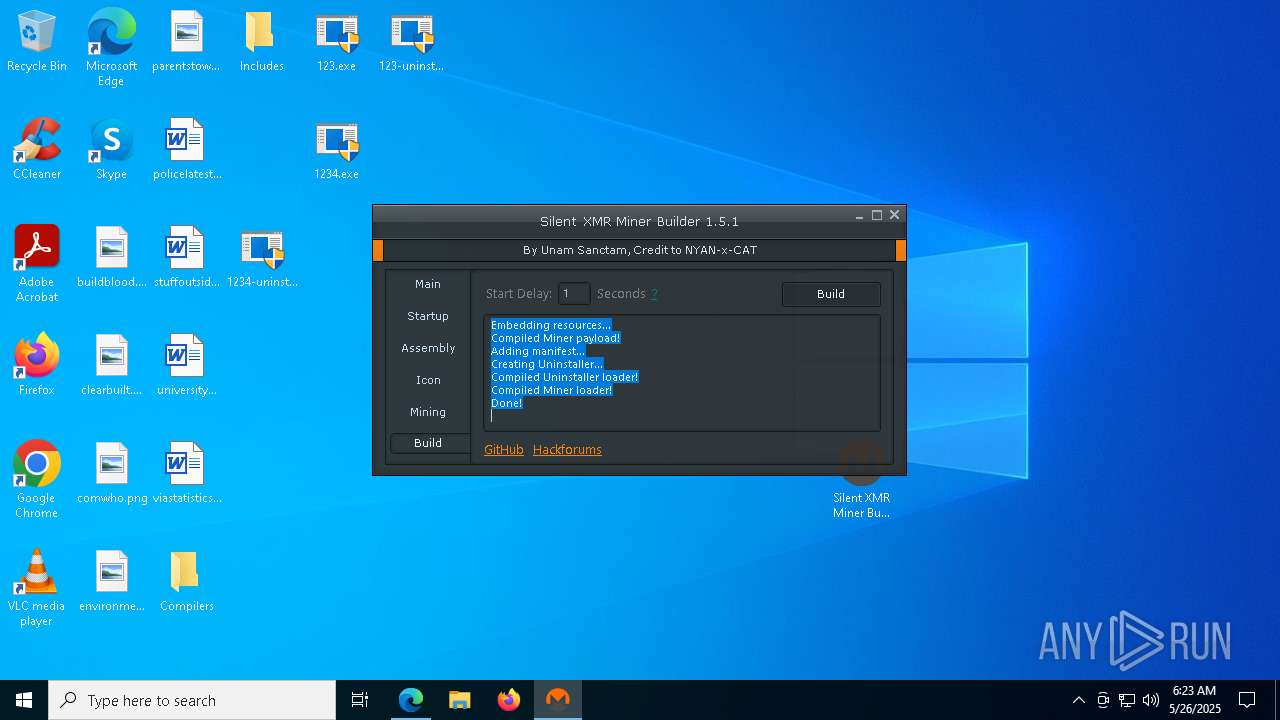
| URL: | https://github.com/UnamSanctam/SilentXMRMiner/releases/download/sxmrm-v1.5.1/Silent.XMR.Miner.Builder.zip |
| Full analysis: | https://app.any.run/tasks/b8ee4c13-107f-4cfa-b881-270a2886f0cc |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 06:19:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3220905B68442828B7B635A92F229145 |
| SHA1: | BBD8DFA31FB01D39E70D2DA2E0D2FE244B8CAE70 |
| SHA256: | 76891AB2C36EE76A7E71336EE7BA1F9421730D453B5DE1F903906A467C5C33ED |
| SSDEEP: | 3:N8tEdnELGsOLbuGAE2kC82UKCLtKeX9J+kV:2ulLsOLyGArXUnLnJ+kV |
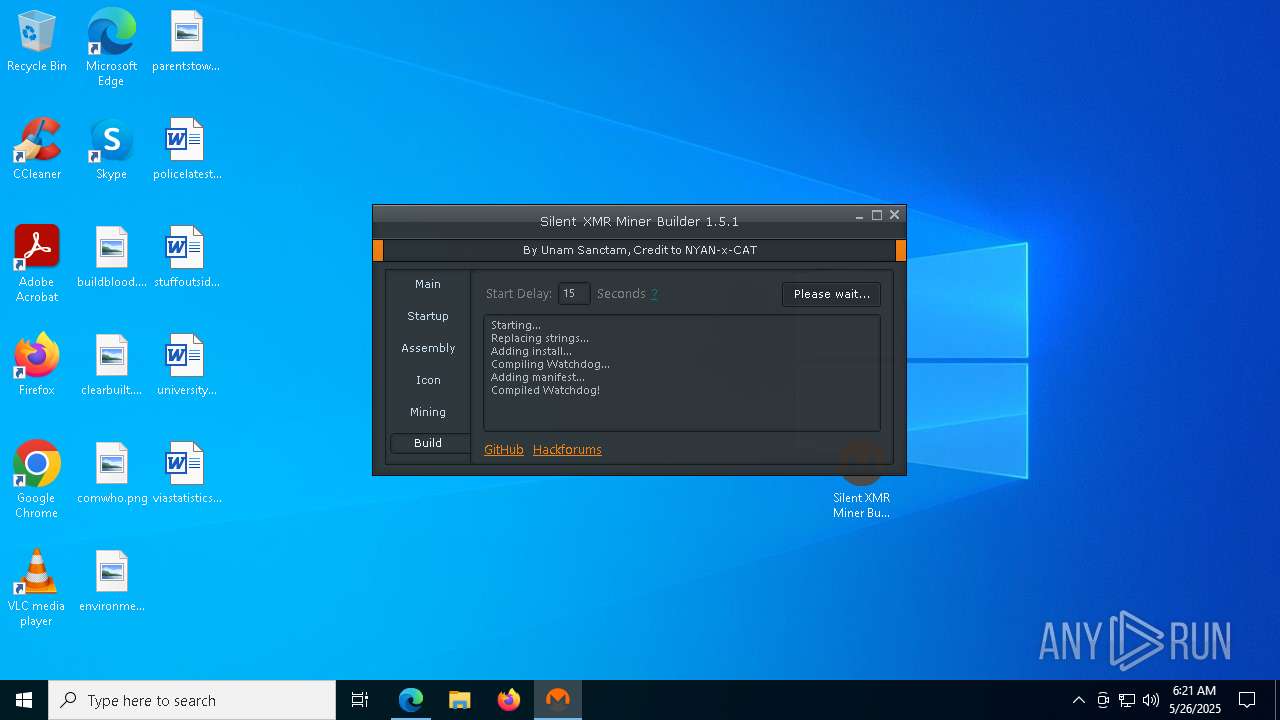
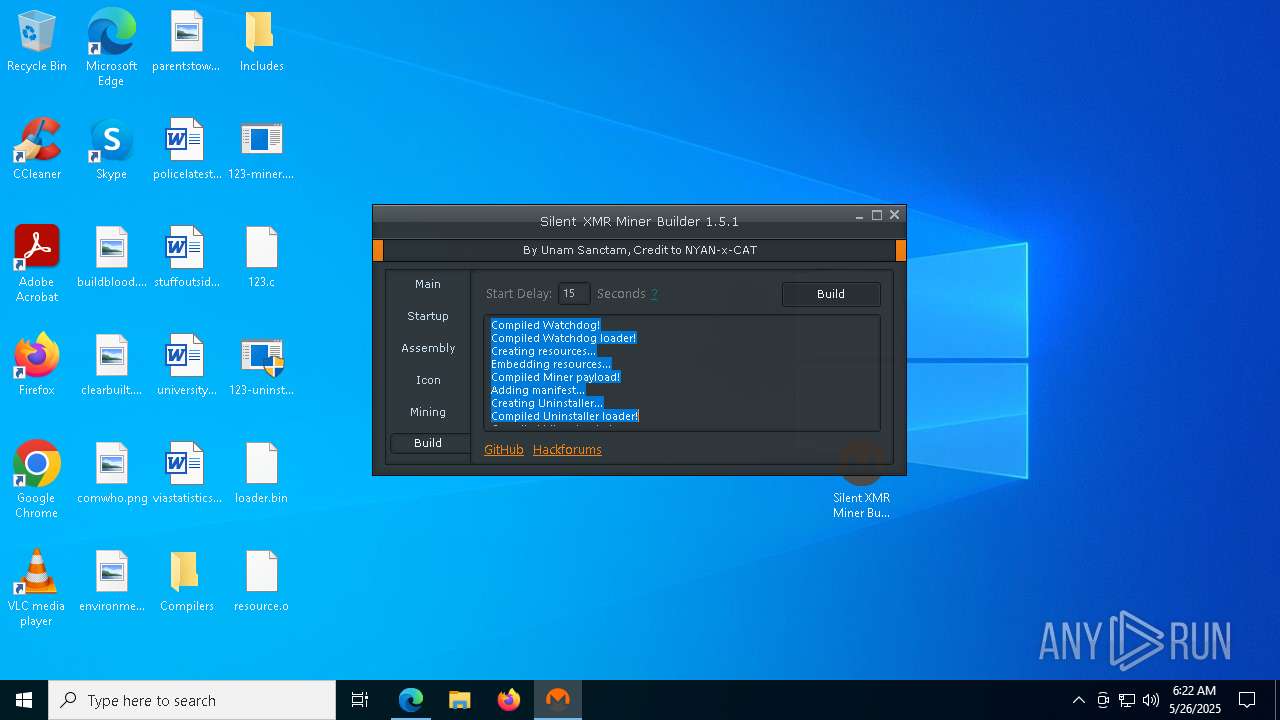
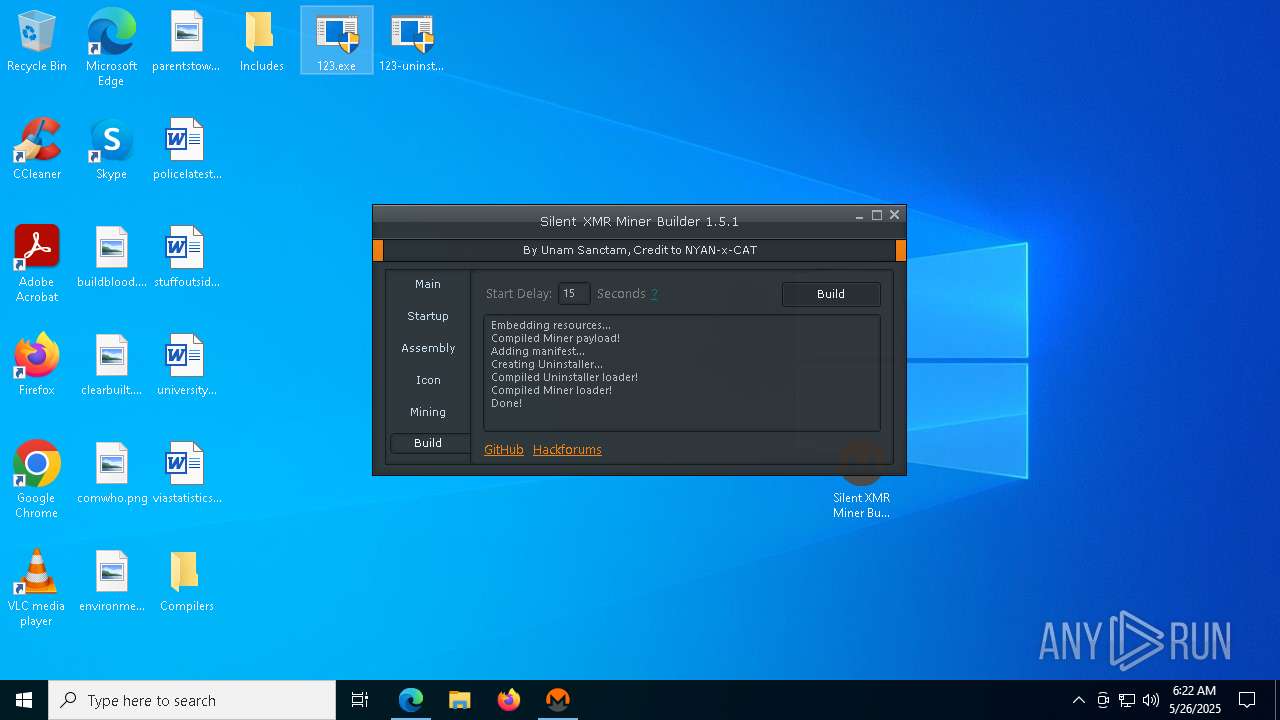
MALICIOUS
Execute application with conhost.exe as parent process
- cmd.exe (PID: 2416)
SUSPICIOUS
Creates file in the systems drive root
- Silent XMR Miner Builder.exe (PID: 4220)
Reads security settings of Internet Explorer
- Silent XMR Miner Builder.exe (PID: 4220)
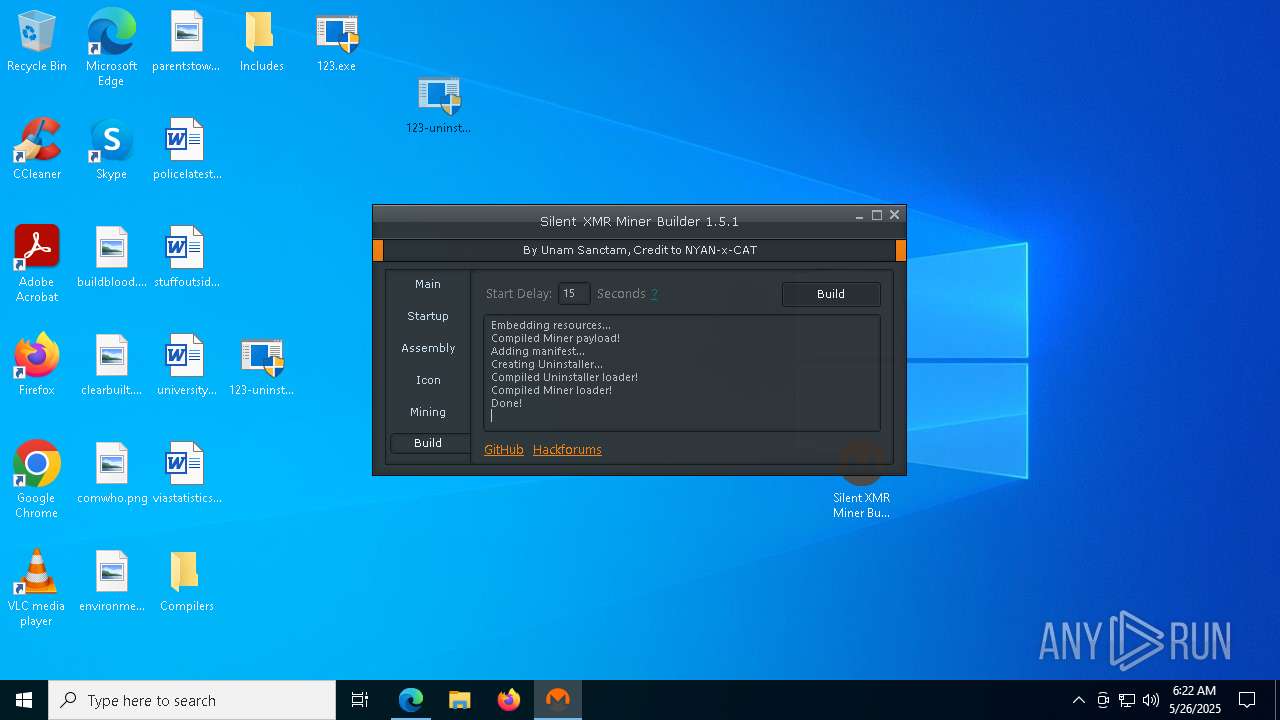
