| File name: | 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe |
| Full analysis: | https://app.any.run/tasks/da55809d-f7cd-4dfe-8413-cc555baf3517 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2020, 00:43:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | C3720C25734B84453050945AE914A3CC |
| SHA1: | 144161E00486A581B3AFEC54DEFF969F1F3E0D76 |
| SHA256: | 7682E484DE90C5340CCD6A34273D800AA7506F1C7BBFF253012AFF2A3C06C9E6 |
| SSDEEP: | 196608:A1htVLyh/g4uM+1YSVJ8mlaDnSwUA7gFWj9qdWKQ:AbtVLE4RMOZk2aDIQgFWj9aQ |
MALICIOUS
Loads dropped or rewritten executable
- install.exe (PID: 3660)
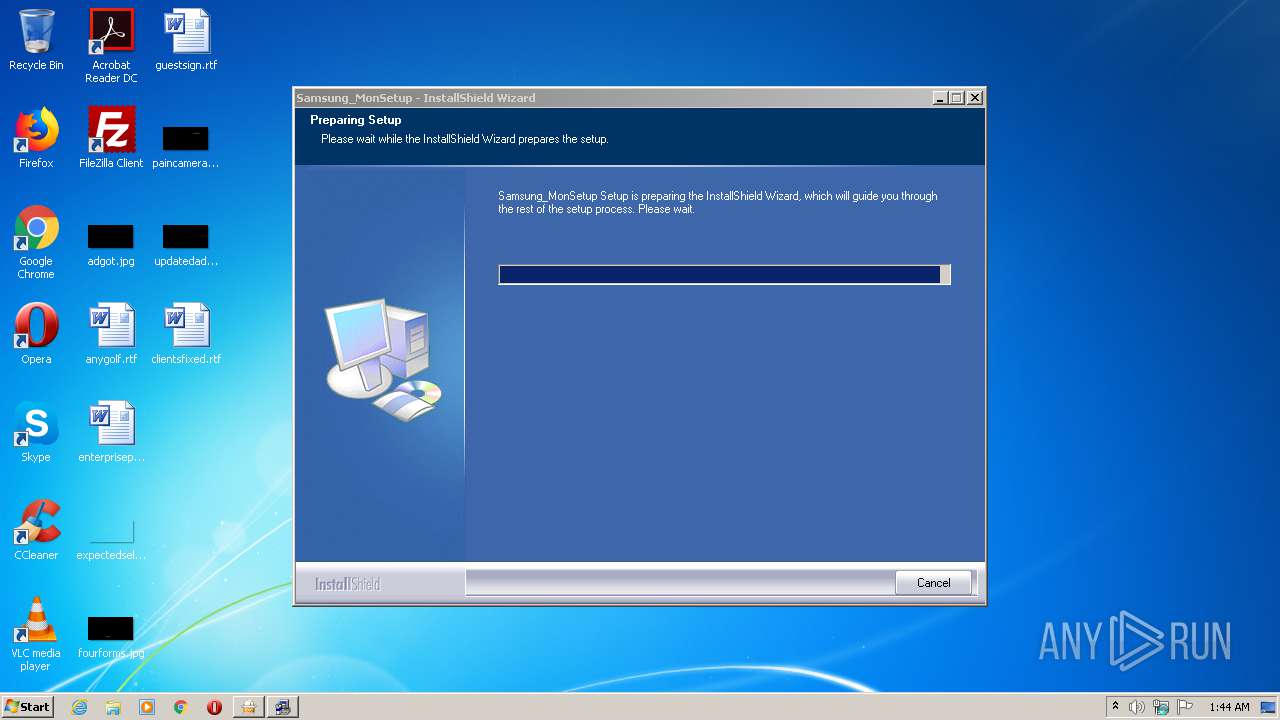
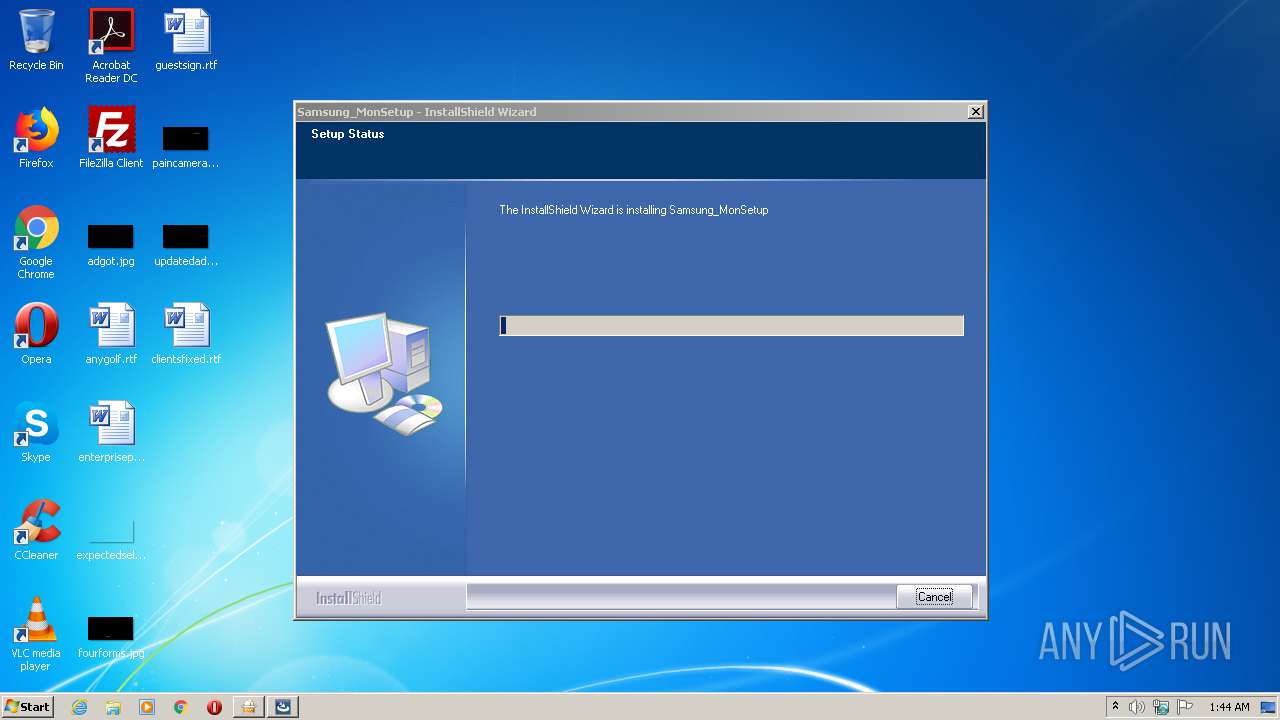
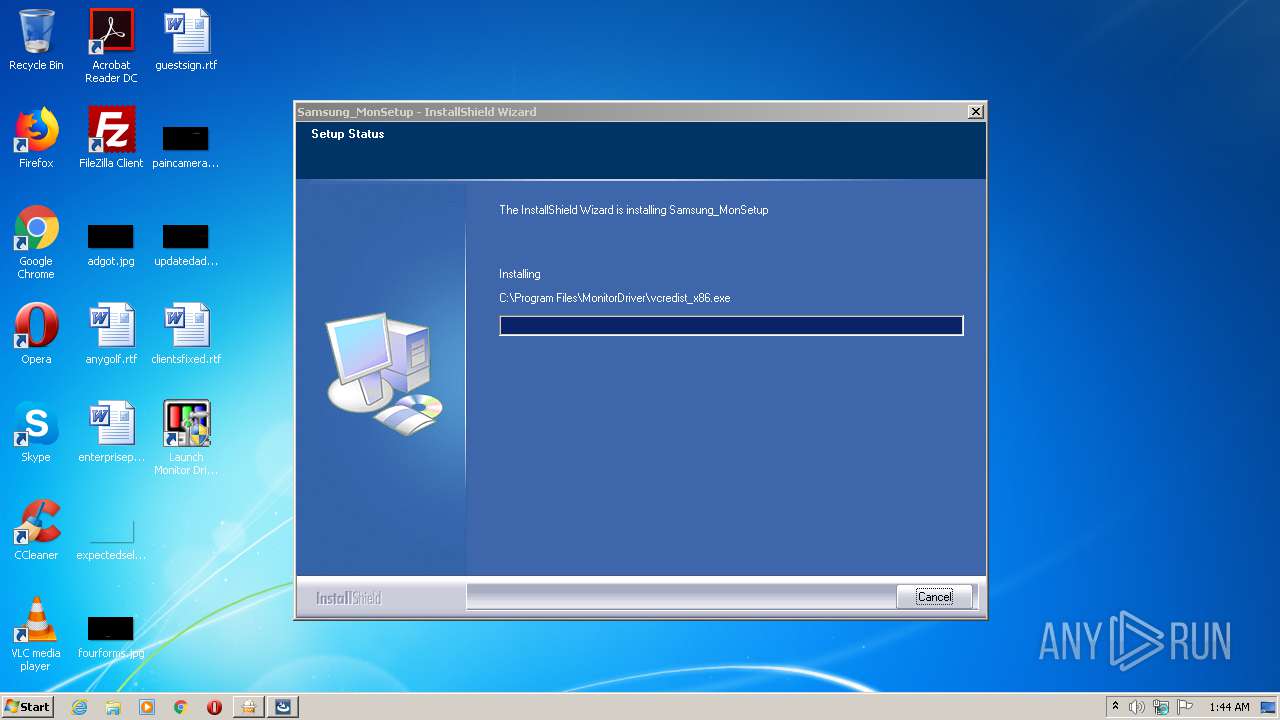
- Samsung_MonSetup_091006.exe (PID: 276)
Application was dropped or rewritten from another process
- Samsung_MonSetup_091006.exe (PID: 3348)
- MonSetup.exe (PID: 1280)
- vcredist_x86.exe (PID: 1824)
- install.exe (PID: 3660)
- Samsung_MonSetup_091006.exe (PID: 276)
SUSPICIOUS
Creates files in the user directory
- Samsung_MonSetup_091006.exe (PID: 276)
Executable content was dropped or overwritten
- 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe (PID: 3088)
- Samsung_MonSetup_091006.exe (PID: 276)
- vcredist_x86.exe (PID: 1824)
Executed via COM
- DllHost.exe (PID: 3348)
Creates a software uninstall entry