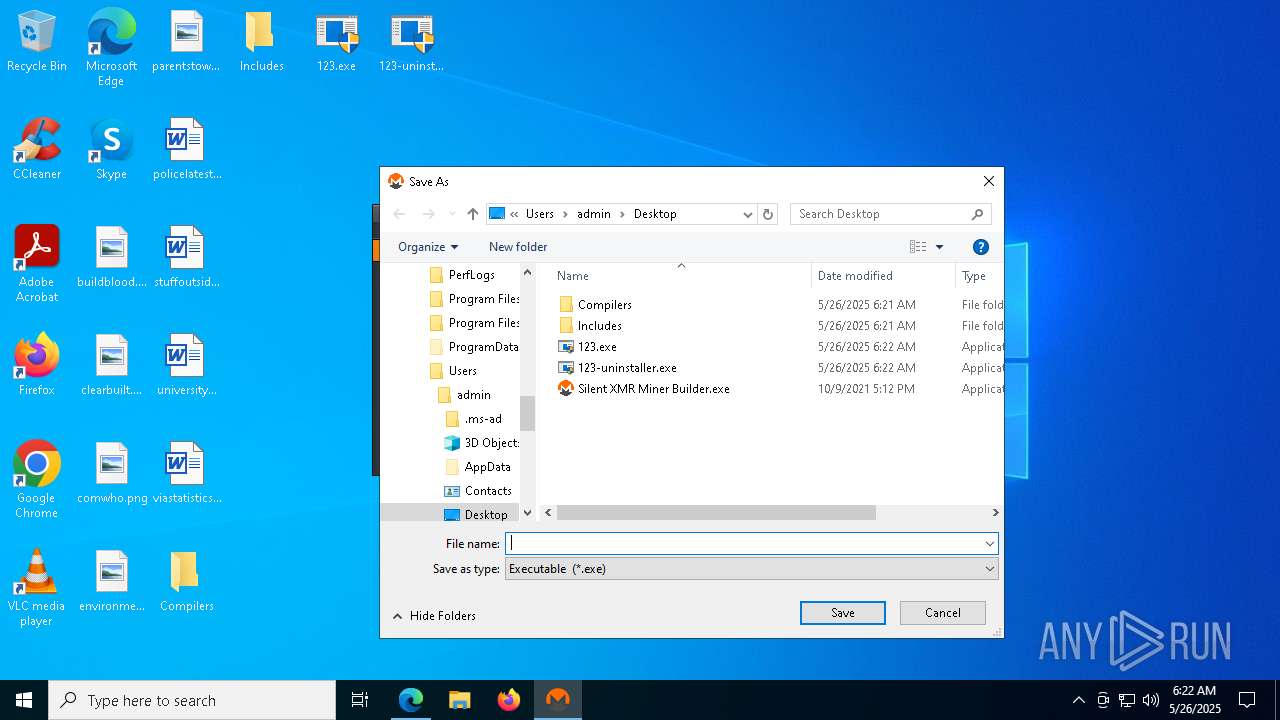
Executable content was dropped or overwritten
- csc.exe (PID: 6972)
- Silent XMR Miner Builder.exe (PID: 4220)
- tcc.exe (PID: 776)
- csc.exe (PID: 4572)
- csc.exe (PID: 4056)
- tcc.exe (PID: 2852)
- csc.exe (PID: 3968)
- tcc.exe (PID: 856)
- tcc.exe (PID: 3992)
- csc.exe (PID: 6132)
- tcc.exe (PID: 2984)
- tcc.exe (PID: 3020)
- csc.exe (PID: 3332)
Starts CMD.EXE for commands execution
- Silent XMR Miner Builder.exe (PID: 4220)
- windres.exe (PID: 8156)
- windres.exe (PID: 6660)
- windres.exe (PID: 7236)
- windres.exe (PID: 6712)
- windres.exe (PID: 3100)
- windres.exe (PID: 8076)
- conhost.exe (PID: 8168)
Working with threads in the GNU C Compiler (GCC) libraries related mutex has been found
- cc1.exe (PID: 7812)
- gcc.exe (PID: 2064)
- gcc.exe (PID: 2344)
- cc1.exe (PID: 3976)
- gcc.exe (PID: 2236)
- cc1.exe (PID: 6892)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6584)
INFO
Checks supported languages
- identity_helper.exe (PID: 6424)
- Silent XMR Miner Builder.exe (PID: 4220)
- cvtres.exe (PID: 8092)