- Samsung_MonSetup_091006.exe (PID: 276)
Creates files in the program directory
- Samsung_MonSetup_091006.exe (PID: 276)
Searches for installed software
- Samsung_MonSetup_091006.exe (PID: 276)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:11 04:12:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 188416 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | 352256 |
| EntryPoint: | 0x842b0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.7.11.0 |
| ProductVersionNumber: | 16.7.11.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
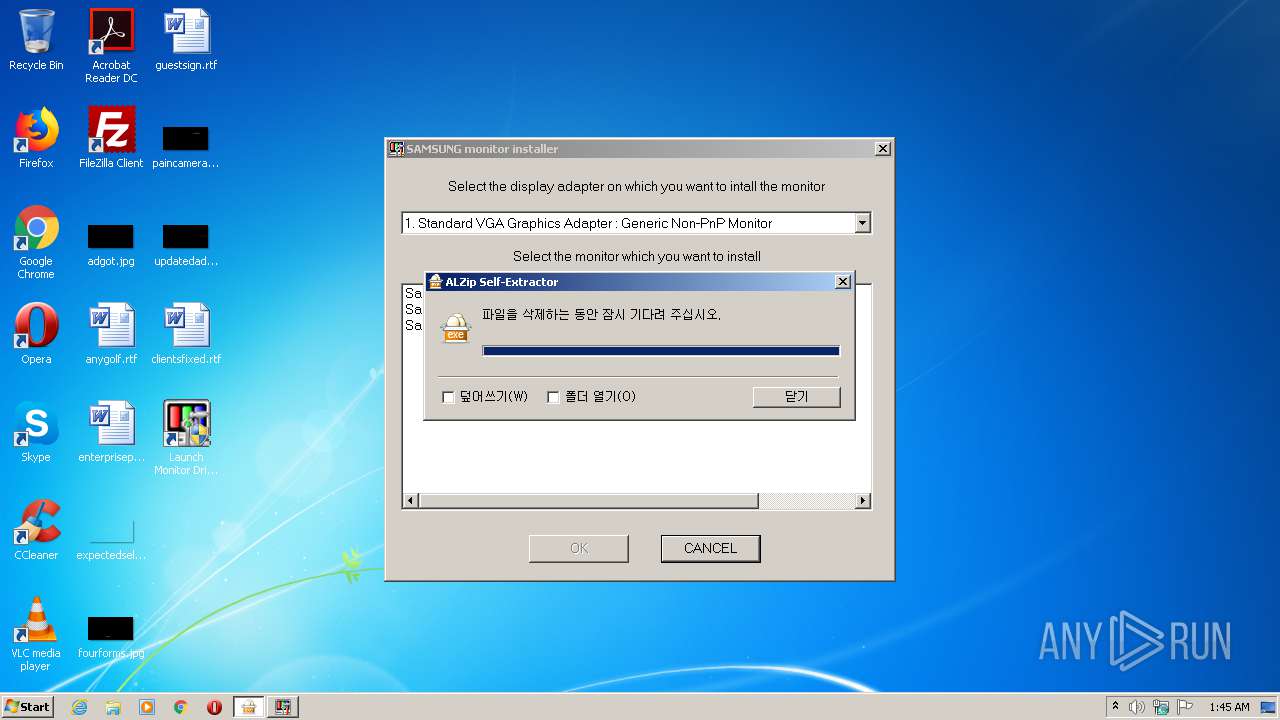
| CompanyName: | ESTsoft Corp. |
| FileDescription: | ALZip Self Extractor |
| FileVersion: | 16, 7, 11, 0 |
| InternalName: | EGGSFX |
| LegalCopyright: | Copyright (c) 1999 - present ESTsoft Corp. All right reserved. |
| OriginalFileName: | EGGSFX.sfx |
| ProductName: | ALZip |
| ProductVersion: | 16, 7, 11, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Jul-2016 02:12:47 |
| Detected languages: |
|
| CompanyName: | ESTsoft Corp. |
| FileDescription: | ALZip Self Extractor |
| FileVersion: | 16, 7, 11, 0 |
| InternalName: | EGGSFX |
| LegalCopyright: | Copyright (c) 1999 - present ESTsoft Corp. All right reserved. |
| OriginalFilename: | EGGSFX.sfx |
| ProductName: | ALZip |
| ProductVersion: | 16, 7, 11, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 11-Jul-2016 02:12:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00056000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00057000 | 0x0002E000 | 0x0002D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92472 |
.rsrc | 0x00085000 | 0x0000E000 | 0x0000DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.99512 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02301 | 622 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.95916 | 2216 | Latin 1 / Western European | Korean - Korea | RT_ICON |
3 | 3.26596 | 1384 | Latin 1 / Western European | Korean - Korea | RT_ICON |
4 | 7.9714 | 31077 | Latin 1 / Western European | Korean - Korea | RT_ICON |
5 | 4.71296 | 9640 | Latin 1 / Western European | Korean - Korea | RT_ICON |
6 | 4.85769 | 4264 | Latin 1 / Western European | Korean - Korea | RT_ICON |
7 | 6.69642 | 386 | Latin 1 / Western European | Korean - Korea | RT_STRING |
8 | 7.24858 | 336 | Latin 1 / Western European | Korean - Korea | RT_STRING |
9 | 7.29165 | 346 | Latin 1 / Western European | Korean - Korea | RT_STRING |
10 | 7.4032 | 610 | Latin 1 / Western European | Korean - Korea | RT_STRING |
Imports
COMDLG32.dll |
KERNEL32.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
48
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Users\admin\AppData\Local\Temp\Driver\Samsung_MonSetup_091006.exe" | C:\Users\admin\AppData\Local\Temp\Driver\Samsung_MonSetup_091006.exe | 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe | ||||||||||||
User: admin Company: Macrovision Corporation Integrity Level: HIGH Description: Setup.exe Exit code: 0 Version: 12.0.49974 Modules
| |||||||||||||||
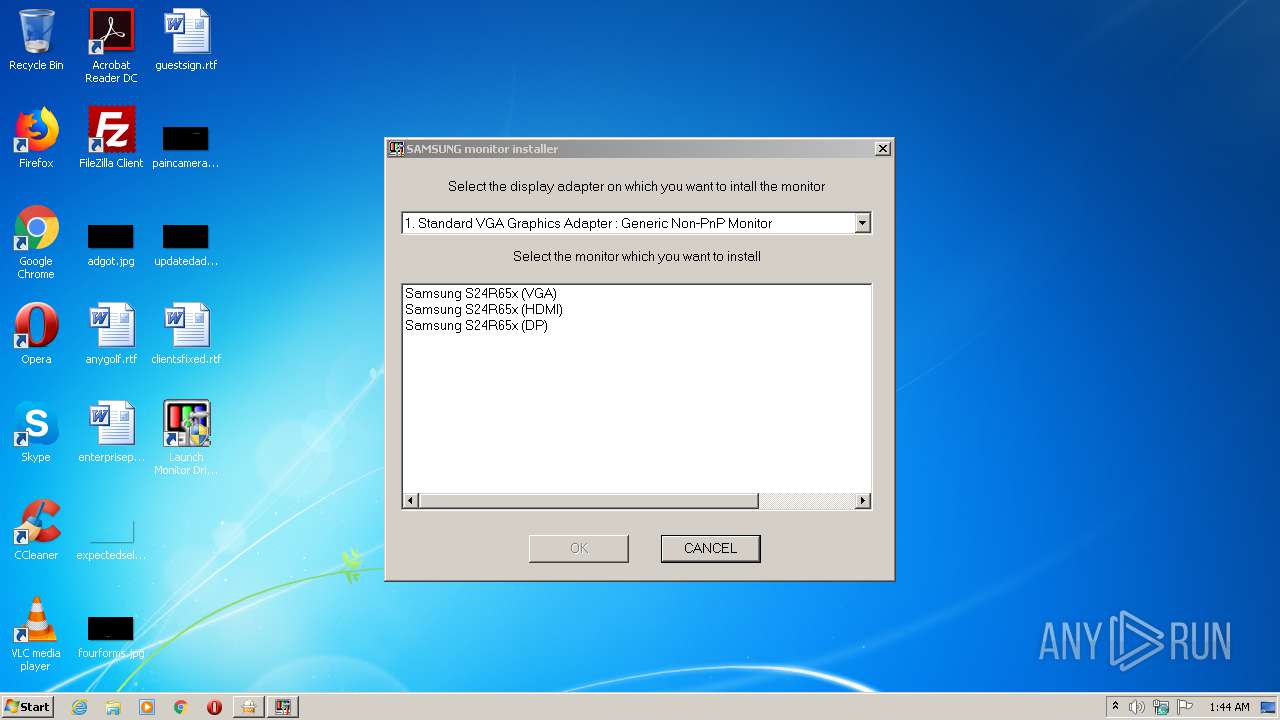
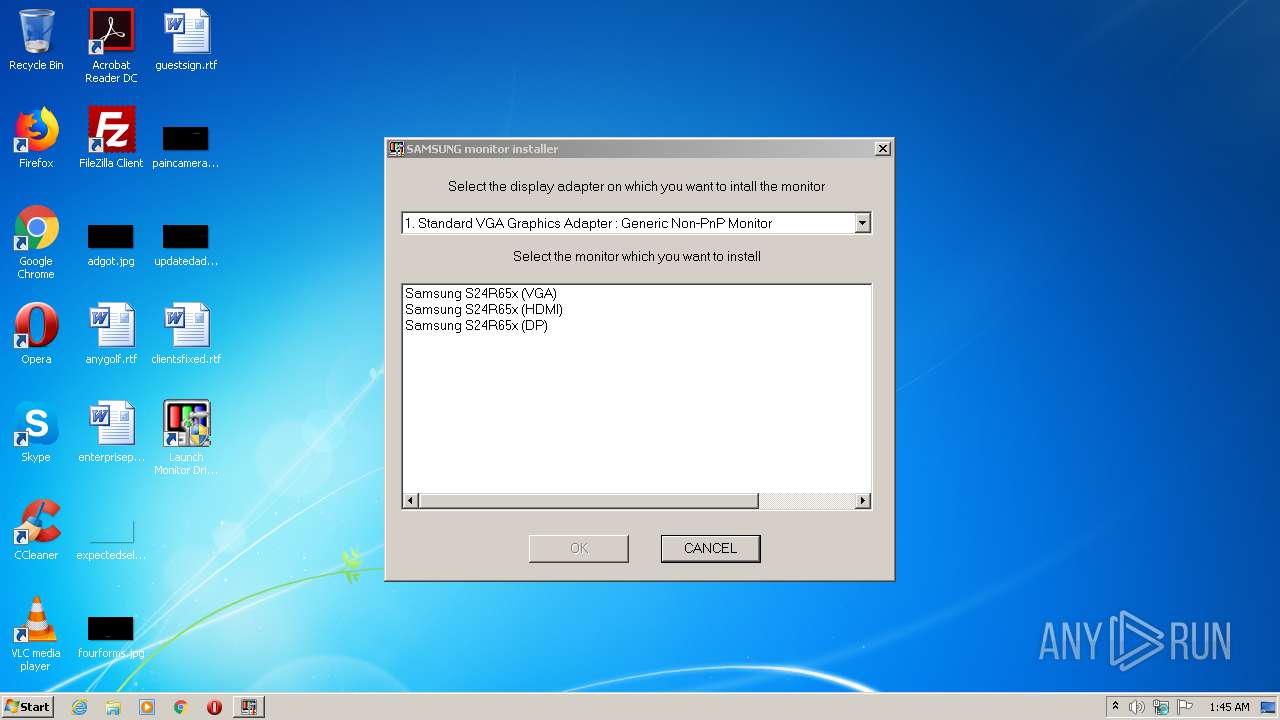
| 1280 | "C:\Program Files\MonitorDriver\MonSetup.exe" | C:\Program Files\MonitorDriver\MonSetup.exe | — | Samsung_MonSetup_091006.exe | |||||||||||
User: admin Company: Samsung Electronics Integrity Level: HIGH Description: MonSetup32 Exit code: 0 Version: 2, 0, 0, 1 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\MonitorDriver\vcredist_x86.exe" "/q:a" | C:\Program Files\MonitorDriver\vcredist_x86.exe | Samsung_MonSetup_091006.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2008 Redistributable Setup Exit code: 0 Version: 9.0.21022.08 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\AppData\Local\Temp\7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe" | C:\Users\admin\AppData\Local\Temp\7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe | explorer.exe | ||||||||||||
User: admin Company: ESTsoft Corp. Integrity Level: MEDIUM Description: ALZip Self Extractor Exit code: 1 Version: 16, 7, 11, 0 Modules
| |||||||||||||||
| 3348 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3348 | "C:\Users\admin\AppData\Local\Temp\Driver\Samsung_MonSetup_091006.exe" | C:\Users\admin\AppData\Local\Temp\Driver\Samsung_MonSetup_091006.exe | — | 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe | |||||||||||
User: admin Company: Macrovision Corporation Integrity Level: MEDIUM Description: Setup.exe Exit code: 3221226540 Version: 12.0.49974 Modules
| |||||||||||||||
| 3660 | c:\202cd223f1821d5a24\.\install.exe "/q:a" | c:\202cd223f1821d5a24\install.exe | — | vcredist_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: External Installer Exit code: 0 Version: 9.0.21022.8 built by: RTM Modules
| |||||||||||||||
Total events
679
Read events
606
Write events
73
Delete events
0
Modification events
| (PID) Process: | (3088) 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3088) 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3348) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000007E53600AD471D601140D0000A8040000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3348) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 42 | |||
| (PID) Process: | (3348) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000003218650AD471D601140D0000A8040000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3348) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008C7A670AD471D601140D000038010000E80300000100000000000000000000009E1B8AC21F50C14DBF419918F0A9CC3F0000000000000000 | |||
| (PID) Process: | (276) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000008A430F0AD471D60114010000D0050000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (276) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000E4A5110AD471D60114010000D0050000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (276) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 41 | |||
| (PID) Process: | (276) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000A6911D0AD471D60114010000D0050000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
25
Suspicious files
20
Text files
47
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{706C7E8C-8874-4A59-9F0E-A119867623EA}\_ispackdel.ini | text | |
MD5:0388291FBB1A6EDC10820DB538B7E1B5 | SHA256:B41315EB30B426E347DCF82A2D9365E8EF7A1E31A11E83E16AAD997344F0FD3B | |||
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{59629EF6-7D79-49B8-BF81-C1301B32A74E}\{8EA79DBF-D637-448A-89D6-410A087A4493}\setu469a.rra | — | |
MD5:— | SHA256:— | |||
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{706C7E8C-8874-4A59-9F0E-A119867623EA}\Disk1\data1.cab | compressed | |
MD5:FB6965BDB88CFBF43BC62A845F148170 | SHA256:3756E2BFB4245F7488E98B47BD63B292506DB2E81E4713FBD09DF1BEB3EBC744 | |||