- csc.exe (PID: 6972)
- donut.exe (PID: 2416)
- windres.exe (PID: 8156)
- tcc.exe (PID: 776)
- csc.exe (PID: 4056)
- cvtres.exe (PID: 5404)
- csc.exe (PID: 4572)
- windres.exe (PID: 6660)
- gcc.exe (PID: 2064)
- cc1.exe (PID: 7812)
- tcc.exe (PID: 2852)
- cc1.exe (PID: 3976)
- donut.exe (PID: 4528)
- cvtres.exe (PID: 3132)
- gcc.exe (PID: 2344)
- windres.exe (PID: 7236)
- tcc.exe (PID: 856)
- cc1.exe (PID: 6892)
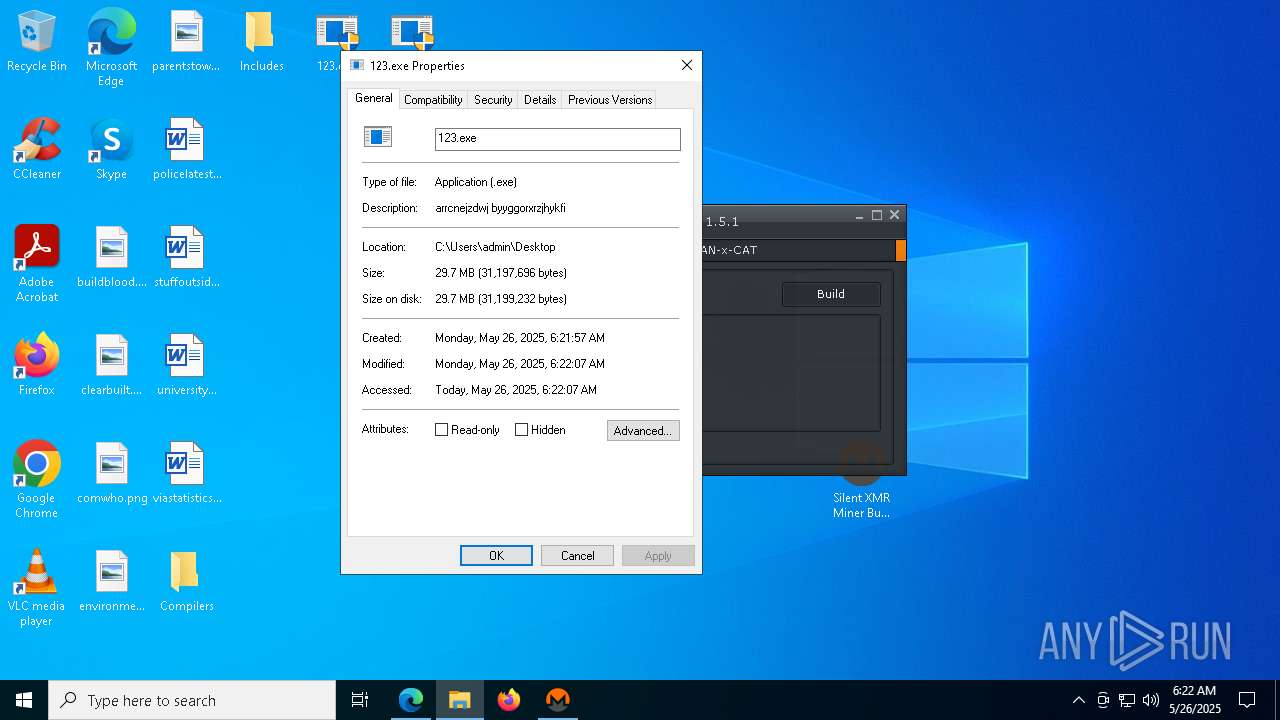
- 123.exe (PID: 7980)
- gcc.exe (PID: 2236)
- donut.exe (PID: 6612)
Reads the computer name
- Silent XMR Miner Builder.exe (PID: 4220)
- identity_helper.exe (PID: 6424)
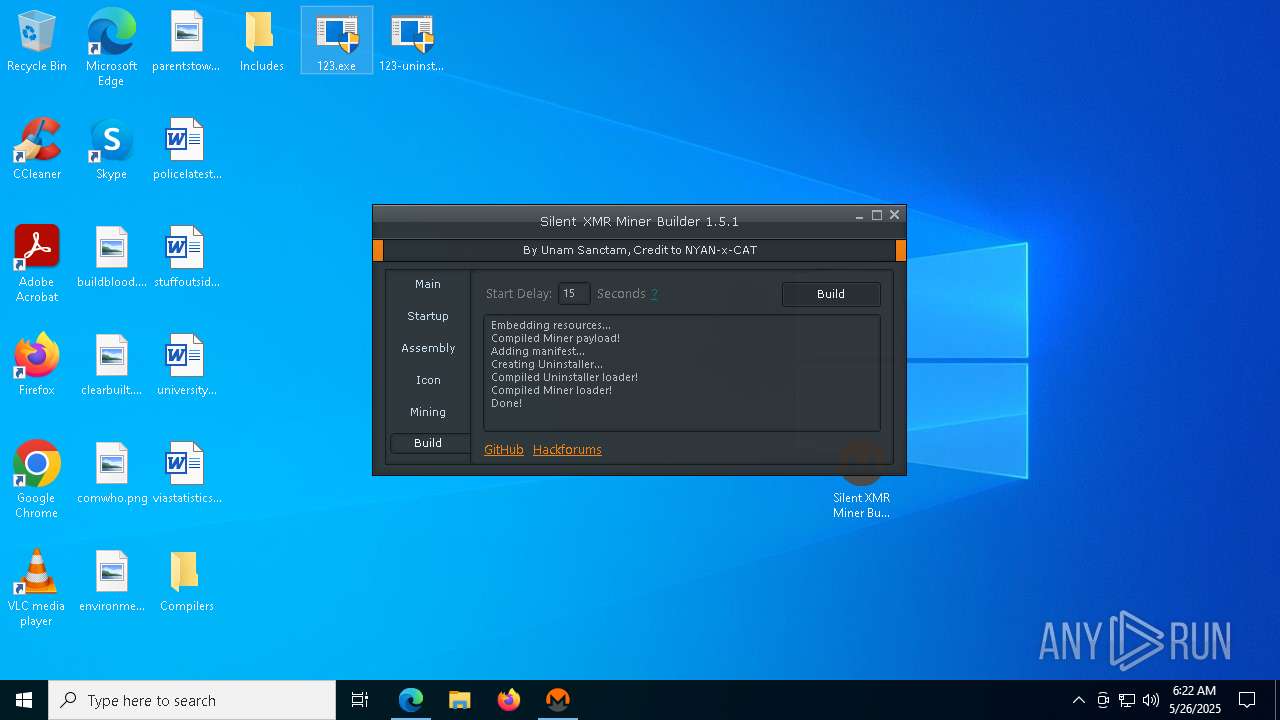
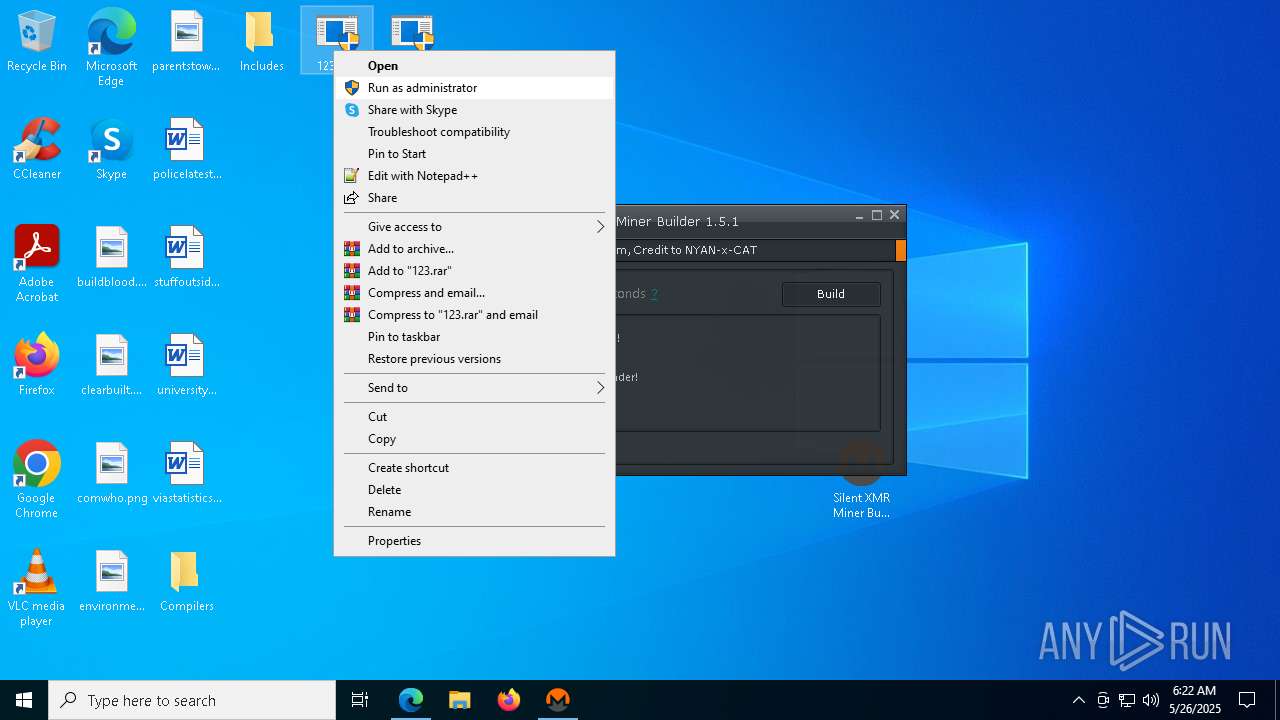
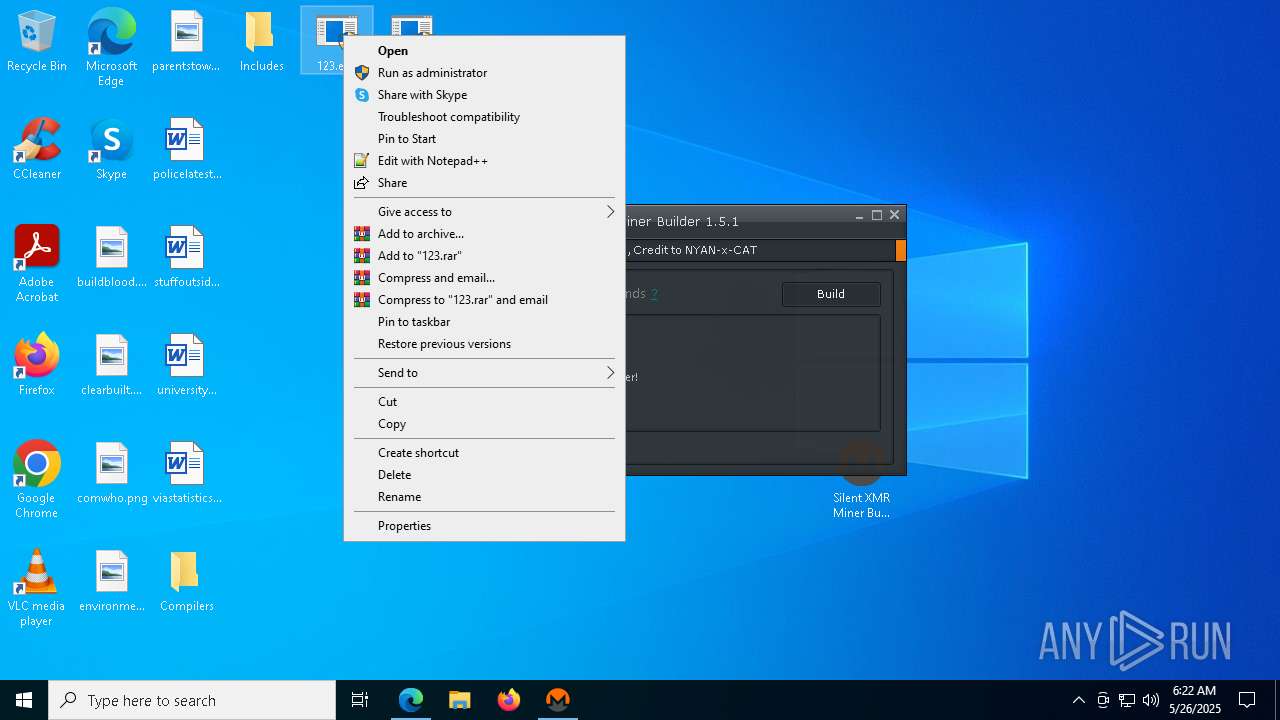
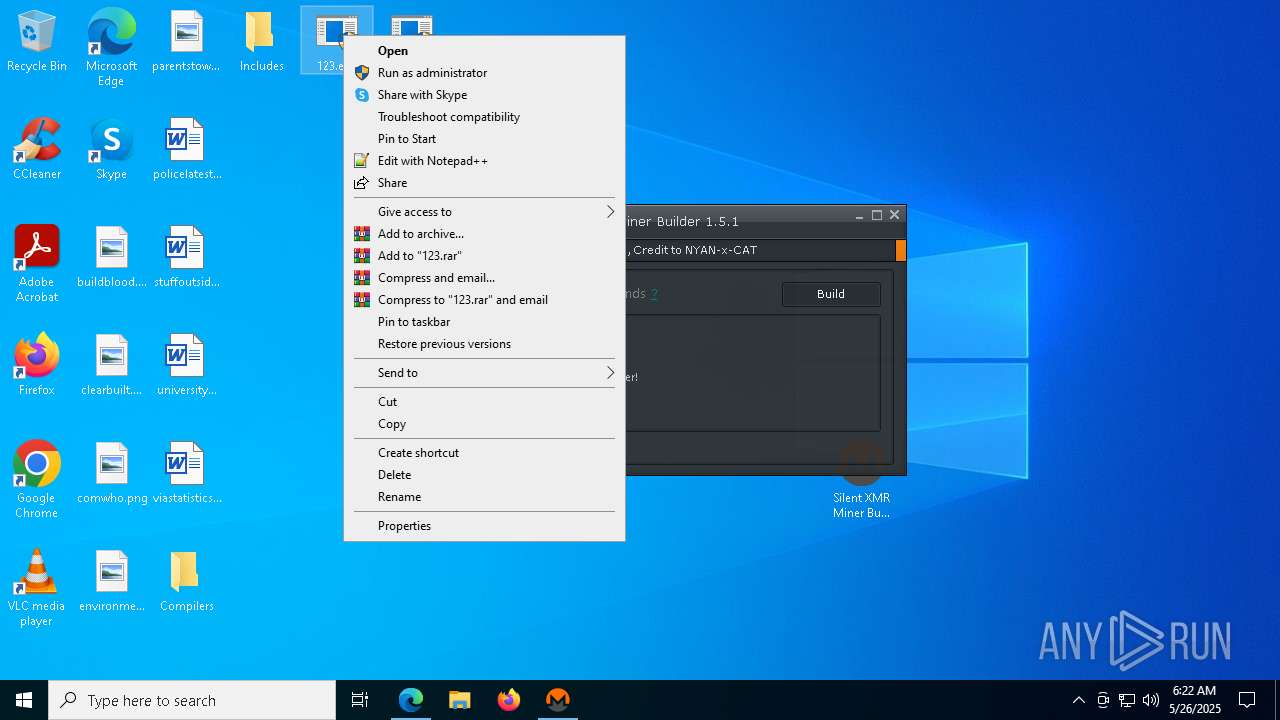
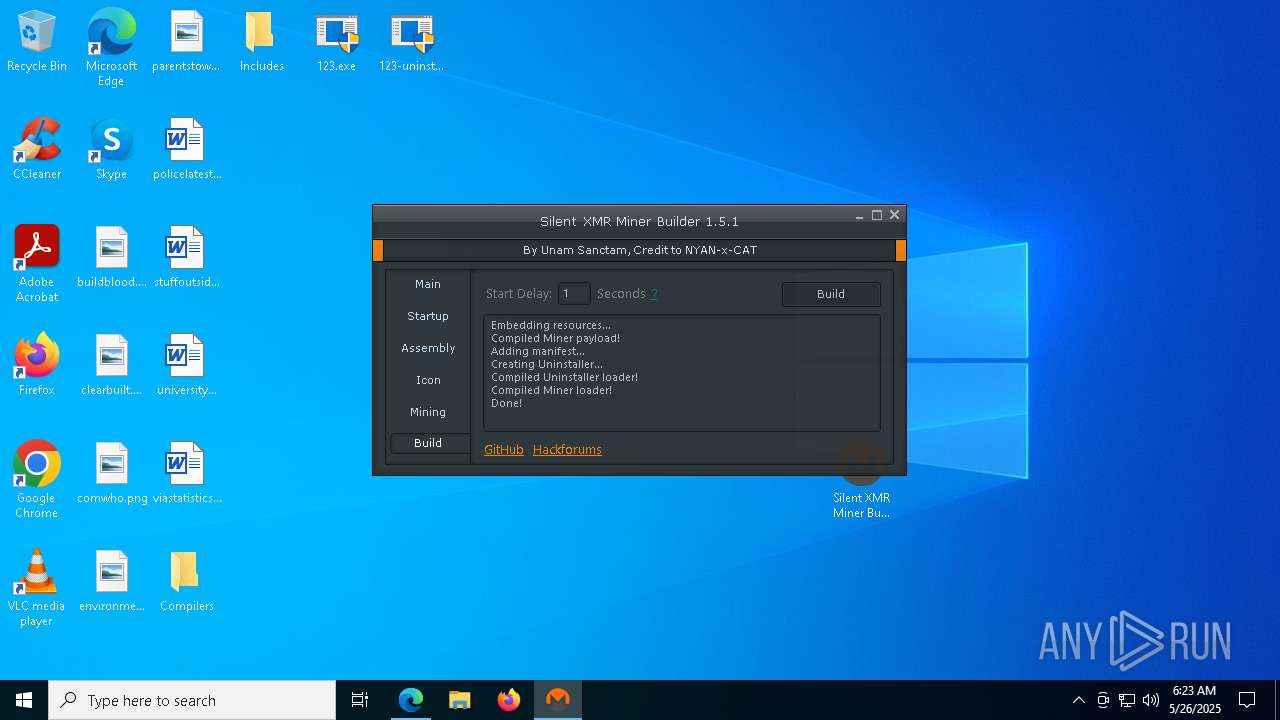
Manual execution by a user
- Silent XMR Miner Builder.exe (PID: 4220)
- 123.exe (PID: 7856)
- 123.exe (PID: 7980)
- 123-uninstaller.exe (PID: 5136)
- 123-uninstaller.exe (PID: 7940)
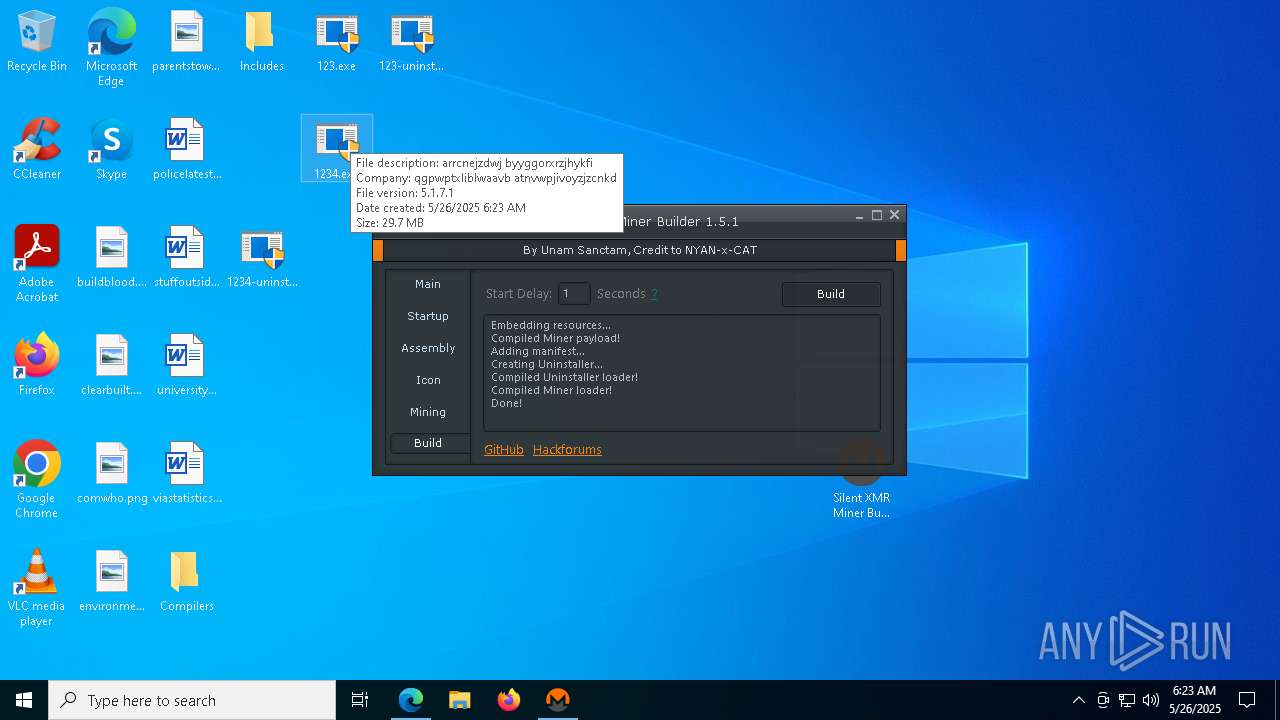
- 1234.exe (PID: 496)
- 1234.exe (PID: 1184)
Reads Environment values
- identity_helper.exe (PID: 6424)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5072)
Application launched itself
- msedge.exe (PID: 5072)
Reads the machine GUID from the registry
- Silent XMR Miner Builder.exe (PID: 4220)
- csc.exe (PID: 6972)
- csc.exe (PID: 4572)
- donut.exe (PID: 2416)
- donut.exe (PID: 4528)
- csc.exe (PID: 4056)
- donut.exe (PID: 6612)
Reads the software policy settings
- slui.exe (PID: 4696)
- slui.exe (PID: 3676)
Create files in a temporary directory
- Silent XMR Miner Builder.exe (PID: 4220)
- cvtres.exe (PID: 8092)
- cvtres.exe (PID: 5404)
- cvtres.exe (PID: 3132)
Checks proxy server information
- slui.exe (PID: 3676)
The sample compiled with english language support
- Silent XMR Miner Builder.exe (PID: 4220)
- tcc.exe (PID: 856)
- msedge.exe (PID: 6660)
- tcc.exe (PID: 3020)
Executable content was dropped or overwritten
- msedge.exe (PID: 6660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
279
Monitored processes
140
Malicious processes
2
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | C:\WINDOWS\system32\cmd.exe /c "C:\Users\admin\Desktop\Compilers\MinGW64\bin\gcc" -E -xc -DRC_INVOKED -DDefAdmin resource.rc | C:\Windows\SysWOW64\cmd.exe | — | windres.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6116 --field-trial-handle=2400,i,14524103710942979349,8725329480060142208,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | "C:\Users\admin\Desktop\1234.exe" | C:\Users\admin\Desktop\1234.exe | — | explorer.exe | |||||||||||
User: admin Company: qgpwptxliblwaavb atnvwpjivoyzjzcnkd Integrity Level: MEDIUM Description: arrcnejzdwj byyggorxrzjhykfi Exit code: 3221226540 Version: 5,1,7,1 Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\Users\admin\Desktop\Compilers\tinycc\tcc.exe" -Wl,-subsystem=windows "123-watchdog-loader.c" resource.o "C:\Users\admin\Desktop\Includes\syscalls.c" -xa "C:\Users\admin\Desktop\Includes\syscallsstubs.asm" | C:\Users\admin\Desktop\Compilers\tinycc\tcc.exe | Silent XMR Miner Builder.