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{59629EF6-7D79-49B8-BF81-C1301B32A74E}\{8EA79DBF-D637-448A-89D6-410A087A4493}\lice469a.rra | — | |
MD5:— | SHA256:— | |||
| 3088 | 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe | C:\Users\admin\AppData\Local\Temp\Driver\s24r65x.cat | cat | |
MD5:1F88E7518935AB064EDA6C3EDCA9D49B | SHA256:41B1E19D62F386B42EBB3AB771191E250FD2618CDF5618B43CCFFF61AEF66791 | |||
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{59629EF6-7D79-49B8-BF81-C1301B32A74E}\{8EA79DBF-D637-448A-89D6-410A087A4493}\_ISU469a.rra | — | |
MD5:— | SHA256:— | |||
| 3088 | 7682e484de90c5340ccd6a34273d800aa7506f1c7bbff253012aff2a3c06c9e6.exe | C:\Users\admin\AppData\Local\Temp\Driver\S24R65x.inf | binary | |
MD5:779E9CA6A1FBC7A47DB7F3504907A1B4 | SHA256:E487B10756F8D83902E90BD04654DCE198124F808AA8C2946379D6E6D5013FC6 | |||
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{59629EF6-7D79-49B8-BF81-C1301B32A74E}\core46a9.rra | — | |
MD5:— | SHA256:— | |||
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{706C7E8C-8874-4A59-9F0E-A119867623EA}\Disk1\data1.hdr | compressed | |
MD5:333F557585ED45E69BA5199AFF9A7B72 | SHA256:E543012B9437B10145537D087460770ADF72CEC52F268C42513AFA6B229AF786 | |||
| 276 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{59629EF6-7D79-49B8-BF81-C1301B32A74E}\dotn46a9.rra | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report