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 856 | "C:\Users\admin\Desktop\Compilers\tinycc\tcc.exe" -Wl,-subsystem=windows "123.c" resource.o "C:\Users\admin\Desktop\Includes\syscalls.c" -xa "C:\Users\admin\Desktop\Includes\syscallsstubs.asm" | C:\Users\admin\Desktop\Compilers\tinycc\tcc.exe | Silent XMR Miner Builder.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5668 --field-trial-handle=2400,i,14524103710942979349,8725329480060142208,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | "C:\Users\admin\Desktop\Compilers\donut\donut.exe" "C:\Users\admin\Desktop\1234-watchdog.exe" -a 2 -f 1 | C:\Users\admin\Desktop\Compilers\donut\donut.exe | — | Silent XMR Miner Builder.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Donut shellcode generator Exit code: 0 Version: 0.9.3 Modules
| |||||||||||||||
Total events
17 505
Read events
17 395
Write events
106
Delete events
4
Modification events
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 08C8BD379A942F00 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4031C7379A942F00 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328524 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9DB2DA30-4D21-4A0F-91D9-DC38F7078B5F} | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328524 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {679CA927-556D-4E8C-9DA4-9F1F87E97B4F} | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
36
Suspicious files
240
Text files
199
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b335.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b400.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
50
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5968 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748299181&P2=404&P3=2&P4=HD6KRA6AlXOm%2fXln9opWCvJQVN04VTg2OqGUozjzIUiUdaIRq9Dr1XDDGPHAsP0fX2pL7ZM2XUyPisxp9SAlxQ%3d%3d | unknown | — | — | whitelisted |
5968 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748299181&P2=404&P3=2&P4=HD6KRA6AlXOm%2fXln9opWCvJQVN04VTg2OqGUozjzIUiUdaIRq9Dr1XDDGPHAsP0fX2pL7ZM2XUyPisxp9SAlxQ%3d%3d | unknown | — | — | whitelisted |
5968 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748299181&P2=404&P3=2&P4=HD6KRA6AlXOm%2fXln9opWCvJQVN04VTg2OqGUozjzIUiUdaIRq9Dr1XDDGPHAsP0fX2pL7ZM2XUyPisxp9SAlxQ%3d%3d | unknown | — | — | whitelisted |
5968 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748299181&P2=404&P3=2&P4=UN4JuxhZQPAXI%2bSJRi7VaoV6mo9uRUFvXViF7zu0SZyvXYDpZoQZ0WdO2CqOL3MCR49eLMo3TCK7v3FpRTEYgg%3d%3d | unknown | — | — | whitelisted |
5968 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748299181&P2=404&P3=2&P4=UN4JuxhZQPAXI%2bSJRi7VaoV6mo9uRUFvXViF7zu0SZyvXYDpZoQZ0WdO2CqOL3MCR49eLMo3TCK7v3FpRTEYgg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7388 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5072 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7388 | msedge.exe | 150.171.29.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7388 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7388 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
business.bing.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |